| File name: | MerakiPCCAgent.msi |
| Full analysis: | https://app.any.run/tasks/77811bb6-6f6a-4acb-9cf9-1c10428c9c58 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2020, 06:59:52 |
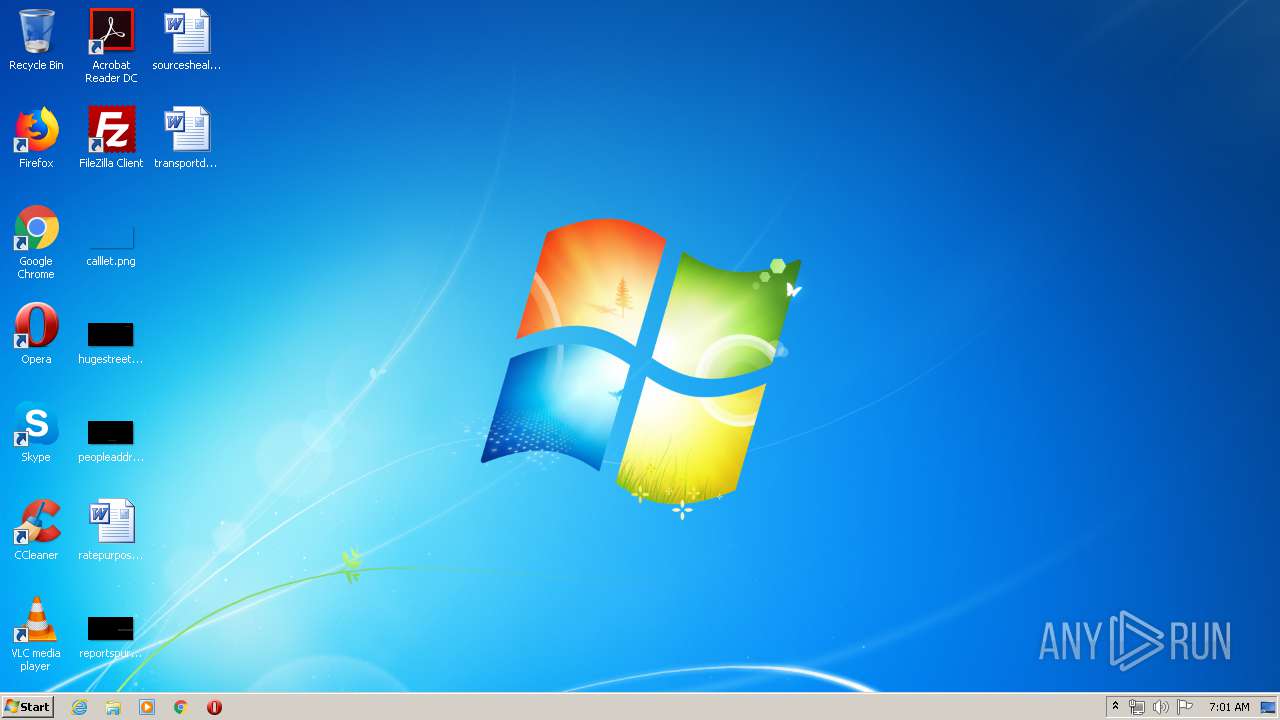
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
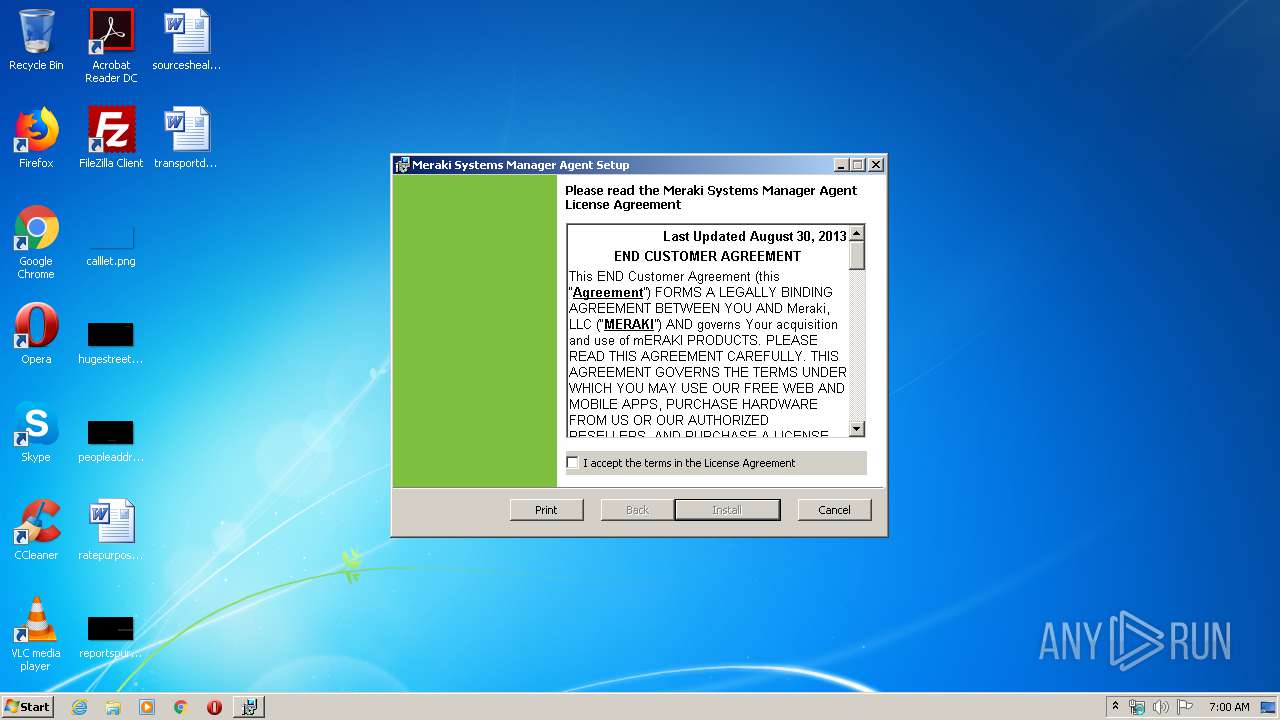
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Meraki Systems Manager Agent Installer, Author: Meraki, Inc., Keywords: Installer, Comments: This installer database contains the logic and data required to install Meraki Systems Manager Agent., Template: Intel;1033, Revision Number: {2A0C5B3F-8516-42A5-944A-8A996F186531}, Create Time/Date: Thu Jun 7 21:52:20 2018, Last Saved Time/Date: Thu Jun 7 21:52:20 2018, Number of Pages: 301, Number of Words: 2, Name of Creating Application: Windows Installer XML (3.0.5419.0), Security: 2 |
| MD5: | 1C6747E40832602BA6E3482FC1F81A9E |
| SHA1: | F6B352C044FD08F6B5F303E159263AB48A529E9A |
| SHA256: | 8604B5C0CF6BA6A63FF7DA29E80F554067086C110173C6A39113E03621AAD660 |
| SSDEEP: | 98304:Njf4duMkvdusy0DHQsyBtmEOBsooFaX3W+XRwdiTTVJYPgNTvYfNNhq17jMdBWvu:NjS7kvdu2DHDdEOBsSXR/LIhqJjMdgcj |
MALICIOUS
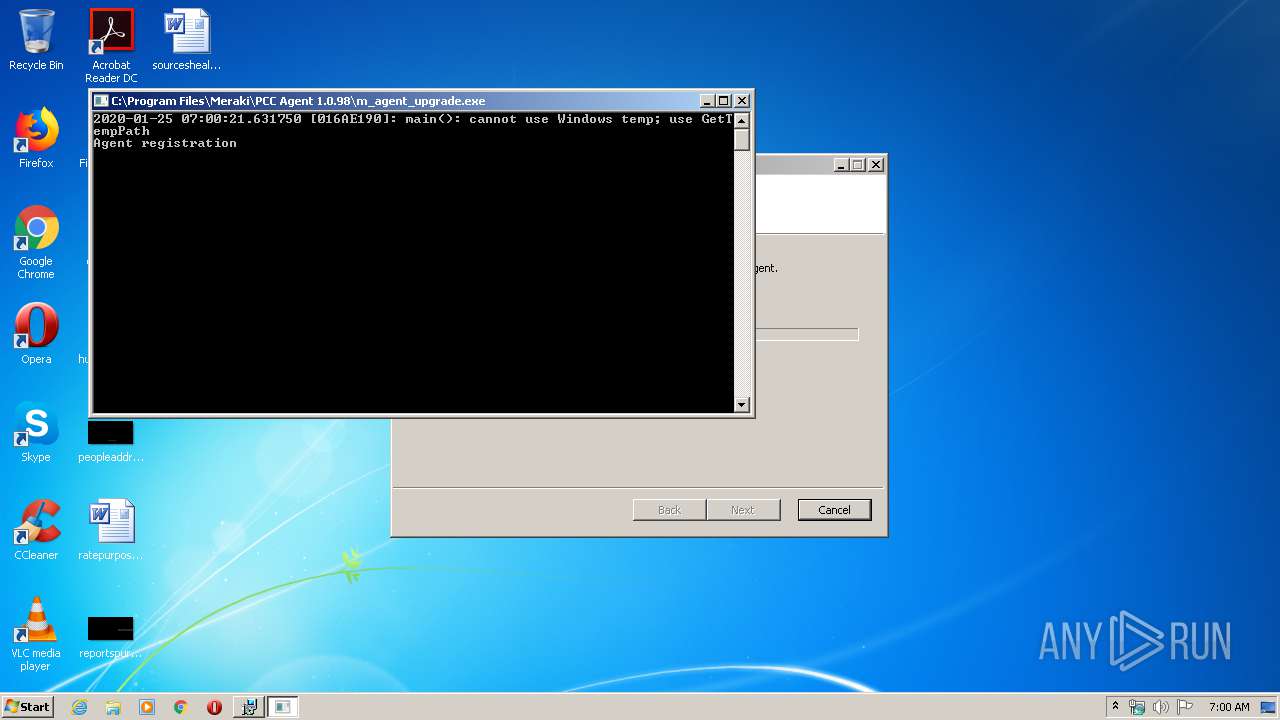
Application was dropped or rewritten from another process
- m_agent_service.exe (PID: 2128)
- m_agent_upgrade.exe (PID: 2124)
- windows_wlan.exe (PID: 4580)
- windows_wlan.exe (PID: 3996)
- ndisscan.exe (PID: 5836)
SUSPICIOUS
Executed as Windows Service
- vssvc.exe (PID: 4008)
- m_agent_service.exe (PID: 2128)
Executes scripts
- cmd.exe (PID: 3720)
- cmd.exe (PID: 2500)
- cmd.exe (PID: 2364)
- m_agent_service.exe (PID: 2128)
- cmd.exe (PID: 3504)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3468)
Creates files in the Windows directory
- m_agent_upgrade.exe (PID: 2124)
- m_agent_service.exe (PID: 2128)
Starts CMD.EXE for commands execution
- m_agent_upgrade.exe (PID: 2124)
- m_agent_service.exe (PID: 2128)
Removes files from Windows directory
- m_agent_service.exe (PID: 2128)
Uses NETSH.EXE for network configuration
- m_agent_service.exe (PID: 2128)
Connects to unusual port
- m_agent_service.exe (PID: 2128)
Modifies files in Chrome extension folder
- chrome.exe (PID: 576)
Executed via COM
- DllHost.exe (PID: 4576)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3168)
- cmd.exe (PID: 5056)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3056)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 5056)
Searches for installed software
- reg.exe (PID: 1756)
- reg.exe (PID: 4080)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 4008)
Reads settings of System Certificates
- msiexec.exe (PID: 3468)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 952)
Creates files in the program directory
- msiexec.exe (PID: 3468)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3468)
- chrome.exe (PID: 3232)
Reads the hosts file
- chrome.exe (PID: 3232)
- chrome.exe (PID: 5864)
- chrome.exe (PID: 576)
- chrome.exe (PID: 952)
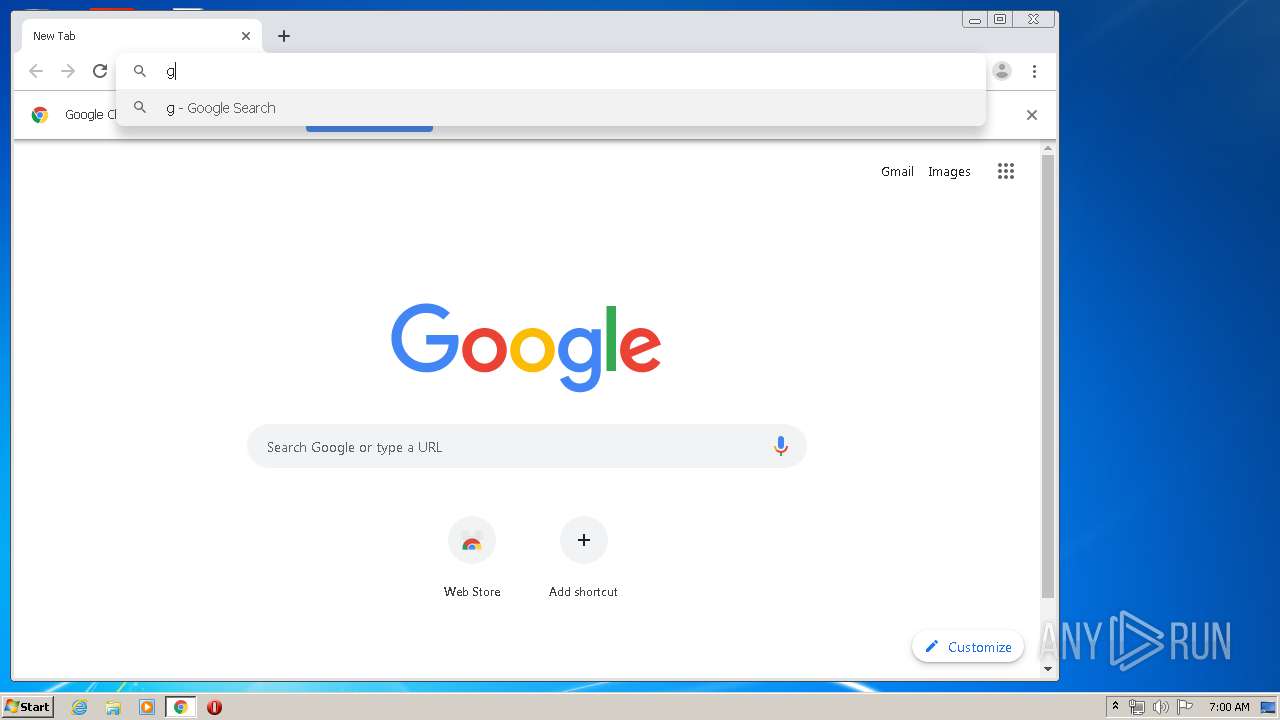
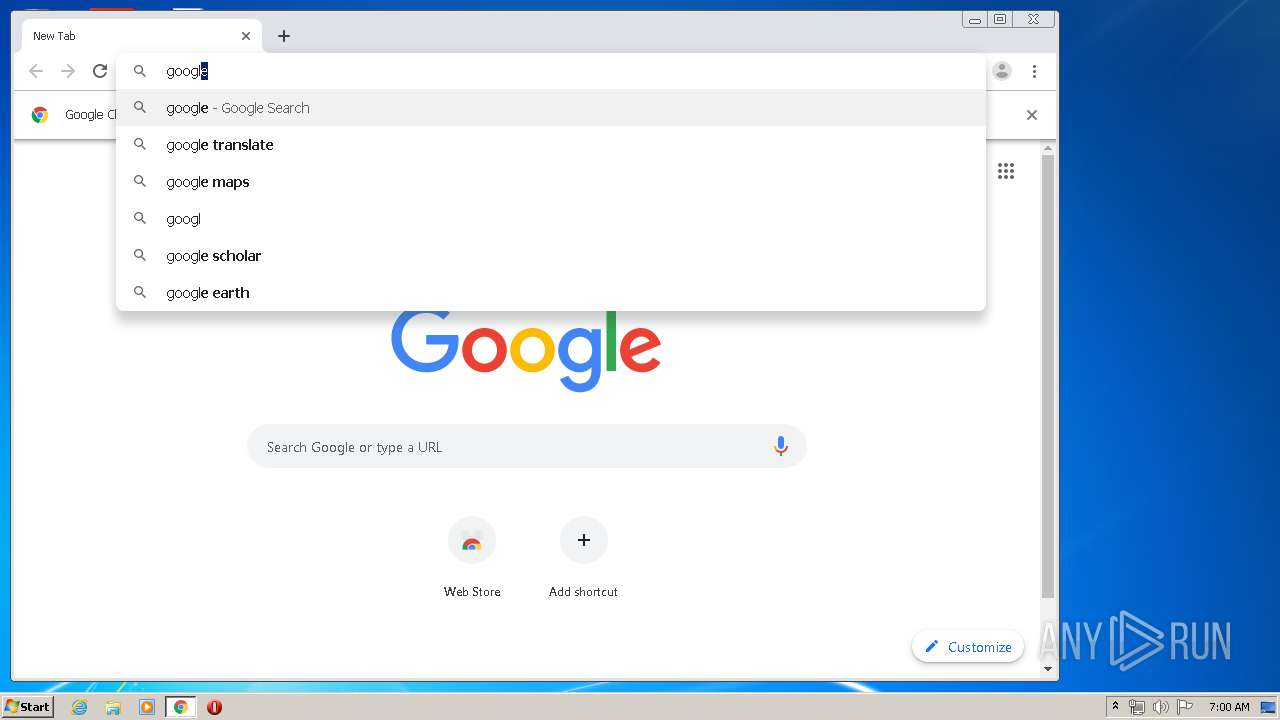
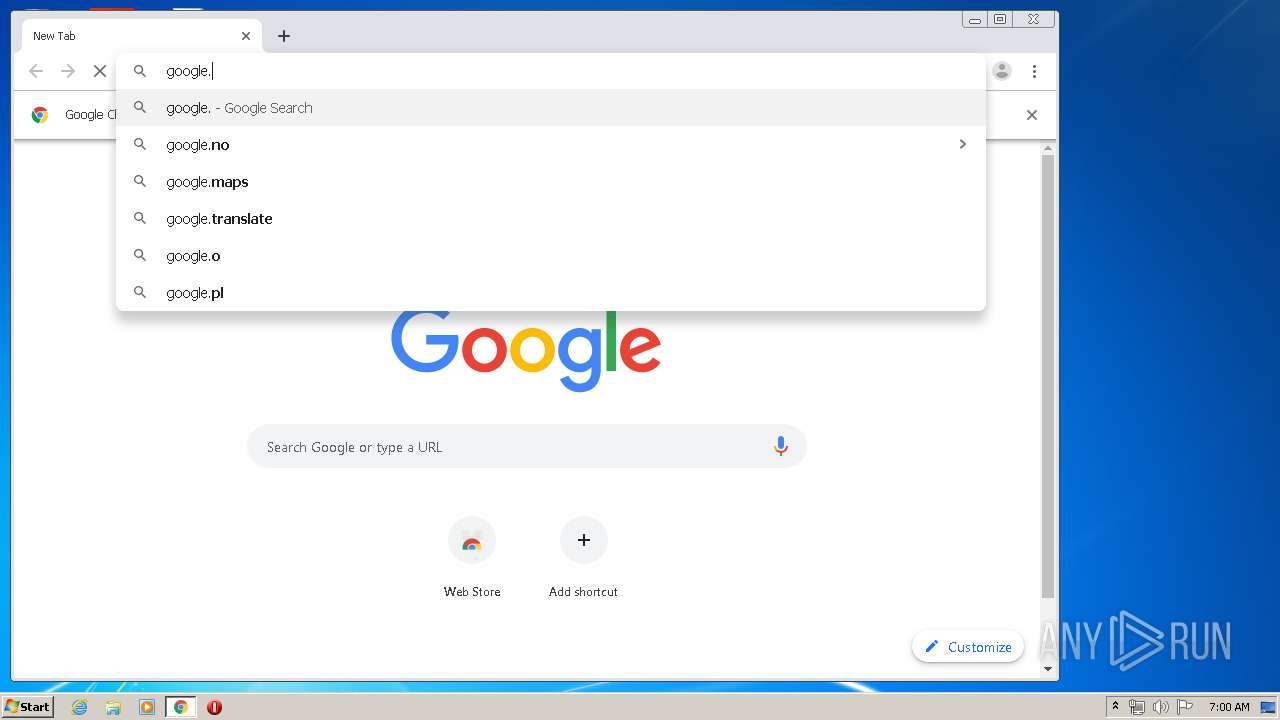
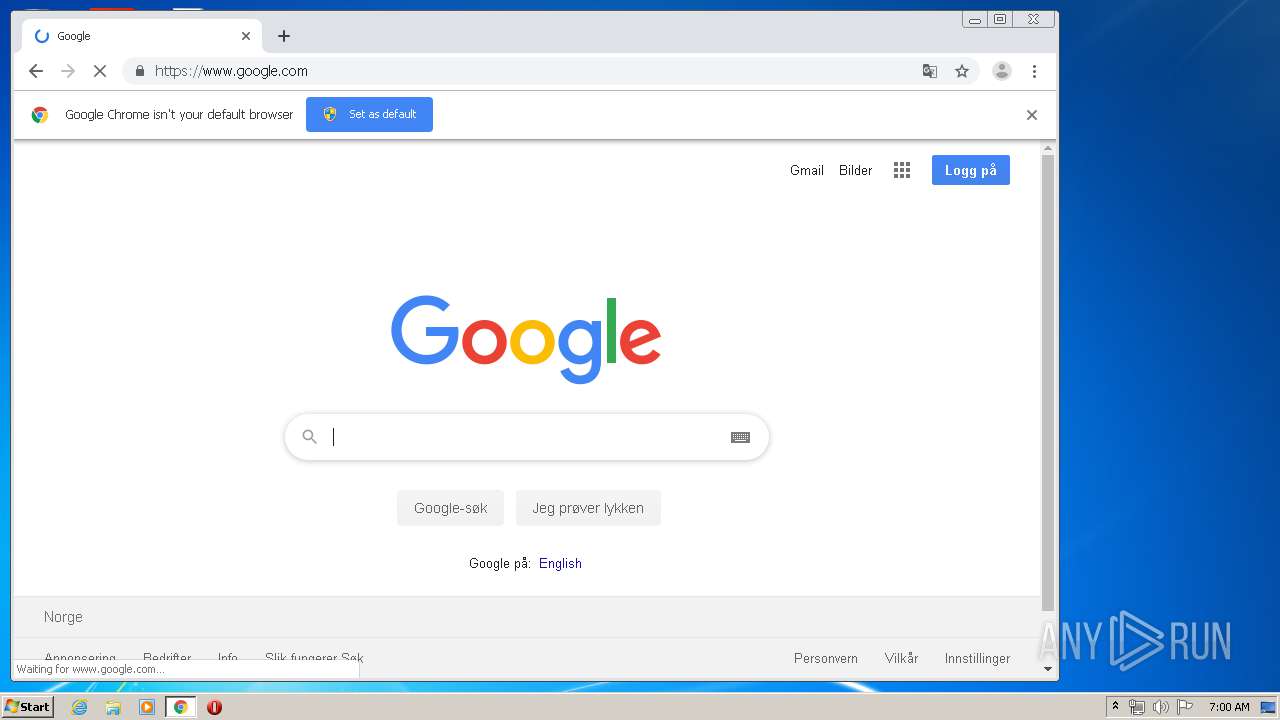
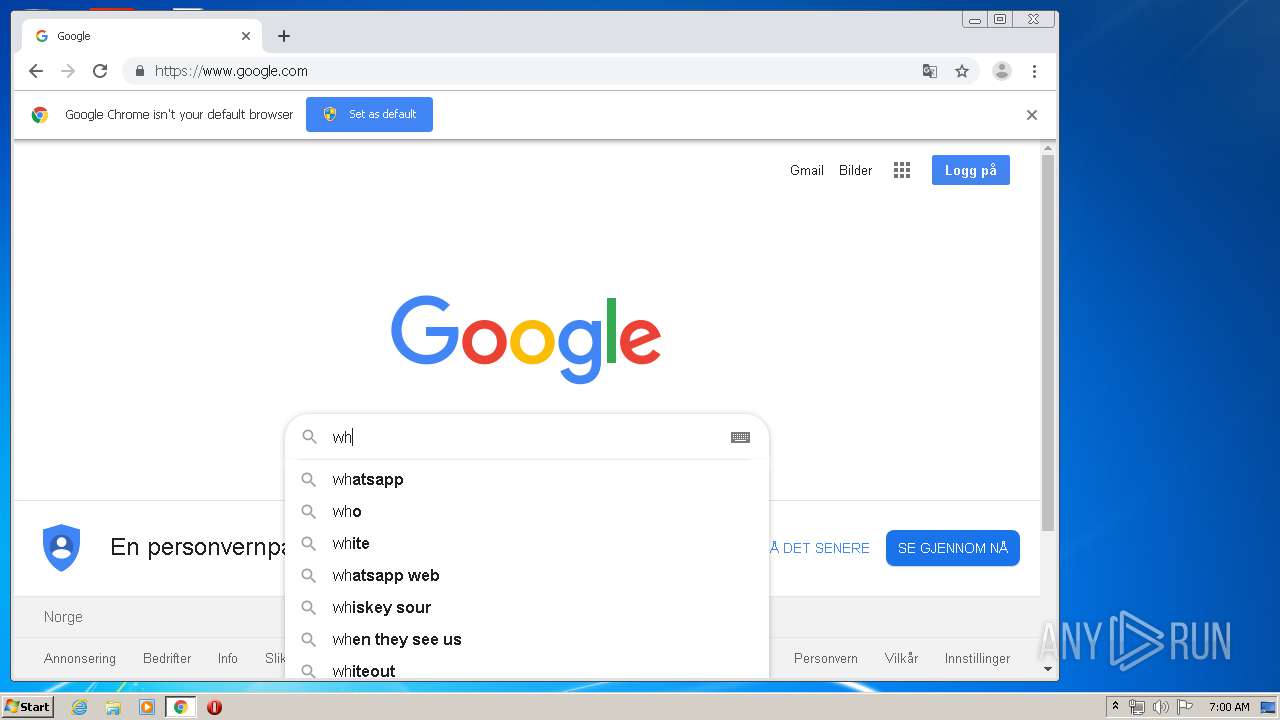
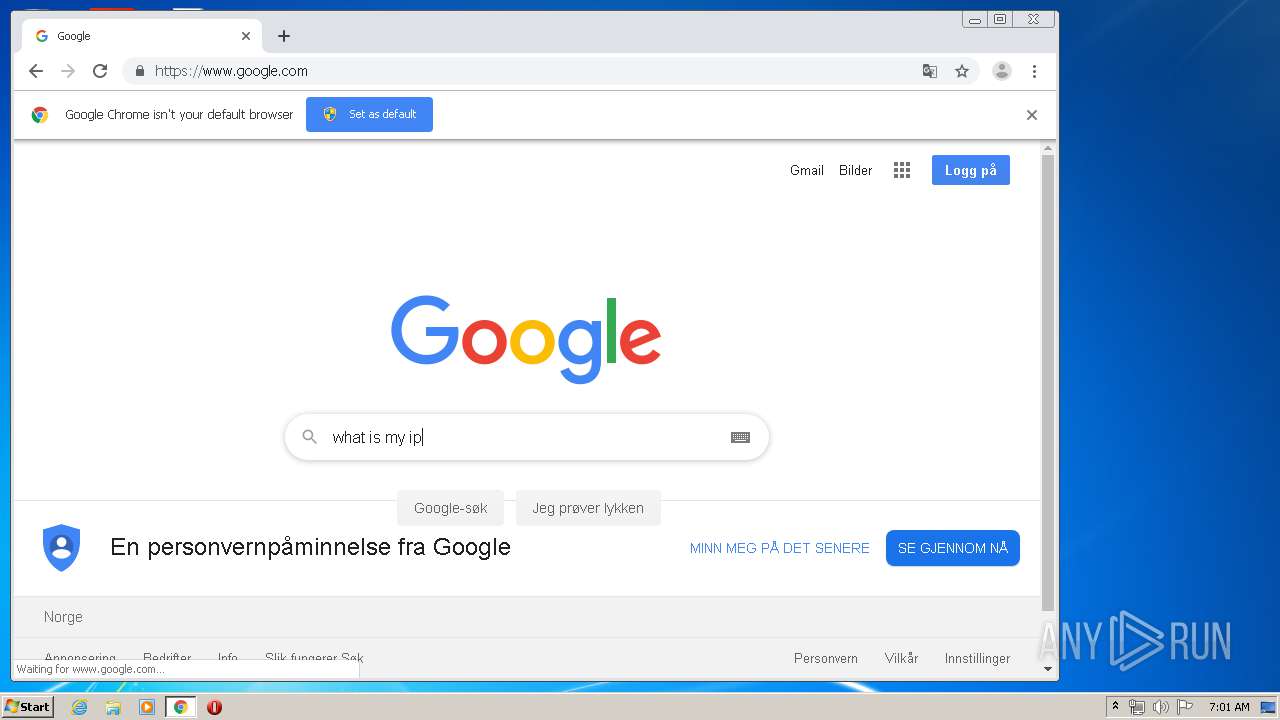
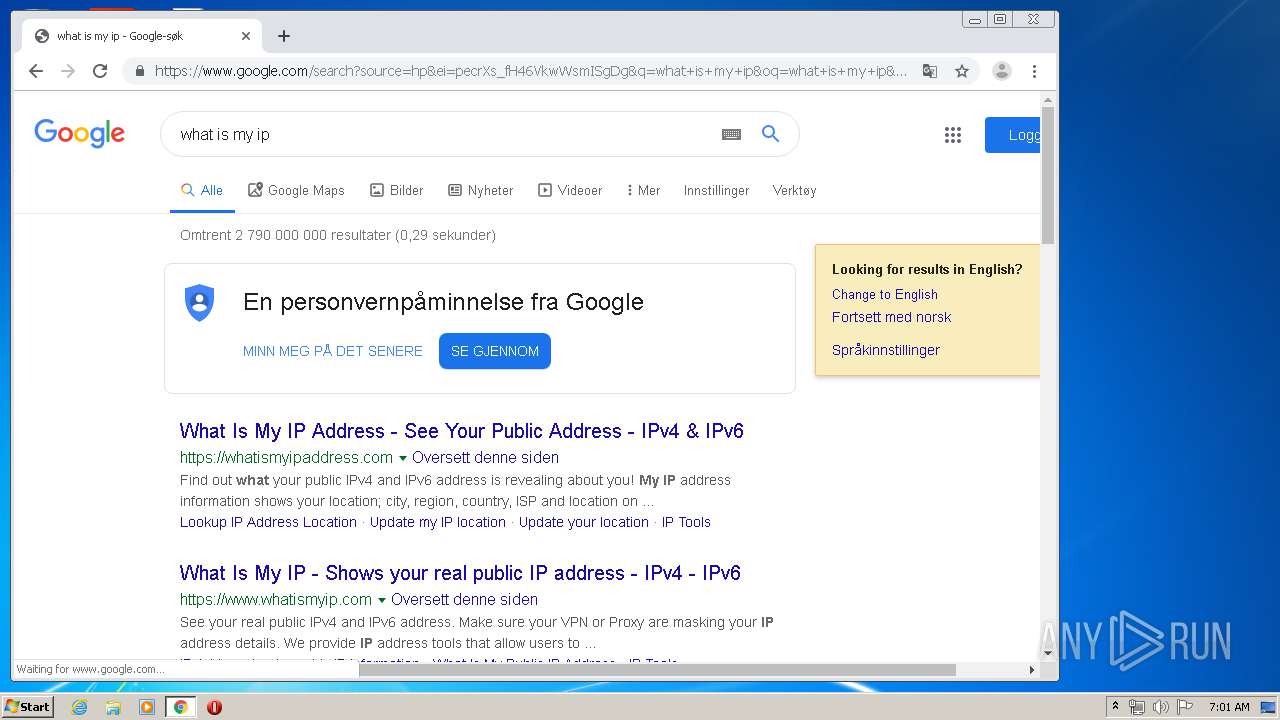
Manual execution by user
- chrome.exe (PID: 5864)
- chrome.exe (PID: 576)
Application launched itself
- chrome.exe (PID: 576)
- chrome.exe (PID: 5864)
Creates a software uninstall entry
- msiexec.exe (PID: 3468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Meraki Systems Manager Agent Installer |
| Author: | Meraki, Inc. |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Meraki Systems Manager Agent. |
| Template: | Intel;1033 |
| RevisionNumber: | {2A0C5B3F-8516-42A5-944A-8A996F186531} |
| CreateDate: | 2018:06:07 20:52:20 |
| ModifyDate: | 2018:06:07 20:52:20 |
| Pages: | 301 |
| Words: | 2 |
| Software: | Windows Installer XML (3.0.5419.0) |
| Security: | Read-only recommended |
Total processes
210
Monitored processes
123
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | netstat -p tcp | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12781179115304549131,8382363103850851954,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2665603294910320810 --mojo-platform-channel-handle=4028 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13253511017880970330,3118814014257024358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=880086234631450401 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | C:\Windows\system32\cscript.exe //E:vbscript //Nologo C:\Windows\TEMP\m_aBC36.tmp | C:\Windows\system32\cscript.exe | — | m_agent_service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1352 | C:\Windows\System32\netsh.exe wlan show interfaces | C:\Windows\System32\netsh.exe | — | m_agent_service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12781179115304549131,8382363103850851954,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10197197667942534770 --mojo-platform-channel-handle=3336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12781179115304549131,8382363103850851954,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7565003428839516029 --mojo-platform-channel-handle=4116 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d36a9d0,0x6d36a9e0,0x6d36a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,12781179115304549131,8382363103850851954,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2845939977260905946 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
11 440
Read events
10 189
Write events
1 230
Delete events
21
Modification events
| (PID) Process: | (3332) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000982166154DD3D5018C0D0000040F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000F28368154DD3D5018C0D0000040F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000001681A6154DD3D5018C0D0000040F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3468) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000001681A6154DD3D5018C0D0000EC0E0000E8030000010000000000000000000000DCAD6DEF728B5A4DB030C8F2E3FE129F0000000000000000 | |||
| (PID) Process: | (4008) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000032CFB4154DD3D501A80F000008080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4008) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000032CFB4154DD3D501A80F0000E40C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4008) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000032CFB4154DD3D501A80F0000600C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4008) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000032CFB4154DD3D501A80F000078010000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
166
Text files
246
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3468 | msiexec.exe | C:\Windows\Installer\a6989e.msi | — | |
MD5:— | SHA256:— | |||
| 3468 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF02BD06308BAFC978.TMP | — | |
MD5:— | SHA256:— | |||
| 4008 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2128 | m_agent_service.exe | C:\Windows\TEMP\m_aB87B.tmp | — | |
MD5:— | SHA256:— | |||
| 2128 | m_agent_service.exe | C:\Windows\TEMP\m_aBC36.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | msiexec.exe | C:\Windows\Installer\a698a1.msi | — | |
MD5:— | SHA256:— | |||
| 3468 | msiexec.exe | C:\Config.Msi\a698a0.rbs | — | |
MD5:— | SHA256:— | |||
| 3468 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF4571CE56588BA78D.TMP | — | |
MD5:— | SHA256:— | |||
| 576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E2BE79E-240.pma | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
254
DNS requests
166
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
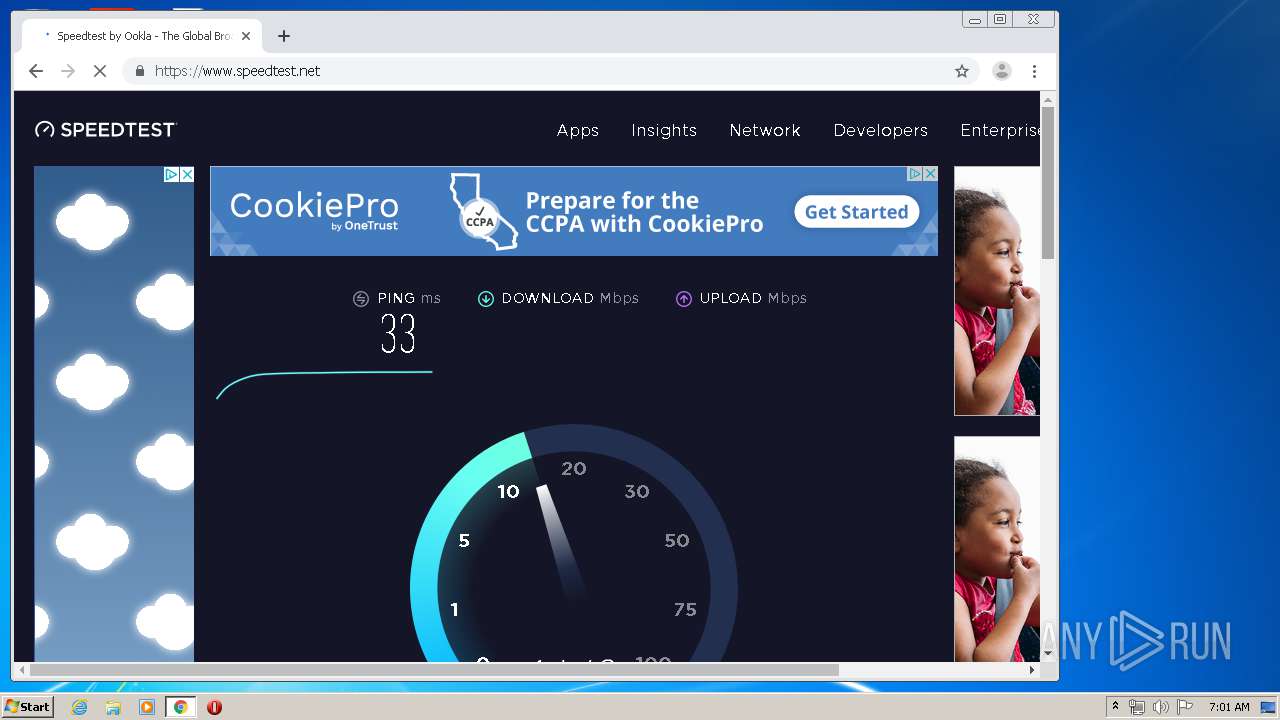
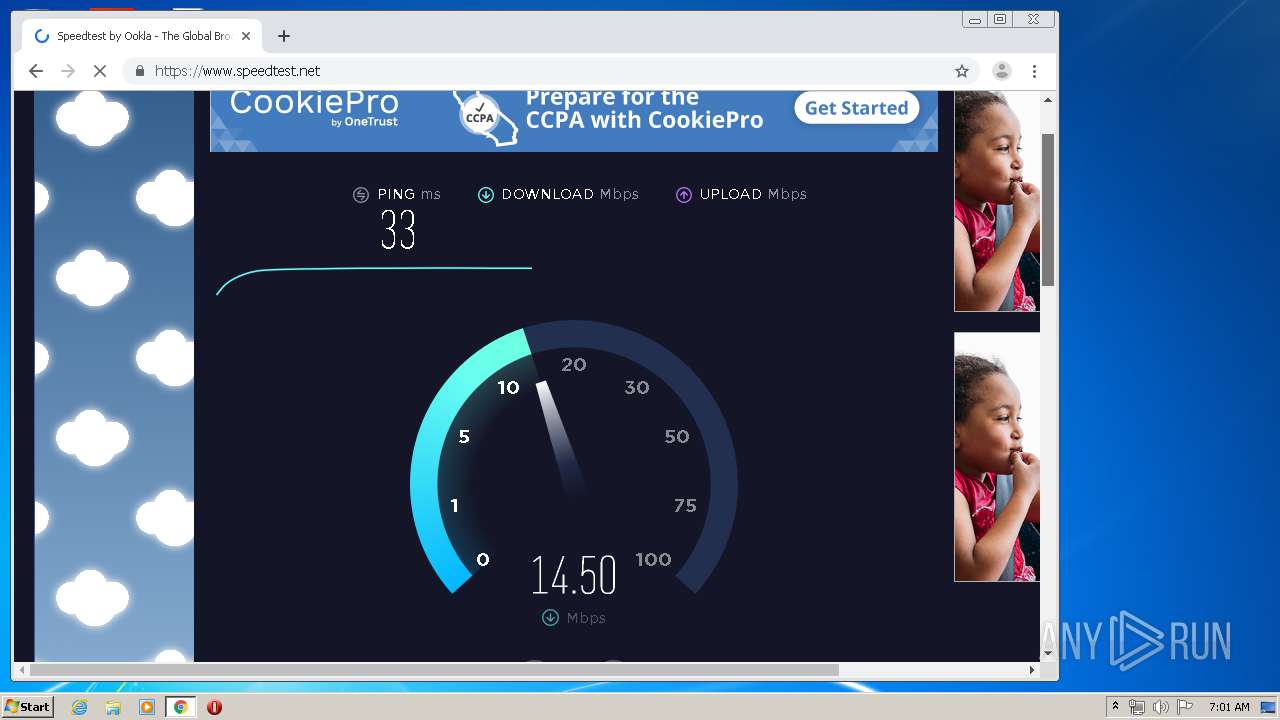
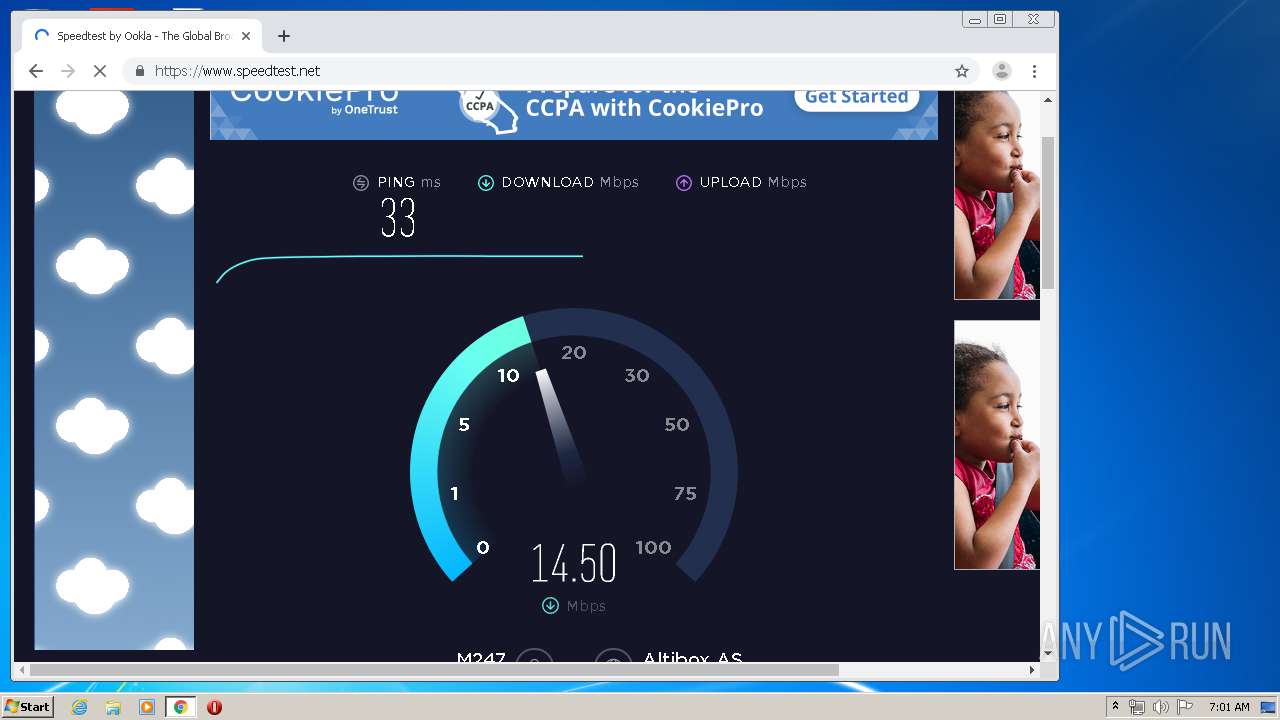
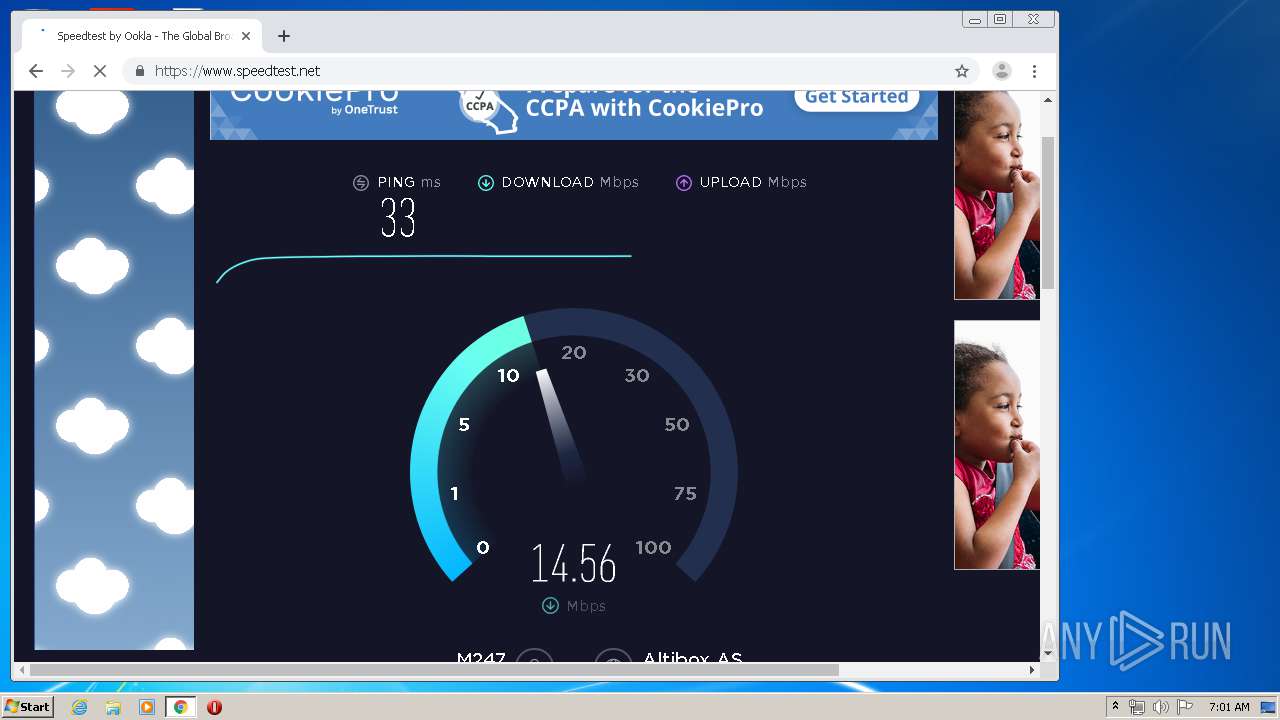
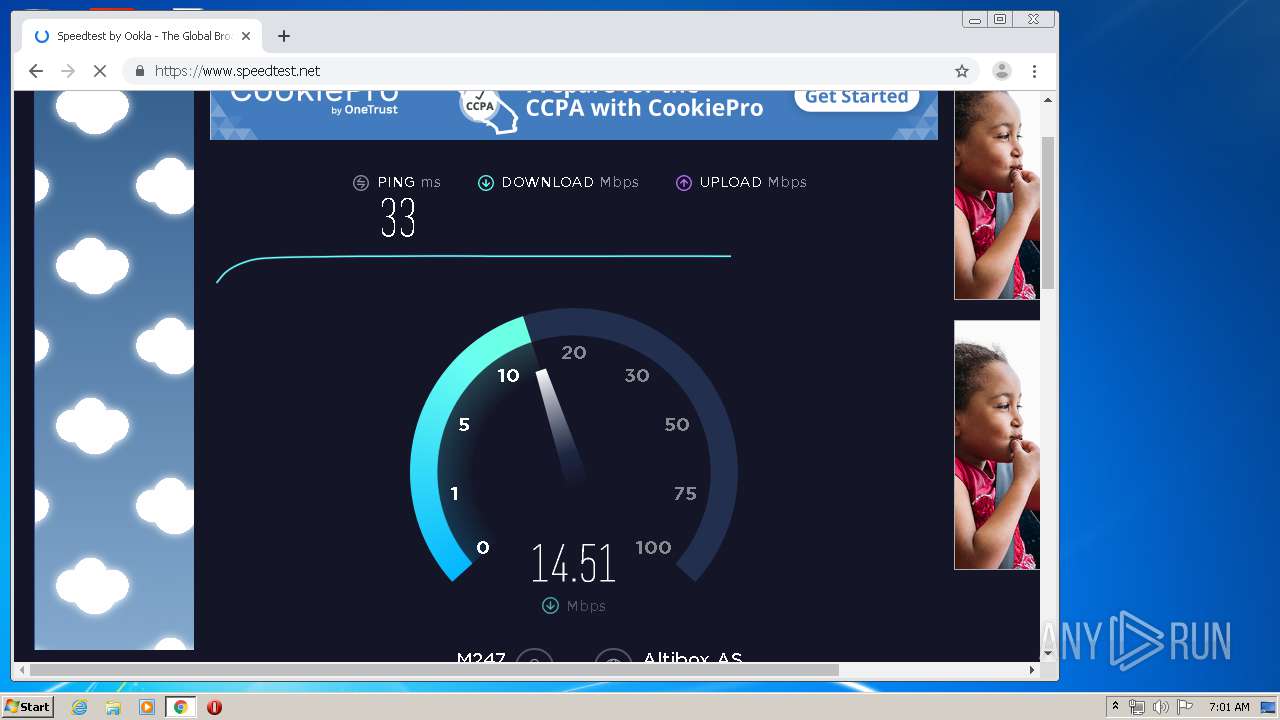
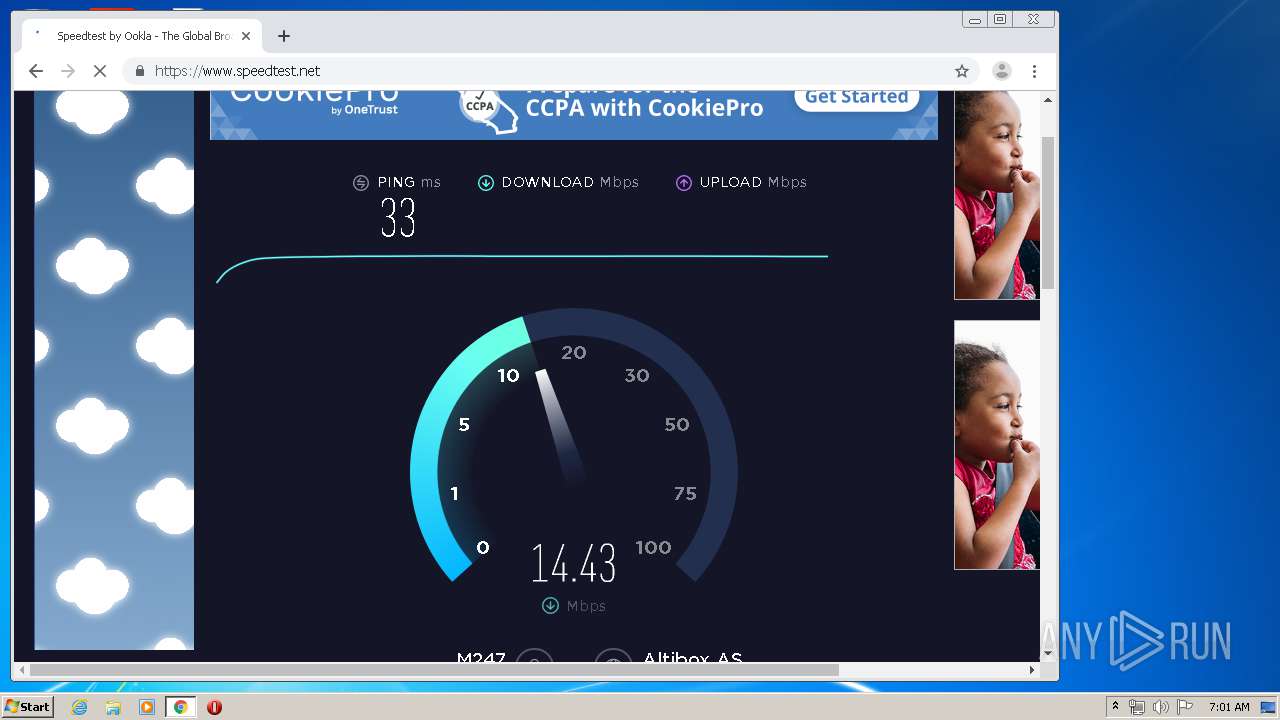
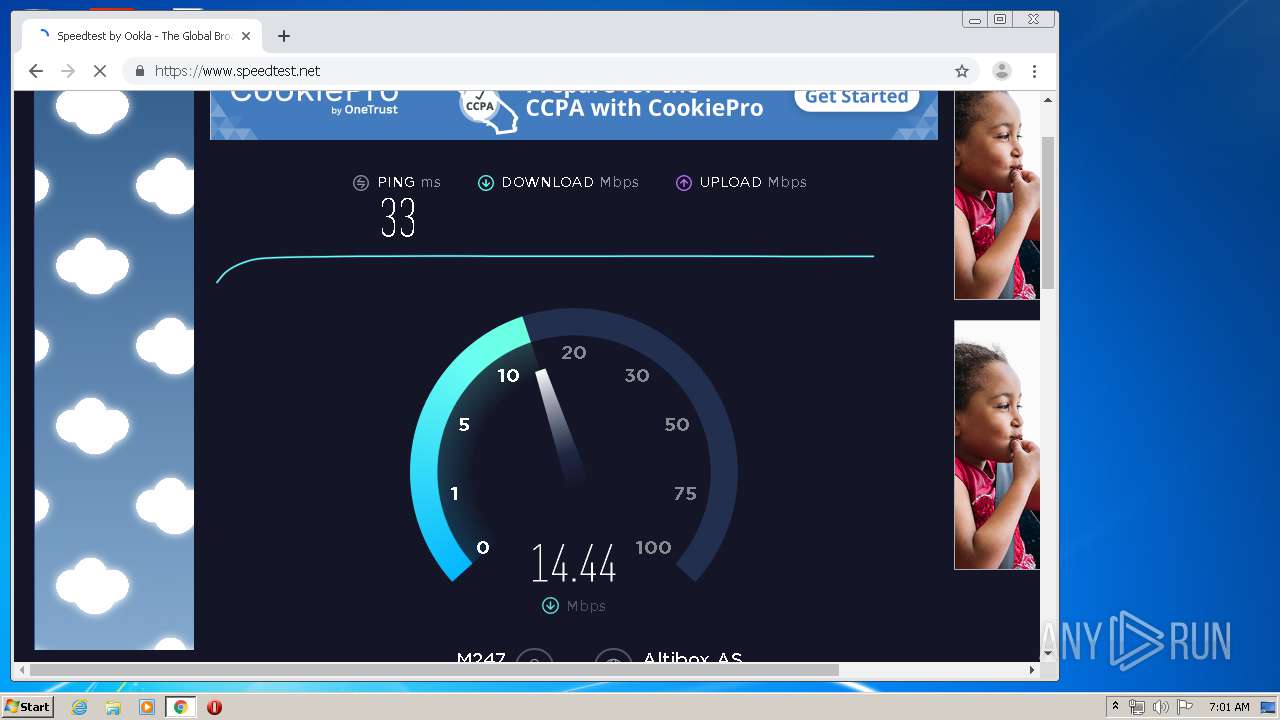
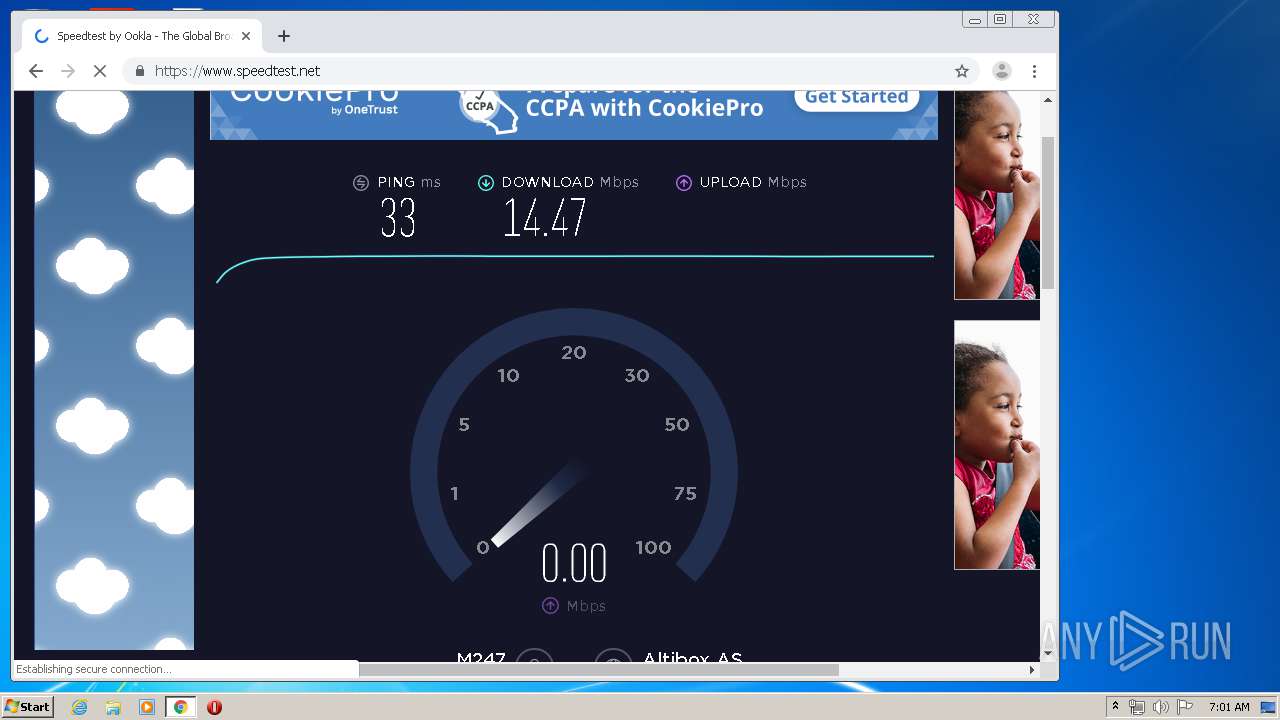
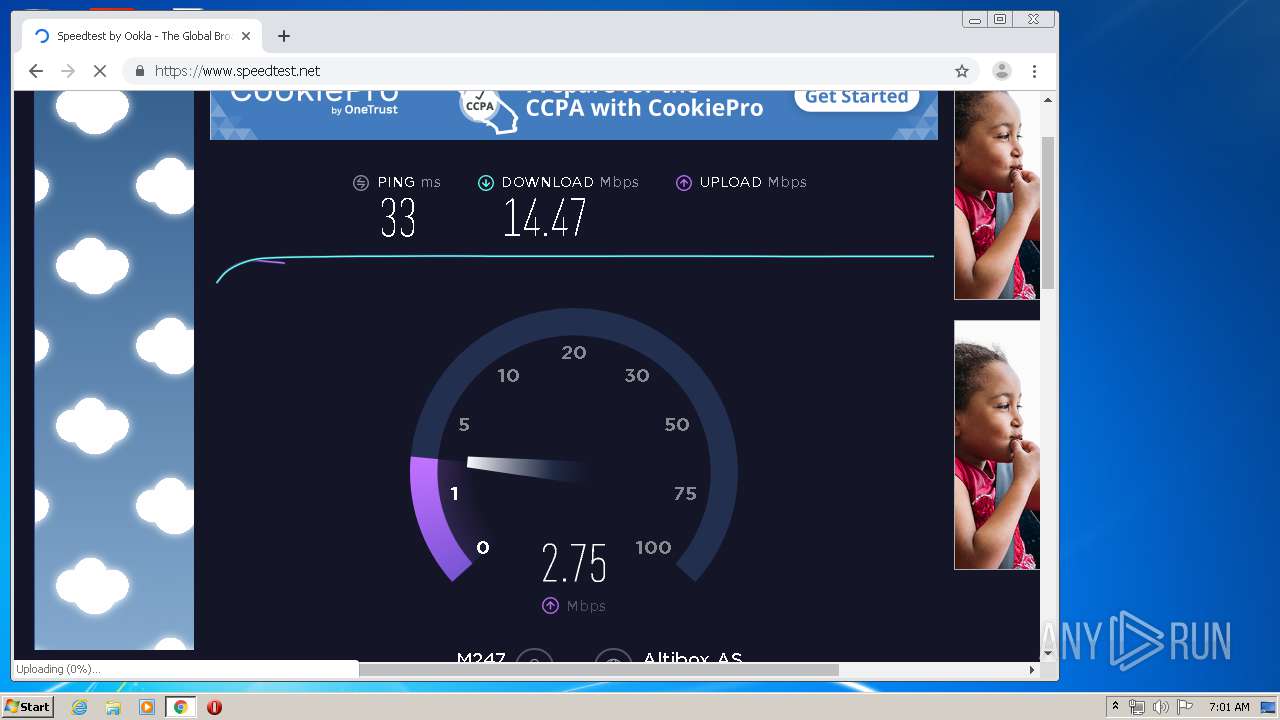
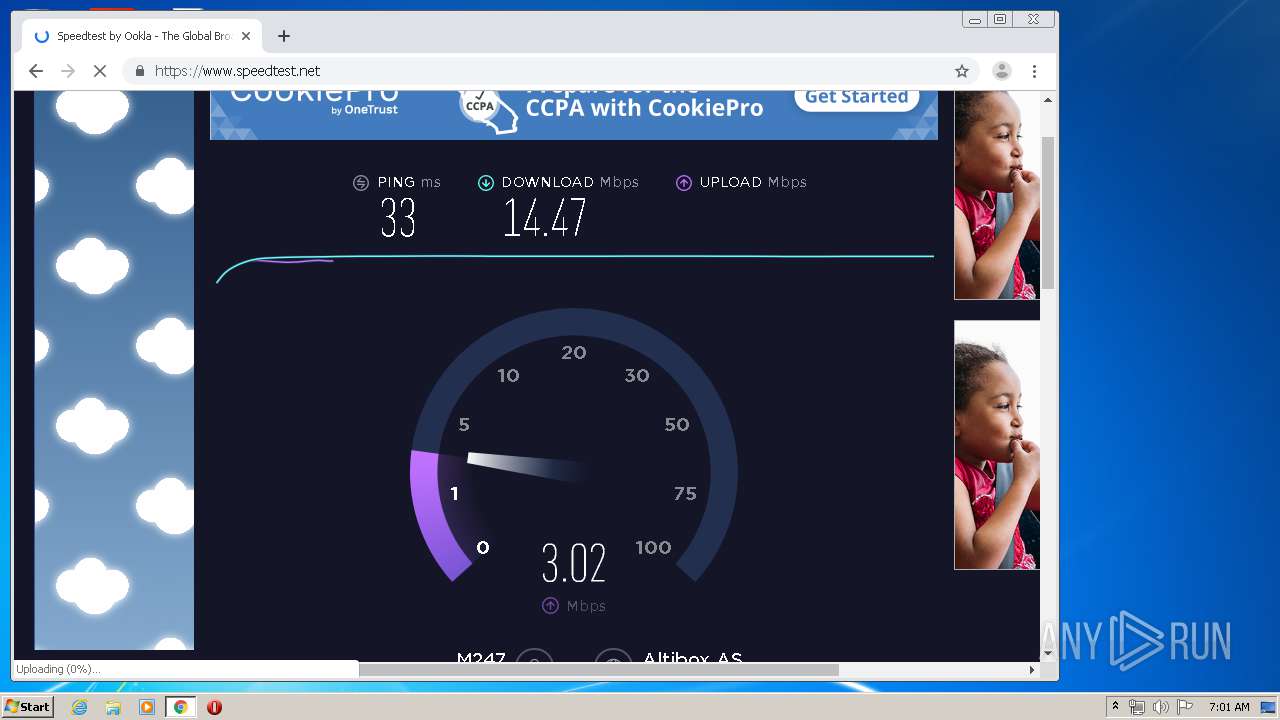
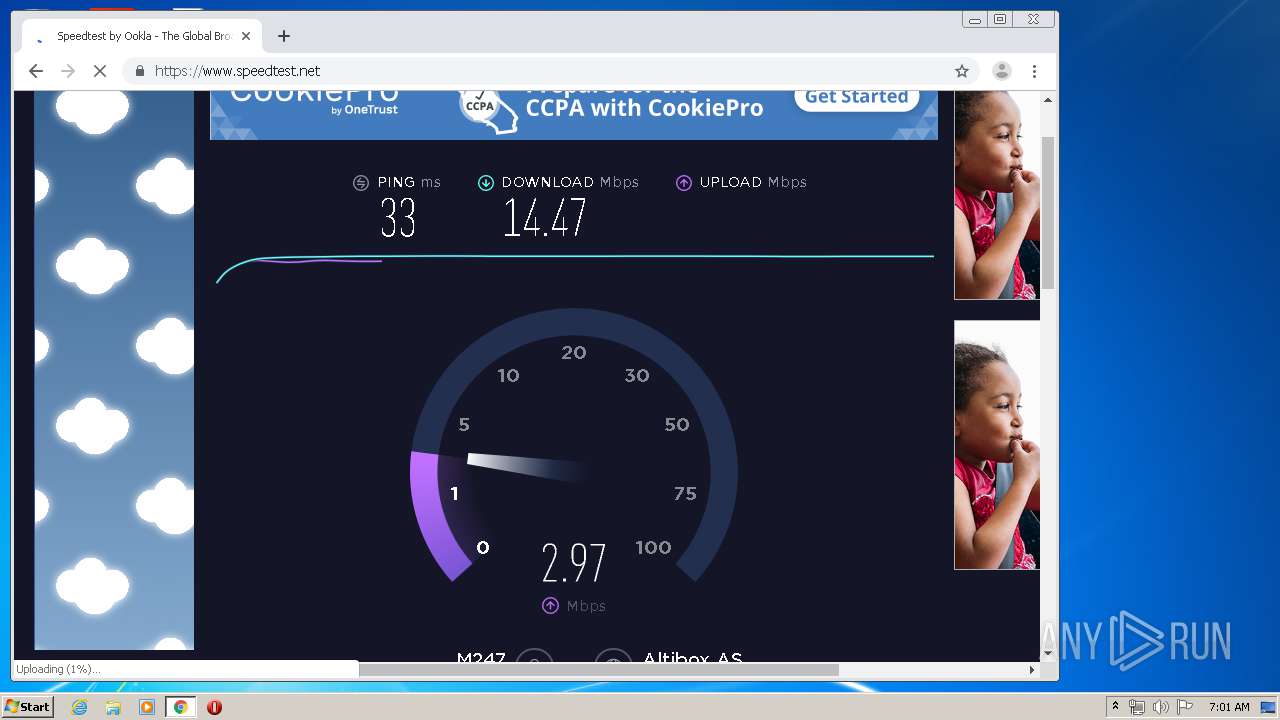
3232 | chrome.exe | GET | 301 | 151.101.194.219:80 | http://speedtest.net/ | US | — | — | whitelisted |
3232 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3232 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3232 | chrome.exe | GET | 200 | 74.125.110.137:80 | http://r4---sn-5goeen7y.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=45.12.223.184&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1579935342&mv=u&mvi=3&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3232 | chrome.exe | GET | 200 | 173.194.150.219:80 | http://r5---sn-5goeen7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=45.12.223.184&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1579935342&mv=u&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3232 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2124 | m_agent_upgrade.exe | 54.241.7.184:443 | cf.meraki.com | Amazon.com, Inc. | US | unknown |
2124 | m_agent_upgrade.exe | 209.206.62.5:443 | n85.meraki.com | Colocation Australia Pty Ltd | US | unknown |
2128 | m_agent_service.exe | 209.206.62.5:443 | n85.meraki.com | Colocation Australia Pty Ltd | US | unknown |
2128 | m_agent_service.exe | 54.241.7.184:443 | cf.meraki.com | Amazon.com, Inc. | US | unknown |
2128 | m_agent_service.exe | 209.206.62.5:993 | n85.meraki.com | Colocation Australia Pty Ltd | US | unknown |
3232 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 172.217.23.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3232 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cf.meraki.com |
| unknown |
n85.meraki.com |
| unknown |
pcc85.meraki.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
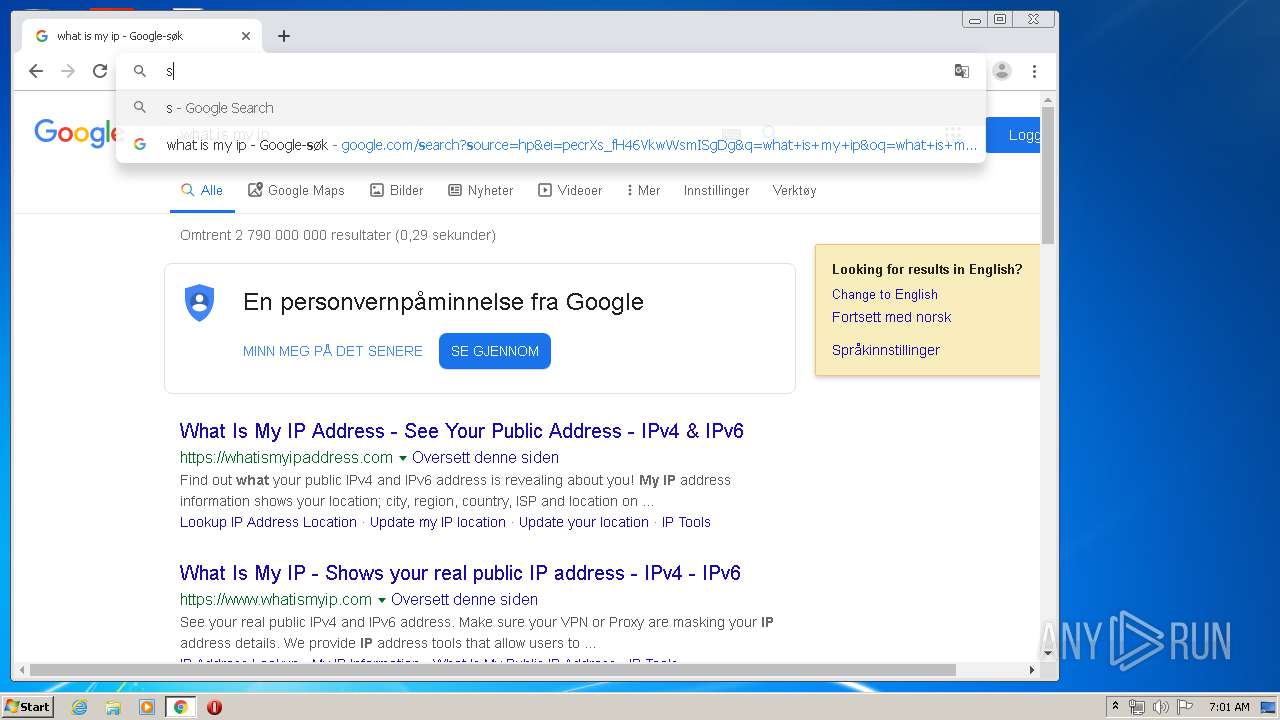
3232 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
3232 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |