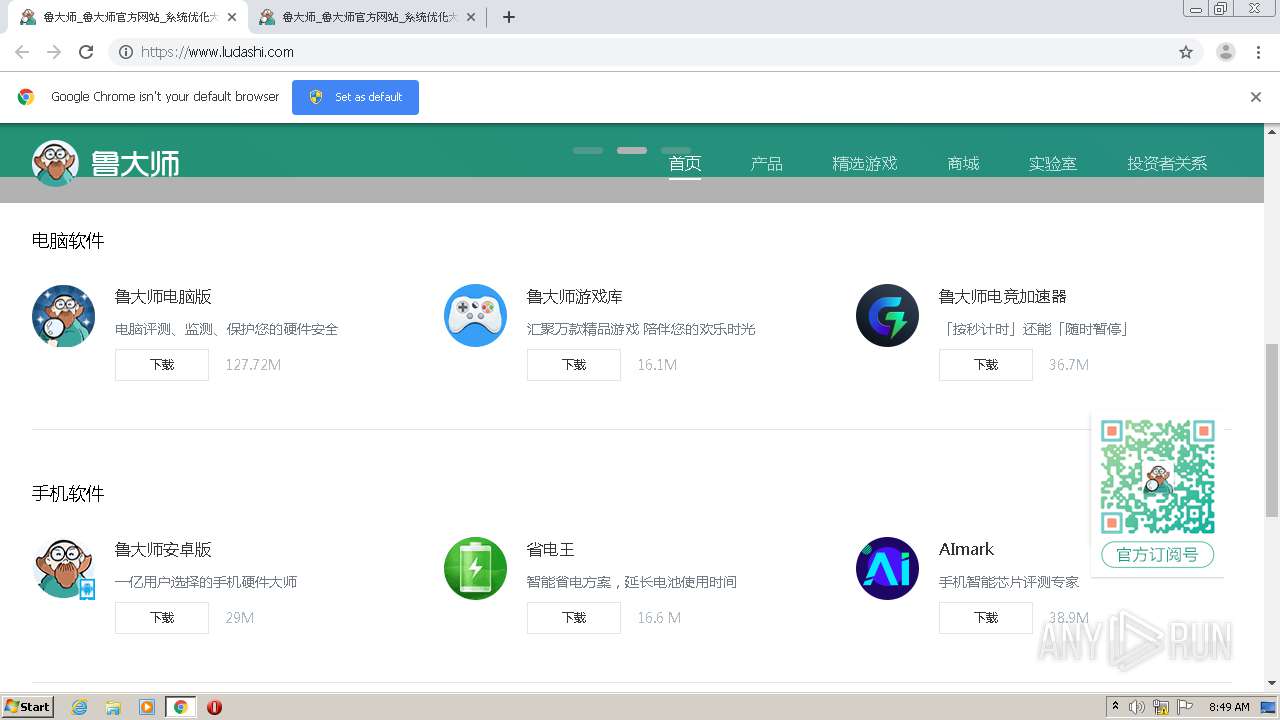
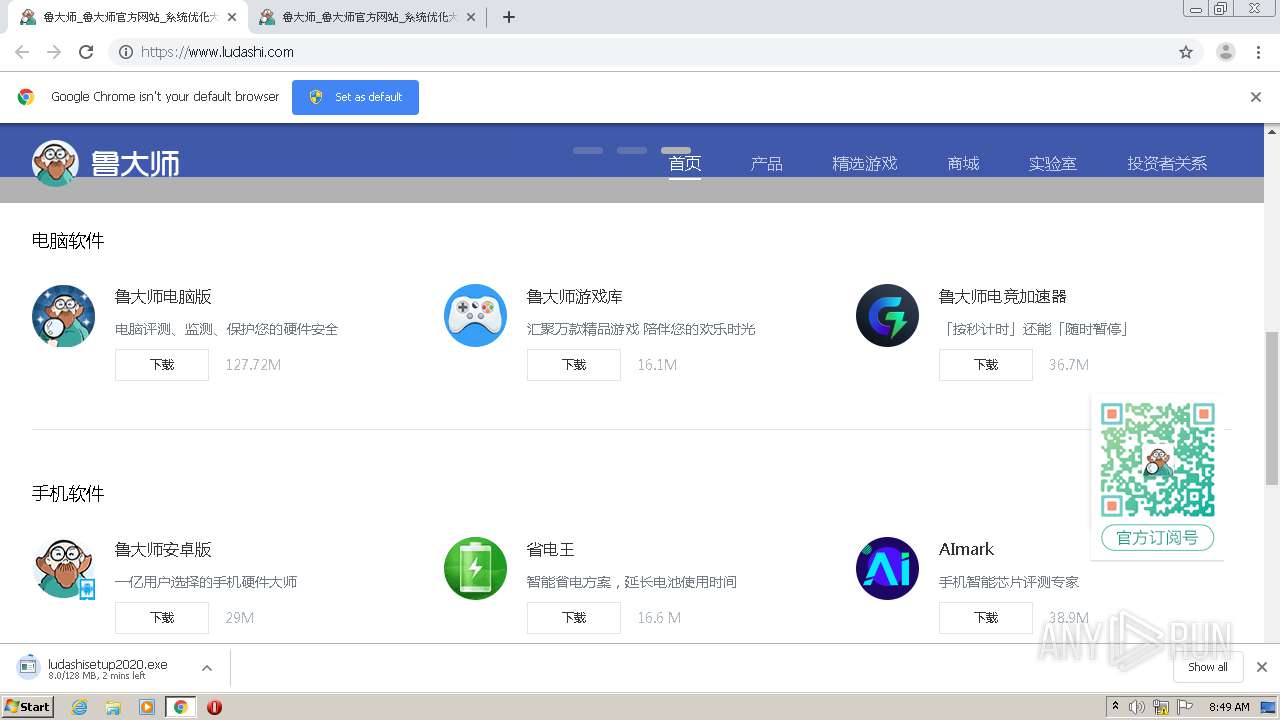
| URL: | http://ludashi.com/ |
| Full analysis: | https://app.any.run/tasks/7567d36b-0273-477e-a5b4-9baf668e70da |
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2020, 08:48:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7136AC66AF60D60A29287DCD9041858E |
| SHA1: | B850A5997D288CF710888DE796ACD4E7FB0A5E51 |
| SHA256: | 85C83047D06DA5D3A123185A306C96B7EBE66119E404CE60B136ABD5BE085383 |
| SSDEEP: | 3:N1KSQFNMt:CSUMt |
MALICIOUS
Application was dropped or rewritten from another process
- ludashisetup2020.exe (PID: 3536)
- ludashisetup2020.exe (PID: 3276)
- KB931125.exe (PID: 3308)
- updroots.exe (PID: 3676)
- updroots.exe (PID: 2472)
- updroots.exe (PID: 2272)
- updroots.exe (PID: 2784)
Changes the autorun value in the registry
- KB931125.exe (PID: 3308)
Drops executable file immediately after starts
- ludashisetup2020.exe (PID: 3276)
- KB931125.exe (PID: 3308)
Changes settings of System certificates
- updroots.exe (PID: 3676)
- updroots.exe (PID: 2472)
- ludashisetup2020.exe (PID: 3276)
- updroots.exe (PID: 2272)
SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 2728)
- KB931125.exe (PID: 3308)
Drops a file with too old compile date
- ludashisetup2020.exe (PID: 3276)
- KB931125.exe (PID: 3308)
Executable content was dropped or overwritten
- chrome.exe (PID: 2728)
- KB931125.exe (PID: 3308)
- ludashisetup2020.exe (PID: 3276)
Drops a file that was compiled in debug mode
- ludashisetup2020.exe (PID: 3276)
- KB931125.exe (PID: 3308)
Low-level read access rights to disk partition
- ludashisetup2020.exe (PID: 3276)
Adds / modifies Windows certificates
- updroots.exe (PID: 3676)
- updroots.exe (PID: 2472)
- ludashisetup2020.exe (PID: 3276)
INFO
Application launched itself
- chrome.exe (PID: 2728)
Reads the hosts file
- chrome.exe (PID: 2728)
- chrome.exe (PID: 2428)
Reads settings of System Certificates
- chrome.exe (PID: 2728)
- ludashisetup2020.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
18
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,10216282300834464934,13764971542981919432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4122625679467256275 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,10216282300834464934,13764971542981919432,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11066734746921360154 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,10216282300834464934,13764971542981919432,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6728377285210595186 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,10216282300834464934,13764971542981919432,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5482200442406413566 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2272 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updroots.exe -l roots.sst | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updroots.exe | — | KB931125.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: UPDROOTS Exit code: 0 Version: 5.1.2484.0 (main.010529-2005) Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10216282300834464934,13764971542981919432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4301837800851474075 --mojo-platform-channel-handle=1488 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2472 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updroots.exe updroots.sst | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updroots.exe | — | KB931125.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: UPDROOTS Exit code: 0 Version: 5.1.2484.0 (main.010529-2005) Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2732 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://ludashi.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2784 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updroots.exe -d delroots.sst | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updroots.exe | — | KB931125.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 879
Read events
1 244
Write events
1 316
Delete events
319
Modification events
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2728-13252495759753000 |
Value: 259 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
8
Suspicious files
19
Text files
78
Unknown types
1
Dropped files
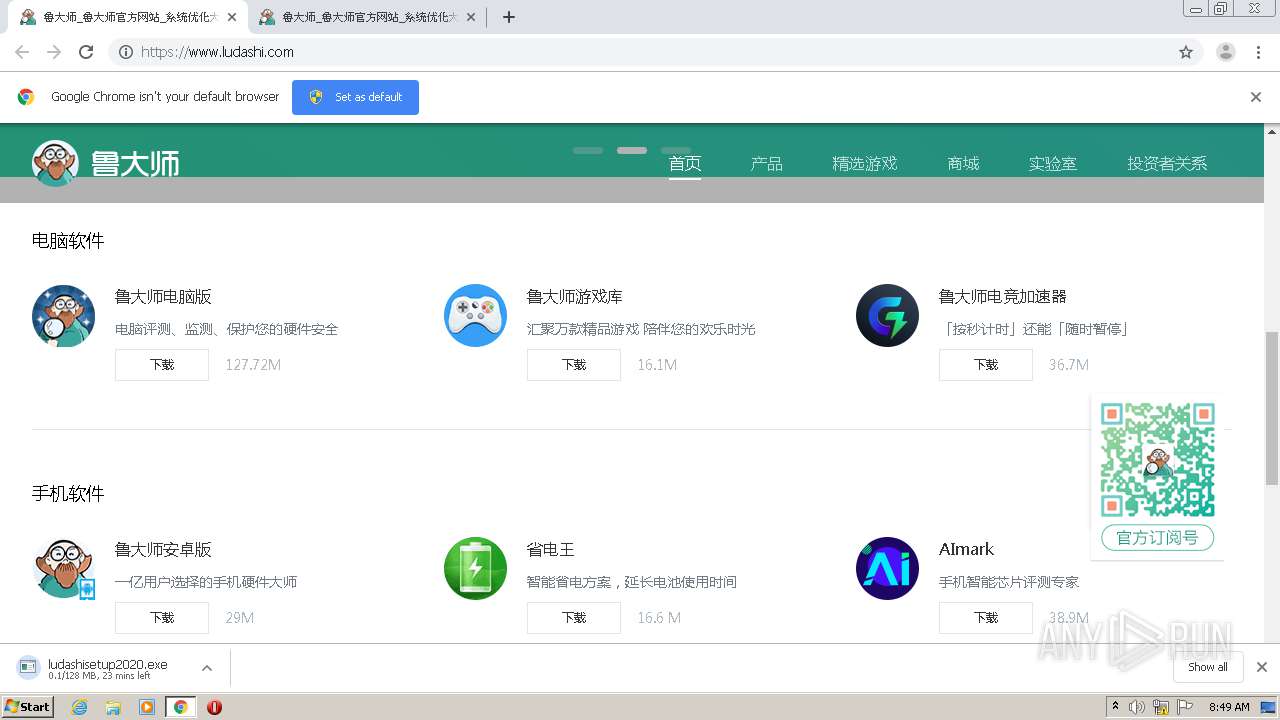
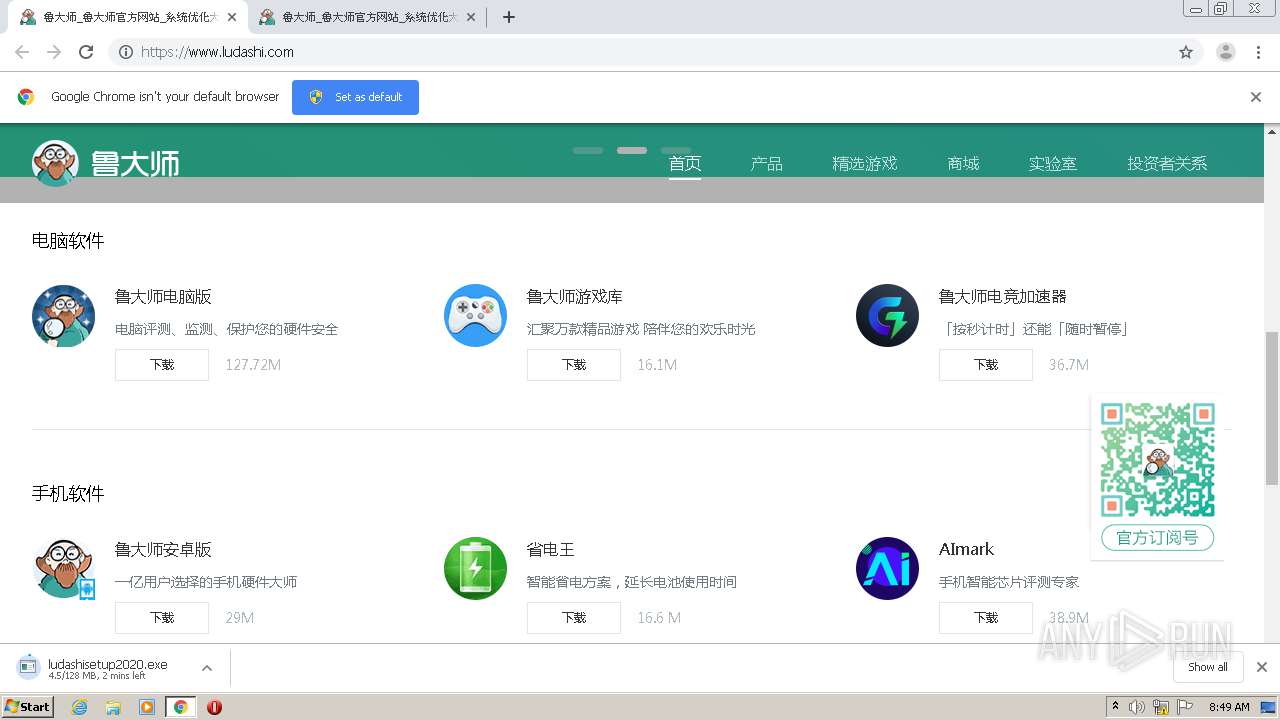
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FD87890-AA8.pma | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3d5d501e-f00f-4f24-961a-2241b15b008c.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF153ee7.TMP | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF153f45.TMP | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF154129.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
39
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | ludashisetup2020.exe | GET | 200 | 112.126.122.111:80 | http://s.ludashi.com/url2?pid=ludashi&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=6.1020.3030.1215&modver=6.1020.3030.1215&type=instnew&action=prepare_file&ex_ary[ex7]=4 | CN | — | — | suspicious |
— | — | GET | — | 112.126.122.111:80 | http://s.ludashi.com/url2?pid=ludashi&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=6.1020.3030.1215&modver=6.1020.3030.1215&type=instnew&action=prepare_init_netbridge&ex_ary[ex7]=4 | CN | — | — | suspicious |
3276 | ludashisetup2020.exe | GET | 200 | 112.126.122.111:80 | http://s.ludashi.com/url2?pid=ludashi&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=6.1020.3030.1215&modver=6.1020.3030.1215&type=instnew&action=res_pid&ex_ary[ex7]=4 | CN | — | — | suspicious |
3276 | ludashisetup2020.exe | GET | 200 | 112.126.122.111:80 | http://s.ludashi.com/url2?pid=ludashi&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=6.1020.3030.1215&modver=6.1020.3030.1215&type=instnew&action=run&ex_ary[ex7]=4 | CN | — | — | suspicious |
3276 | ludashisetup2020.exe | GET | 200 | 112.126.122.111:80 | http://s.ludashi.com/url2?pid=ludashi&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=6.1020.3030.1215&modver=6.1020.3030.1215&type=instnew&action=setup_pid&ex_ary[ex7]=4 | CN | — | — | suspicious |
3276 | ludashisetup2020.exe | GET | 200 | 112.126.122.111:80 | http://s.ludashi.com/url2?pid=ludashi&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=6.1020.3030.1215&modver=6.1020.3030.1215&type=instnew&action=prepare_init_7z&ex_ary[ex7]=4 | CN | — | — | suspicious |
3276 | ludashisetup2020.exe | GET | — | 114.116.39.220:80 | http://www.ludashi.com/cms/pc_mobile/quickxiaolu.php?channel=ludashi&s=0&q=0&k=0&h=0 | CN | — | — | suspicious |
— | — | GET | — | 112.126.122.111:80 | http://s.ludashi.com/url2?pid=ludashi&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=6.1020.3030.1215&modver=6.1020.3030.1215&type=instnew&action=prepare_check_inst_limit&ex_ary[ex7]=4 | CN | — | — | suspicious |
— | — | GET | — | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
— | — | GET | — | 112.126.122.111:80 | http://s.ludashi.com/url2?pid=ludashi&mid=98fbba90914e8b88d84161065028cd94&mid2=0df2acc0e9a4e42dc278db3d0cbafd6a76b4ffda2bf4&appver=6.1020.3030.1215&modver=6.1020.3030.1215&type=instnew&action=prepare_check_setup_ok&ex_ary[ex7]=4 | CN | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2428 | chrome.exe | 114.116.39.220:80 | ludashi.com | — | CN | suspicious |
2428 | chrome.exe | 173.194.220.84:443 | accounts.google.com | Google Inc. | US | unknown |
2428 | chrome.exe | 114.116.39.220:443 | ludashi.com | — | CN | suspicious |
2428 | chrome.exe | 47.246.59.232:80 | cdn-img.ludashi.com | — | US | unknown |
2428 | chrome.exe | 203.119.215.3:443 | z3.cnzz.com | — | CN | unknown |
2428 | chrome.exe | 106.11.84.7:443 | hm2.cnzz.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2428 | chrome.exe | 115.231.155.220:443 | cdn-file-ssl-pc.ludashi.com | No.31,Jin-rong Street | CN | suspicious |
2428 | chrome.exe | 143.204.202.78:80 | p0.qhimg.com | — | US | suspicious |
2428 | chrome.exe | 172.217.18.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
3276 | ludashisetup2020.exe | 114.116.39.220:80 | ludashi.com | — | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ludashi.com |
| whitelisted |
accounts.google.com |
| shared |
www.ludashi.com |
| suspicious |
cdn-file.ludashi.com |
| suspicious |
s0.ssl.qhimg.com |
| whitelisted |
cdn-img.ludashi.com |
| whitelisted |
s4.cnzz.com |
| whitelisted |
s.360.cn |
| whitelisted |
c.cnzz.com |
| whitelisted |
z3.cnzz.com |
| whitelisted |