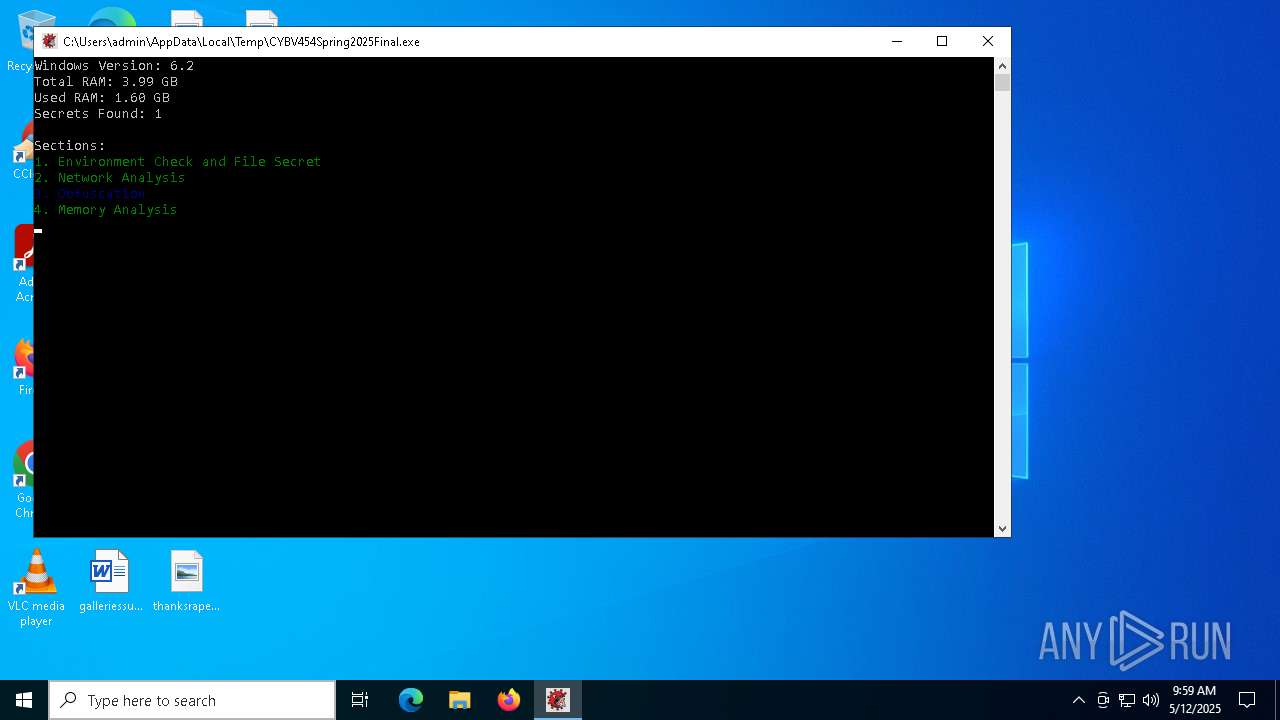
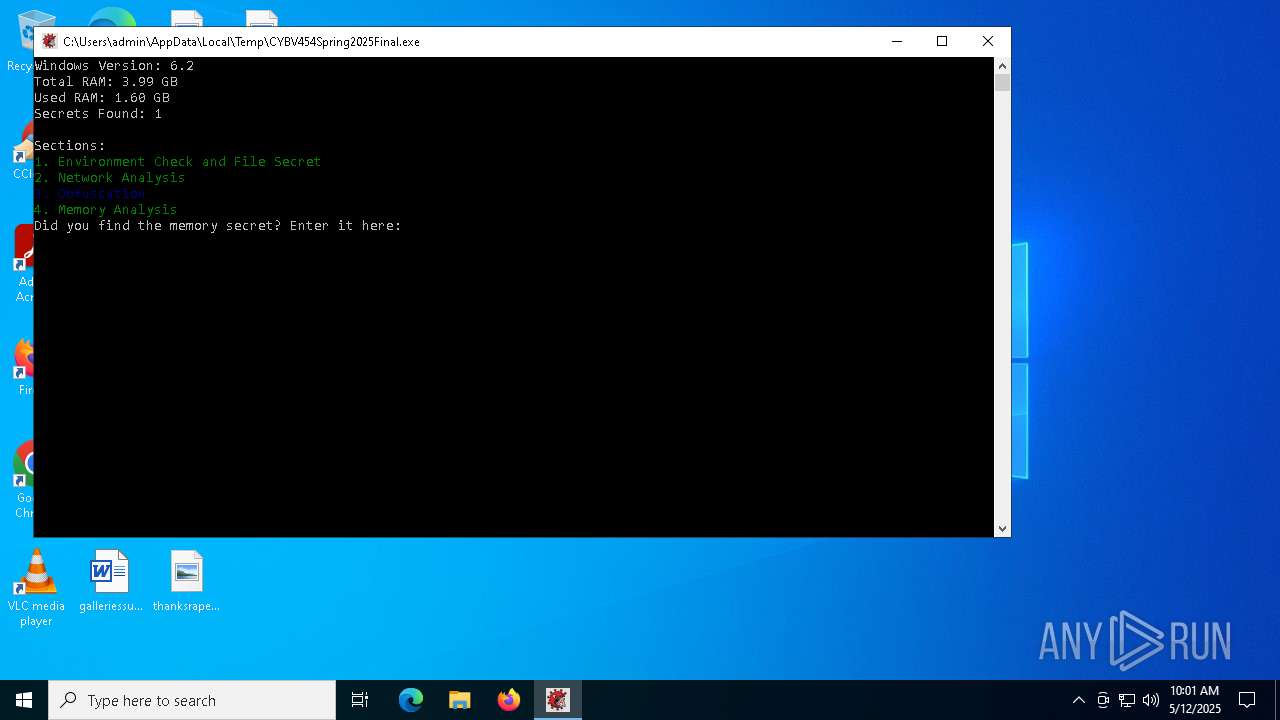
| File name: | CYBV454Spring2025Final.exe |
| Full analysis: | https://app.any.run/tasks/18071088-4a13-477f-a3eb-cb26f356c46d |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 09:58:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows, 10 sections |
| MD5: | 266A512555EE570433C778D5CFD7797A |
| SHA1: | 9BBD58CF2502C0E78E19317834BFA03FF3C126A8 |
| SHA256: | 860393613CAD462E64697D395678BE3CB915AA835B0BAD1A47622CA9A547BB8A |
| SSDEEP: | 6144:QFrYhBQHKBRNnwEPzmjPFUT0x2J2qyZzn:tPwEkCTAw2hZzn |
MALICIOUS
Create files in the Startup directory
- cmd.exe (PID: 5680)
- cscript.exe (PID: 5428)
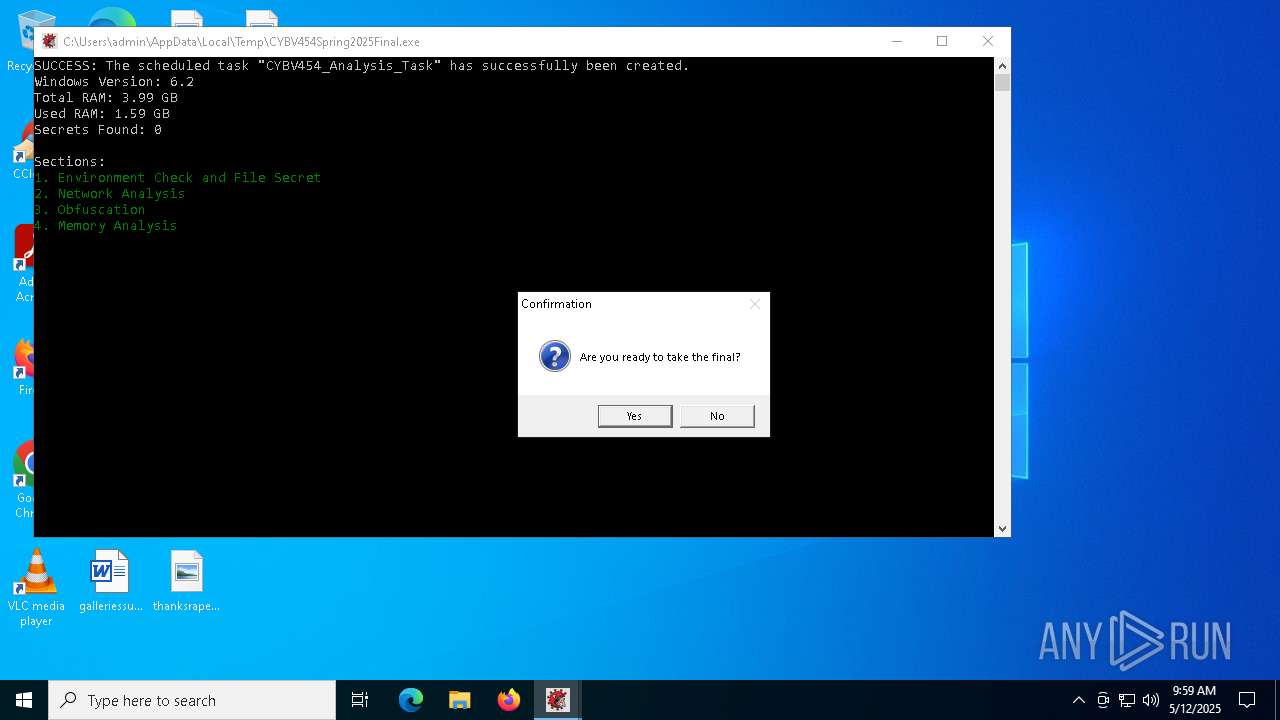
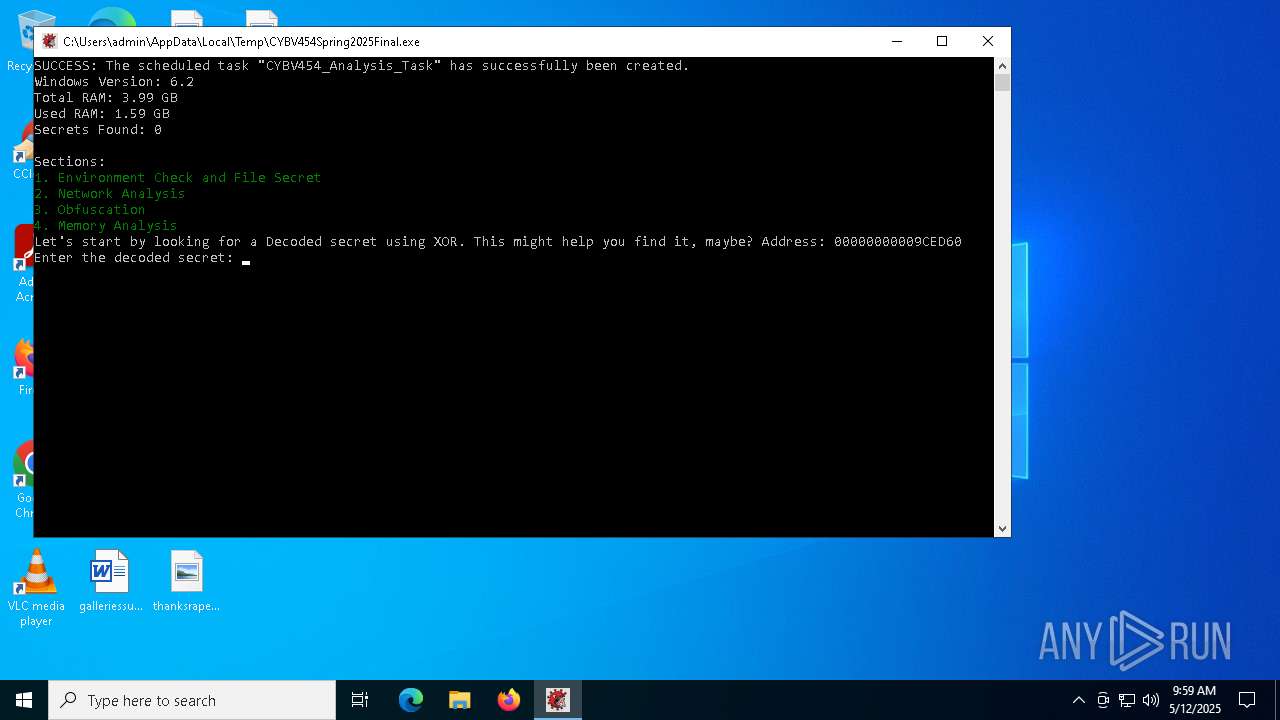
Uses Task Scheduler to run other applications
- CYBV454Spring2025Final.exe (PID: 6184)
SUSPICIOUS
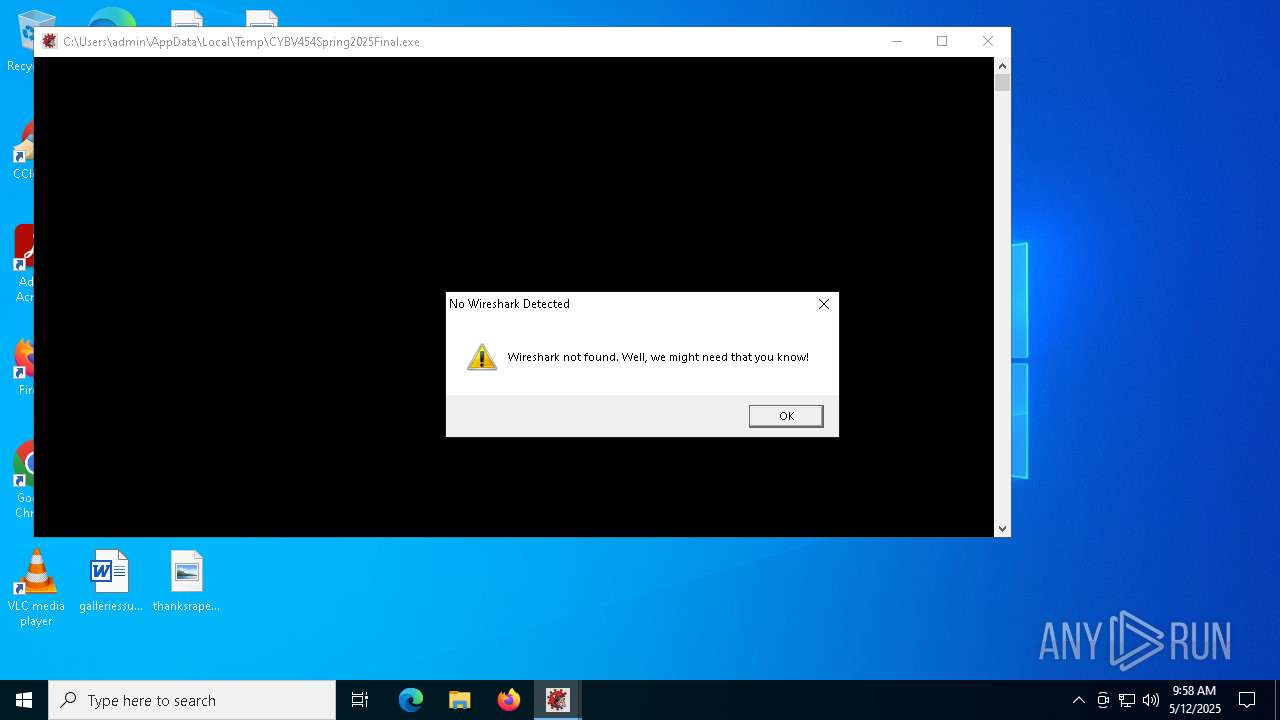
The process executes VB scripts
- cmd.exe (PID: 5680)
Starts CMD.EXE for commands execution
- CYBV454Spring2025Final.exe (PID: 6184)
Runs shell command (SCRIPT)
- cscript.exe (PID: 5428)
INFO
Checks supported languages
- CYBV454Spring2025Final.exe (PID: 6184)
The sample compiled with english language support
- CYBV454Spring2025Final.exe (PID: 6184)
Reads the computer name
- CYBV454Spring2025Final.exe (PID: 6184)
Reads security settings of Internet Explorer
- cscript.exe (PID: 5428)
Creates files or folders in the user directory
- cscript.exe (PID: 5428)
Reads the software policy settings
- slui.exe (PID: 5408)
- slui.exe (PID: 5384)
Checks proxy server information
- slui.exe (PID: 5384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:28 18:27:50+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.3 |
| CodeSize: | 15872 |
| InitializedDataSize: | 303104 |
| UninitializedDataSize: | 2560 |
| EntryPoint: | 0x14e0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
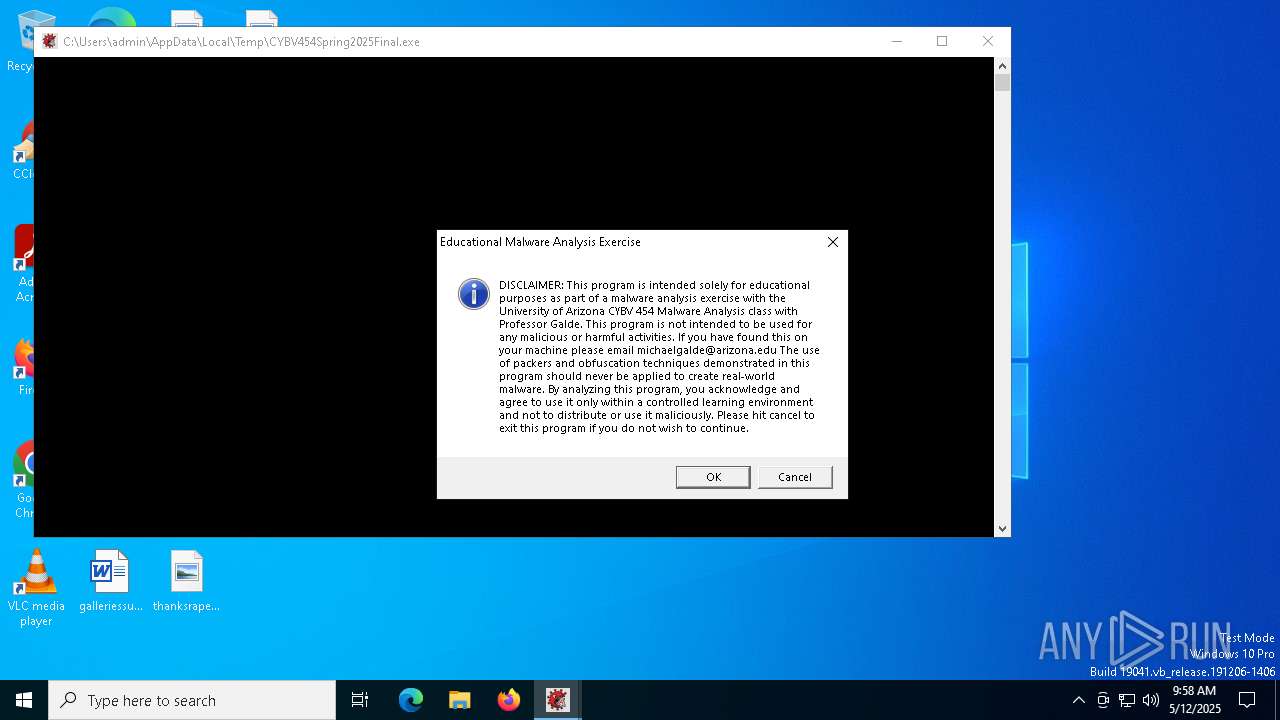
| CompanyName: | University of Arizona - CYBV 454 |
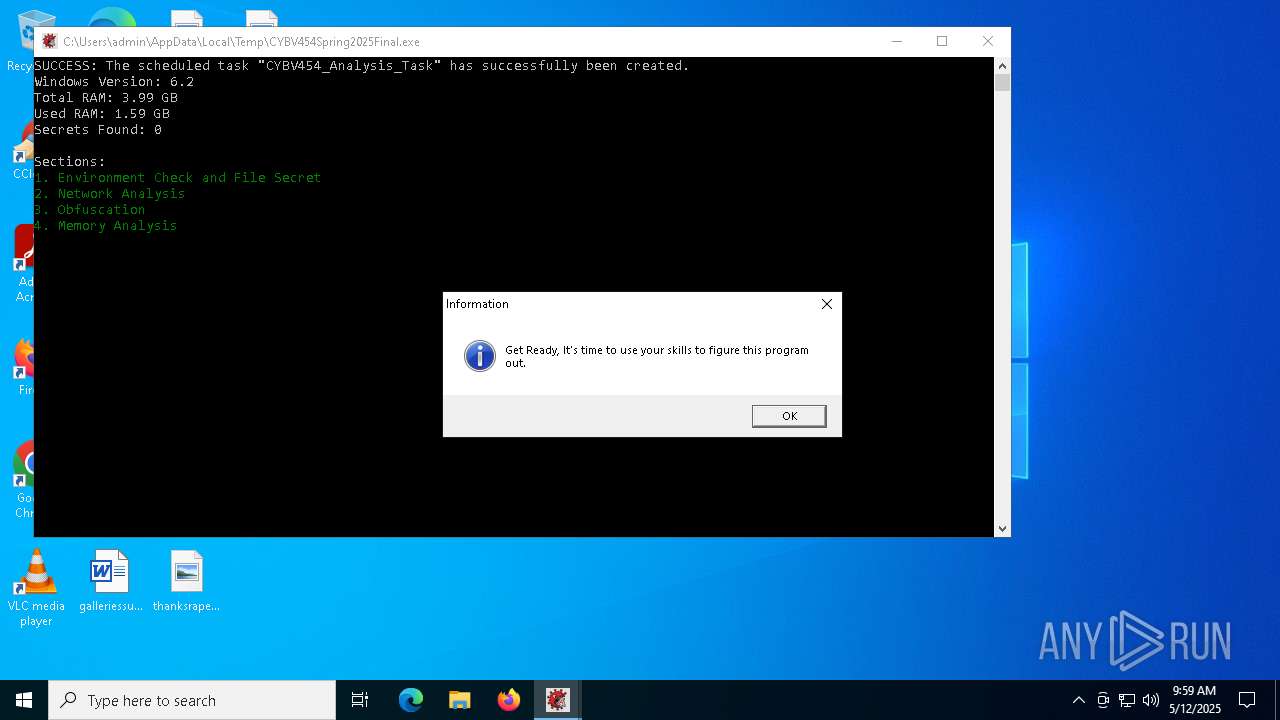
| FileDescription: | Educational Malware Analysis Exercise |
| FileVersion: | 1.0.0.0 |
| InternalName: | CYBV454_Final.exe |
| OriginalFileName: | CYBV454_Final.exe |
| ProductName: | CYBV 454 Malware Final |
| ProductVersion: | 1.0.0.0 |
| Author: | Professor Michael Galde |
Total processes
138
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | CYBV454Spring2025Final.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4996 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CYBV454Spring2025Final.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5384 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5408 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5428 | cscript "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk.vbs" | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5592 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5680 | cmd.exe /c echo Set oWS = WScript.CreateObject("WScript.Shell") > "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk.vbs" && echo sLinkFile = "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk" >> "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk.vbs" && echo Set oLink = oWS.CreateShortcut(sLinkFile) >> "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk.vbs" && echo oLink.TargetPath = "C:\Users\admin\AppData\Local\Temp\CYBV454Spring2025Final.exe" >> "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk.vbs" && echo oLink.Save >> "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk.vbs" && cscript "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk.vbs" && del "C:\Users\admin\AppData\RPXרü | C:\Windows\System32\cmd.exe | CYBV454Spring2025Final.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | schtasks /Create /F /SC DAILY /TN "CYBV454_Analysis_Task" /TR "C:\Users\admin\AppData\Local\Temp\CYBV454Spring2025Final.exe" /ST 12:00 | C:\Windows\System32\schtasks.exe | — | CYBV454Spring2025Final.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | "C:\Users\admin\AppData\Local\Temp\CYBV454Spring2025Final.exe" | C:\Users\admin\AppData\Local\Temp\CYBV454Spring2025Final.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 6744 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | CYBV454Spring2025Final.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 358
Read events
7 358
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
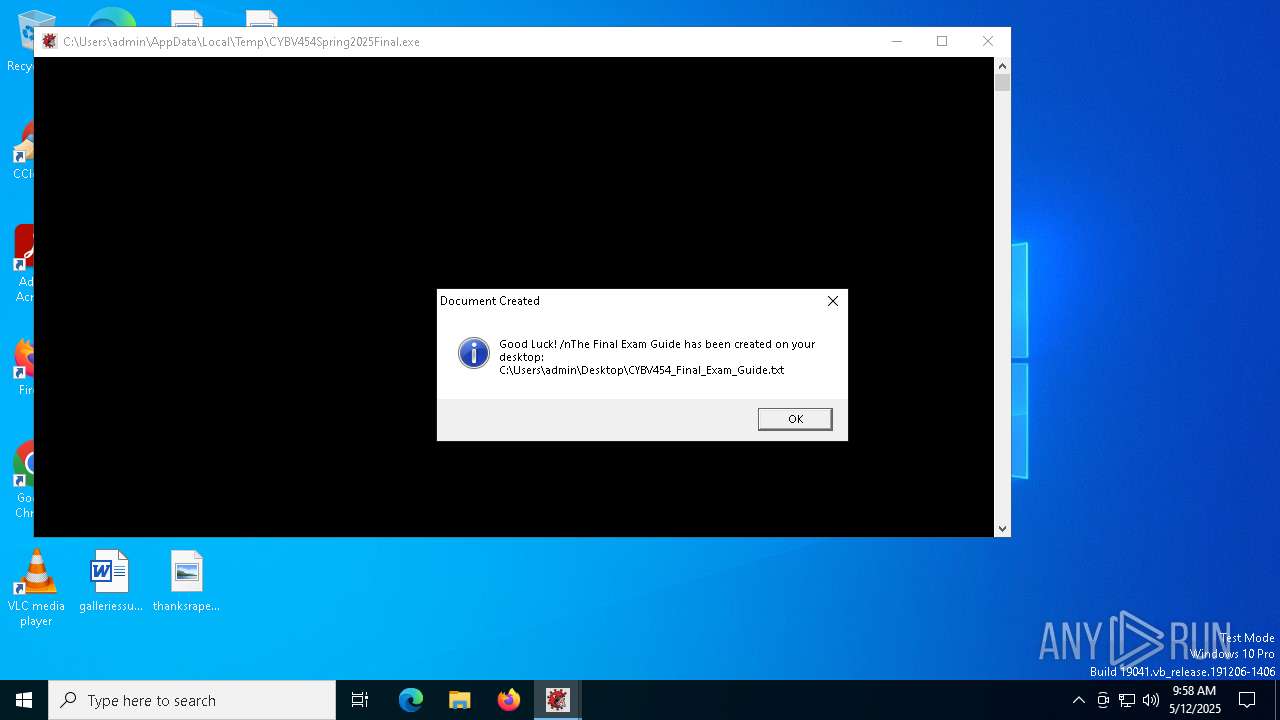
| 6184 | CYBV454Spring2025Final.exe | C:\Users\admin\Desktop\CYBV454_Final_Exam_Guide.txt | text | |
MD5:E417490785CBE6807A80F6C176E58F4B | SHA256:F66B38B4758426E7C3E7194D3E8148A15FA975F2B43C91CA3664202FF8EBC56B | |||
| 5680 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk.vbs | text | |
MD5:3BB5A0D3C6260993DB8651A95AD2D951 | SHA256:65AAD678C0C364AB5A08B3BBD93385FAFBDC49DF8DB63CD90666A3C3EAFD8BDD | |||
| 5428 | cscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\CYBV454_Exercise.lnk | binary | |
MD5:F3D0CF26108C36869911EA32E8005D85 | SHA256:0161F202A8CBBD55A8CAB3A0B0C270B6EA2213A67785438C002EFEB9901C6B93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
41
DNS requests
14
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6808 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6808 | SIHClient.exe | 20.242.39.171:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
171.39.242.20.in-addr.arpa |
| unknown |
4.8.2.0.0.0.0.0.0.0.0.0.0.0.0.0.2.0.0.0.2.0.c.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |