| File name: | 075f08419c69a46a2d2986913c92d4c0N.exe |
| Full analysis: | https://app.any.run/tasks/845c16de-196a-4590-a3ac-cf495531dba6 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2024, 11:57:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 075F08419C69A46A2D2986913C92D4C0 |
| SHA1: | C04F9D95A502349074A77FD92AD35CA788A5A9C7 |
| SHA256: | 85BF5EEE950E9A42488A11530CF32D0662AC786F8B82B32E0551CA7C8EFC1E7E |
| SSDEEP: | 3072:CVTetbZDl2mGbjyZAjDD+3Sl0Tq6WdkGuYhhp9a+Wag1oWxsKG+Lfj0cFmv96ece:hfx4kWdkGuelL+Lfiv9ffd3x |
MALICIOUS
Drops the executable file immediately after the start
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 3724)
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
SUSPICIOUS
Executable content was dropped or overwritten
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
Reads the date of Windows installation
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
Reads security settings of Internet Explorer
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
- jusched.exe (PID: 2668)
Connects to FTP
- jusched.exe (PID: 2668)
INFO
Checks supported languages
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 3724)
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
- jusched.exe (PID: 2668)
Creates files or folders in the user directory
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 3724)
Reads the computer name
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 3724)
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
- jusched.exe (PID: 2668)
Creates files in the program directory
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
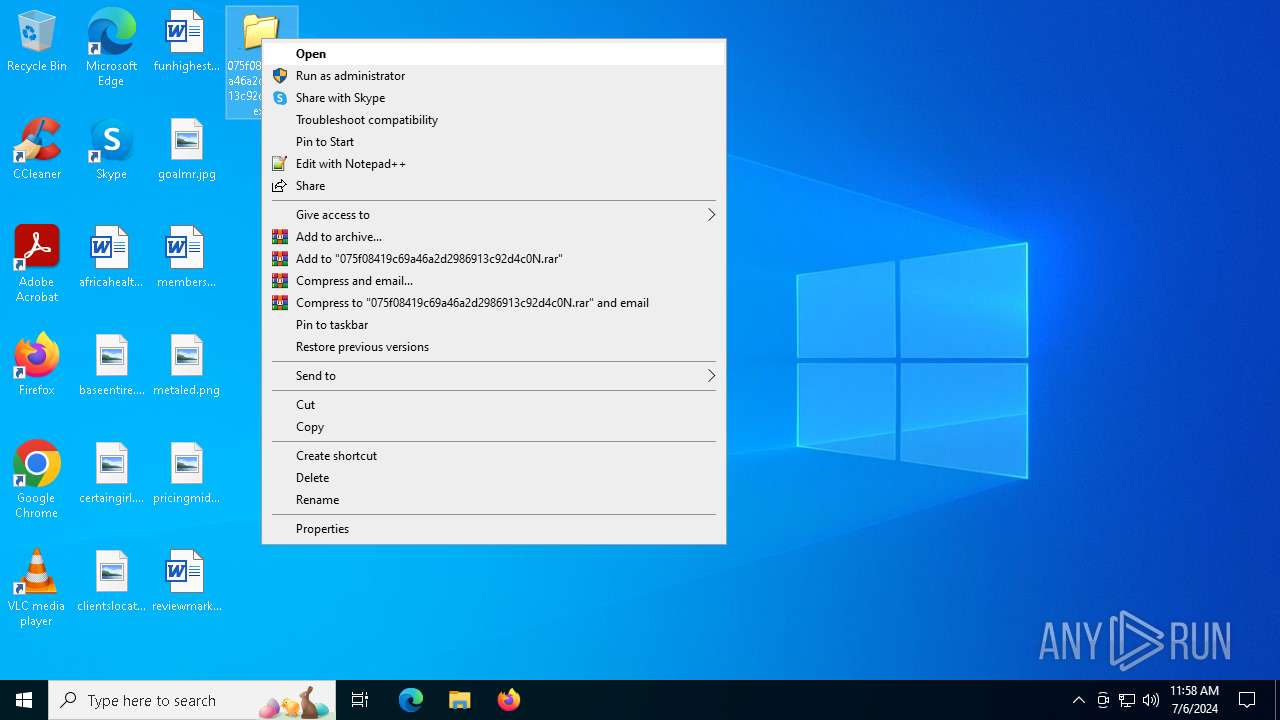
Manual execution by a user
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
Process checks computer location settings
- 075f08419c69a46a2d2986913c92d4c0N.exe (PID: 780)
Checks proxy server information
- jusched.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2068:07:15 22:12:55+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 155648 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6e20 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.150.3 |
| ProductVersionNumber: | 6.0.150.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 6.0.150.3 |
| InternalName: | jusched |
| LegalCopyright: | Copyright © 2011 |
| LegalTrademarks: | - |
| OriginalFileName: | jusched |
| PrivateBuild: | Sun Microsystems, Inc. |
| ProductName: | Java(TM) Platform SE 6 U15 |
| ProductVersion: | 6.0.150.3 |
| SpecialBuild: | - |
Total processes
124
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Users\admin\Desktop\075f08419c69a46a2d2986913c92d4c0N.exe" | C:\Users\admin\Desktop\075f08419c69a46a2d2986913c92d4c0N.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Version: 6.0.150.3 Modules
| |||||||||||||||
| 2668 | "C:\Program Files (x86)\26b79a31\jusched.exe" | C:\Program Files (x86)\26b79a31\jusched.exe | 075f08419c69a46a2d2986913c92d4c0N.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 6.0.150.3 Modules
| |||||||||||||||
| 3724 | "C:\Users\admin\Desktop\075f08419c69a46a2d2986913c92d4c0N.exe" | C:\Users\admin\Desktop\075f08419c69a46a2d2986913c92d4c0N.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 6.0.150.3 Modules
| |||||||||||||||
Total events
1 547
Read events
1 539
Write events
8
Delete events
0
Modification events
| (PID) Process: | (780) 075f08419c69a46a2d2986913c92d4c0N.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (780) 075f08419c69a46a2d2986913c92d4c0N.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (780) 075f08419c69a46a2d2986913c92d4c0N.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (780) 075f08419c69a46a2d2986913c92d4c0N.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3724 | 075f08419c69a46a2d2986913c92d4c0N.exe | C:\WINDOWS\Tasks\Update23.job | binary | |
MD5:087E67E0F64E21D22CCA5466531F0D3A | SHA256:B74B01B6817060E838917BBDF00B4B4831CD9CC59A65C8BADC155ABC02C30FA9 | |||
| 3724 | 075f08419c69a46a2d2986913c92d4c0N.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files (x86)\26b79a31\26b79a31 | text | |
MD5:89931A70501A3362B6823B53523F5A77 | SHA256:D30D9A0E64BC9F4A306617F087F30DE6D57A5413793AB7BDE13A299777A1B254 | |||
| 780 | 075f08419c69a46a2d2986913c92d4c0N.exe | C:\Program Files (x86)\26b79a31\jusched.exe | executable | |
MD5:75C88336280D66010B261D69830DE16F | SHA256:D2530D9AC72377F60CED1984B387CD1CAEEF68D2F7D0EF94AA8E75A4BCC0F30E | |||
| 780 | 075f08419c69a46a2d2986913c92d4c0N.exe | C:\Program Files (x86)\26b79a31\26b79a31 | text | |
MD5:89931A70501A3362B6823B53523F5A77 | SHA256:D30D9A0E64BC9F4A306617F087F30DE6D57A5413793AB7BDE13A299777A1B254 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1888 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2052 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
368 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1888 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
2052 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | POST | 200 | 40.79.173.40:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2052 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
368 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1888 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1888 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2052 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1888 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2052 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2052 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
368 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
dictio_802884.di.funpic.org |
| unknown |
griptoloji.host-ed.net |
| unknown |
ftp.tripod.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2668 | jusched.exe | A Network Trojan was detected | ET MALWARE W32.Duptwux/Ganelp FTP Username - onthelinux |
2668 | jusched.exe | A Network Trojan was detected | ET MALWARE W32.Duptwux/Ganelp FTP Username - onthelinux |