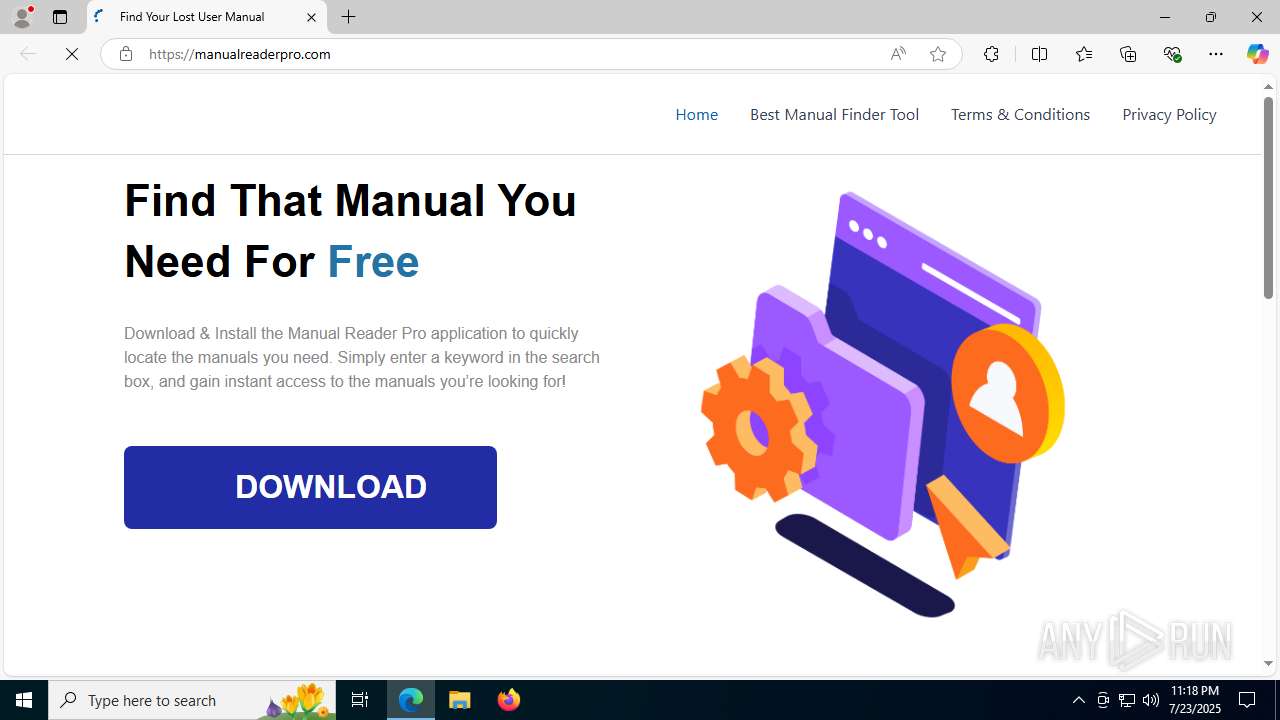
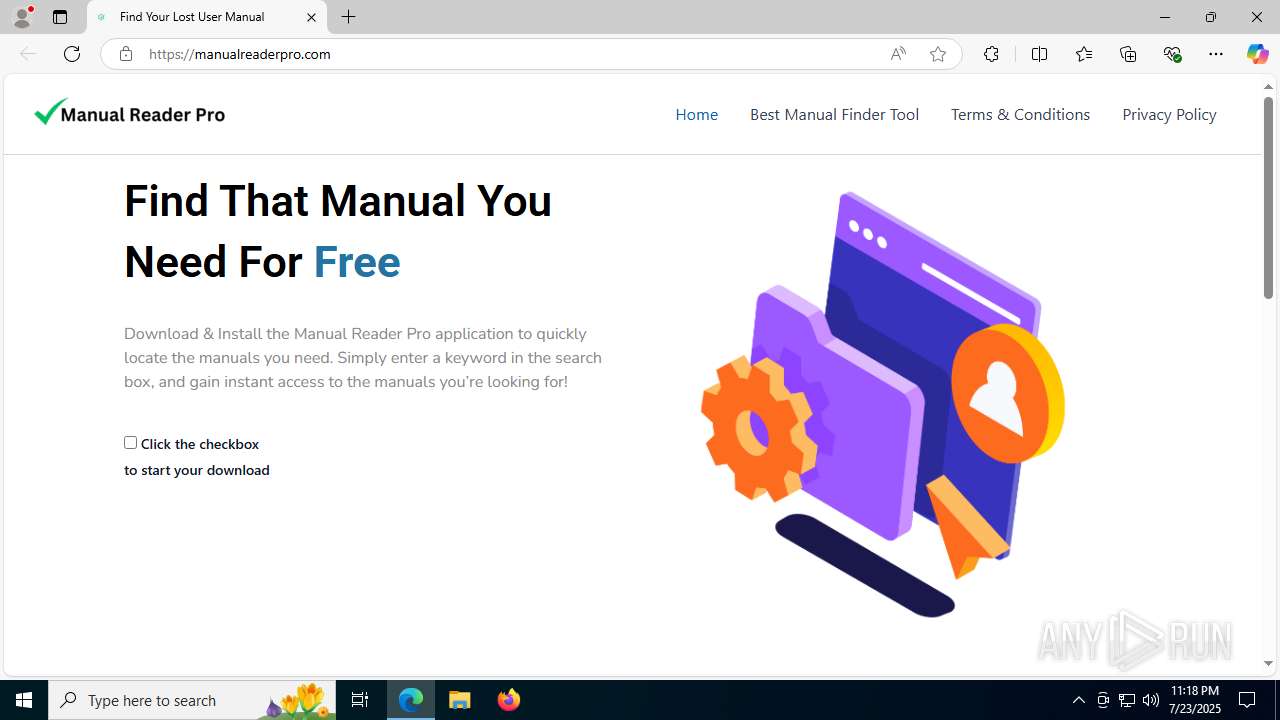
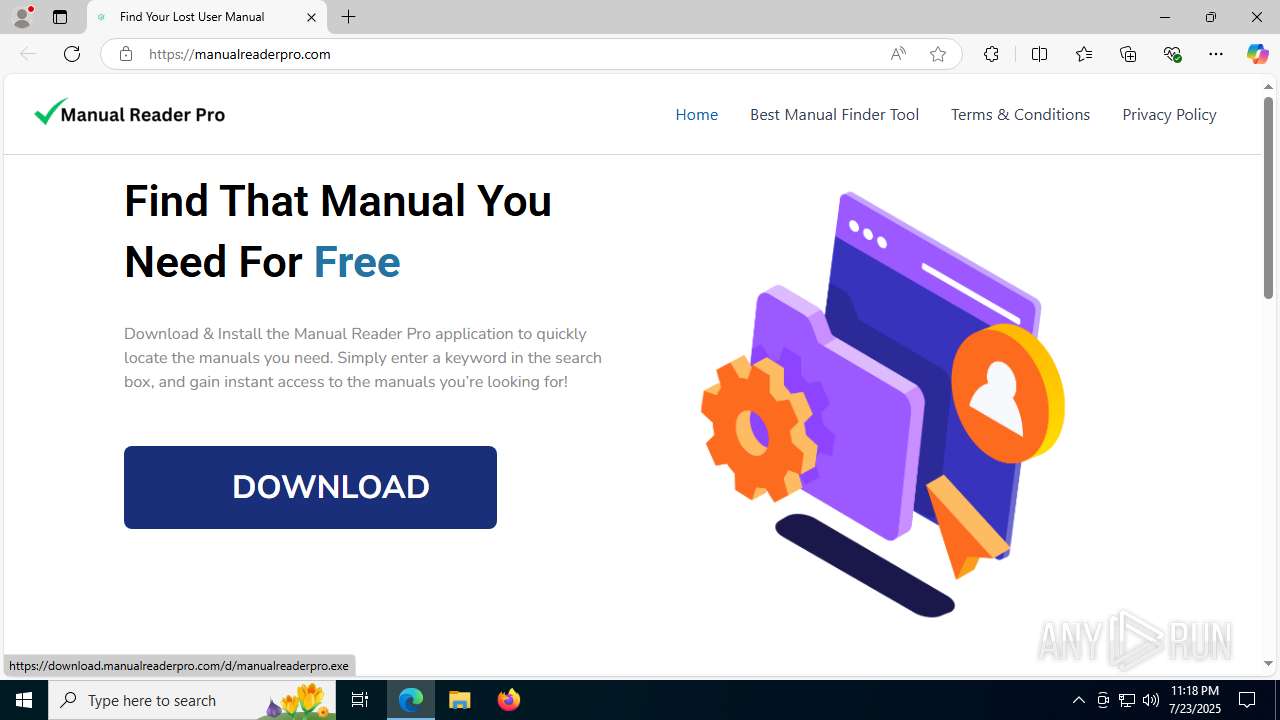
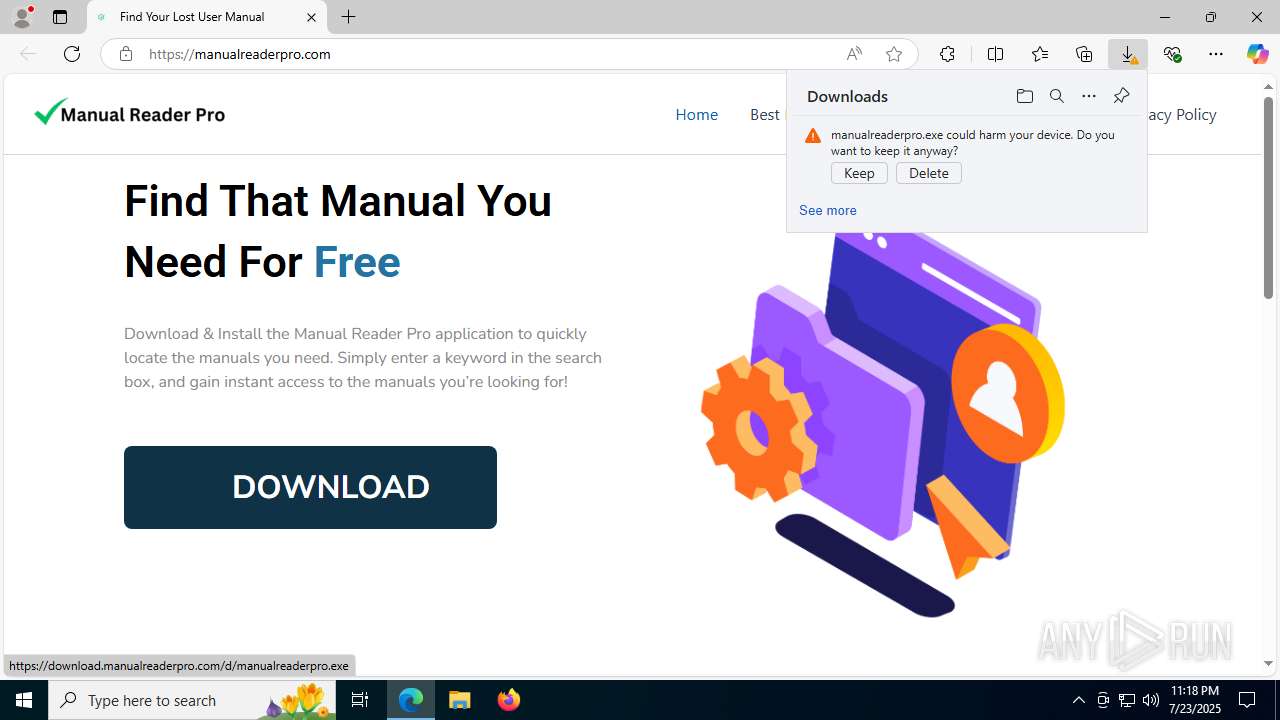
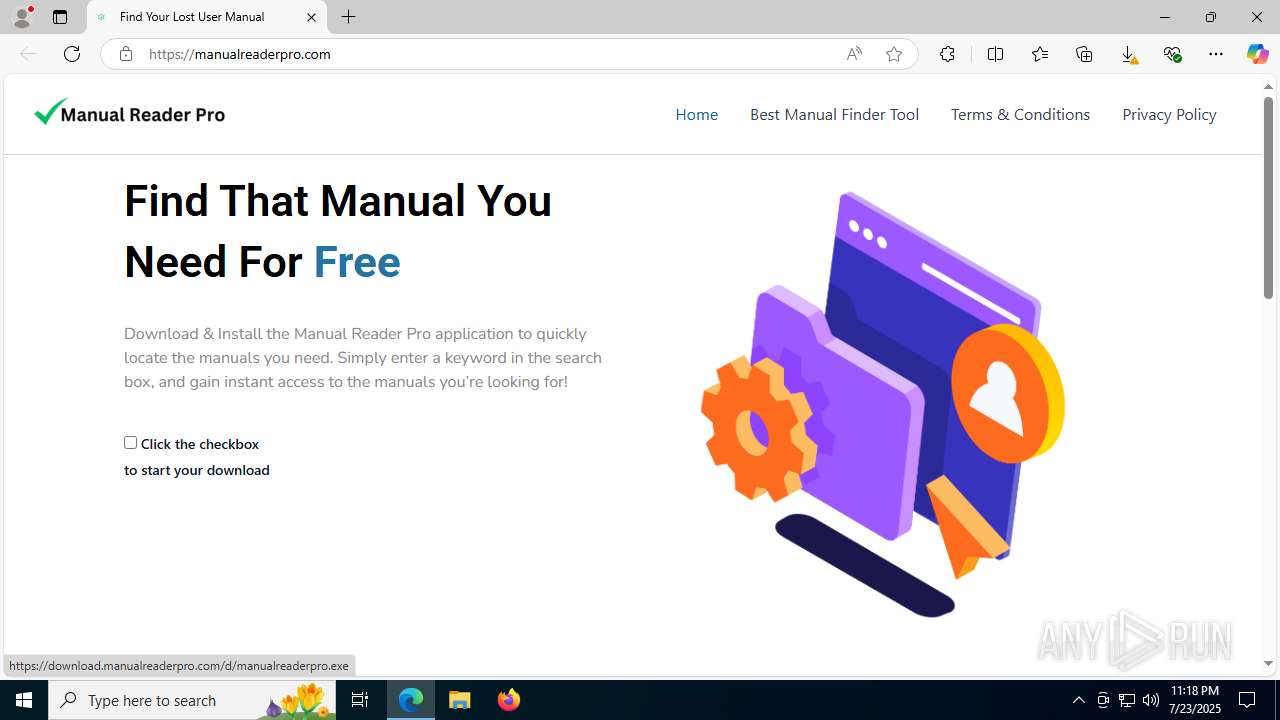
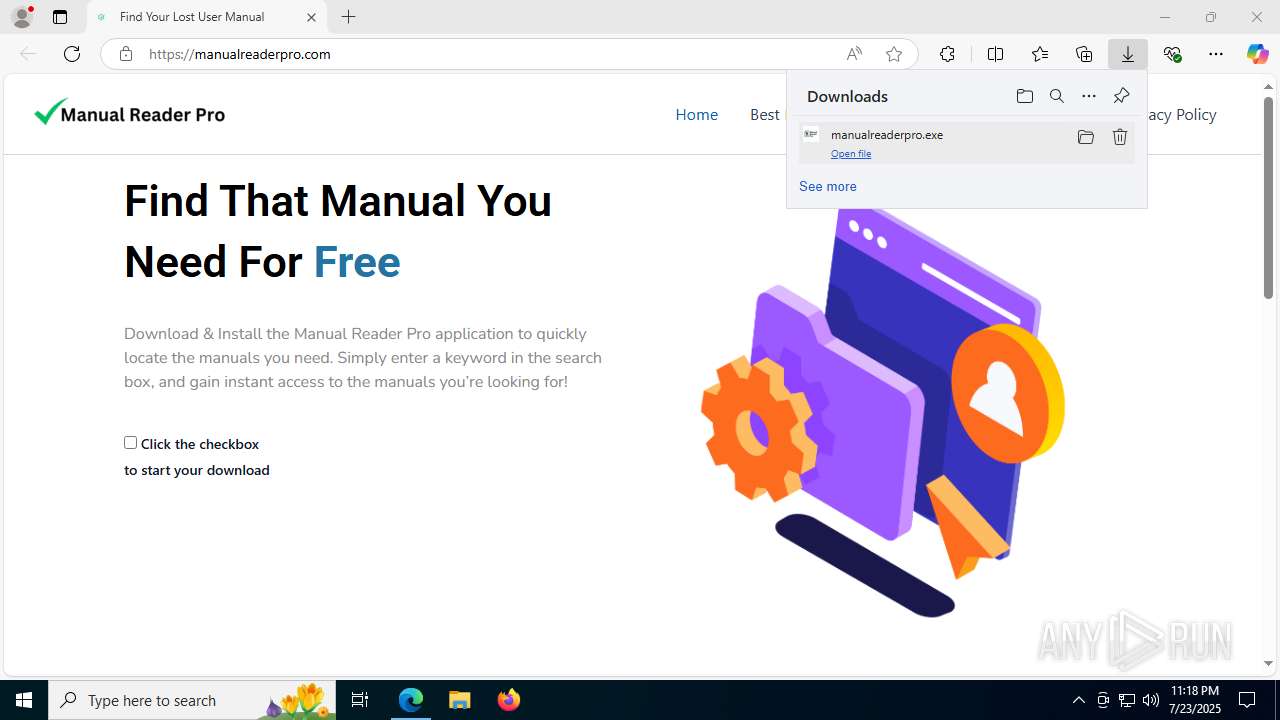
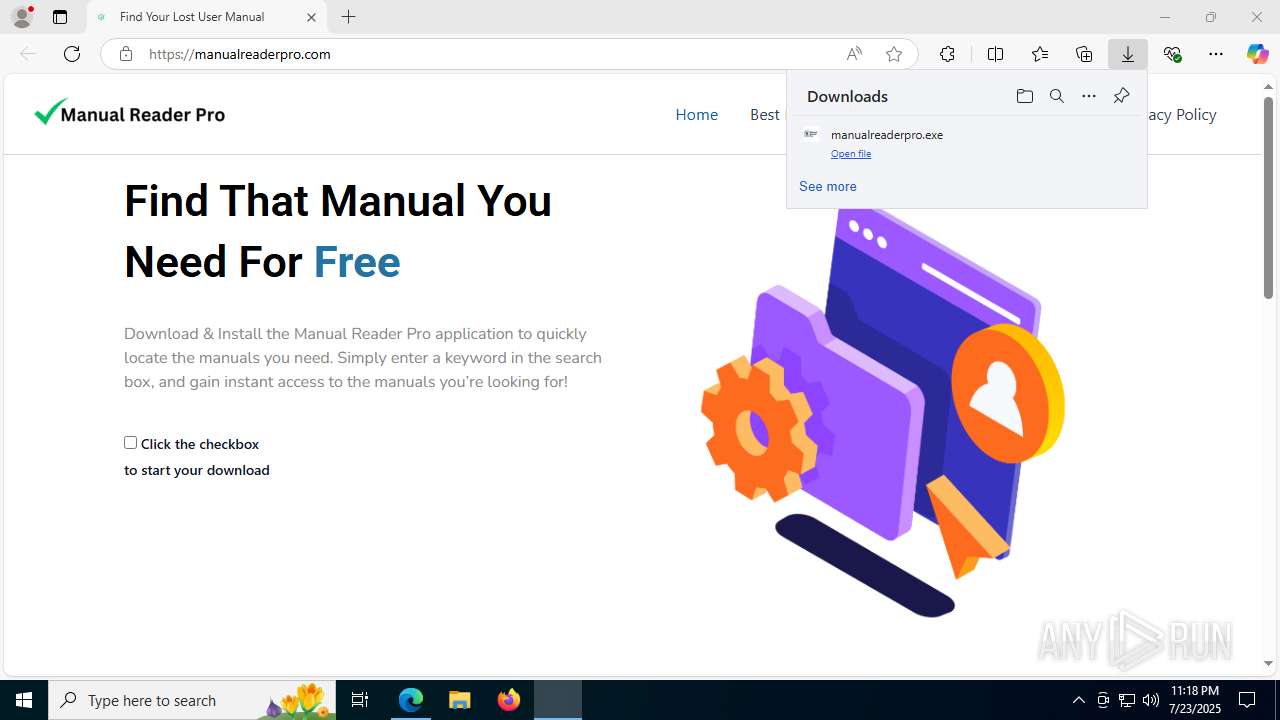
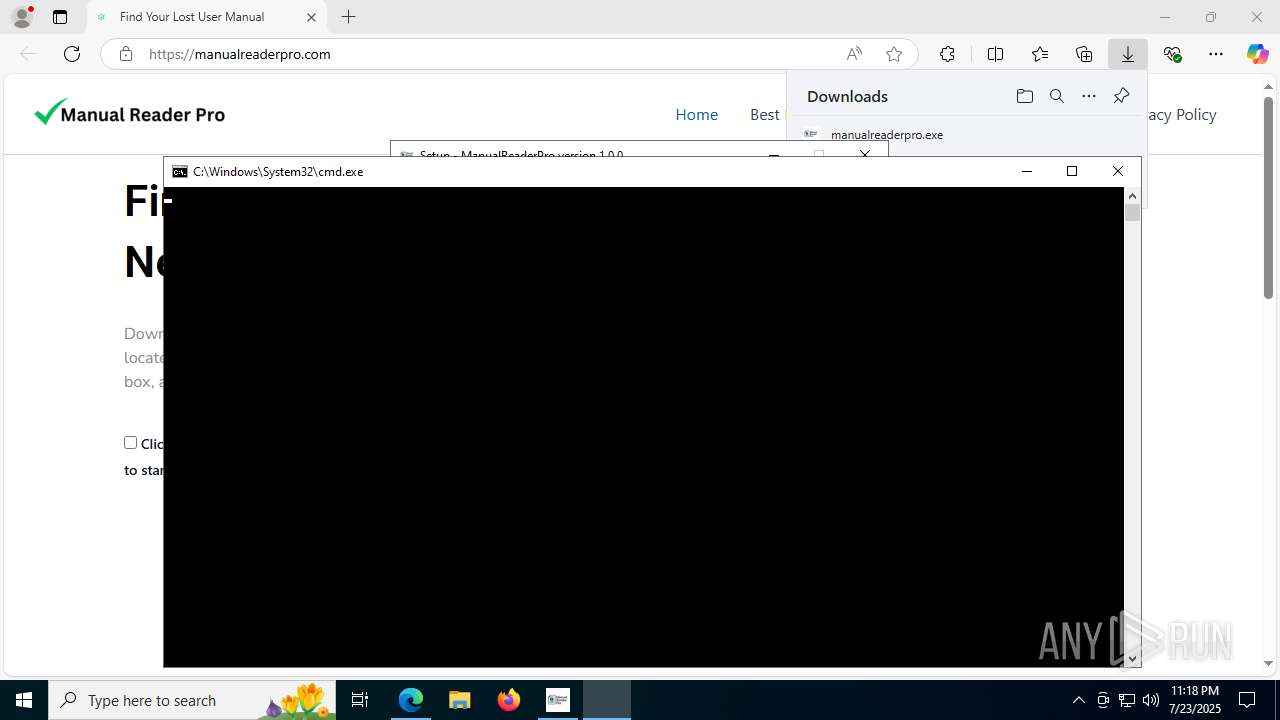
| URL: | https://manualreaderpro.com/ |
| Full analysis: | https://app.any.run/tasks/f56b3264-673f-424f-be36-25da38ca1fe1 |
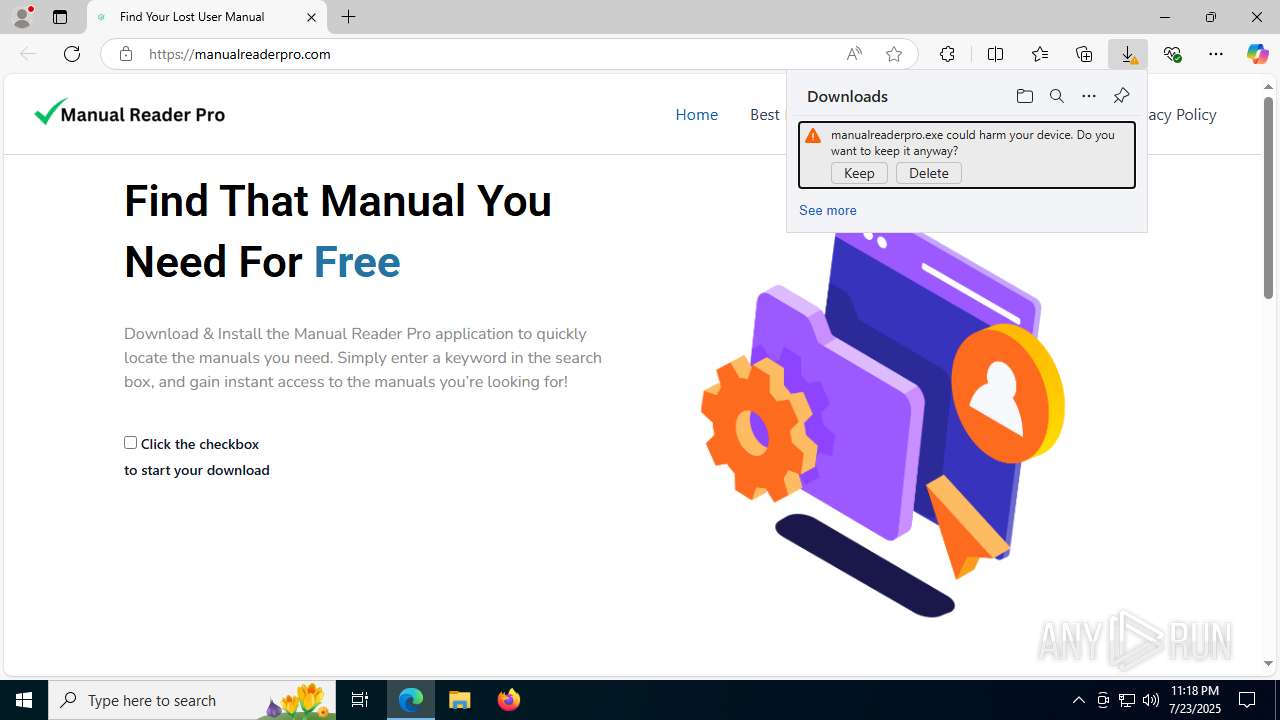
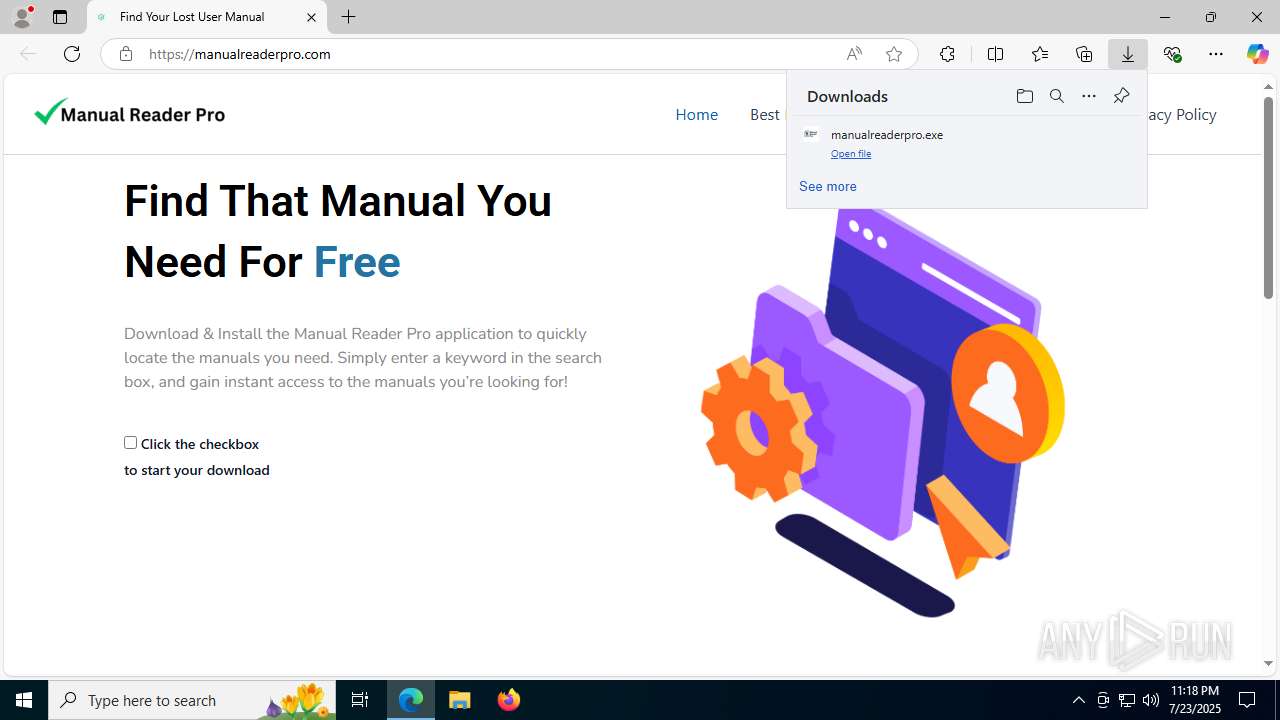
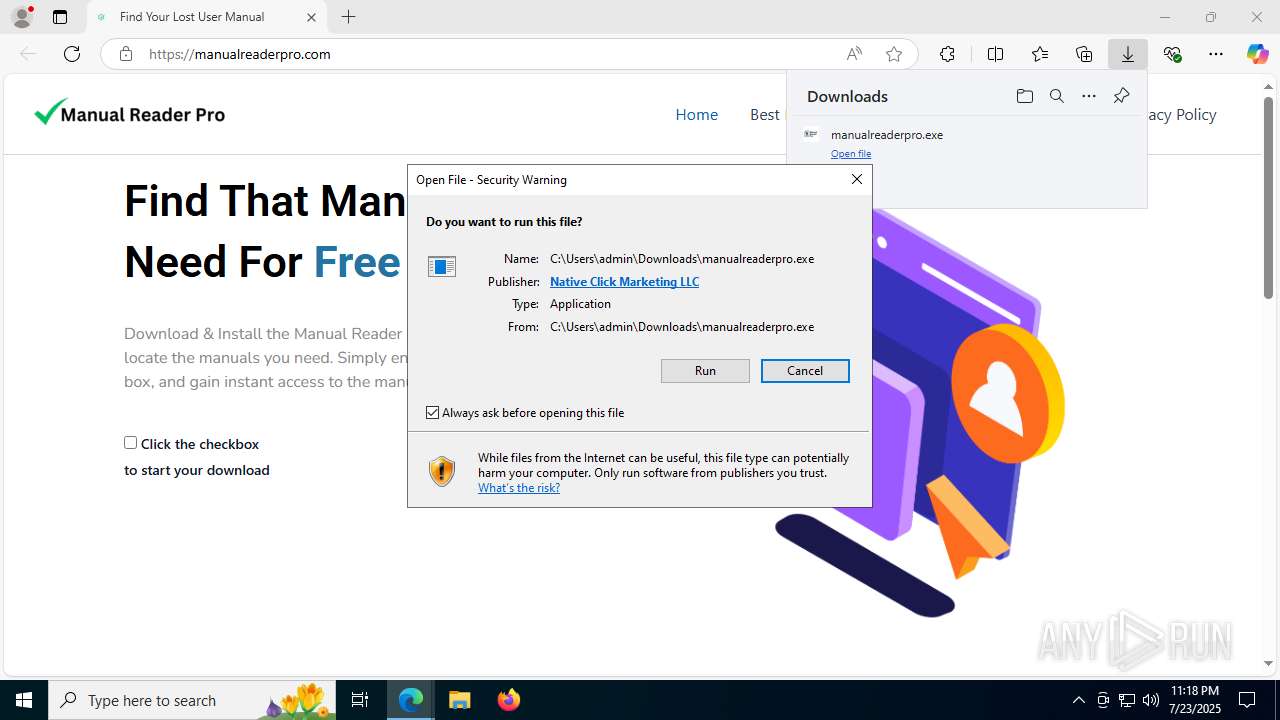
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2025, 23:18:21 |
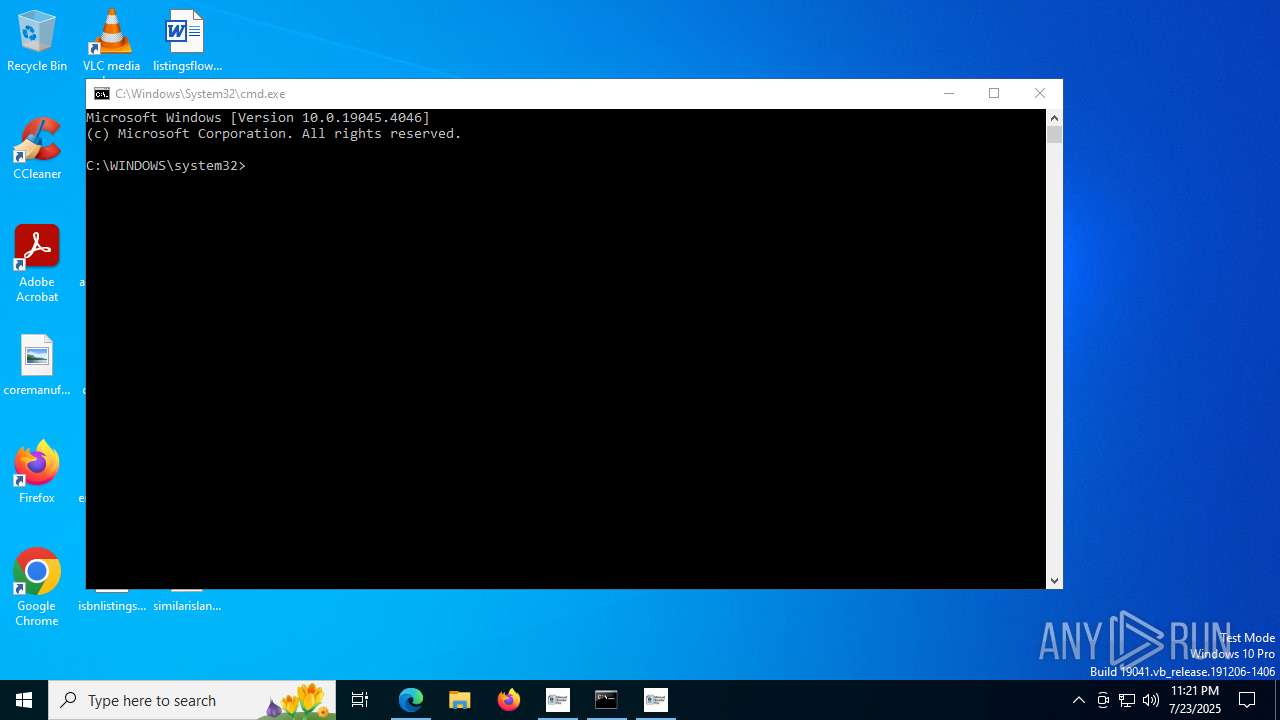
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 01D17ED2979F58B1831841CB2100AB32 |
| SHA1: | 271ABED69348BC5C0F47F2E2CC0EE2D5AB46AA56 |
| SHA256: | 85D8D527FCFDAF325A65B25064612662CA8E80D778C349B2E0FCFC23A19AB13D |
| SSDEEP: | 3:N8QgQE5t:2Qo5t |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7904)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 7840)
The DLL Hijacking
- msedgewebview2.exe (PID: 2384)
SUSPICIOUS
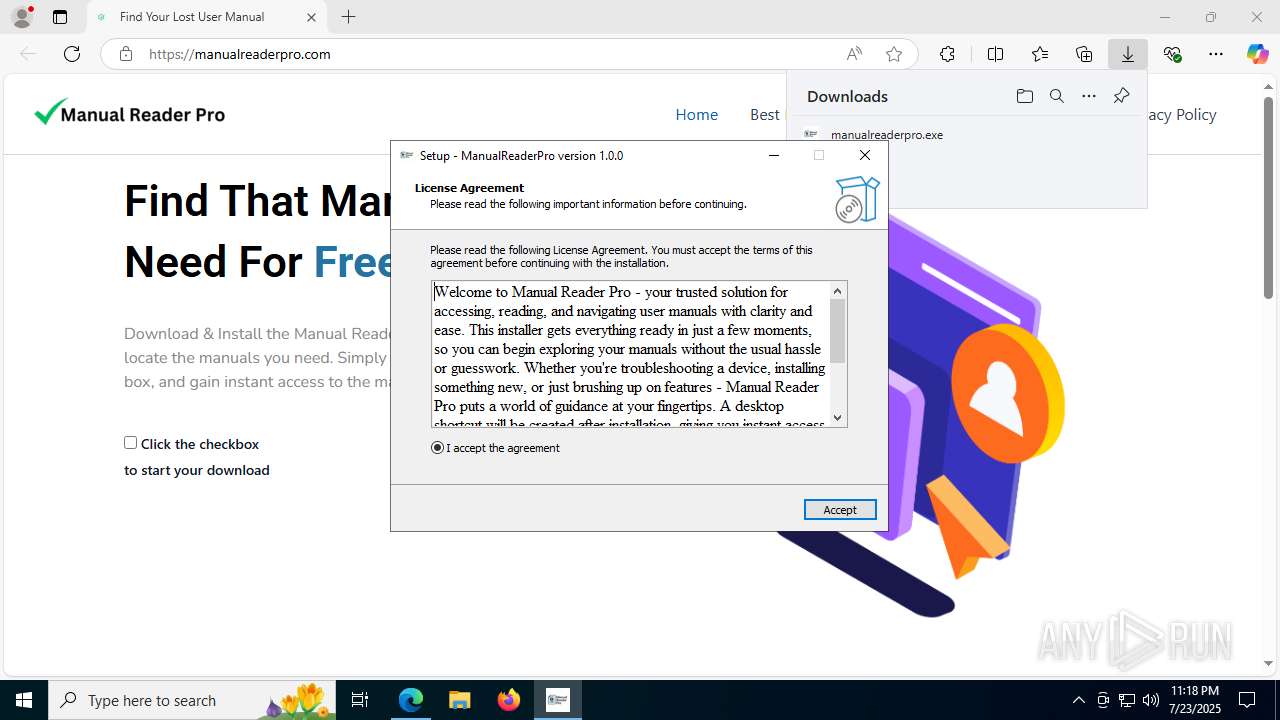
Reads the Windows owner or organization settings
- manualreaderpro.tmp (PID: 4228)
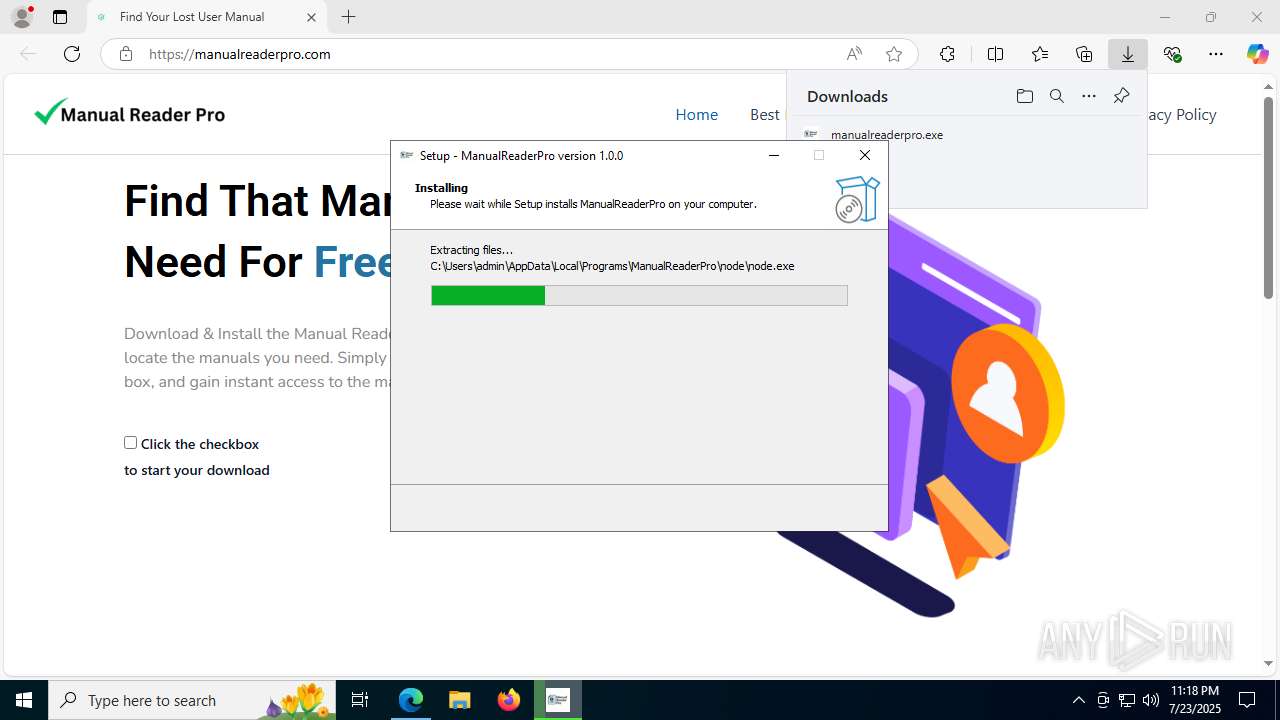
Executable content was dropped or overwritten
- manualreaderpro.exe (PID: 7428)
- manualreaderpro.tmp (PID: 4228)
- ManualReaderPro.exe (PID: 8016)
- tmp3CD0.exe (PID: 1216)
- MicrosoftEdgeUpdate.exe (PID: 7840)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 3112)
- setup.exe (PID: 7000)
- msedgewebview2.exe (PID: 5968)
- msedgewebview2.exe (PID: 7056)
Reads security settings of Internet Explorer
- manualreaderpro.tmp (PID: 4228)
- ManualReaderPro.exe (PID: 8016)
- MicrosoftEdgeUpdate.exe (PID: 7840)
- MicrosoftEdgeUpdate.exe (PID: 7468)
- msedgewebview2.exe (PID: 8176)
The process executes via Task Scheduler
- cmd.exe (PID: 7824)
Executes script using NodeJS
- node.exe (PID: 7992)
Process drops legitimate windows executable
- manualreaderpro.tmp (PID: 4228)
- ManualReaderPro.exe (PID: 8016)
- tmp3CD0.exe (PID: 1216)
- MicrosoftEdgeUpdate.exe (PID: 7840)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 3112)
- setup.exe (PID: 7000)
- msedgewebview2.exe (PID: 5968)
- msedgewebview2.exe (PID: 7056)
Starts CMD.EXE for commands execution
- manualreaderpro.tmp (PID: 4228)
- node.exe (PID: 7992)
Starts a Microsoft application from unusual location
- tmp3CD0.exe (PID: 1216)
- MicrosoftEdgeUpdate.exe (PID: 7840)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 7840)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8144)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8136)
- MicrosoftEdgeUpdate.exe (PID: 1192)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1880)
Application launched itself
- setup.exe (PID: 7000)
- MicrosoftEdgeUpdate.exe (PID: 7468)
- msedgewebview2.exe (PID: 8176)
Searches for installed software
- setup.exe (PID: 7000)
- msedgewebview2.exe (PID: 8176)
Creates a software uninstall entry
- setup.exe (PID: 7000)
Checks for external IP
- msedgewebview2.exe (PID: 5968)
INFO
Application launched itself
- msedge.exe (PID: 5172)
Reads Environment values
- identity_helper.exe (PID: 7820)
- node.exe (PID: 7992)
- MicrosoftEdgeUpdate.exe (PID: 6256)
- MicrosoftEdgeUpdate.exe (PID: 7812)
- msedgewebview2.exe (PID: 8176)
Reads the computer name
- identity_helper.exe (PID: 7820)
- manualreaderpro.tmp (PID: 4228)
- ManualReaderPro.exe (PID: 8016)
- node.exe (PID: 7992)
- MicrosoftEdgeUpdate.exe (PID: 1192)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8136)
- MicrosoftEdgeUpdate.exe (PID: 7840)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8144)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1880)
- MicrosoftEdgeUpdate.exe (PID: 6256)
- MicrosoftEdgeUpdate.exe (PID: 1976)
- MicrosoftEdgeUpdate.exe (PID: 7468)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 3112)
- setup.exe (PID: 7000)
- MicrosoftEdgeUpdateCore.exe (PID: 5968)
- MicrosoftEdgeUpdate.exe (PID: 6036)
- MicrosoftEdgeUpdate.exe (PID: 7812)
- msedgewebview2.exe (PID: 8176)
- msedgewebview2.exe (PID: 2384)
- msedgewebview2.exe (PID: 5968)
- msedgewebview2.exe (PID: 3944)
Checks supported languages
- identity_helper.exe (PID: 7820)
- manualreaderpro.exe (PID: 7428)
- manualreaderpro.tmp (PID: 4228)
- ManualReaderPro.exe (PID: 8016)
- node.exe (PID: 7992)
- tmp3CD0.exe (PID: 1216)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8136)
- MicrosoftEdgeUpdate.exe (PID: 1192)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8144)
- MicrosoftEdgeUpdate.exe (PID: 6256)
- MicrosoftEdgeUpdate.exe (PID: 1976)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1880)
- MicrosoftEdgeUpdate.exe (PID: 7840)
- MicrosoftEdgeUpdate.exe (PID: 7468)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 3112)
- setup.exe (PID: 7000)
- setup.exe (PID: 3688)
- MicrosoftEdgeUpdateCore.exe (PID: 5968)
- MicrosoftEdgeUpdate.exe (PID: 6036)
- MicrosoftEdgeUpdate.exe (PID: 7812)
- msedgewebview2.exe (PID: 8176)
- msedgewebview2.exe (PID: 2384)
- msedgewebview2.exe (PID: 5968)
- msedgewebview2.exe (PID: 1156)
- msedgewebview2.exe (PID: 7840)
- msedgewebview2.exe (PID: 7708)
- msedgewebview2.exe (PID: 7340)
- msedgewebview2.exe (PID: 4192)
- msedgewebview2.exe (PID: 4788)
- msedgewebview2.exe (PID: 7304)
- msedgewebview2.exe (PID: 4120)
- msedgewebview2.exe (PID: 7996)
- msedgewebview2.exe (PID: 2876)
- msedgewebview2.exe (PID: 7620)
- msedgewebview2.exe (PID: 6876)
- msedgewebview2.exe (PID: 4104)
- msedgewebview2.exe (PID: 5708)
- msedgewebview2.exe (PID: 7056)
- msedgewebview2.exe (PID: 7500)
- msedgewebview2.exe (PID: 8188)
- msedgewebview2.exe (PID: 3944)
Executable content was dropped or overwritten
- msedge.exe (PID: 3720)
- msedge.exe (PID: 5172)
Create files in a temporary directory
- manualreaderpro.exe (PID: 7428)
- manualreaderpro.tmp (PID: 4228)
- ManualReaderPro.exe (PID: 8016)
- tmp3CD0.exe (PID: 1216)
- msedgewebview2.exe (PID: 8176)
Reads the machine GUID from the registry
- ManualReaderPro.exe (PID: 8016)
- manualreaderpro.tmp (PID: 4228)
- MicrosoftEdgeUpdate.exe (PID: 7468)
- msedgewebview2.exe (PID: 8176)
- msedgewebview2.exe (PID: 3944)
Reads the software policy settings
- manualreaderpro.tmp (PID: 4228)
- ManualReaderPro.exe (PID: 8016)
- MicrosoftEdgeUpdate.exe (PID: 6256)
- MicrosoftEdgeUpdate.exe (PID: 7468)
- MicrosoftEdgeUpdate.exe (PID: 7812)
- slui.exe (PID: 1880)
Creates files or folders in the user directory
- manualreaderpro.tmp (PID: 4228)
- node.exe (PID: 7992)
- MicrosoftEdgeUpdate.exe (PID: 7840)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 3112)
- MicrosoftEdgeUpdate.exe (PID: 7468)
- setup.exe (PID: 7000)
- setup.exe (PID: 3688)
- msedgewebview2.exe (PID: 8176)
- msedgewebview2.exe (PID: 1156)
- msedgewebview2.exe (PID: 5968)
- msedgewebview2.exe (PID: 3944)
The sample compiled with english language support
- manualreaderpro.tmp (PID: 4228)
- ManualReaderPro.exe (PID: 8016)
- MicrosoftEdgeUpdate.exe (PID: 7840)
- tmp3CD0.exe (PID: 1216)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 3112)
- setup.exe (PID: 7000)
- msedgewebview2.exe (PID: 7056)
Creates a software uninstall entry
- manualreaderpro.tmp (PID: 4228)
Disables trace logs
- ManualReaderPro.exe (PID: 8016)
Checks proxy server information
- ManualReaderPro.exe (PID: 8016)
- MicrosoftEdgeUpdate.exe (PID: 6256)
- MicrosoftEdgeUpdate.exe (PID: 7468)
- MicrosoftEdgeUpdate.exe (PID: 7812)
- slui.exe (PID: 1880)
- msedgewebview2.exe (PID: 8176)
Detects InnoSetup installer (YARA)
- manualreaderpro.exe (PID: 7428)
- manualreaderpro.tmp (PID: 4228)
Compiled with Borland Delphi (YARA)
- manualreaderpro.exe (PID: 7428)
- manualreaderpro.tmp (PID: 4228)
Process checks computer location settings
- ManualReaderPro.exe (PID: 8016)
- MicrosoftEdgeUpdate.exe (PID: 7840)
- setup.exe (PID: 7000)
- msedgewebview2.exe (PID: 8176)
- msedgewebview2.exe (PID: 7708)
- msedgewebview2.exe (PID: 7840)
- msedgewebview2.exe (PID: 4192)
- msedgewebview2.exe (PID: 4120)
- msedgewebview2.exe (PID: 7996)
- msedgewebview2.exe (PID: 2876)
- msedgewebview2.exe (PID: 7620)
- msedgewebview2.exe (PID: 6876)
- msedgewebview2.exe (PID: 4104)
Reads product name
- node.exe (PID: 7992)
Launching a file from a Registry key
- MicrosoftEdgeUpdate.exe (PID: 7840)
Manual execution by a user
- cmd.exe (PID: 7876)
- MicrosoftEdgeUpdateCore.exe (PID: 5968)
Reads CPU info
- msedgewebview2.exe (PID: 8176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
246
Monitored processes
93
Malicious processes
9
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6640,i,14511287859450950199,1243110670371307182,262144 --variations-seed-version --mojo-platform-channel-handle=9008 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3672,i,14511287859450950199,1243110670371307182,262144 --variations-seed-version --mojo-platform-channel-handle=3744 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 828 | C:\WINDOWS\system32\cmd.exe /d /s /c "C:\WINDOWS\system32\reg.exe QUERY "HKLM\Software\Microsoft\Cryptography" /v MachineGuid" | C:\Windows\System32\cmd.exe | — | node.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.95\msedgewebview2.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Programs\ManualReaderPro\ManualReaderPro.exe.WebView2\EBWebView /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Programs\ManualReaderPro\ManualReaderPro.exe.WebView2\EBWebView\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=138.0.7204.158 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.95\msedgewebview2.exe --annotation=plat=Win64 "--annotation=prod=Edge WebView2" --annotation=ver=138.0.3351.95 --initial-client-data=0x184,0x188,0x18c,0x160,0x194,0x7ffc44eda178,0x7ffc44eda184,0x7ffc44eda190 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.95\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 138.0.3351.95 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://manualreaderpro.com/thank | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | manualreaderpro.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /regserver | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\AppData\Local\Temp\tmp3CD0.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\tmp3CD0.exe | ManualReaderPro.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2760,i,14511287859450950199,1243110670371307182,262144 --variations-seed-version --mojo-platform-channel-handle=2304 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1880 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 244
Read events
23 418
Write events
1 758
Delete events
68
Modification events
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3B75AC3537992F00 | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7E64B25E-EFB4-4A69-843C-76E24B0D4D63} | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F95DD5FB-9AD6-44FE-9B1E-C9FAB8D956E5} | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {91185362-6010-4FD4-9F9B-7636DC8E80A2} | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {75F552F8-66FE-4145-B78C-1F0A62532A3B} | |||
| (PID) Process: | (5172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459454 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1D3CBA81-FCAC-4AA9-B159-6635D6F1C439} | |||
Executable files
234
Suspicious files
640
Text files
159
Unknown types
109
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d0b8.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d0b8.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d0b8.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d0b8.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d0a9.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
188
DNS requests
208
Threats
106
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2528 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5172 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
5172 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEDE8qcg4zdsh5ONU5tvwIWo%3D | unknown | — | — | whitelisted |
3720 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:kClww3Ah1ypOwpvoDbNtl85WmNVu4vTUyWKqsbg4j04&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7668 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7668 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4320 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7aa19579-c418-44fd-8406-8933fb3edba4?P1=1753917540&P2=404&P3=2&P4=HlKHyZ%2f9h5iFgsq%2fYyjs0f3j0p6zhbYbjjSsx8MCuo4p2v7Zl5aH1Ii3M4kevg%2fSyvk%2fv6if3HFtWbuwxvH3QQ%3d%3d | unknown | — | — | whitelisted |
4320 | svchost.exe | GET | — | 199.232.214.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7aa19579-c418-44fd-8406-8933fb3edba4?P1=1753917540&P2=404&P3=2&P4=HlKHyZ%2f9h5iFgsq%2fYyjs0f3j0p6zhbYbjjSsx8MCuo4p2v7Zl5aH1Ii3M4kevg%2fSyvk%2fv6if3HFtWbuwxvH3QQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3876 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3720 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3720 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3720 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3720 | msedge.exe | 188.114.96.3:443 | manualreaderpro.com | CLOUDFLARENET | NL | malicious |
3720 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
manualreaderpro.com |
| malicious |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google.com |
| whitelisted |
cdn.mxpnl.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3720 | msedge.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (manualreaderpro .com) |
3720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2200 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (manualreaderproweb .com) |
Process | Message |
|---|---|
ManualReaderPro.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ManualReaderPro.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ManualReaderPro.exe | WebView2 Warning: Using default User Data Folder is not recommended, please see documentation. https://go.microsoft.com/fwlink/?linkid=2187341
|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Programs\ManualReaderPro\ManualReaderPro.exe.WebView2 directory exists )
|