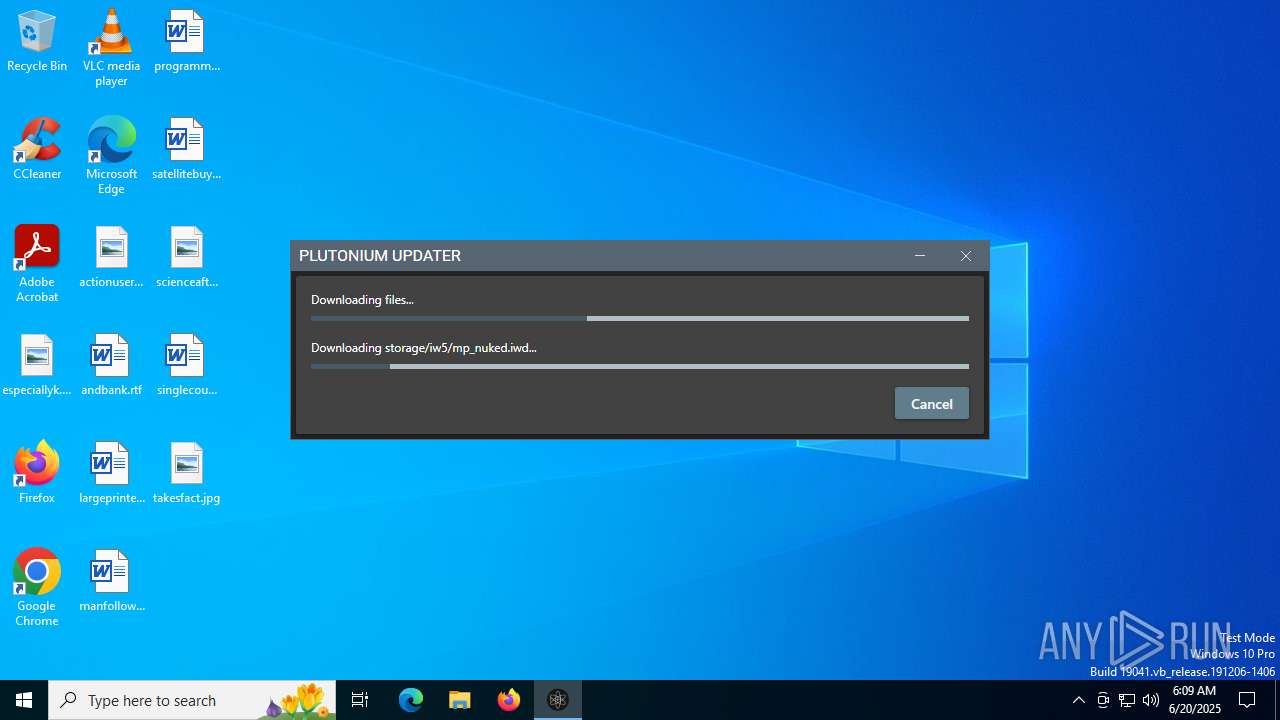
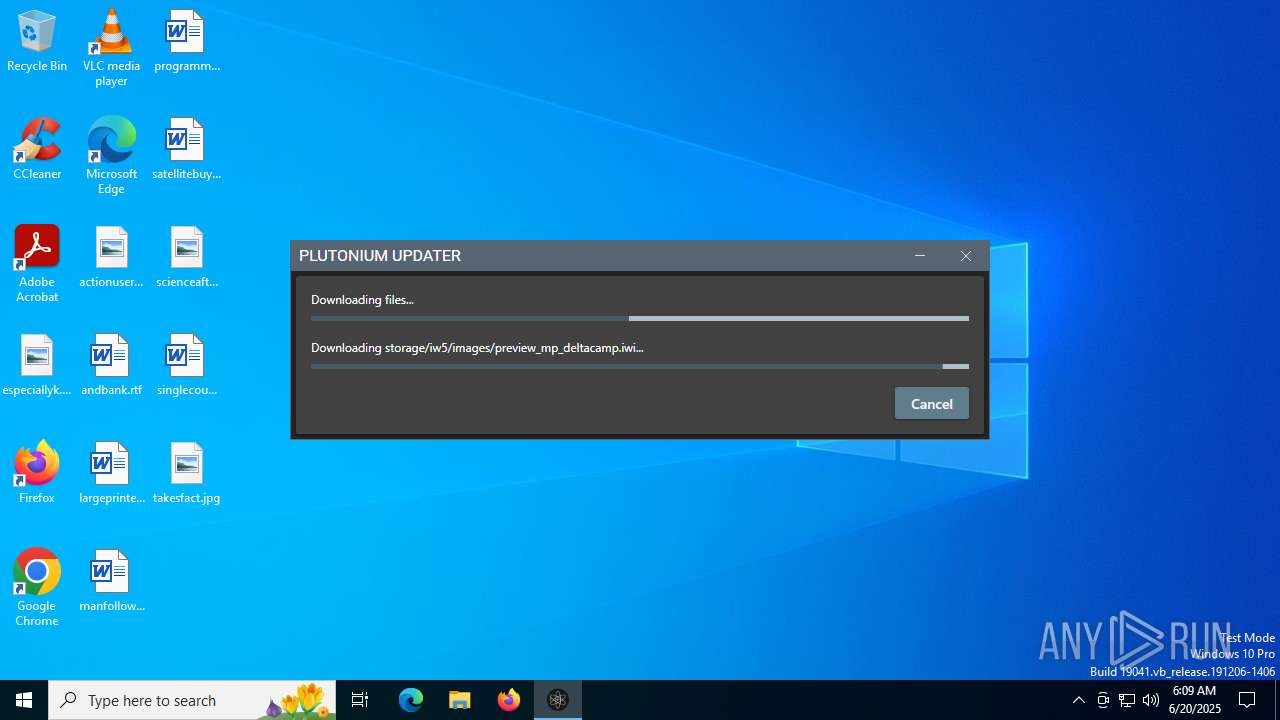
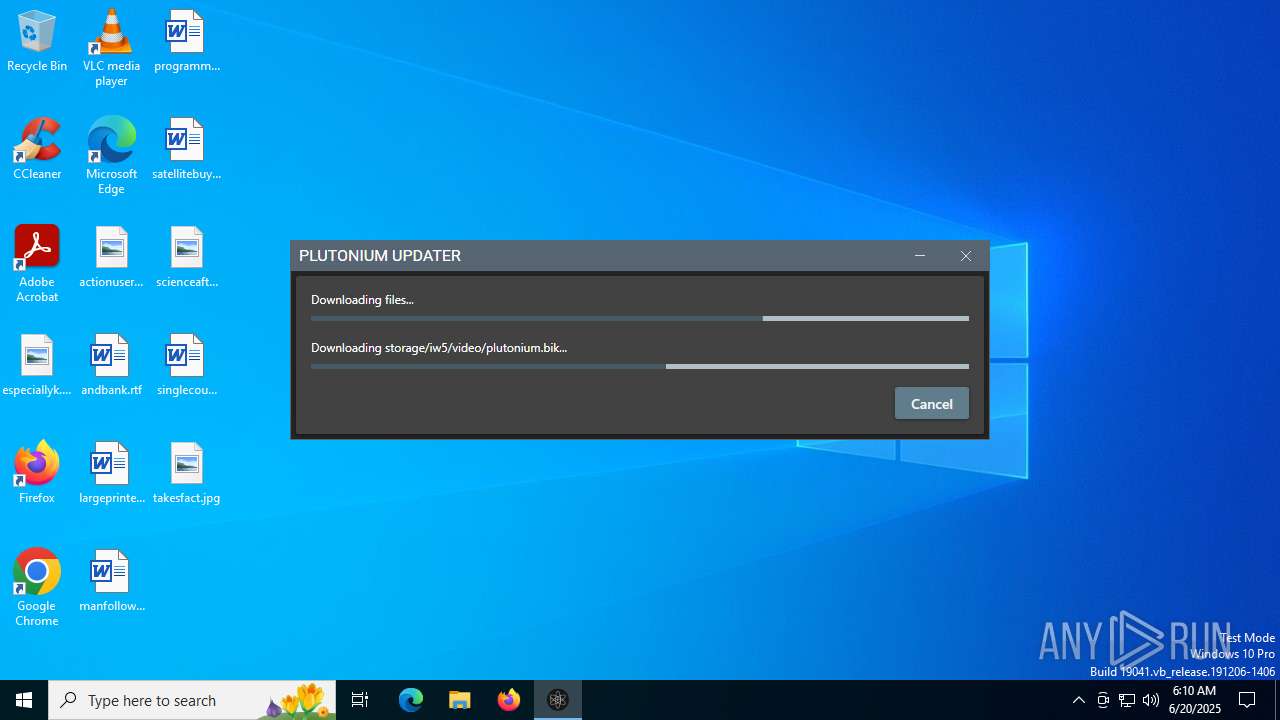
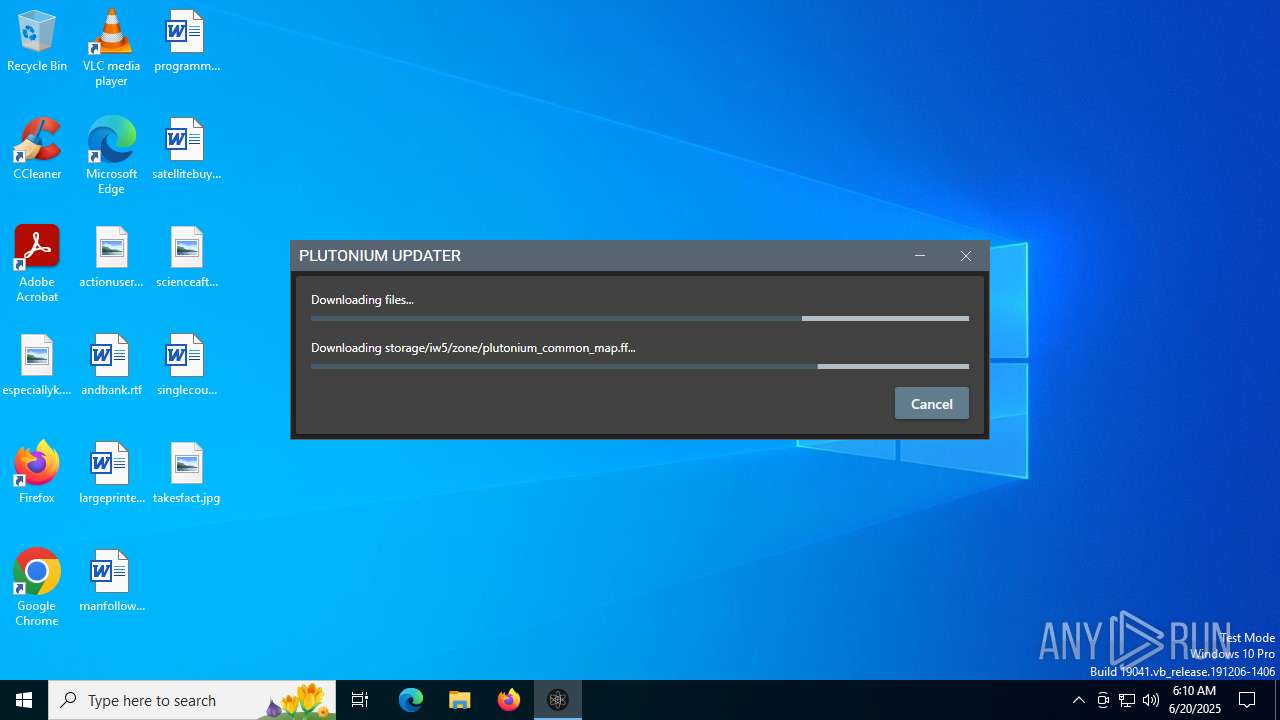
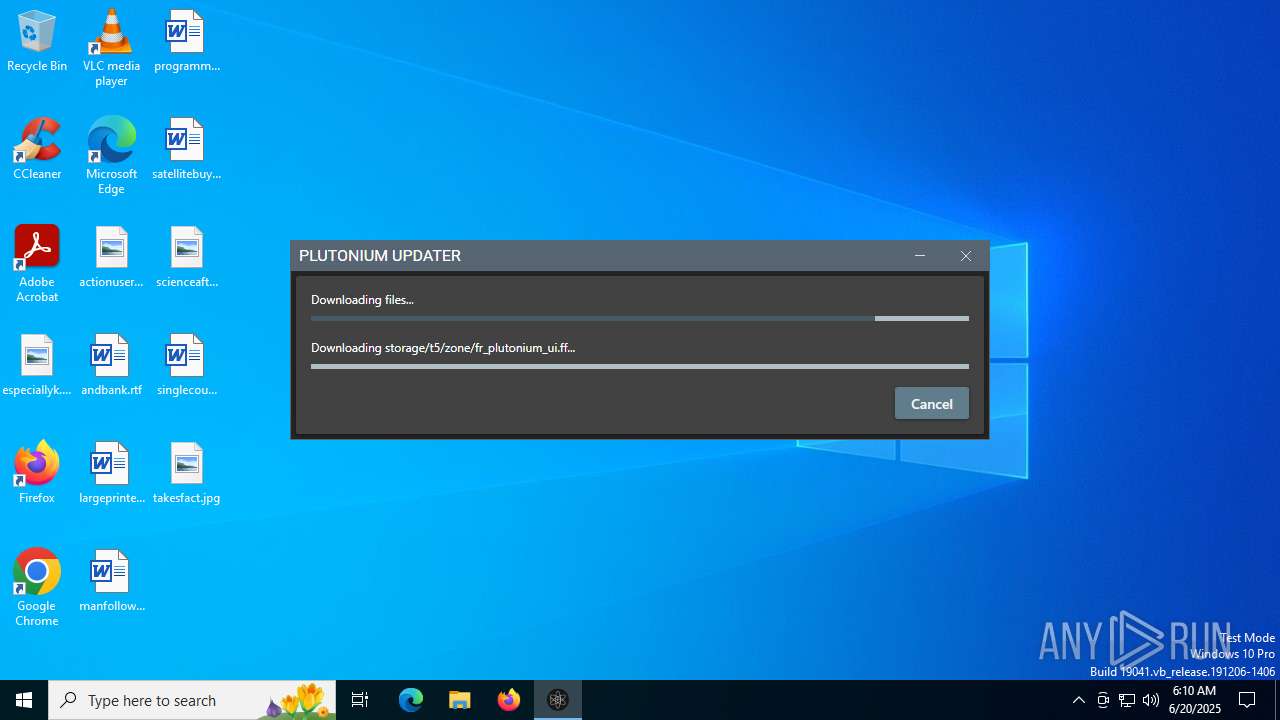
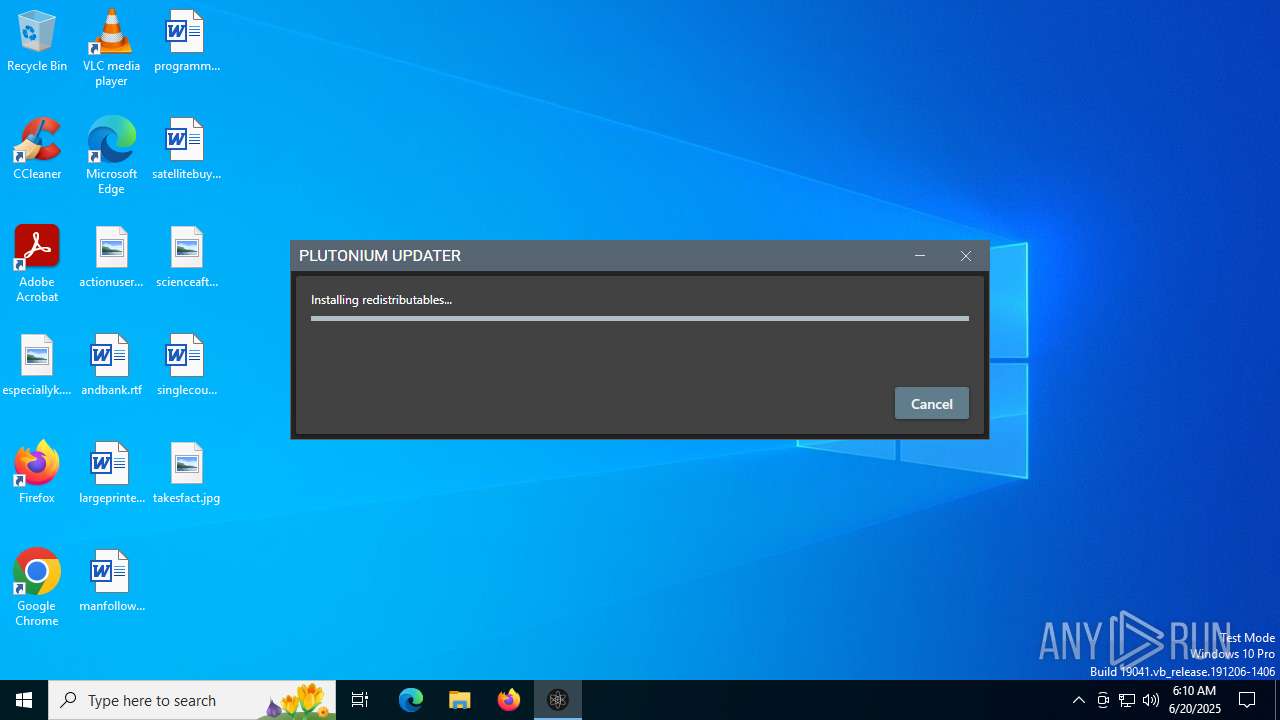
| File name: | plutonium.exe |
| Full analysis: | https://app.any.run/tasks/a150e6e3-8b75-4d30-bf7b-c78b4d58e7c9 |
| Verdict: | Malicious activity |
| Analysis date: | June 20, 2025, 06:09:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 72CB7C6D98E9E47274733825C9176679 |
| SHA1: | 8681469349254C5203A7F9A189833D22A14F5CD9 |
| SHA256: | 85D1D1CA4D5881D9B98928C2006FB0EEC9655E2705FE74088E6F974A19703F0F |
| SSDEEP: | 98304:zUaMwIBAoUcmmxVA5/xDnLx0yu+5TeRXExXYAxZ:Ia+AobhATd0yH0RXUo2Z |
MALICIOUS
Executing a file with an untrusted certificate
- plutonium.exe (PID: 6508)
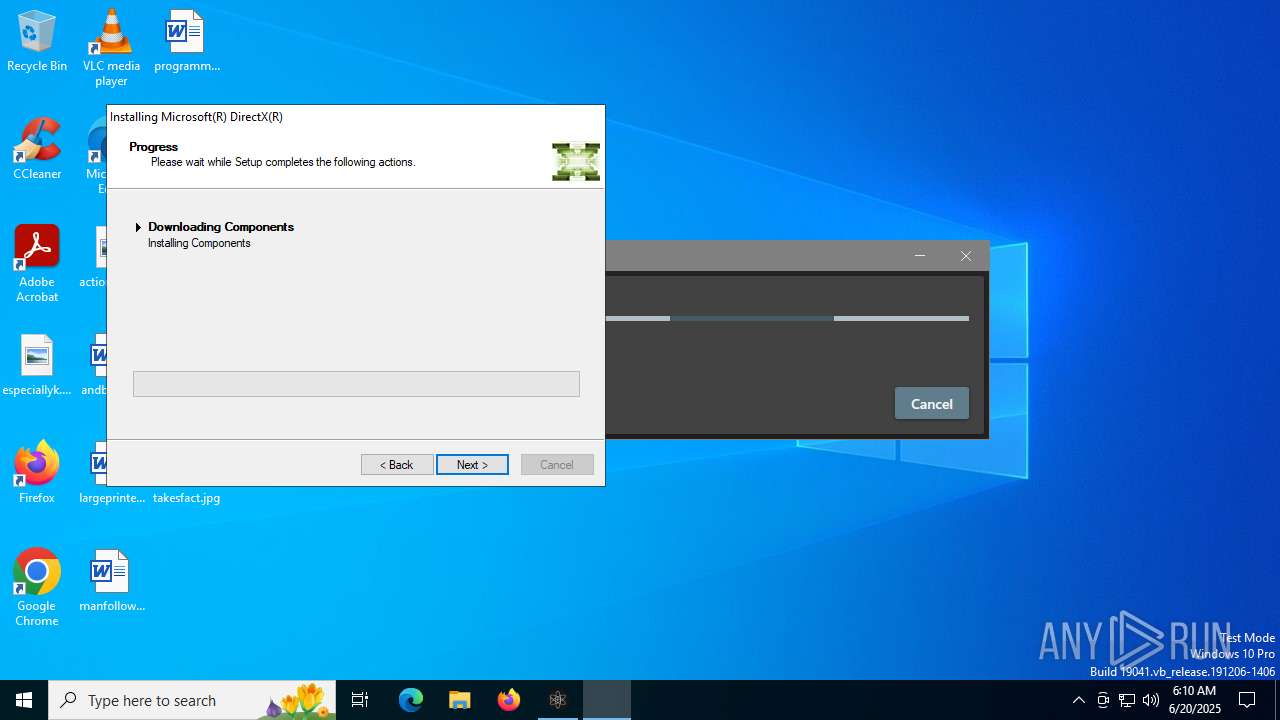
- Setup.exe (PID: 3844)
MENORAH has been detected (YARA)
- plutonium.exe (PID: 6508)
Changes the autorun value in the registry
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 4120)
SUSPICIOUS
Reads security settings of Internet Explorer
- plutonium.exe (PID: 6508)
- Setup.exe (PID: 3844)
- dxwsetup.exe (PID: 3944)
Executable content was dropped or overwritten
- plutonium.exe (PID: 6508)
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 4120)
- dxwsetup.exe (PID: 3944)
Process drops legitimate windows executable
- plutonium.exe (PID: 6508)
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 4120)
- dxwsetup.exe (PID: 3944)
There is functionality for taking screenshot (YARA)
- plutonium.exe (PID: 6508)
Reads the date of Windows installation
- plutonium.exe (PID: 6508)
Starts a Microsoft application from unusual location
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 4312)
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 4120)
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 6172)
- dxwsetup.exe (PID: 3944)
The process drops C-runtime libraries
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
Creates file in the systems drive root
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1700)
INFO
Creates files in the program directory
- plutonium.exe (PID: 6508)
Disables trace logs
- plutonium.exe (PID: 6508)
Checks supported languages
- plutonium.exe (PID: 6508)
- Setup.exe (PID: 3844)
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
- dxwsetup.exe (PID: 3944)
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 4120)
Reads the computer name
- plutonium.exe (PID: 6508)
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- Setup.exe (PID: 3844)
- msiexec.exe (PID: 1700)
- dxwsetup.exe (PID: 3944)
Reads the machine GUID from the registry
- plutonium.exe (PID: 6508)
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- Setup.exe (PID: 3844)
- msiexec.exe (PID: 1700)
- dxwsetup.exe (PID: 3944)
Checks proxy server information
- plutonium.exe (PID: 6508)
- dxwsetup.exe (PID: 3944)
Create files in a temporary directory
- plutonium.exe (PID: 6508)
- Setup.exe (PID: 3844)
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 4120)
- dxwsetup.exe (PID: 3944)
Creates files or folders in the user directory
- plutonium.exe (PID: 6508)
- msiexec.exe (PID: 1700)
- dxwsetup.exe (PID: 3944)
Reads Environment values
- plutonium.exe (PID: 6508)
The sample compiled with english language support
- plutonium.exe (PID: 6508)
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 4120)
- dxwsetup.exe (PID: 3944)
Process checks computer location settings
- plutonium.exe (PID: 6508)
Reads the software policy settings
- plutonium.exe (PID: 6508)
- msiexec.exe (PID: 1700)
- Setup.exe (PID: 3844)
- dxwsetup.exe (PID: 3944)
The sample compiled with Italian language support
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
The sample compiled with chinese language support
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
The sample compiled with japanese language support
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
The sample compiled with korean language support
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
The sample compiled with german language support
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
The sample compiled with spanish language support
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
The sample compiled with french language support
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
The sample compiled with russian language support
- a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe (PID: 5900)
- msiexec.exe (PID: 1700)
Reads CPU info
- Setup.exe (PID: 3844)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1700)
Launching a file from a Registry key
- 747bf211-a780-44d1-9e20-91782cbe2a36.exe (PID: 4120)
Creates a software uninstall entry
- msiexec.exe (PID: 1700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2097:01:09 15:42:18+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 4820480 |
| InitializedDataSize: | 34816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49adde |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.221.0 |
| ProductVersionNumber: | 1.0.221.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Plutonium.Updater.App |
| FileDescription: | Plutonium.Updater.App |
| FileVersion: | 1.0.221.0 |
| InternalName: | Plutonium.Updater.App.exe |
| LegalCopyright: | |
| OriginalFileName: | Plutonium.Updater.App.exe |
| ProductName: | Plutonium.Updater.App |
| ProductVersion: | 1.0.221-25b01eea |
| AssemblyVersion: | 1.0.221.0 |
Total processes
147
Monitored processes
10
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3844 | c:\8deb5d95a3c93e81f80d503bc0be\Setup.exe /quiet /install /norestart | C:\8deb5d95a3c93e81f80d503bc0be\Setup.exe | a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 10.0.40219.325 built by: SP1LDR Modules
| |||||||||||||||
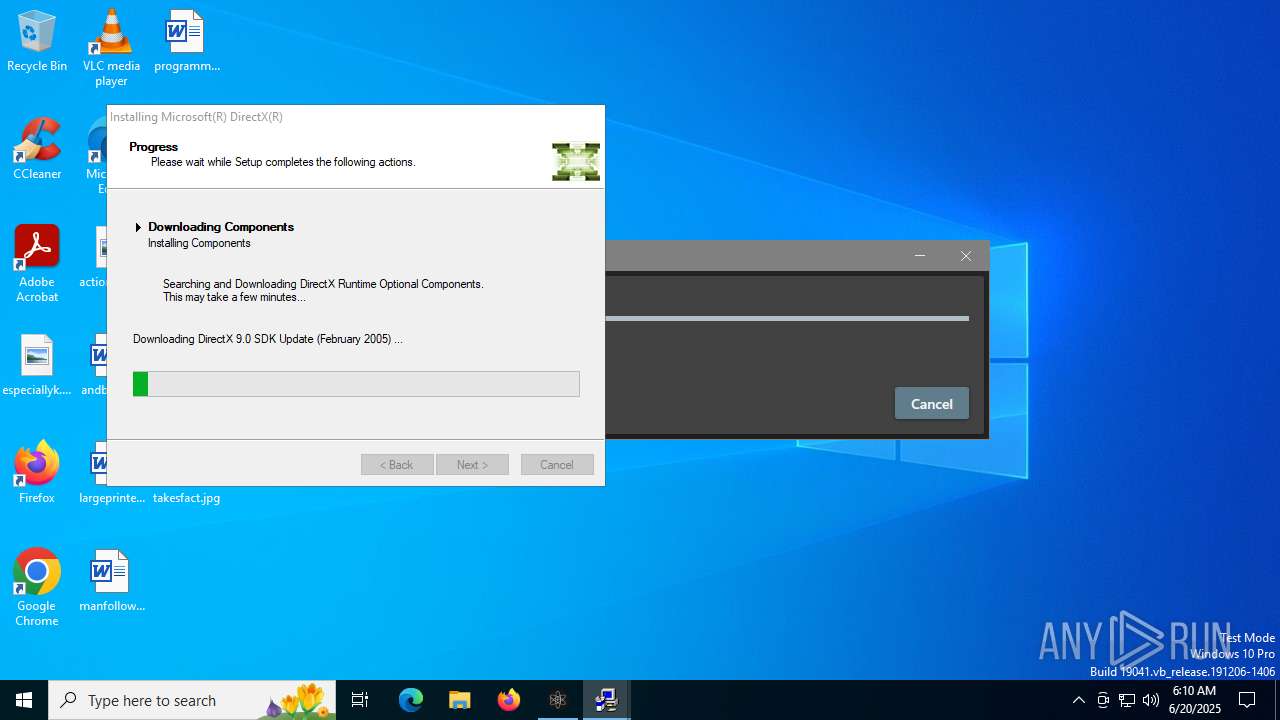
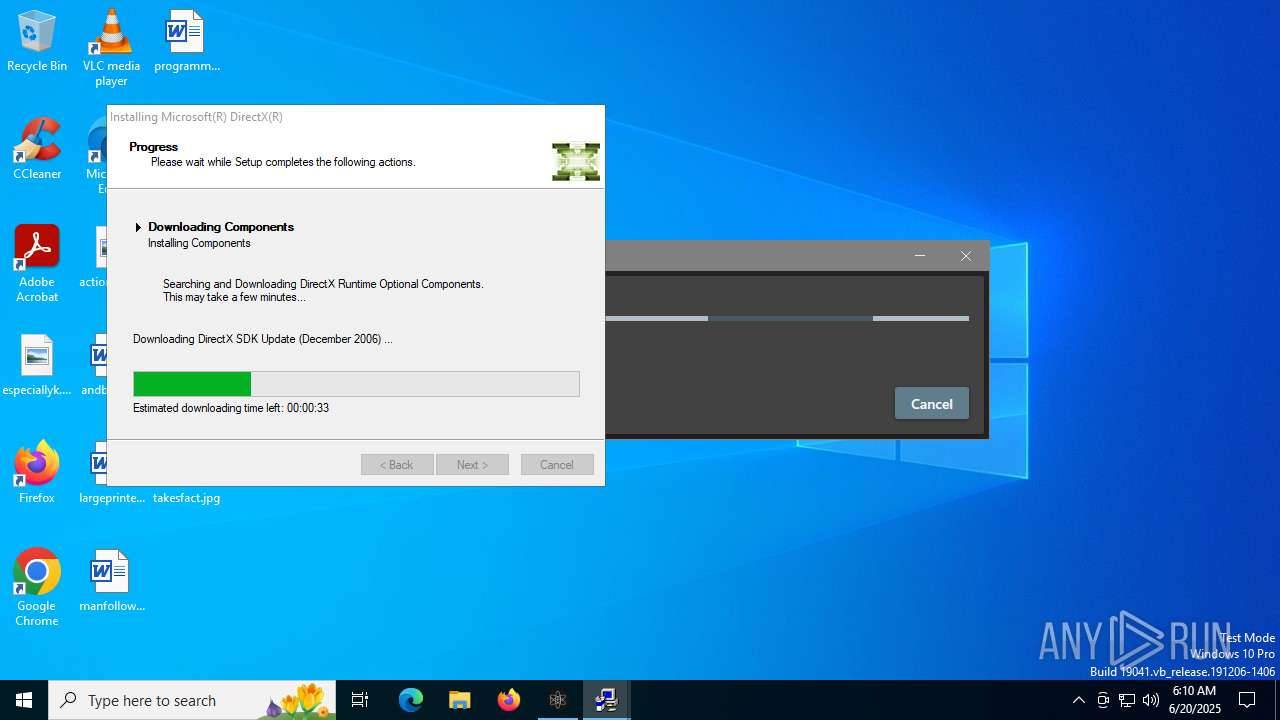
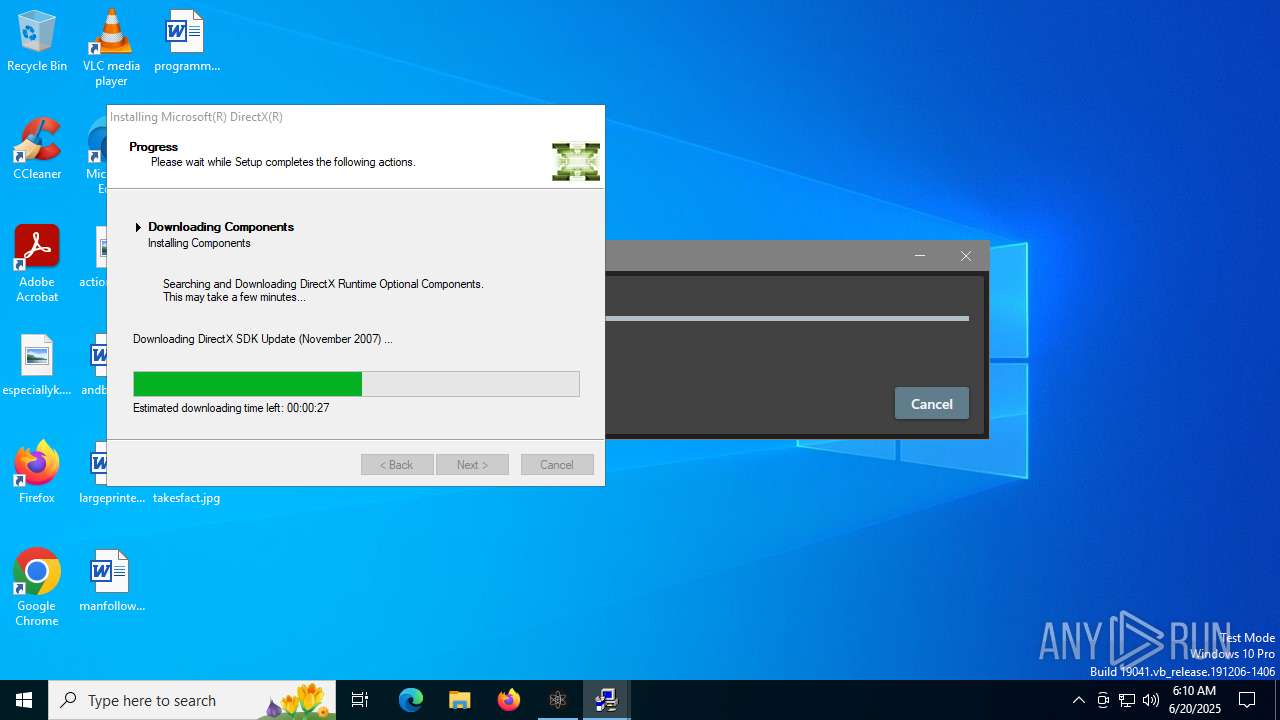
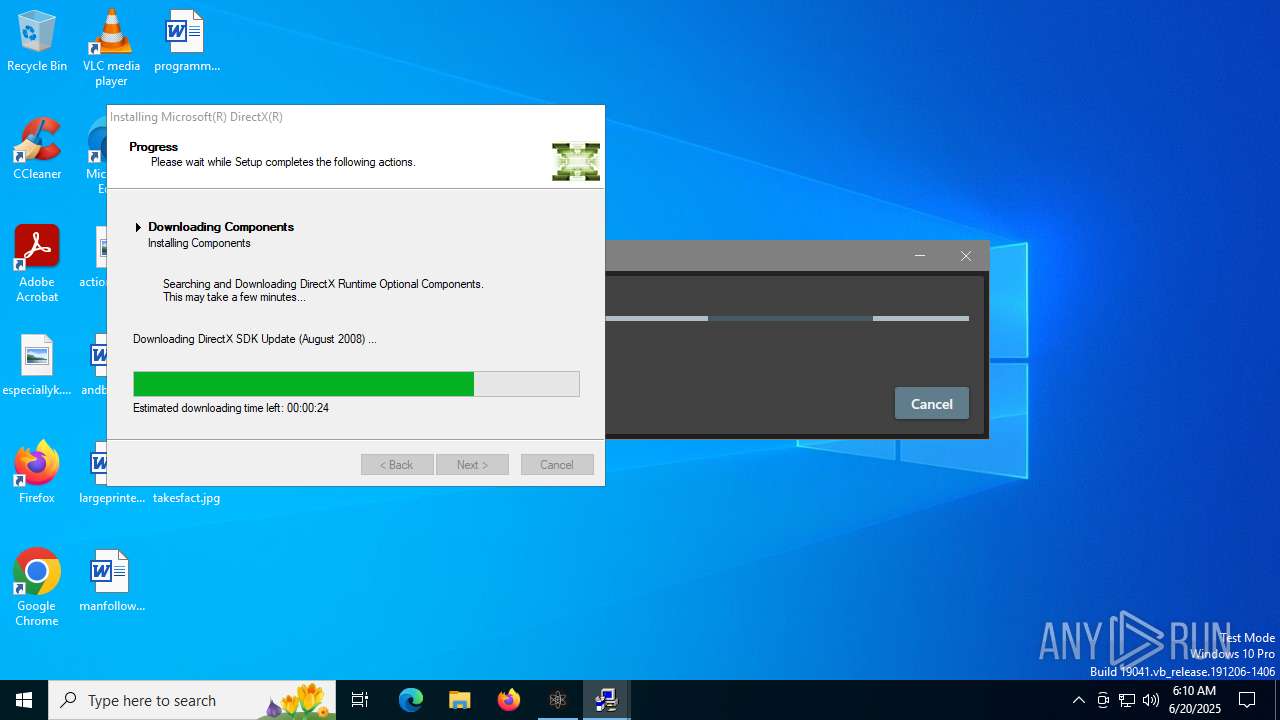
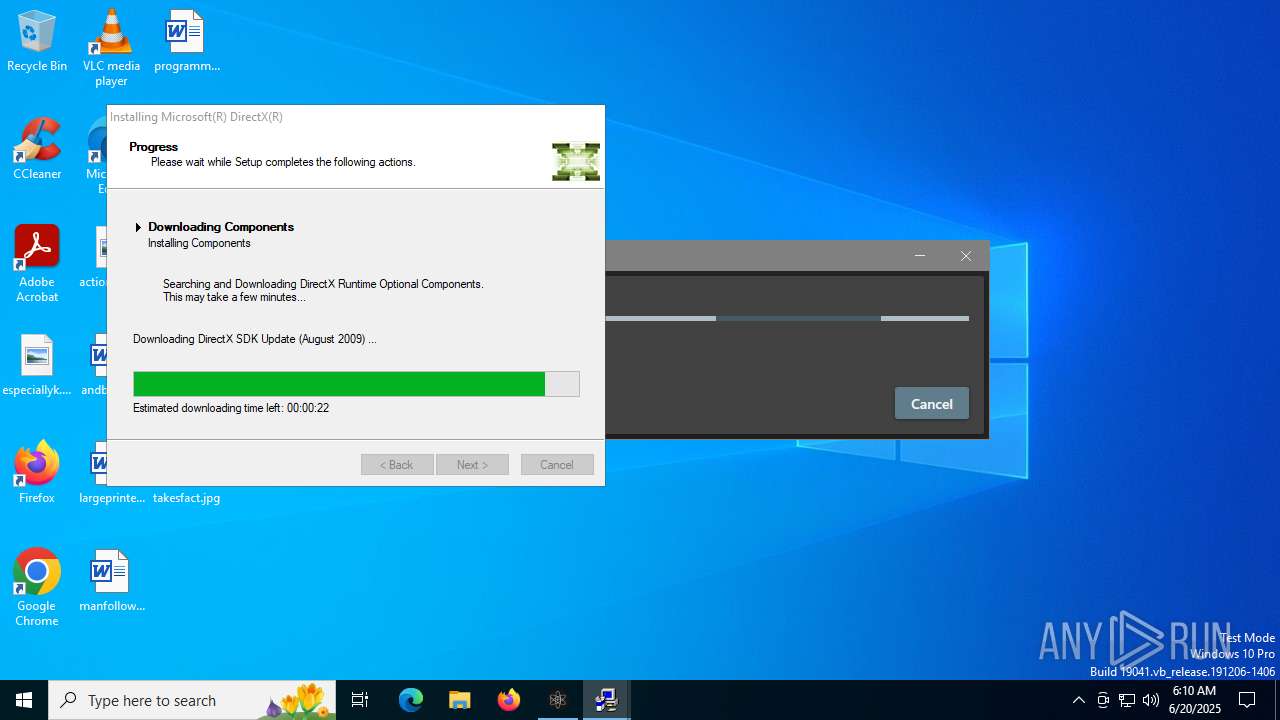
| 3944 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe /windowsupdate | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | 747bf211-a780-44d1-9e20-91782cbe2a36.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX Setup Version: 4.9.0.0904 Modules
| |||||||||||||||
| 4120 | "C:\Users\admin\AppData\Local\Temp\747bf211-a780-44d1-9e20-91782cbe2a36.exe" /Q | C:\Users\admin\AppData\Local\Temp\747bf211-a780-44d1-9e20-91782cbe2a36.exe | plutonium.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX 9.0 Web setup Version: 9.29.1974.0 Modules
| |||||||||||||||
| 4312 | "C:\Users\admin\AppData\Local\Temp\a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe" /quiet /install /norestart | C:\Users\admin\AppData\Local\Temp\a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe | — | plutonium.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2010 x86 Redistributable Setup Exit code: 3221226540 Version: 10.0.40219.325 Modules
| |||||||||||||||
| 5900 | "C:\Users\admin\AppData\Local\Temp\a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe" /quiet /install /norestart | C:\Users\admin\AppData\Local\Temp\a3ee200c-eef0-49ba-84a0-da7cf29134e4.exe | plutonium.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2010 x86 Redistributable Setup Exit code: 0 Version: 10.0.40219.325 Modules
| |||||||||||||||
| 6172 | "C:\Users\admin\AppData\Local\Temp\747bf211-a780-44d1-9e20-91782cbe2a36.exe" /Q | C:\Users\admin\AppData\Local\Temp\747bf211-a780-44d1-9e20-91782cbe2a36.exe | — | plutonium.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DirectX 9.0 Web setup Exit code: 3221226540 Version: 9.29.1974.0 Modules
| |||||||||||||||
| 6508 | "C:\Users\admin\AppData\Local\Temp\plutonium.exe" | C:\Users\admin\AppData\Local\Temp\plutonium.exe | explorer.exe | ||||||||||||
User: admin Company: Plutonium.Updater.App Integrity Level: MEDIUM Description: Plutonium.Updater.App Version: 1.0.221.0 Modules
| |||||||||||||||
Total events
14 430
Read events
13 834
Write events
573
Delete events
23
Modification events
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6508) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
85
Suspicious files
263
Text files
146
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\UltralightCore.dll | executable | |
MD5:CD3768E013636A12E6CE7937A7F69365 | SHA256:9ED2701BA7C3349ECBBCF276C280A09262B4DA72BE9FDCDDD81A8BAC9C9B3D69 | |||
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\AppCore.dll | executable | |
MD5:80C3806A12959987AC012E28F63AD150 | SHA256:B5338B858E5C65F9C36BBC817673BA5E1A05EED8F4DCF007B6BC4FF6140FC8F8 | |||
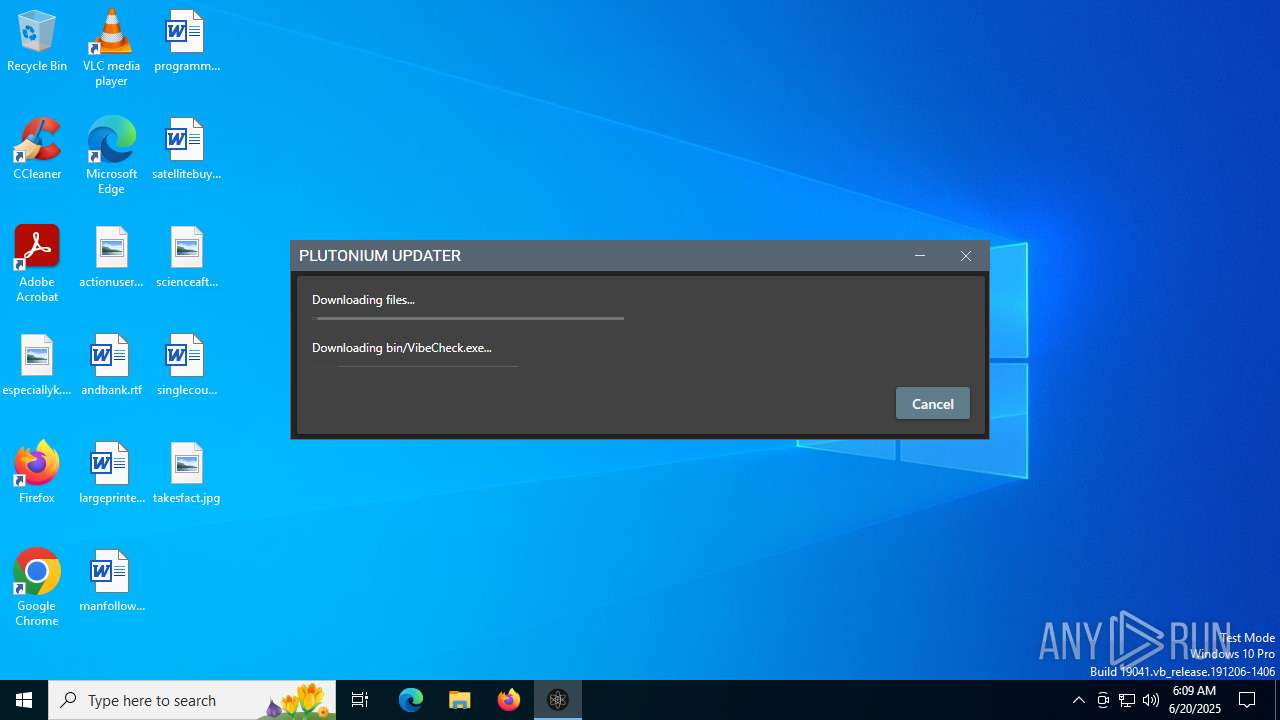
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\VibeCheck.exe | executable | |
MD5:BE1EE42858B55352E0FB154D76F31562 | SHA256:4B053F45887ED35E584B3DDC4C44BAA1533372161B96DEAAA2C3C1EA6FCE7F2B | |||
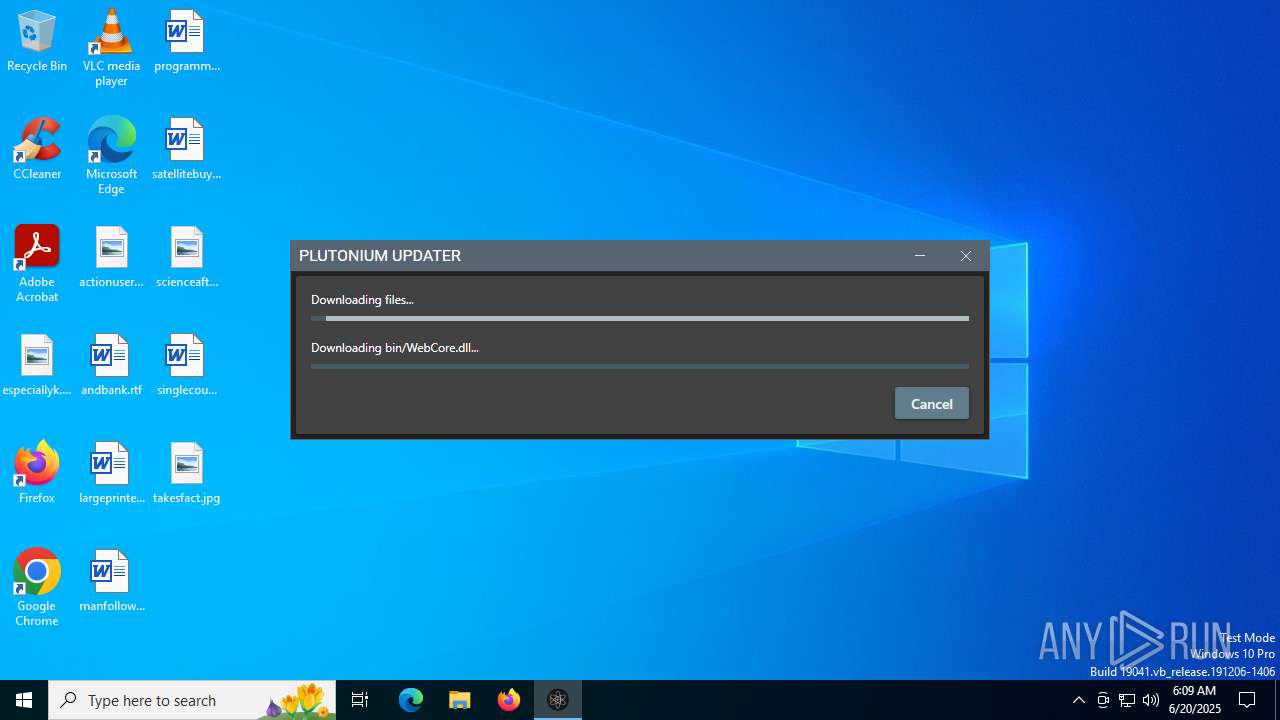
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\WebCore.dll | executable | |
MD5:90B16ABE7F82DCAE822174B4503F4E1B | SHA256:B4D361BF13F98C96C21C3DEC94D14914FF80C3515A48CD3DF974378CD6052082 | |||
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\discord_game_sdk.dll | executable | |
MD5:955AF9BE4A97316D73AFAE1E7365E97E | SHA256:D8E7D9FEB3DE8482B186AE44FD1C9ABB41FE2B3B3D2C7CD3A4D742EBBAD30CDF | |||
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\Ultralight.dll | executable | |
MD5:6C2949787D48F3B0C0CBD4A872253F12 | SHA256:758CA54BAC8288487CFA6EA276C724FC4AD29C6D6A4294D74EA34E0726CE8661 | |||
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\plutonium-launcher-win32.exe | executable | |
MD5:2A793B85AD6DC2F72288F57740994E65 | SHA256:E8221301941656889E48C5AAC51968216550CD2AAA6FB21B38D8E128E13D9D7F | |||
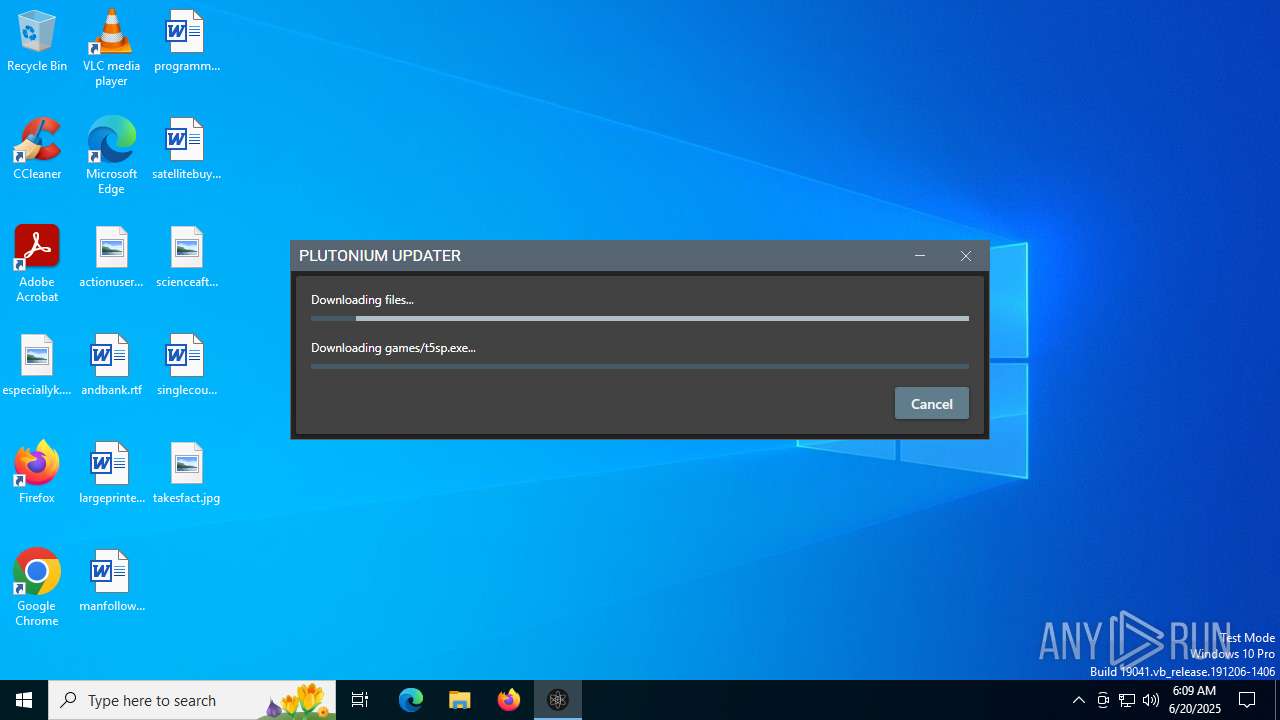
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\games\iw5mp.exe | executable | |
MD5:607FB4AF50010C99157FE3AF8DAAA2B0 | SHA256:DB3E87DCEE15A172D393A32CD79159FD07BFEF8B318A1E9BF3CF5FC98734BDE2 | |||
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\plutonium-bootstrapper-win32.exe | executable | |
MD5:D34B1855FCD10A83F3043A487420291A | SHA256:1FCBAEB0873BA5B166F57ABF398062A0B5E979B4C717BA71EDB435406FEB2DF6 | |||
| 6508 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\games\t6zm.exe | executable | |
MD5:837C6AE7DC13412FB4DD346CD7C987FF | SHA256:2AFF340F22F0C68BF46511C7BBC6167E4BB84524817F54CAE08E8F60E6F9AFC3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
34
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
188 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 420 b | whitelisted |
188 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
3944 | dxwsetup.exe | GET | 302 | 2.18.160.223:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/dxupdate.cab | DE | — | — | whitelisted |
1700 | msiexec.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/CSPCA.crl | DE | binary | 506 b | whitelisted |
3944 | dxwsetup.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | DE | binary | 471 b | whitelisted |
3944 | dxwsetup.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
3944 | dxwsetup.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | NL | binary | 1.05 Kb | whitelisted |
3944 | dxwsetup.exe | GET | 302 | 2.18.160.223:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Apr2005_d3dx9_25_x86.cab | DE | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3388 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6508 | plutonium.exe | 104.26.15.172:443 | cdn.plutonium.pw | CLOUDFLARENET | US | suspicious |
6508 | plutonium.exe | 104.21.96.1:443 | cdn.plutoniummod.com | CLOUDFLARENET | — | unknown |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4476 | svchost.exe | 20.190.160.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4476 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
cdn.plutonium.pw |
| unknown |
cdn.plutoniummod.com |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|