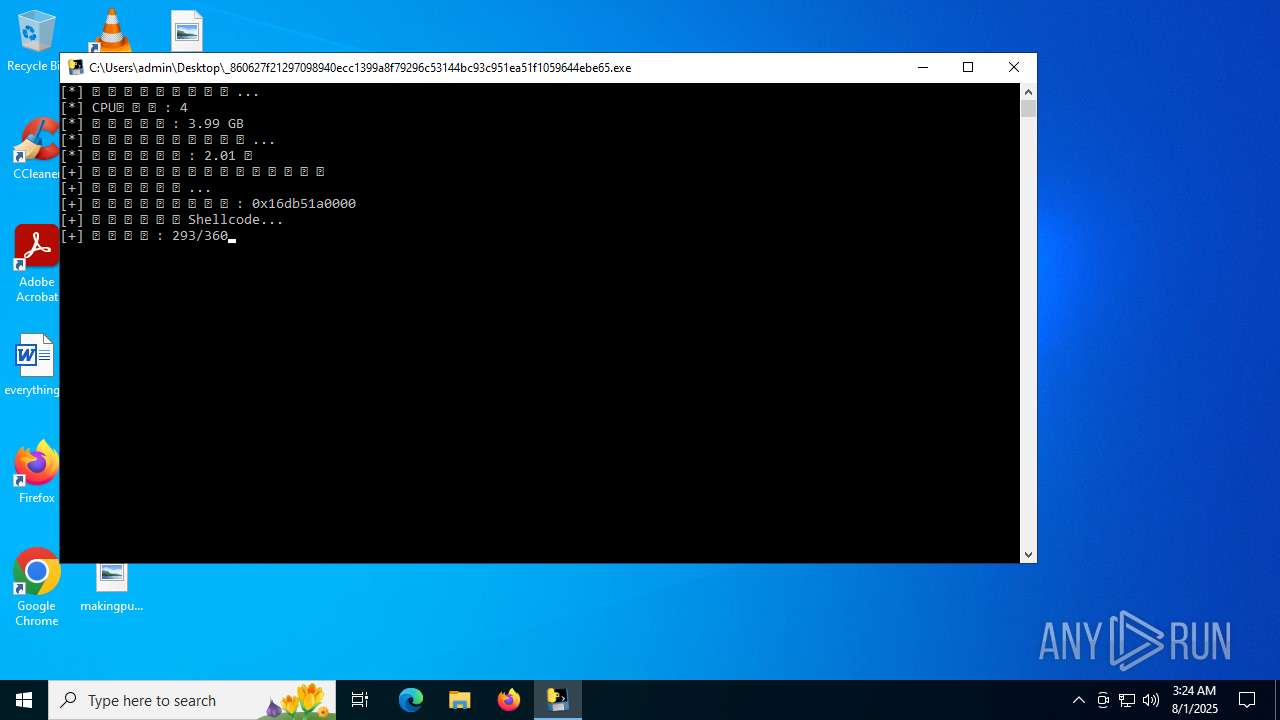
| File name: | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe |
| Full analysis: | https://app.any.run/tasks/a668fd0d-a0a7-47fb-adb6-b640999ded5c |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 03:23:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | E46F7F671C4B5E1A37E7F8F96A13778E |
| SHA1: | 82D824804C70A895733696C308C0406B71B258FE |
| SHA256: | 860627F21297098940ECC1399A8F79296C53144BC93C951EA51F1059644EBE65 |
| SSDEEP: | 98304:7D/lMEIRgsuDg2+acSU5jqV5HnE0Gf+k4l/onUZXFCh0bRor2x5hREcokzJ244LE:EcpP/qIpivyNlw446 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops python dynamic module
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
Process drops legitimate windows executable
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
Executable content was dropped or overwritten
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
Loads Python modules
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 2716)
Application launched itself
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
- updater.exe (PID: 2580)
Connects to unusual port
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 2716)
The process executes via Task Scheduler
- updater.exe (PID: 2580)
The process drops C-runtime libraries
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
INFO
Reads the computer name
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
- updater.exe (PID: 2580)
Checks supported languages
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 2716)
- updater.exe (PID: 2120)
- updater.exe (PID: 2580)
PyInstaller has been detected (YARA)
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 2716)
Create files in a temporary directory
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
Process checks whether UAC notifications are on
- updater.exe (PID: 2580)
Reads the software policy settings
- slui.exe (PID: 4544)
Checks proxy server information
- slui.exe (PID: 4544)
The sample compiled with english language support
- _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe (PID: 640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:07:19 04:06:35+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 179712 |
| InitializedDataSize: | 155136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc650 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
139
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Users\admin\Desktop\_860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe" | C:\Users\admin\Desktop\_860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x214,0x2a4,0x111c460,0x111c46c,0x111c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 2140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\Desktop\_860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe" | C:\Users\admin\Desktop\_860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4544 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 731
Read events
3 731
Write events
0
Delete events
0
Modification events
Executable files
52
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\VCRUNTIME140.dll | executable | |
MD5:4585A96CC4EEF6AAFD5E27EA09147DC6 | SHA256:A8F950B4357EC12CFCCDDC9094CCA56A3D5244B95E09EA6E9A746489F2D58736 | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\_hashlib.pyd | executable | |
MD5:F495D1897A1B52A2B15C20DCECB84B47 | SHA256:E47E76D70D508B62924FE480F30E615B12FDD7745C0AAC68A2CDDABD07B692AE | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\_ctypes.pyd | executable | |
MD5:10FDCF63D1C3C3B7E5861FBB04D64557 | SHA256:BC3B83D2DC9E2F0E6386ED952384C6CF48F6EED51129A50DFD5EF6CBBC0A8FB3 | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\_socket.pyd | executable | |
MD5:899380B2D48DF53414B974E11BB711E3 | SHA256:B38E66E6EE413E5955EF03D619CADD40FCA8BE035B43093D2342B6F3739E883E | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\_decimal.pyd | executable | |
MD5:21C73E7E0D7DAD7A1FE728E3B80CE073 | SHA256:A28C543976AA4B6D37DA6F94A280D72124B429F458D0D57B7DBCF71B4BEA8F73 | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:6177998C2CE574A177E524746B77EFE7 | SHA256:A0AA340274D4BB46B6D9547D647AB7DC16C229577BBAB836E6A4F3307F310332 | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:7699C096202DA0DB6B07FAFC914D60ED | SHA256:0052515763A1A31D2527A2EB2523FB7B88D8E55C4E4DA5EF352B565476BF21E0 | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:928BE2A3FC2E88BDA5CA0808324E97C4 | SHA256:CC6C2FDF1C34FA82036165B111F91220BCF7E43AAB79DFB284F982F0590BEBB1 | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:C2CD29370B21C0361D7F79D248C05860 | SHA256:550B4F5BA95108B01A24F05496576A4E73642334A10DDE61B09846E0EFB9F260 | |||
| 640 | _860627f21297098940ecc1399a8f79296c53144bc93c951ea51f1059644ebe65.exe | C:\Users\admin\AppData\Local\Temp\_MEI6402\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:E93F34FDCD8E5FFC34AF48C90F6F95D1 | SHA256:ECA63FC5C873CE8B36C507E2B9A88CAAEA9617C84669886B15F6BC38BD0024C6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
52
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5504 | RUXIMICS.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
5504 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
— | — | POST | 200 | 40.126.31.3:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.3:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 16.7 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.73:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5504 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5504 | RUXIMICS.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |