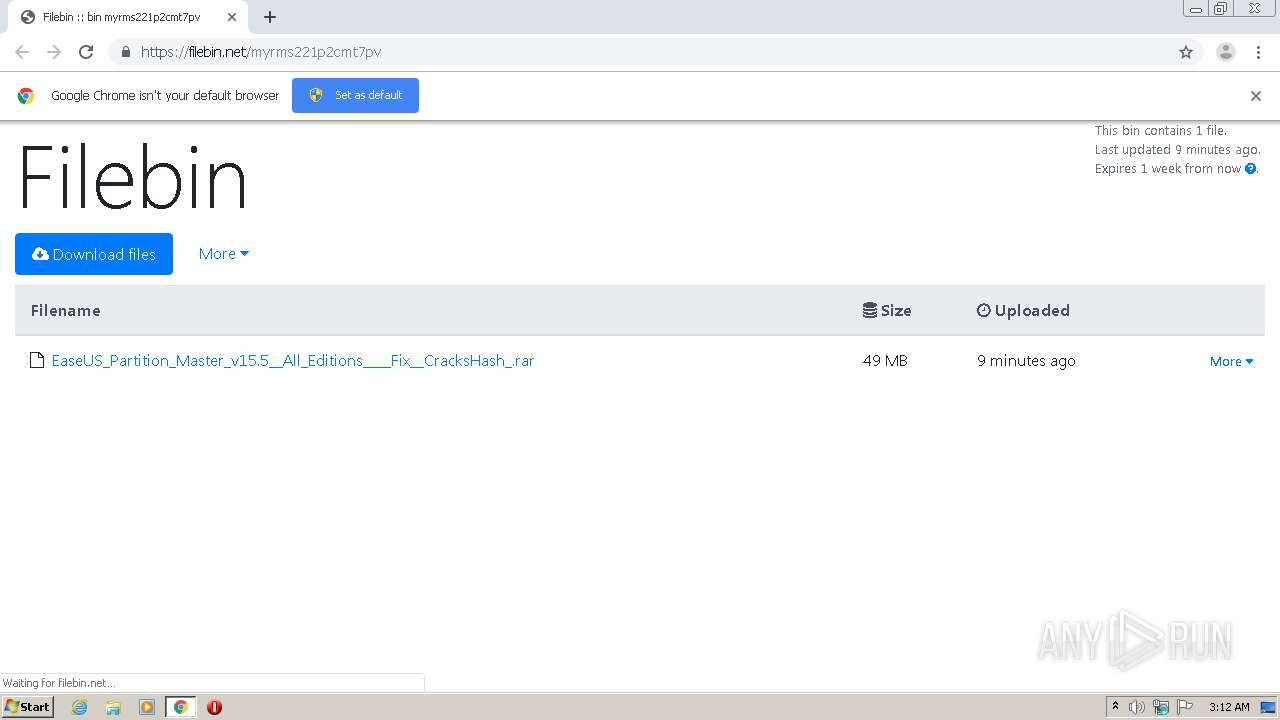
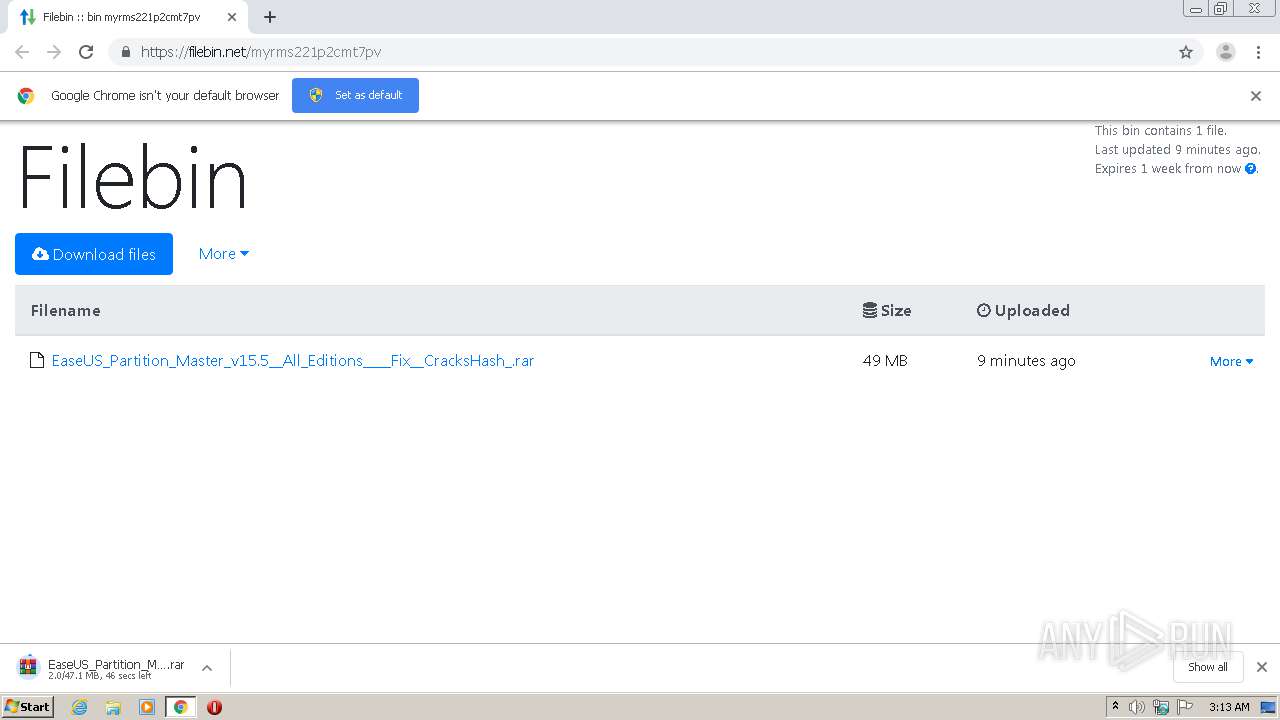
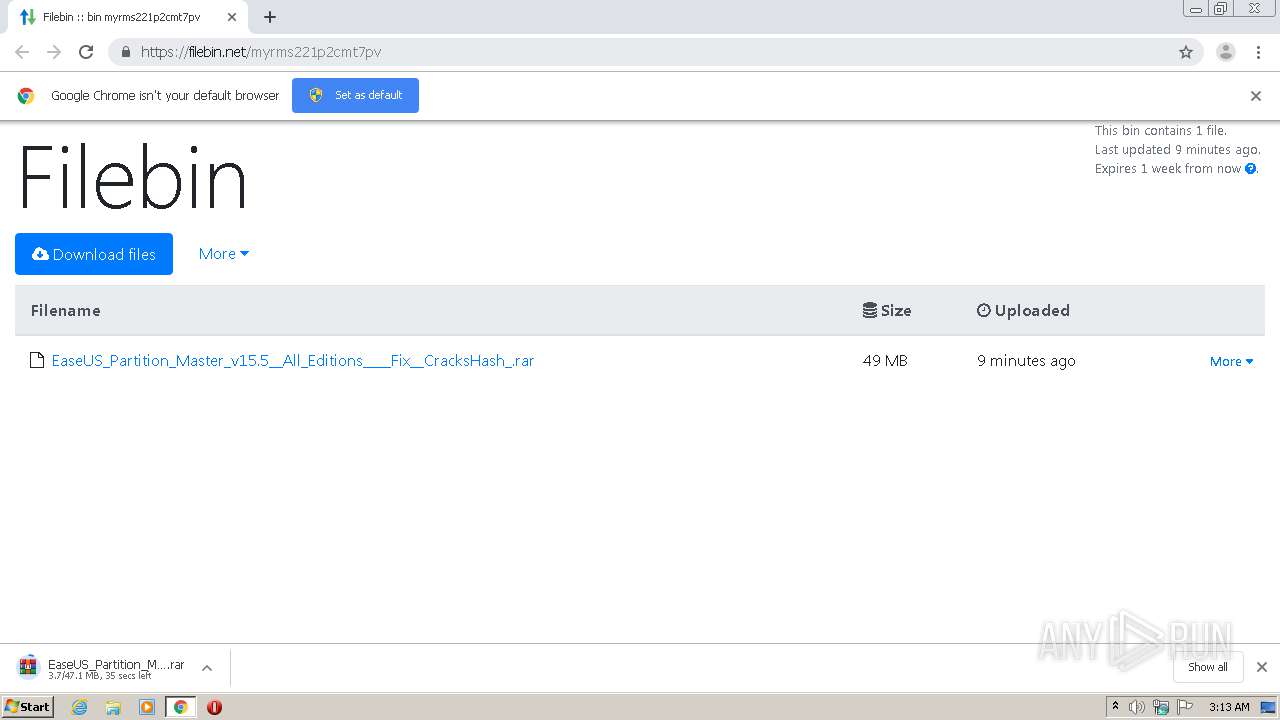
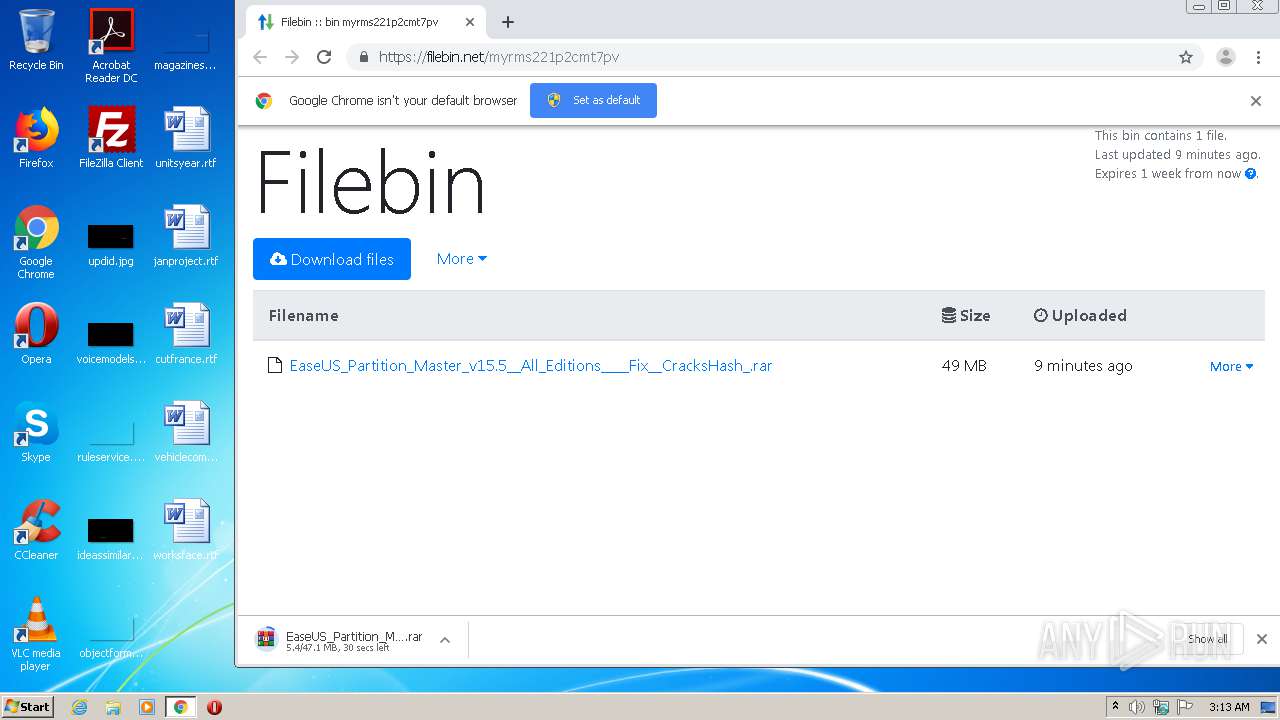
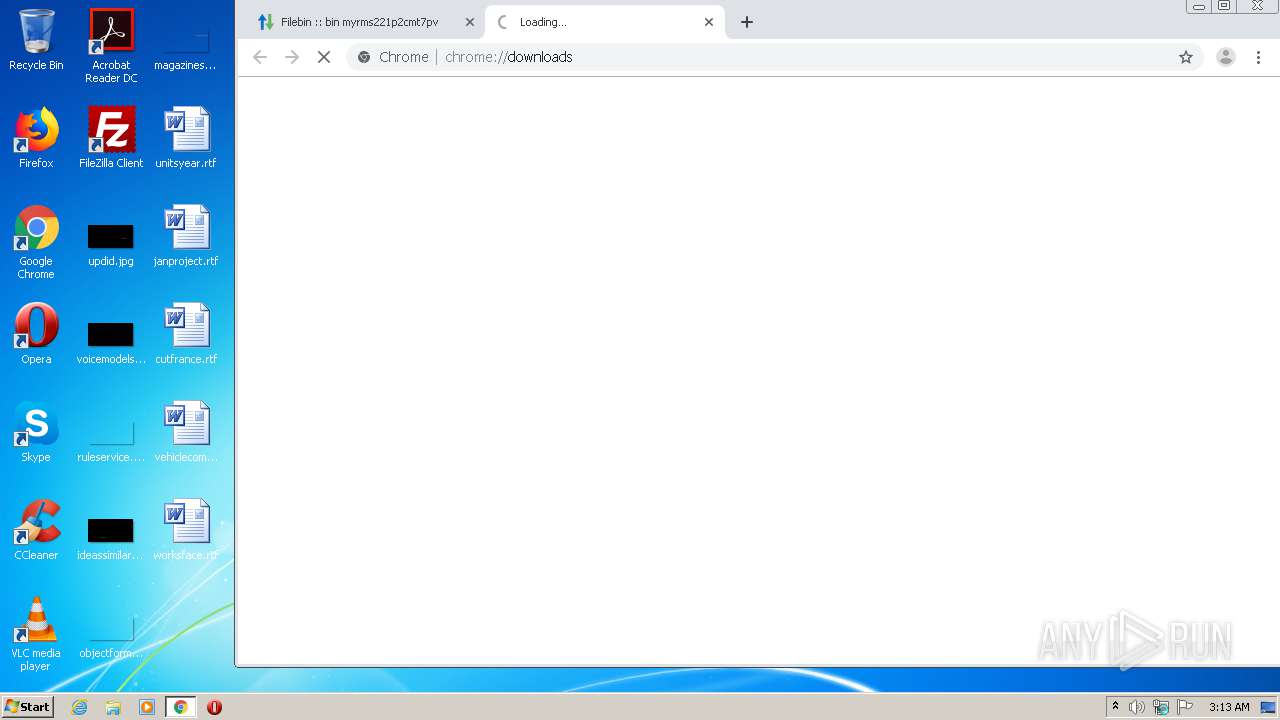
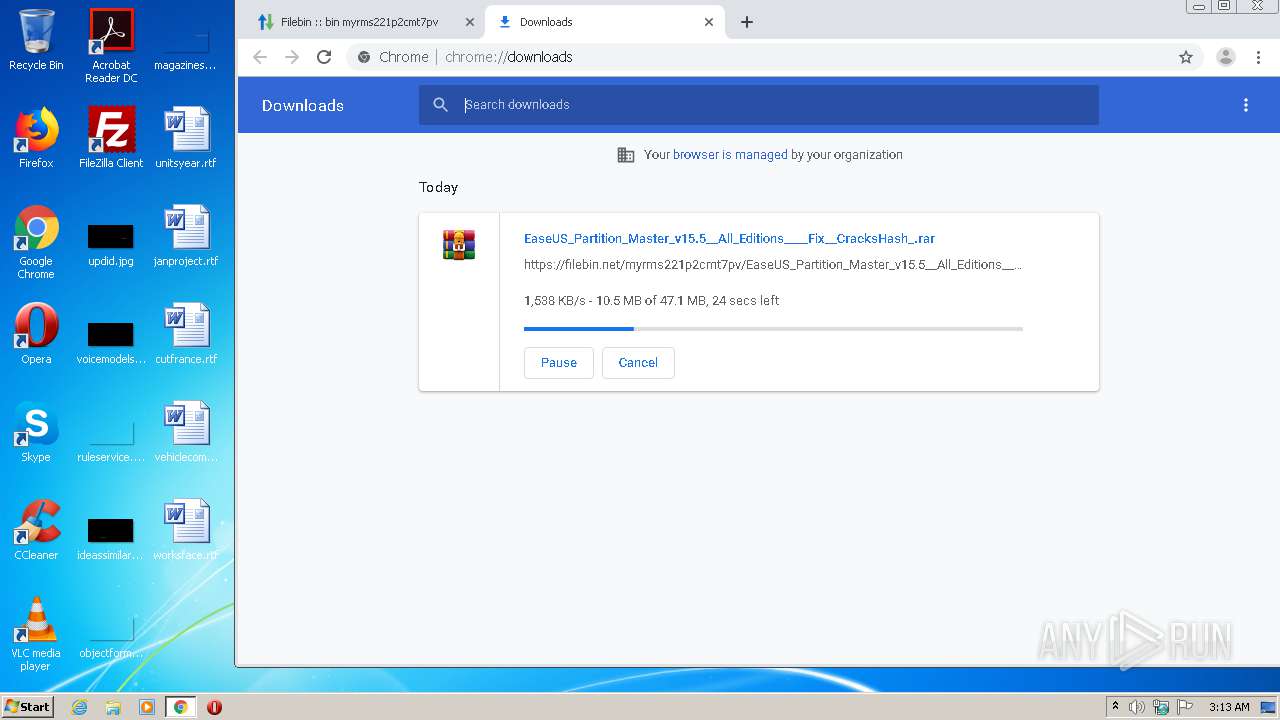
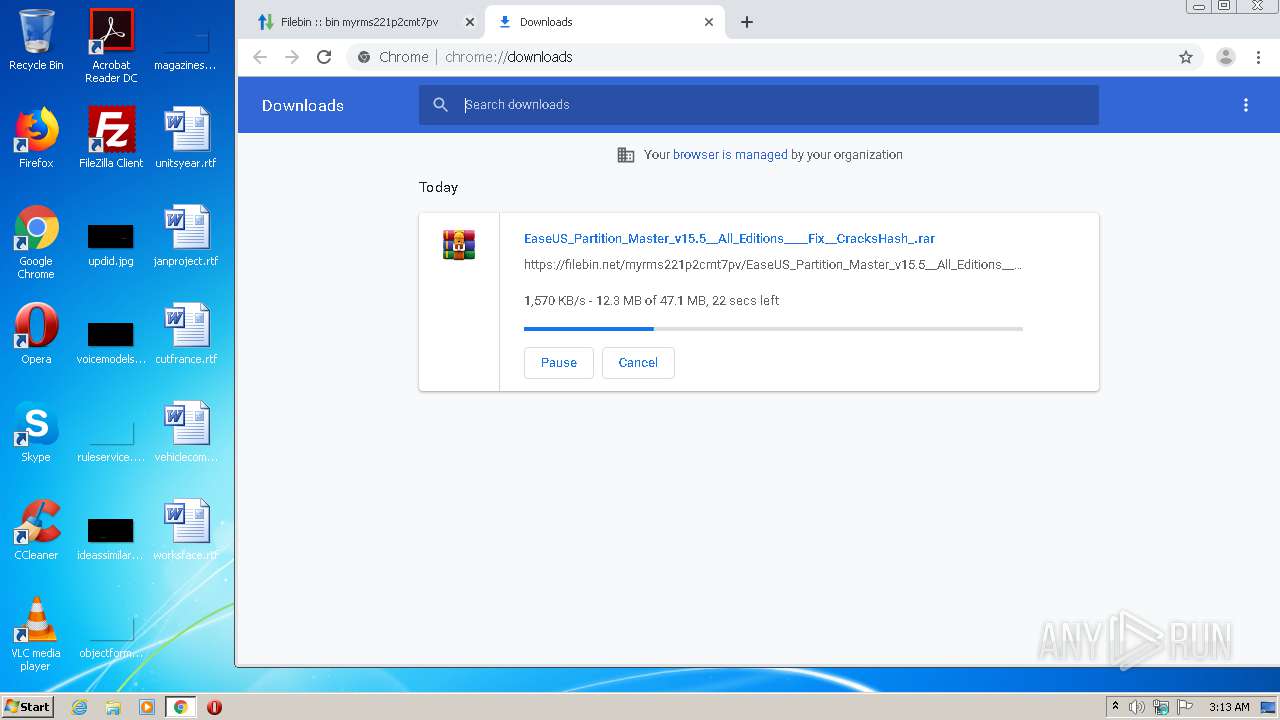
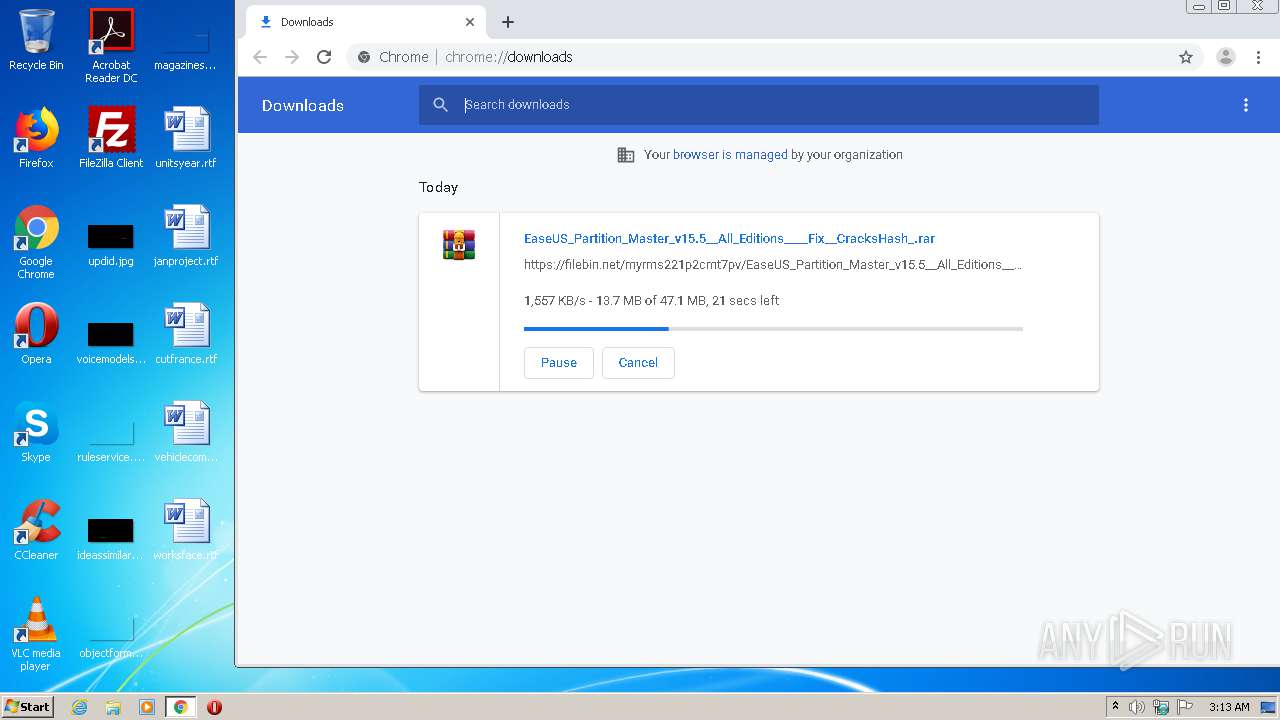
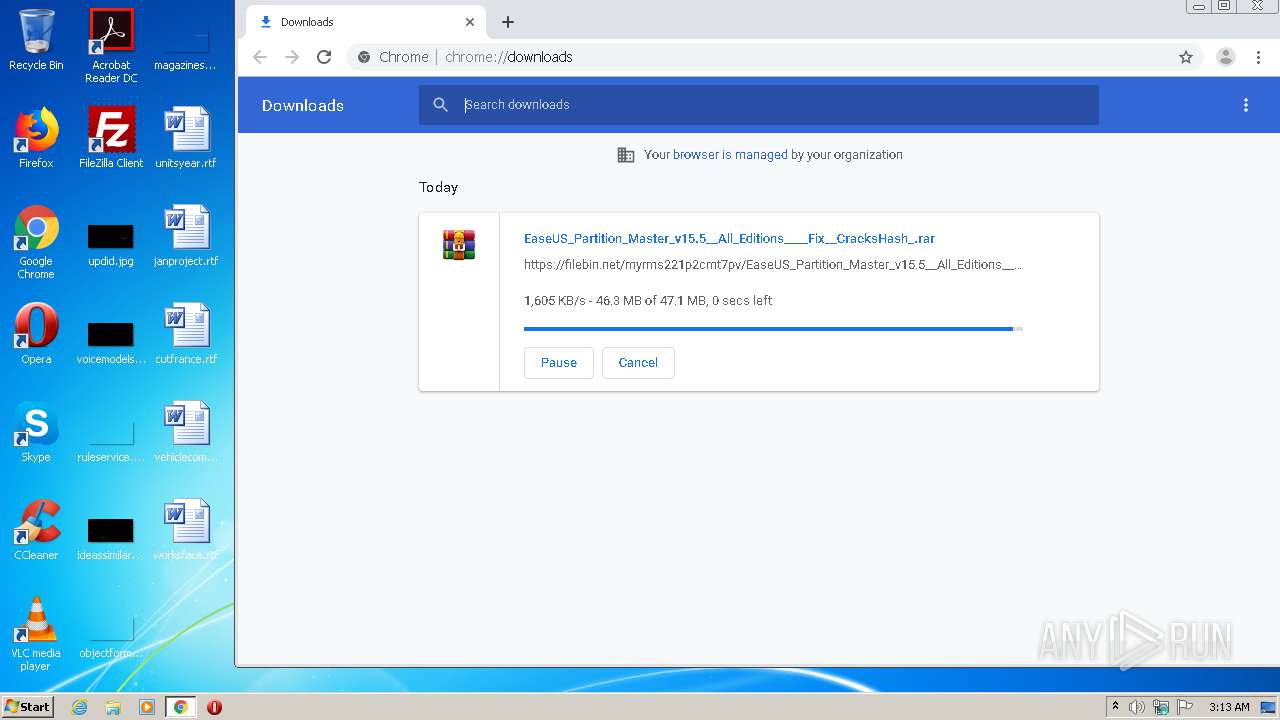
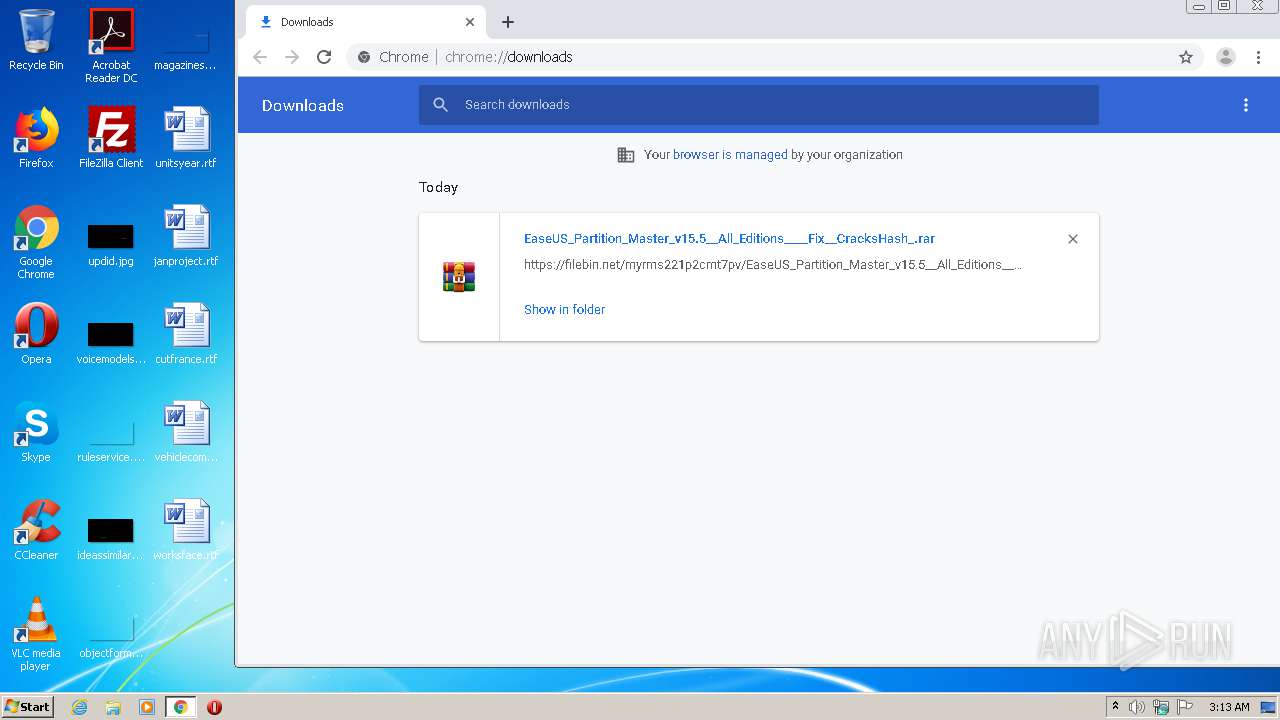
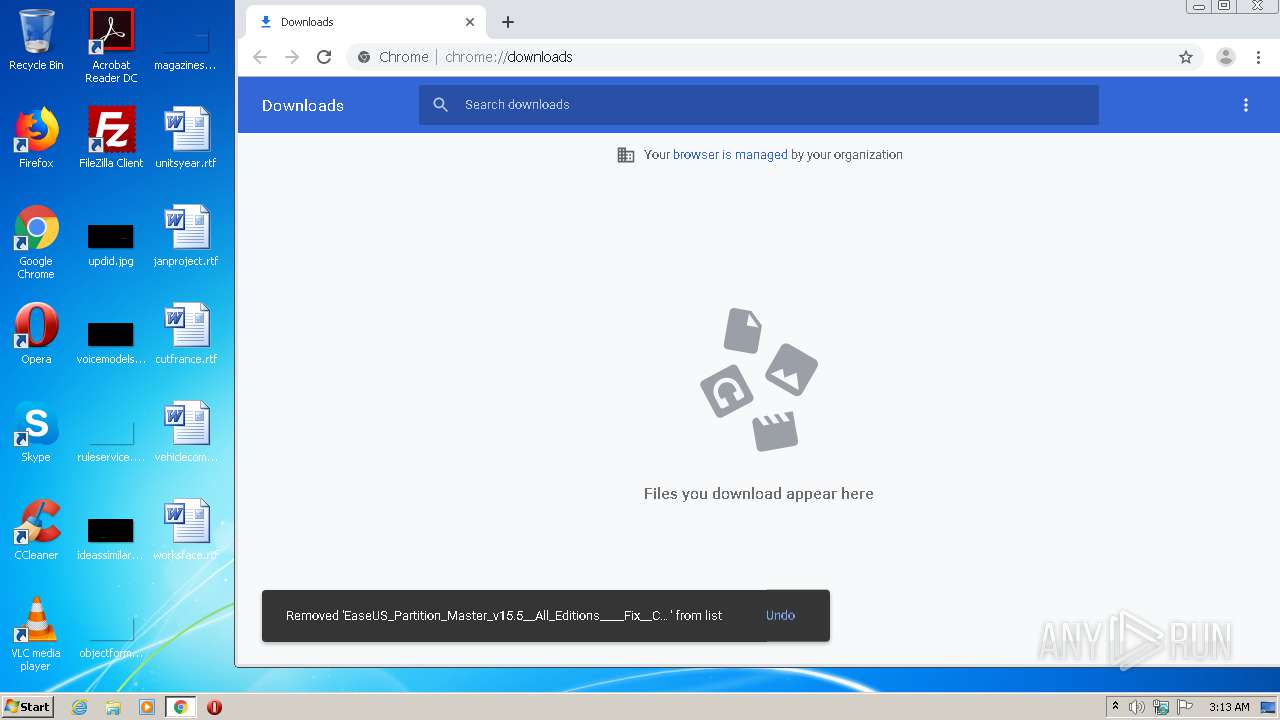
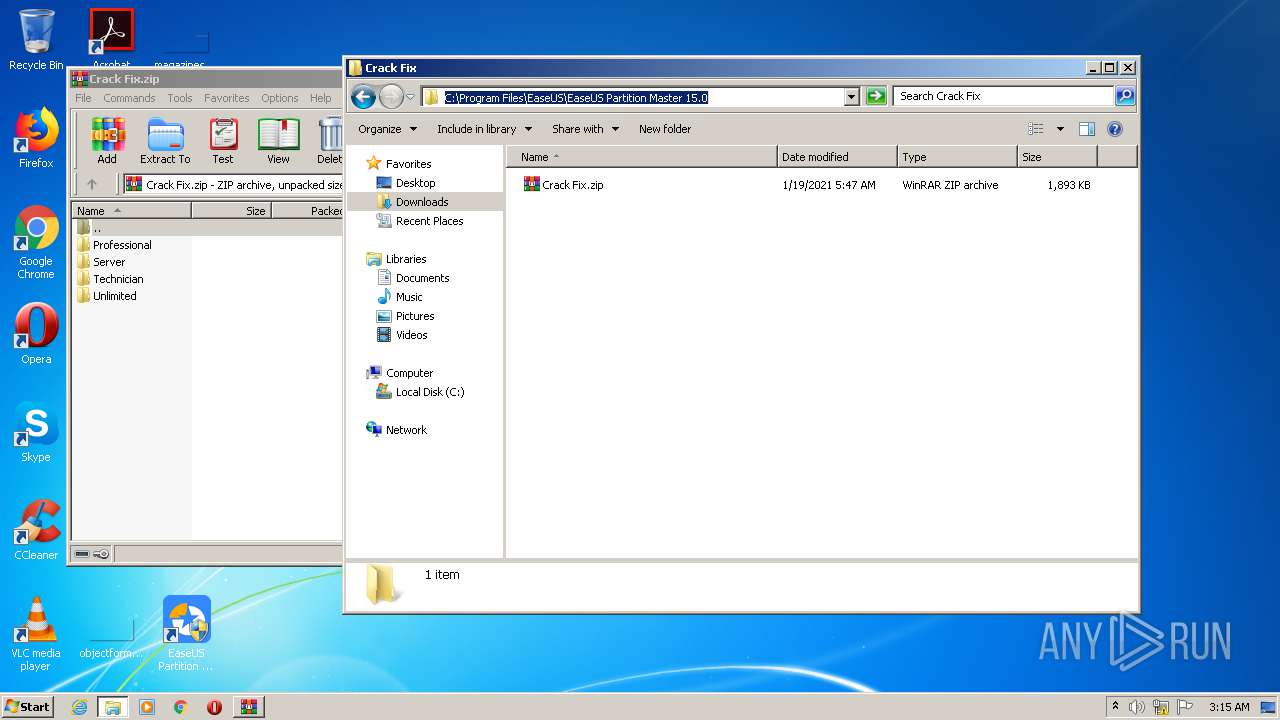
| URL: | https://filebin.net/myrms221p2cmt7pv |
| Full analysis: | https://app.any.run/tasks/7c0f2081-607f-436b-8fc5-46872445ec07 |
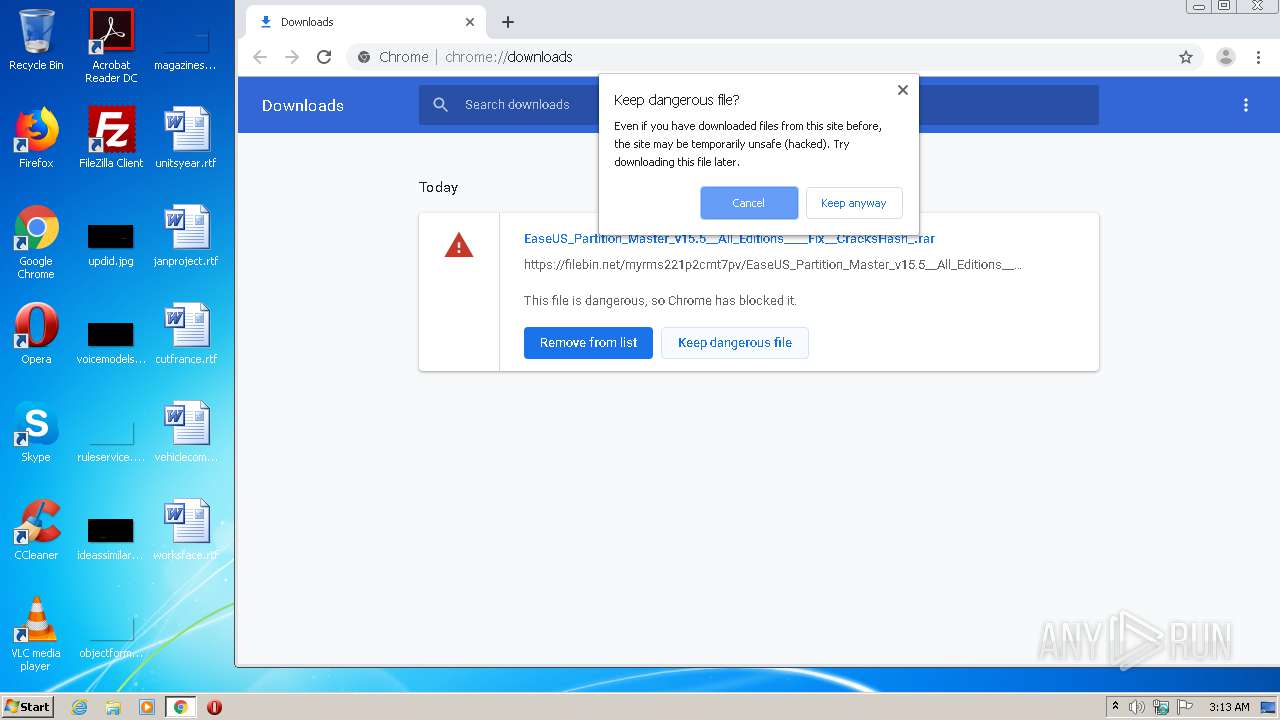
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2021, 02:12:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D624513CBFB1E1774CFBBD4D0DC7F524 |
| SHA1: | 770931D6C79BB85E97DC82C04F5A694949E38DAA |
| SHA256: | 85CBCFCE5A60CBDE4E82249D02DE280CFD9D2E6598DF771F24D5AF3843B272F4 |
| SSDEEP: | 3:N8wLqFpS5n:2yn |
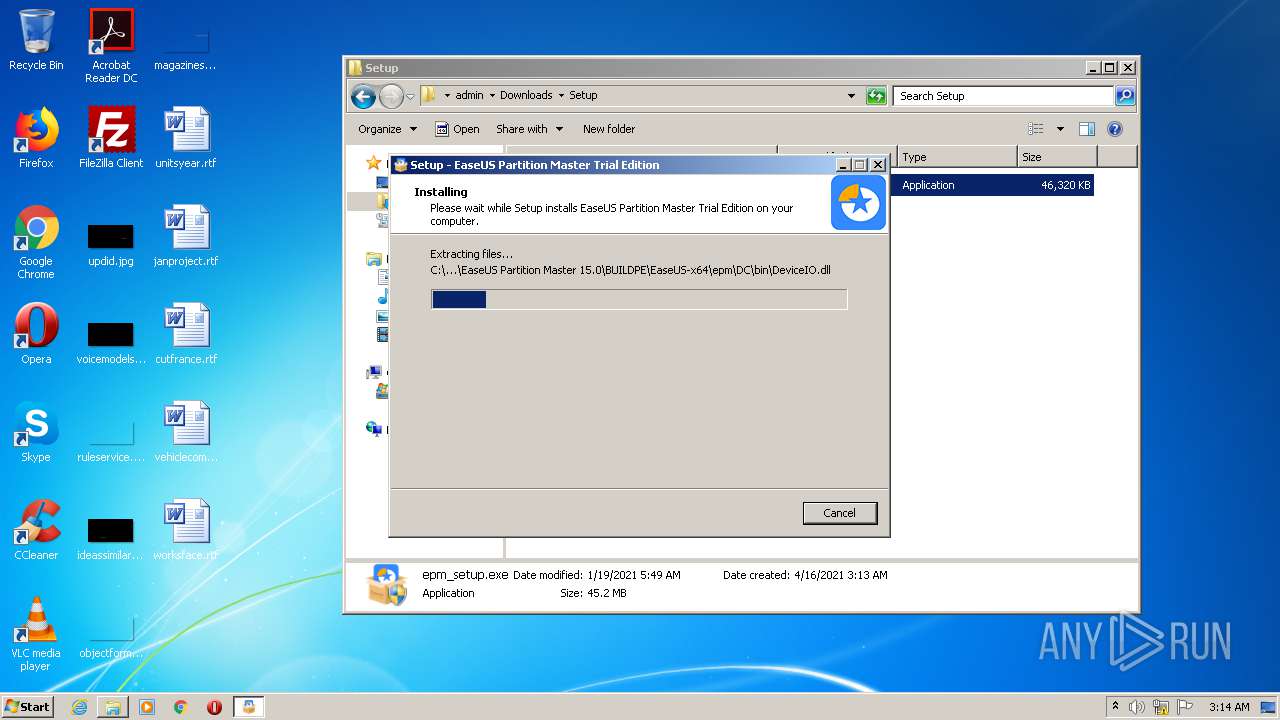
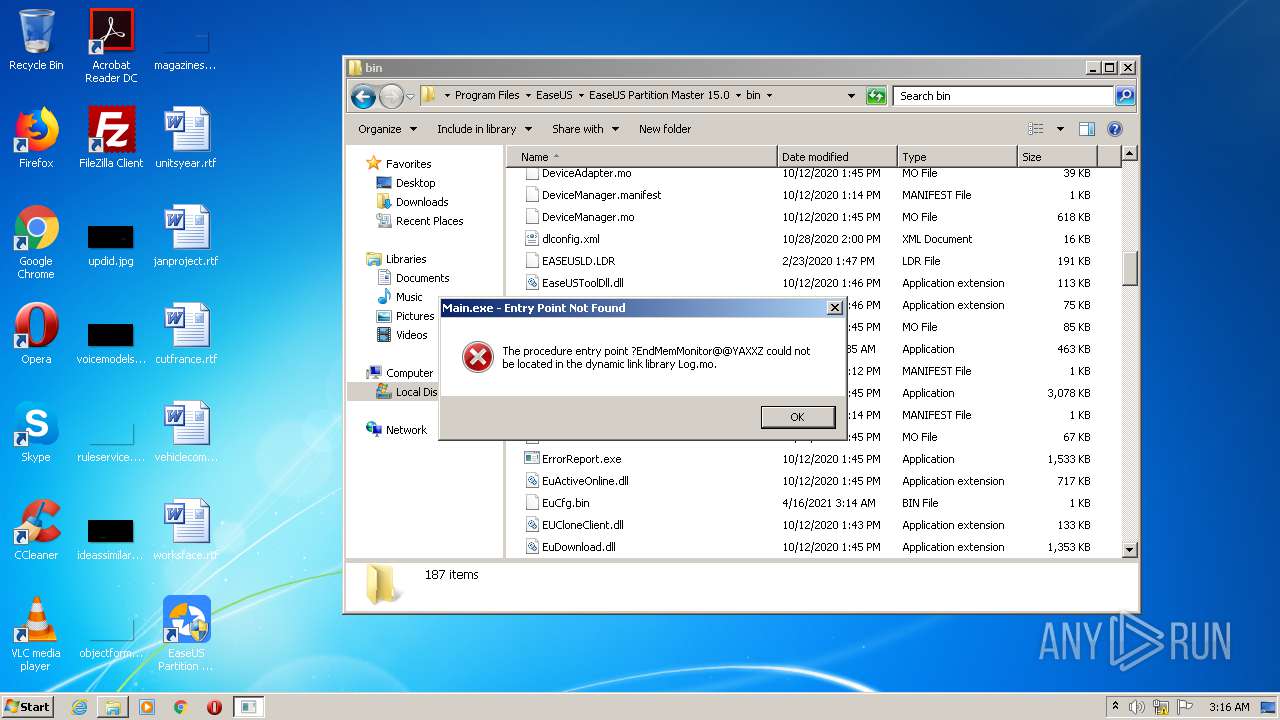
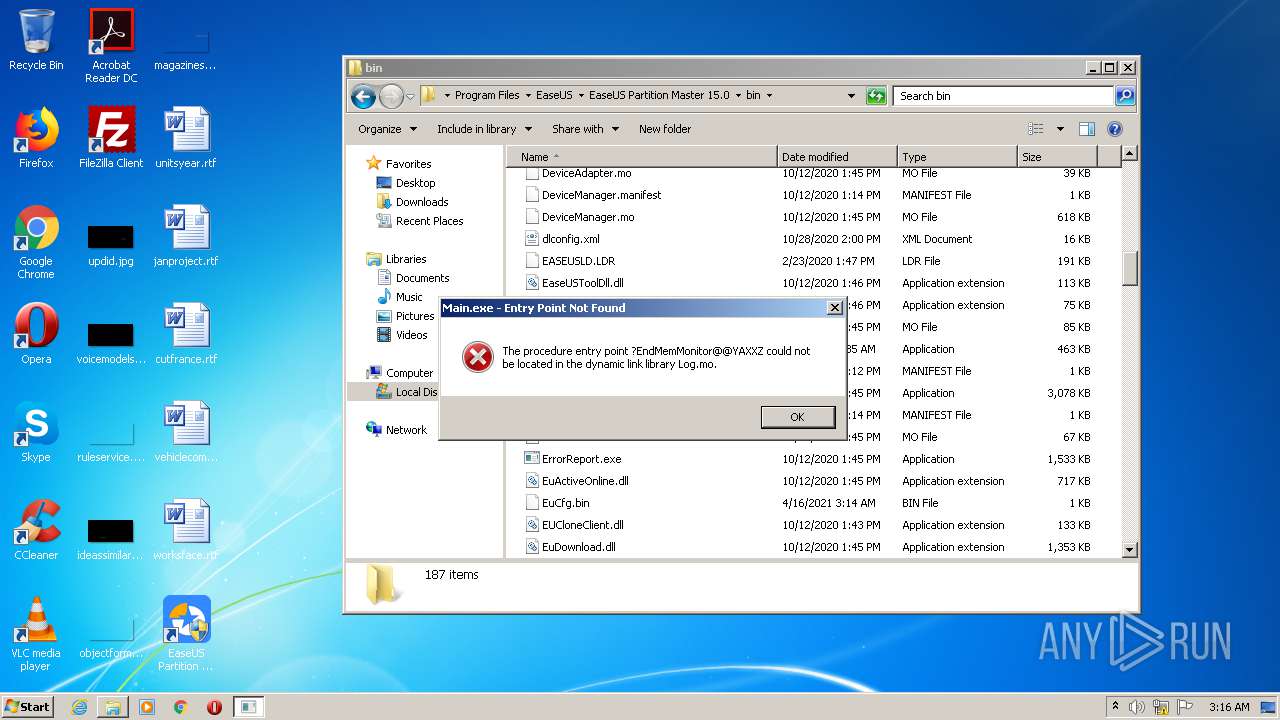
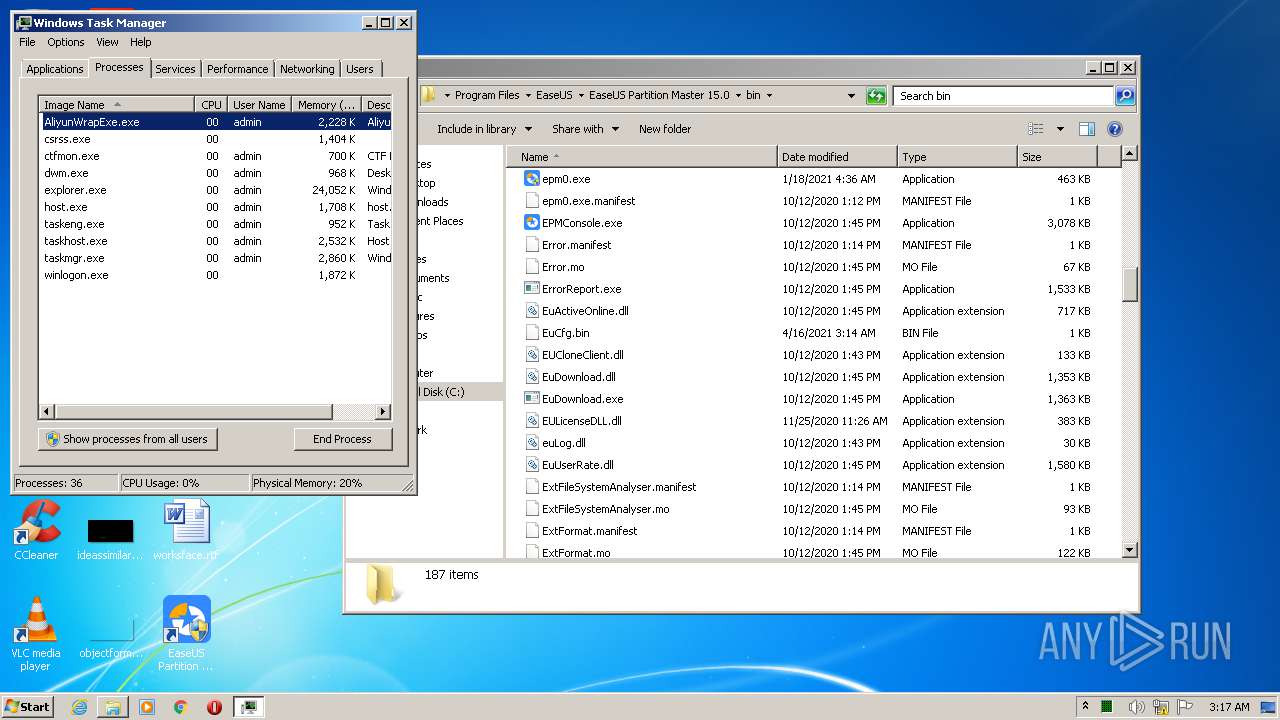
MALICIOUS
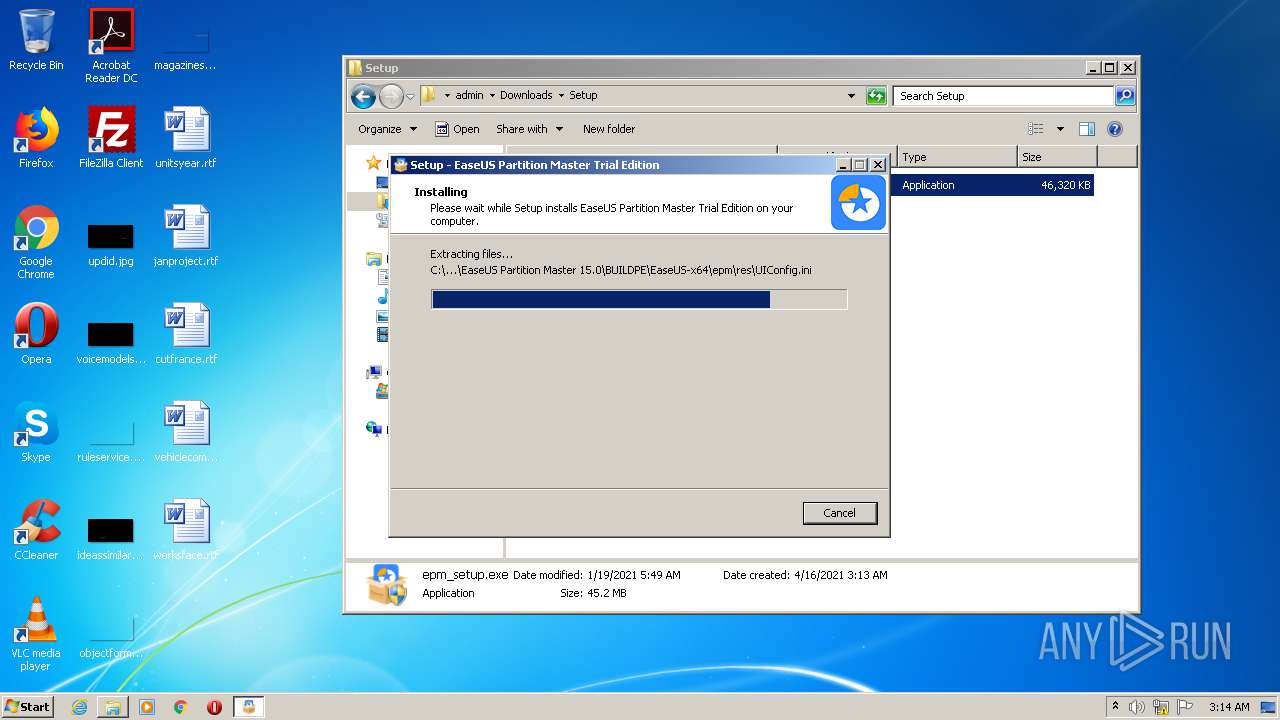
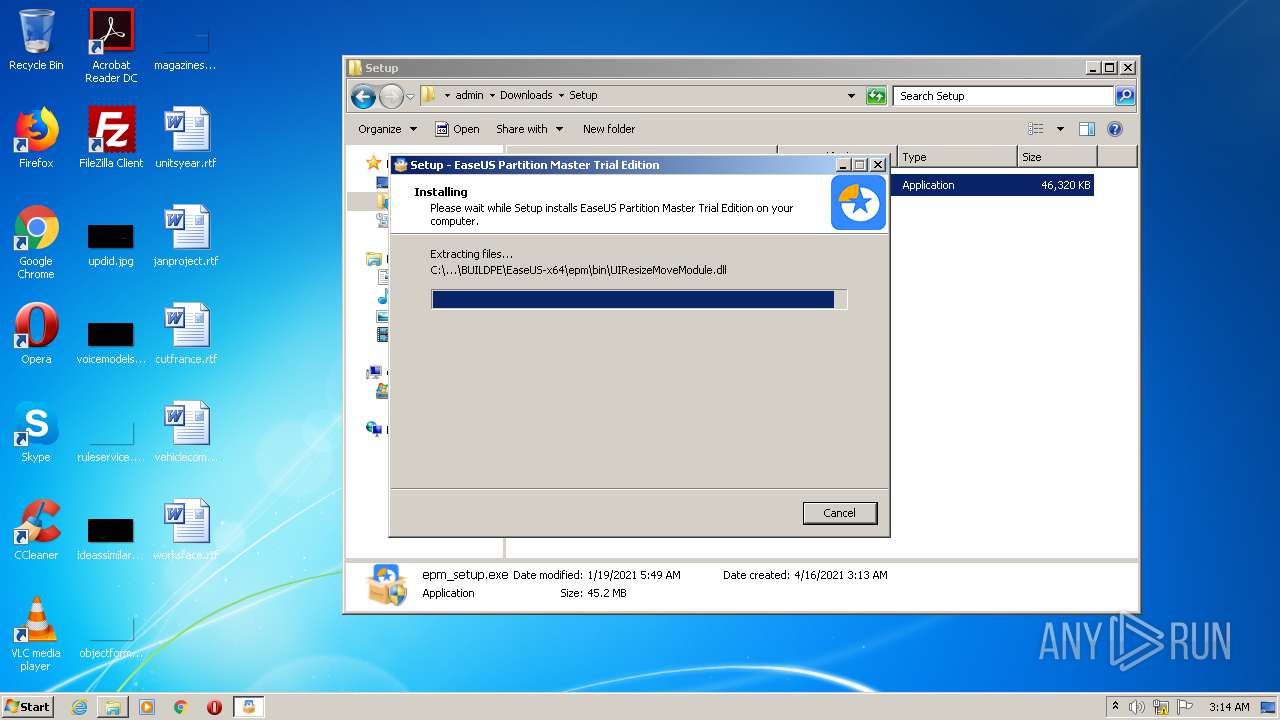
Drops executable file immediately after starts
- epm_setup.exe (PID: 3632)
- DllHost.exe (PID: 3768)
Actions looks like stealing of personal data
- epm_setup.tmp (PID: 3884)
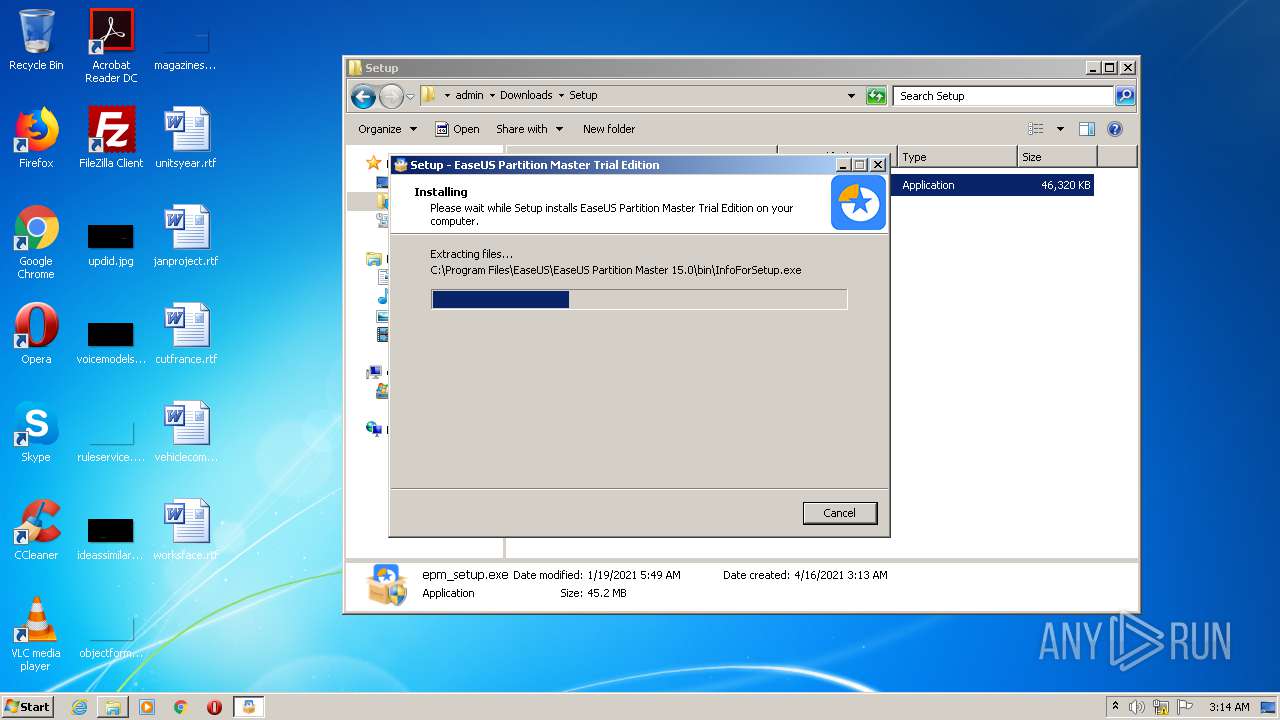
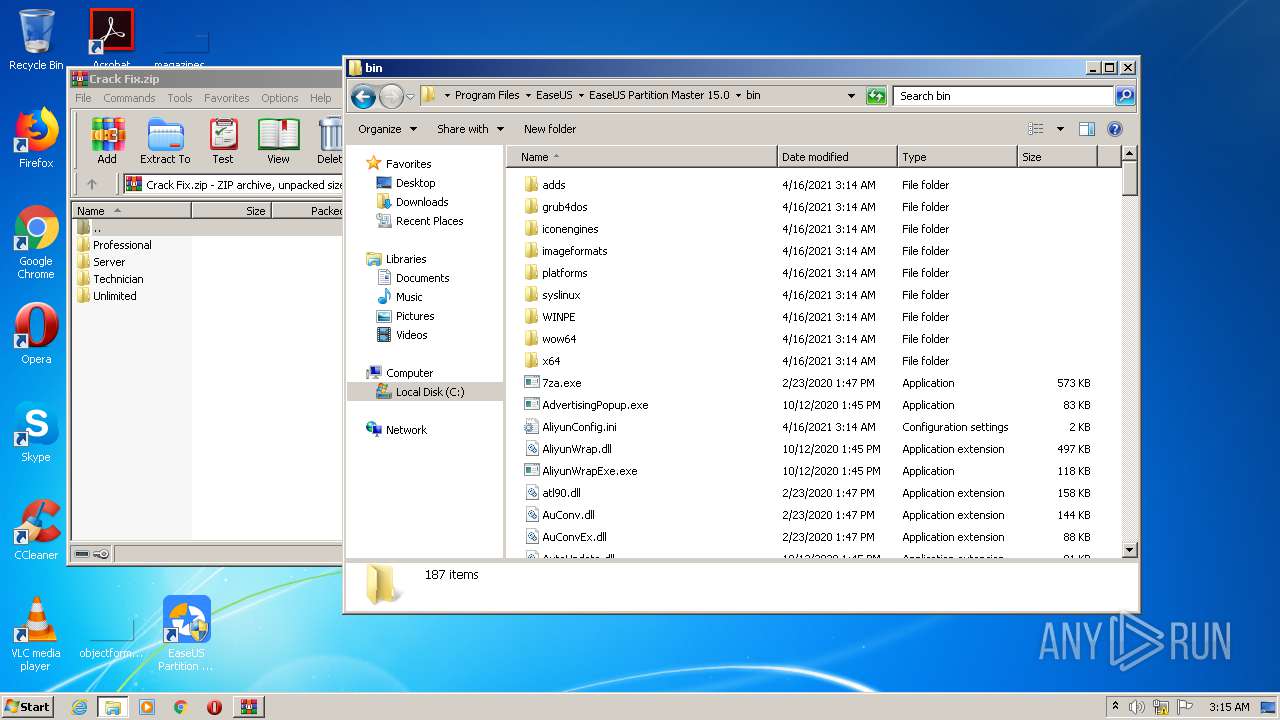
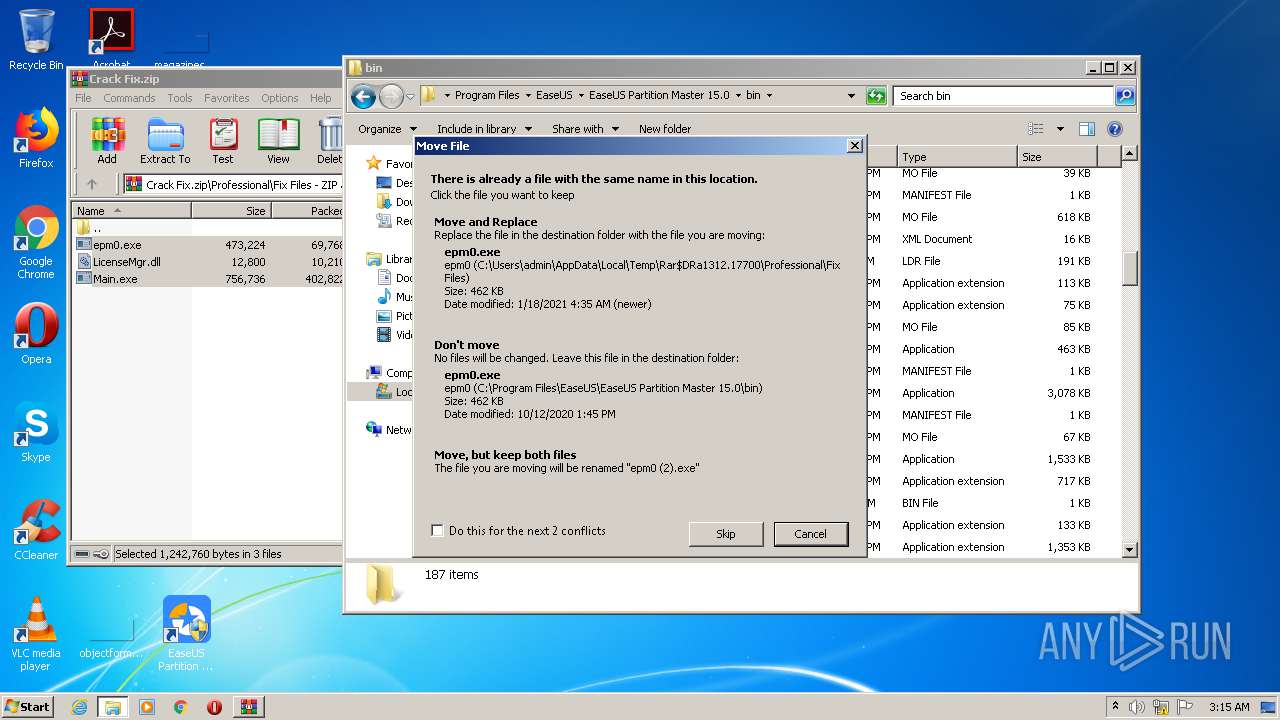
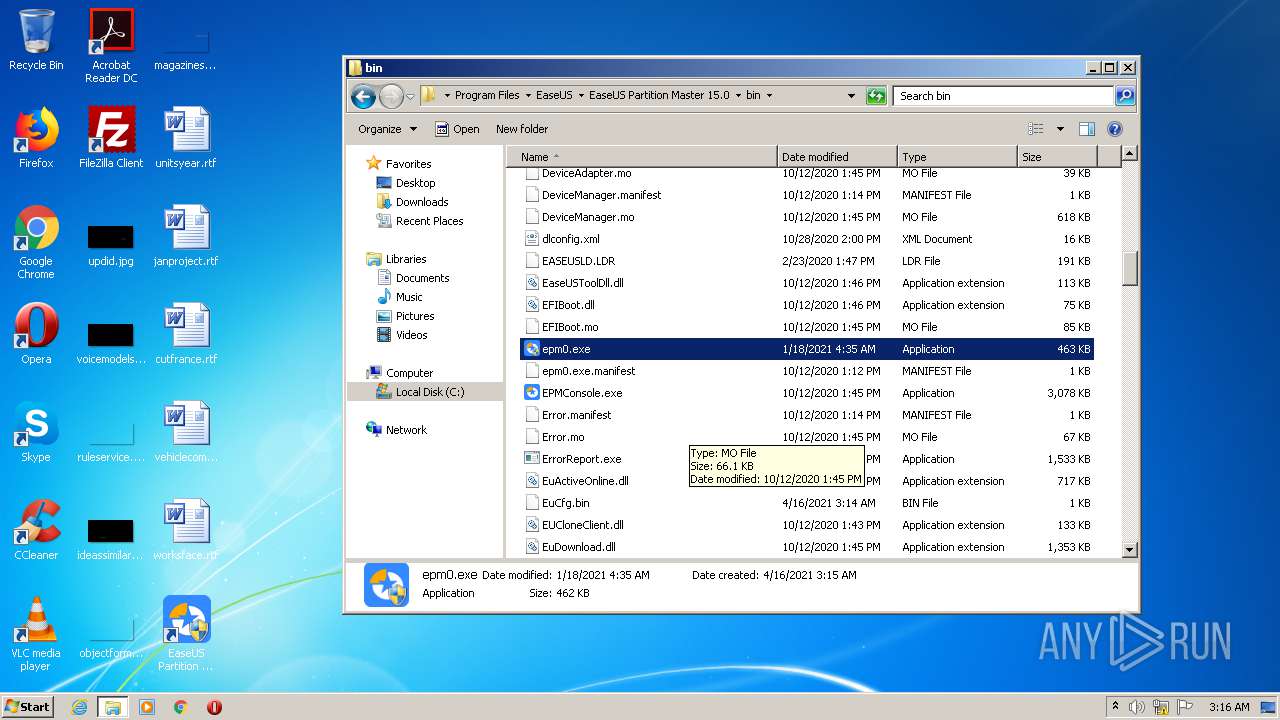
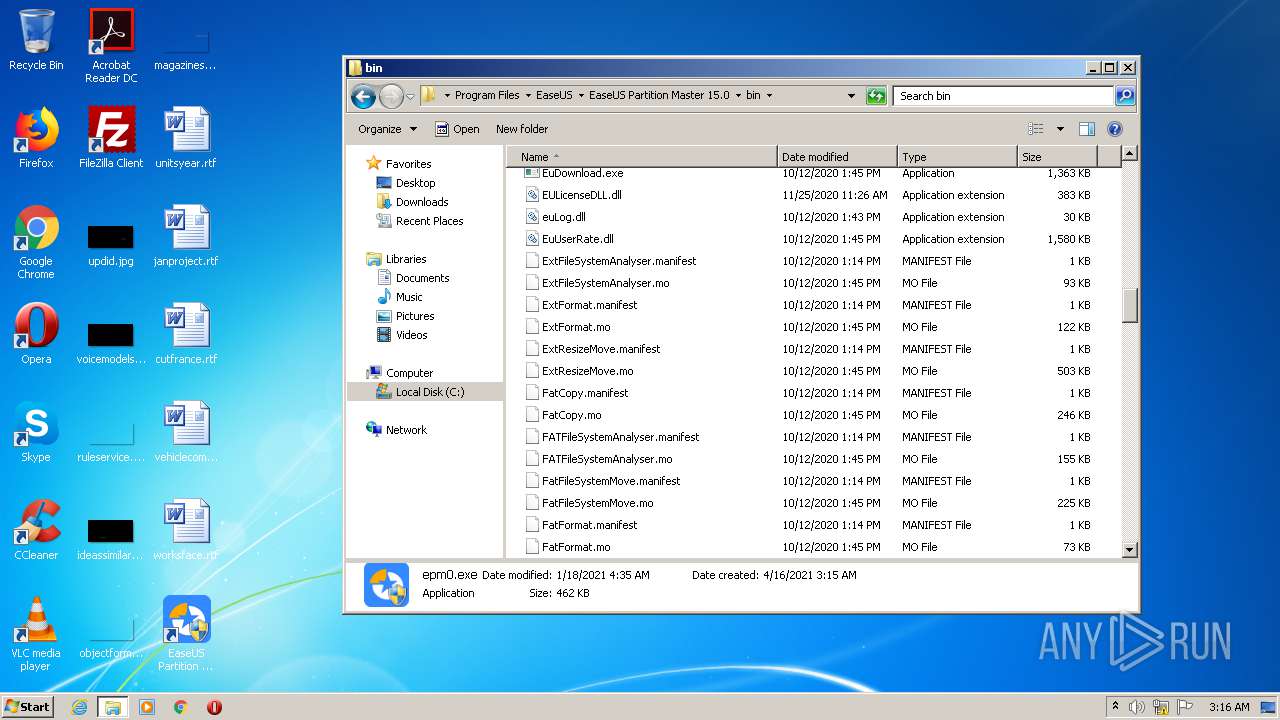
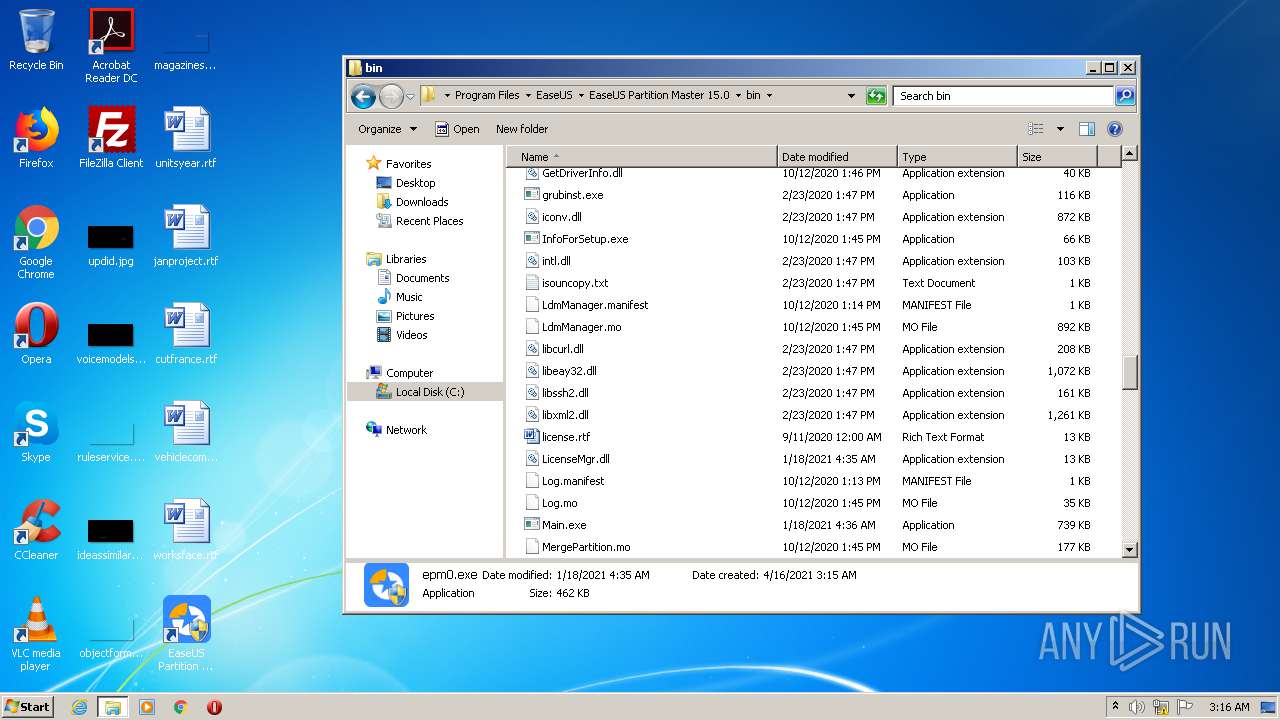
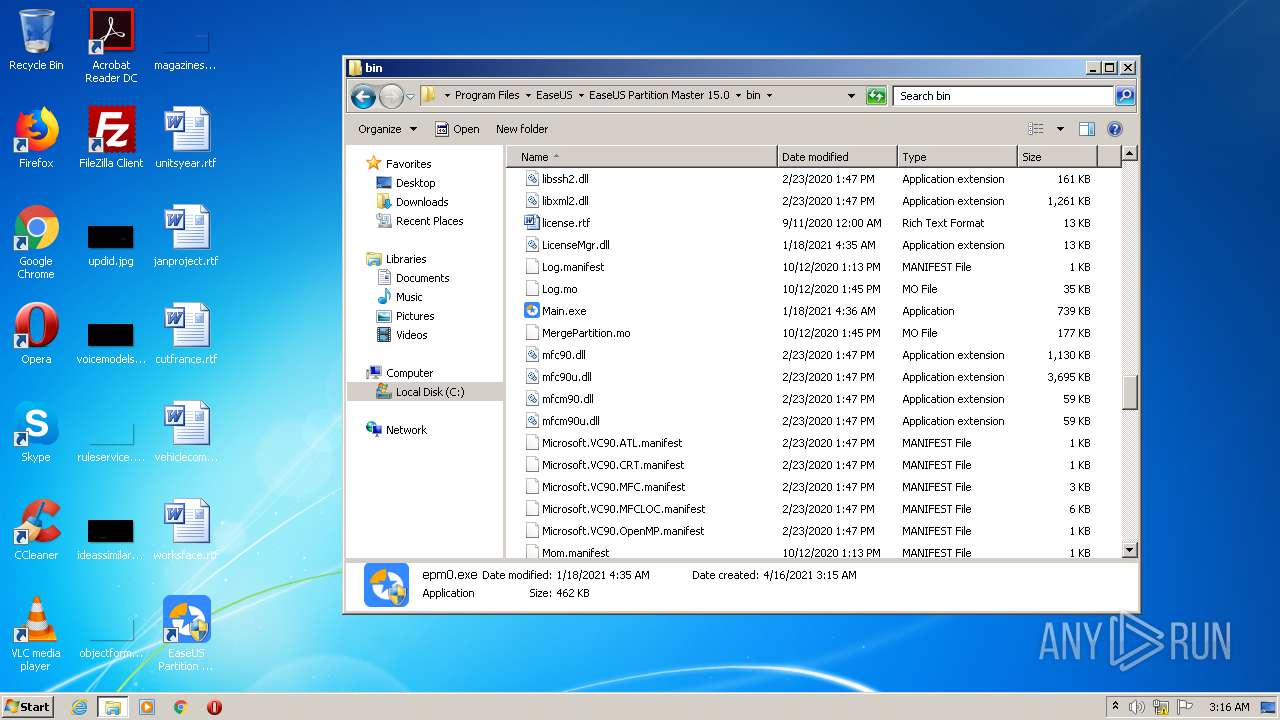
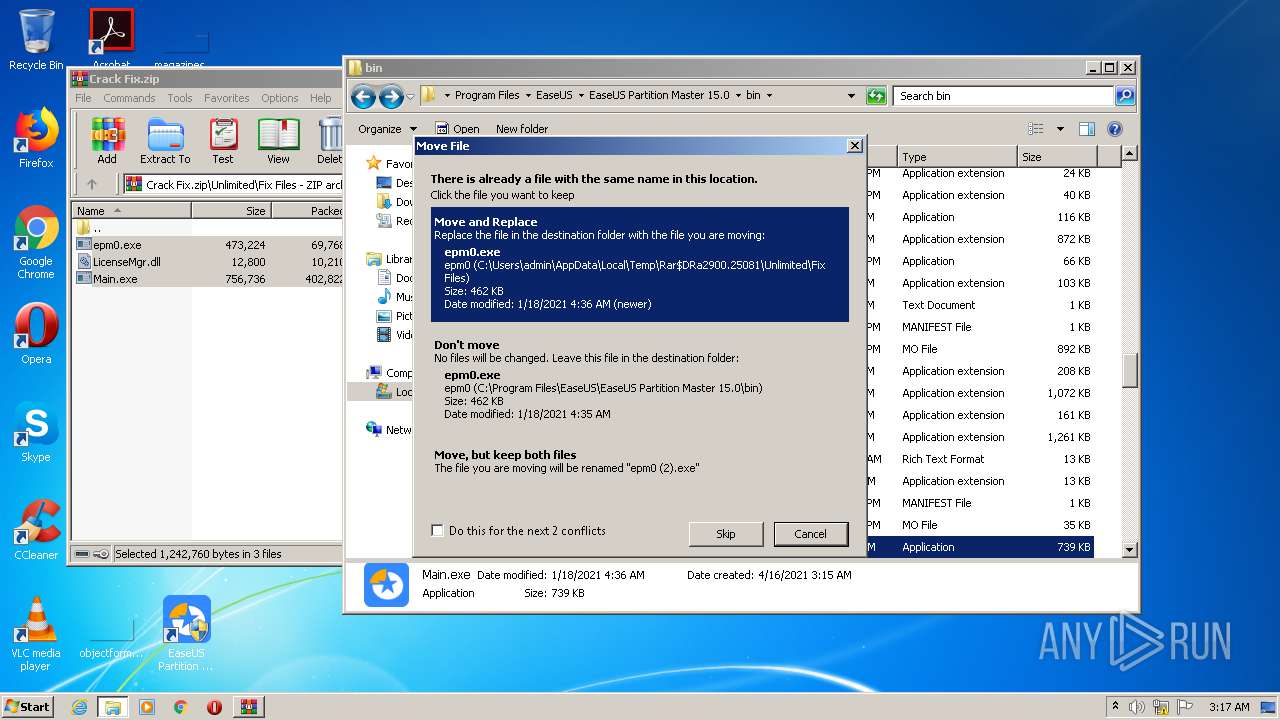
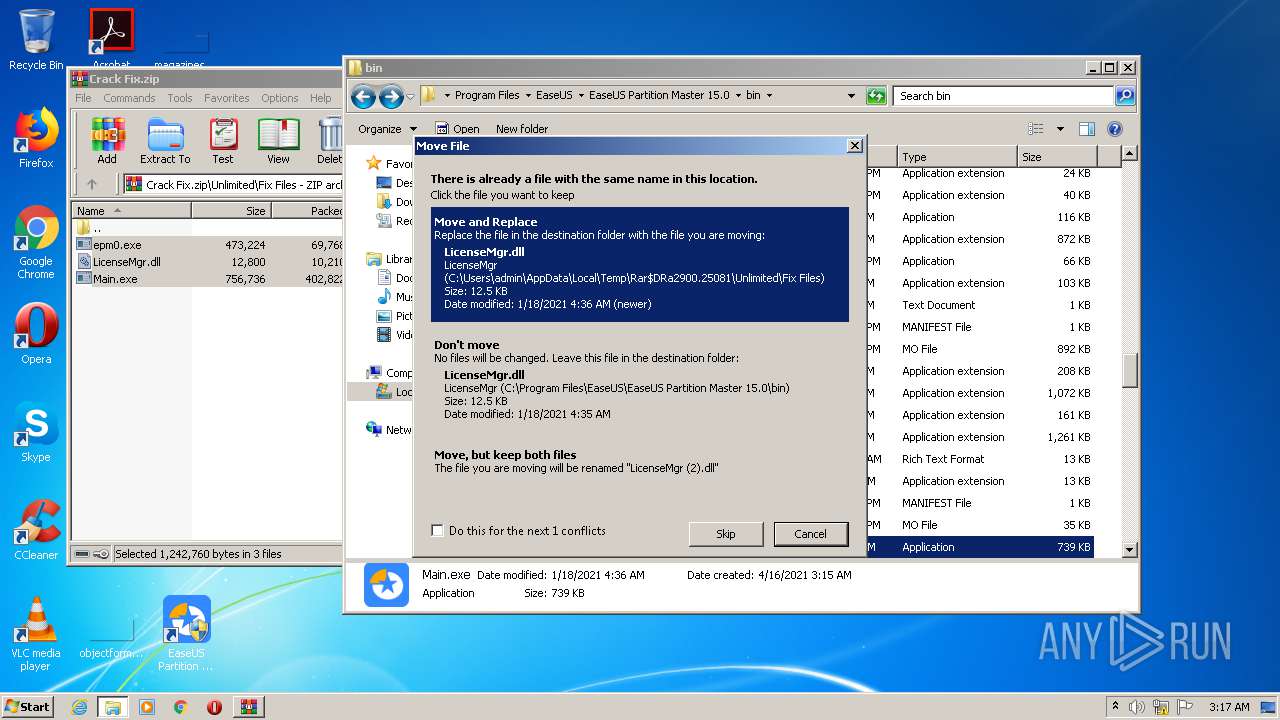
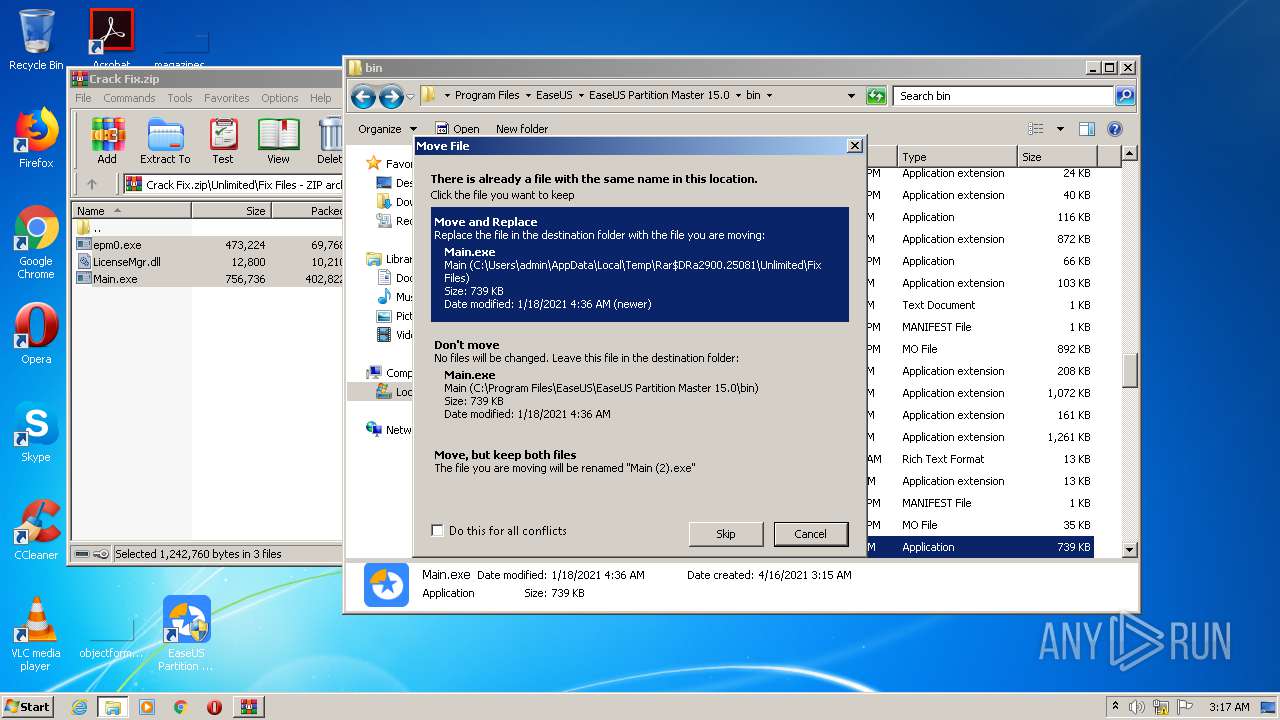
Application was dropped or rewritten from another process
- drvsetup.exe (PID: 2372)
- SetupUE.exe (PID: 2300)
- InfoForSetup.exe (PID: 3980)
- EUinApp.exe (PID: 2424)
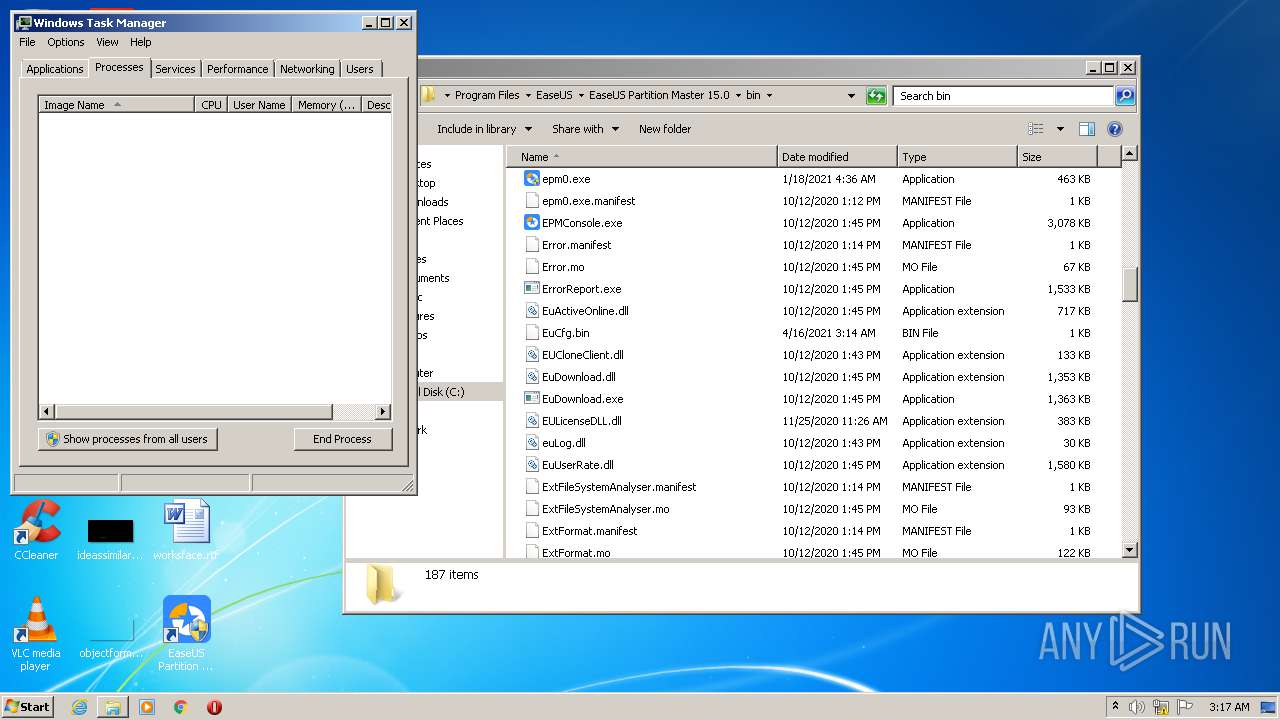
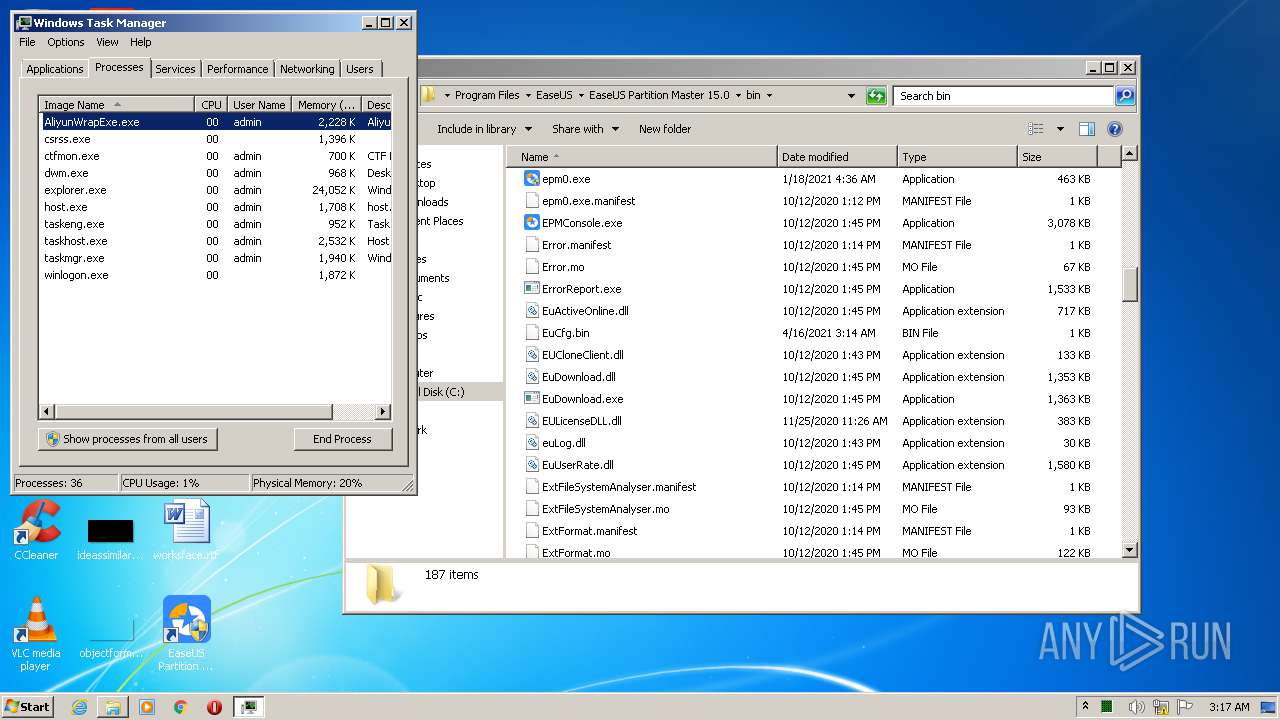
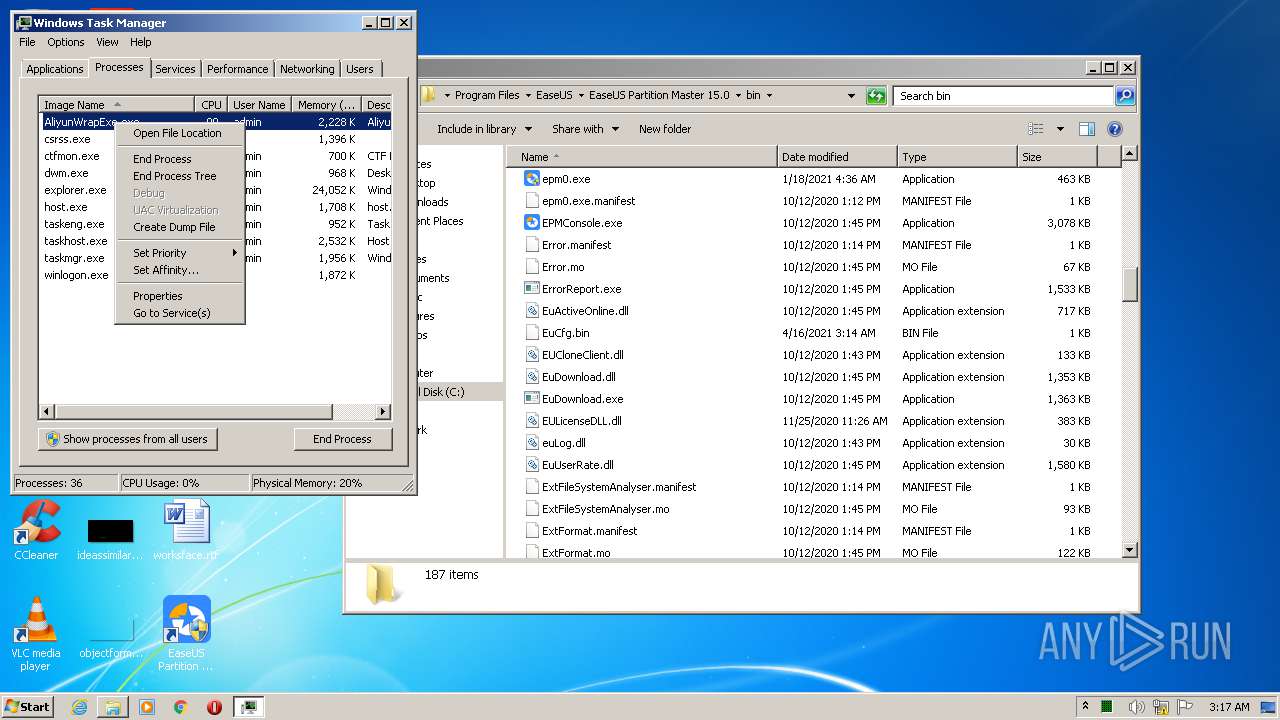
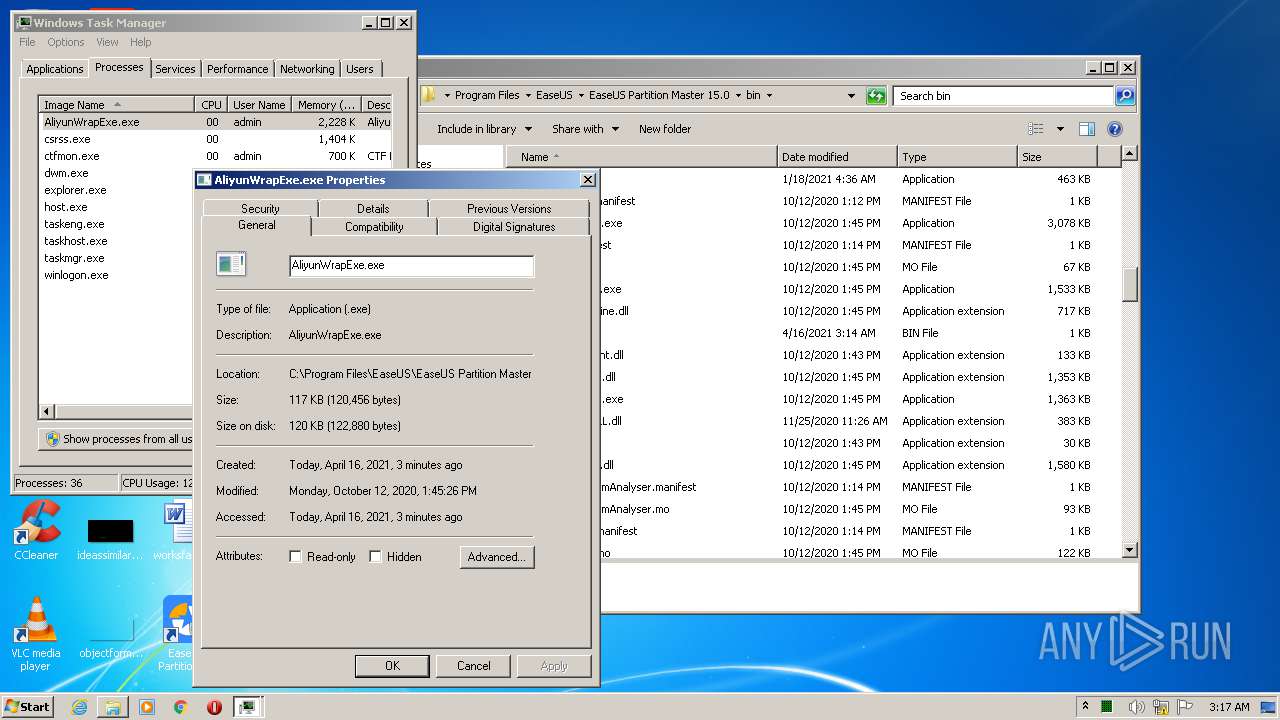
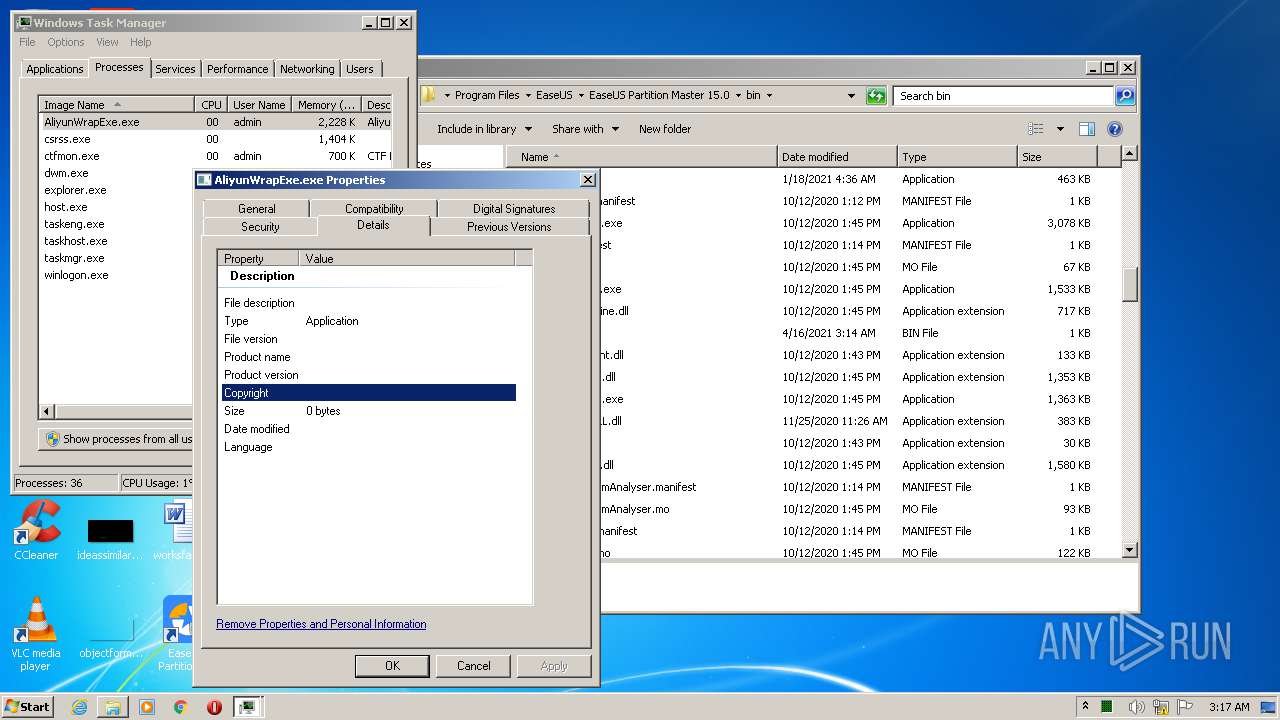
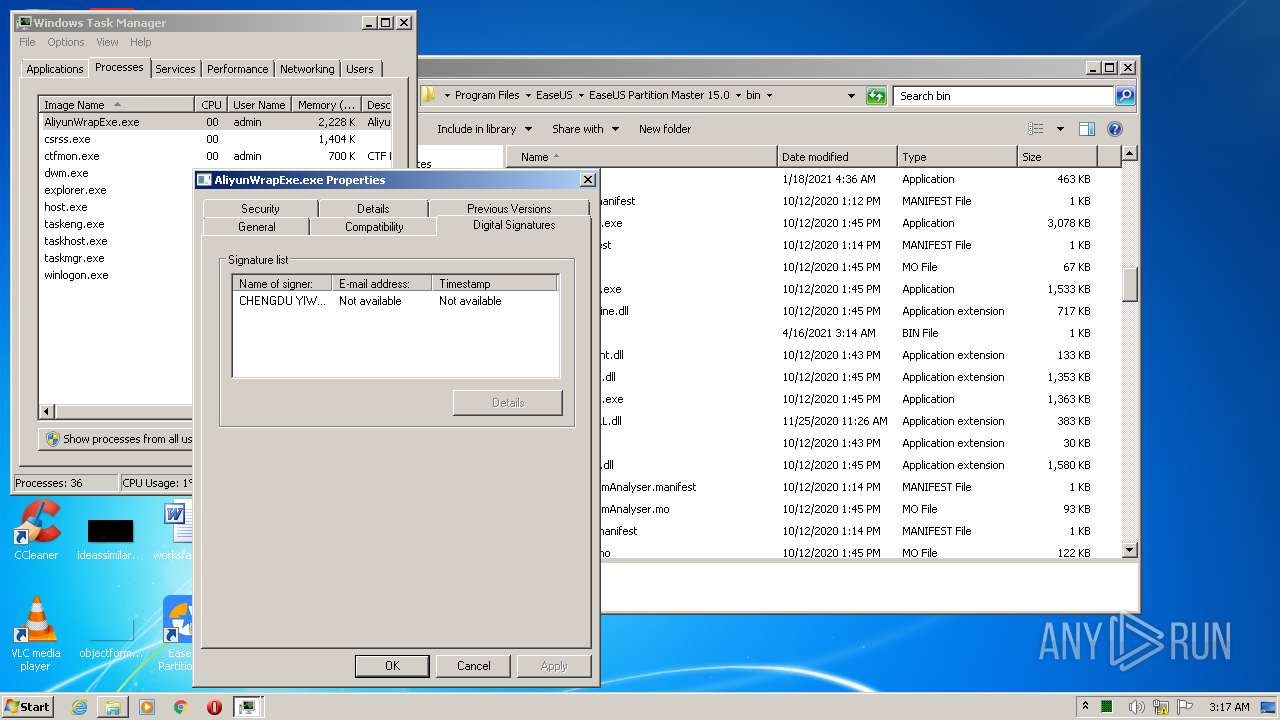
- AliyunWrapExe.Exe (PID: 2552)
- InfoForSetup.exe (PID: 2068)
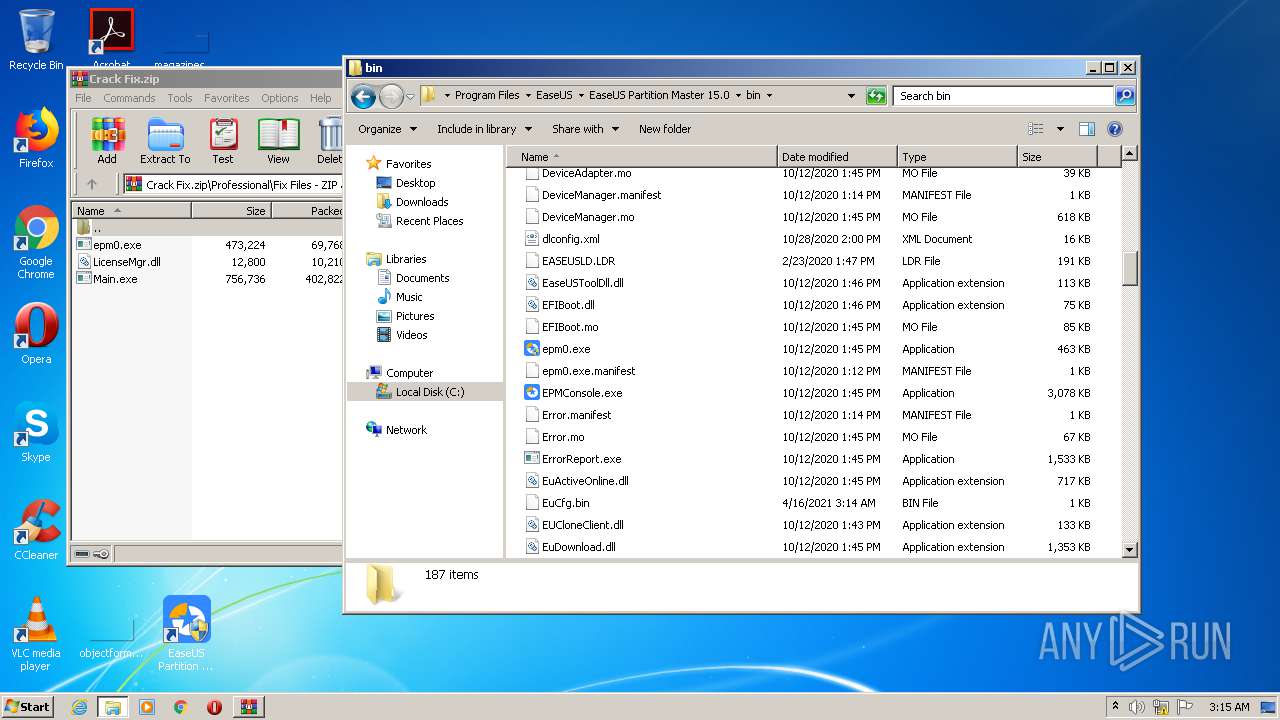
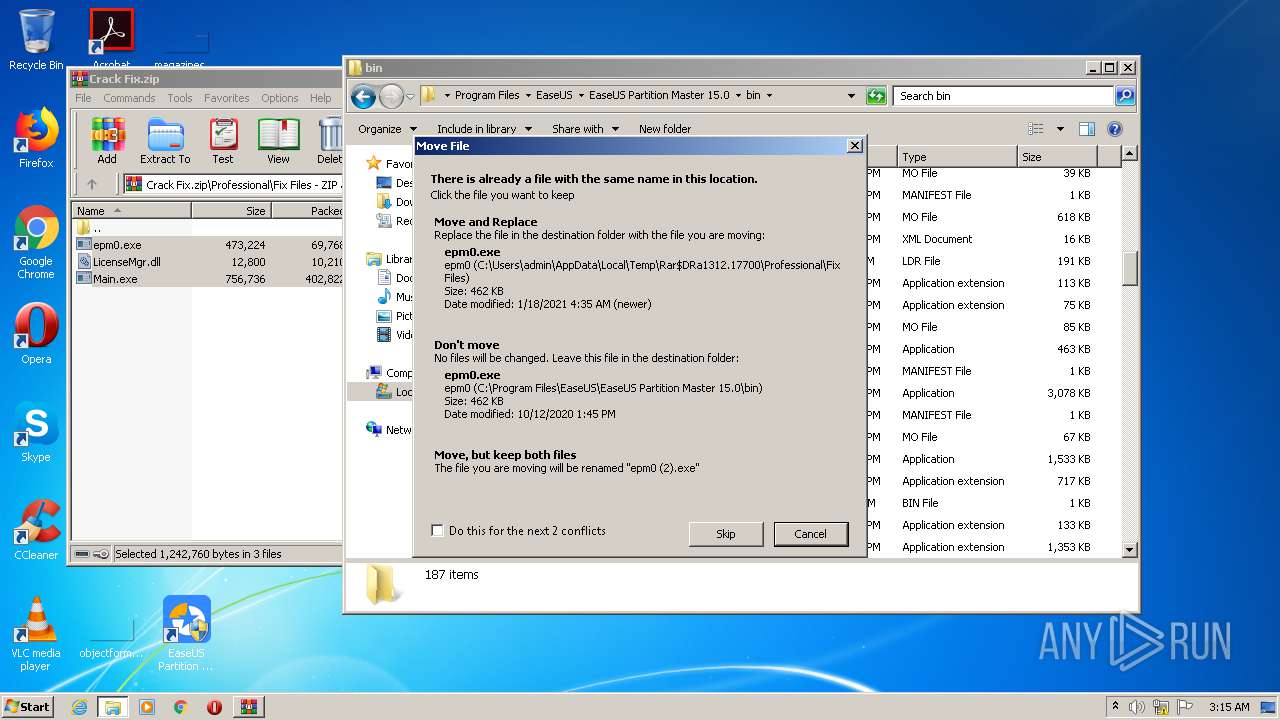
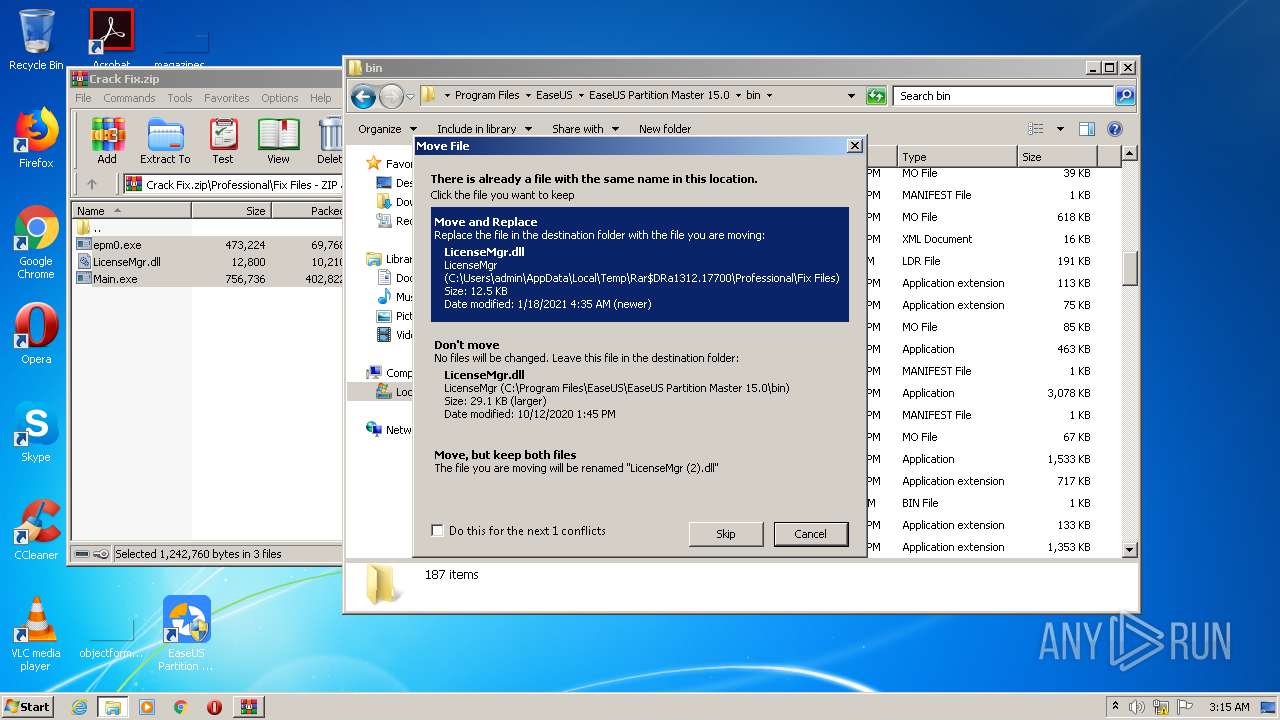
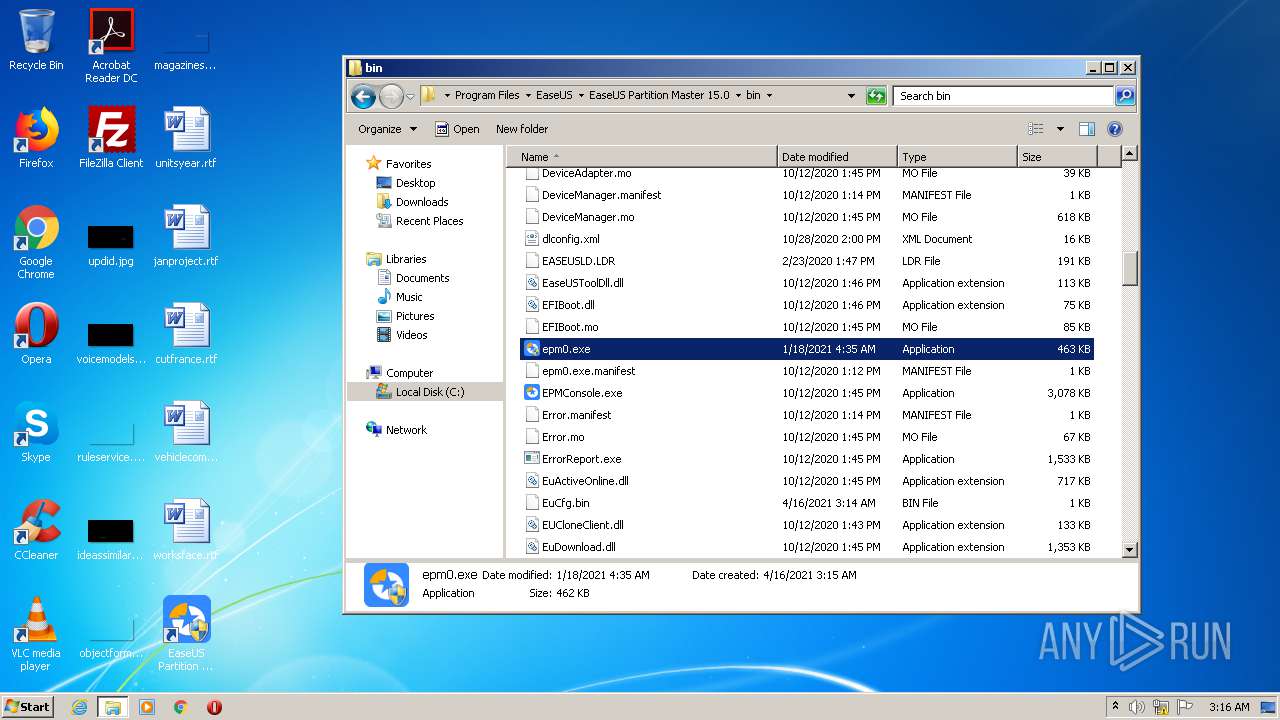
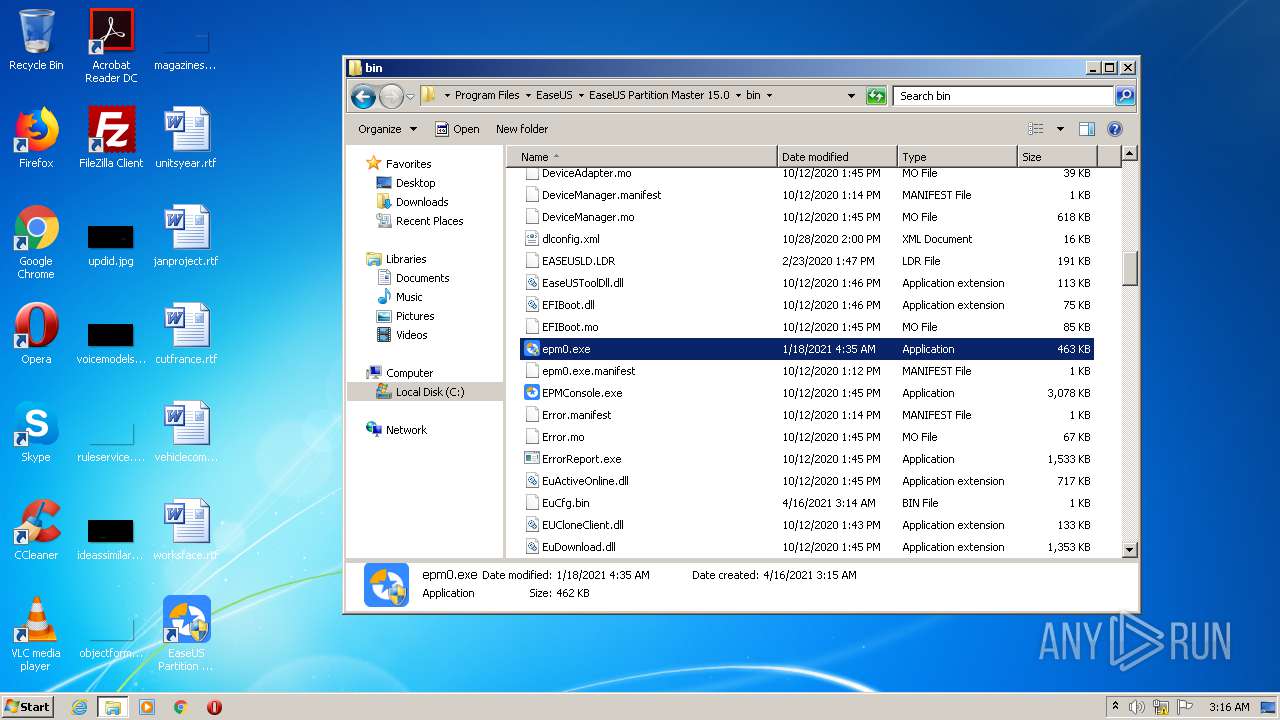
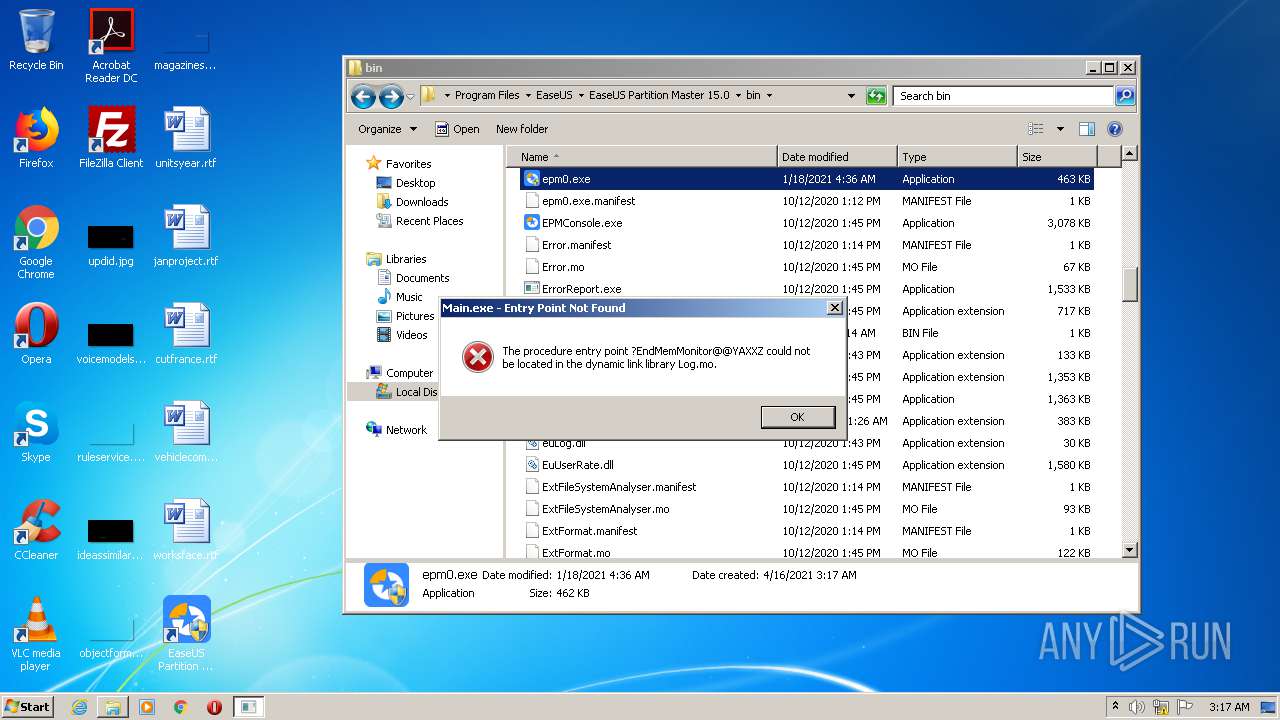
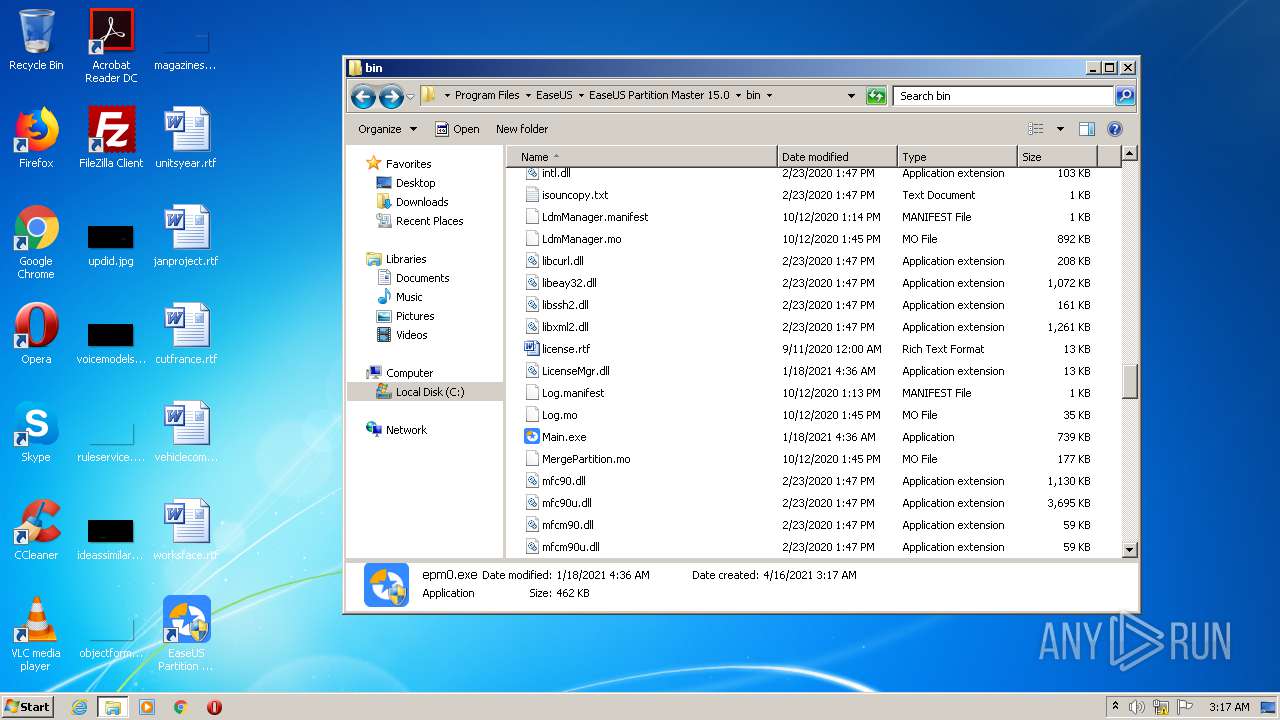
- epm0.exe (PID: 2848)
- epm0.exe (PID: 1996)
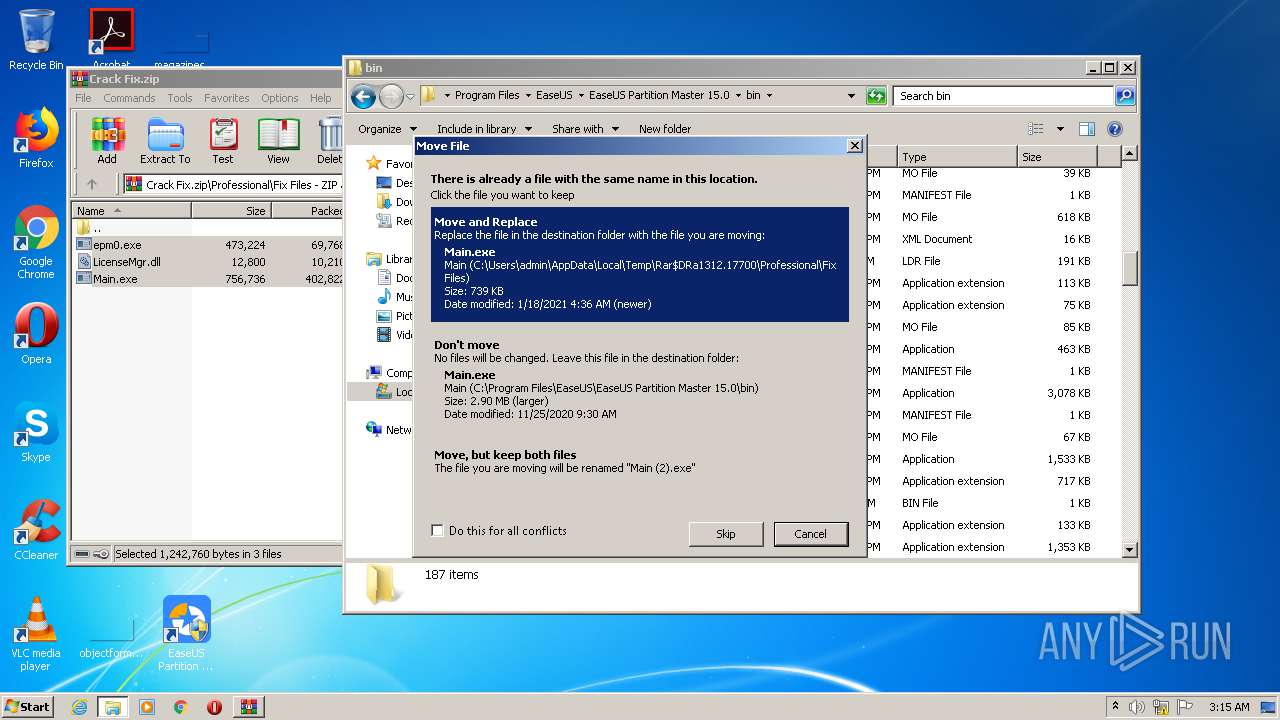
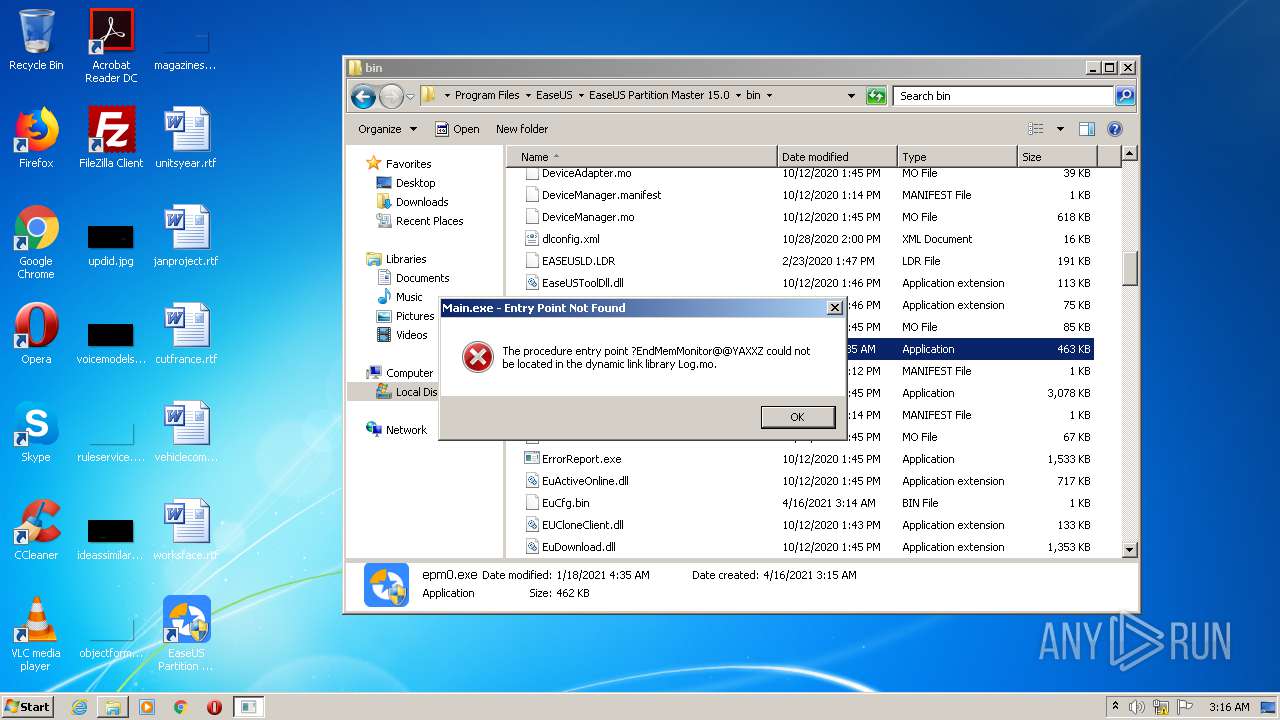
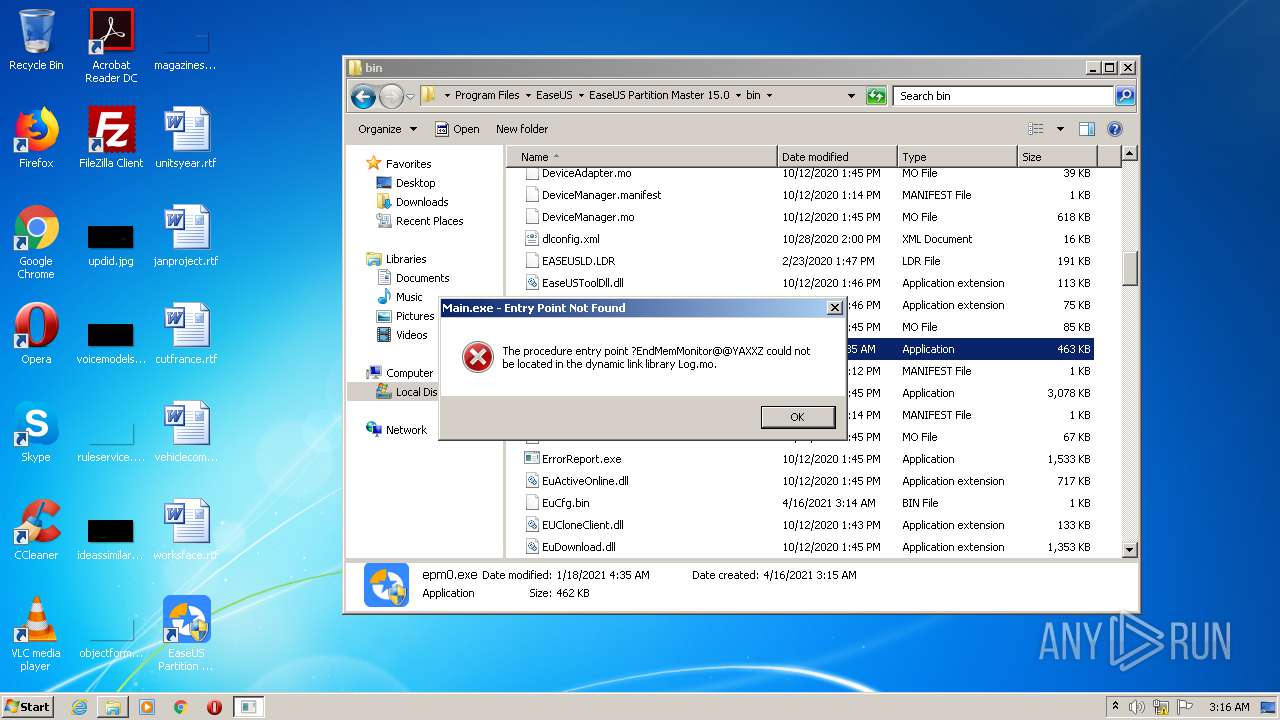
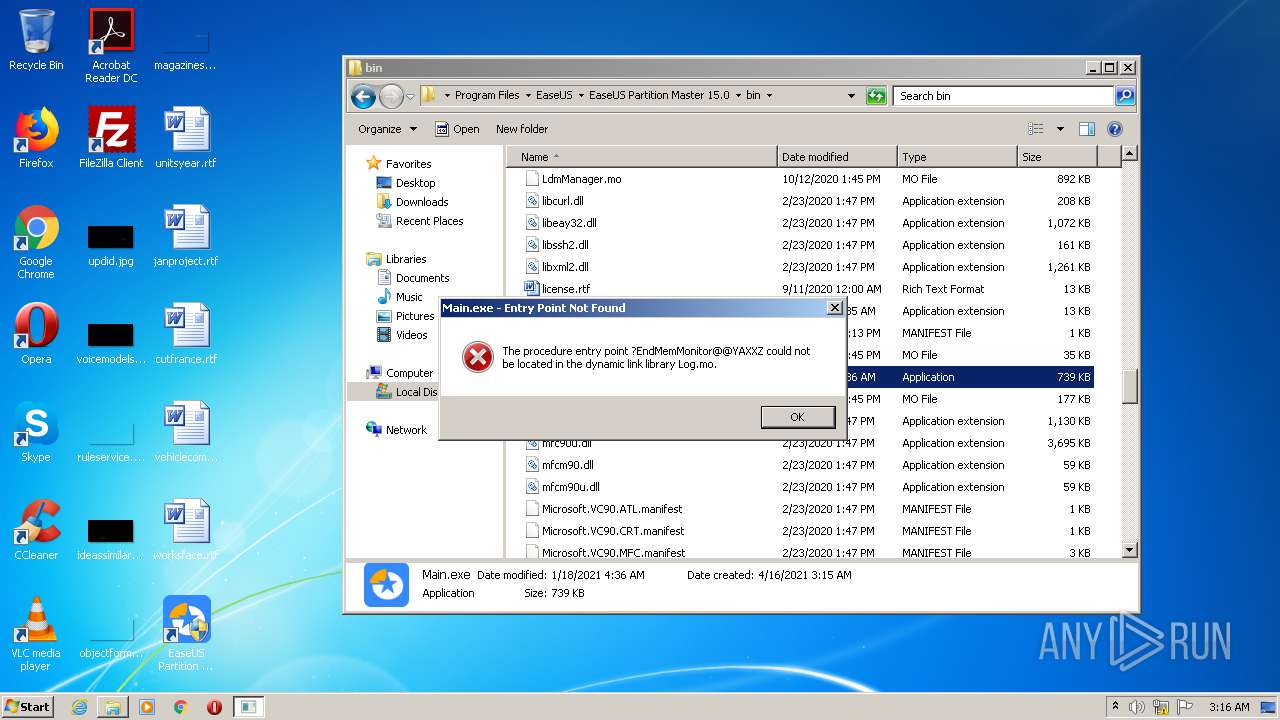
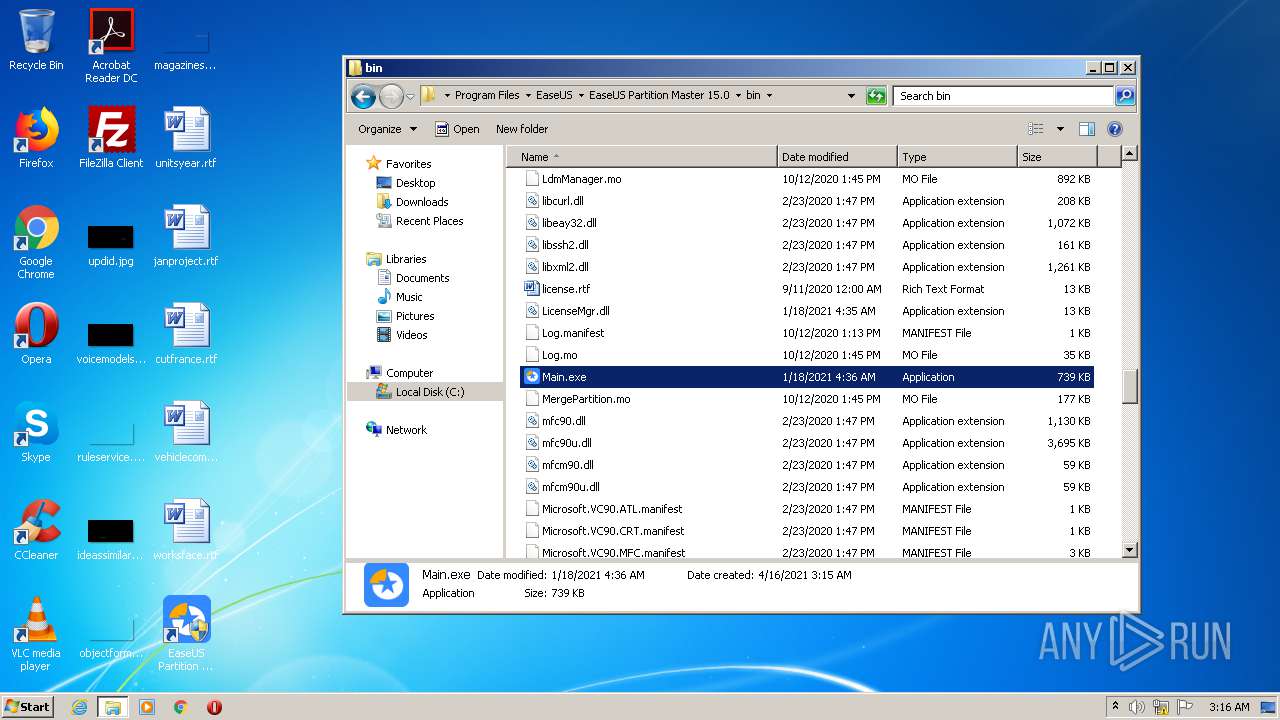
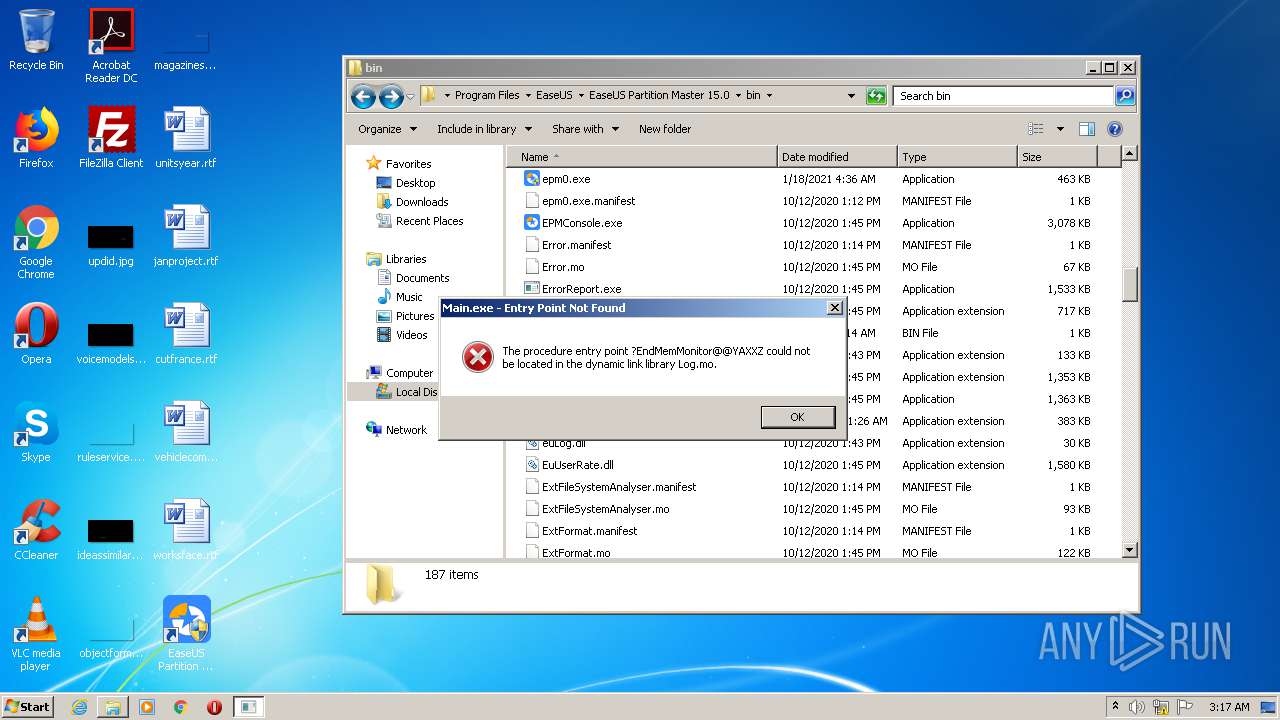
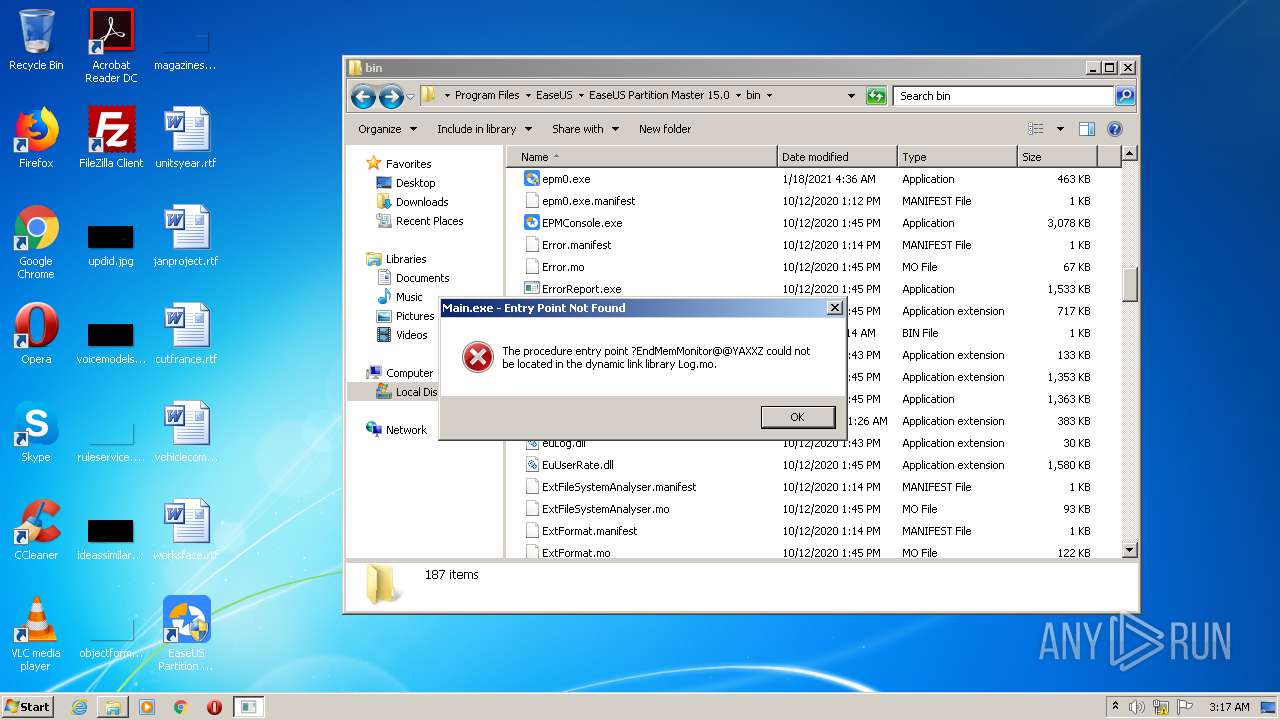
- Main.exe (PID: 2700)
- epm0.exe (PID: 1688)
- epm0.exe (PID: 3728)
- setupempdrv03.exe (PID: 1676)
- epm0.exe (PID: 2608)
- Main.exe (PID: 3940)
- epm0.exe (PID: 2792)
- epm0.exe (PID: 3284)
- epm0.exe (PID: 2724)
- Main.exe (PID: 3136)
- Main.exe (PID: 3152)
- Main.exe (PID: 2688)
- epm0.exe (PID: 316)
- Main.exe (PID: 2340)
- Main.exe (PID: 1636)
- epm0.exe (PID: 1700)
- epm0.exe (PID: 3488)
- epm0.exe (PID: 2072)
- epm0.exe (PID: 2172)
- epm0.exe (PID: 1780)
- Main.exe (PID: 2120)
Loads dropped or rewritten executable
- InfoForSetup.exe (PID: 3980)
- InfoForSetup.exe (PID: 2068)
- AliyunWrapExe.Exe (PID: 2552)
- explorer.exe (PID: 656)
- Main.exe (PID: 2700)
- epm0.exe (PID: 2848)
- epm0.exe (PID: 2792)
- Main.exe (PID: 3940)
- epm0.exe (PID: 2724)
- Main.exe (PID: 3136)
- epm0.exe (PID: 3728)
- Main.exe (PID: 2688)
- Main.exe (PID: 2120)
- epm0.exe (PID: 316)
- Main.exe (PID: 3152)
- Main.exe (PID: 1636)
- epm0.exe (PID: 1700)
- epm0.exe (PID: 2072)
- Main.exe (PID: 2340)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1548)
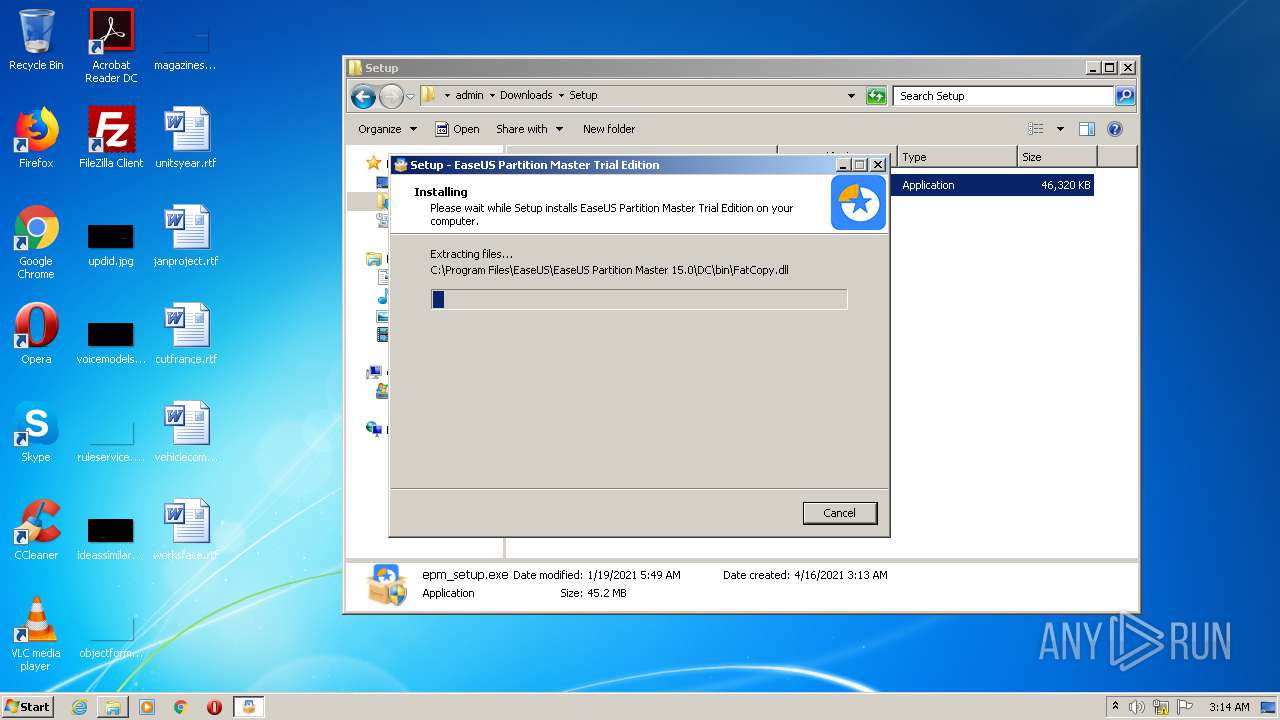
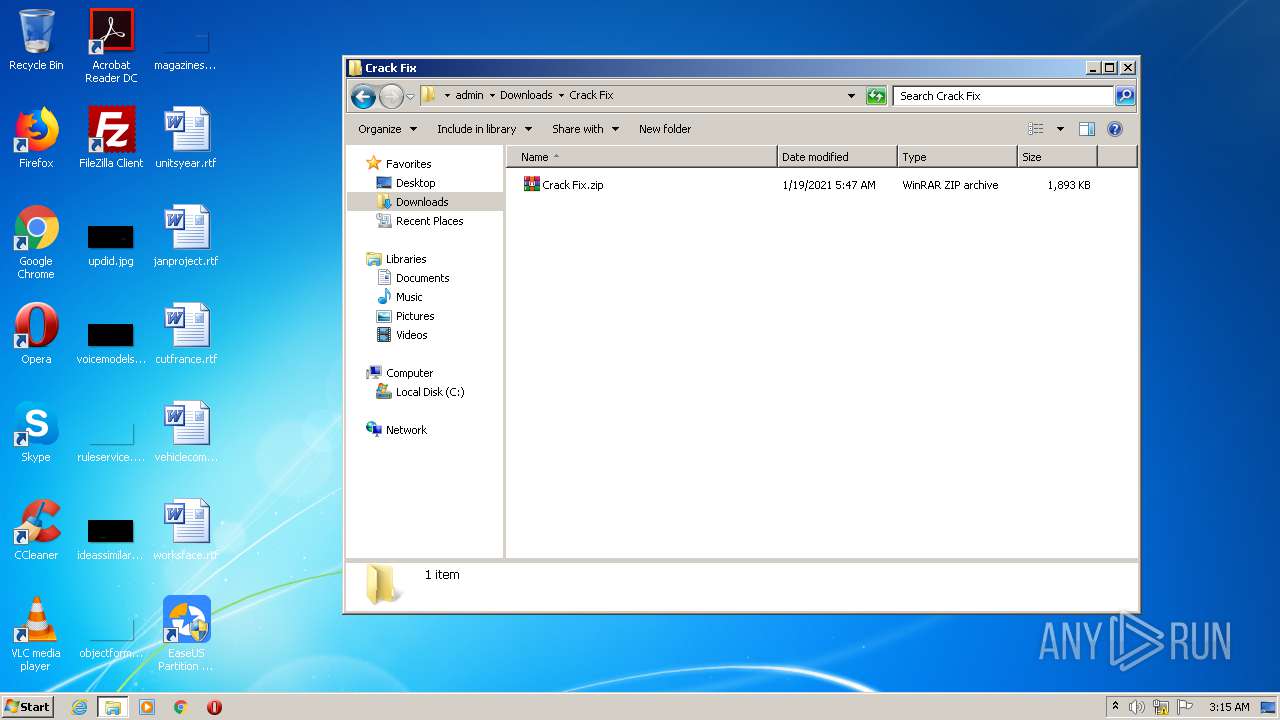
Executable content was dropped or overwritten
- epm_setup.exe (PID: 3632)
- epm_setup.tmp (PID: 3884)
- drvsetup.exe (PID: 2372)
- DllHost.exe (PID: 3768)
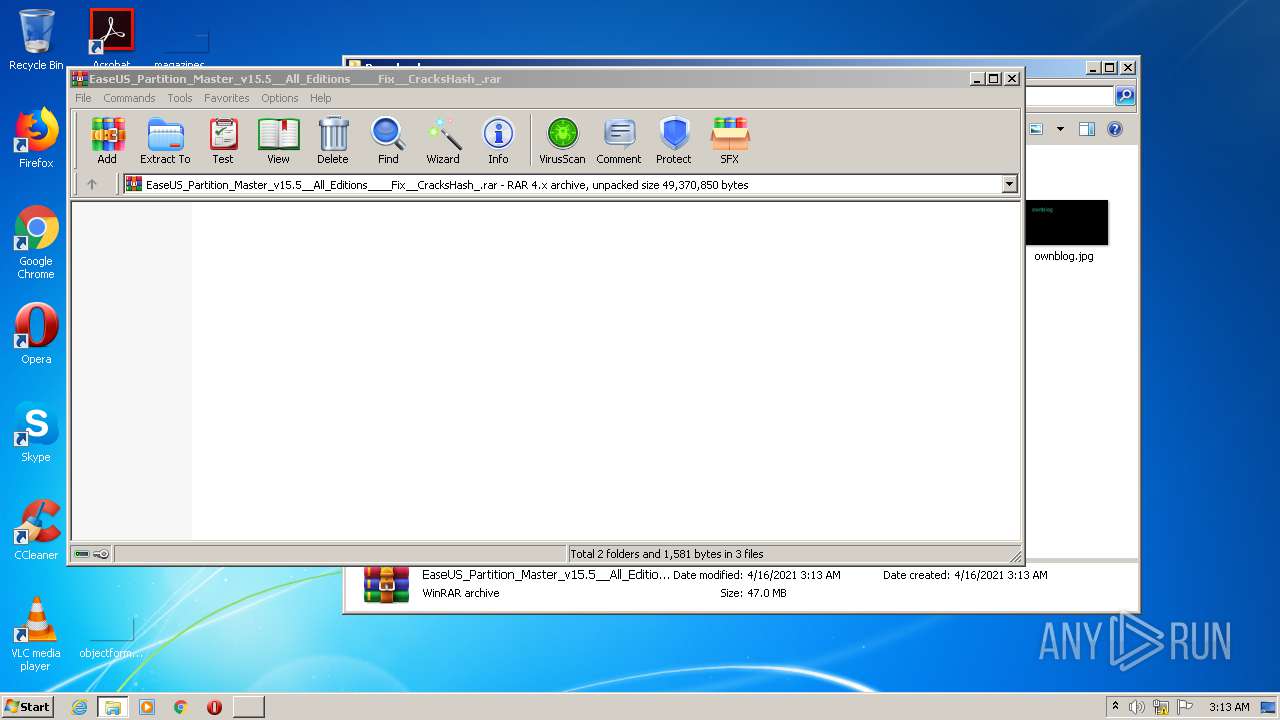
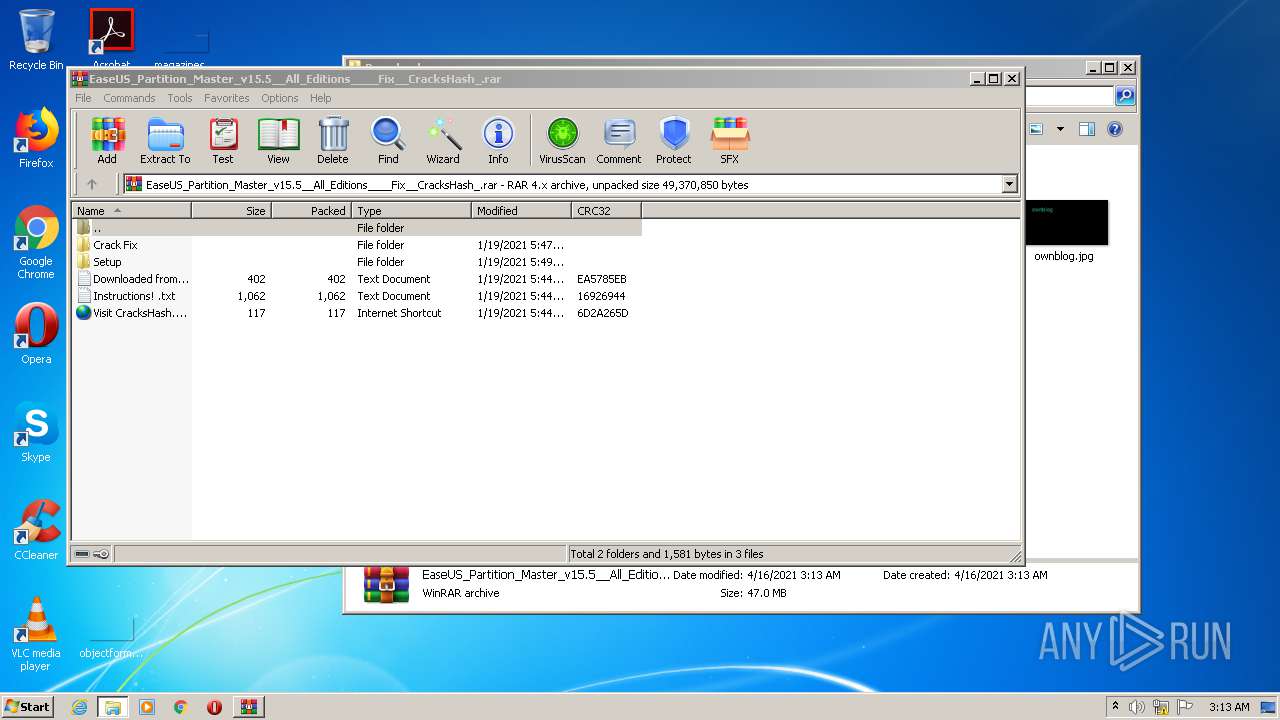
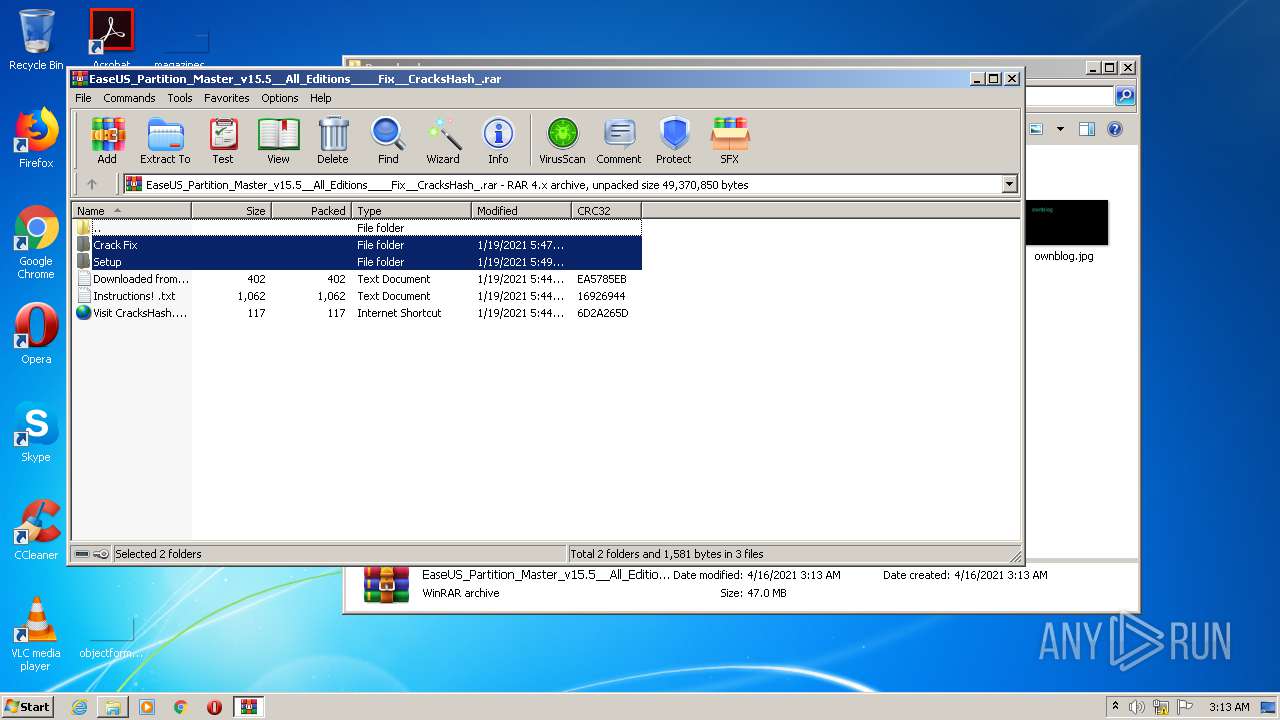
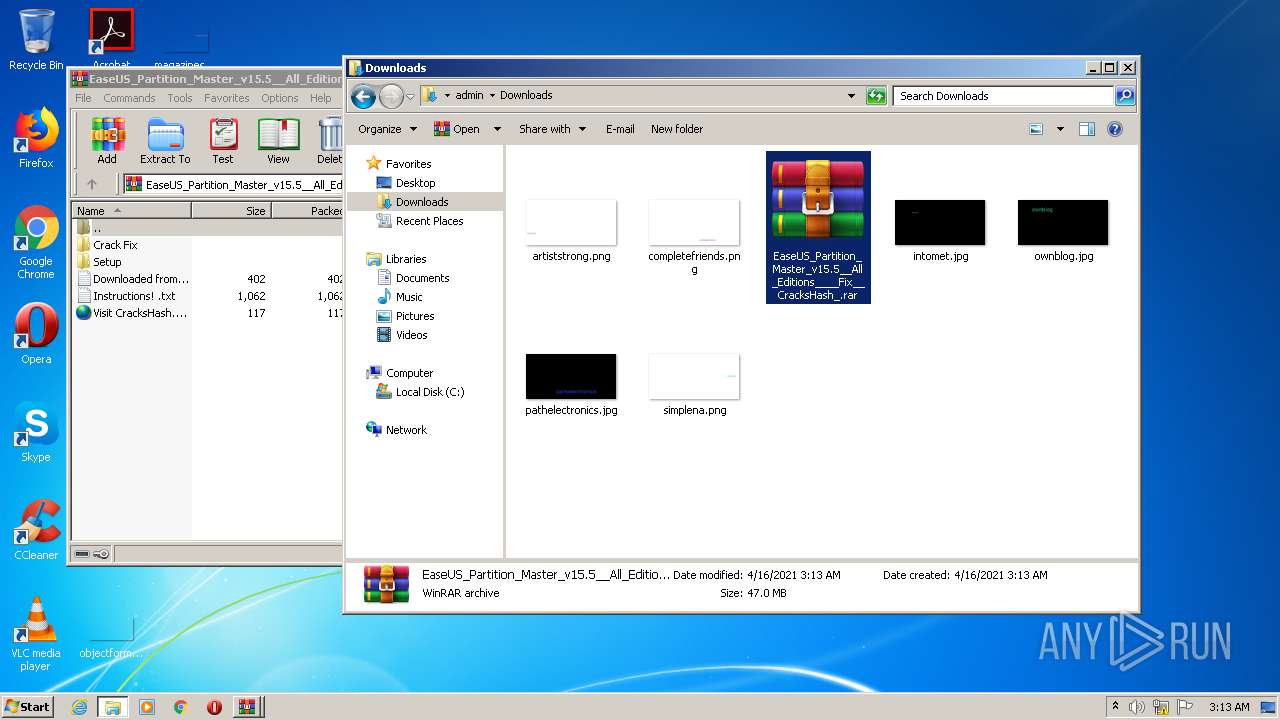
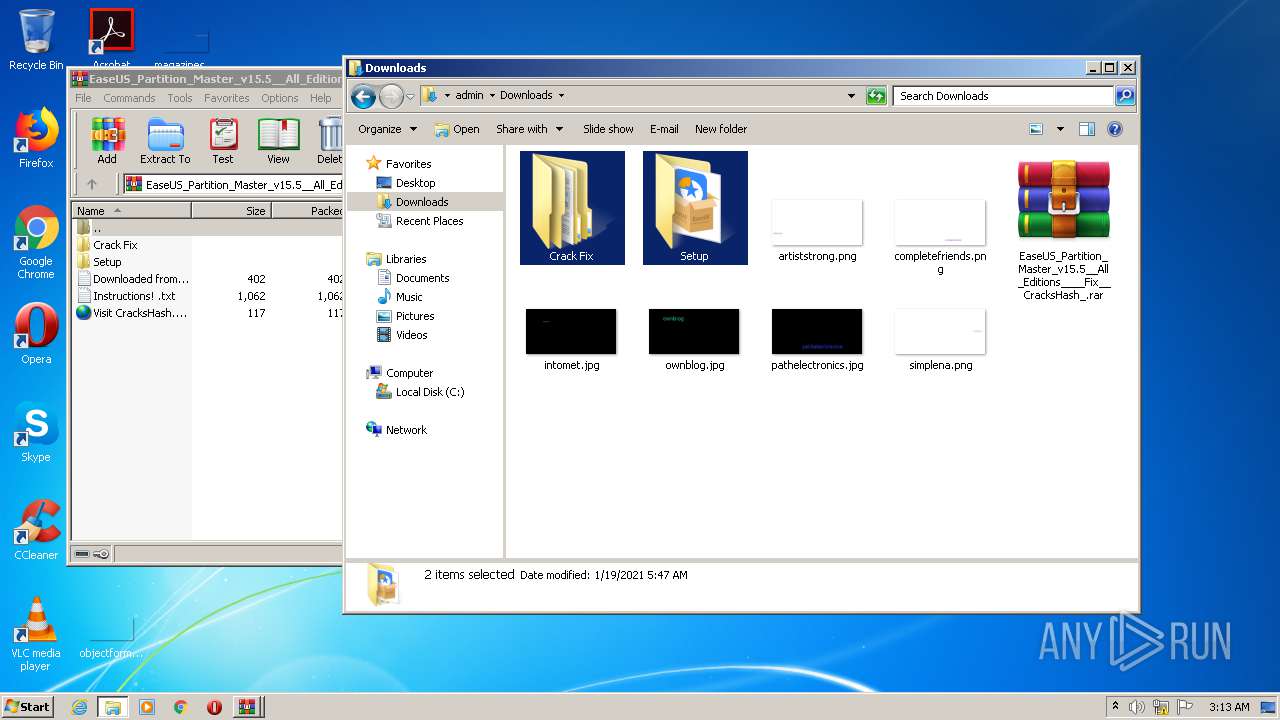
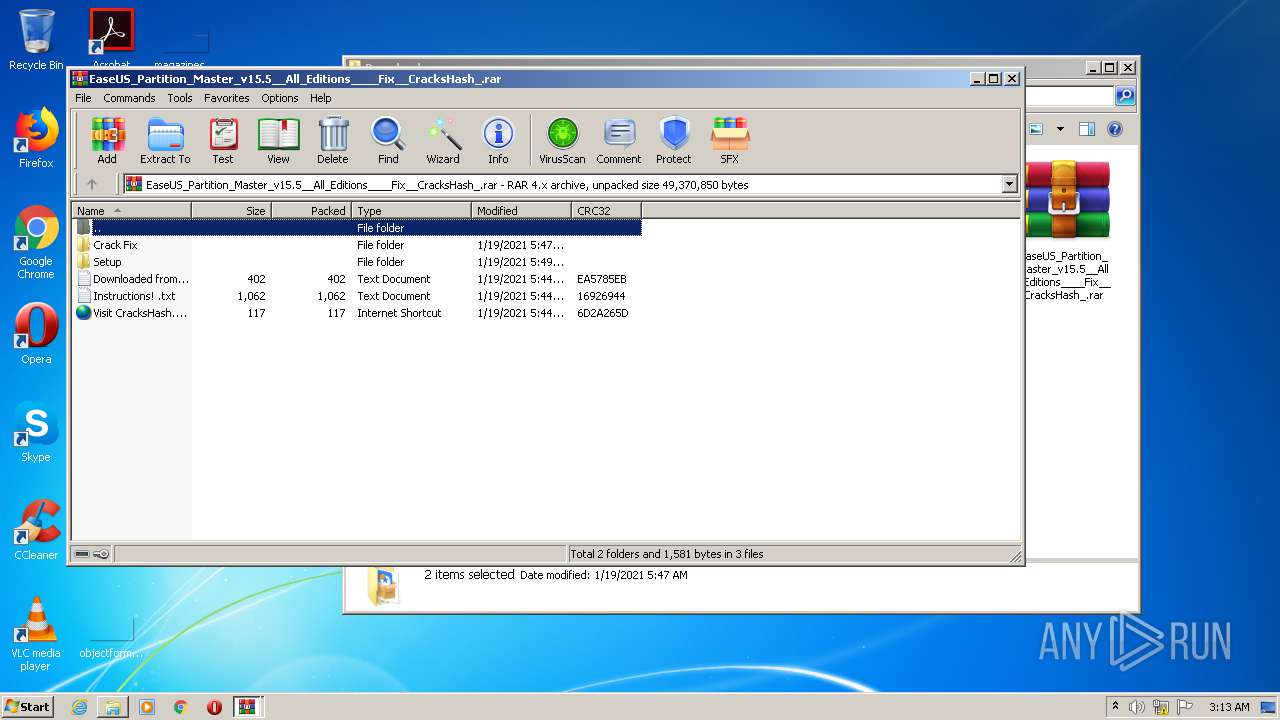
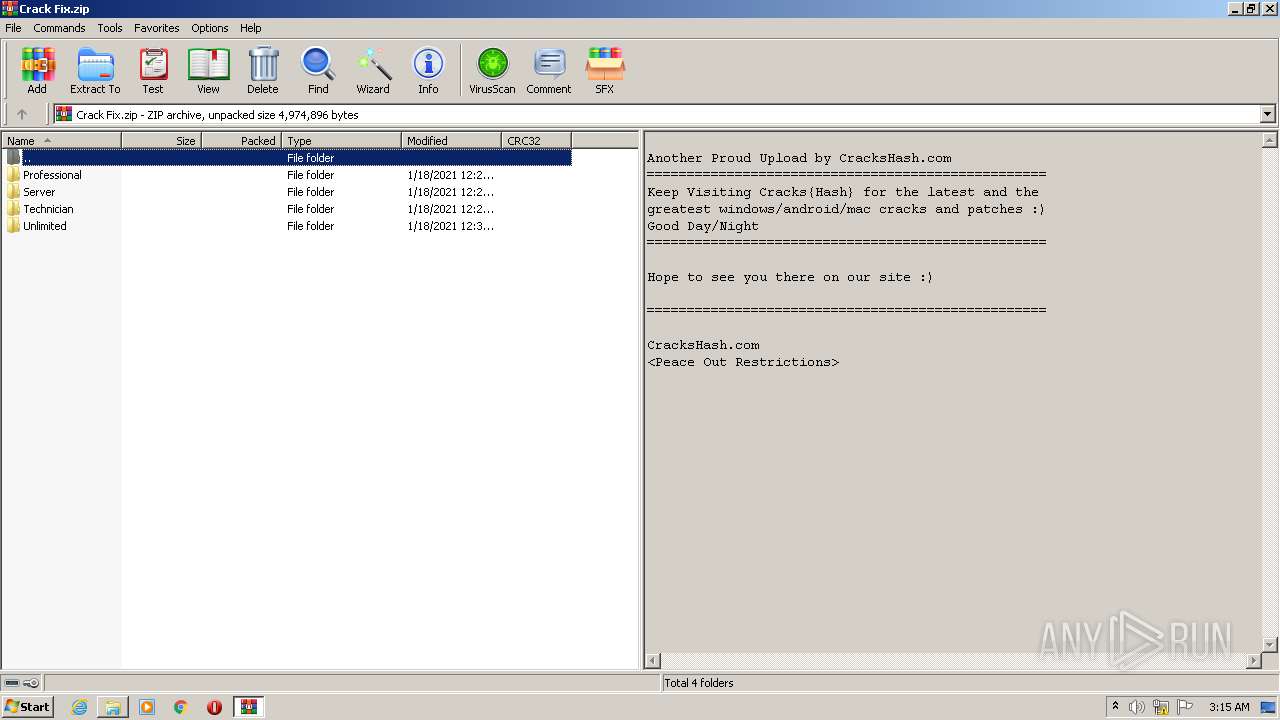
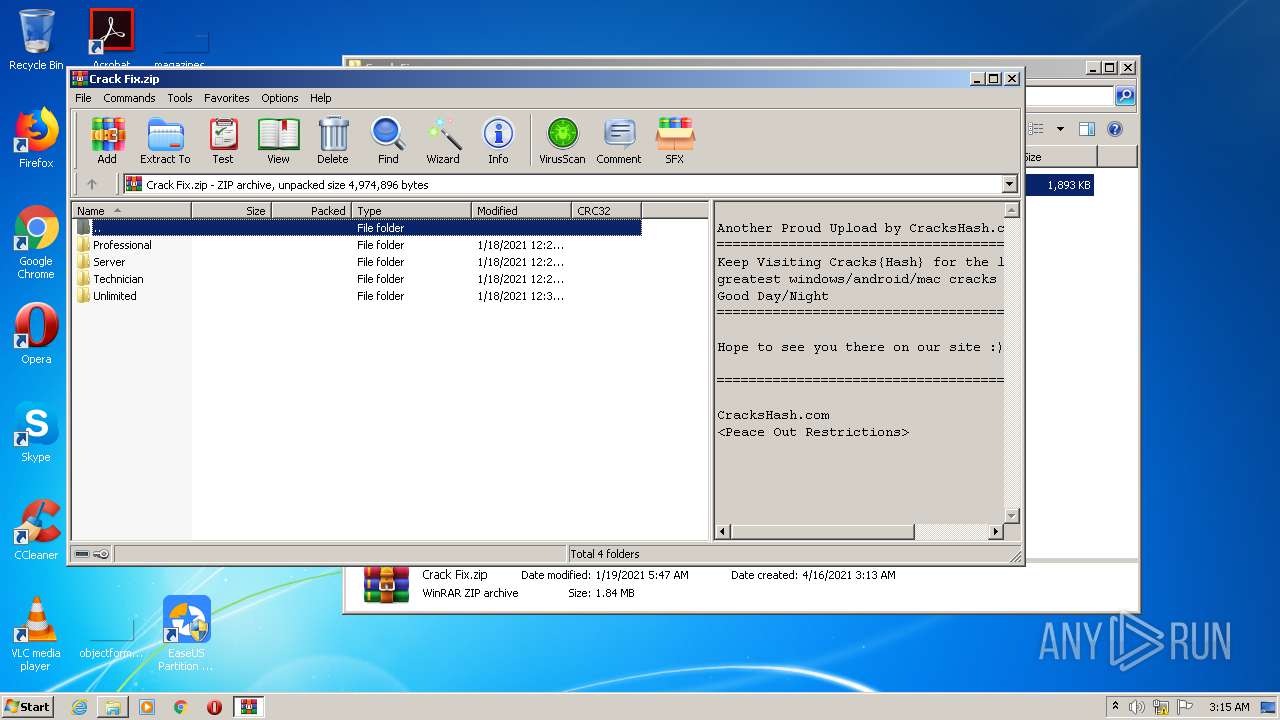
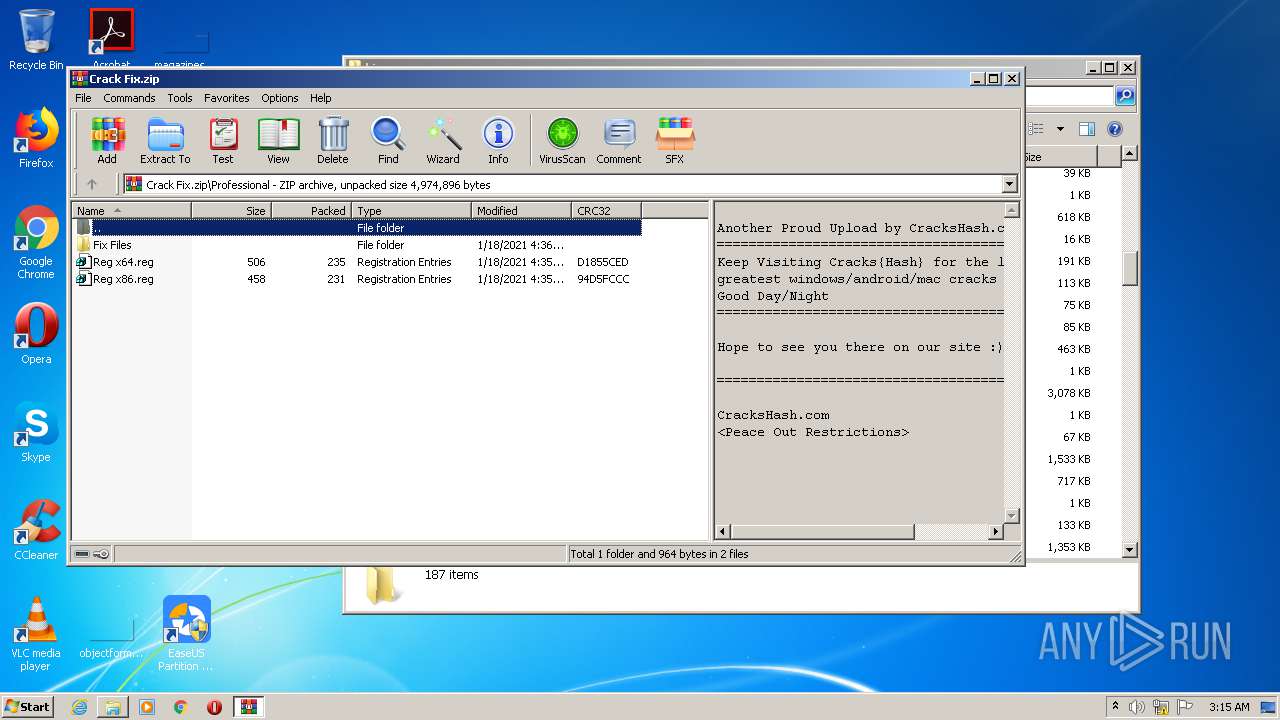
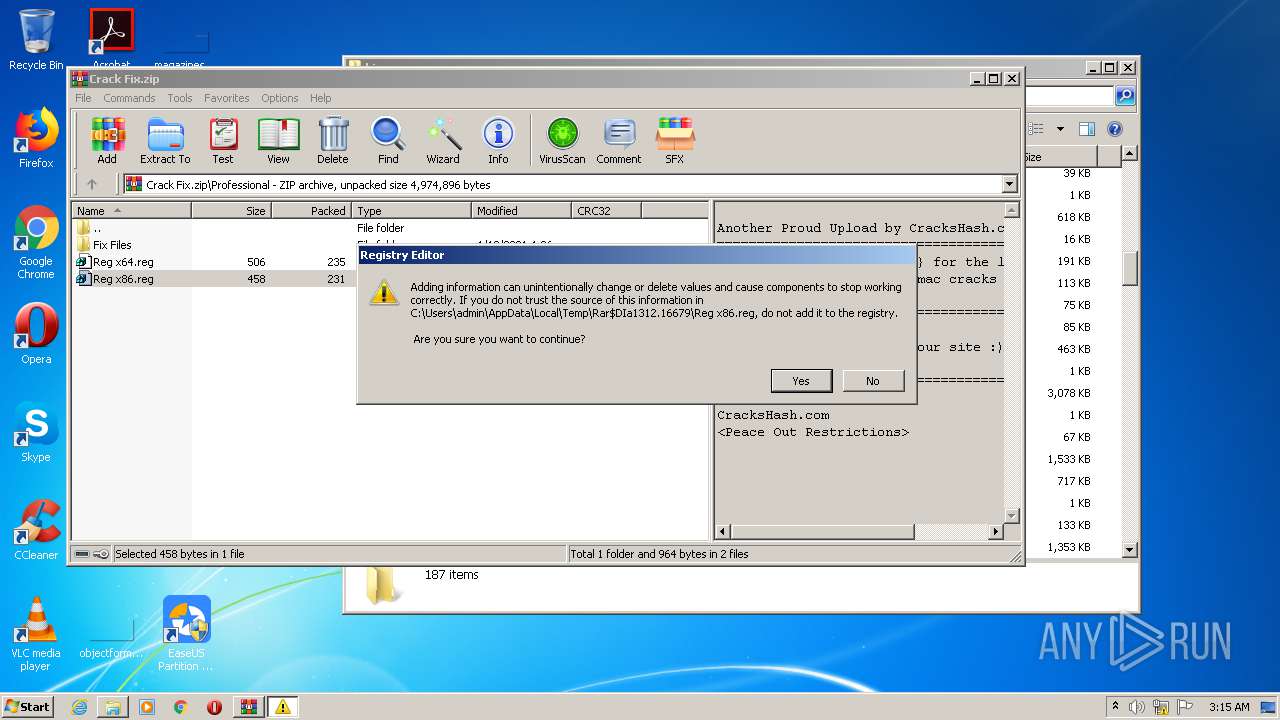
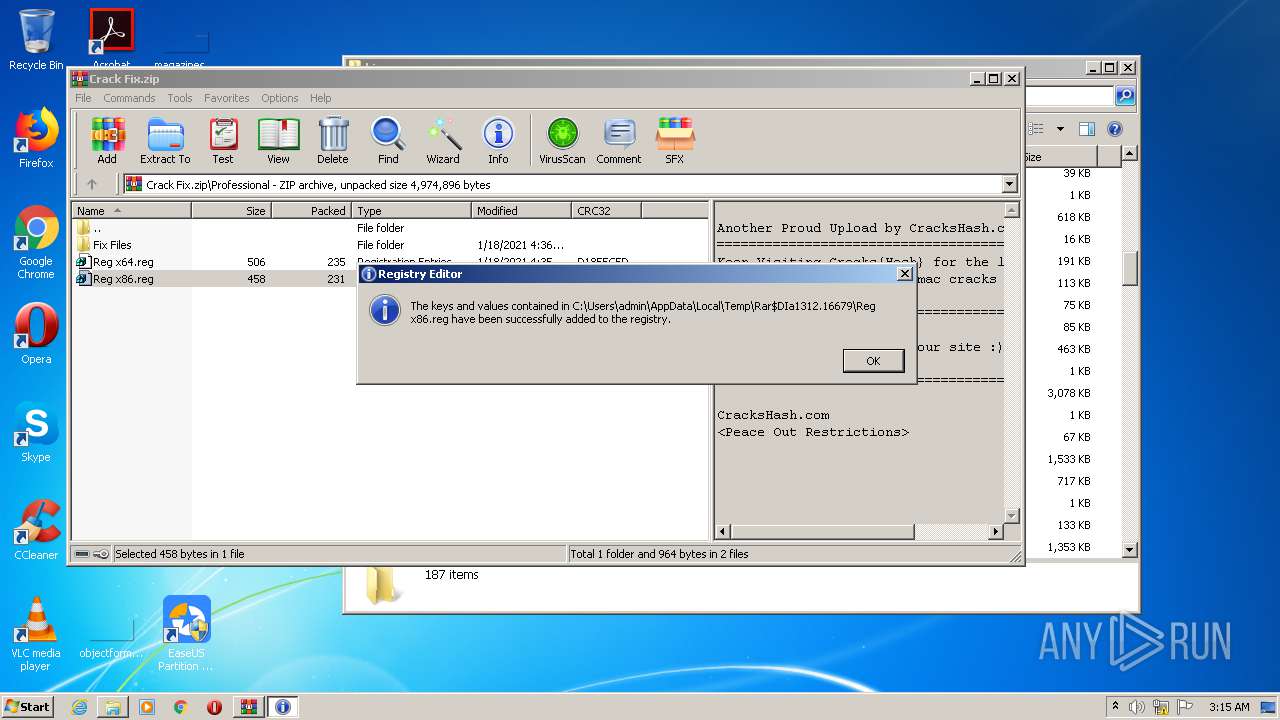
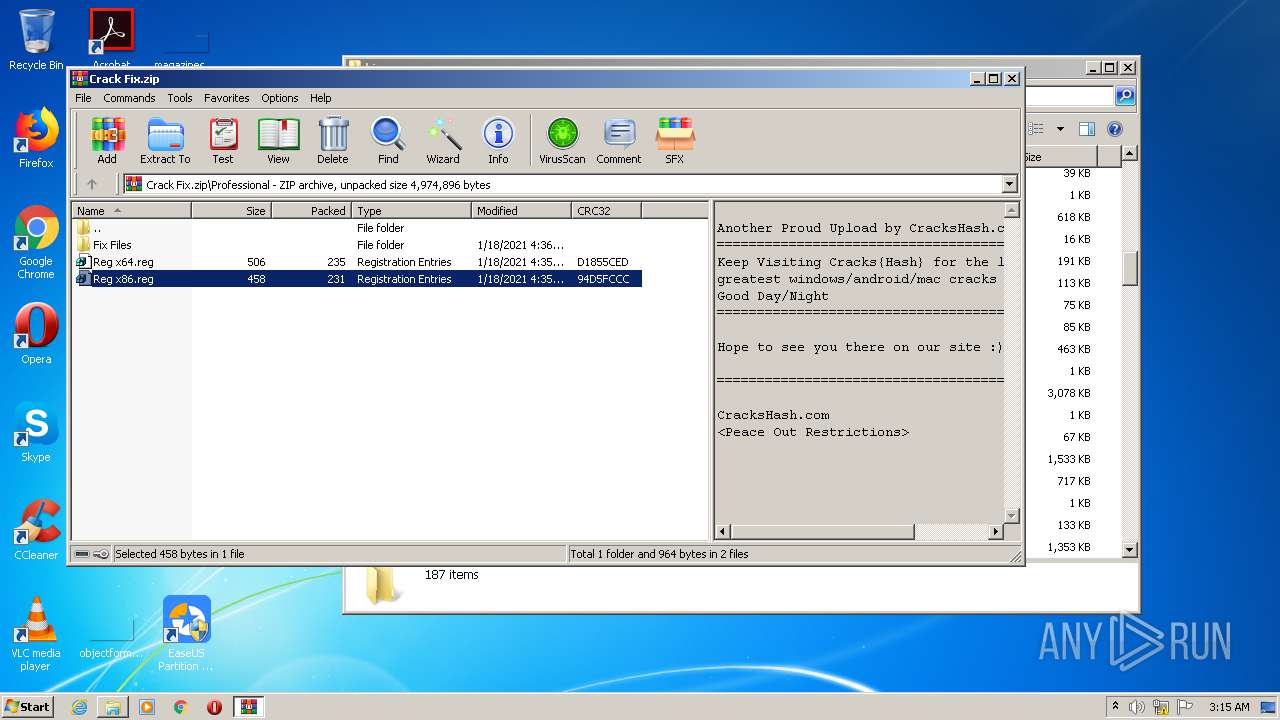
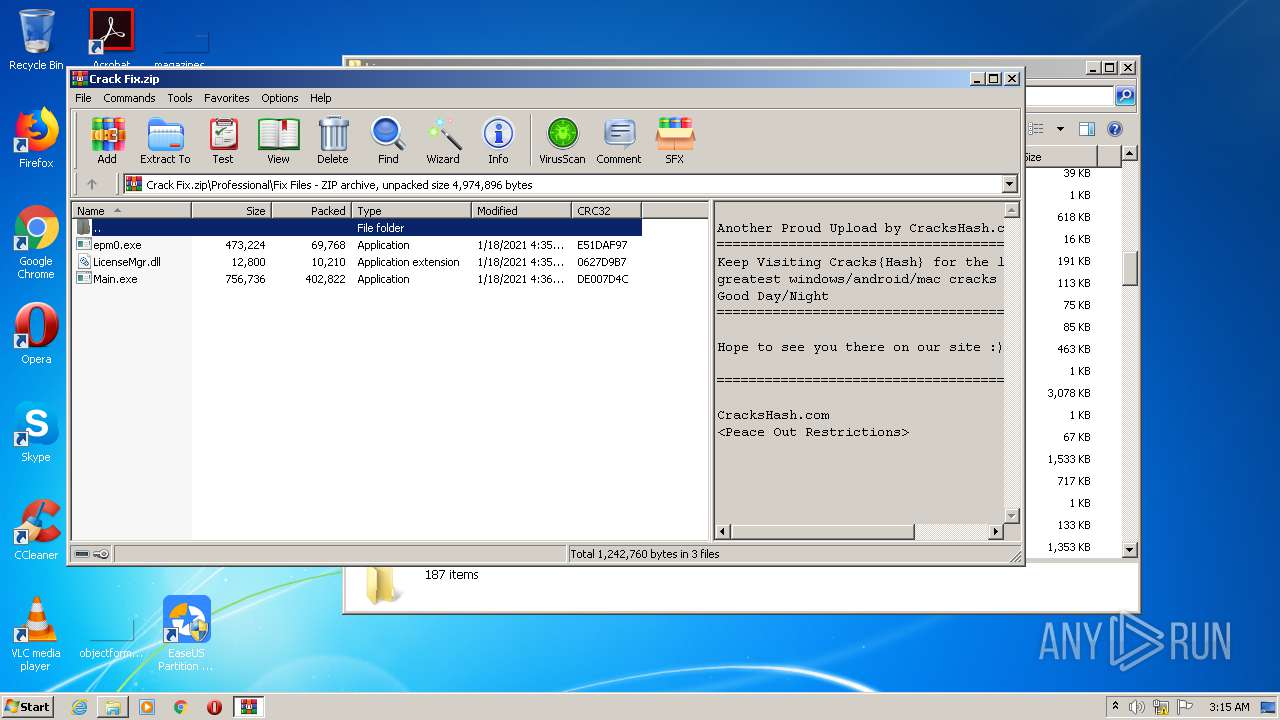
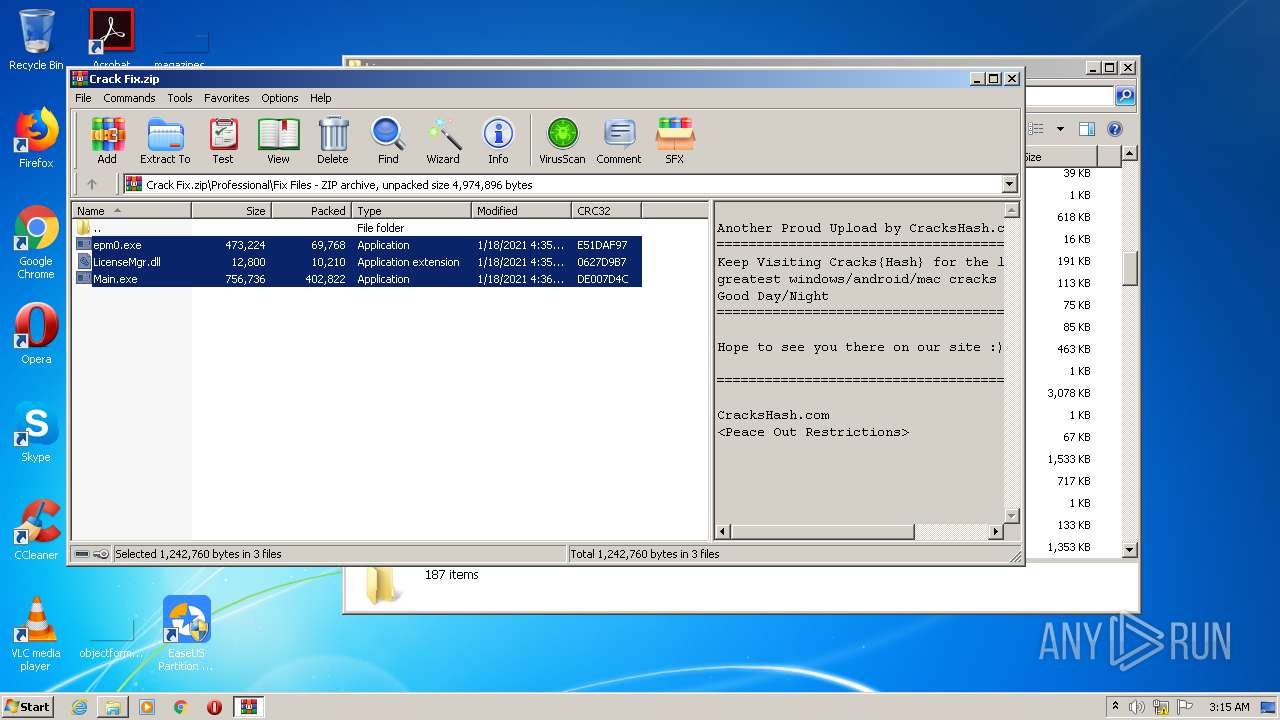
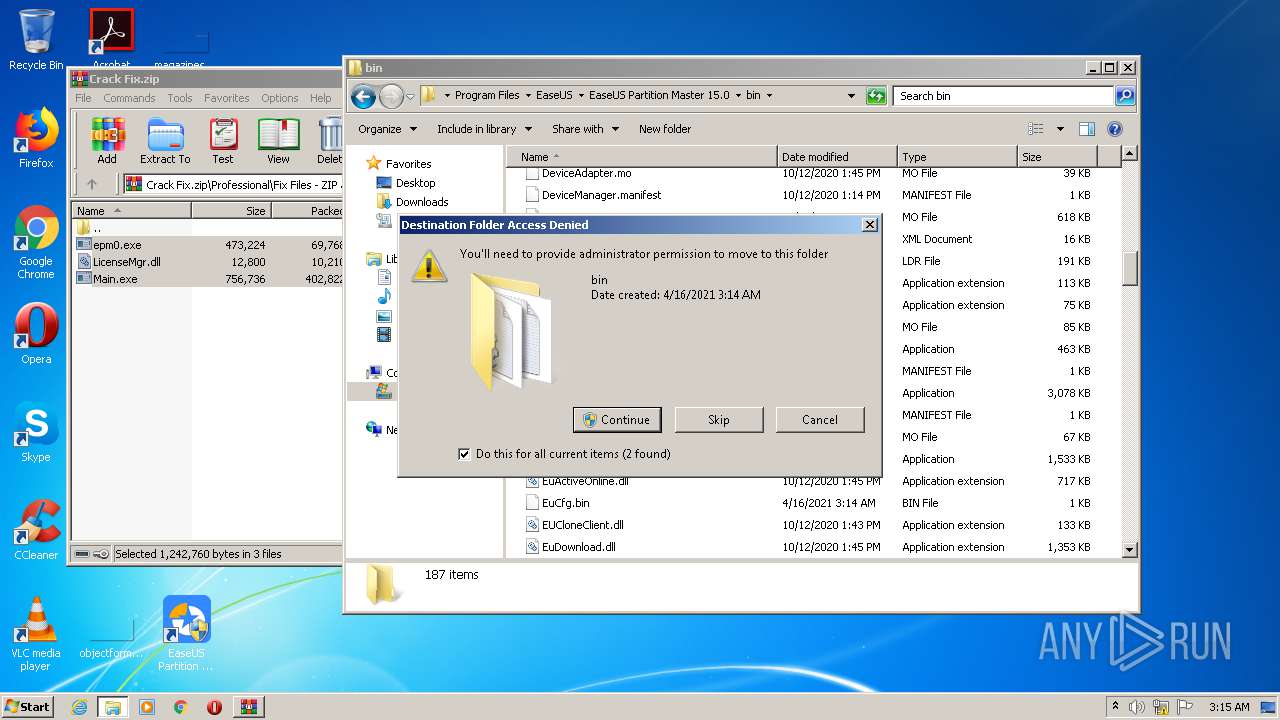
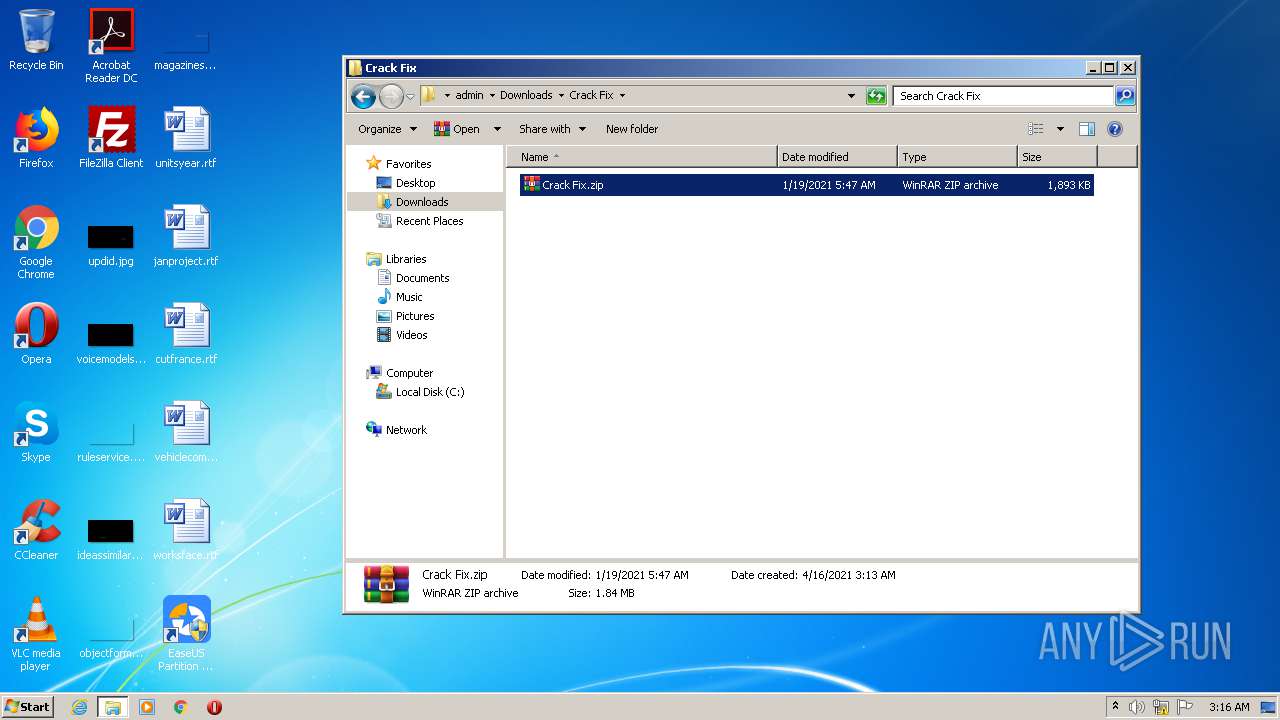
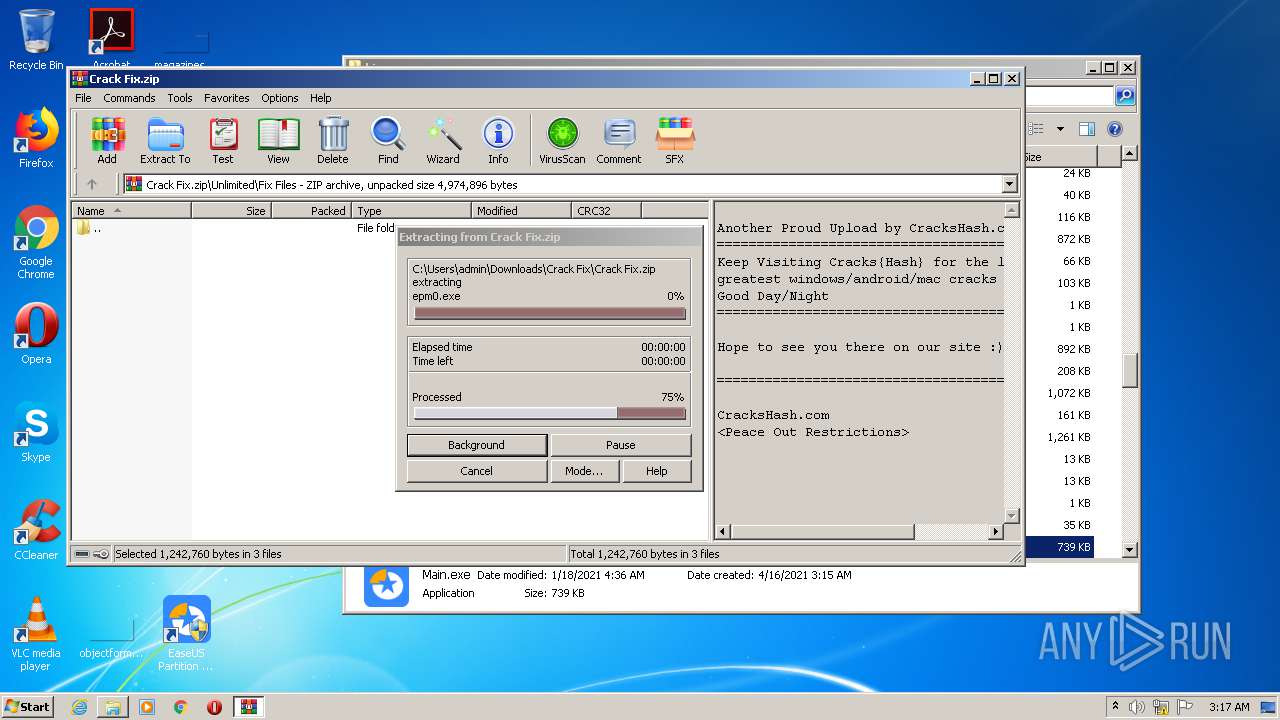
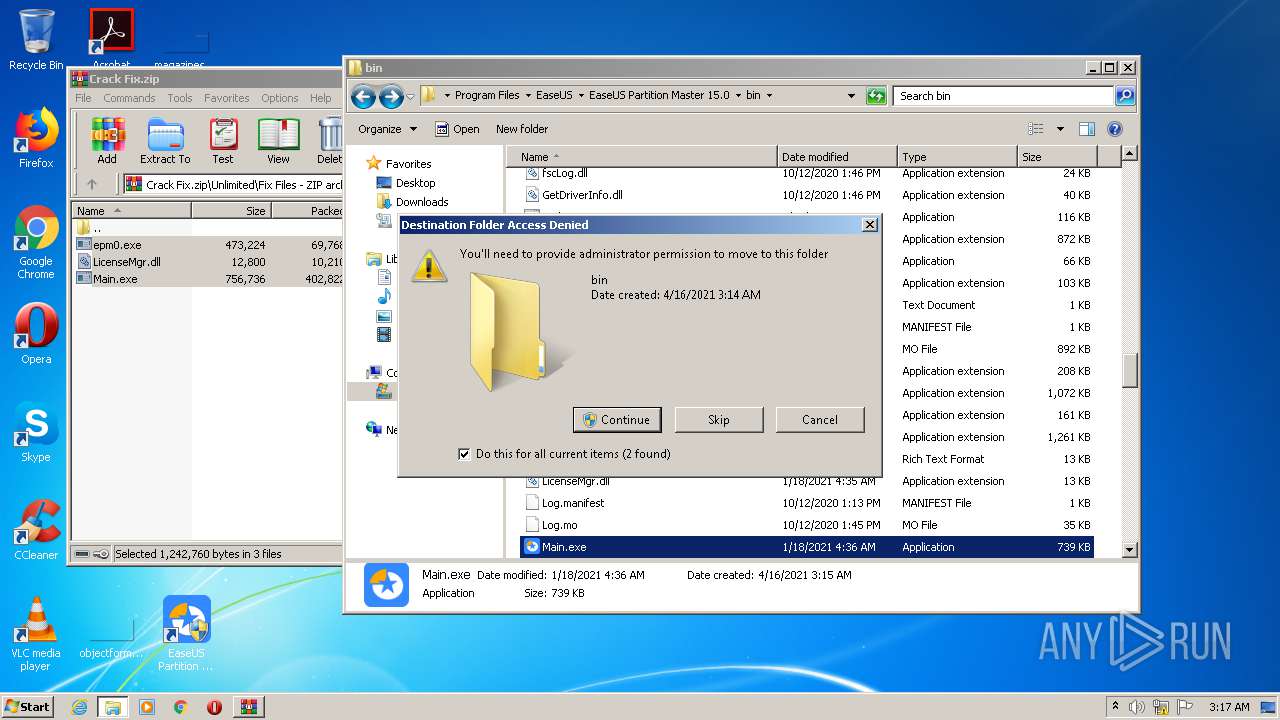
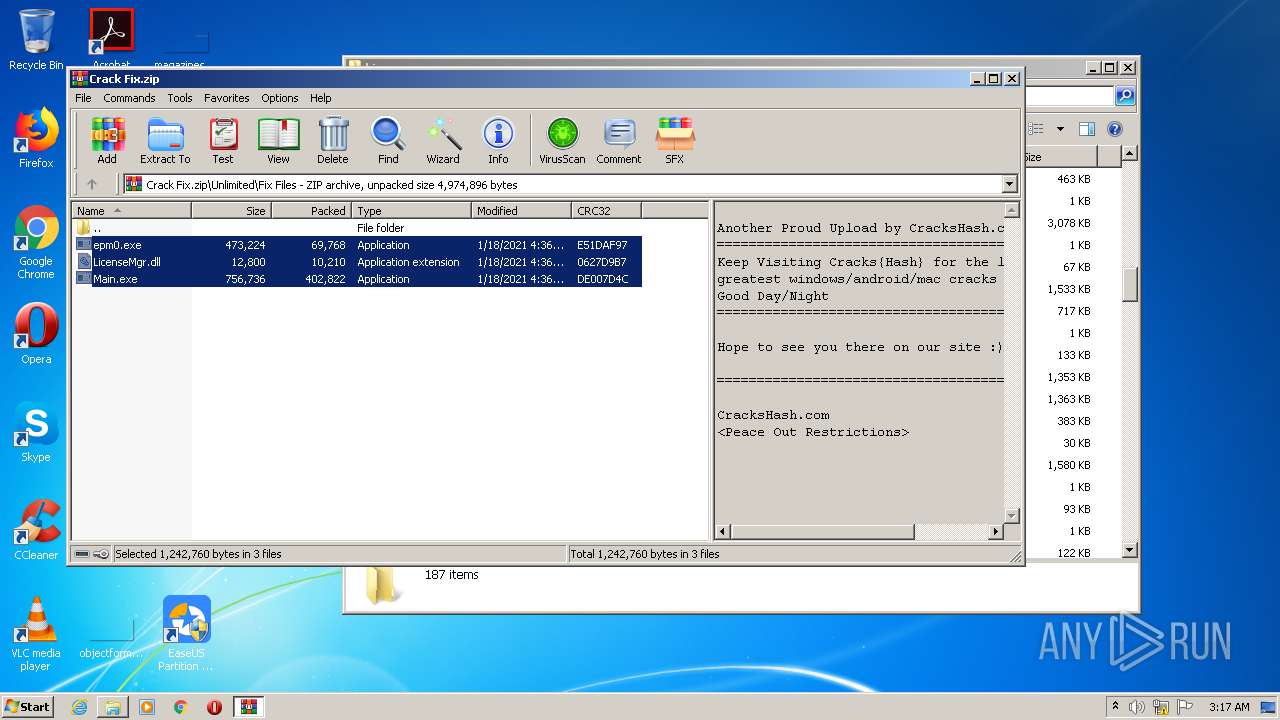
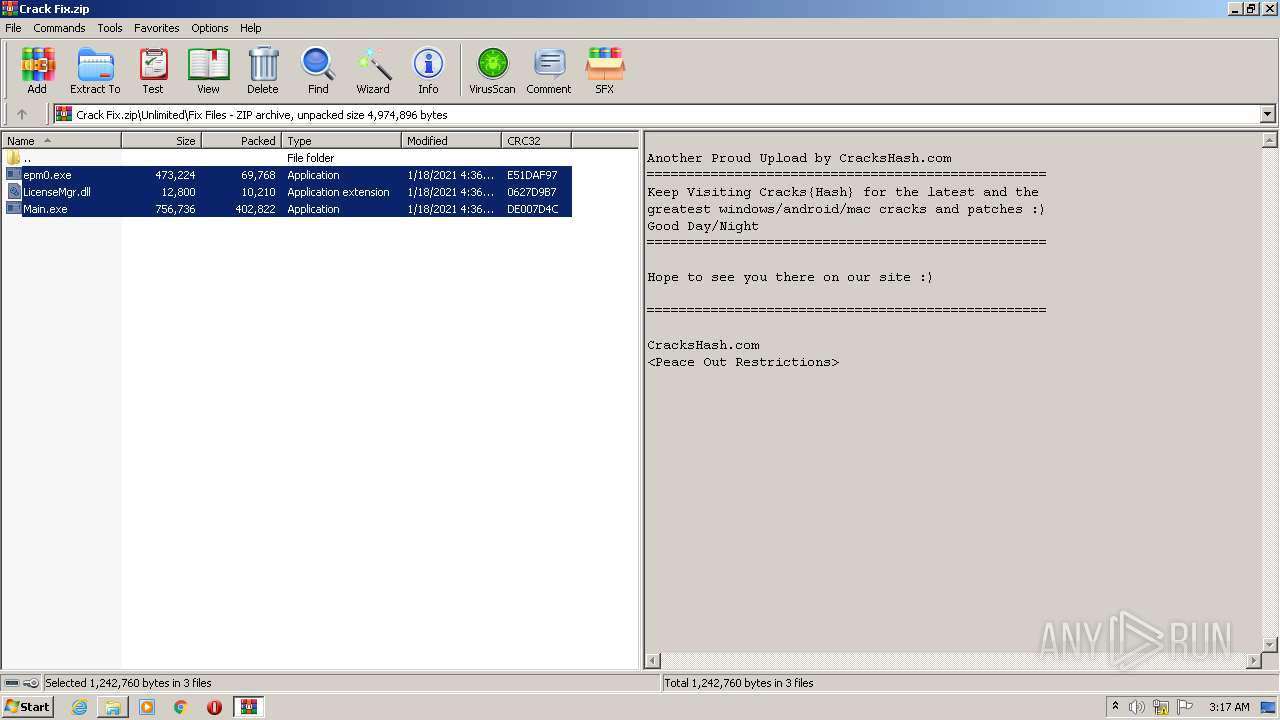
- WinRAR.exe (PID: 1312)
- WinRAR.exe (PID: 2900)
- DllHost.exe (PID: 956)
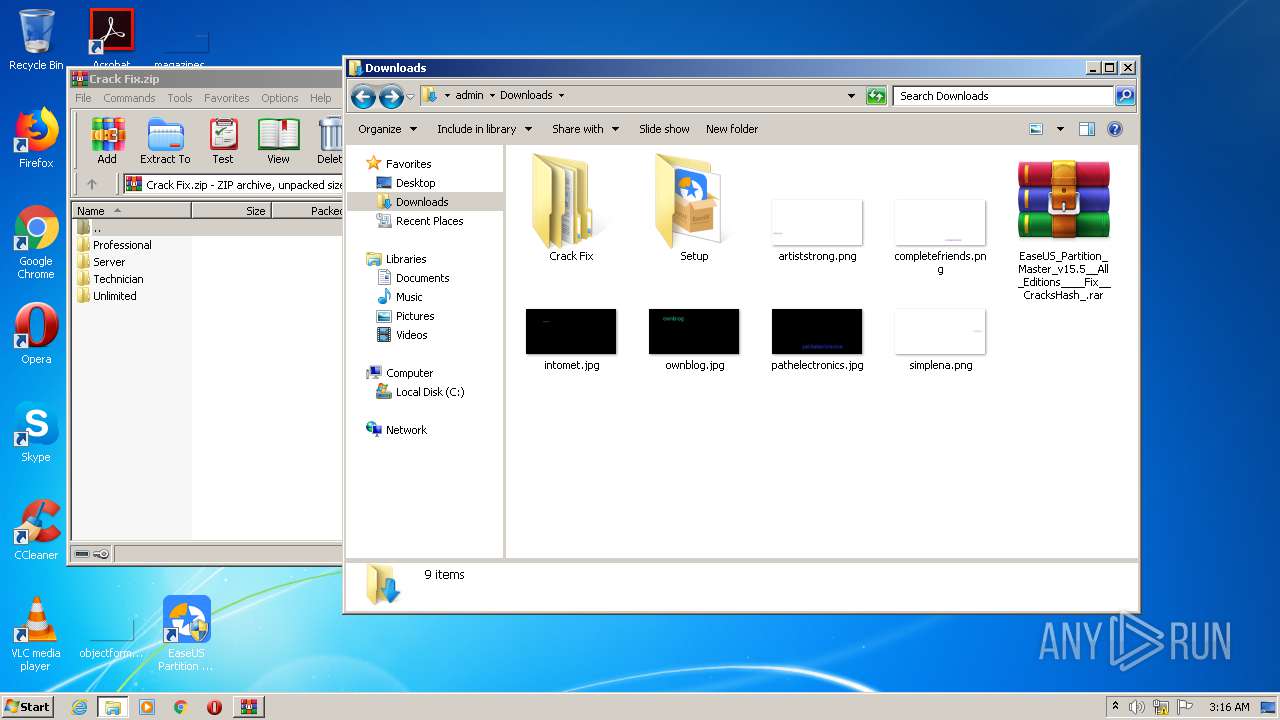
Creates files in the user directory
- explorer.exe (PID: 656)
- epm_setup.tmp (PID: 3884)
Reads Windows owner or organization settings
- epm_setup.tmp (PID: 3884)
Reads the Windows organization settings
- epm_setup.tmp (PID: 3884)
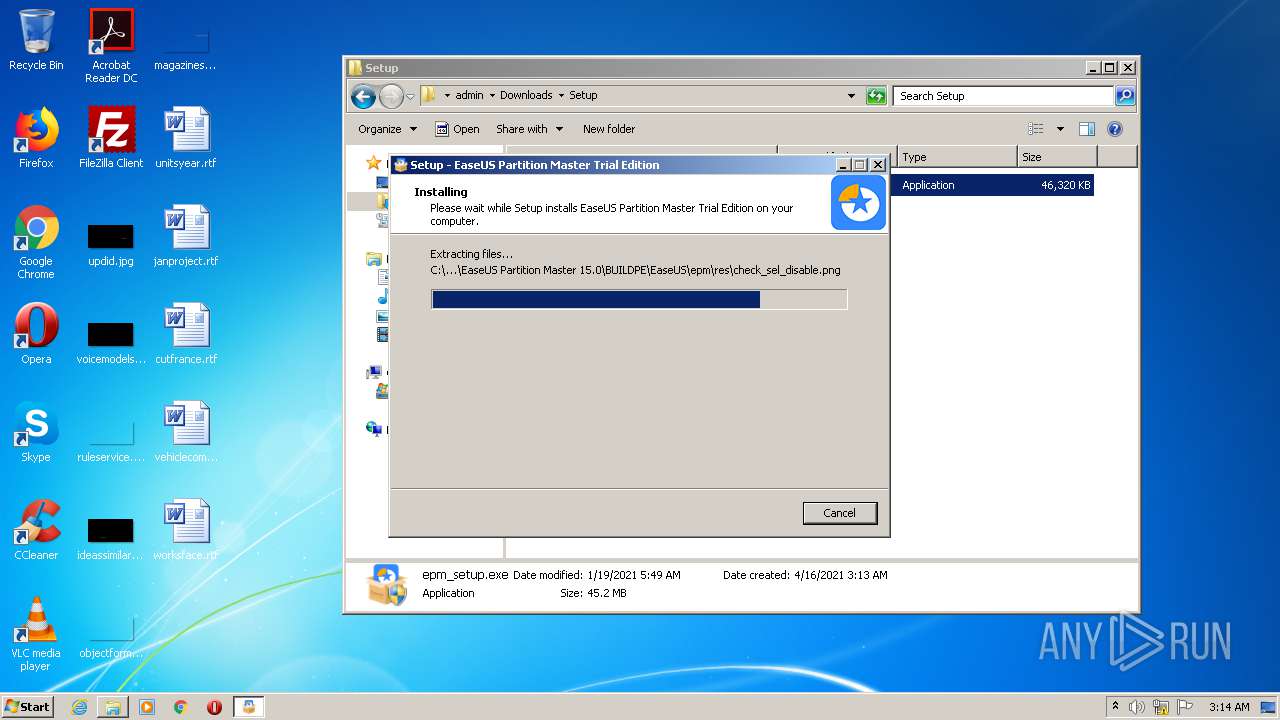
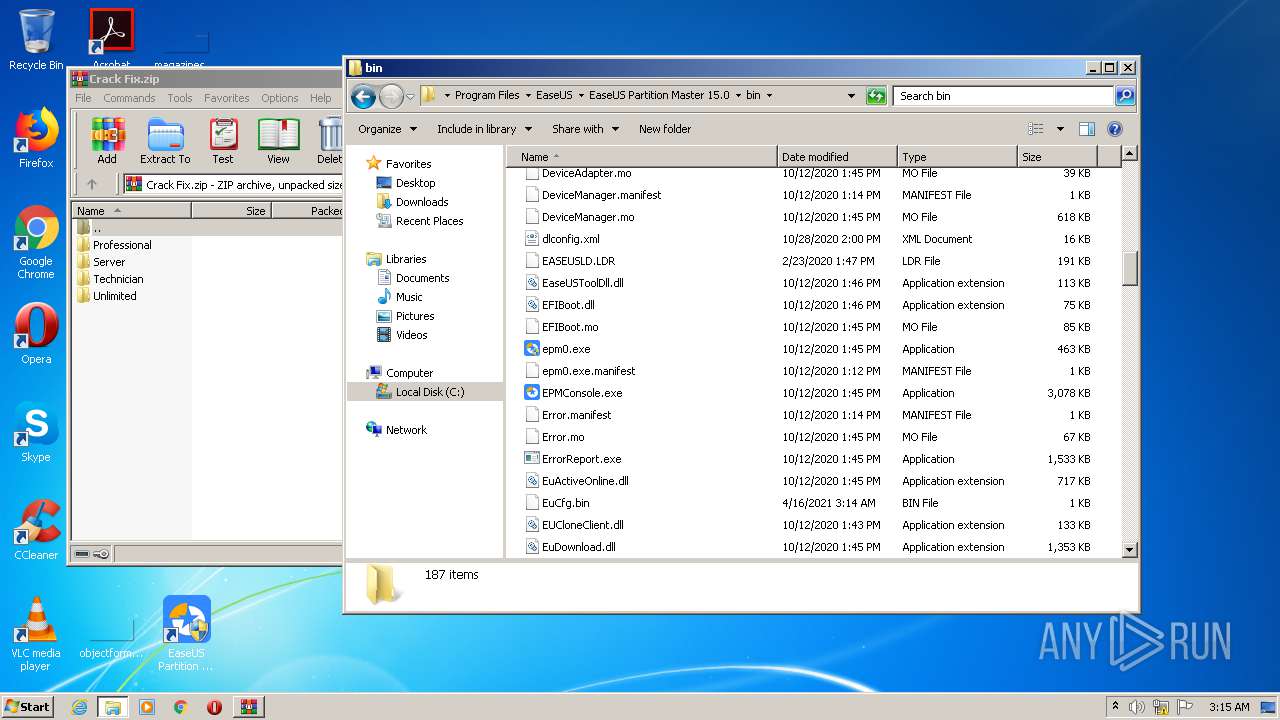
Drops a file with too old compile date
- epm_setup.tmp (PID: 3884)
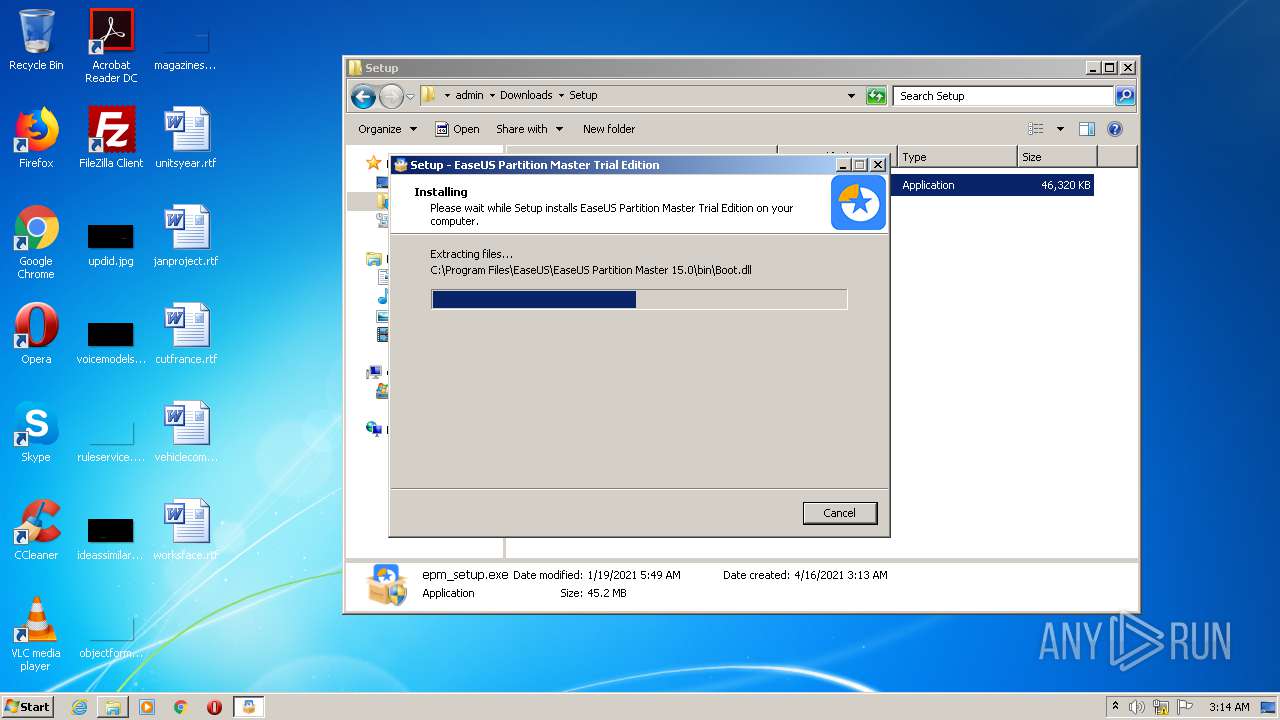
Creates files in the driver directory
- epm_setup.tmp (PID: 3884)
- drvsetup.exe (PID: 2372)
Creates files in the Windows directory
- epm_setup.tmp (PID: 3884)
- drvsetup.exe (PID: 2372)
Changes IE settings (feature browser emulation)
- epm_setup.tmp (PID: 3884)
- EUinApp.exe (PID: 2424)
Creates files in the program directory
- drvsetup.exe (PID: 2372)
- AliyunWrapExe.Exe (PID: 2552)
Drops a file that was compiled in debug mode
- epm_setup.tmp (PID: 3884)
- drvsetup.exe (PID: 2372)
- WinRAR.exe (PID: 1312)
- DllHost.exe (PID: 3768)
- WinRAR.exe (PID: 2900)
- DllHost.exe (PID: 956)
Creates or modifies windows services
- drvsetup.exe (PID: 2372)
- setupempdrv03.exe (PID: 1676)
Removes files from Windows directory
- drvsetup.exe (PID: 2372)
Starts Internet Explorer
- epm_setup.tmp (PID: 3884)
Executed via COM
- DllHost.exe (PID: 3768)
- DllHost.exe (PID: 956)
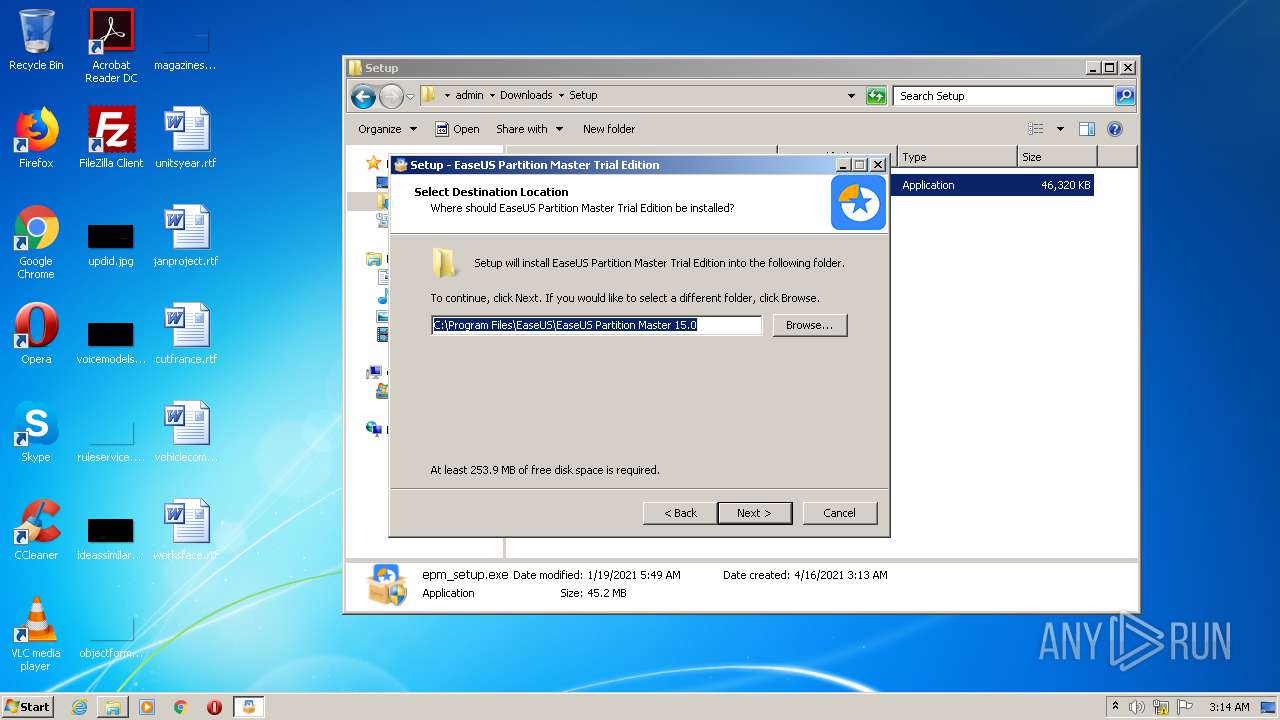
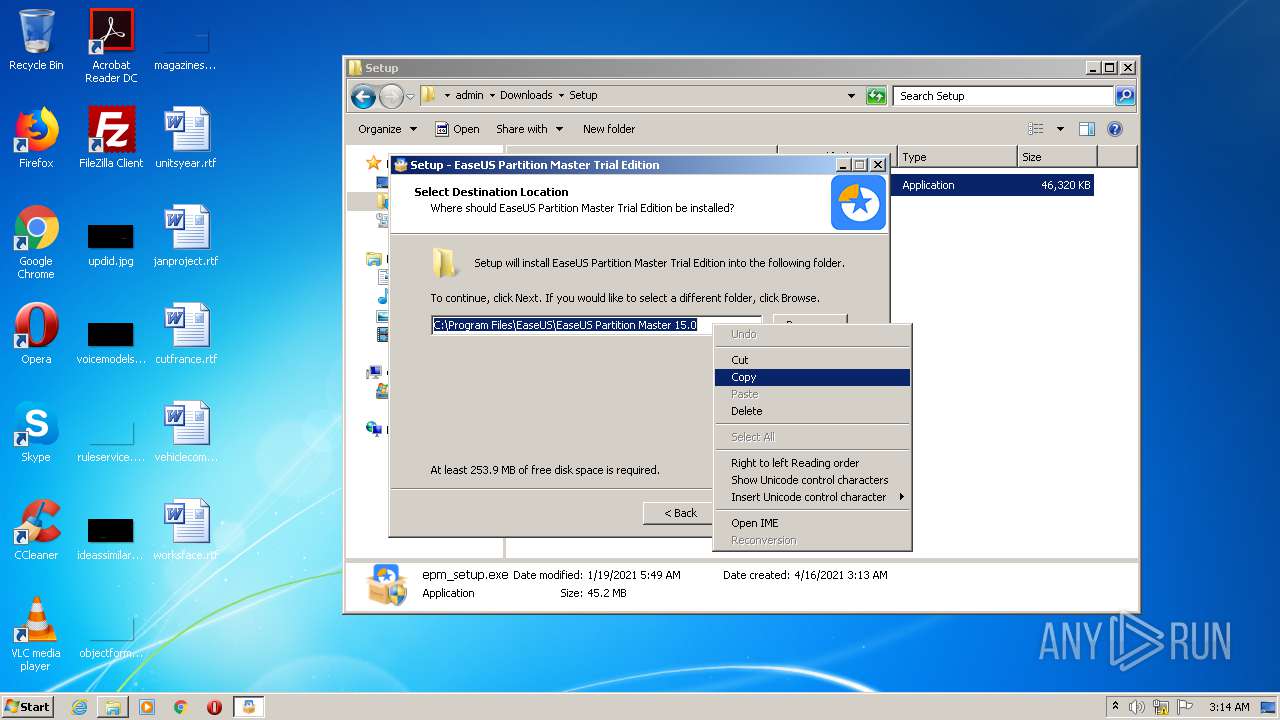
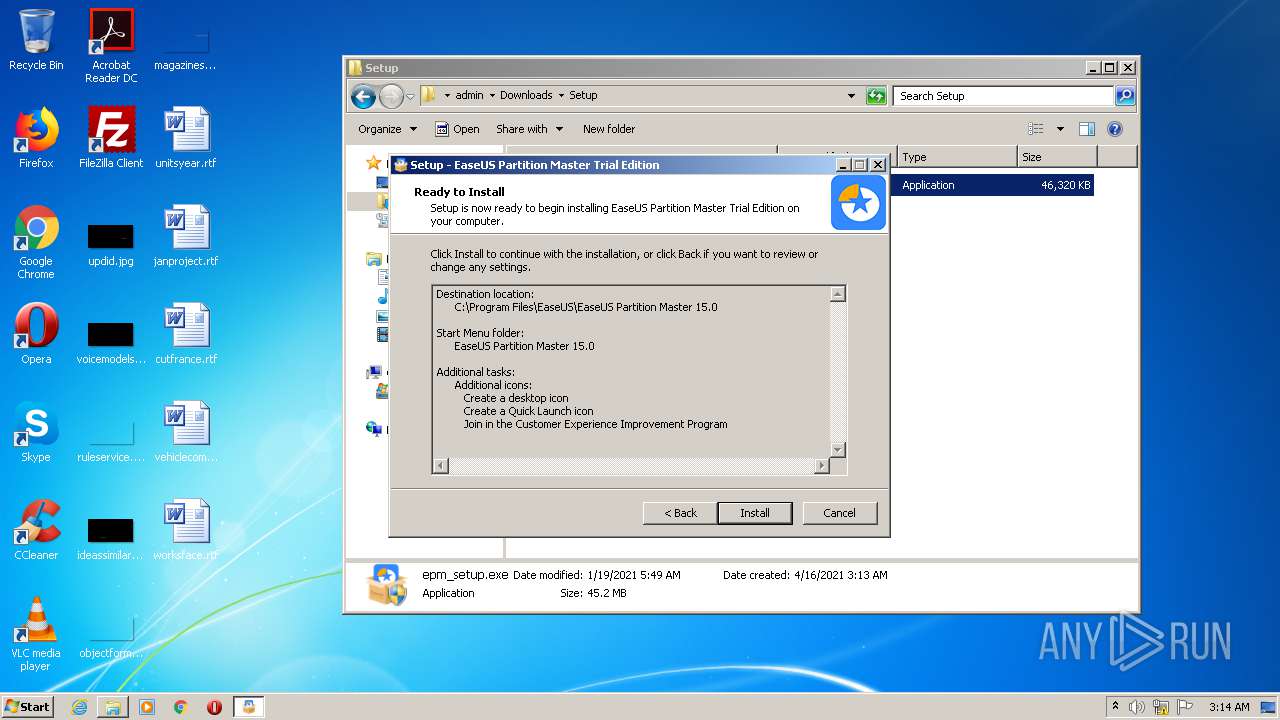
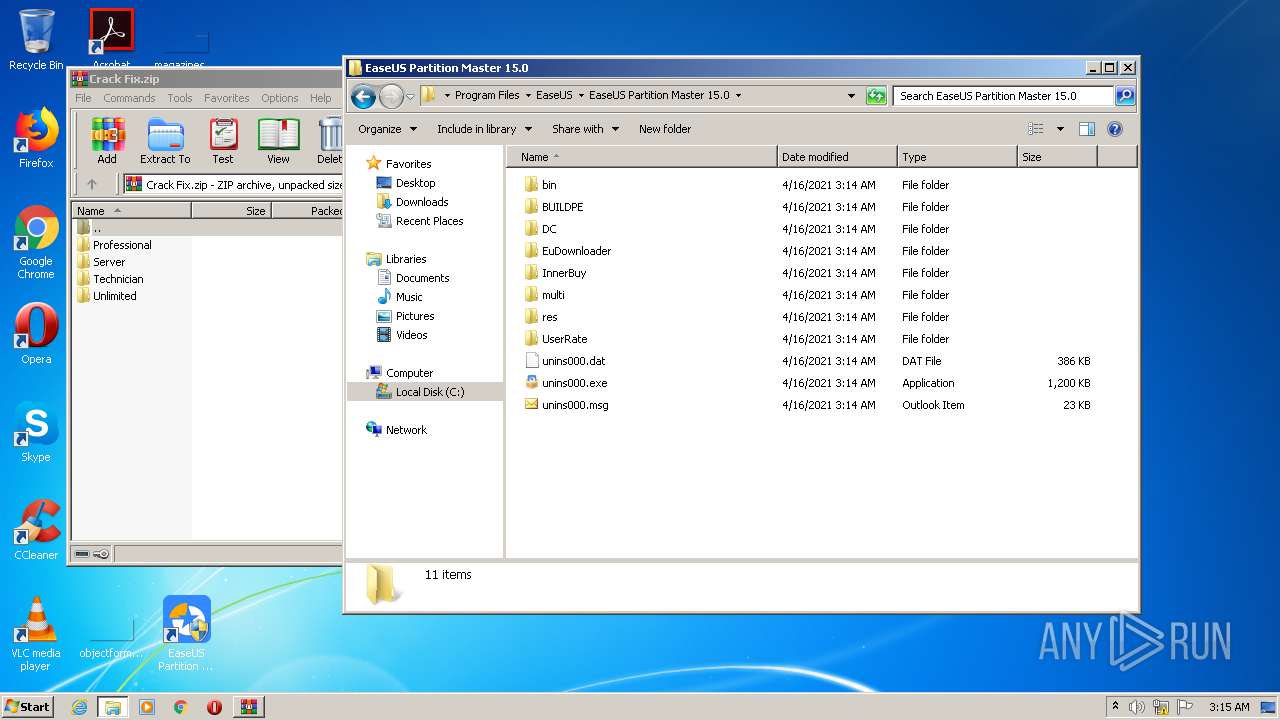
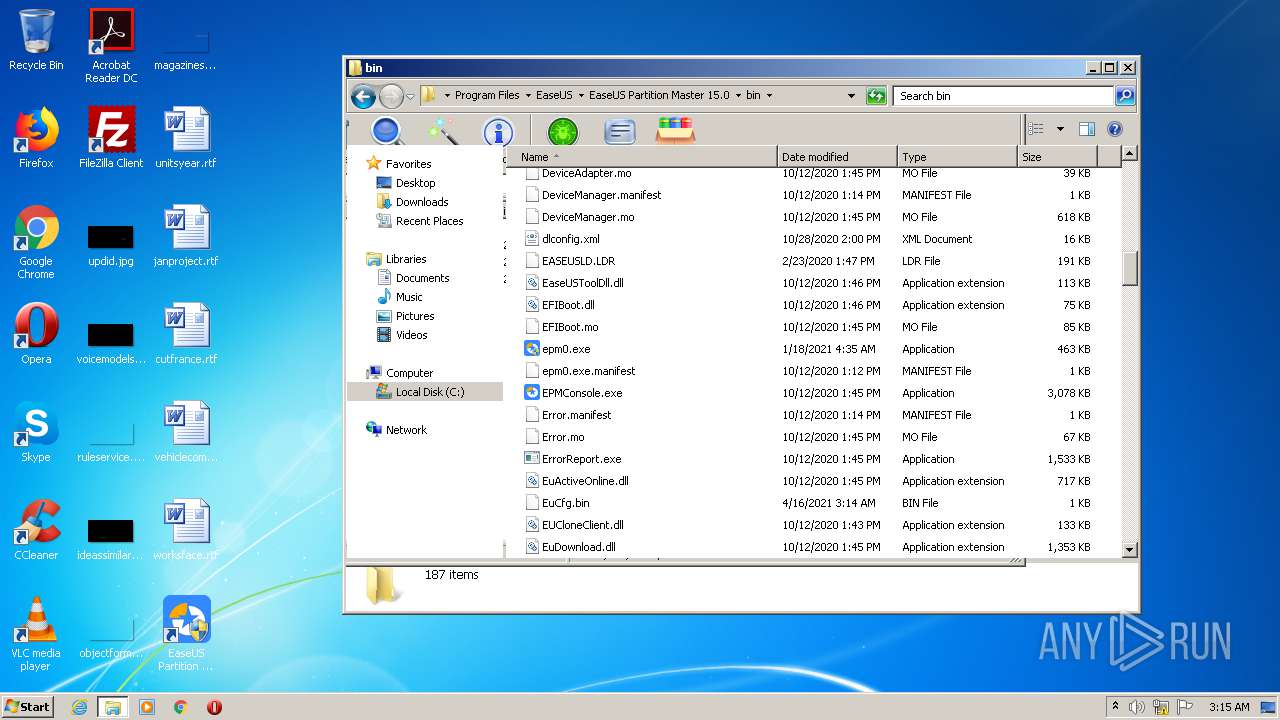
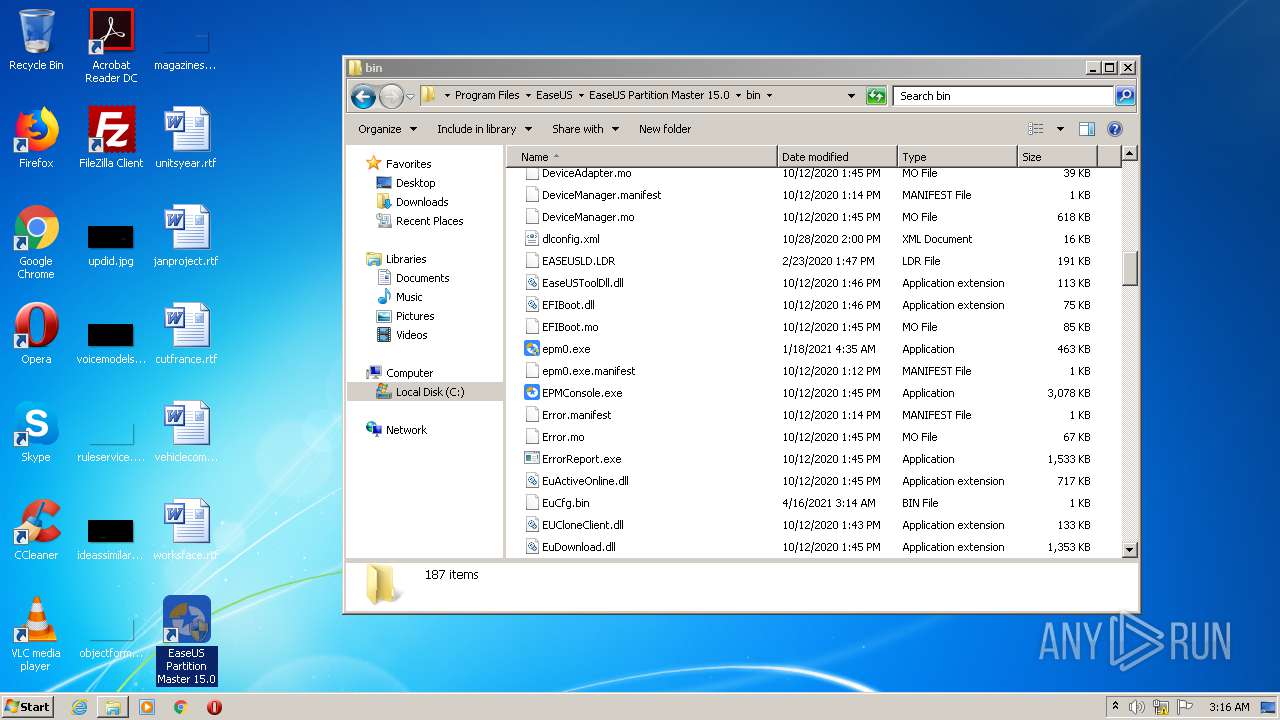
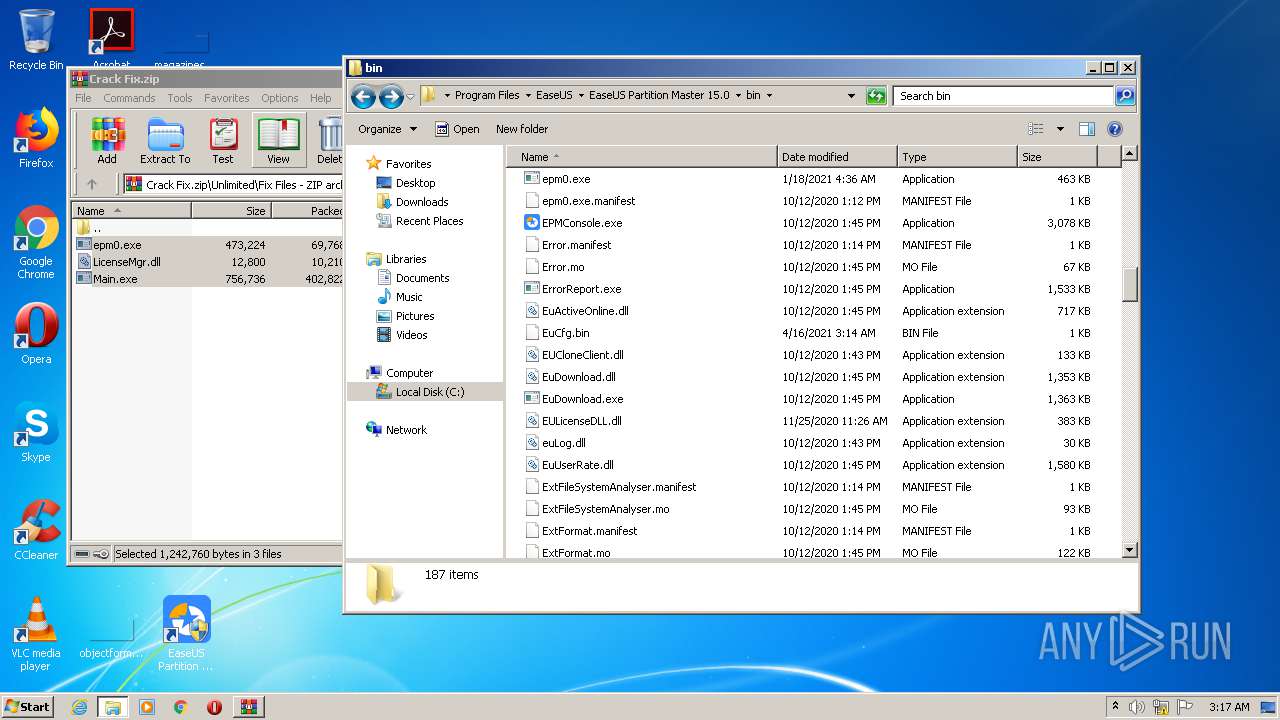
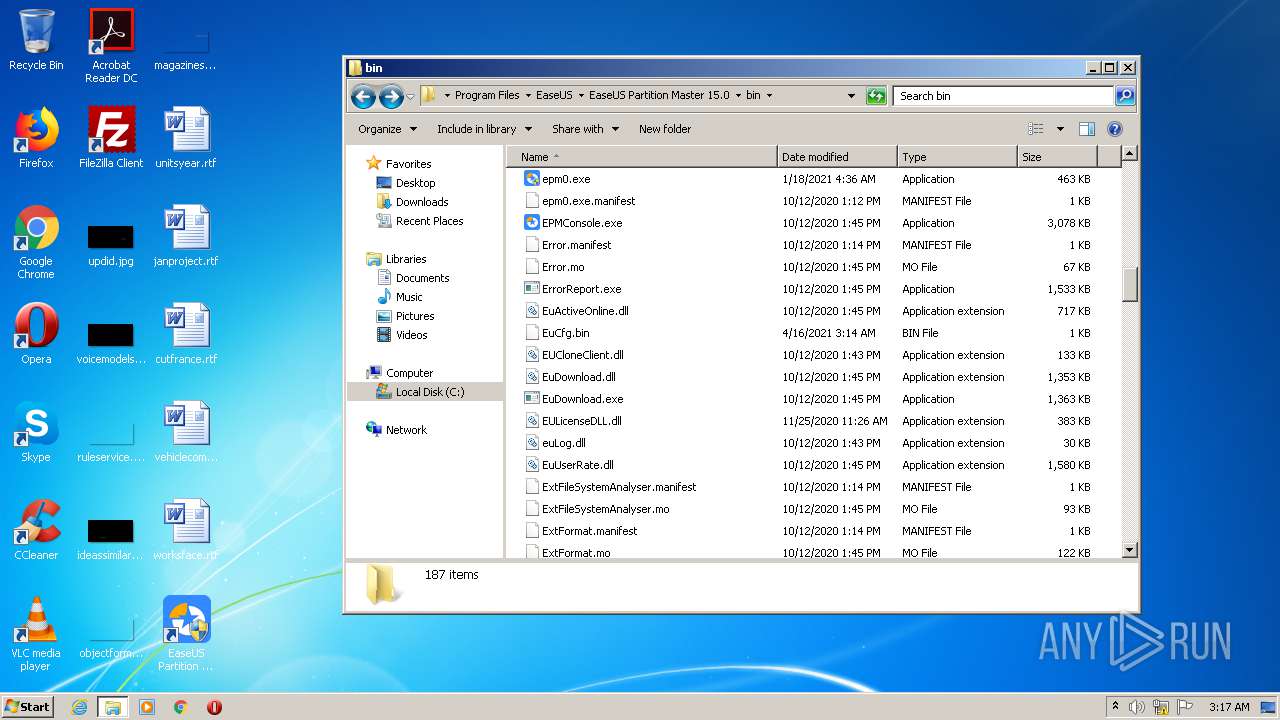
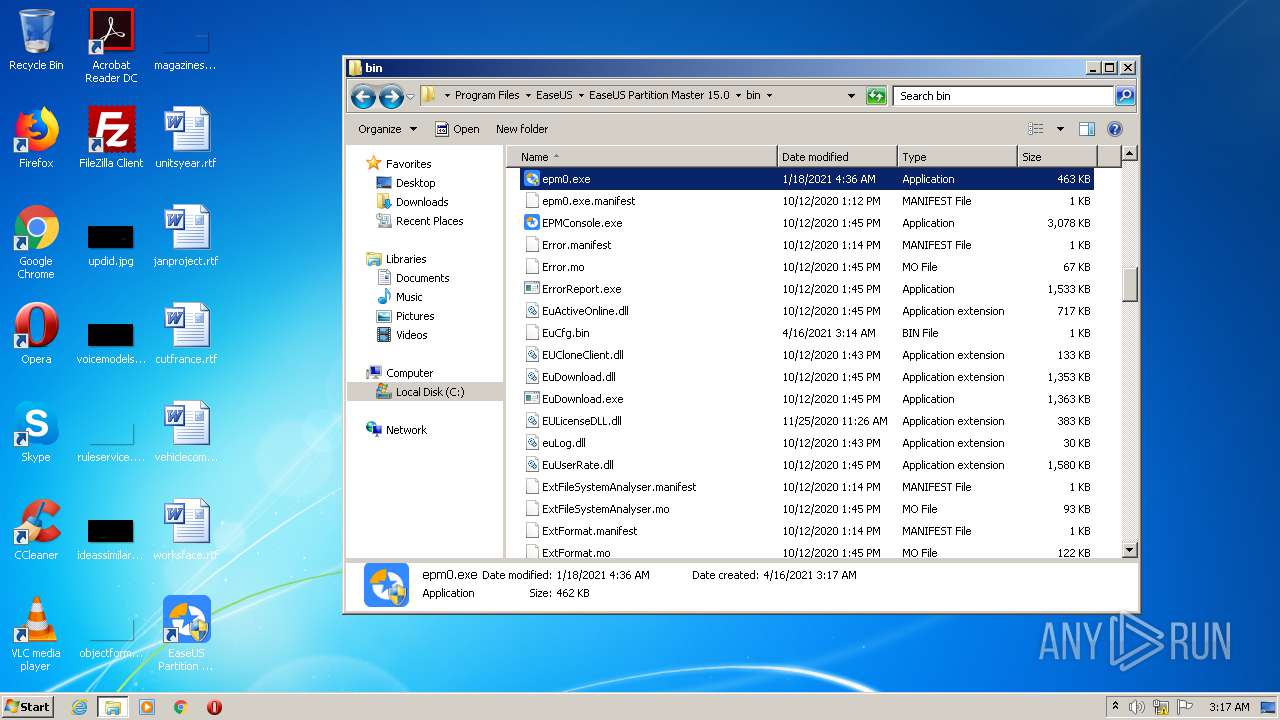
Creates a directory in Program Files
- epm_setup.tmp (PID: 3884)
INFO
Reads the hosts file
- chrome.exe (PID: 1548)
- chrome.exe (PID: 1264)
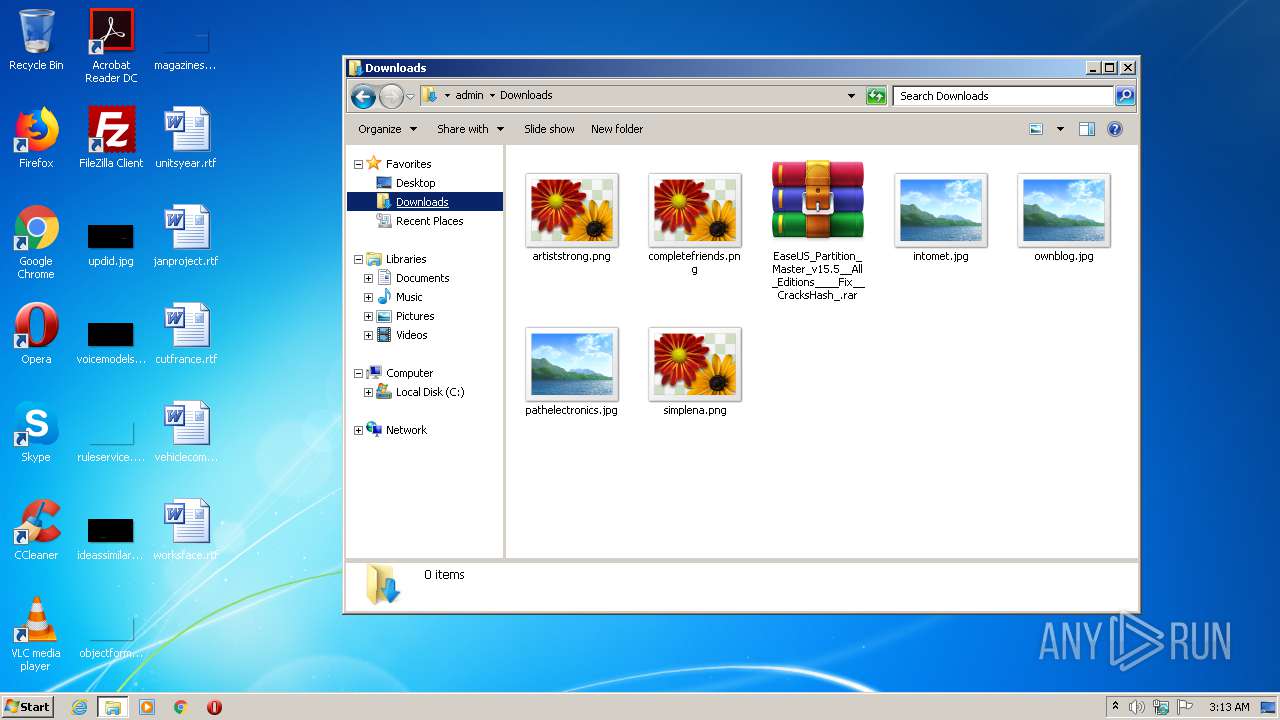
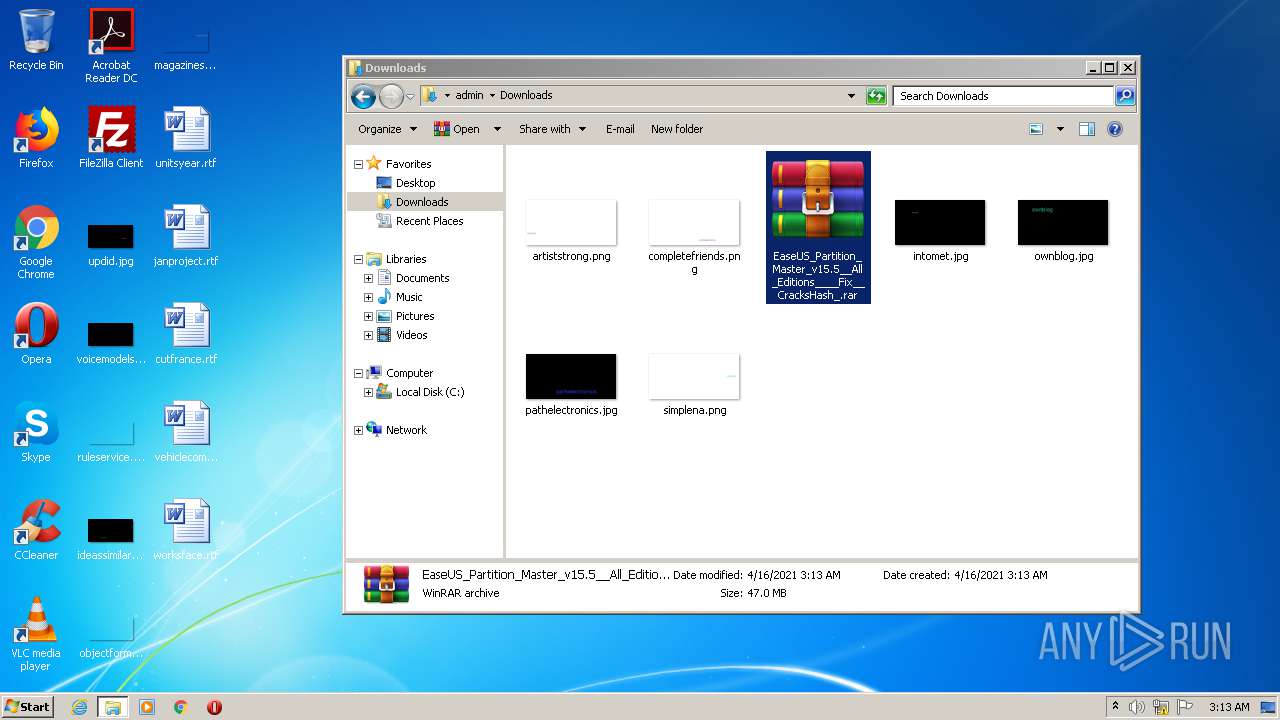
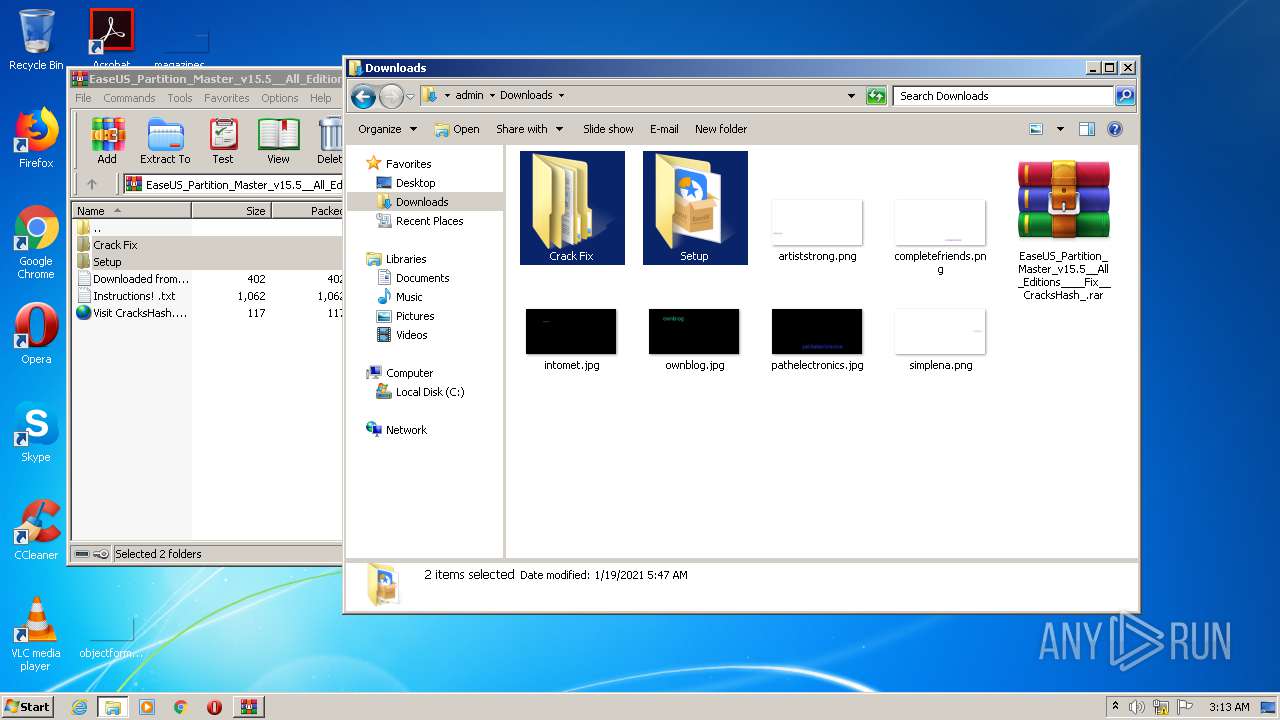
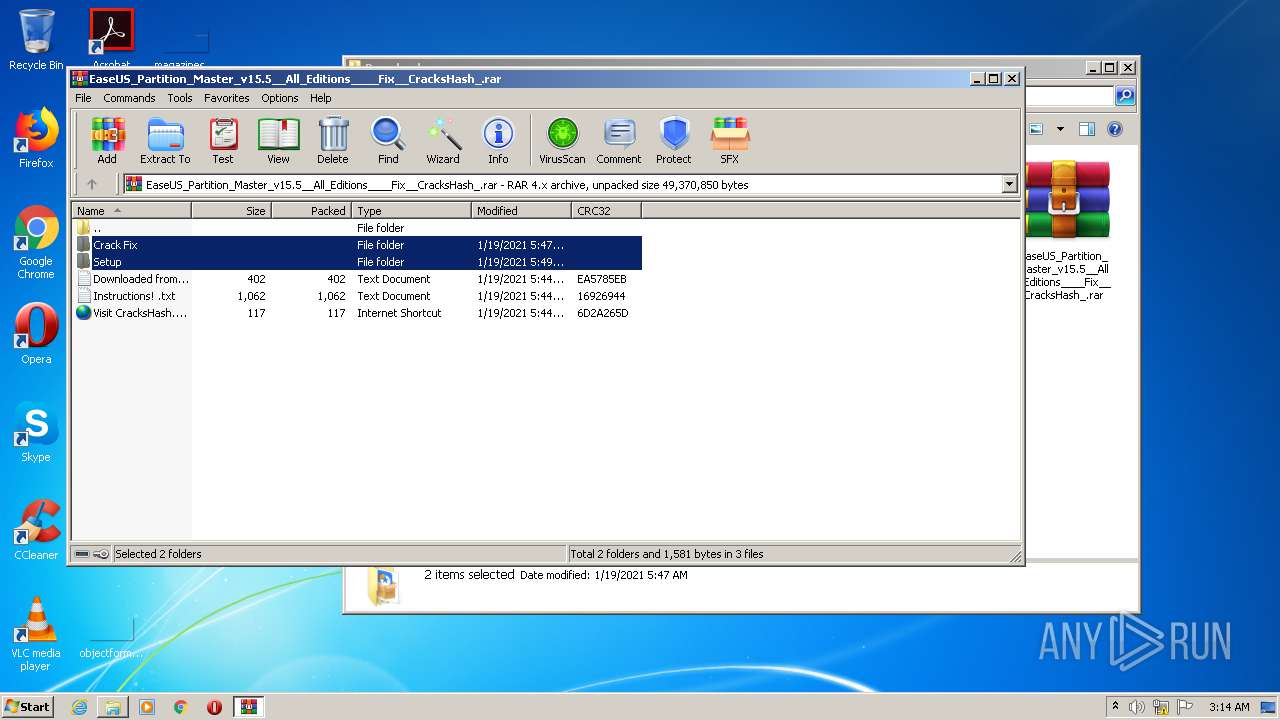
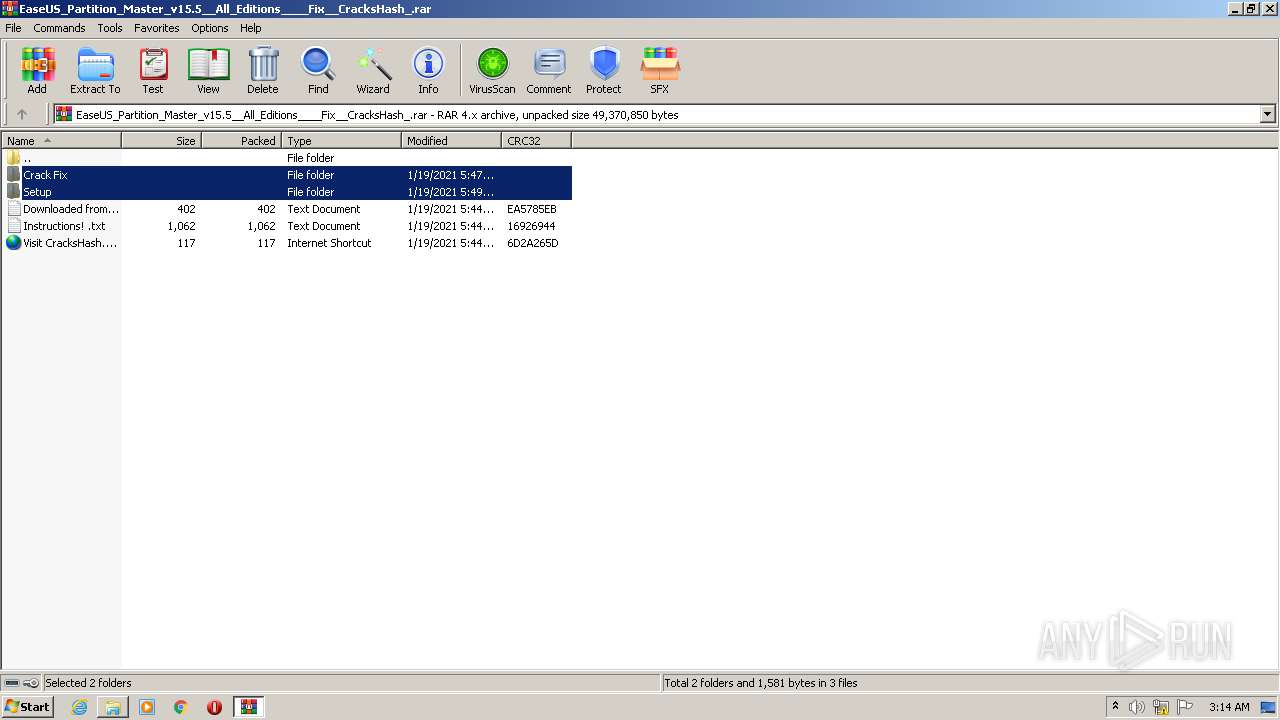
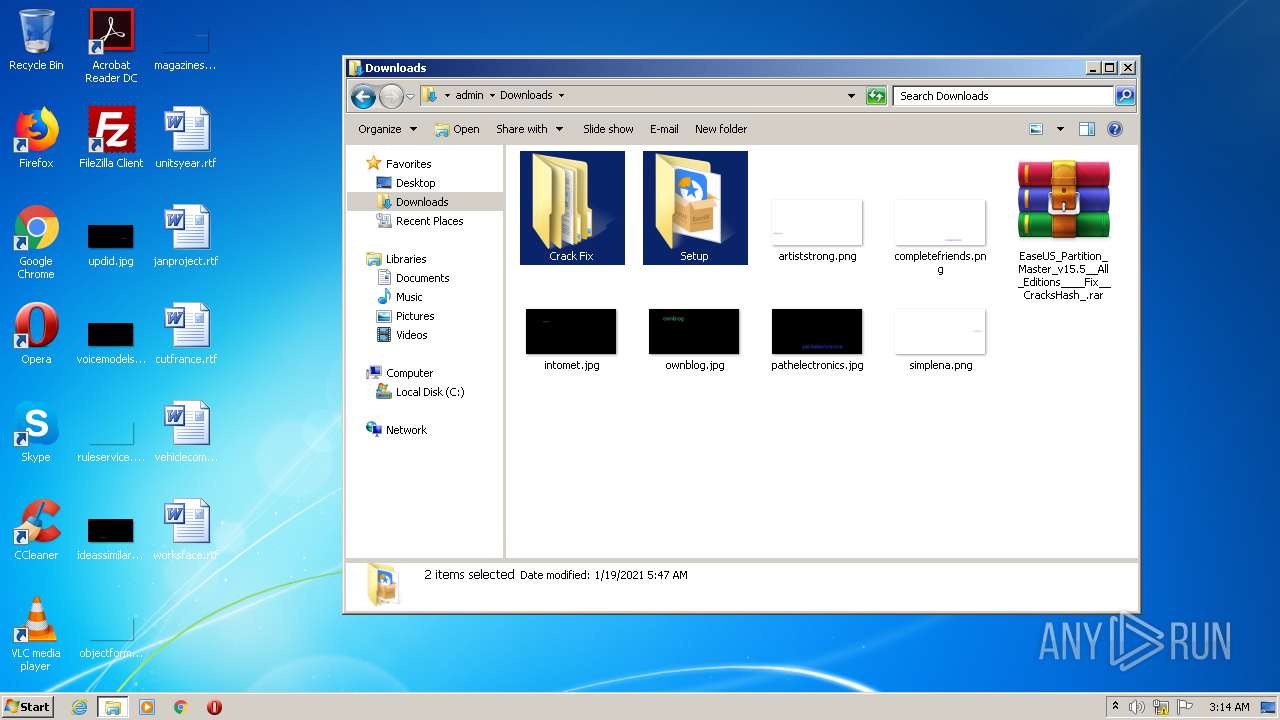
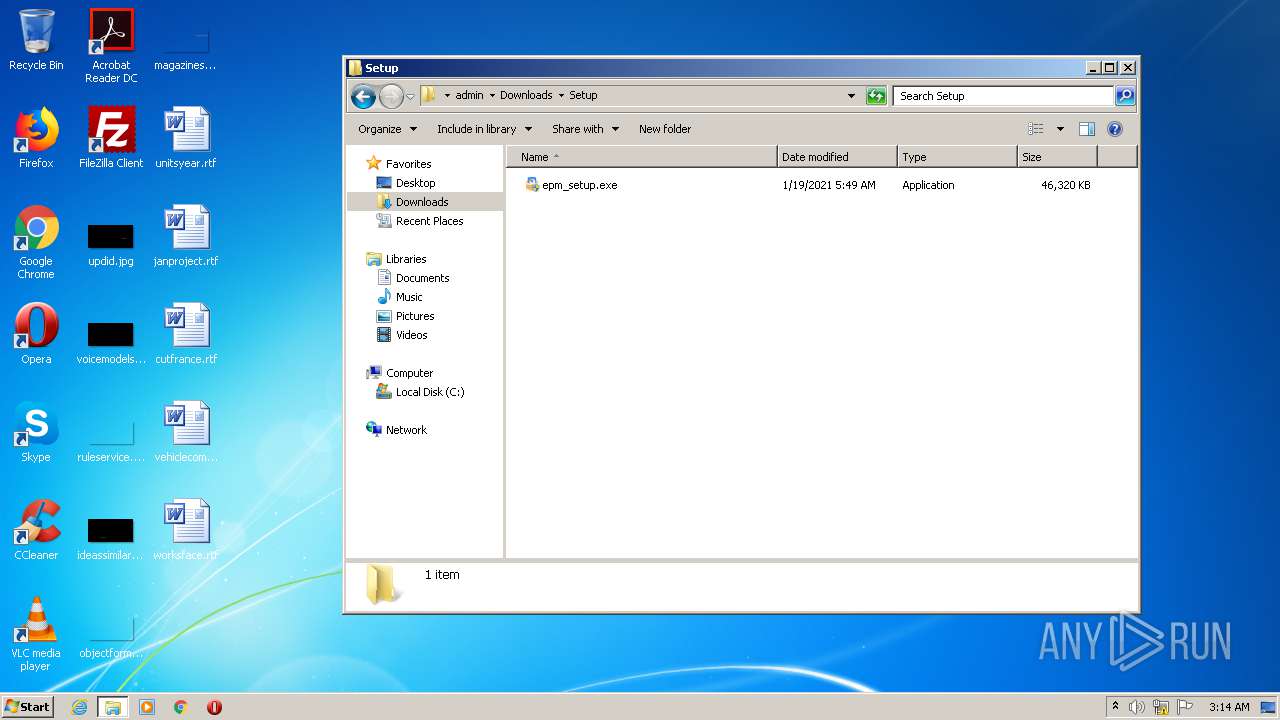
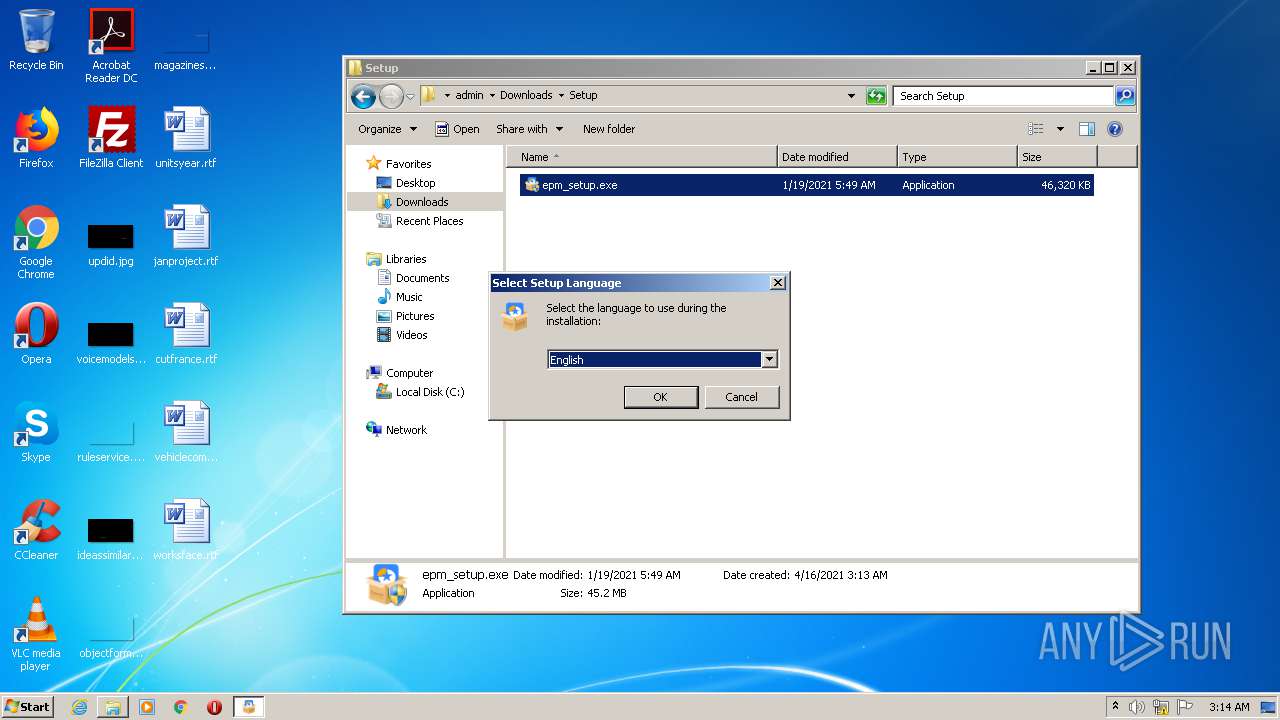
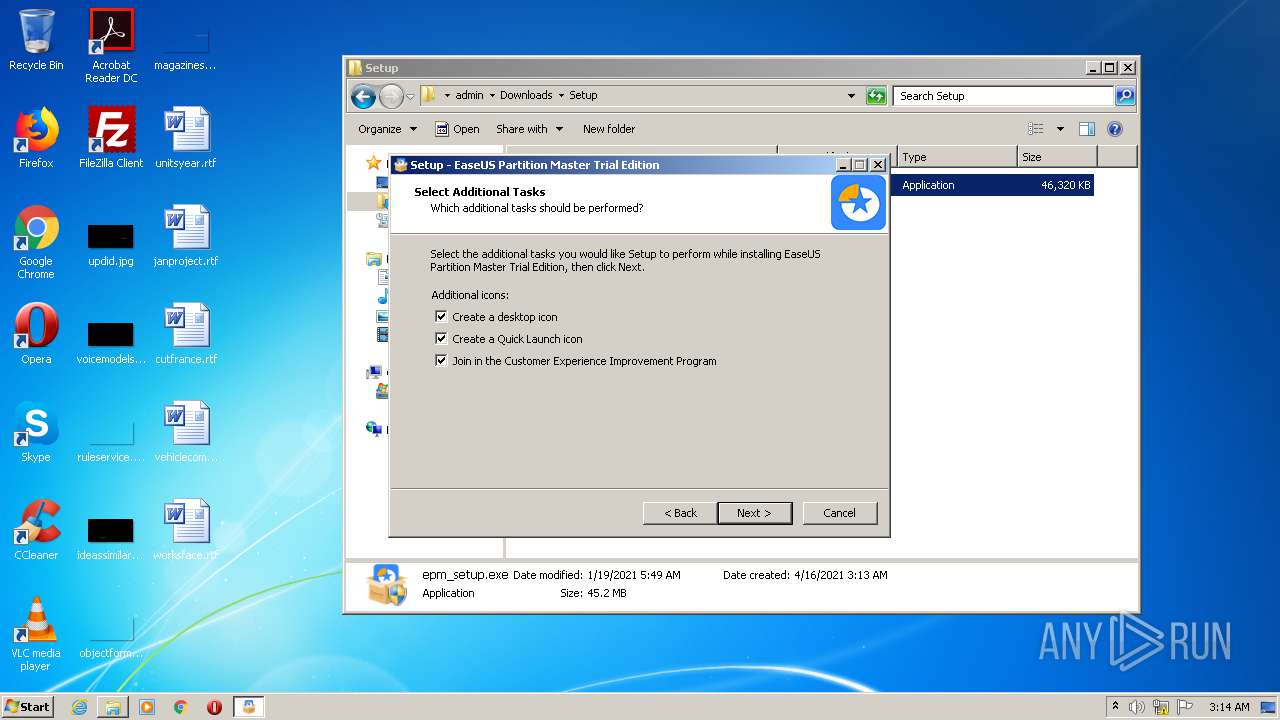
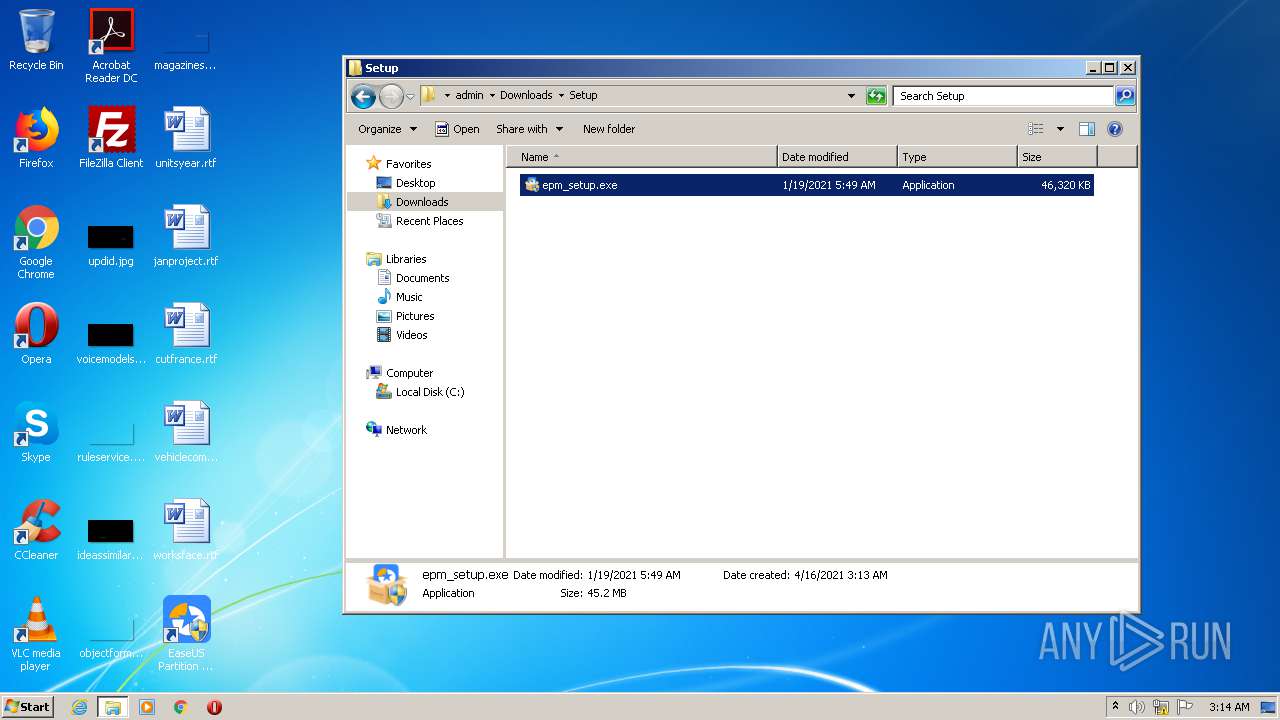
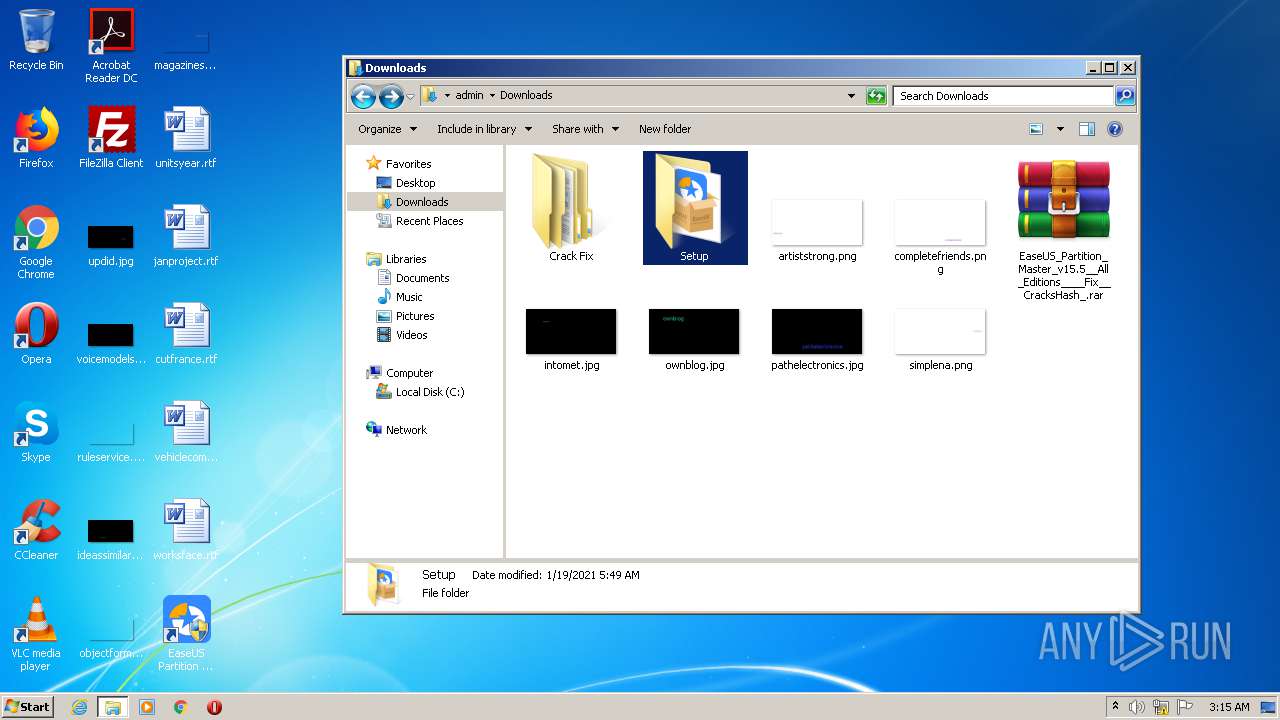
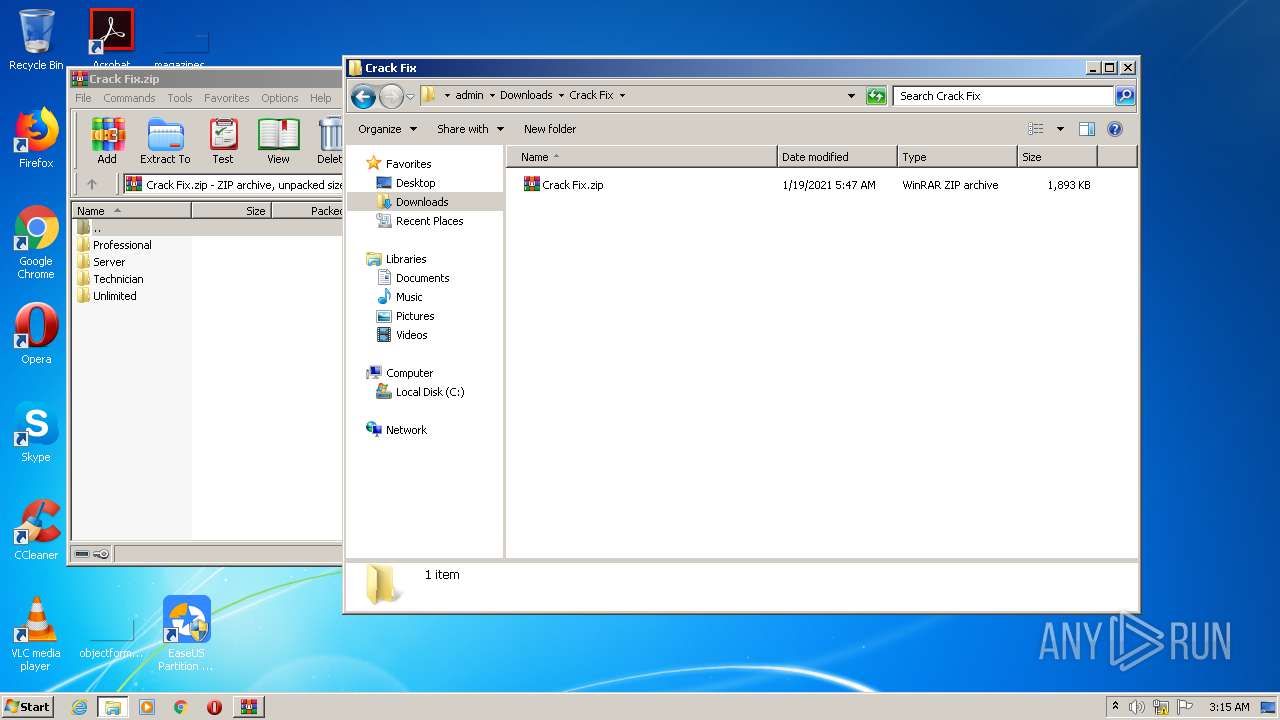
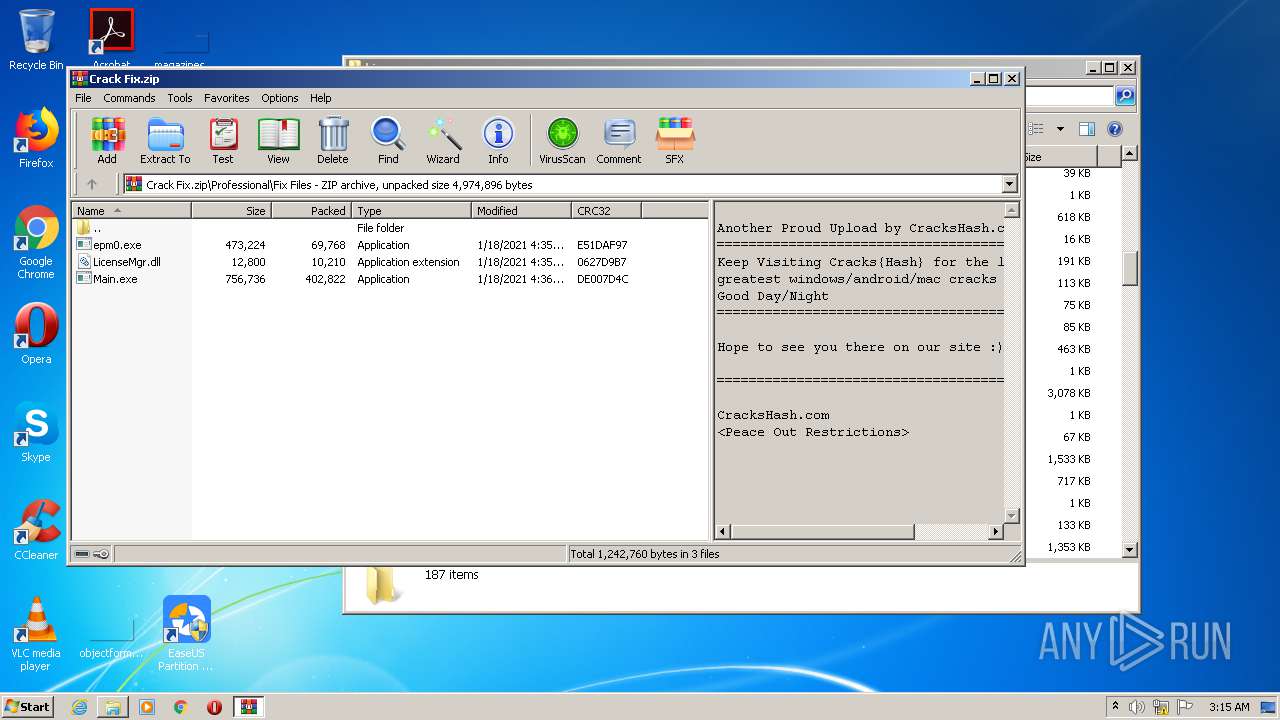
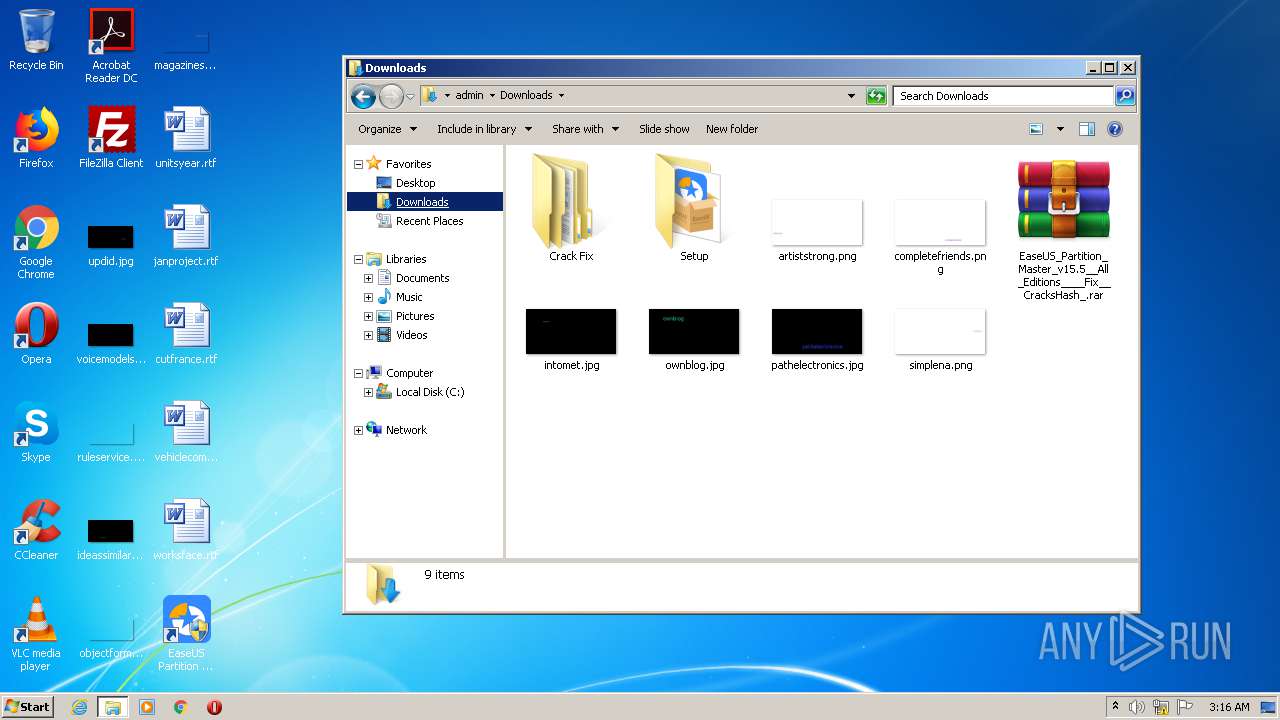
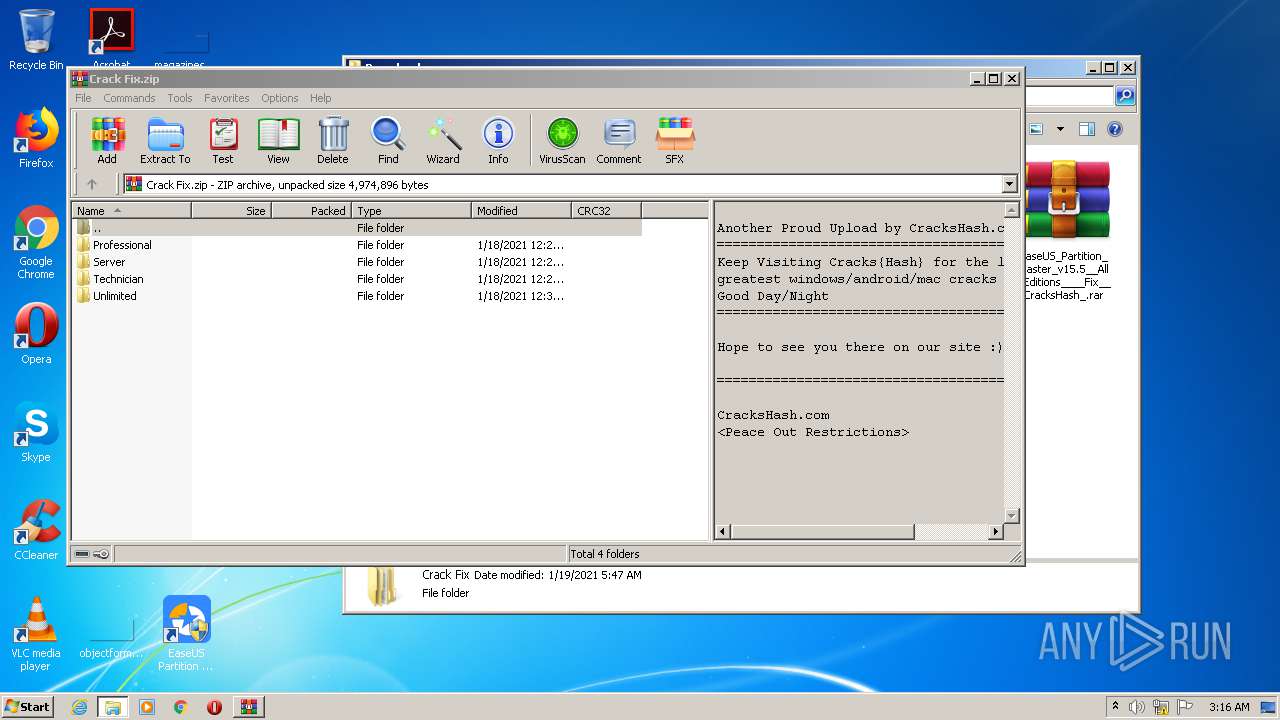
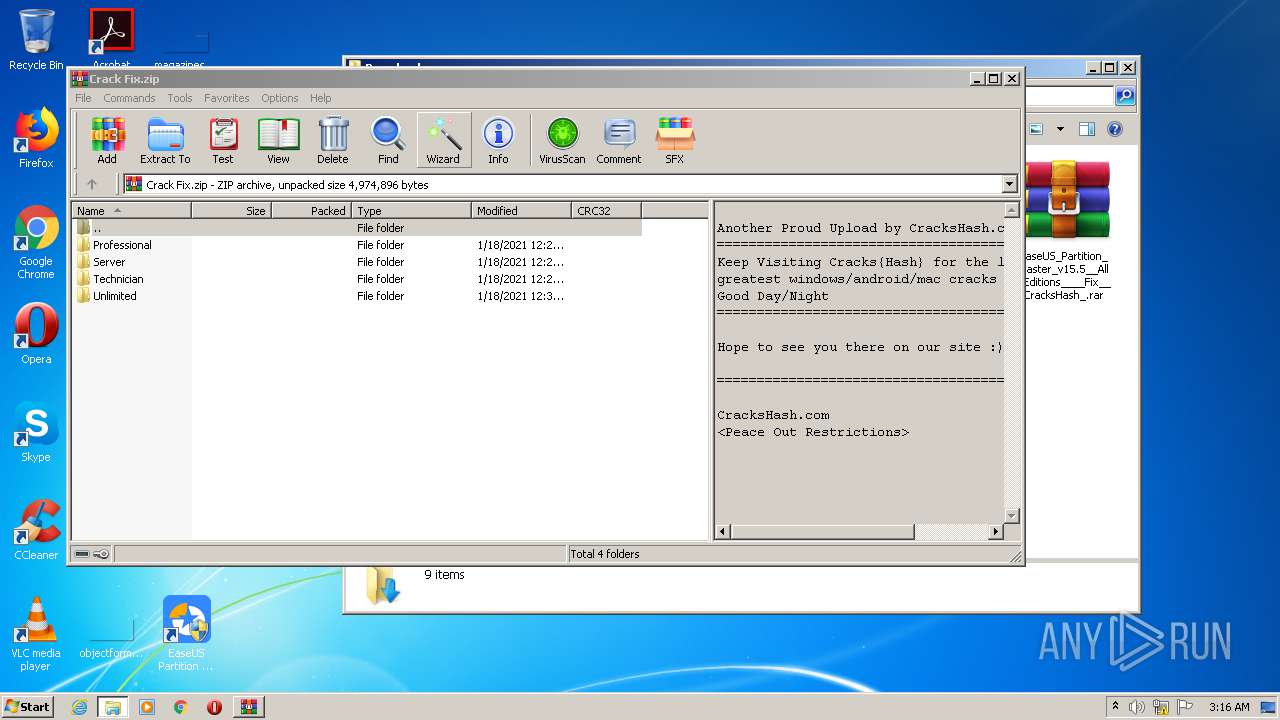
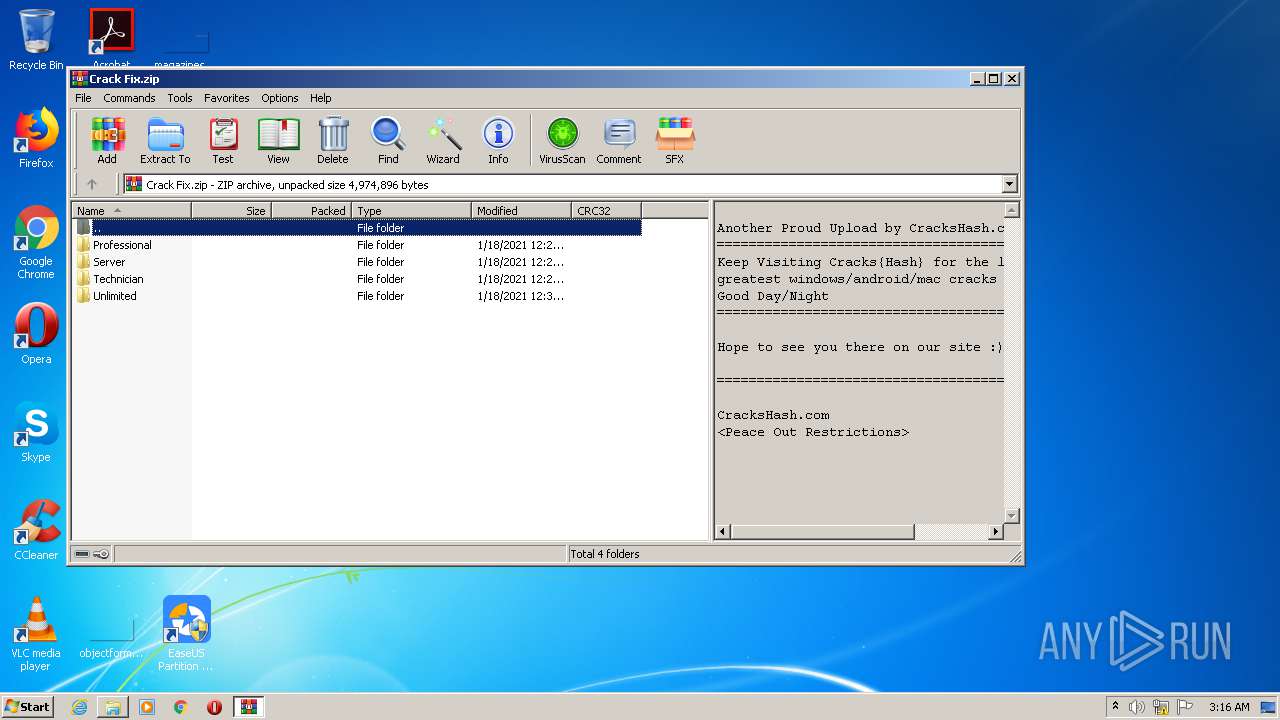
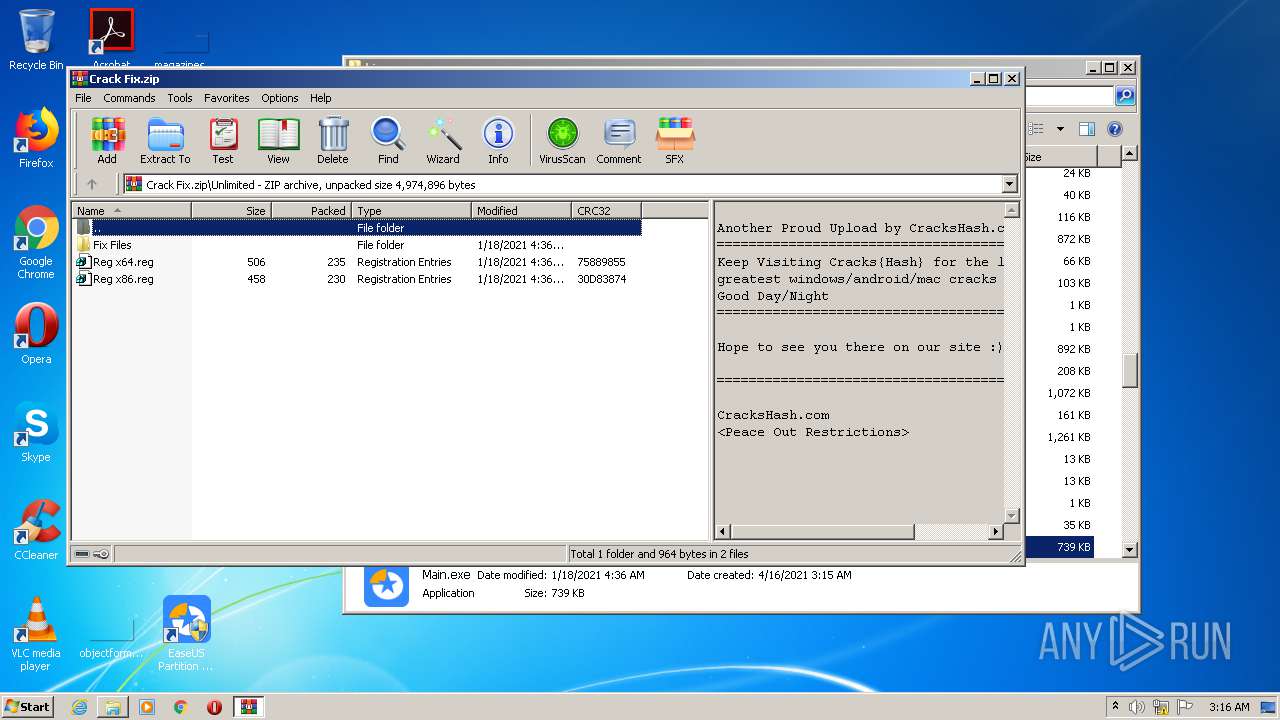
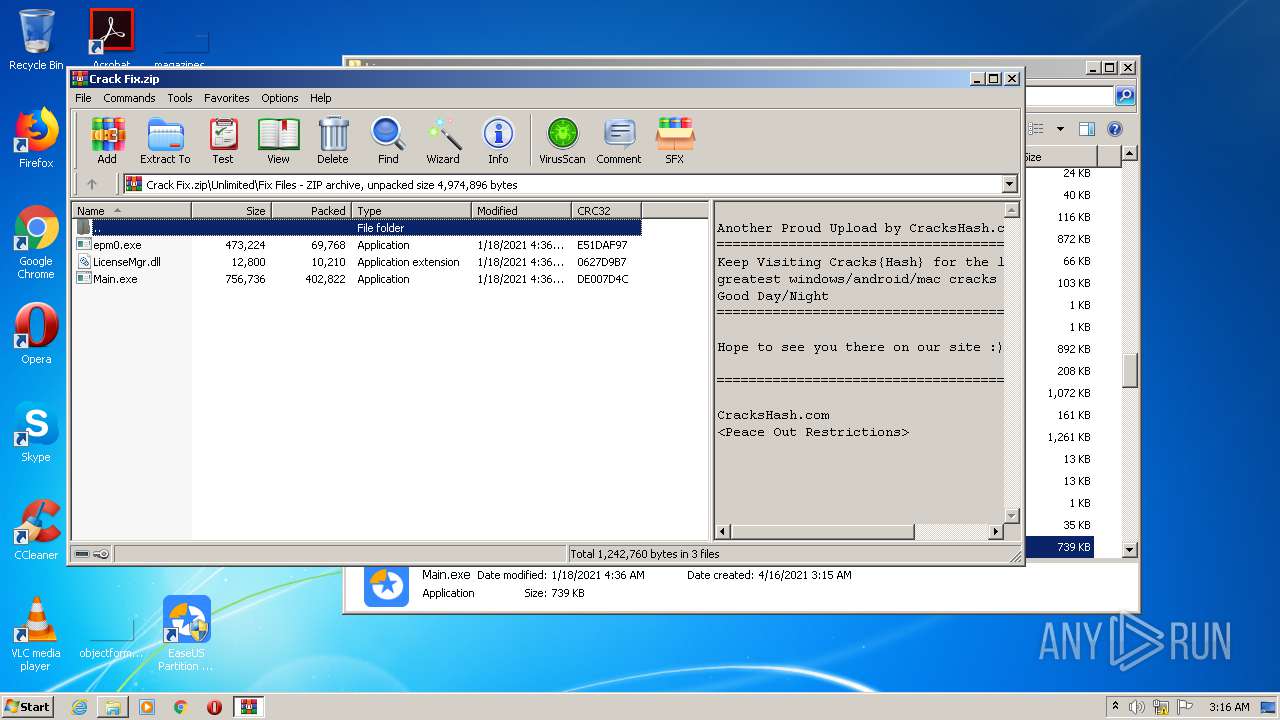
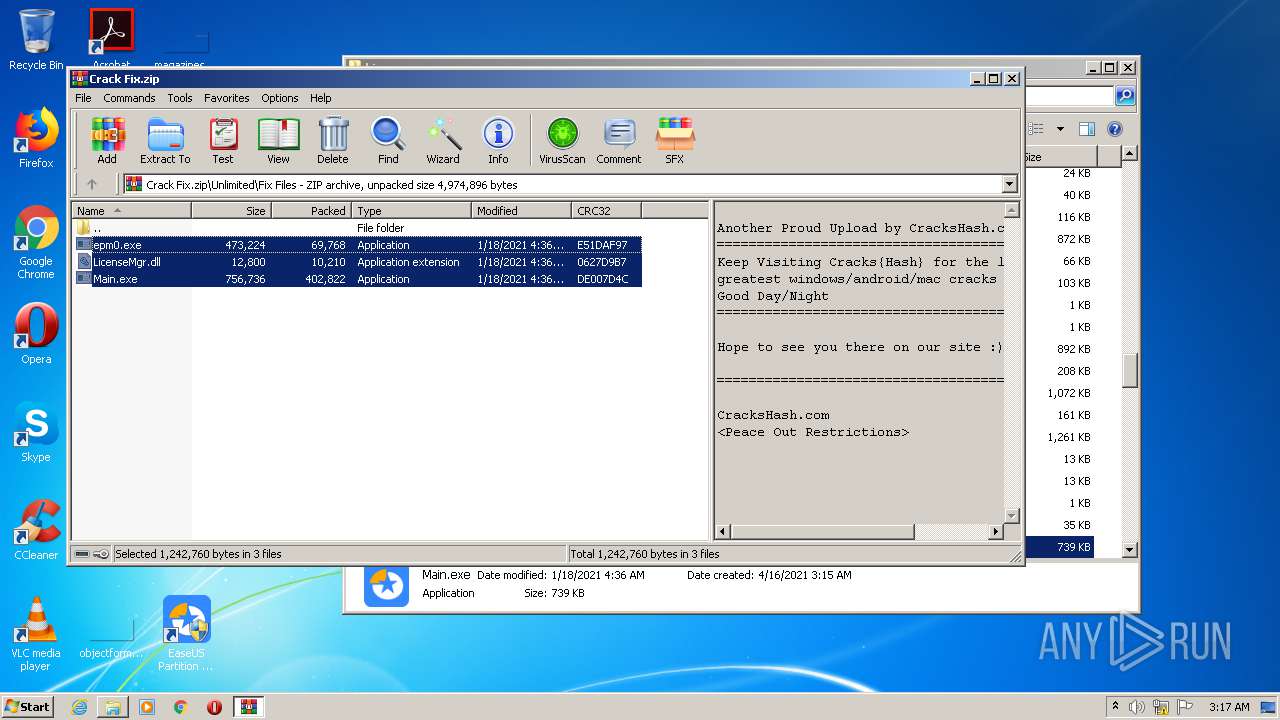
Manual execution by user
- explorer.exe (PID: 716)
- WinRAR.exe (PID: 184)
- epm_setup.exe (PID: 2556)
- WinRAR.exe (PID: 2976)
- epm_setup.exe (PID: 3632)
- WinRAR.exe (PID: 1312)
Application was dropped or rewritten from another process
- epm_setup.tmp (PID: 3884)
Loads dropped or rewritten executable
- epm_setup.tmp (PID: 3884)
Application launched itself
- chrome.exe (PID: 1548)
- iexplore.exe (PID: 1456)
Dropped object may contain Bitcoin addresses
- epm_setup.tmp (PID: 3884)
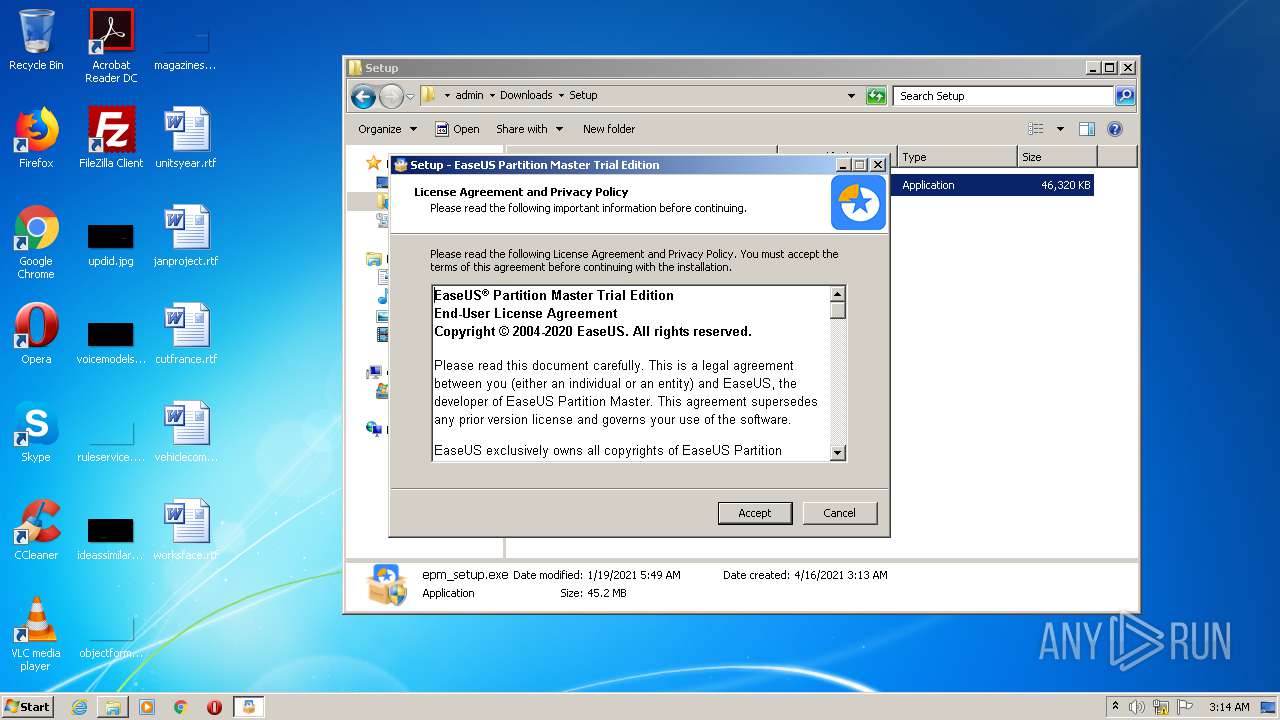
Creates a software uninstall entry
- epm_setup.tmp (PID: 3884)
Reads settings of System Certificates
- iexplore.exe (PID: 4060)
Changes settings of System certificates
- iexplore.exe (PID: 4060)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4060)
Creates files in the user directory
- iexplore.exe (PID: 4060)
Reads internet explorer settings
- iexplore.exe (PID: 4060)
Changes internet zones settings
- iexplore.exe (PID: 1456)
Creates files in the program directory
- epm_setup.tmp (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
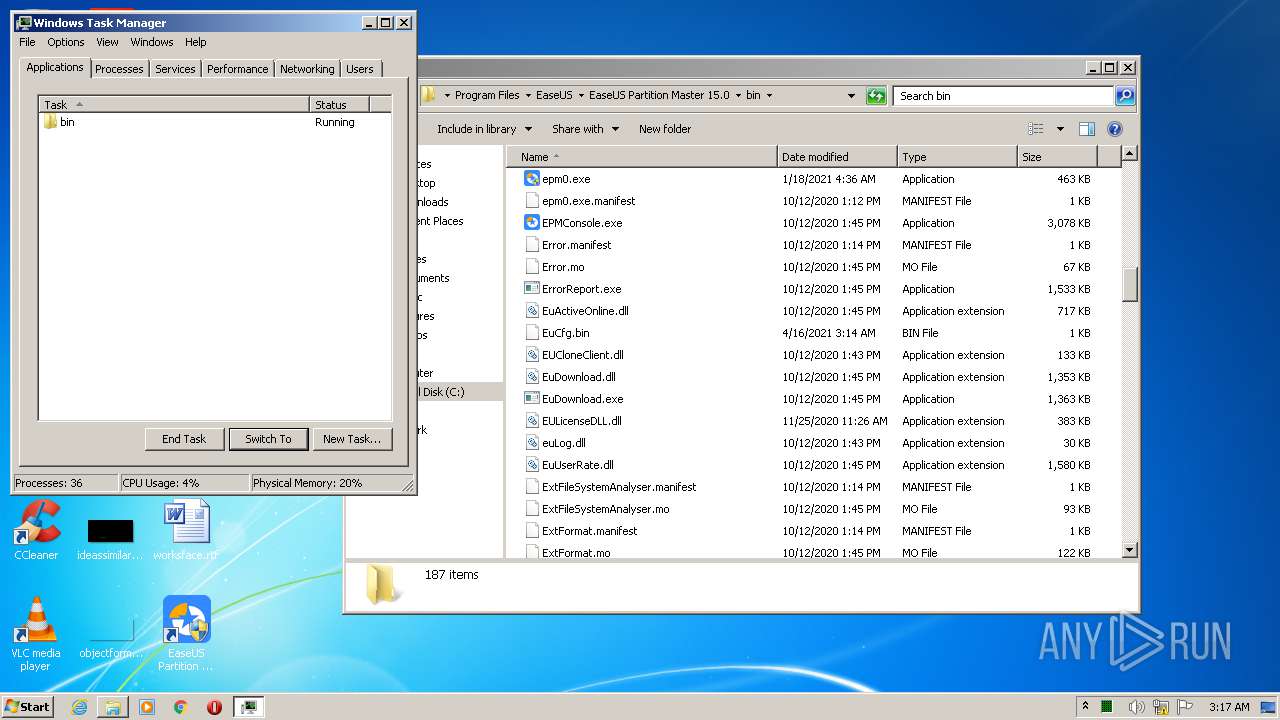
Total processes
154
Monitored processes
76
Malicious processes
20
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
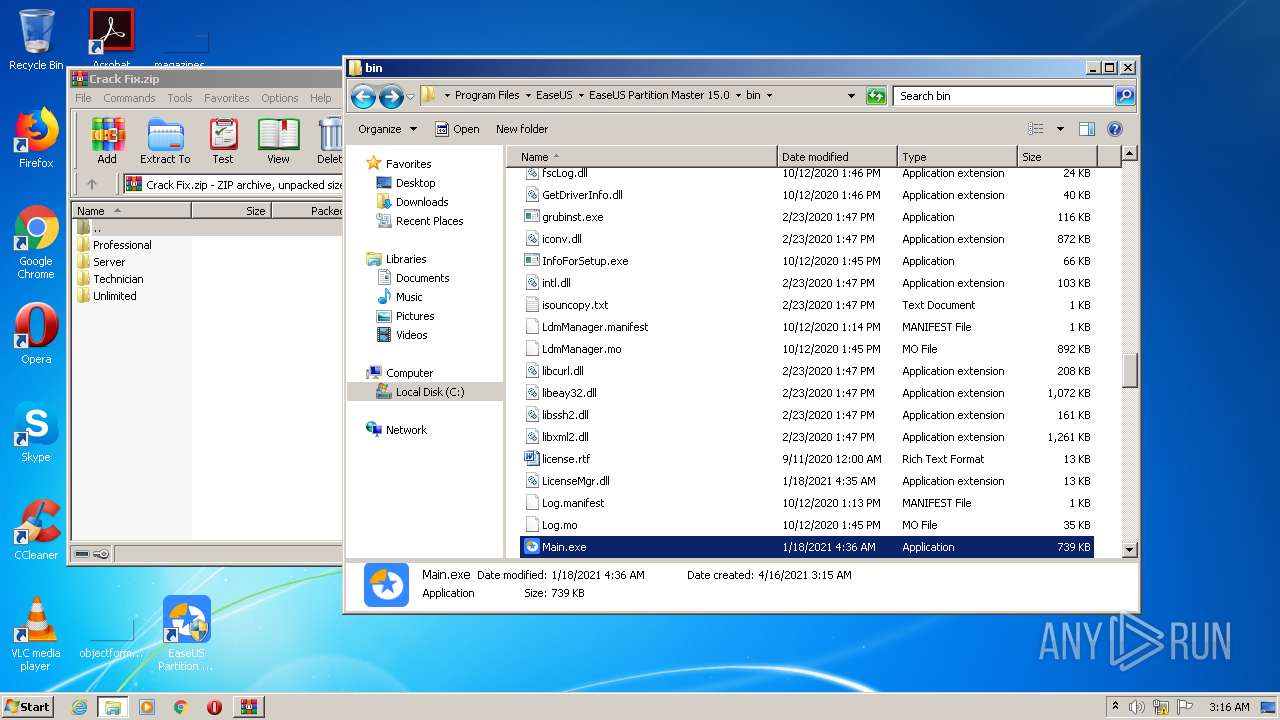
| 184 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\EaseUS_Partition_Master_v15.5__All_Editions____Fix__CracksHash_.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
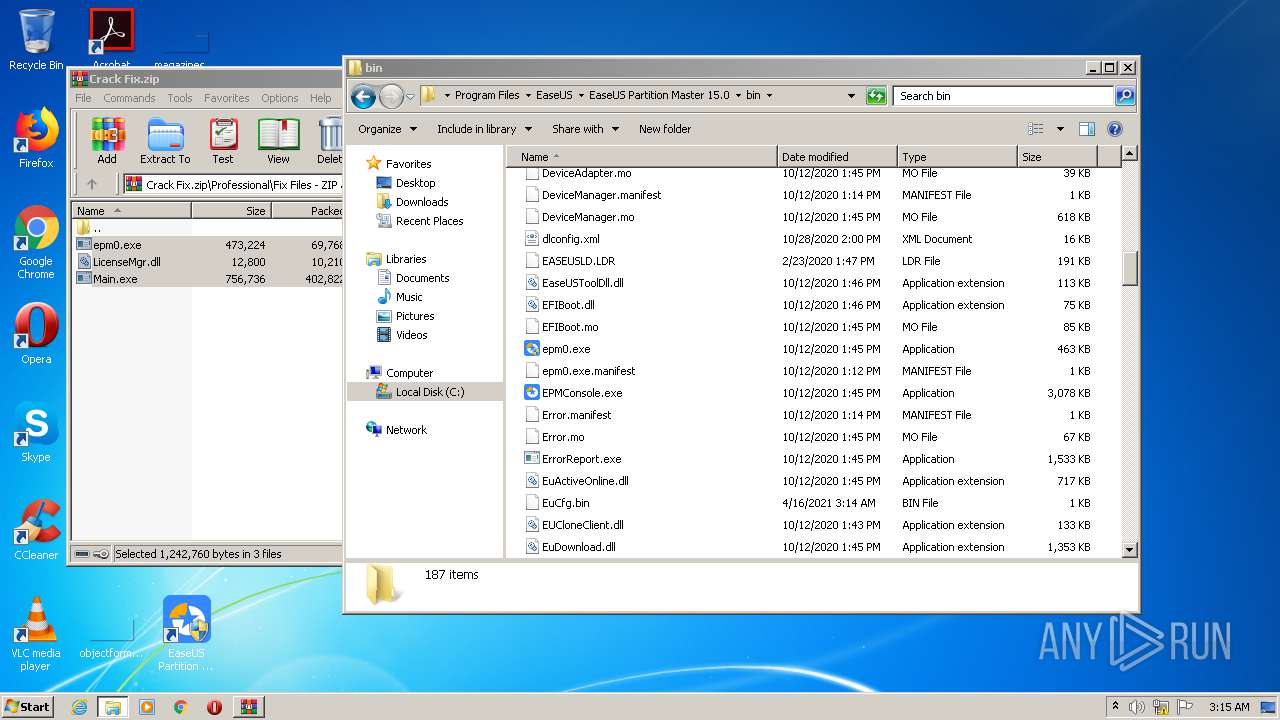
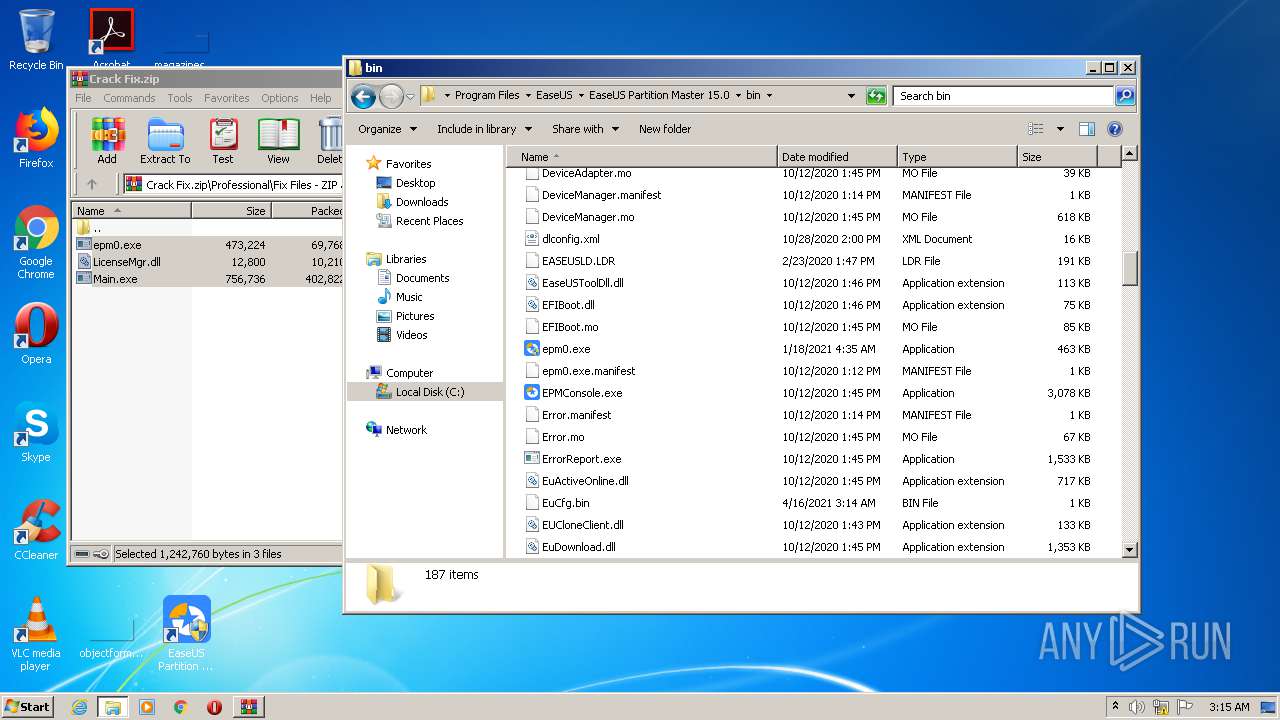
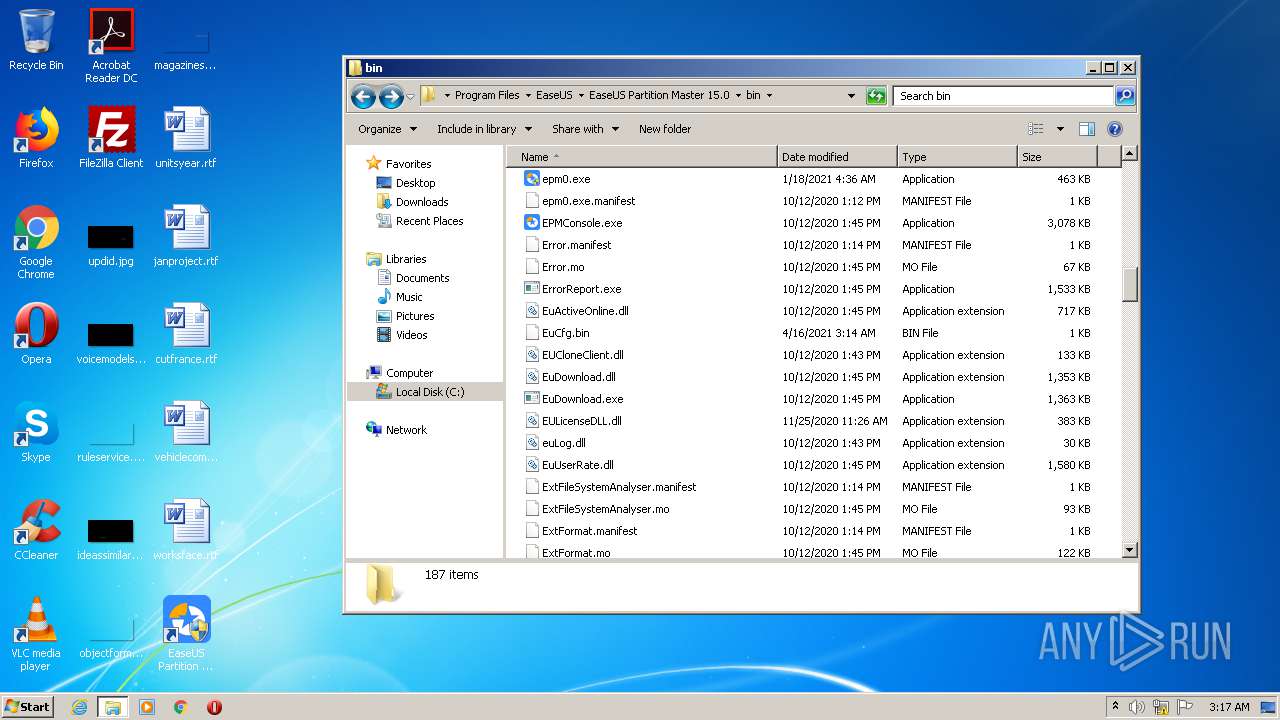
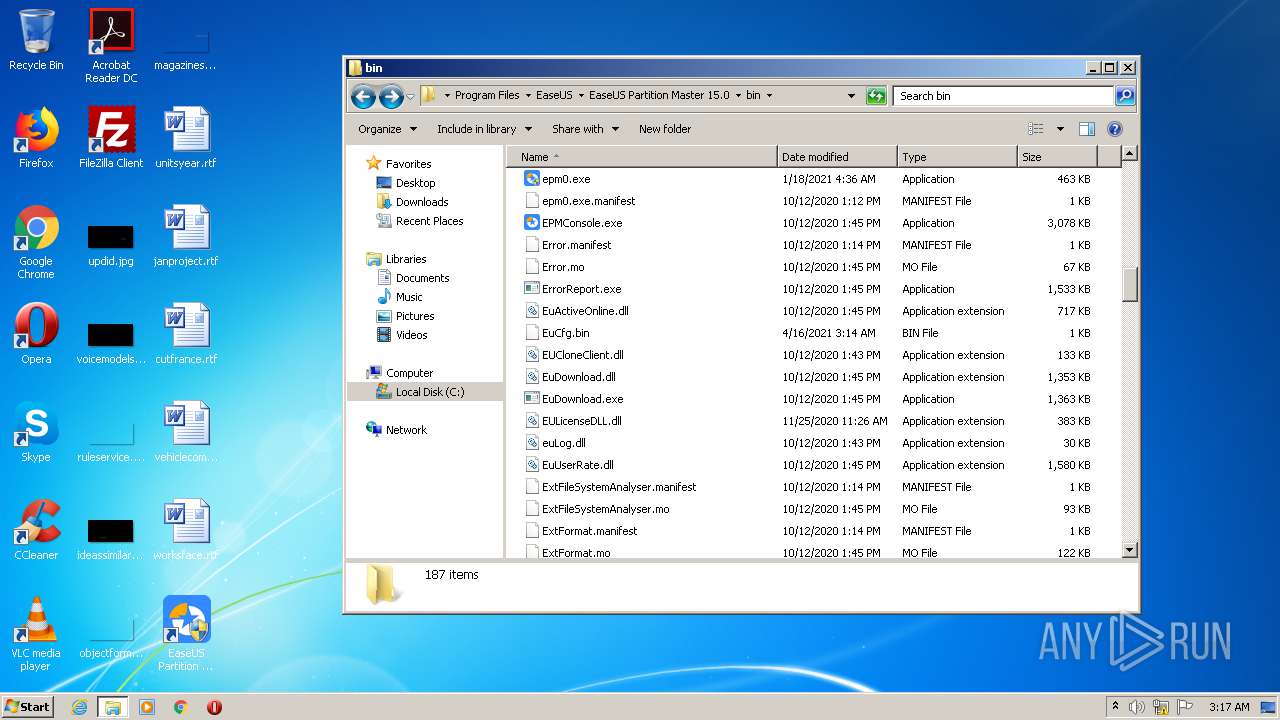
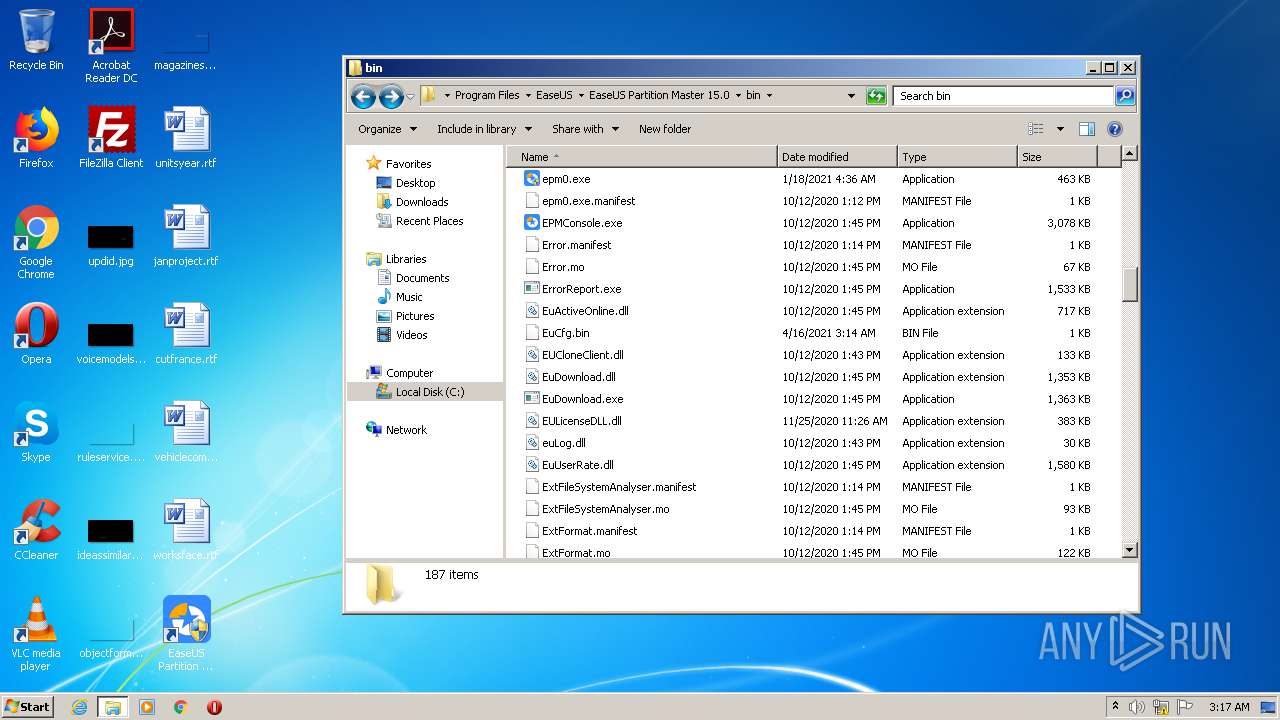
| 316 | "C:\Program Files\EaseUS\EaseUS Partition Master 15.0\bin\epm0.exe" | C:\Program Files\EaseUS\EaseUS Partition Master 15.0\bin\epm0.exe | explorer.exe | ||||||||||||
User: admin Company: EaseUS Integrity Level: HIGH Description: EaseUS Partition Master Loader Application Exit code: 0 Version: 15.5.0.0 Modules
| |||||||||||||||
| 656 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9125632160074386776 --mojo-platform-channel-handle=4068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3283450153751209964 --mojo-platform-channel-handle=3404 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10210592912549265736 --mojo-platform-channel-handle=3880 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,10385802059951406465,4191571536852758493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18363496895695587012 --mojo-platform-channel-handle=1660 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1312 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Crack Fix\Crack Fix.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
8 283
Read events
7 203
Write events
1 049
Delete events
31
Modification events
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1548-13263012773218000 |
Value: 259 | |||
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1548) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
468
Suspicious files
50
Text files
1 320
Unknown types
109
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6078F2A6-60C.pma | — | |
MD5:— | SHA256:— | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4b70e858-0396-42b9-90c7-391370946040.tmp | — | |
MD5:— | SHA256:— | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF12d0d5.TMP | text | |
MD5:1C97B70A4BAD7C026F79467C7D496AFA | SHA256:C5A02E4984DE3F30DADFC0A89A93F45418C06653C3962EAA94C93909E51D272D | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF12d058.TMP | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1548 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12d356.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
38
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1264 | chrome.exe | GET | 200 | 173.194.138.200:80 | http://r3---sn-aigzrn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=85.203.34.125&mm=28&mn=sn-aigzrn7d&ms=nvh&mt=1618538908&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 242 Kb | whitelisted |
1264 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
2552 | AliyunWrapExe.Exe | GET | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=0 | US | binary | 1 b | suspicious |
4060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
4060 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
4060 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.starfieldtech.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCAzkUhA%3D%3D | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1264 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 185.47.40.36:443 | filebin.net | Redpill Linpro AS | NO | malicious |
1264 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 142.250.74.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 172.217.23.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 173.194.138.200:80 | r3---sn-aigzrn7d.gvt1.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 142.250.186.132:443 | www.google.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 142.250.185.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 142.250.185.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 216.58.212.142:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filebin.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-aigzrn7d.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |