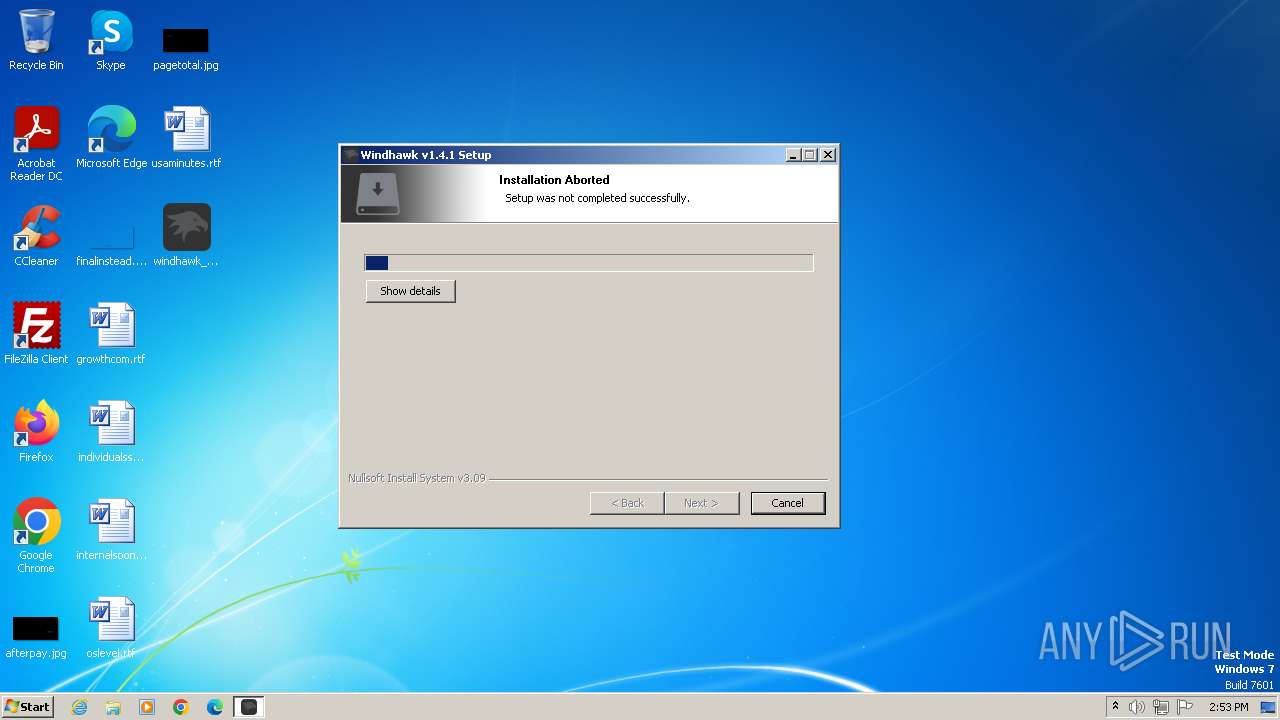
| File name: | windhawk_setup.exe |
| Full analysis: | https://app.any.run/tasks/22916be2-b06c-4241-ab6a-6581996e0f60 |
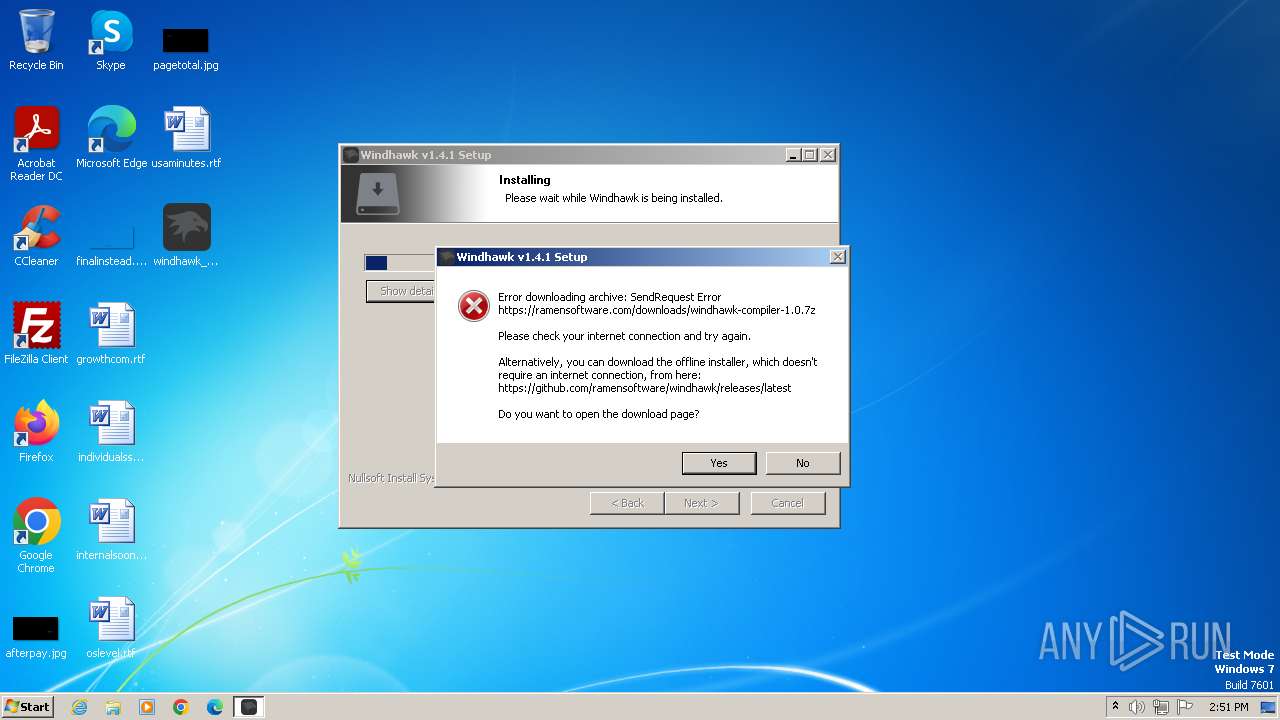
| Verdict: | Malicious activity |
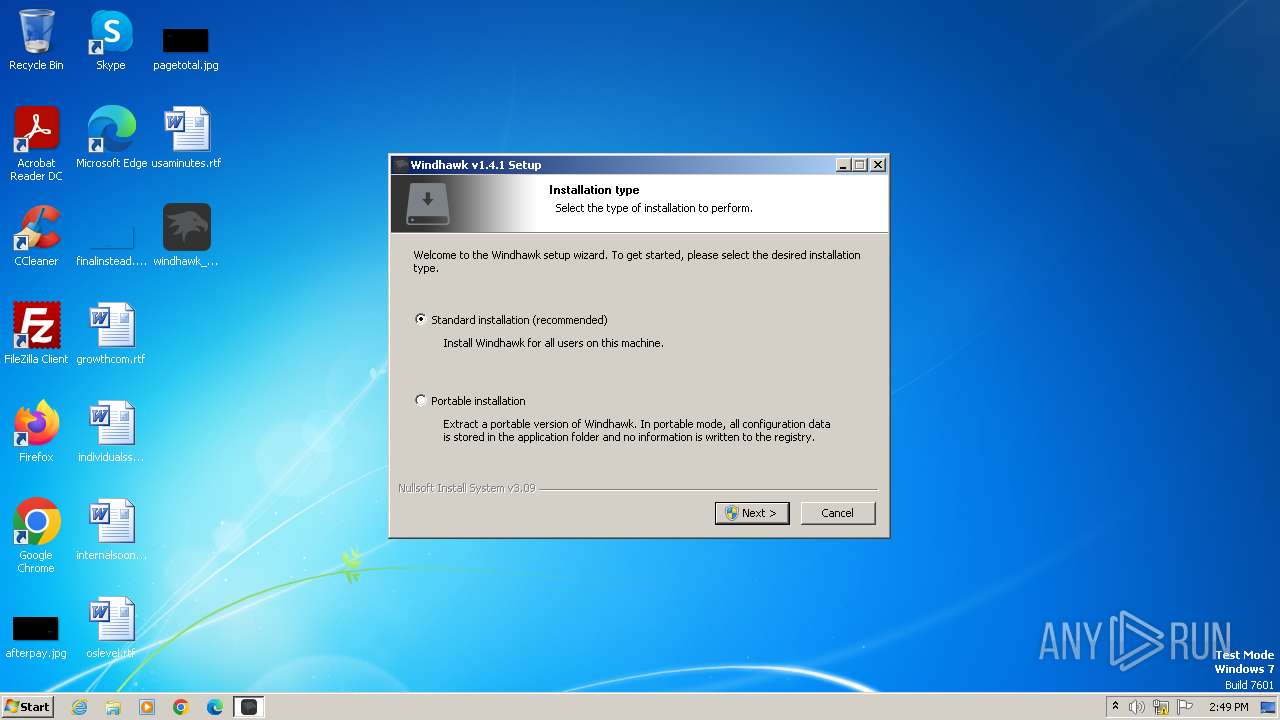
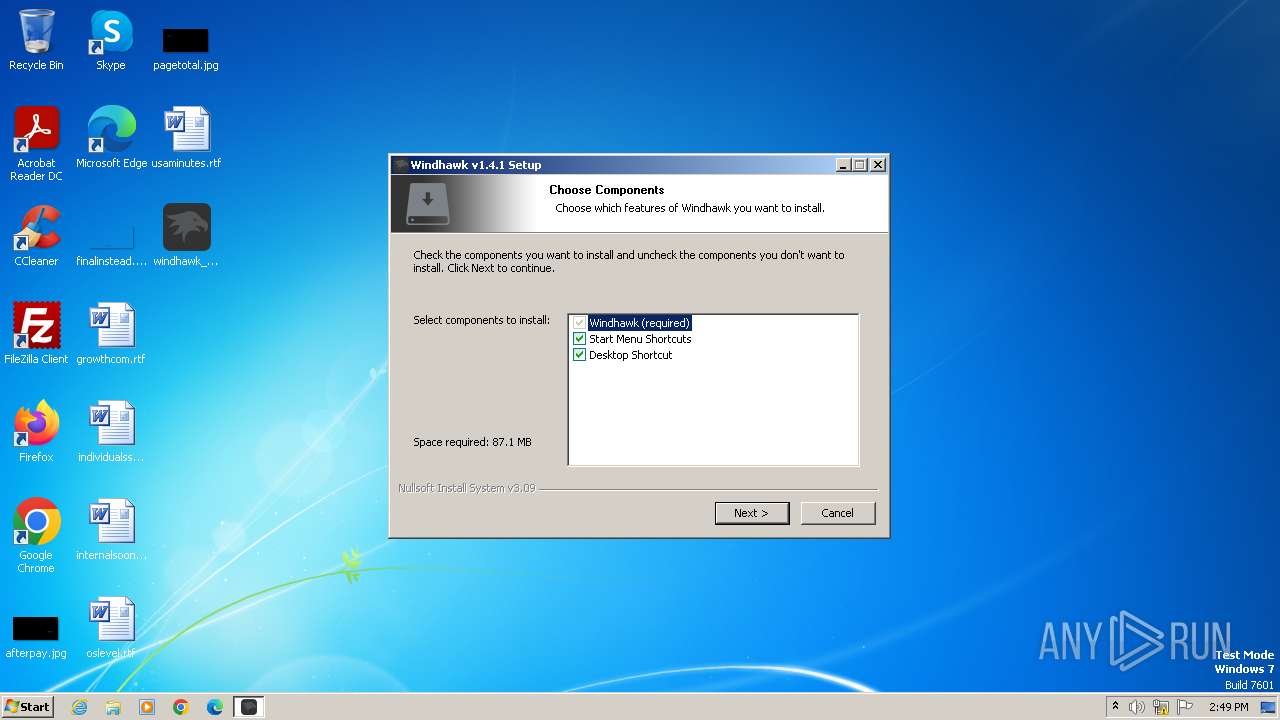
| Analysis date: | May 16, 2024, 13:48:50 |
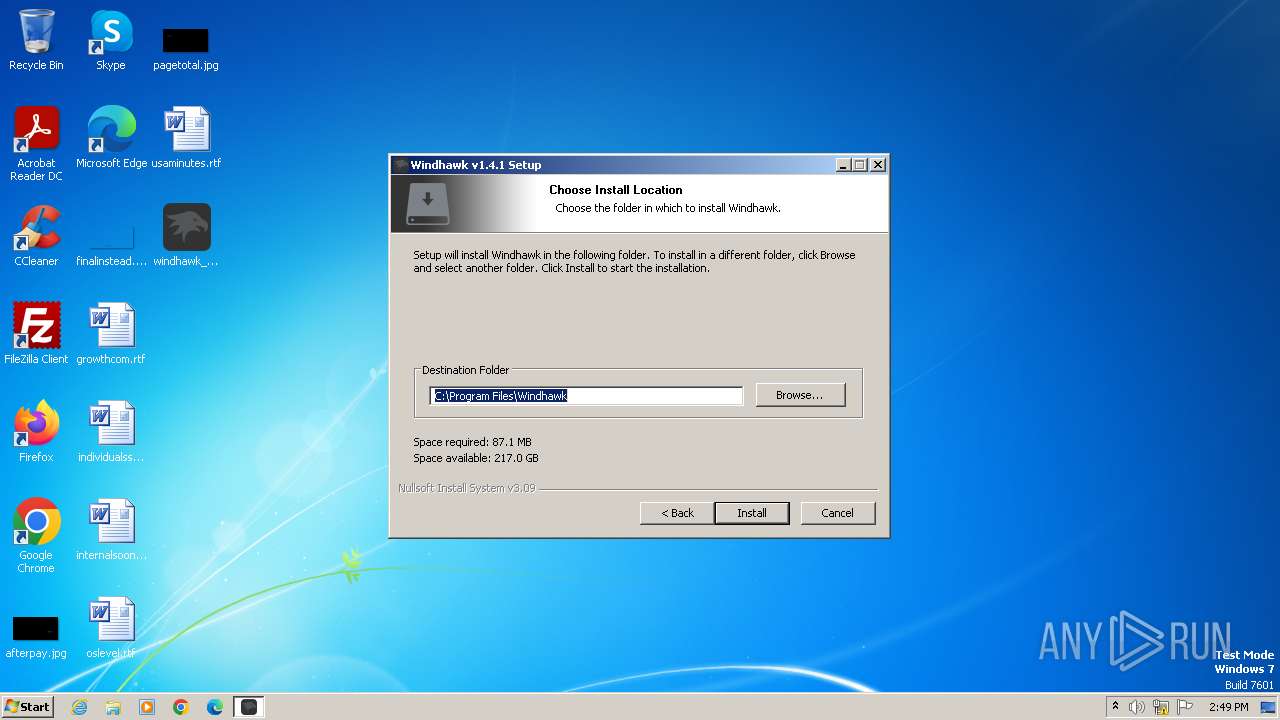
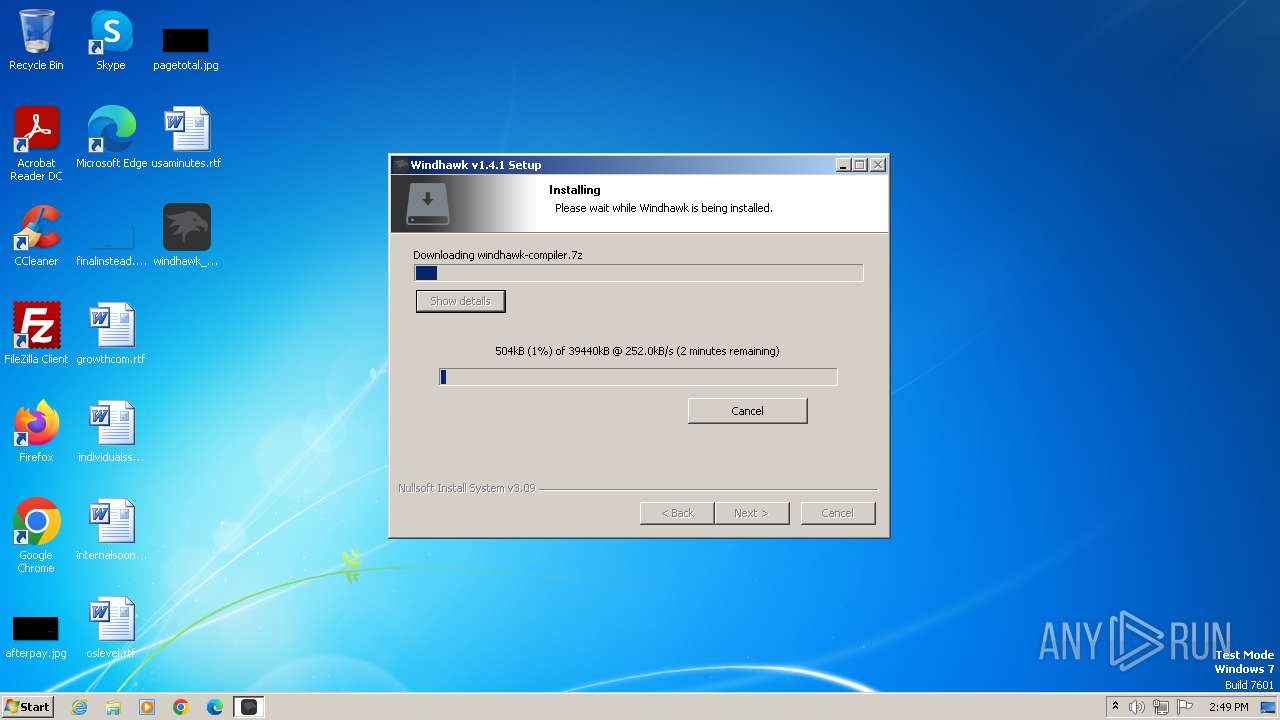
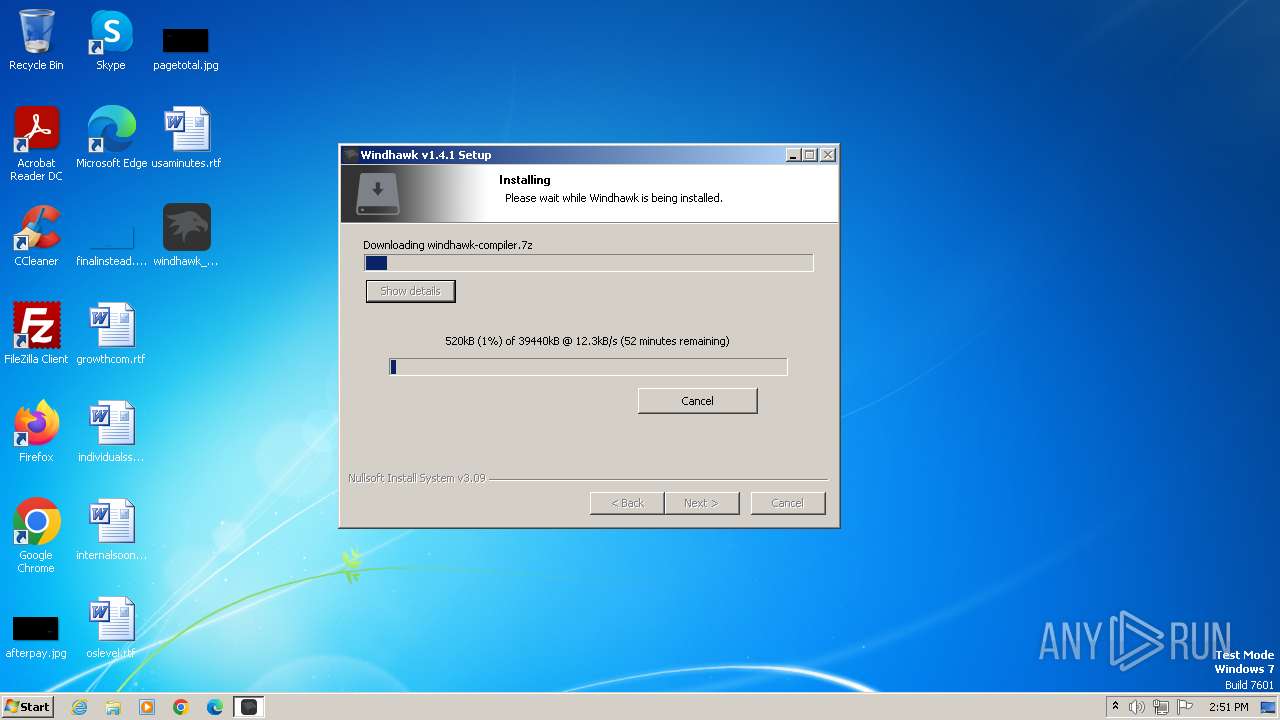
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A7699DF432C7A074CC1D26BAC0579C1B |
| SHA1: | 87CEDA7562E1FF4A8771BEAC0D51660E51AF3BA8 |
| SHA256: | 85DBFDA445BA4B23C167E9C3767FB812366642C6F40D3B4D1BA00040595CEC30 |
| SSDEEP: | 98304:iV/bU6bjxdPM6litq1SIRD8LypRf+tI6X6vp82uCSXI4T+YvN/BPS7sgjIvrOdYP:QUAZ4kmXAQjUYj |
MALICIOUS
Drops the executable file immediately after the start
- windhawk_setup.exe (PID: 4000)
- windhawk_setup.exe (PID: 1116)
SUSPICIOUS
The process creates files with name similar to system file names
- windhawk_setup.exe (PID: 4000)
- windhawk_setup.exe (PID: 1116)
Malware-specific behavior (creating "System.dll" in Temp)
- windhawk_setup.exe (PID: 4000)
- windhawk_setup.exe (PID: 1116)
Reads security settings of Internet Explorer
- windhawk_setup.exe (PID: 4000)
- windhawk_setup.exe (PID: 1116)
Executable content was dropped or overwritten
- windhawk_setup.exe (PID: 4000)
- windhawk_setup.exe (PID: 1116)
Reads the Internet Settings
- windhawk_setup.exe (PID: 4000)
- windhawk_setup.exe (PID: 1116)
Application launched itself
- windhawk_setup.exe (PID: 4000)
Adds/modifies Windows certificates
- windhawk_setup.exe (PID: 1116)
Reads settings of System Certificates
- windhawk_setup.exe (PID: 1116)
Checks Windows Trust Settings
- windhawk_setup.exe (PID: 1116)
INFO
Checks supported languages
- windhawk_setup.exe (PID: 4000)
- windhawk_setup.exe (PID: 1116)
- wmpnscfg.exe (PID: 524)
Reads the computer name
- windhawk_setup.exe (PID: 4000)
- windhawk_setup.exe (PID: 1116)
- wmpnscfg.exe (PID: 524)
Create files in a temporary directory
- windhawk_setup.exe (PID: 1116)
- windhawk_setup.exe (PID: 4000)
Checks proxy server information
- windhawk_setup.exe (PID: 1116)
Creates files in the program directory
- windhawk_setup.exe (PID: 1116)
Creates files or folders in the user directory
- windhawk_setup.exe (PID: 1116)
Manual execution by a user
- wmpnscfg.exe (PID: 524)
Reads the machine GUID from the registry
- windhawk_setup.exe (PID: 1116)
Reads the software policy settings
- windhawk_setup.exe (PID: 1116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 02:09:43+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3645 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.1.0 |
| ProductVersionNumber: | 1.4.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Ramen Software |
| FileDescription: | Windhawk |
| FileVersion: | 1.4.1 |
| LegalCopyright: | https://windhawk.net/ |
| ProductName: | Windhawk |
| ProductVersion: | 1.4.1 |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1116 | "C:\Users\admin\Desktop\windhawk_setup.exe" /STANDARD /LANG=1033 | C:\Users\admin\Desktop\windhawk_setup.exe | windhawk_setup.exe | ||||||||||||
User: admin Company: Ramen Software Integrity Level: HIGH Description: Windhawk Exit code: 2 Version: 1.4.1 Modules
| |||||||||||||||
| 4000 | "C:\Users\admin\Desktop\windhawk_setup.exe" | C:\Users\admin\Desktop\windhawk_setup.exe | explorer.exe | ||||||||||||
User: admin Company: Ramen Software Integrity Level: MEDIUM Description: Windhawk Exit code: 0 Version: 1.4.1 Modules
| |||||||||||||||
Total events
7 875
Read events
7 796
Write events
63
Delete events
16
Modification events
| (PID) Process: | (4000) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4000) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4000) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4000) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1116) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1116) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (1116) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (1116) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (1116) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (1116) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
14
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4000 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsg53A2.tmp\modern-header.bmp | image | |
MD5:DA5C5013B5FEABD247AC98460D5F4077 | SHA256:42023BAF6AB9CC3DAF47FBEBE76B78C6B22C560A863B557BEFEF4A68304928A5 | |||
