| download: | Login |
| Full analysis: | https://app.any.run/tasks/3fcaaaff-2b6b-4edf-9899-2321b361caae |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 23:41:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF line terminators |
| MD5: | E65479B2AFBCD48D34C37CDBC8510DD1 |
| SHA1: | D751240ED6B3CA08A194CD4103405418B724BFDD |
| SHA256: | 85EA1168A5BC867047563DC1359C081FB9D9A8F7AA6A4A1B4E24ABB828D56D5C |
| SSDEEP: | 1536:b62FFY02drHAsJ4KIhayr1H+03BPEyZsn:O2FO4Syr1HA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 4012)
INFO
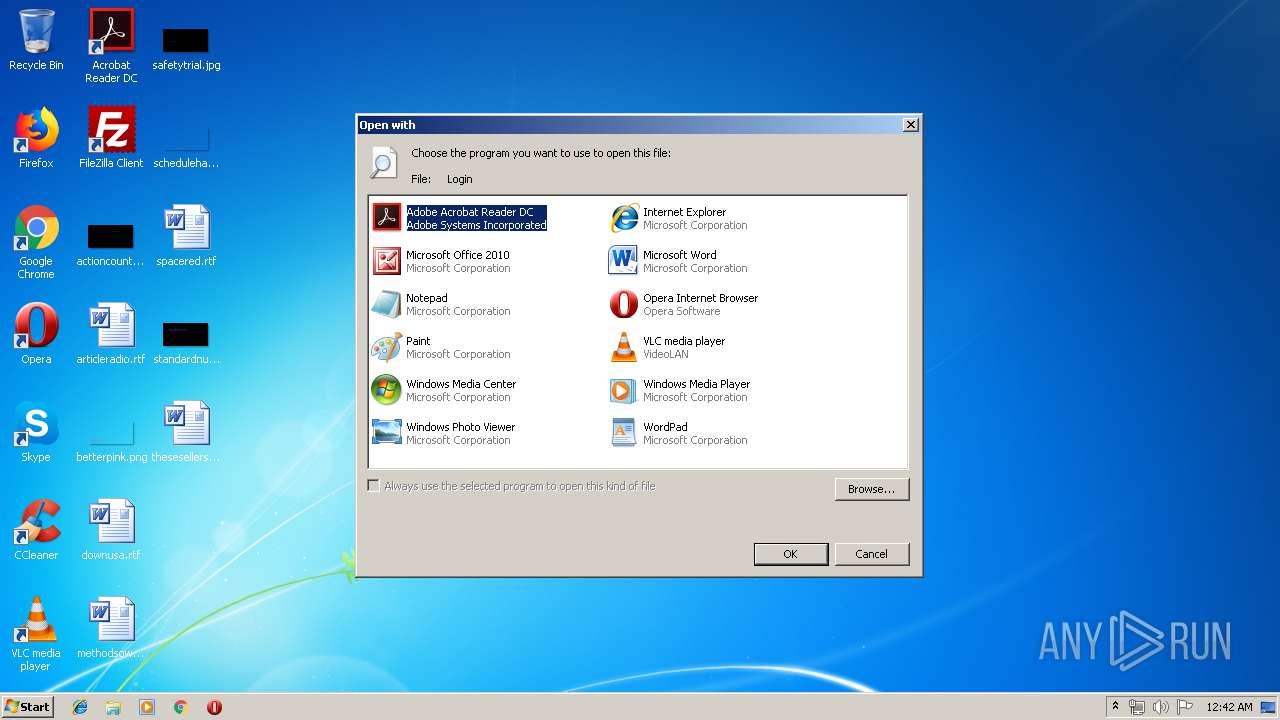
Manual execution by user
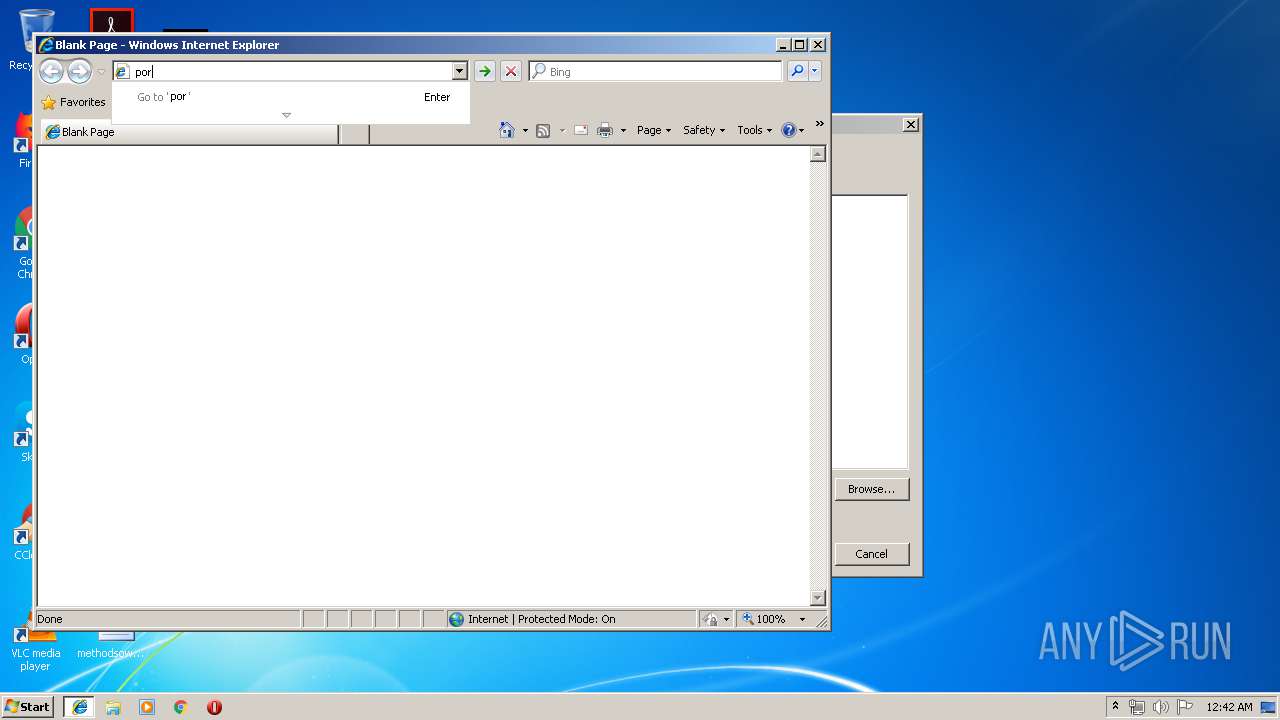
- iexplore.exe (PID: 3572)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1412)
Reads Internet Cache Settings
- iexplore.exe (PID: 1412)
Changes internet zones settings
- iexplore.exe (PID: 3572)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 4012)
- iexplore.exe (PID: 1412)
Reads settings of System Certificates
- iexplore.exe (PID: 3572)
Application launched itself
- iexplore.exe (PID: 3572)
Reads internet explorer settings
- iexplore.exe (PID: 1412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| Title: | Roblox |
|---|---|
| HTTPEquivXUACompatible: | IE=edge,requiresActiveX=true |
| Author: | Roblox Corporation |
| Description: | Roblox is a global platform that brings people together through play. |
| Keywords: | free games, online games, building games, virtual worlds, free mmo, gaming cloud, physics engine |
| appleItunesApp: | app-id=431946152 |
| viewport: | width=device-width, initial-scale=1, maximum-scale=1, user-scalable=0 |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3572 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2216 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Login | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3572 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4012 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
614
Read events
465
Write events
147
Delete events
2
Modification events
| (PID) Process: | (2216) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2216) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2216) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (3572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3572) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {FA326413-BE23-11E9-9885-5254004A04AF} |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
239
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3572 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1412 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
| 1412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WSBU0SXR\search[1].txt | — | |
MD5:— | SHA256:— | |||
| 1412 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 1412 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 3572 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 1412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1412 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\LQAFKR10\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
82
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/14/cj,nj/83a49848/f2056989.js?bu=DikuX293e2tjZ7MBtwEupwEu | US | text | 7.54 Kb | whitelisted |
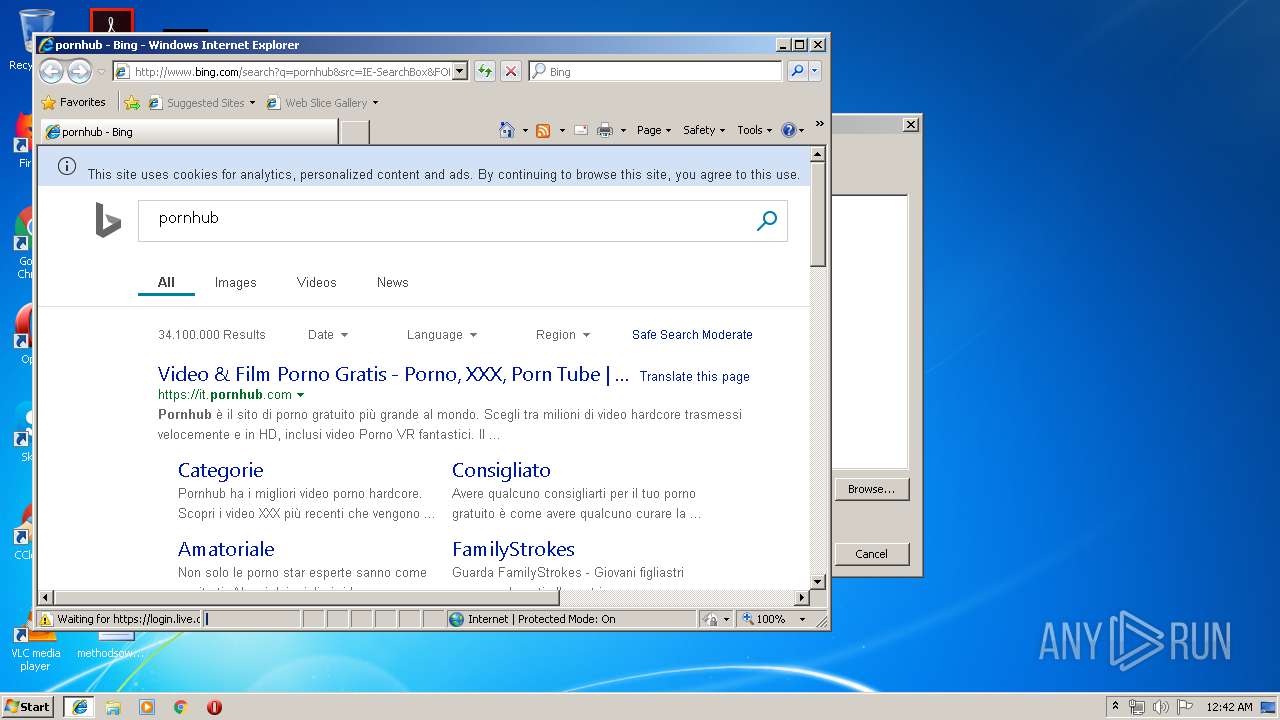
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=5C48496546394A0CA87C77F8FBD20D8F&CID=3A21823665AB66972C918F81641E67F6&Type=Event.ClientInst&DATA=[{"T":"CI.GetError","FID":"CI","Name":"JSGetError","Text":"%27SVGElement%27%20is%20undefined","Meta":"http%3A//www.bing.com/search%3Fq%3Dpornhub%26src%3DIE-SearchBox%26FORM%3DIE8SRC","Line":24096399,"Char":%20undefined}] | US | compressed | 181 b | whitelisted |
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5k/cj,nj/c44ec255/9a358300.js?bu=Eq4fzB_vHv0e1gSGH4gf4x-KH58flB-3H78fxR-qHrYduR2lHg | US | text | 4.95 Kb | whitelisted |
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/6n/4T/cj,nj/dd882357/b8881a70.js | US | text | 1.77 Kb | whitelisted |
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/30/26/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/5k/1nG/cj,nj/e90431ed/b2fe50be.js | US | text | 171 b | whitelisted |
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/30/1b/cj,nj/3f1e2270/f8c6dd44.js | US | text | 773 b | whitelisted |
1412 | iexplore.exe | POST | 204 | 204.79.197.200:80 | http://www.bing.com/fd/ls/lsp.aspx | US | compressed | 174 b | whitelisted |
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=5C48496546394A0CA87C77F8FBD20D8F&CID=3A21823665AB66972C918F81641E67F6&Type=Event.CPT&DATA={"pp":{"S":"L","FC":78,"BC":156,"SE":-1,"TC":-1,"H":328,"BP":422,"CT":437,"IL":3},"ad":[-1,-1,772,444,1089,498,0]}&P=SERP&DA=DUB02 | US | image | 5.73 Kb | whitelisted |
1412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.73 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1412 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1412 | iexplore.exe | 52.231.32.10:80 | 9dc6f0fdfc56bdba9cf004c63b533186.clo.footprintdns.com | Microsoft Corporation | KR | whitelisted |
1412 | iexplore.exe | 204.79.197.222:80 | 69b6fd5d4466708c0cd57682c7069730.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
1412 | iexplore.exe | 64.4.16.218:443 | login.live.com | Microsoft Corporation | US | whitelisted |
1412 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1412 | iexplore.exe | 69.16.175.10:443 | smpop.icfcdn.com | Highwinds Network Group, Inc. | US | malicious |
1412 | iexplore.exe | 66.254.114.41:443 | it.pornhub.com | Reflected Networks, Inc. | US | malicious |
1412 | iexplore.exe | 205.185.208.79:443 | static.trafficjunky.com | Highwinds Network Group, Inc. | US | unknown |
1412 | iexplore.exe | 74.125.140.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
69b6fd5d4466708c0cd57682c7069730.clo.footprintdns.com |
| suspicious |
24ee41a1aed5a956163449b0265b5773.clo.footprintdns.com |
| suspicious |
9dc6f0fdfc56bdba9cf004c63b533186.clo.footprintdns.com |
| unknown |
fp.msedge.net |
| whitelisted |
it.pornhub.com |
| malicious |
ci.phncdn.com |
| whitelisted |
cdn1d-static-shared.phncdn.com |
| whitelisted |
smpop.icfcdn.com |
| malicious |