| File name: | ULTIMATE.exe |
| Full analysis: | https://app.any.run/tasks/87569817-8b3f-4fd9-8121-dfc50353404f |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2020, 21:28:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A32F2CA8C78954BDC4EB8B6DEFBD7245 |
| SHA1: | 22774BB3DDD22A02CC0E1087023C43E86F0712F6 |
| SHA256: | 85F478A29F56BA2A0C781751DE53A5202EA077614DF2512DA1138FBDB6F7FB07 |
| SSDEEP: | 98304:d32SnXmTjJ5q7x243PYUbONjTfXRU7eIY6BUdqzR:Fn4J5q1FYU0/vRU7eIfidq |
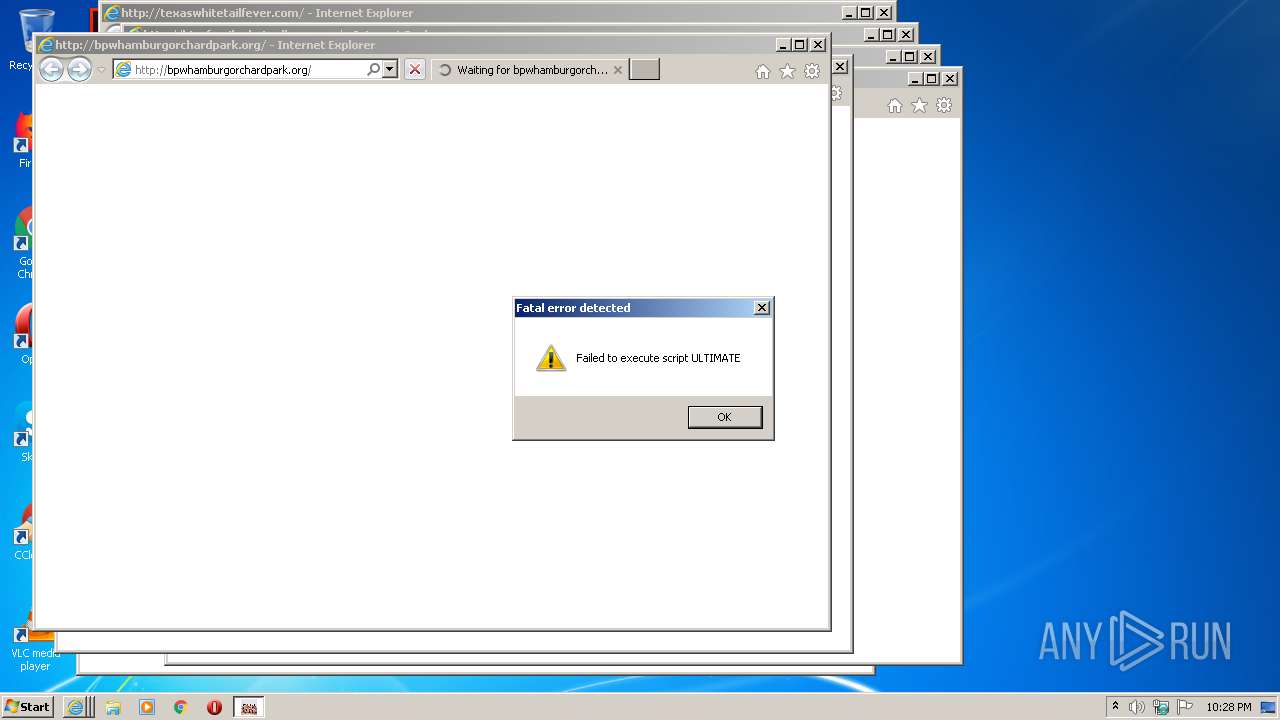
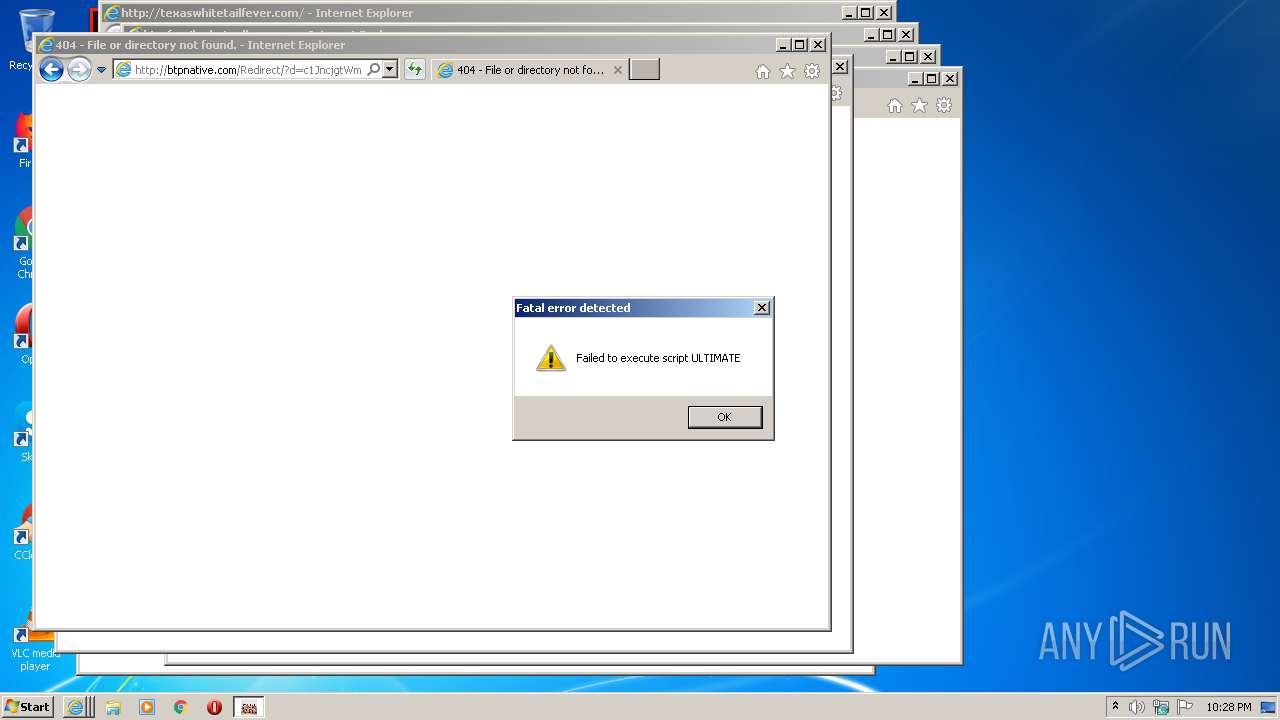
MALICIOUS
Loads dropped or rewritten executable
- ULTIMATE.exe (PID: 2716)
SUSPICIOUS
Application launched itself
- ULTIMATE.exe (PID: 1012)
Loads Python modules
- ULTIMATE.exe (PID: 2716)
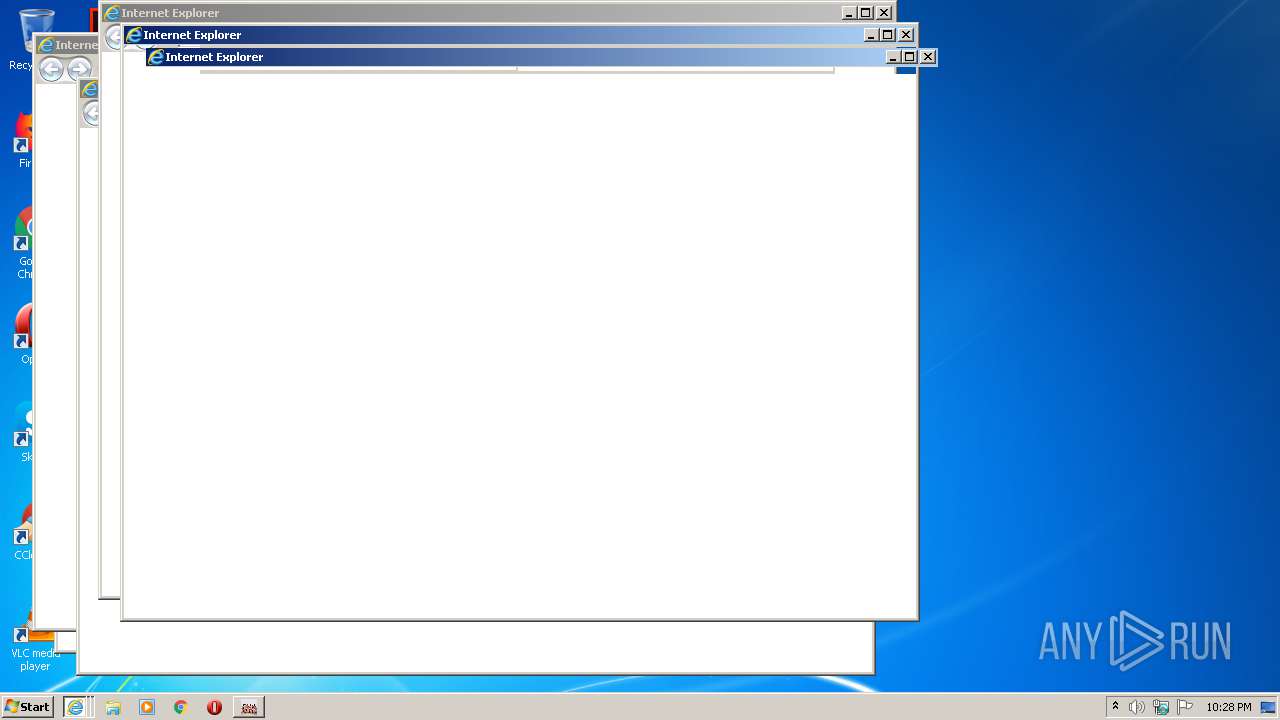
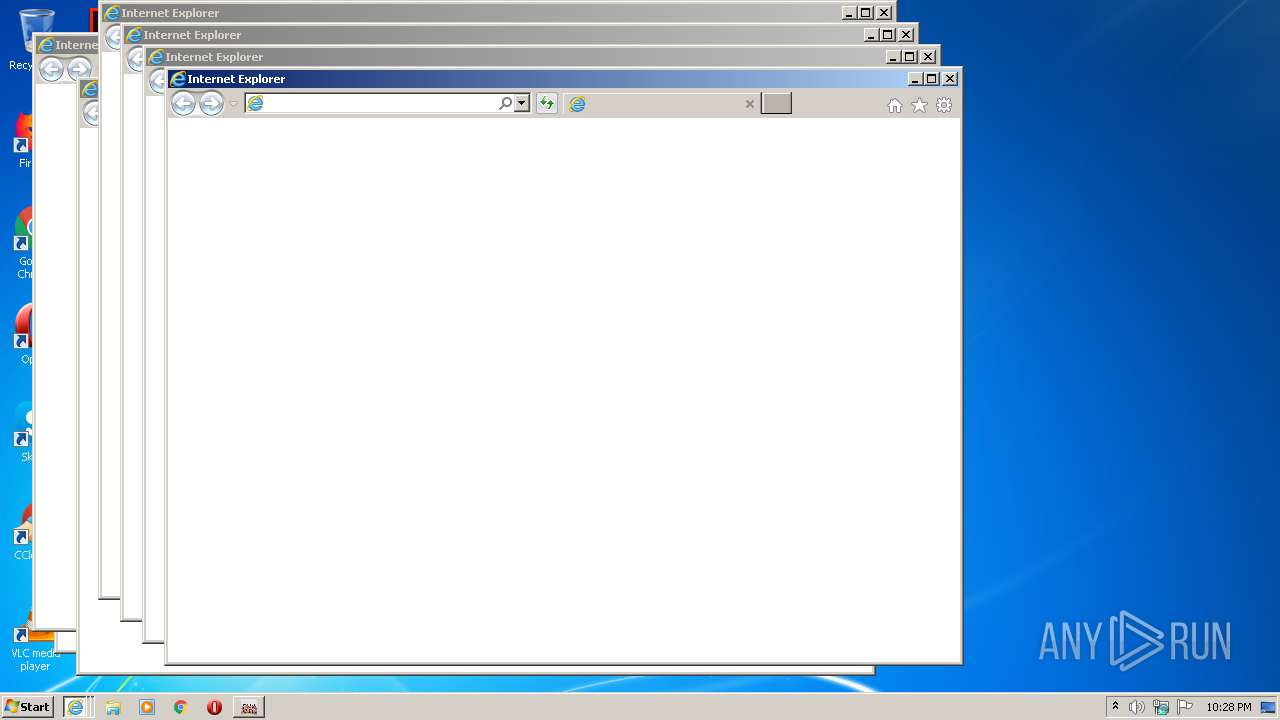
Starts Internet Explorer
- ULTIMATE.exe (PID: 2716)
Executable content was dropped or overwritten
- ULTIMATE.exe (PID: 1012)
INFO
Application launched itself
- IEXPLORE.EXE (PID: 2424)
- IEXPLORE.EXE (PID: 3060)
- IEXPLORE.EXE (PID: 1472)
- IEXPLORE.EXE (PID: 2964)
- IEXPLORE.EXE (PID: 2104)
- IEXPLORE.EXE (PID: 1712)
- IEXPLORE.EXE (PID: 1708)
- IEXPLORE.EXE (PID: 2292)
- IEXPLORE.EXE (PID: 2320)
Reads Internet Cache Settings
- IEXPLORE.EXE (PID: 2424)
- IEXPLORE.EXE (PID: 1472)
- IEXPLORE.EXE (PID: 3060)
- IEXPLORE.EXE (PID: 1712)
- IEXPLORE.EXE (PID: 1716)
- IEXPLORE.EXE (PID: 4068)
- IEXPLORE.EXE (PID: 2964)
- IEXPLORE.EXE (PID: 1920)
- IEXPLORE.EXE (PID: 2104)
- IEXPLORE.EXE (PID: 2320)
- IEXPLORE.EXE (PID: 2556)
- IEXPLORE.EXE (PID: 1708)
- IEXPLORE.EXE (PID: 2664)
- IEXPLORE.EXE (PID: 2292)
- IEXPLORE.EXE (PID: 2124)
- IEXPLORE.EXE (PID: 2276)
- IEXPLORE.EXE (PID: 1360)
- IEXPLORE.EXE (PID: 2860)
- IEXPLORE.EXE (PID: 2144)
- IEXPLORE.EXE (PID: 2532)
Changes internet zones settings
- IEXPLORE.EXE (PID: 2424)
- IEXPLORE.EXE (PID: 1472)
- IEXPLORE.EXE (PID: 3060)
- IEXPLORE.EXE (PID: 2964)
- IEXPLORE.EXE (PID: 2104)
- IEXPLORE.EXE (PID: 1712)
- IEXPLORE.EXE (PID: 1708)
- IEXPLORE.EXE (PID: 2320)
- IEXPLORE.EXE (PID: 2292)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 1920)
- IEXPLORE.EXE (PID: 2556)
- IEXPLORE.EXE (PID: 2860)
- IEXPLORE.EXE (PID: 4068)
- IEXPLORE.EXE (PID: 2664)
- IEXPLORE.EXE (PID: 1360)
- IEXPLORE.EXE (PID: 2276)
- IEXPLORE.EXE (PID: 2144)
- IEXPLORE.EXE (PID: 1716)
- IEXPLORE.EXE (PID: 2532)
- IEXPLORE.EXE (PID: 2124)
Creates files in the user directory
- IEXPLORE.EXE (PID: 1920)
- IEXPLORE.EXE (PID: 1360)
- IEXPLORE.EXE (PID: 4068)
- IEXPLORE.EXE (PID: 2124)
- IEXPLORE.EXE (PID: 2144)
- IEXPLORE.EXE (PID: 1716)
- IEXPLORE.EXE (PID: 2860)
Reads settings of System Certificates
- IEXPLORE.EXE (PID: 1716)
- IEXPLORE.EXE (PID: 2860)
- IEXPLORE.EXE (PID: 1712)
- IEXPLORE.EXE (PID: 2276)
- IEXPLORE.EXE (PID: 2124)
Adds / modifies Windows certificates
- IEXPLORE.EXE (PID: 1712)
Changes settings of System certificates
- IEXPLORE.EXE (PID: 1712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (54.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.8) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:05 13:16:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 126976 |
| InitializedDataSize: | 262144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7cd3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Jan-2020 12:16:35 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Jan-2020 12:16:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001EE04 | 0x0001F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64212 |
.rdata | 0x00020000 | 0x0000B206 | 0x0000B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.06574 |
.data | 0x0002C000 | 0x0000E688 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.92321 |
.gfids | 0x0003B000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.82374 |
.rsrc | 0x0003C000 | 0x00032658 | 0x00032800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.62988 |
.reloc | 0x0006F000 | 0x000017B4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65769 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.01924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.32939 | 1031 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.44895 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.77742 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 7.95095 | 38188 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.0521 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 6.15081 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.39466 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
57
Monitored processes
24
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1012 | "C:\Users\admin\AppData\Local\Temp\ULTIMATE.exe" | C:\Users\admin\AppData\Local\Temp\ULTIMATE.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" SCODEF:1712 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | IEXPLORE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" bpwhamburgorchardpark.org | C:\Program Files\Internet Explorer\IEXPLORE.EXE | ULTIMATE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" kingfamilyphotoalbum.com | C:\Program Files\Internet Explorer\IEXPLORE.EXE | ULTIMATE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" ginedis.com | C:\Program Files\Internet Explorer\IEXPLORE.EXE | ULTIMATE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" SCODEF:2424 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | IEXPLORE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" SCODEF:3060 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | IEXPLORE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" hdvideoforums.org | C:\Program Files\Internet Explorer\IEXPLORE.EXE | ULTIMATE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" SCODEF:2104 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | IEXPLORE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" SCODEF:2292 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | IEXPLORE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 719
Read events
3 044
Write events
588
Delete events
87
Modification events
| (PID) Process: | (1472) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3282105638 | |||
| (PID) Process: | (1472) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30824997 | |||
| (PID) Process: | (1472) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1472) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1472) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2424) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2424) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2424) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1472) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1472) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
12
Suspicious files
55
Text files
112
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1012 | ULTIMATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\ULTIMATE.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 1012 | ULTIMATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\_bz2.pyd | executable | |
MD5:2DD25AC2510C5640169D89EE220E748E | SHA256:F5086031019C5E03AFCFEE227C4D30E82B68C24F5A5871640C3E8682852D9A54 | |||
| 1012 | ULTIMATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\base_library.zip | compressed | |
MD5:— | SHA256:— | |||
| 2424 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1716 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\570JM2J5.htm | compressed | |
MD5:— | SHA256:— | |||
| 1472 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1012 | ULTIMATE.exe | C:\Users\admin\AppData\Local\Temp\_MEI10122\VCRUNTIME140.dll | executable | |
MD5:AE96651CFBD18991D186A029CBECB30C | SHA256:1B372F064EACB455A0351863706E6326CA31B08E779A70DE5DE986B5BE8069A1 | |||
| 1920 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\9RE0Z8H0.htm | html | |
MD5:— | SHA256:— | |||
| 2716 | ULTIMATE.exe | C:\Users\admin\AppData\Local\Temp\REP1.dead | binary | |
MD5:— | SHA256:— | |||
| 2664 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\VZKOS9RS.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
118
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1716 | IEXPLORE.EXE | GET | 301 | 184.168.131.241:80 | http://dfwdiesel.net/ | US | — | — | malicious |
2144 | IEXPLORE.EXE | GET | 302 | 103.224.212.222:80 | http://tathli.com/ | AU | — | — | malicious |
2556 | IEXPLORE.EXE | GET | 200 | 208.91.196.105:80 | http://texaswhitetailfever.com/ | VG | html | 195 b | malicious |
1360 | IEXPLORE.EXE | GET | 200 | 46.166.182.63:80 | http://ginedis.com/ | NL | html | 467 b | malicious |
1920 | IEXPLORE.EXE | GET | 200 | 45.33.2.79:80 | http://divineenterprises.net/ | US | html | 1.50 Kb | malicious |
2860 | IEXPLORE.EXE | GET | 200 | 52.222.136.50:80 | http://d1lxhc4jvstzrp.cloudfront.net/themes/assets/style.css | US | text | 343 b | shared |
2664 | IEXPLORE.EXE | GET | 200 | 208.91.196.105:80 | http://texaswhitetailfever.com/ | VG | html | 195 b | malicious |
1920 | IEXPLORE.EXE | GET | 200 | 45.33.2.79:80 | http://divineenterprises.net/mtm/async/eyJ1cmkiOiIvIiwiYXJncyI6IiIsInJlZmVyZXIiOiIifQ:1jvSTS:VcYBLVEitZpO6ADMpSFX2Gg9JVo/2 | US | text | 124 b | malicious |
2276 | IEXPLORE.EXE | GET | 200 | 35.186.238.101:80 | http://gncr.org/ | US | html | 2.39 Kb | whitelisted |
2860 | IEXPLORE.EXE | GET | 200 | 104.247.82.134:80 | http://kingfamilyphotoalbum.com/ | CA | html | 5.18 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1716 | IEXPLORE.EXE | 184.168.131.241:80 | dfwdiesel.net | GoDaddy.com, LLC | US | shared |
1920 | IEXPLORE.EXE | 45.33.2.79:80 | divineenterprises.net | Linode, LLC | US | malicious |
4068 | IEXPLORE.EXE | 46.166.182.64:80 | bpwhamburgorchardpark.org | NForce Entertainment B.V. | NL | unknown |
1716 | IEXPLORE.EXE | 166.62.110.213:80 | cyclonediesel.com | GoDaddy.com, LLC | US | malicious |
2664 | IEXPLORE.EXE | 208.91.196.105:80 | texaswhitetailfever.com | Confluence Networks Inc | VG | malicious |
2556 | IEXPLORE.EXE | 208.91.196.105:80 | texaswhitetailfever.com | Confluence Networks Inc | VG | malicious |
1716 | IEXPLORE.EXE | 166.62.110.213:443 | cyclonediesel.com | GoDaddy.com, LLC | US | malicious |
1360 | IEXPLORE.EXE | 46.166.182.63:80 | ginedis.com | NForce Entertainment B.V. | NL | malicious |
2860 | IEXPLORE.EXE | 104.247.82.134:80 | kingfamilyphotoalbum.com | — | CA | unknown |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
divineenterprises.net |
| malicious |
dfwdiesel.net |
| malicious |
bpwhamburgorchardpark.org |
| malicious |
cyclonediesel.com |
| suspicious |
texaswhitetailfever.com |
| malicious |
ginedis.com |
| malicious |
kingfamilyphotoalbum.com |
| malicious |
gncr.org |
| whitelisted |