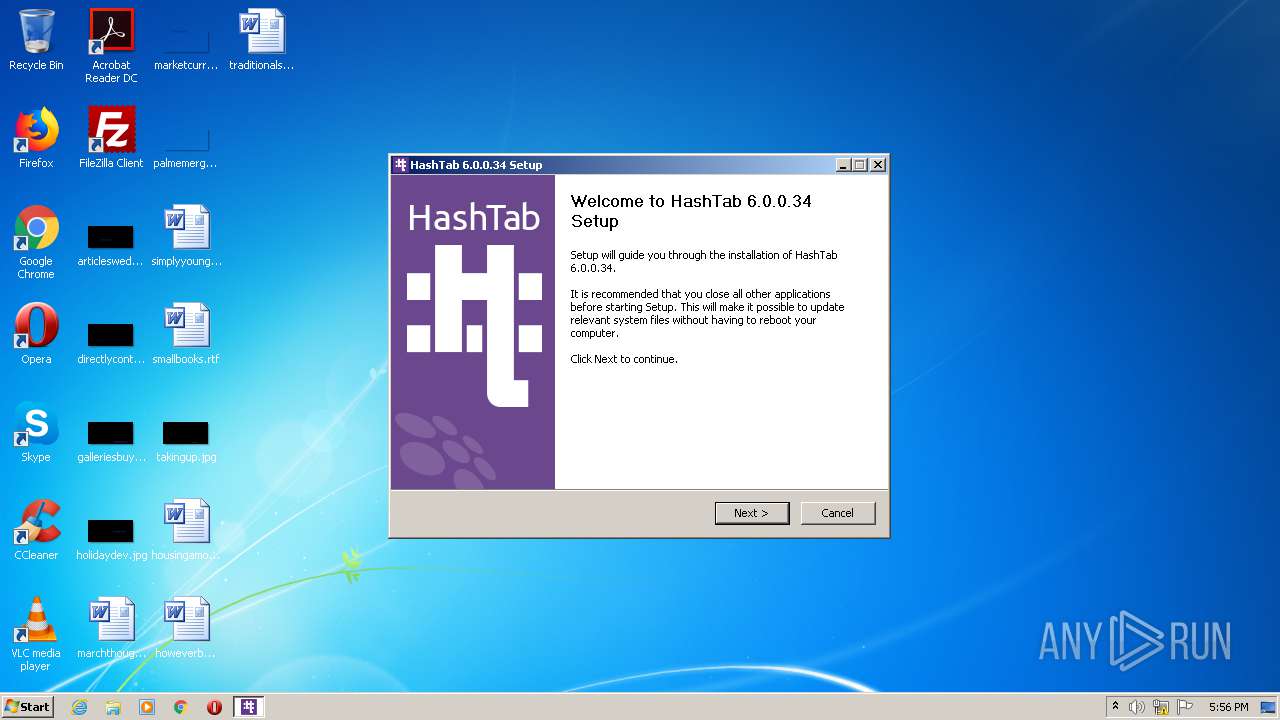
| download: | HashTab_v6.0.0.34_Setup.exe |
| Full analysis: | https://app.any.run/tasks/2b6e9f1e-1630-43cb-acac-8ebdee695119 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2020, 16:56:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 62130C39647BC30A03F654459E9FEE2D |
| SHA1: | 6AF44F2FAD30D5DF85CEEE01CED80085F7C67DC0 |
| SHA256: | 85CAA9EA0BB91DA273E4D02B5F0A1C1736CC7314C4F2C839882339CC69DDAF10 |
| SSDEEP: | 24576:c7LyKHCmlCRWCjgzh5gHE9WIrAp8YOyS1Dm2CyE8rHNQOC:UyKHRERWCszhqEw5qYOygrf1C |
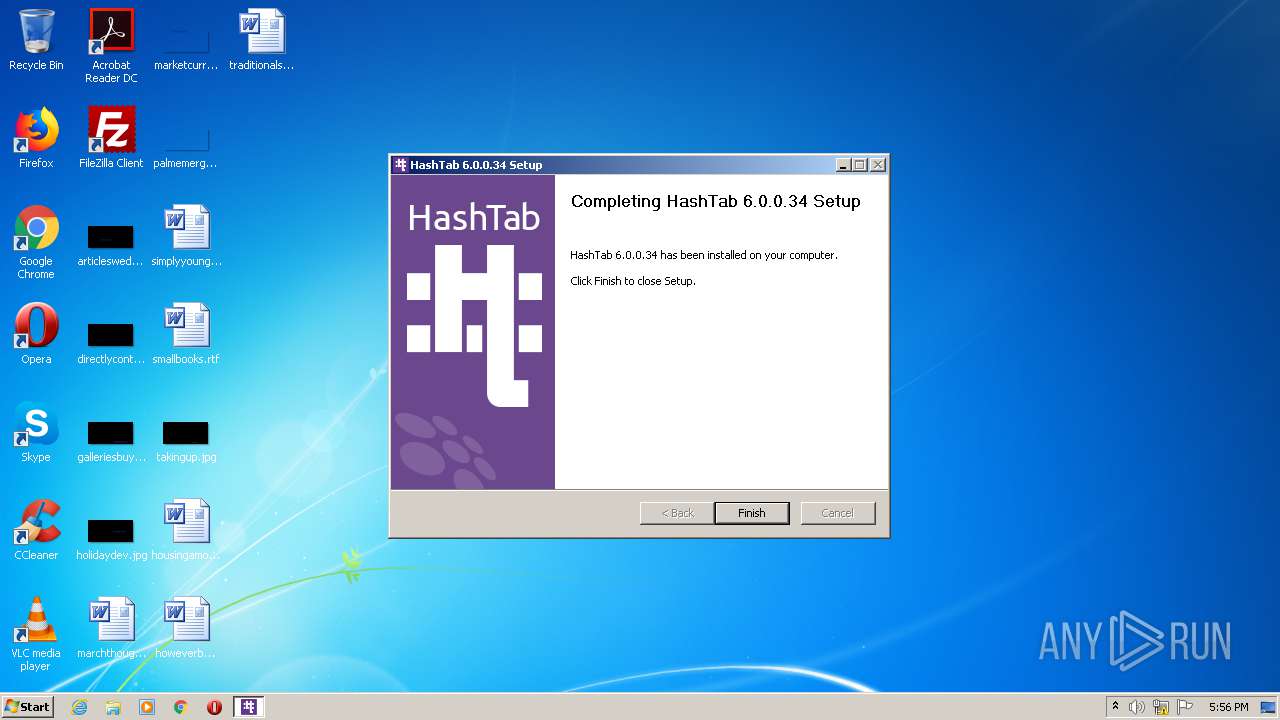
MALICIOUS
Loads dropped or rewritten executable
- HashTab_v6.0.0.34_Setup.exe (PID: 2512)
SUSPICIOUS
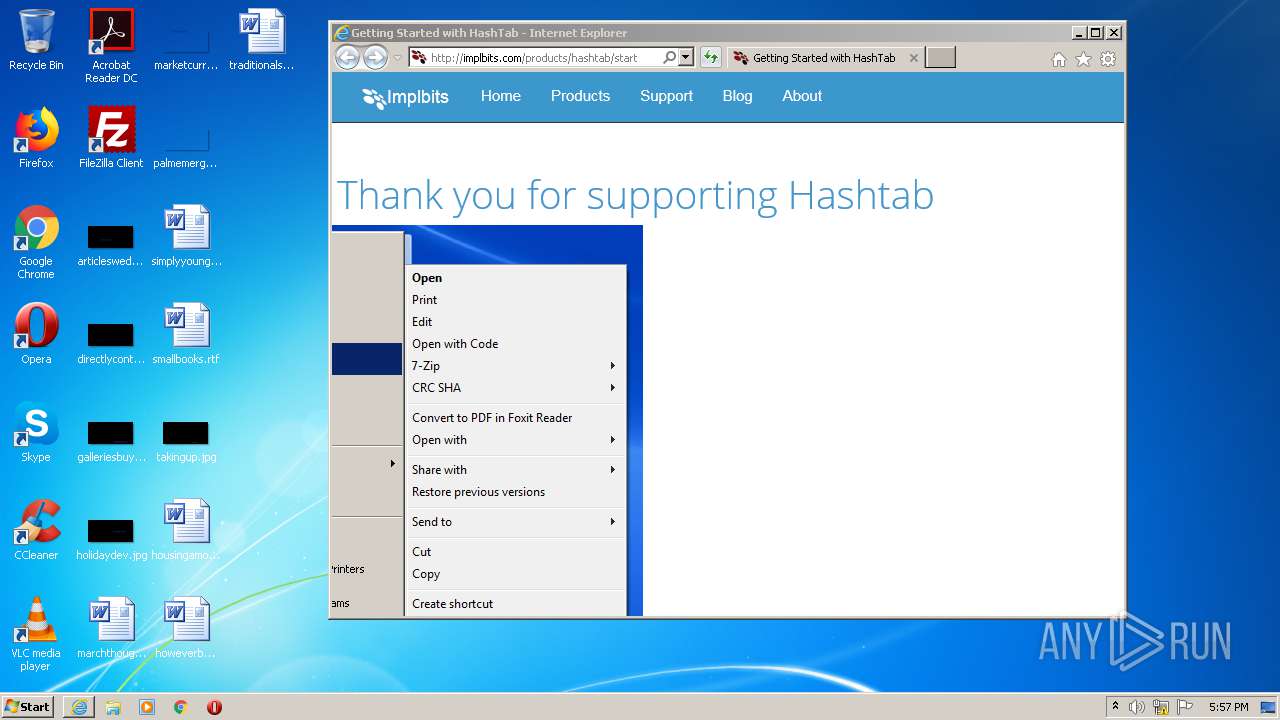
Creates COM task schedule object
- HashTab_v6.0.0.34_Setup.exe (PID: 2512)
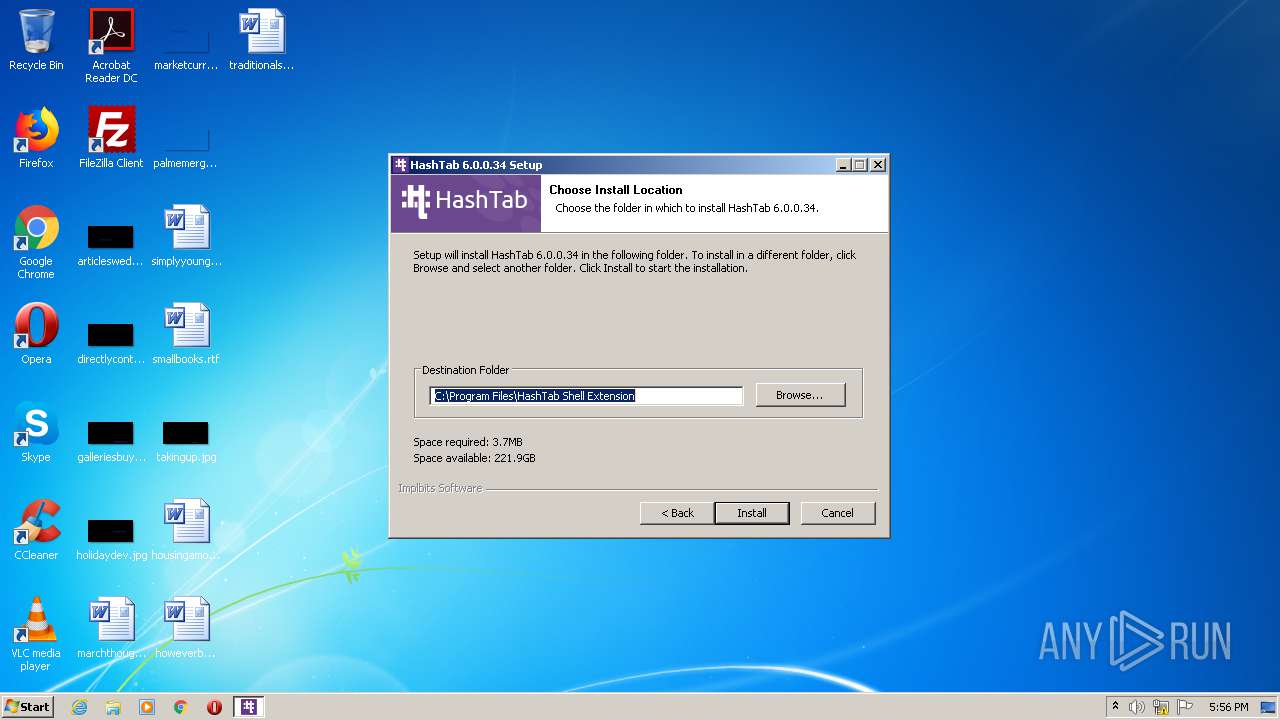
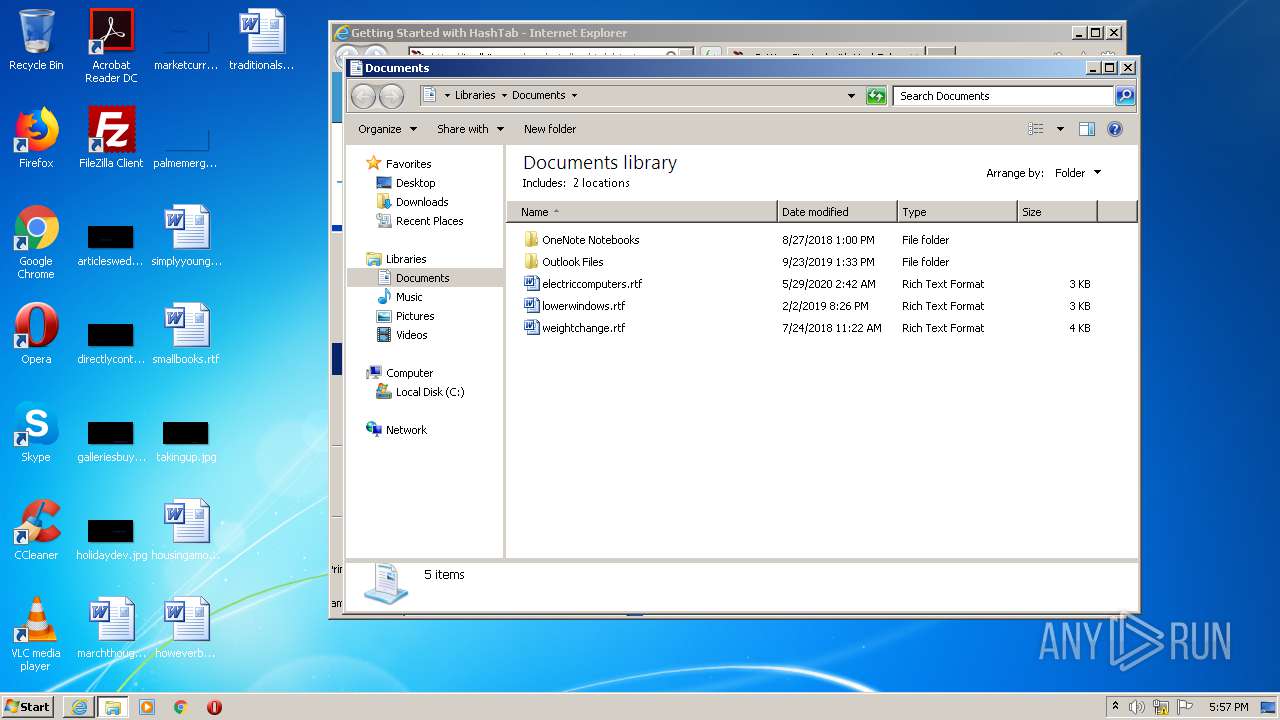
Creates files in the program directory
- HashTab_v6.0.0.34_Setup.exe (PID: 2512)
Executable content was dropped or overwritten
- HashTab_v6.0.0.34_Setup.exe (PID: 2512)
Creates a software uninstall entry
- HashTab_v6.0.0.34_Setup.exe (PID: 2512)
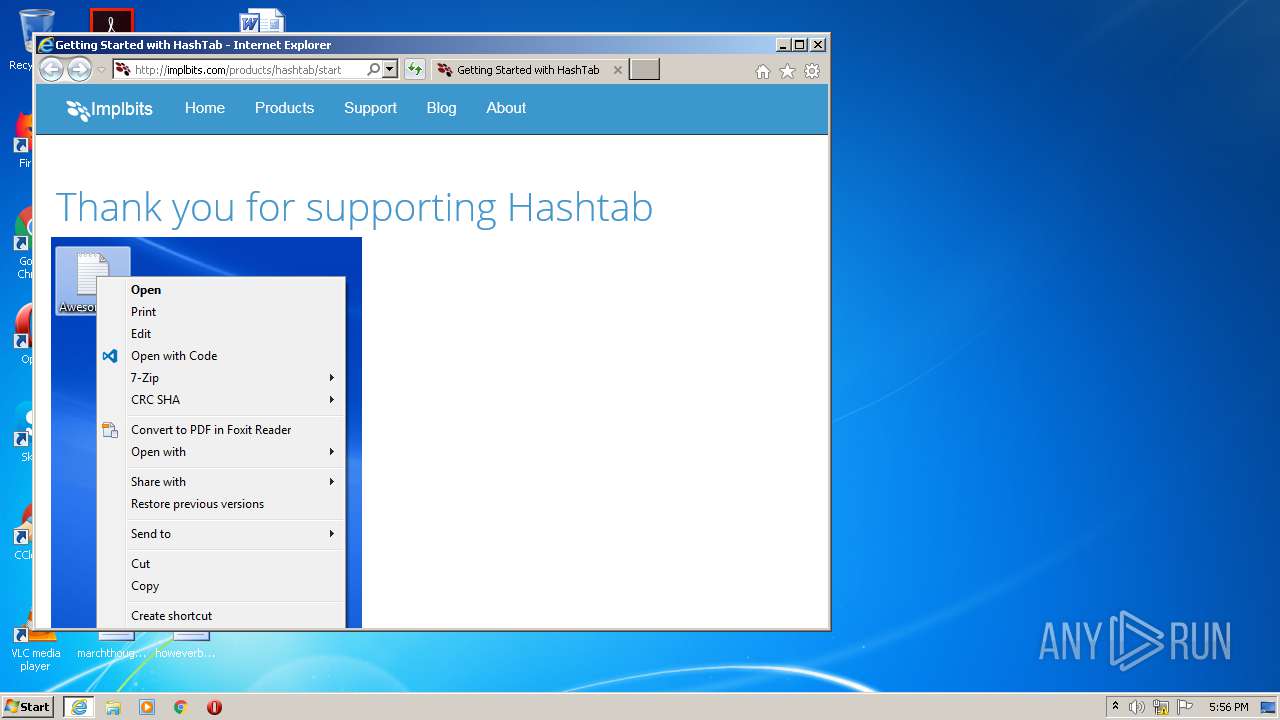
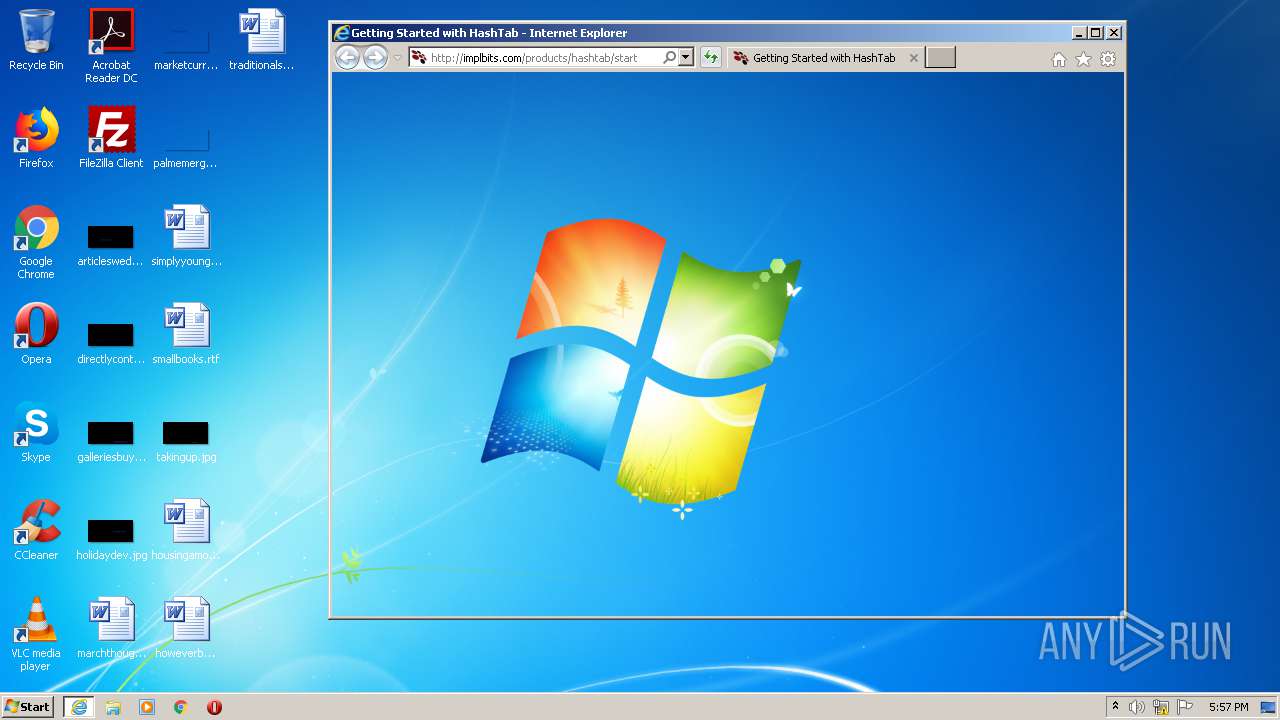
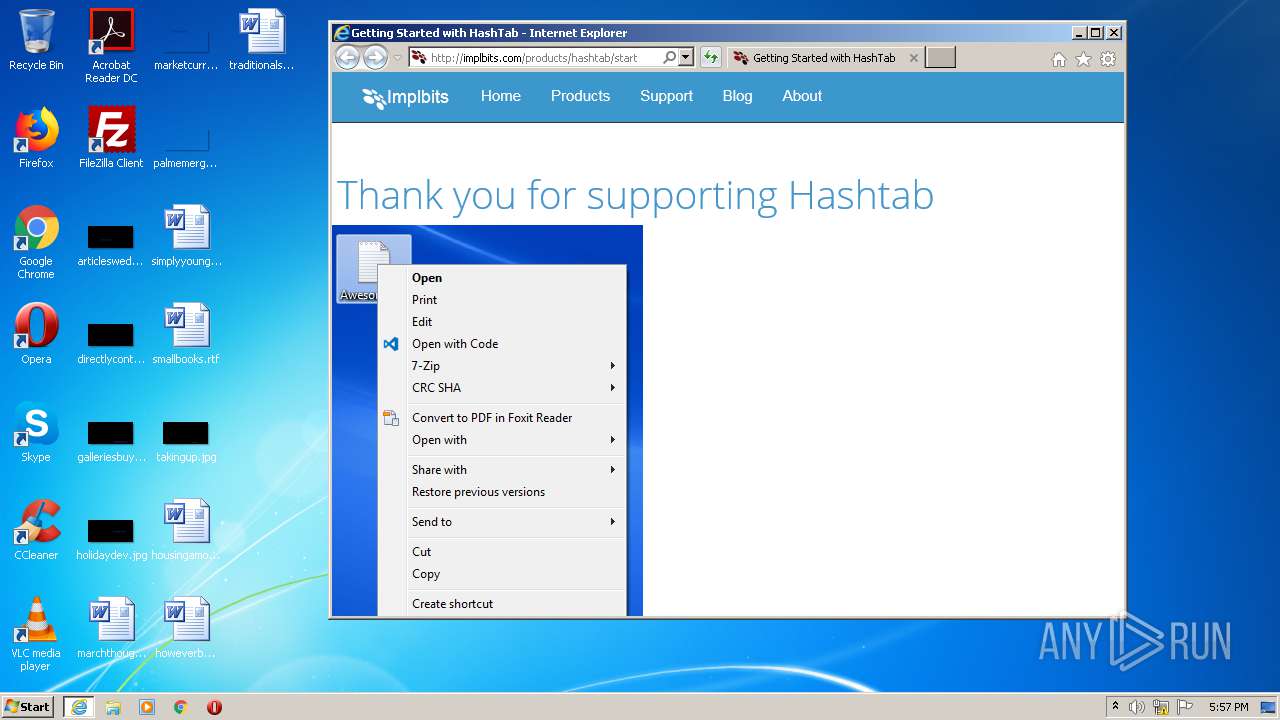
Starts Internet Explorer
- HashTab_v6.0.0.34_Setup.exe (PID: 2512)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3104)
- iexplore.exe (PID: 2972)
Reads internet explorer settings
- iexplore.exe (PID: 2972)
Reads settings of System Certificates
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 3104)
Application launched itself
- iexplore.exe (PID: 3104)
Changes settings of System certificates
- iexplore.exe (PID: 2972)
Changes internet zones settings
- iexplore.exe (PID: 3104)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31a3 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006071 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43434 |
.rdata | 0x00008000 | 0x00001352 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.2373 |
.data | 0x0000A000 | 0x000254F8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03725 |
.ndata | 0x00030000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x00029500 | 0x00029600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.0026 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.77184 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.27049 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 4.12196 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 3.02473 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2512 | "C:\Users\admin\AppData\Local\Temp\HashTab_v6.0.0.34_Setup.exe" | C:\Users\admin\AppData\Local\Temp\HashTab_v6.0.0.34_Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\Temp\HashTab_v6.0.0.34_Setup.exe" | C:\Users\admin\AppData\Local\Temp\HashTab_v6.0.0.34_Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3104 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3104 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.implbits.com/products/hashtab/start | C:\Program Files\Internet Explorer\iexplore.exe | HashTab_v6.0.0.34_Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 450
Read events
1 276
Write events
173
Delete events
1
Modification events
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{0A3C1C8E-5829-4CFD-B1CC-475DB010B883} |
| Operation: | write | Name: | (default) |
Value: HashTab | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\HashTab.DLL |
| Operation: | write | Name: | AppID |
Value: {0A3C1C8E-5829-4CFD-B1CC-475DB010B883} | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved |
| Operation: | write | Name: | {B1883831-F0D8-4453-8245-EEAAD866DD6E} |
Value: HashTab Context Menu | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved |
| Operation: | write | Name: | {8A56567E-A333-4843-B6E1-C3A262E41D8C} |
Value: HashTab Property Page | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\HashTab.DropTargetImpl.1 |
| Operation: | write | Name: | (default) |
Value: DropTargetImpl Class | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\HashTab.DropTargetImpl.1\CLSID |
| Operation: | write | Name: | (default) |
Value: {E7435935-AAEF-4CE2-AD7C-66D46C192A0F} | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\HashTab.DropTargetImpl |
| Operation: | write | Name: | (default) |
Value: DropTargetImpl Class | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\HashTab.DropTargetImpl\CLSID |
| Operation: | write | Name: | (default) |
Value: {E7435935-AAEF-4CE2-AD7C-66D46C192A0F} | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\HashTab.DropTargetImpl\CurVer |
| Operation: | write | Name: | (default) |
Value: HashTab.DropTargetImpl.1 | |||
| (PID) Process: | (2512) HashTab_v6.0.0.34_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E7435935-AAEF-4CE2-AD7C-66D46C192A0F} |
| Operation: | write | Name: | (default) |
Value: DropTargetImpl Class | |||
Executable files
4
Suspicious files
9
Text files
45
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD507.tmp | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarD508.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | HashTab_v6.0.0.34_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsl7D34.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\implbits[1].css | text | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\start[1].htm | html | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\ibits[1].svg | image | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\css[1].css | text | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\bootstrap.min[1].css | text | |
MD5:— | SHA256:— | |||
| 2512 | HashTab_v6.0.0.34_Setup.exe | C:\Program Files\HashTab Shell Extension\uninst.exe | executable | |
MD5:DB6FED01C5A525795AC90DCEA5BDE75E | SHA256:A6C4CDD2E6CF928C1636930FF503ADA217C78A4F594921A8808F5B5D791B2B8E | |||
| 2512 | HashTab_v6.0.0.34_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsl7D34.tmp\InstallOptions.dll | executable | |
MD5:3E277798B9D8F48806FBB5EBFD4990DB | SHA256:FE19353288A08A5D2640A9C022424A1D20E4909A351F2114423E087313A40D7C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
40
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | iexplore.exe | GET | 200 | 192.30.252.153:80 | http://implbits.com/products/hashtab/start | US | html | 1.04 Kb | malicious |
2972 | iexplore.exe | GET | 200 | 192.30.252.153:80 | http://implbits.com/css/bootstrap.min.css | US | text | 18.8 Kb | malicious |
2972 | iexplore.exe | GET | 200 | 192.30.252.153:80 | http://implbits.com/img/hashtab-2.png | US | image | 38.9 Kb | malicious |
2972 | iexplore.exe | GET | 200 | 192.30.252.153:80 | http://implbits.com/img/ibits.svg | US | image | 638 b | malicious |
2972 | iexplore.exe | GET | 200 | 192.30.252.153:80 | http://implbits.com/css/implbits.css | US | text | 1.22 Kb | malicious |
2972 | iexplore.exe | GET | 200 | 172.217.22.74:80 | http://fonts.googleapis.com/css?family=Open+Sans:300italic,400italic,700italic,400,300,700 | US | text | 320 b | whitelisted |
2972 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://fonts.gstatic.com/s/opensans/v17/memnYaGs126MiZpBA-UFUKWyV9hrIqU.woff | US | woff | 17.2 Kb | whitelisted |
2972 | iexplore.exe | GET | 301 | 192.30.252.154:80 | http://www.implbits.com/products/hashtab/start | US | html | 162 b | malicious |
2972 | iexplore.exe | GET | 200 | 192.30.252.153:80 | http://implbits.com/js/neotoma.js | US | text | 854 b | malicious |
2972 | iexplore.exe | GET | 200 | 192.30.252.153:80 | http://implbits.com/img/hashtab-1.png | US | image | 35.2 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | iexplore.exe | 192.30.252.154:80 | www.implbits.com | GitHub, Inc. | US | shared |
2972 | iexplore.exe | 192.30.252.153:80 | www.implbits.com | GitHub, Inc. | US | shared |
2972 | iexplore.exe | 209.197.3.15:80 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2972 | iexplore.exe | 172.217.16.195:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.74:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2972 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2972 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3104 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3104 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.implbits.com |
| malicious |
implbits.com |
| malicious |
code.jquery.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |