| File name: | lw_11.3_build7_web.exe |
| Full analysis: | https://app.any.run/tasks/9830da2d-4515-4318-9a4a-b28f8bbbecdd |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2024, 20:59:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 40D2C291E8DBD369D7FAAB6EA6058552 |
| SHA1: | A4603D376C5B0E73F0C9769B4FE6C26A76D118ED |
| SHA256: | 85E00942AEF51D7AB98BCFB6C0E9EF70E755996DFD5F3769B42286DC6D875A09 |
| SSDEEP: | 98304:GxL5qjsL7nvuwQLXZAPCmo4bEL/bWTU8a8hHE+32PekRM57UEaX/eo/9wOXlIv+V:PA+Vpe7k7WrUZ |
MALICIOUS
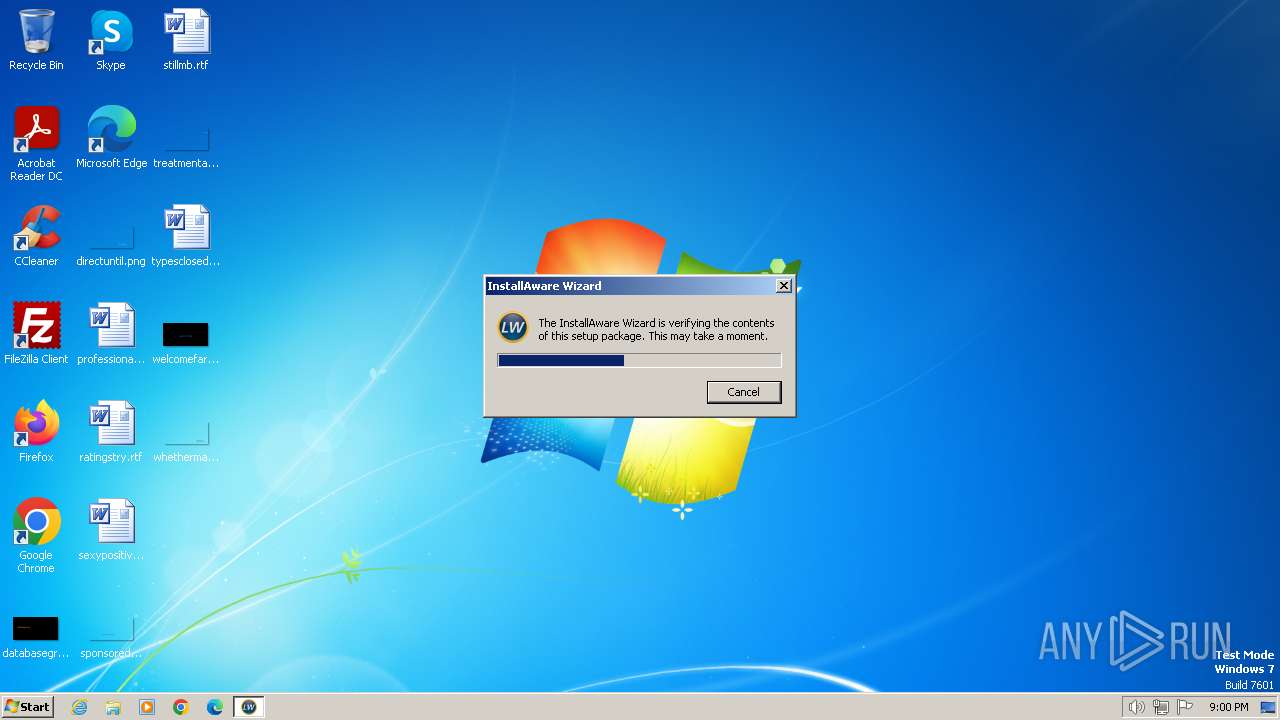
Drops the executable file immediately after the start
- lw_11.3_build7_web.exe (PID: 1344)
- setup.exe (PID: 3768)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- lw_11.3_build7_web.exe (PID: 1344)
Reads the Windows owner or organization settings
- setup.exe (PID: 3768)
The process creates files with name similar to system file names
- setup.exe (PID: 3768)
Executable content was dropped or overwritten
- lw_11.3_build7_web.exe (PID: 1344)
- setup.exe (PID: 3768)
Reads the Internet Settings
- setup.exe (PID: 3768)
INFO
Checks supported languages
- lw_11.3_build7_web.exe (PID: 1344)
- setup.exe (PID: 3768)
Reads the computer name
- setup.exe (PID: 3768)
Create files in a temporary directory
- lw_11.3_build7_web.exe (PID: 1344)
- setup.exe (PID: 3768)
Checks proxy server information
- setup.exe (PID: 3768)
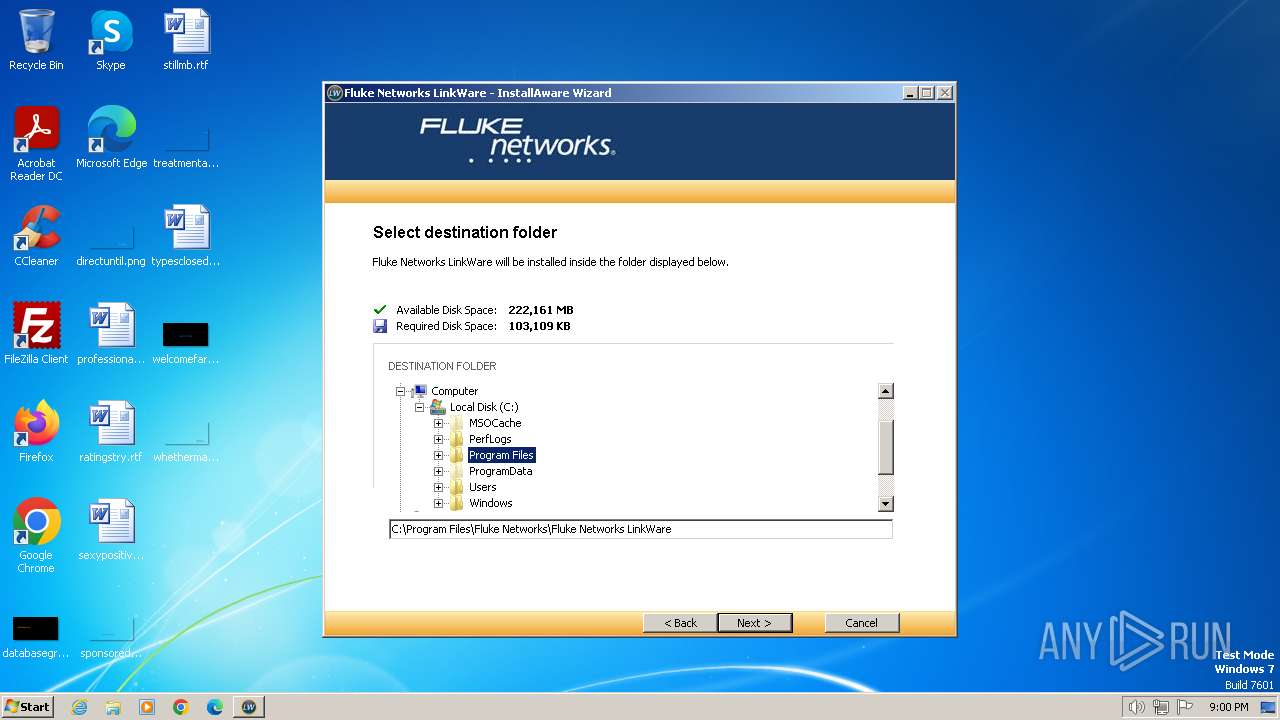
Creates files in the program directory
- setup.exe (PID: 3768)
Reads the machine GUID from the registry
- setup.exe (PID: 3768)
Creates files or folders in the user directory
- setup.exe (PID: 3768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:04:15 22:43:49+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 98816 |
| InitializedDataSize: | 286720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12a70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
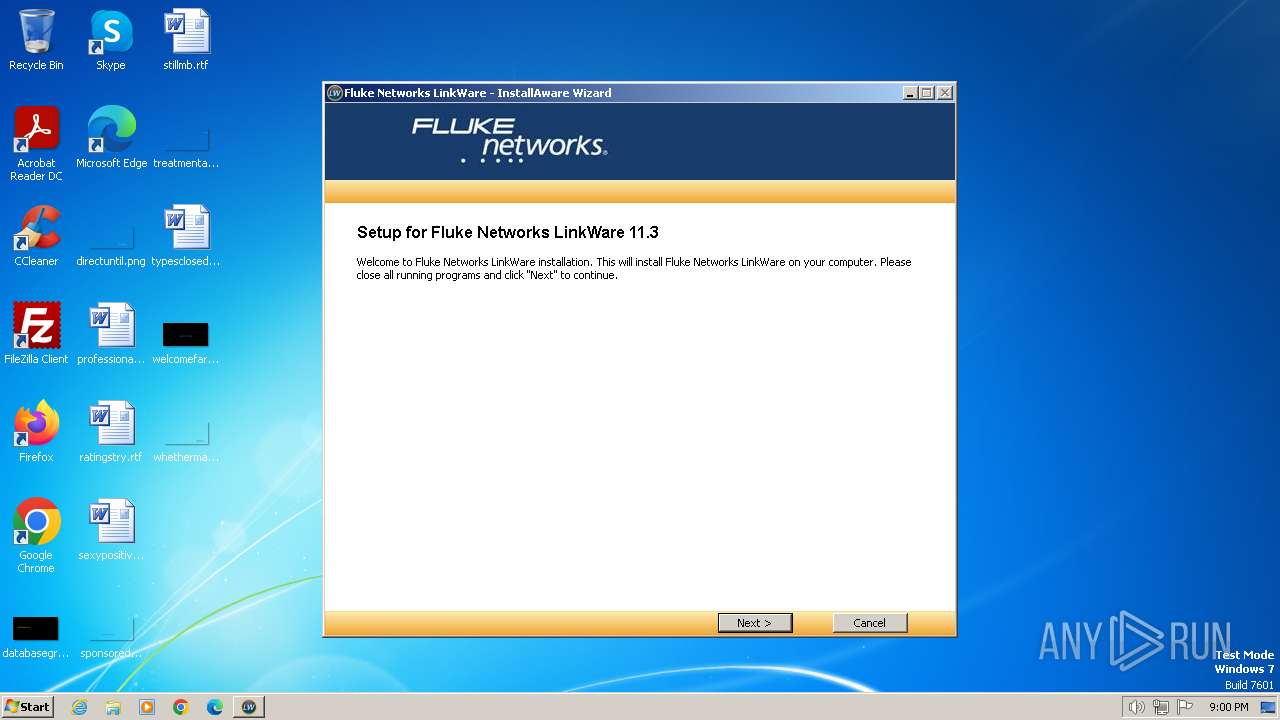
| FileVersionNumber: | 11.3.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
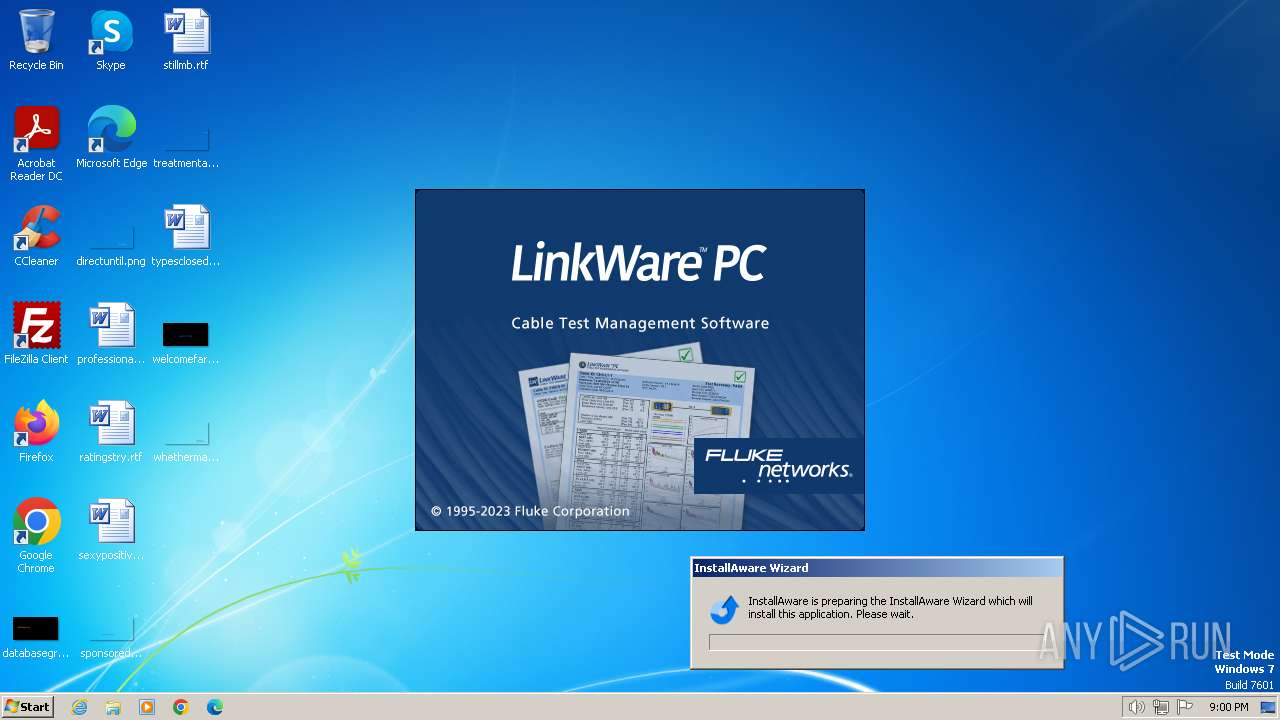
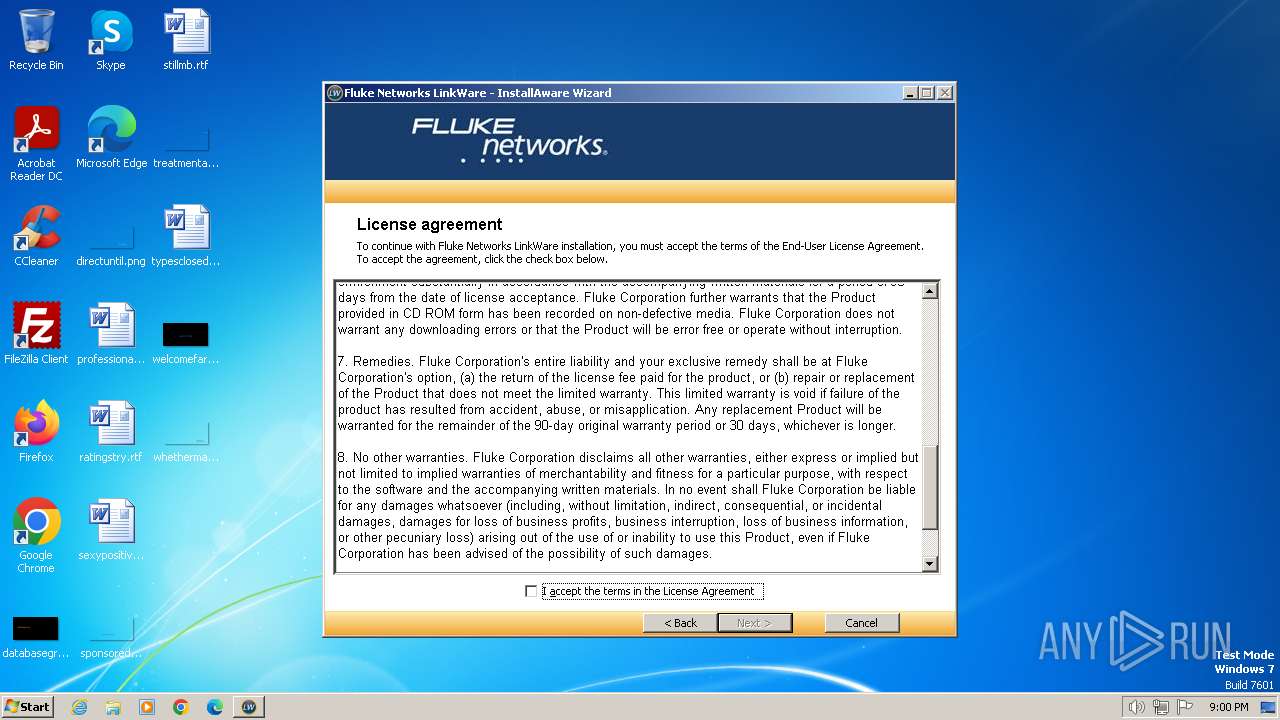
| Comments: | This installation was built with InstallAware: http://www.installaware.com |
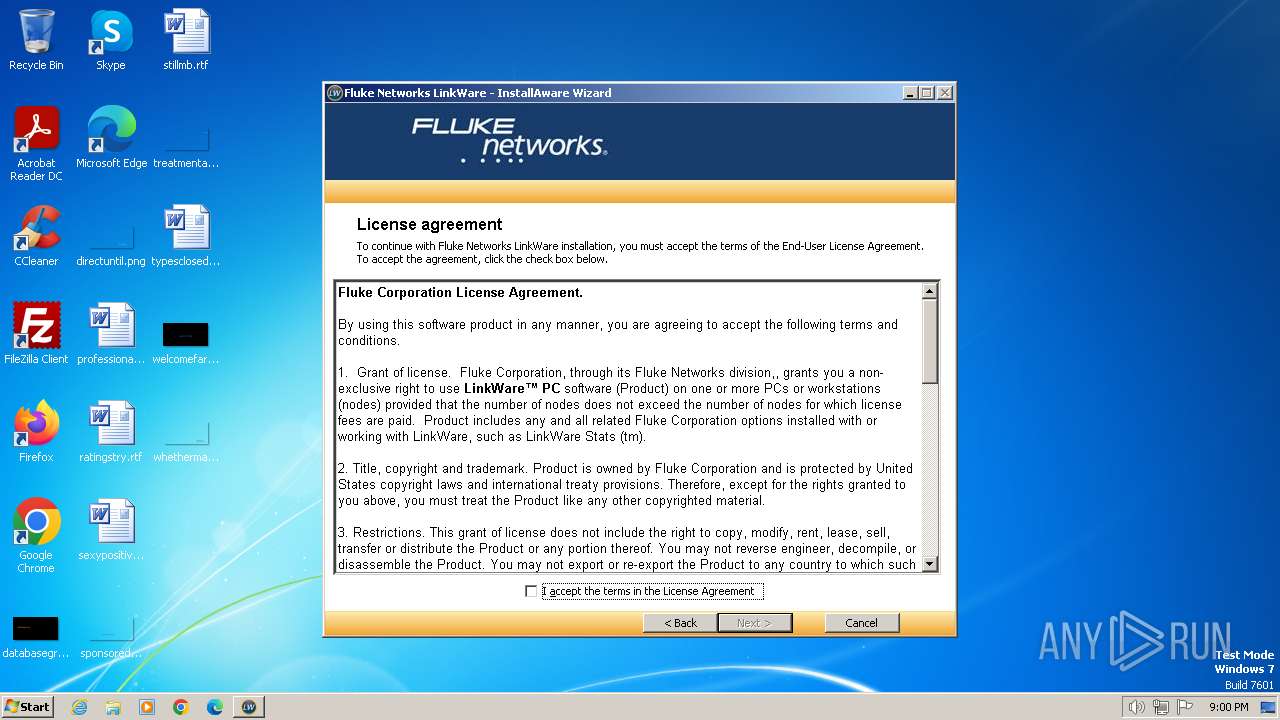
| CompanyName: | Fluke Networks |
| FileDescription: | LinkWare Installation |
| FileVersion: | 11.3 |
| LegalCopyright: | Fluke Corporation. Copyright © 1995-2023 |
Total processes
42
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Users\admin\AppData\Local\Temp\lw_11.3_build7_web.exe" | C:\Users\admin\AppData\Local\Temp\lw_11.3_build7_web.exe | — | explorer.exe | |||||||||||
User: admin Company: Fluke Networks Integrity Level: MEDIUM Description: LinkWare Installation Exit code: 3221226540 Version: 11.3 Modules
| |||||||||||||||
| 1344 | "C:\Users\admin\AppData\Local\Temp\lw_11.3_build7_web.exe" | C:\Users\admin\AppData\Local\Temp\lw_11.3_build7_web.exe | explorer.exe | ||||||||||||
User: admin Company: Fluke Networks Integrity Level: HIGH Description: LinkWare Installation Exit code: 0 Version: 11.3 Modules
| |||||||||||||||
| 3768 | .\setup.exe /m="C:\Users\admin\AppData\Local\Temp\LW_113~1.EXE" /k="" | C:\Users\admin\AppData\Local\Temp\mia3B0A.tmp\setup.exe | lw_11.3_build7_web.exe | ||||||||||||
User: admin Company: Fluke Networks Integrity Level: HIGH Description: LinkWare Installation Exit code: 0 Version: 11.3 Modules
| |||||||||||||||
Total events
1 361
Read events
1 336
Write events
25
Delete events
0
Modification events
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3768) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
11
Suspicious files
29
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
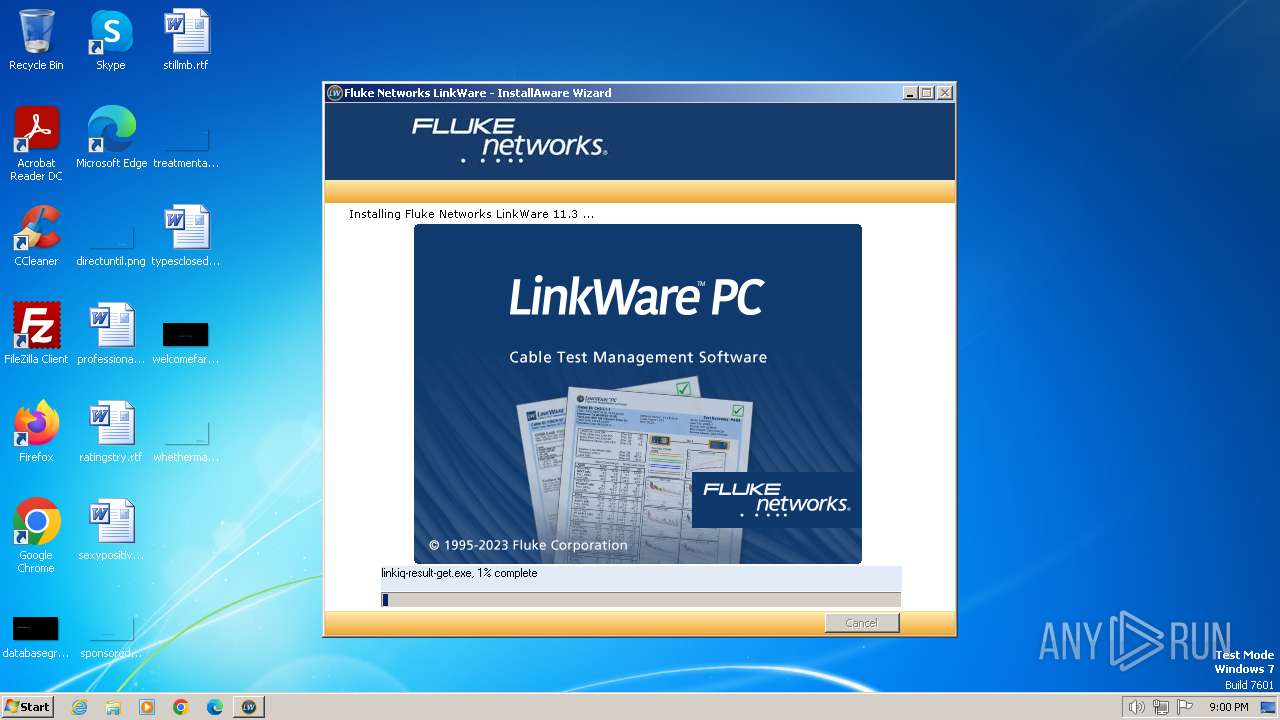
| 1344 | lw_11.3_build7_web.exe | C:\Users\admin\AppData\Local\Temp\mia3B0A.tmp\OFFLINE\3EF170F\798511AD\linkiq-result-get.exe | — | |
MD5:— | SHA256:— | |||
| 1344 | lw_11.3_build7_web.exe | C:\Users\admin\AppData\Local\Temp\mia3B0A.tmp\setup.exe | executable | |
MD5:AF2FD3BDE1303E17C8C28439639C3043 | SHA256:39E84EBC15B349FDA70498371506053507C5C753214C4362088C35CBC1021C94 | |||
| 3768 | setup.exe | C:\Users\admin\AppData\Local\Temp\mia1\componentslist.dfm | binary | |
MD5:7F2BE80E069A6DBFEF7852E539FCABBA | SHA256:EB245CC1BC366CC1640EBA860DC4047849FEF5110BE64BD3B4FDAFAEEBD765A6 | |||
| 1344 | lw_11.3_build7_web.exe | C:\Users\admin\AppData\Local\Temp\mia3B0A.tmp\mia.lib | executable | |
MD5:CBDCAC7234BBBE0682590957087668BA | SHA256:E42B865C76B5A2F5C96E5759C4EA6D492E1DB773F98C5F57B4B0CE1EA3C52498 | |||
| 3768 | setup.exe | C:\Users\admin\AppData\Local\Temp\mia1\componentstree.dfm | binary | |
MD5:BFBA6BFF1D6A35C1CE765F0DEBE3DB33 | SHA256:C393B631DC86575328899028CE82F92B90E1D954EB74C032EAD9BBEFBEE178E8 | |||
| 1344 | lw_11.3_build7_web.exe | C:\Users\admin\AppData\Local\Temp\mia3B0A.tmp\setup.msi | executable | |
MD5:178BD278BF4F821C7CF0FF0B5329640E | SHA256:4D0E4F4C0BA42EB837E5247C7C84E416835014C07D2379008BD51CFB0FEF5F66 | |||
| 1344 | lw_11.3_build7_web.exe | C:\Users\admin\AppData\Local\Temp\mia3B0A.tmp\setup.bmp | image | |
MD5:C19D9A9EF81CE2341EB6026A14BF4BDA | SHA256:0B1E1A8697FC78D691D3D3B875FA4FAF42F96AC8D5B886745380C8EB4E8B9CB1 | |||
| 1344 | lw_11.3_build7_web.exe | C:\Users\admin\AppData\Local\Temp\mia3B0A.tmp\setup.res | compressed | |
MD5:25510F49DAB7E964D735E2BAD6356C66 | SHA256:82D2C1A4D651925AAE244E06865E79E35E3C0415C76B23DD6BFF0549DD8549A6 | |||
| 3768 | setup.exe | C:\Users\admin\AppData\Local\Temp\mia1\finish.dfm.miaf | text | |
MD5:7545E96F48AA37EECA4EE00725F2A54D | SHA256:D8C45CD0993DB50DB71461AB097626928B58B1BD042F449B719AC421D0DC8964 | |||
| 3768 | setup.exe | C:\Users\admin\AppData\Local\Temp\mia.tmp | text | |
MD5:C5E3FF724A8DA478C83446138E05E234 | SHA256:32663D0CDABD0D00CEB1A1E11CD75C8F3E1BD9431F652BBF79B2D800EC898679 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
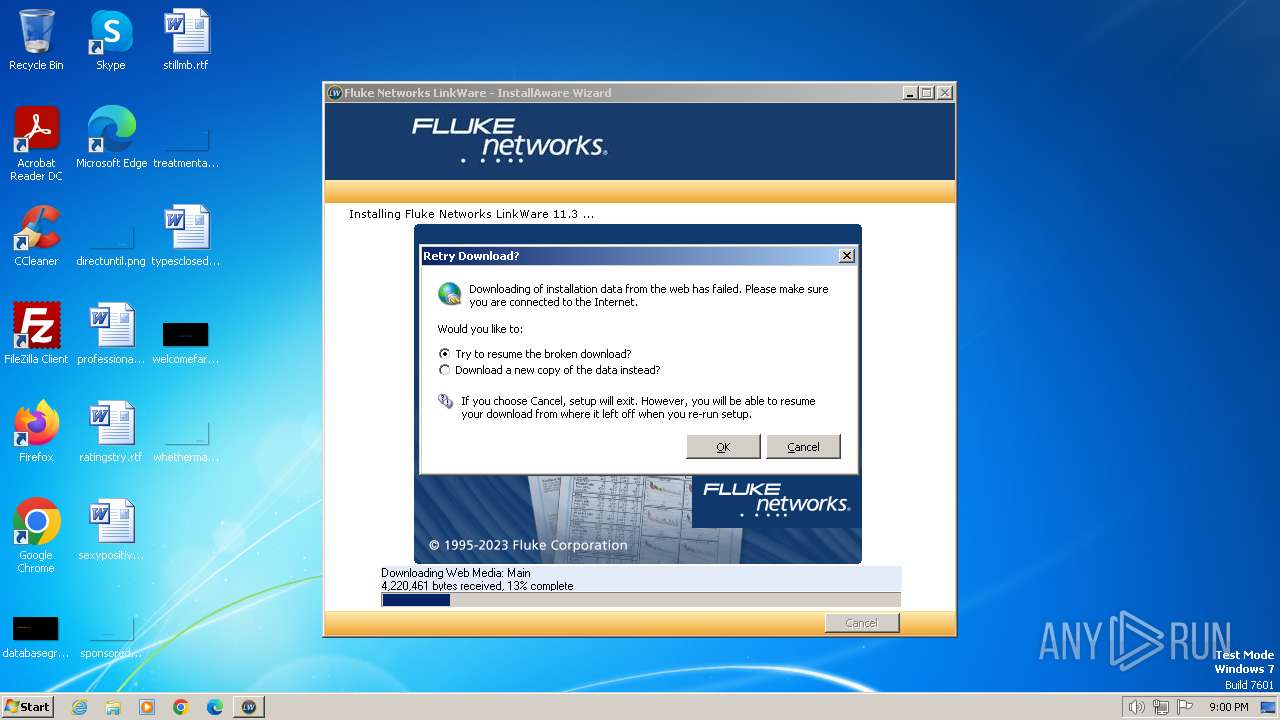
3768 | setup.exe | GET | — | 52.217.118.224:80 | http://s3.amazonaws.com/versiv-updates/linkware/v11.3/main.7zip | unknown | — | — | unknown |
3768 | setup.exe | GET | — | 52.217.118.224:80 | http://s3.amazonaws.com/versiv-updates/linkware/v11.3/main.7zip | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3768 | setup.exe | 52.217.118.224:80 | s3.amazonaws.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s3.amazonaws.com |
| shared |