| 4000 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb5382.tmp | binary | |
MD5:A5EBDD12CF3319FE824D4C64F25242E3 | SHA256:3FBCB036E478F03E9737EE2F1FA75B32657FFC796818FC61584EAA85DBAD7CFC | |||
| 4000 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsg53A2.tmp\System.dll | executable | |
MD5:4ADD245D4BA34B04F213409BFE504C07 | SHA256:9111099EFE9D5C9B391DC132B2FAF0A3851A760D4106D5368E30AC744EB42706 | |||
| 1116 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb79E7.tmp\INetC.dll | executable | |
MD5:40D7ECA32B2F4D29DB98715DD45BFAC5 | SHA256:85E03805F90F72257DD41BFDAA186237218BBB0EC410AD3B6576A88EA11DCCB9 | |||
| 1116 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb79E7.tmp\System.dll | executable | |
MD5:4ADD245D4BA34B04F213409BFE504C07 | SHA256:9111099EFE9D5C9B391DC132B2FAF0A3851A760D4106D5368E30AC744EB42706 | |||
| 1116 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb79E7.tmp\modern-header.bmp | image | |
MD5:DA5C5013B5FEABD247AC98460D5F4077 | SHA256:42023BAF6AB9CC3DAF47FBEBE76B78C6B22C560A863B557BEFEF4A68304928A5 | |||
| 4000 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsg53A2.tmp\nsDialogs.dll | executable | |
MD5:1D8F01A83DDD259BC339902C1D33C8F1 | SHA256:4B7D17DA290F41EBE244827CC295CE7E580DA2F7E9F7CC3EFC1ABC6898E3C9ED | |||
| 1116 | windhawk_setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:F4CF43768F928B60FB50245AA2BA197D | SHA256:7FB836A3BC5B532F165B3AEBFBE605B22ACDD379DB34939F47456864EFEBEC13 | |||
| 4000 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsg53A2.tmp\modern-wizard.bmp | image | |
MD5:566514B5802E326406DF34C35877484F | SHA256:4653F410DCB67A35E280BDEF7D563EF8F5788E72A05D472419F9E864AF563984 | |||
| 1116 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb79E7.tmp\modern-wizard.bmp | image | |
MD5:566514B5802E326406DF34C35877484F | SHA256:4653F410DCB67A35E280BDEF7D563EF8F5788E72A05D472419F9E864AF563984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
16
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1116 | windhawk_setup.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?be36ae1029c3a67f | unknown | — | — | unknown |
1116 | windhawk_setup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | — | — | unknown |
1116 | windhawk_setup.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | unknown |
1116 | windhawk_setup.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | unknown |
1116 | windhawk_setup.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEE4o94a2bBo7lCzSxA63QqU%3D | unknown | — | — | unknown |
1116 | windhawk_setup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
1116 | windhawk_setup.exe | 104.21.74.253:443 | ramensoftware.com | CLOUDFLARENET | — | unknown |
1116 | windhawk_setup.exe | 23.50.131.216:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1116 | windhawk_setup.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1116 | windhawk_setup.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
1116 | windhawk_setup.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | unknown |
1116 | windhawk_setup.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | shared |
1116 | windhawk_setup.exe | 185.199.110.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ramensoftware.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
github.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
objects.githubusercontent.com |
| shared |