| File name: | plutonium.exe |
| Full analysis: | https://app.any.run/tasks/7a7dfe68-d91e-4dbf-b291-ccf72b322bf9 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2025, 11:05:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 72CB7C6D98E9E47274733825C9176679 |
| SHA1: | 8681469349254C5203A7F9A189833D22A14F5CD9 |
| SHA256: | 85D1D1CA4D5881D9B98928C2006FB0EEC9655E2705FE74088E6F974A19703F0F |
| SSDEEP: | 98304:zUaMwIBAoUcmmxVA5/xDnLx0yu+5TeRXExXYAxZ:Ia+AobhATd0yH0RXUo2Z |
MALICIOUS
MENORAH has been detected (YARA)
- plutonium.exe (PID: 1040)
Changes the autorun value in the registry
- 178bffd3-6a59-4141-93c2-1c834413002d.exe (PID: 2616)
Executing a file with an untrusted certificate
- plutonium-launcher-win32.exe (PID: 3432)
SUSPICIOUS
Executable content was dropped or overwritten
- plutonium.exe (PID: 1040)
- 178bffd3-6a59-4141-93c2-1c834413002d.exe (PID: 2616)
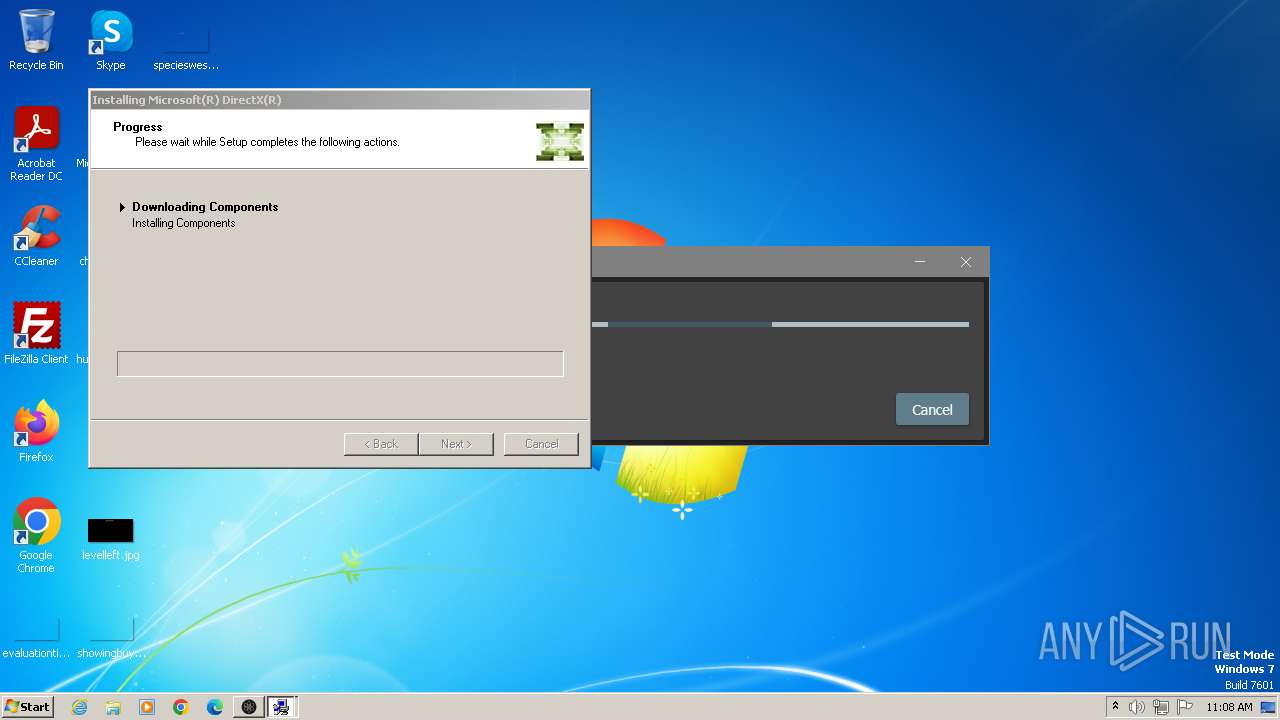
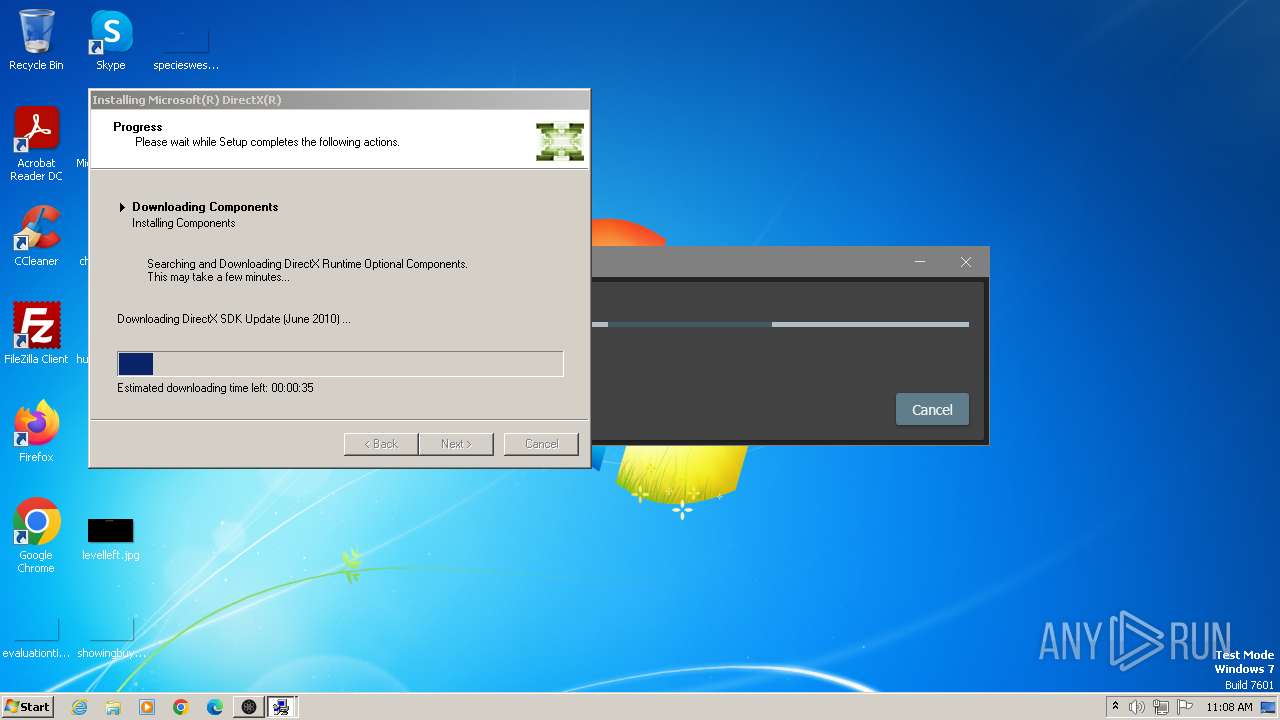
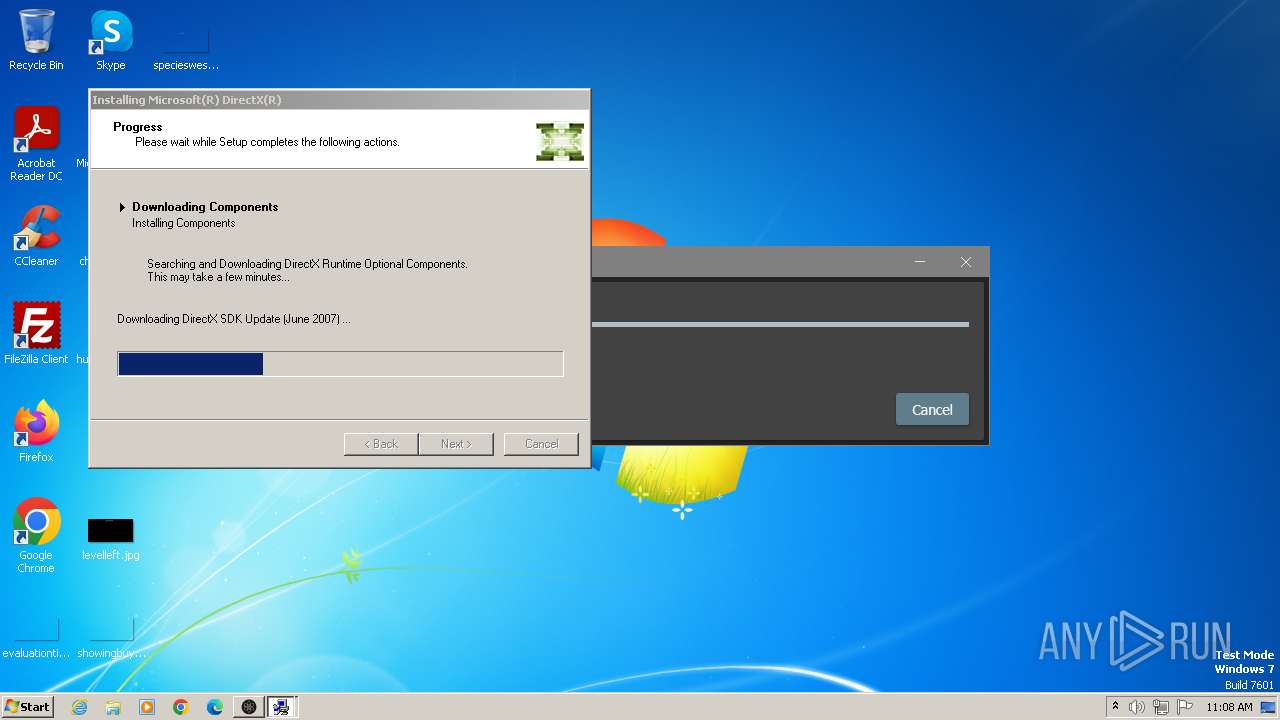
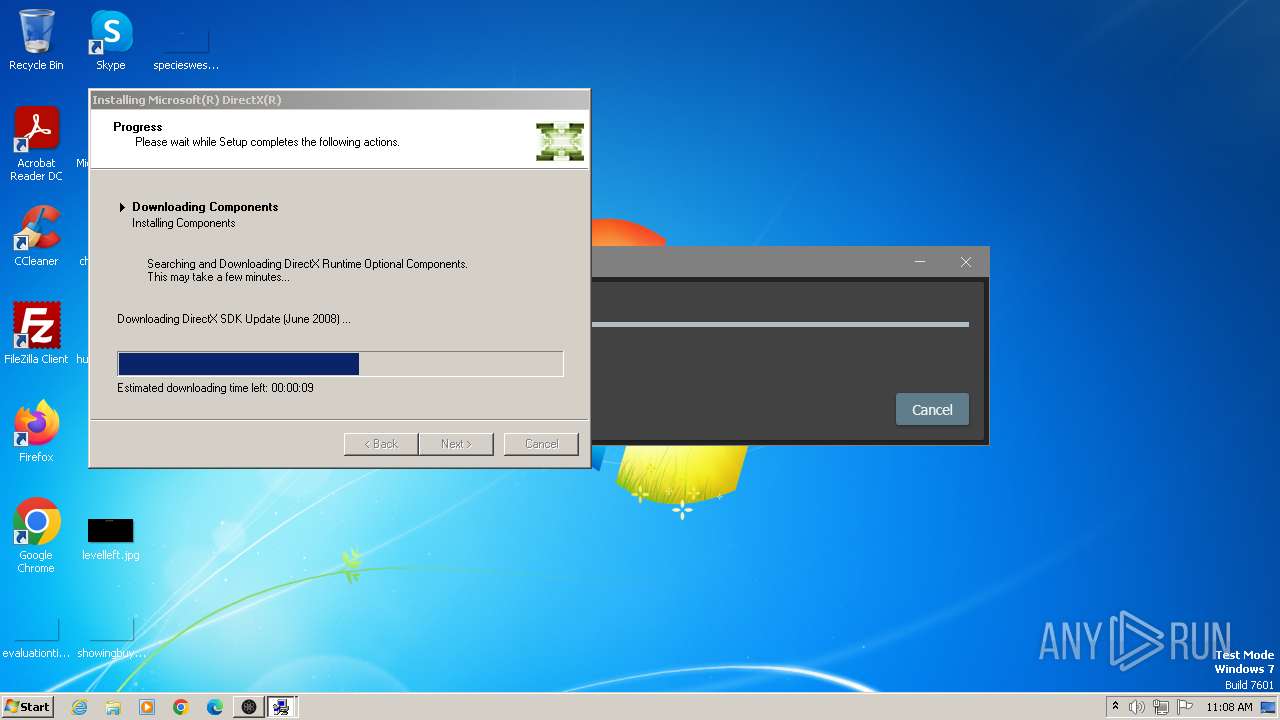
- dxwsetup.exe (PID: 3008)
Reads settings of System Certificates
- plutonium.exe (PID: 1040)
- dxwsetup.exe (PID: 3008)
There is functionality for taking screenshot (YARA)
- plutonium.exe (PID: 1040)
Reads the Internet Settings
- plutonium.exe (PID: 1040)
- dxwsetup.exe (PID: 3008)
Process drops legitimate windows executable
- plutonium.exe (PID: 1040)
- 178bffd3-6a59-4141-93c2-1c834413002d.exe (PID: 2616)
- dxwsetup.exe (PID: 3008)
Reads security settings of Internet Explorer
- plutonium.exe (PID: 1040)
- dxwsetup.exe (PID: 3008)
Starts a Microsoft application from unusual location
- 178bffd3-6a59-4141-93c2-1c834413002d.exe (PID: 2912)
- 178bffd3-6a59-4141-93c2-1c834413002d.exe (PID: 2616)
- dxwsetup.exe (PID: 3008)
Executes as Windows Service
- VSSVC.exe (PID: 3392)
Searches for installed software
- dllhost.exe (PID: 872)
- dxwsetup.exe (PID: 3008)
Checks Windows Trust Settings
- dxwsetup.exe (PID: 3008)
Creates/Modifies COM task schedule object
- dxwsetup.exe (PID: 3008)
INFO
Checks supported languages
- plutonium.exe (PID: 1040)
- 178bffd3-6a59-4141-93c2-1c834413002d.exe (PID: 2616)
- dxwsetup.exe (PID: 3008)
- wmpnscfg.exe (PID: 1556)
- plutonium-launcher-win32.exe (PID: 3432)
Reads Environment values
- plutonium.exe (PID: 1040)
Creates files in the program directory
- plutonium.exe (PID: 1040)
Disables trace logs
- plutonium.exe (PID: 1040)
Reads the machine GUID from the registry
- plutonium.exe (PID: 1040)
- dxwsetup.exe (PID: 3008)
- plutonium-launcher-win32.exe (PID: 3432)
Reads the computer name
- plutonium.exe (PID: 1040)
- dxwsetup.exe (PID: 3008)
- wmpnscfg.exe (PID: 1556)
- plutonium-launcher-win32.exe (PID: 3432)
Reads the software policy settings
- plutonium.exe (PID: 1040)
- dxwsetup.exe (PID: 3008)
Creates files or folders in the user directory
- plutonium.exe (PID: 1040)
- dxwsetup.exe (PID: 3008)
The sample compiled with english language support
- plutonium.exe (PID: 1040)
- 178bffd3-6a59-4141-93c2-1c834413002d.exe (PID: 2616)
- dxwsetup.exe (PID: 3008)
Drops a (possible) Coronavirus decoy
- plutonium.exe (PID: 1040)
Create files in a temporary directory
- plutonium.exe (PID: 1040)
- 178bffd3-6a59-4141-93c2-1c834413002d.exe (PID: 2616)
- dxwsetup.exe (PID: 3008)
Checks proxy server information
- dxwsetup.exe (PID: 3008)
Manual execution by a user
- wmpnscfg.exe (PID: 1556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2097:01:09 15:42:18+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 4820480 |
| InitializedDataSize: | 34816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49adde |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.221.0 |
| ProductVersionNumber: | 1.0.221.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
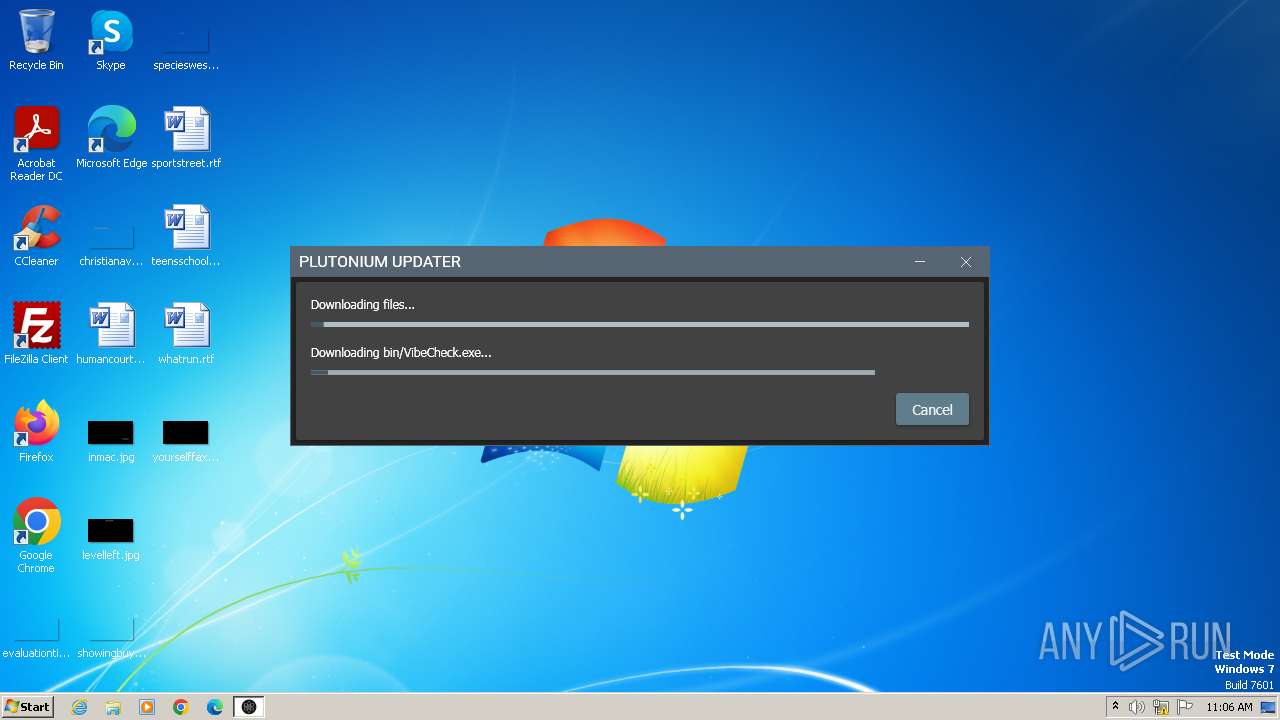
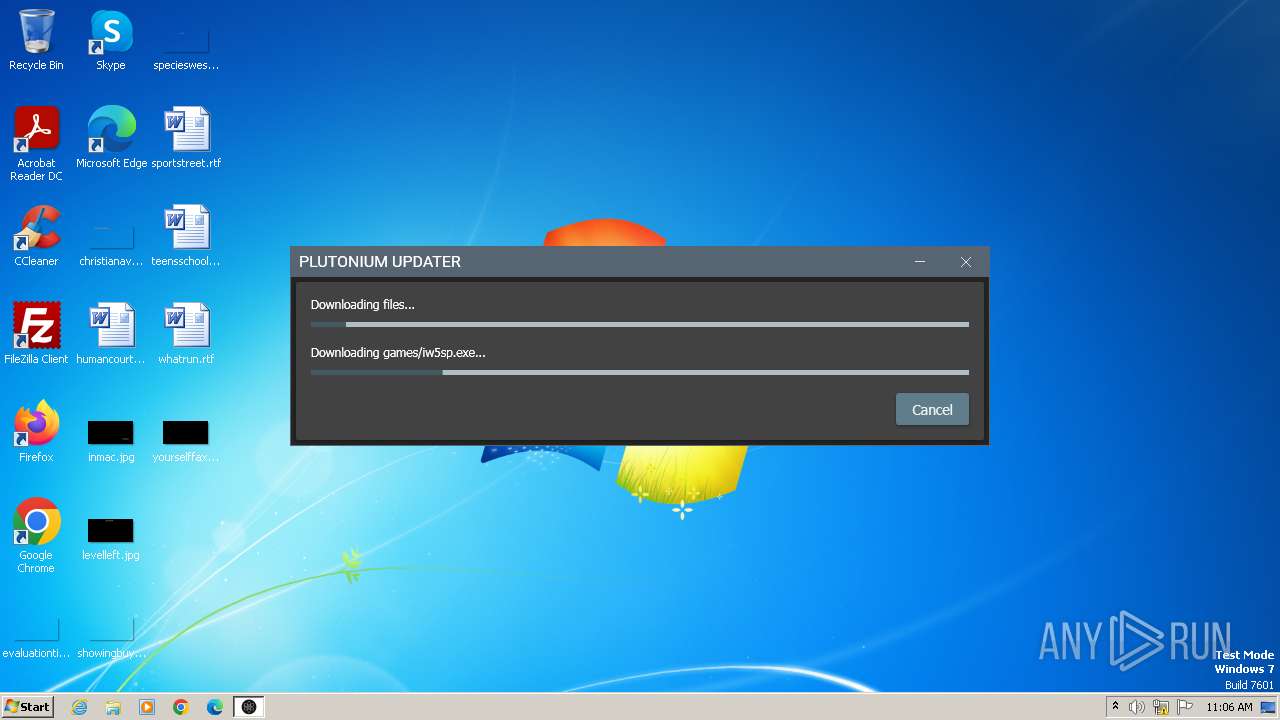
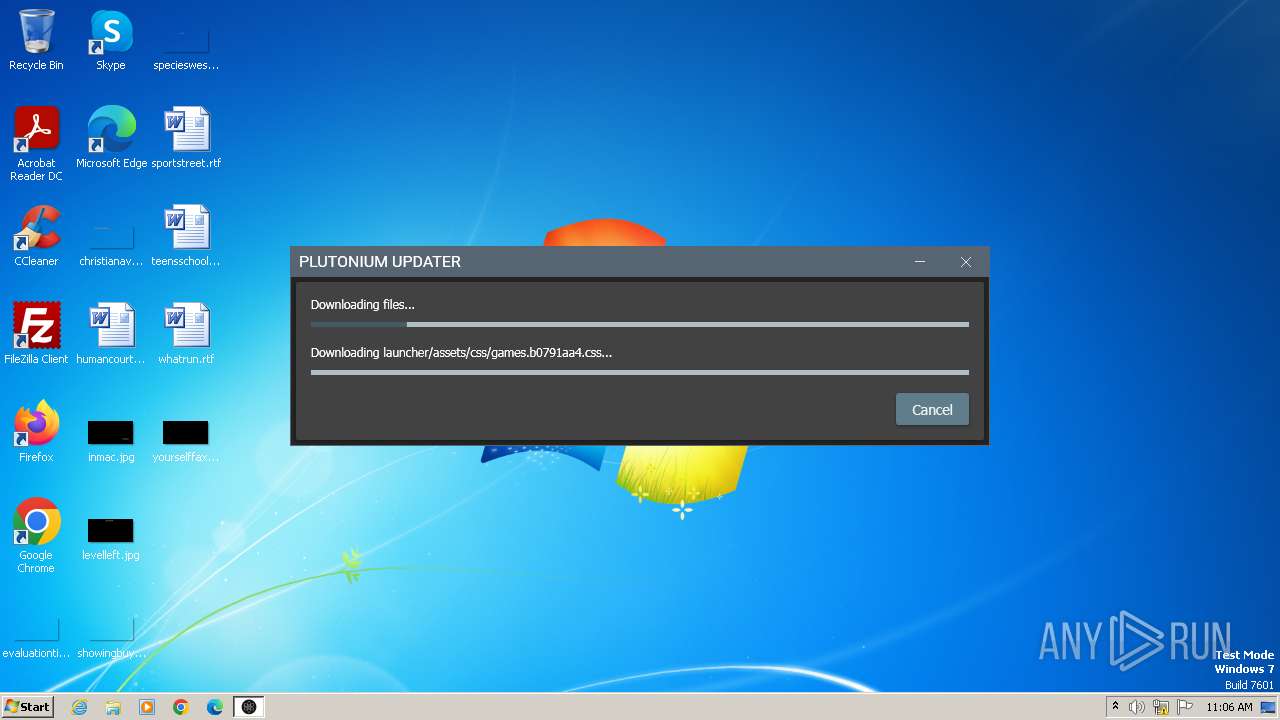
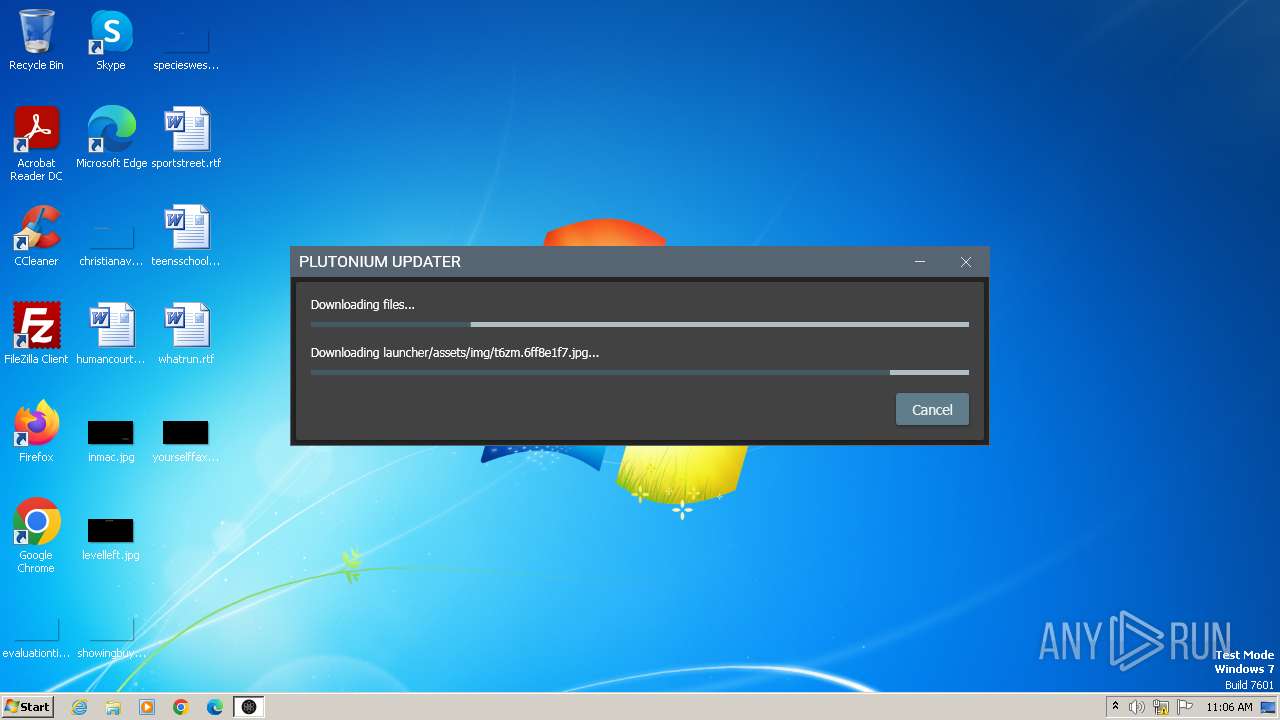
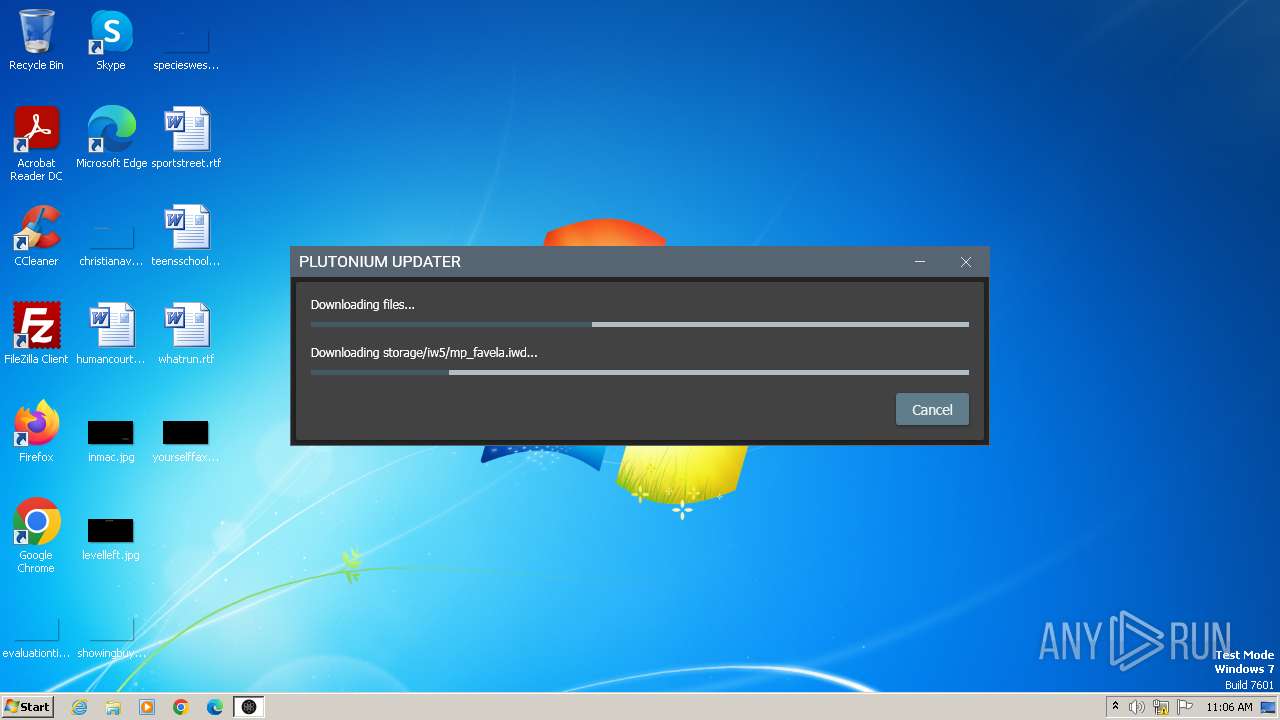
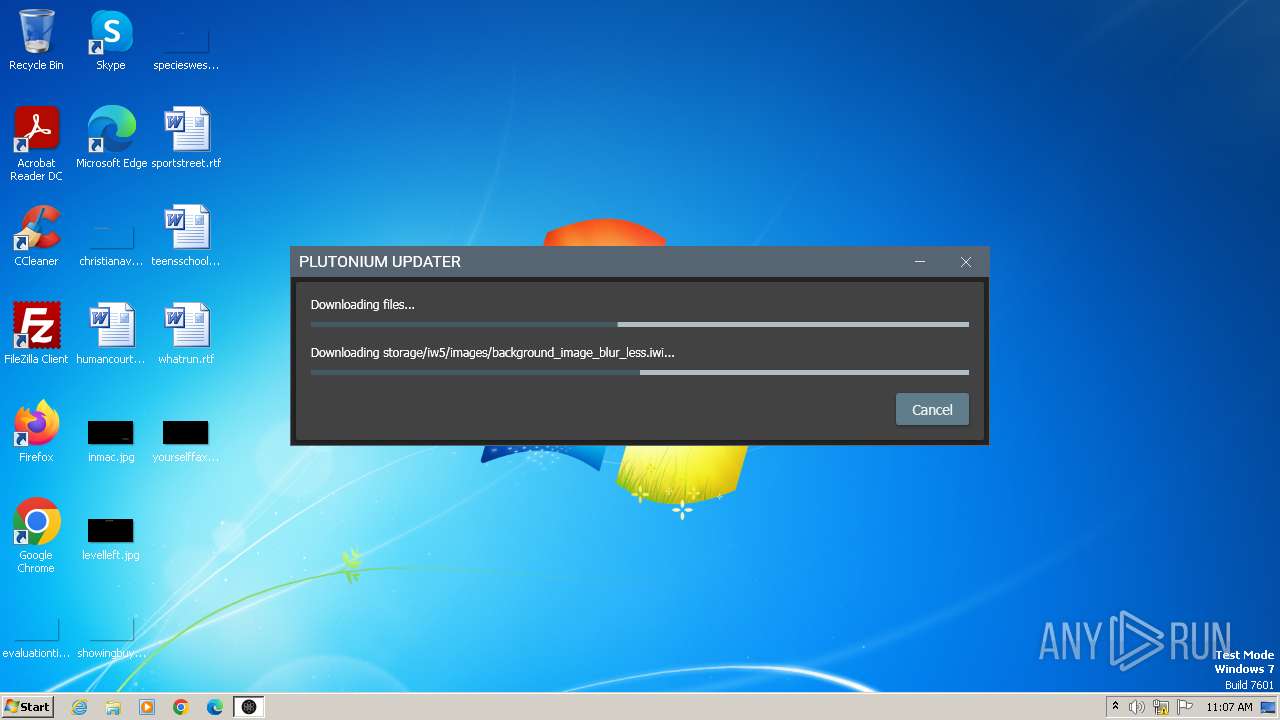
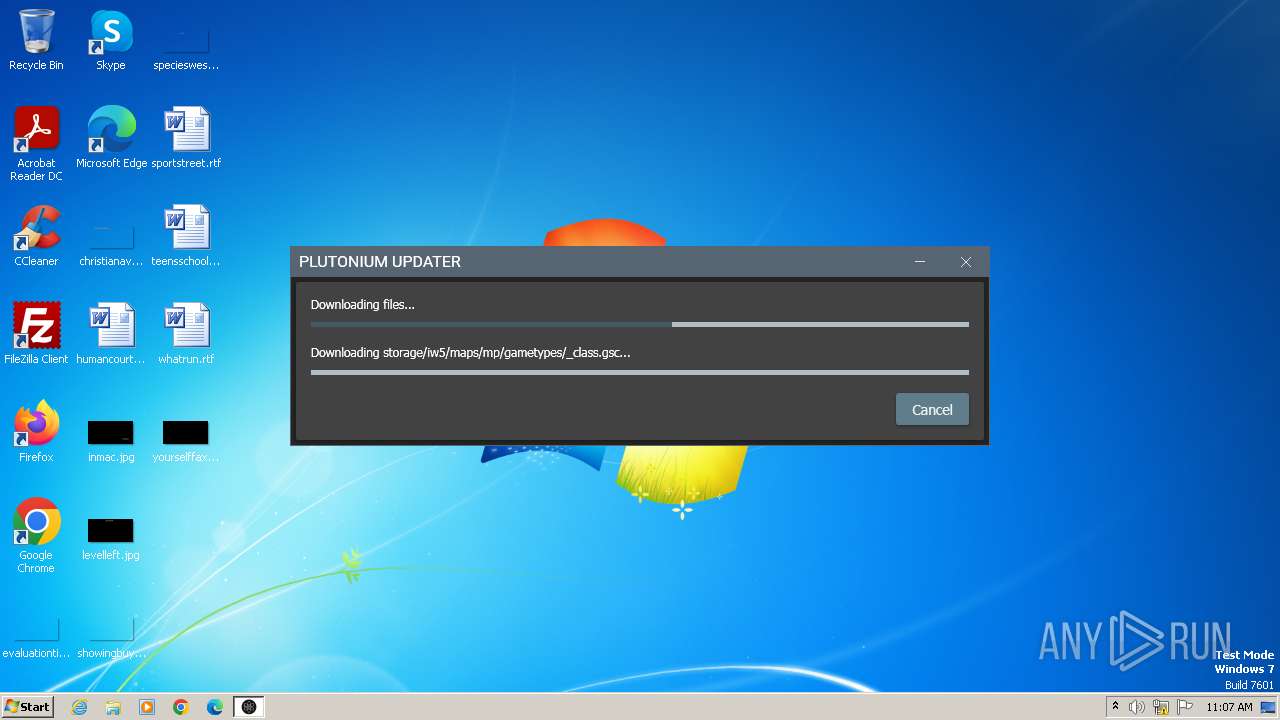
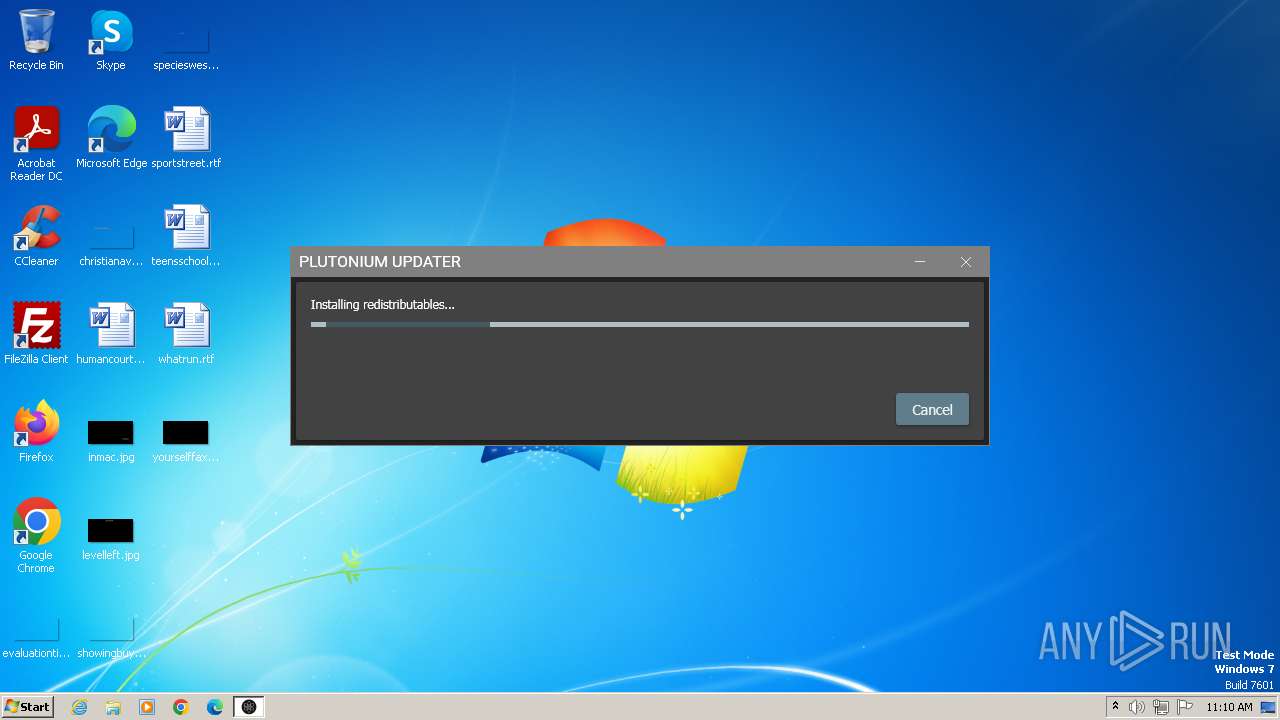
| CompanyName: | Plutonium.Updater.App |
| FileDescription: | Plutonium.Updater.App |
| FileVersion: | 1.0.221.0 |
| InternalName: | Plutonium.Updater.App.exe |
| LegalCopyright: | |
| OriginalFileName: | Plutonium.Updater.App.exe |
| ProductName: | Plutonium.Updater.App |
| ProductVersion: | 1.0.221-25b01eea |
| AssemblyVersion: | 1.0.221.0 |
Total processes
47
Monitored processes
9
Malicious processes
4
Suspicious processes
1
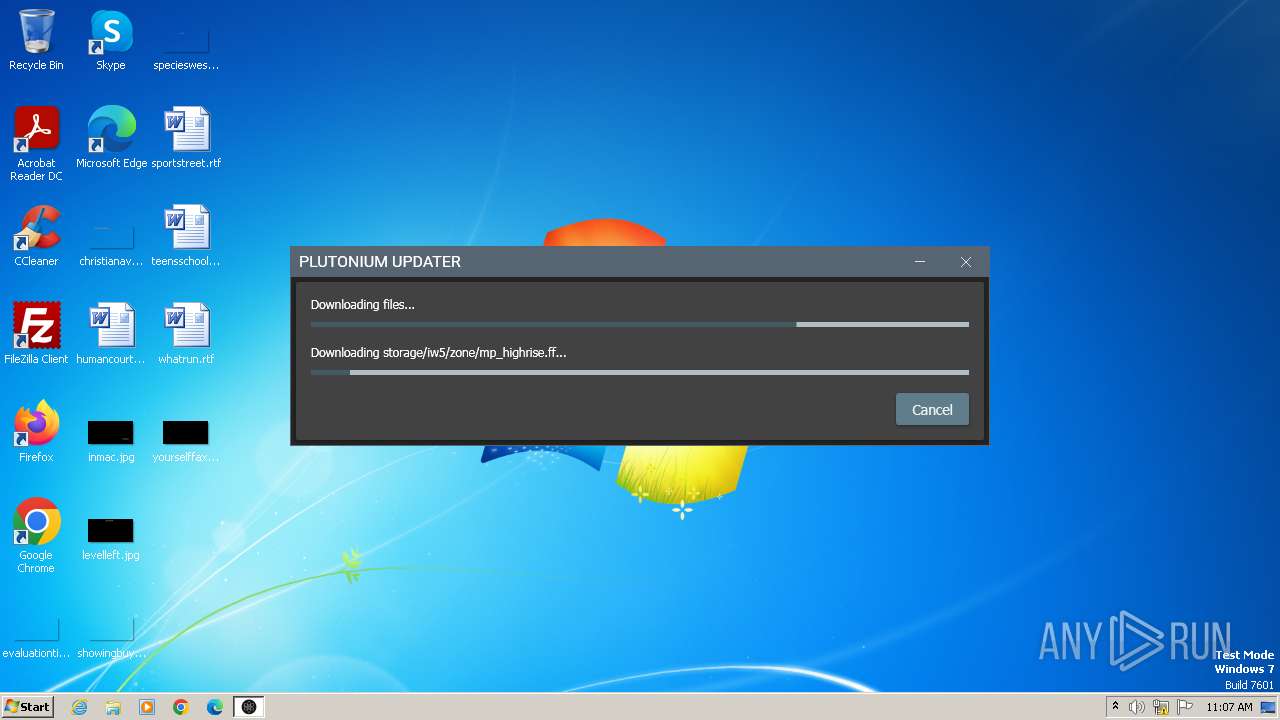
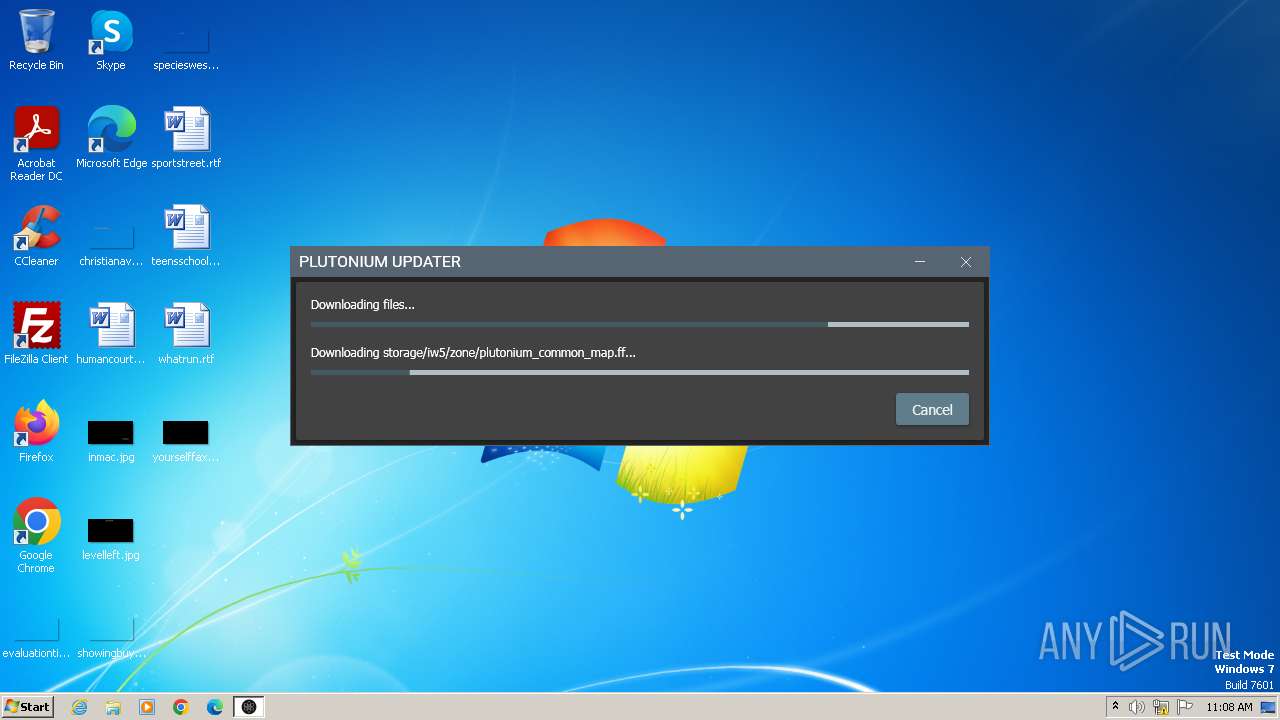
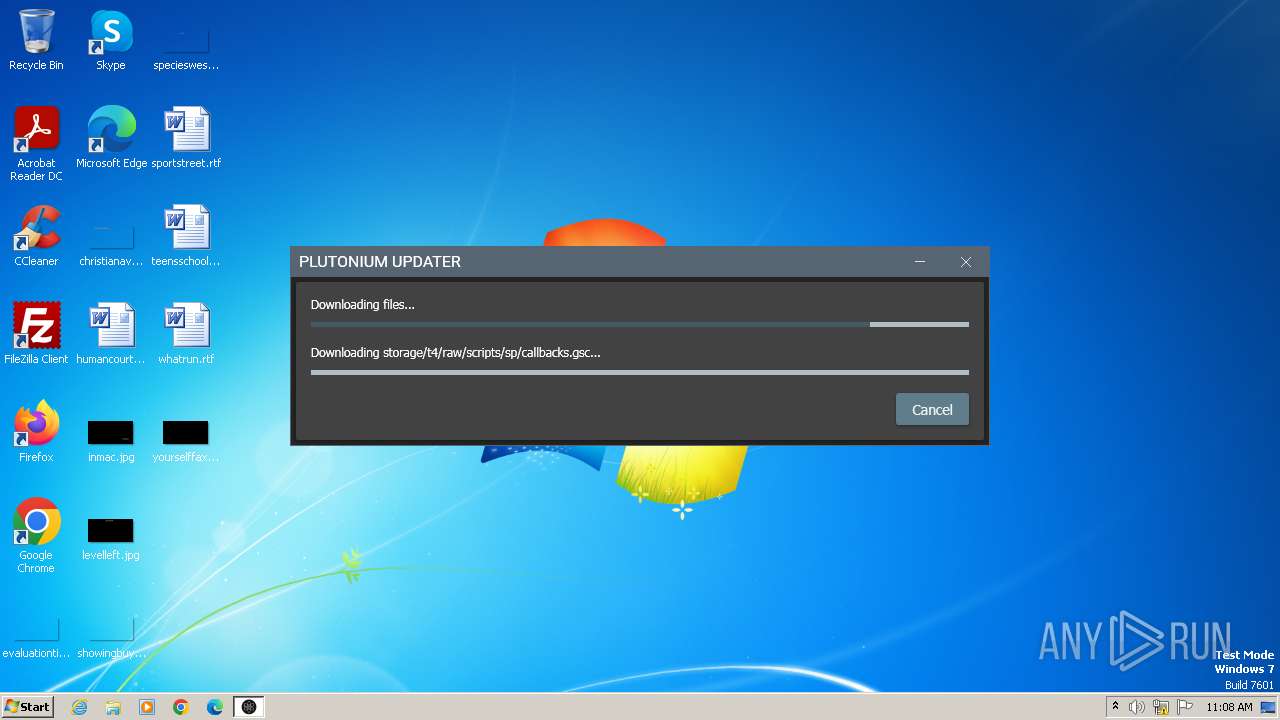
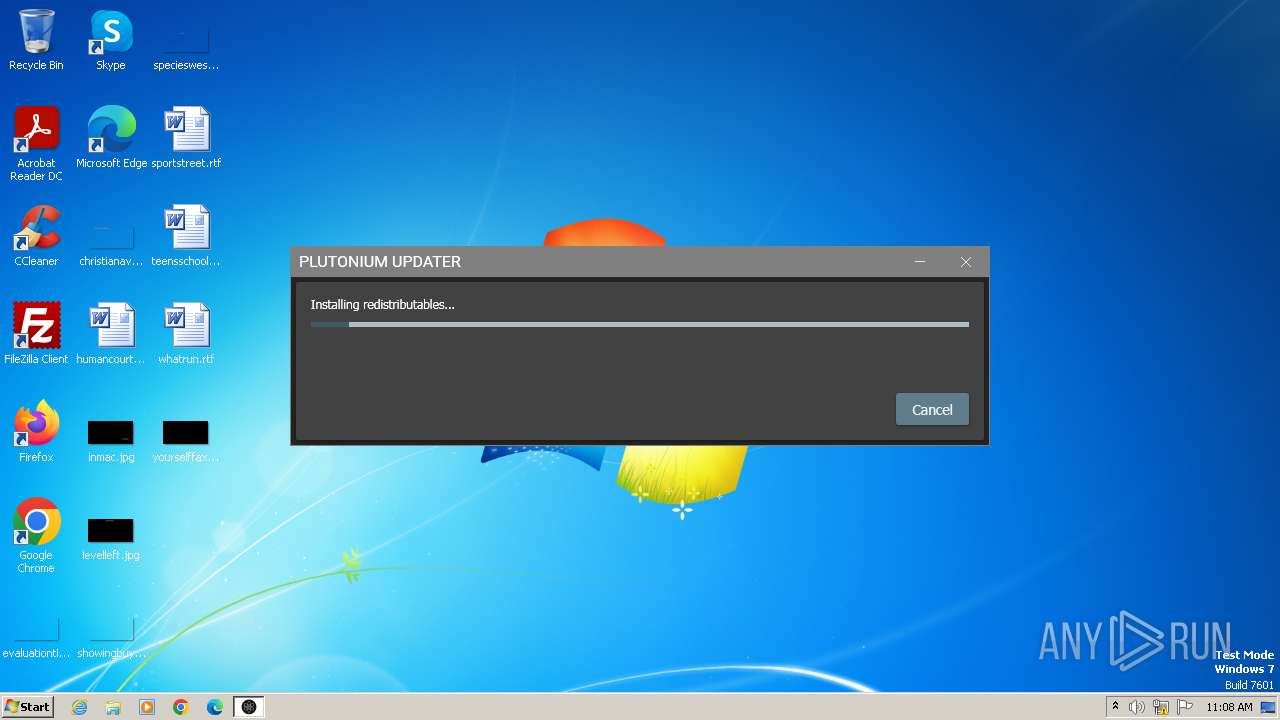
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\AppData\Local\Temp\plutonium.exe" | C:\Users\admin\AppData\Local\Temp\plutonium.exe | explorer.exe | ||||||||||||
User: admin Company: Plutonium.Updater.App Integrity Level: MEDIUM Description: Plutonium.Updater.App Exit code: 0 Version: 1.0.221.0 Modules
| |||||||||||||||
| 1108 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
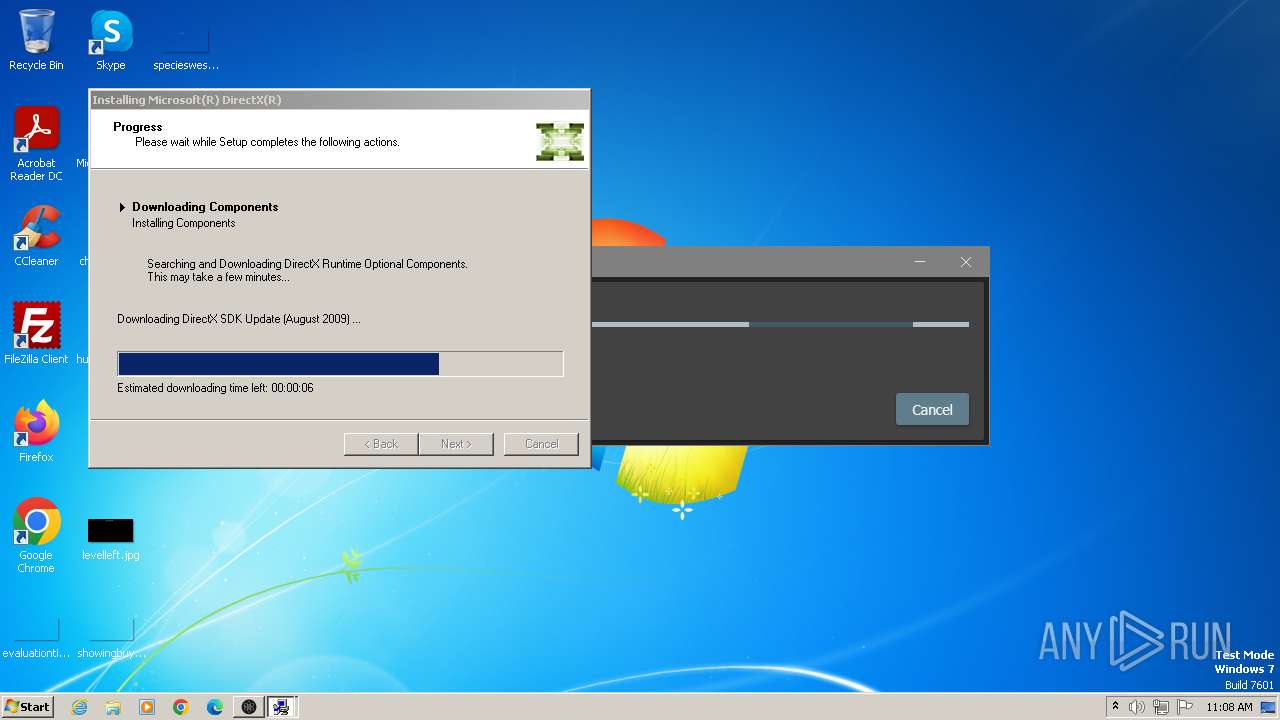
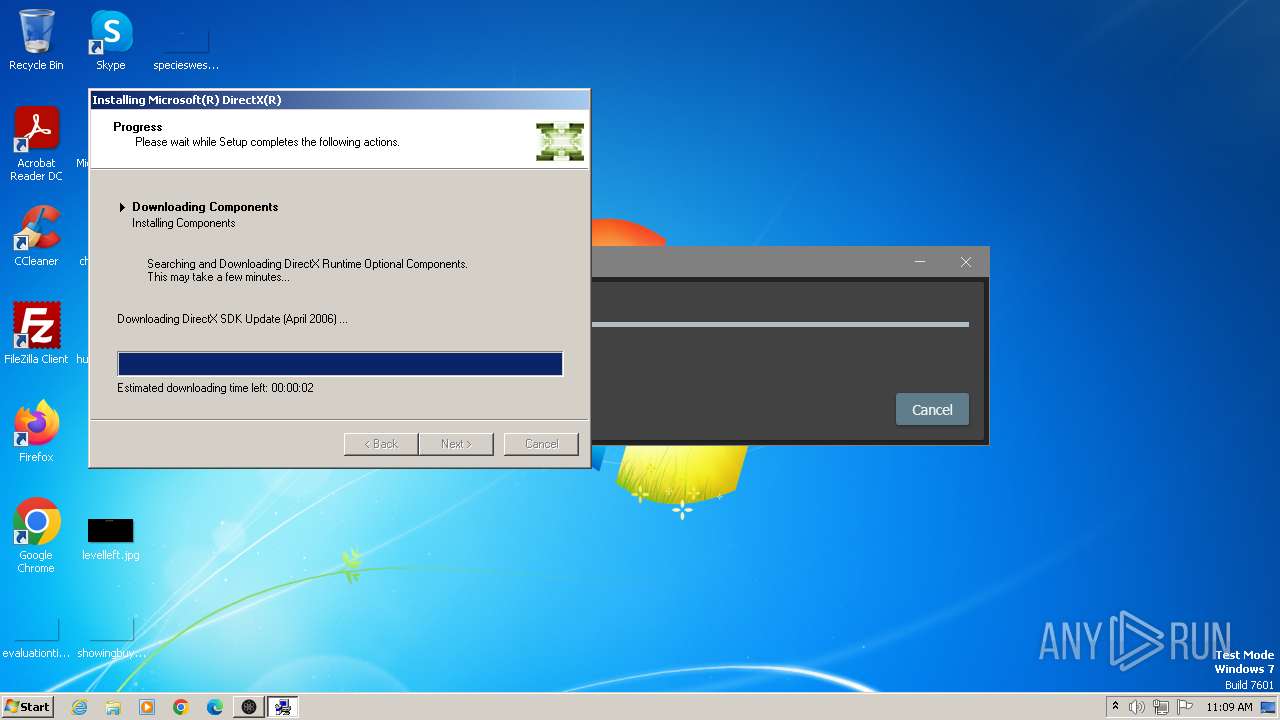
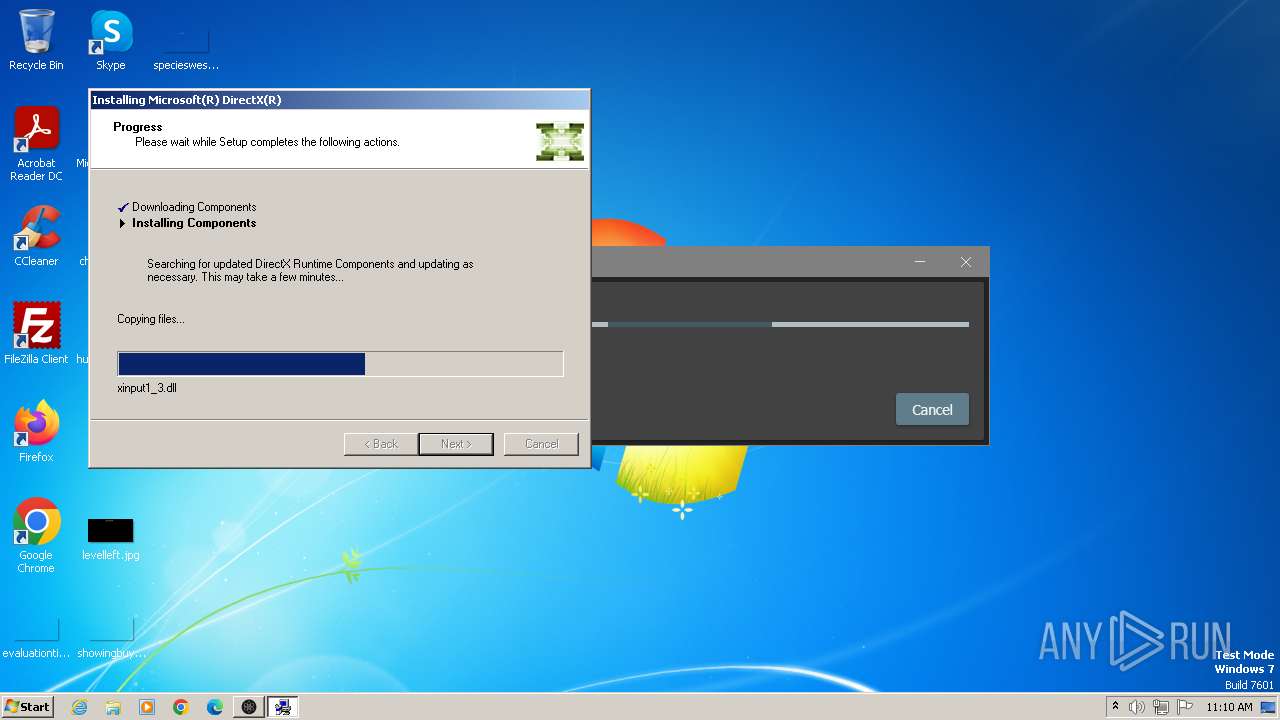
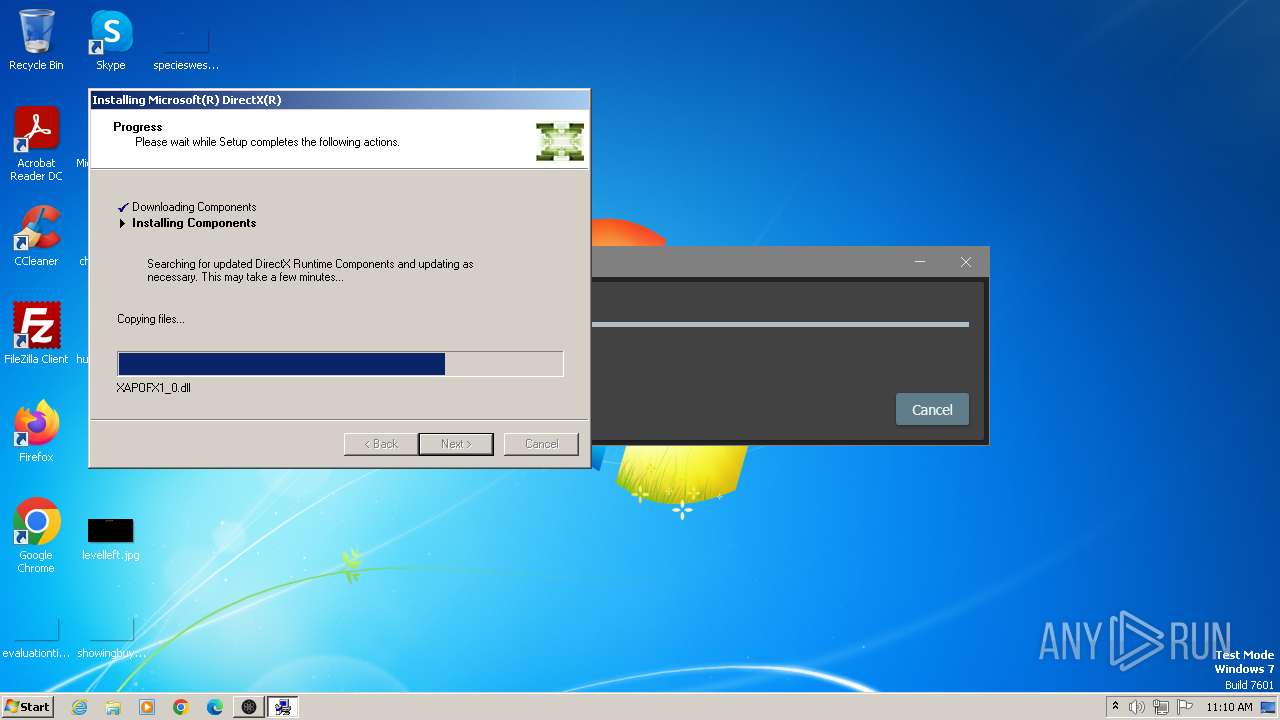
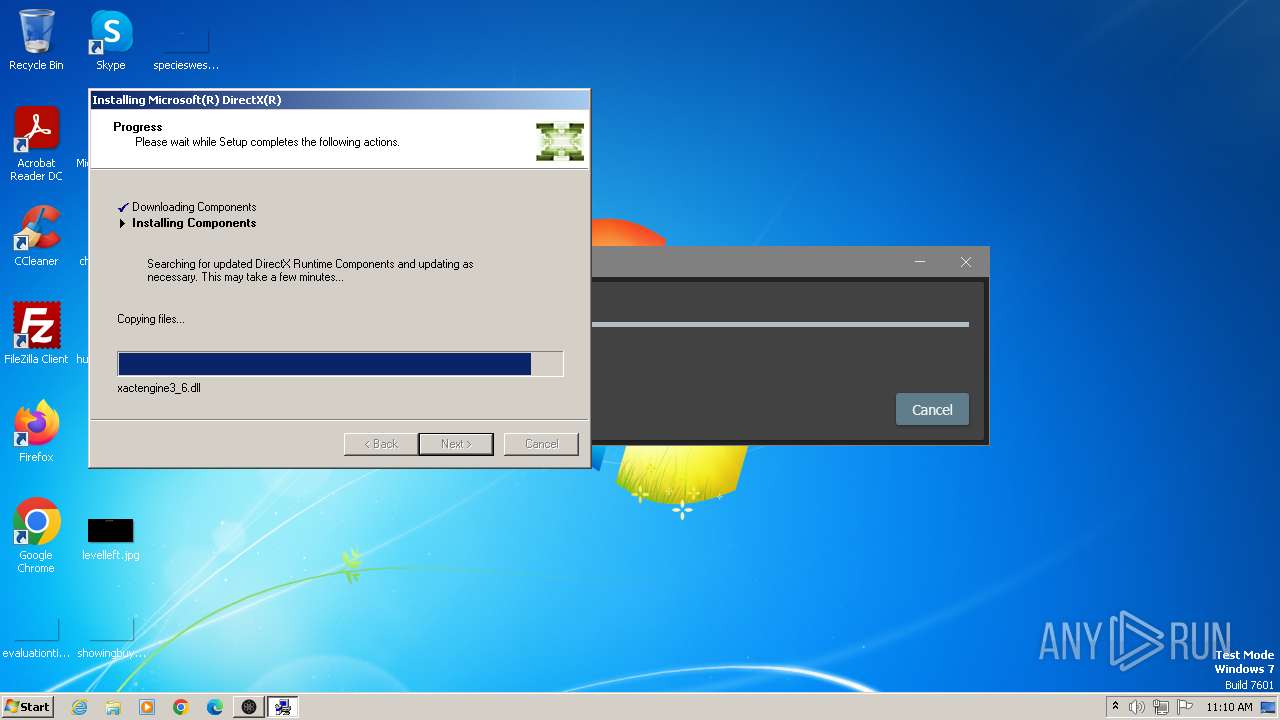
| 2616 | "C:\Users\admin\AppData\Local\Temp\178bffd3-6a59-4141-93c2-1c834413002d.exe" /Q | C:\Users\admin\AppData\Local\Temp\178bffd3-6a59-4141-93c2-1c834413002d.exe | plutonium.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX 9.0 Web setup Exit code: 0 Version: 9.29.1974.0 Modules
| |||||||||||||||
| 2912 | "C:\Users\admin\AppData\Local\Temp\178bffd3-6a59-4141-93c2-1c834413002d.exe" /Q | C:\Users\admin\AppData\Local\Temp\178bffd3-6a59-4141-93c2-1c834413002d.exe | — | plutonium.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DirectX 9.0 Web setup Exit code: 3221226540 Version: 9.29.1974.0 Modules
| |||||||||||||||
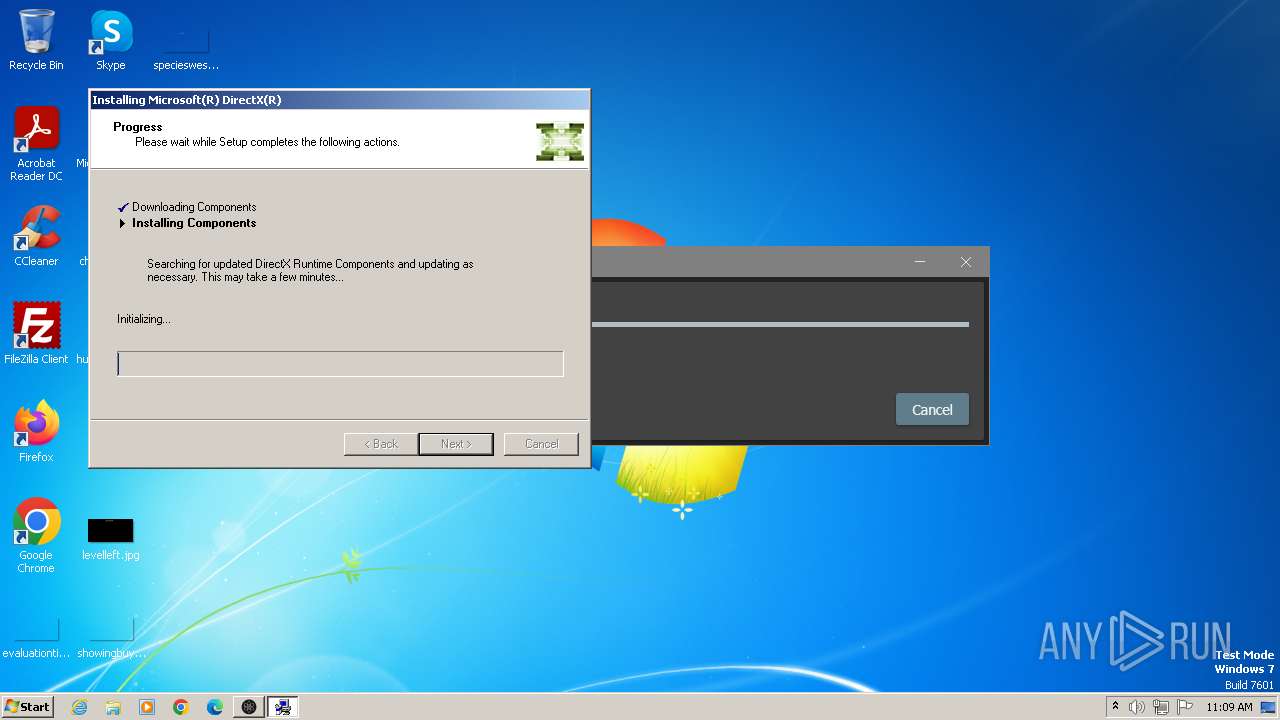
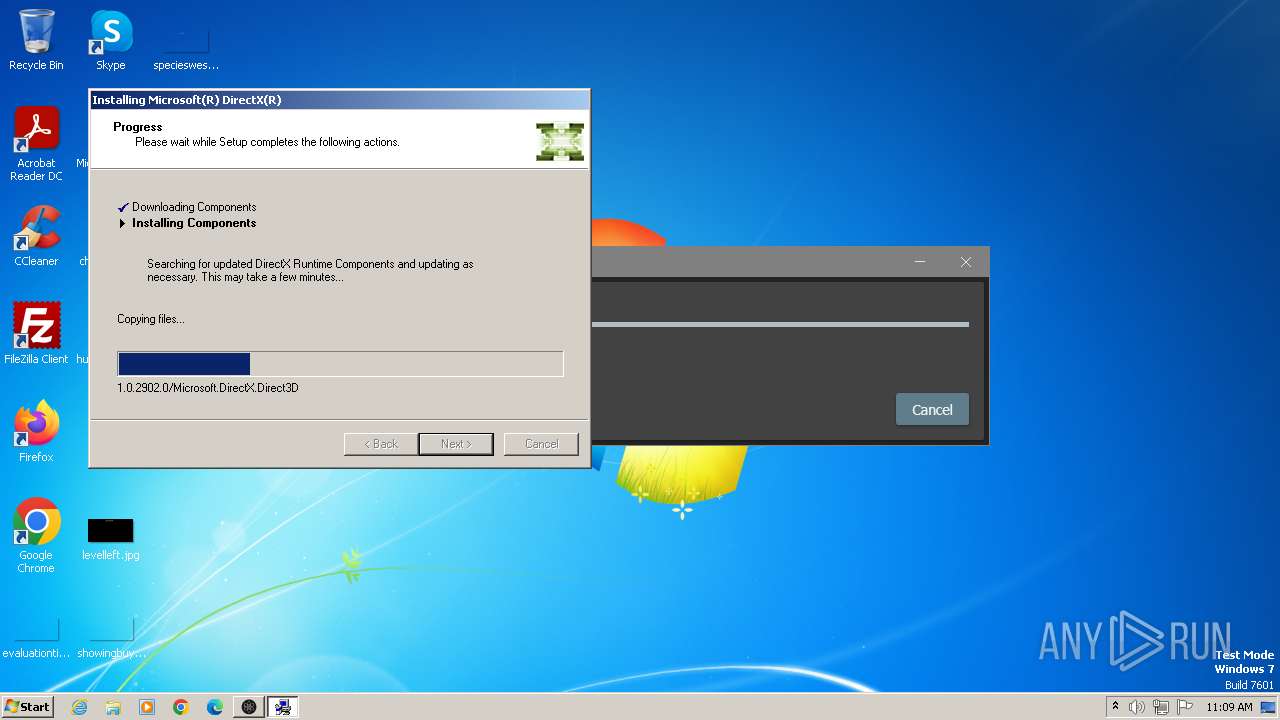
| 3008 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe /windowsupdate | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | 178bffd3-6a59-4141-93c2-1c834413002d.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX Setup Exit code: 0 Version: 4.9.0.0904 Modules
| |||||||||||||||
| 3392 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3432 | "C:\Users\admin\AppData\Local\Plutonium\bin\plutonium-launcher-win32.exe" | C:\Users\admin\AppData\Local\Plutonium\bin\plutonium-launcher-win32.exe | plutonium.exe | ||||||||||||
User: admin Company: Plutonium Project Integrity Level: MEDIUM Description: Plutonium Launcher Version: 1.0.0.4542 | |||||||||||||||
Total events
44 170
Read events
43 824
Write events
339
Delete events
7
Modification events
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1040) plutonium.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\plutonium_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
379
Suspicious files
653
Text files
143
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\games\t4sp.exe | executable | |
MD5:04D5620ACF68F0A9A067DF532EA23B96 | SHA256:F26D45524BFFF7E44C8EBAB4D758CA524EDFB0FB7D52352B6C95E1E908799361 | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\AppCore.dll | executable | |
MD5:80C3806A12959987AC012E28F63AD150 | SHA256:B5338B858E5C65F9C36BBC817673BA5E1A05EED8F4DCF007B6BC4FF6140FC8F8 | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\VibeCheck.exe | executable | |
MD5:BE1EE42858B55352E0FB154D76F31562 | SHA256:4B053F45887ED35E584B3DDC4C44BAA1533372161B96DEAAA2C3C1EA6FCE7F2B | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\UltralightCore.dll | executable | |
MD5:CD3768E013636A12E6CE7937A7F69365 | SHA256:9ED2701BA7C3349ECBBCF276C280A09262B4DA72BE9FDCDDD81A8BAC9C9B3D69 | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\games\t6zm.exe | executable | |
MD5:837C6AE7DC13412FB4DD346CD7C987FF | SHA256:2AFF340F22F0C68BF46511C7BBC6167E4BB84524817F54CAE08E8F60E6F9AFC3 | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\launcher\assets\index.html | html | |
MD5:33D5011A7F471996C0593661135D0850 | SHA256:6DC828B0E444BBCFF8B86F853F124B4D22E7E132C793272C05B22594285271CF | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\games\t5mp.exe | executable | |
MD5:5F078CB9FDAE3B960D616B969AF72C48 | SHA256:6A544494722AAF90AE241D687FCA0AEBD73F97F0D79412D0F8C311F6C369C3FB | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\launcher\assets\manifest.json | binary | |
MD5:515E59F16E9296205663258D761E2471 | SHA256:B287288B090F627E66F2C492B949015BDC2F4F2B76BEEA6591D7F3D2C6F56765 | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\WebCore.dll | executable | |
MD5:90B16ABE7F82DCAE822174B4503F4E1B | SHA256:B4D361BF13F98C96C21C3DEC94D14914FF80C3515A48CD3DF974378CD6052082 | |||
| 1040 | plutonium.exe | C:\Users\admin\AppData\Local\Plutonium\bin\plutonium-bootstrapper-win32.exe | executable | |
MD5:B4BD3FE865E88DD63496D174EF4F8F28 | SHA256:E0049B7B74A2B967F9E90F94C3B1E6BF8CCC3C6D9CE6BE0E6D50693D11C69918 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
87
TCP/UDP connections
16
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3008 | dxwsetup.exe | GET | 302 | 23.32.101.194:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Feb2006_xact_x86.cab | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9290fe536483eb95 | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 302 | 23.32.101.194:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/dxupdate.cab | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 302 | 23.32.101.194:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Apr2006_xinput_x86.cab | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 302 | 23.32.101.194:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Jun2006_xact_x86.cab | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 302 | 23.32.101.194:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Apr2006_xact_x86.cab | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 302 | 23.32.101.194:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Aug2006_xinput_x86.cab | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 302 | 23.32.101.194:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Dec2006_d3dx10_00_x86.cab | unknown | — | — | whitelisted |
3008 | dxwsetup.exe | GET | 302 | 23.32.101.194:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Aug2006_xact_x86.cab | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1040 | plutonium.exe | 104.26.15.172:443 | cdn.plutonium.pw | CLOUDFLARENET | US | suspicious |
1040 | plutonium.exe | 104.21.16.1:443 | cdn.plutoniummod.com | CLOUDFLARENET | — | unknown |
1040 | plutonium.exe | 23.32.101.194:443 | download.microsoft.com | AKAMAI-AS | SE | whitelisted |
3008 | dxwsetup.exe | 23.32.101.194:80 | download.microsoft.com | AKAMAI-AS | SE | whitelisted |
3008 | dxwsetup.exe | 23.32.101.194:443 | download.microsoft.com | AKAMAI-AS | SE | whitelisted |
3008 | dxwsetup.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3008 | dxwsetup.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.plutonium.pw |
| unknown |
cdn.plutoniummod.com |
| unknown |
download.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
use.typekit.net |
| whitelisted |
kit.fontawesome.com |
| whitelisted |
p.typekit.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1108 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
Process | Message |
|---|---|
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |