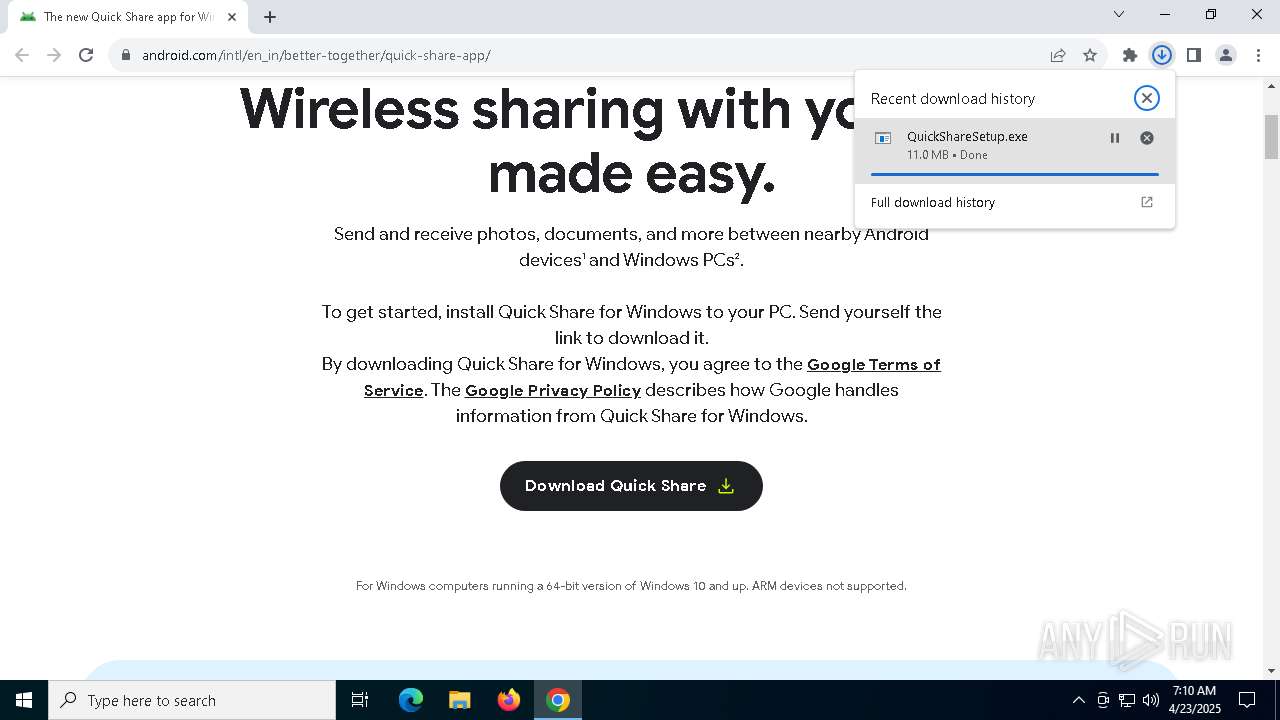
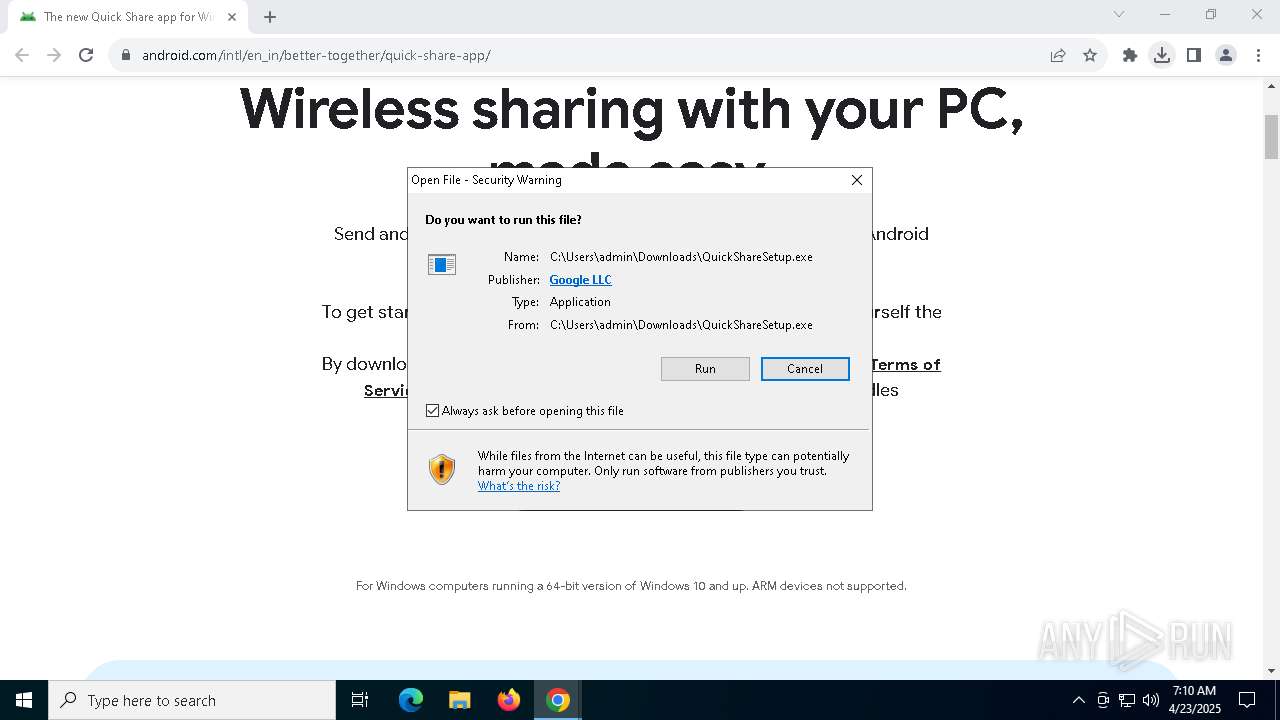
| URL: | https://www.android.com/intl/en_in/better-together/quick-share-app/ |
| Full analysis: | https://app.any.run/tasks/89a891d6-2239-4045-9b0c-3e347d94e501 |
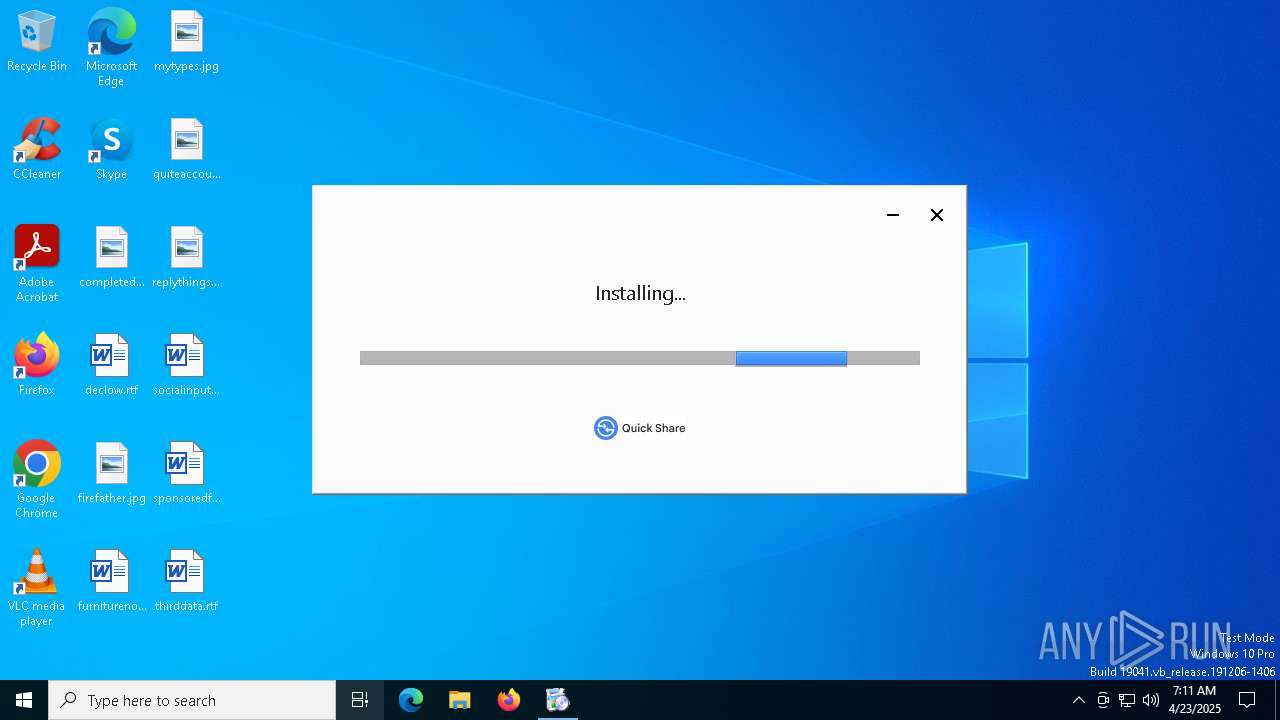
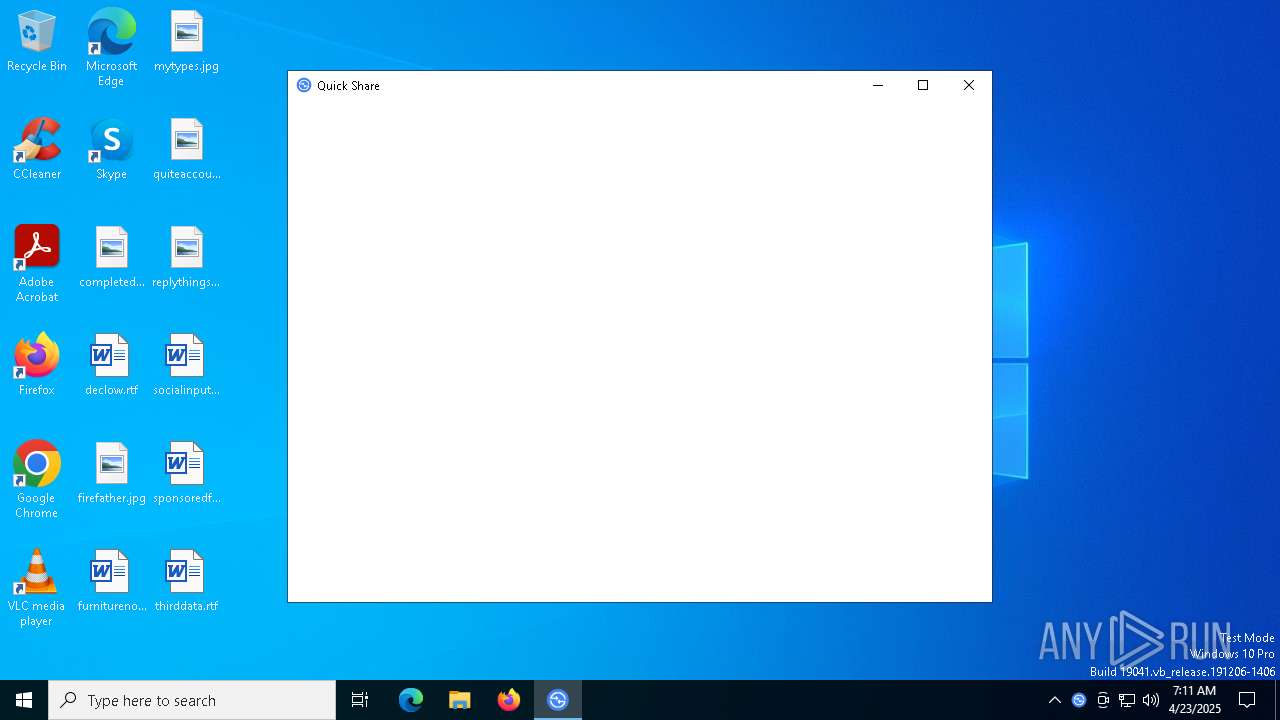
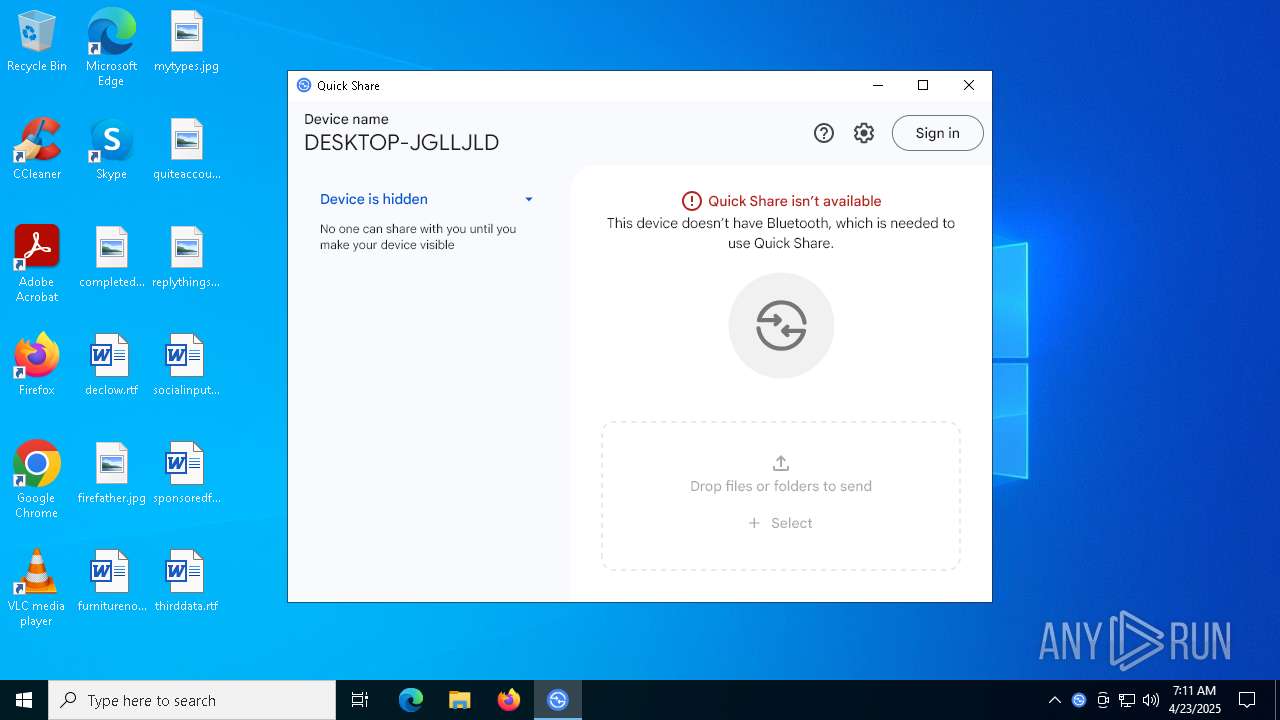
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2025, 07:10:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 1BF3CEE1A2491AB0BE3B4CA4628494A1 |
| SHA1: | 9146B2C06565AEB5F6D1B2854970AC4A0DF94CCC |
| SHA256: | 85AB47B31ECC3041BC4515985F9A462F4ED7BCA7AB27EA95551066AC748AF331 |
| SSDEEP: | 3:N8DSLEUKAAIRKC0DJMGOrVLVK:2OLEMArN56VK |
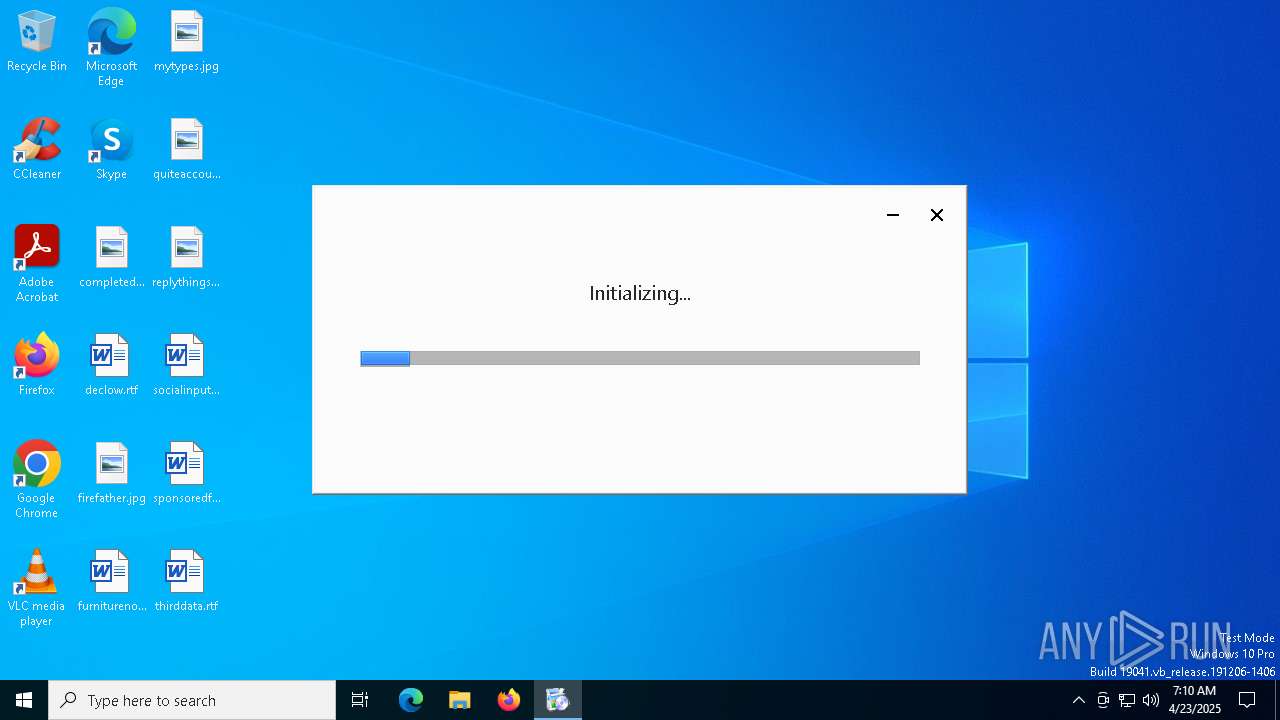
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7772)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7332)
Run PowerShell with an invisible window
- powershell.exe (PID: 7772)
- powershell.exe (PID: 7728)
- powershell.exe (PID: 7332)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 5384)
Changes the autorun value in the registry
- msiexec.exe (PID: 6752)
SUSPICIOUS
Reads security settings of Internet Explorer
- QuickShareSetup.exe (PID: 1324)
- updater.exe (PID: 8048)
- nearby_config.exe (PID: 5772)
- nearby_share_launcher.exe (PID: 7404)
- nearby_share.exe (PID: 7572)
Application launched itself
- QuickShareSetup.exe (PID: 1324)
- updater.exe (PID: 3332)
- updater.exe (PID: 8048)
- updater.exe (PID: 8088)
Executes as Windows Service
- updater.exe (PID: 3332)
- updater.exe (PID: 8088)
Executable content was dropped or overwritten
- updater.exe (PID: 8048)
- updater.exe (PID: 3332)
- drvinst.exe (PID: 4844)
- pnputil.exe (PID: 4408)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 5384)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6752)
Executes powershell module file
- msiexec.exe (PID: 5384)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 5384)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 5384)
The process hides Powershell's copyright startup banner
- msiexec.exe (PID: 5384)
Creates files in the driver directory
- drvinst.exe (PID: 4112)
- drvinst.exe (PID: 4844)
Reads the date of Windows installation
- nearby_share_launcher.exe (PID: 7404)
There is functionality for taking screenshot (YARA)
- updater.exe (PID: 8088)
INFO
The sample compiled with english language support
- chrome.exe (PID: 6876)
- updater.exe (PID: 8048)
- updater.exe (PID: 3332)
- msiexec.exe (PID: 6752)
- drvinst.exe (PID: 4844)
- pnputil.exe (PID: 4408)
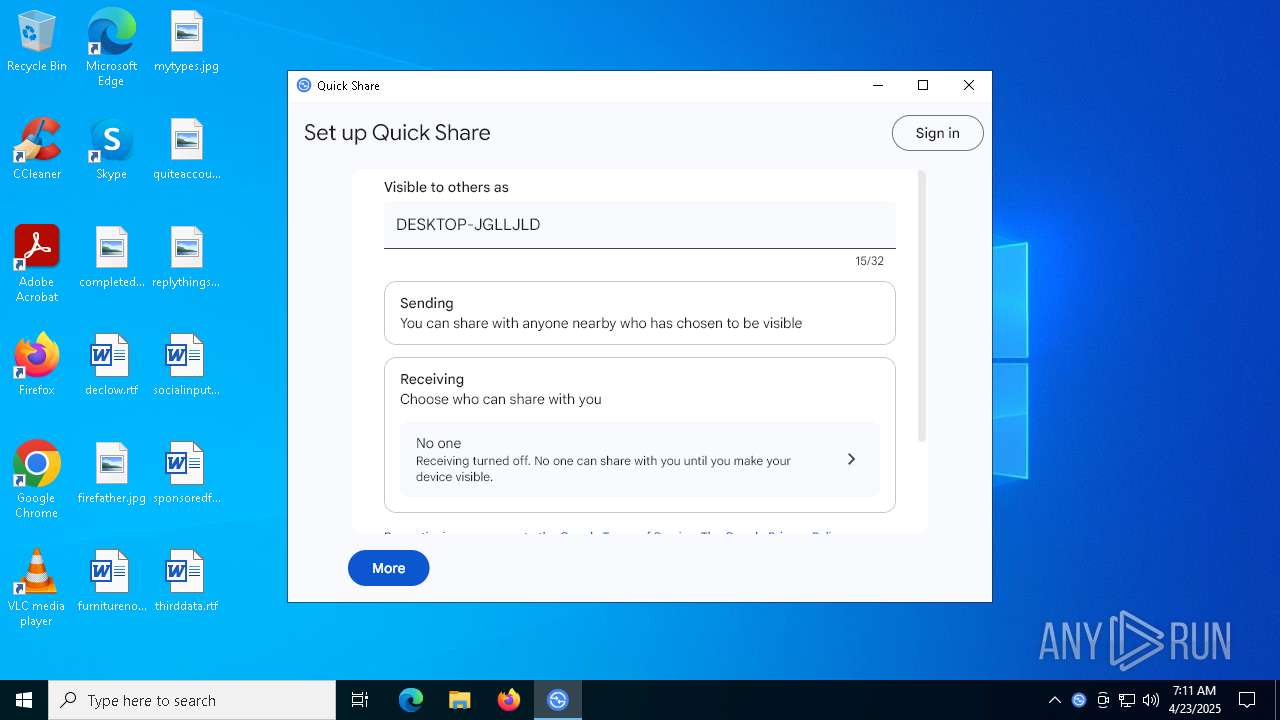
Reads the computer name
- QuickShareSetup.exe (PID: 1324)
- QuickShareSetup.exe (PID: 8096)
- updater.exe (PID: 3332)
- updater.exe (PID: 8048)
- updater.exe (PID: 8088)
- msiexec.exe (PID: 6752)
- msiexec.exe (PID: 5384)
- nearby_config.exe (PID: 7360)
- drvinst.exe (PID: 4112)
- drvinst.exe (PID: 4844)
- nearby_config.exe (PID: 5772)
- nearby_share_launcher.exe (PID: 7404)
- nearby_share.exe (PID: 7572)
Checks supported languages
- QuickShareSetup.exe (PID: 1324)
- QuickShareSetup.exe (PID: 8096)
- updater.exe (PID: 5436)
- updater.exe (PID: 7864)
- updater.exe (PID: 8048)
- updater.exe (PID: 8088)
- updater.exe (PID: 8068)
- msiexec.exe (PID: 6752)
- updater.exe (PID: 3332)
- msiexec.exe (PID: 5384)
- nearby_config.exe (PID: 7360)
- drvinst.exe (PID: 4112)
- drvinst.exe (PID: 4844)
- nearby_config.exe (PID: 8116)
- nearby_share.exe (PID: 7572)
- nearby_share_launcher.exe (PID: 7404)
- crashpad_handler.exe (PID: 7568)
- nearby_config.exe (PID: 5772)
Creates files in the program directory
- QuickShareSetup.exe (PID: 8096)
- updater.exe (PID: 8048)
- updater.exe (PID: 7864)
- updater.exe (PID: 8088)
- updater.exe (PID: 3332)
- nearby_config.exe (PID: 7360)
Process checks computer location settings
- QuickShareSetup.exe (PID: 1324)
- nearby_config.exe (PID: 7360)
- nearby_config.exe (PID: 8116)
- nearby_config.exe (PID: 5772)
- nearby_share_launcher.exe (PID: 7404)
- nearby_share.exe (PID: 7572)
Process checks whether UAC notifications are on
- updater.exe (PID: 3332)
- updater.exe (PID: 8048)
- updater.exe (PID: 8088)
Application launched itself
- chrome.exe (PID: 6876)
Executable content was dropped or overwritten
- chrome.exe (PID: 6876)
- msiexec.exe (PID: 6752)
Reads the software policy settings
- updater.exe (PID: 8048)
- updater.exe (PID: 8088)
- drvinst.exe (PID: 4112)
- drvinst.exe (PID: 4844)
- slui.exe (PID: 7916)
- slui.exe (PID: 8172)
- nearby_share.exe (PID: 7572)
Reads the machine GUID from the registry
- updater.exe (PID: 8048)
- drvinst.exe (PID: 4112)
- drvinst.exe (PID: 4844)
- nearby_share.exe (PID: 7572)
Creates files or folders in the user directory
- updater.exe (PID: 8048)
- crashpad_handler.exe (PID: 7568)
- nearby_share.exe (PID: 7572)
Checks proxy server information
- updater.exe (PID: 8048)
- slui.exe (PID: 8172)
- nearby_share.exe (PID: 7572)
Create files in a temporary directory
- updater.exe (PID: 8048)
Creates a software uninstall entry
- msiexec.exe (PID: 6752)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7728)
Manual execution by a user
- nearby_share_launcher.exe (PID: 7404)
Reads Environment values
- nearby_share.exe (PID: 7572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
187
Monitored processes
48
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1168 | "C:\WINDOWS\SysNative\pnputil.exe" /add-driver "C:\Program Files\Google\NearbyShare\intel\PieExtension.INF" /install | C:\Windows\System32\pnputil.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft PnP Utility - Tool to add, delete, export, and enumerate driver packages. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\WINDOWS\SysNative\pnputil.exe" /enum-devices | C:\Windows\System32\pnputil.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft PnP Utility - Tool to add, delete, export, and enumerate driver packages. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\Downloads\QuickShareSetup.exe" | C:\Users\admin\Downloads\QuickShareSetup.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Installer (x86) Exit code: 0 Version: 137.0.7129.0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5568 --field-trial-handle=1896,i,3716026571074160232,3426693797922692061,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3332 | "C:\Program Files (x86)\Google\GoogleUpdater\137.0.7129.0\updater.exe" --system --windows-service --service=update-internal | C:\Program Files (x86)\Google\GoogleUpdater\137.0.7129.0\updater.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater (x86) Exit code: 0 Version: 137.0.7129.0 Modules
| |||||||||||||||
| 4112 | DrvInst.exe "4" "0" "C:\WINDOWS\TEMP\{a599a5ca-b7e4-4346-9013-ab9815603f53}\PieExtension.INF" "9" "4ff18b62b" "00000000000001DC" "WinSta0\Default" "00000000000001EC" "208" "C:\Program Files\Google\NearbyShare\intel" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | "C:\WINDOWS\SysNative\pnputil.exe" /add-driver "C:\Program Files\Google\NearbyShare\intel\PieComponent.INF" /install | C:\Windows\System32\pnputil.exe | powershell.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft PnP Utility - Tool to add, delete, export, and enumerate driver packages. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4844 | DrvInst.exe "4" "0" "C:\WINDOWS\TEMP\{b802c7f4-bc62-7944-a305-9beacc593fe8}\PieComponent.INF" "9" "4d2f78d7b" "00000000000001EC" "WinSta0\Default" "0000000000000190" "208" "C:\Program Files\Google\NearbyShare\intel" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5384 | C:\Windows\syswow64\MsiExec.exe -Embedding 68397C207EB73A3599980351DCC6BE5E E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5436 | "C:\Program Files (x86)\Google\GoogleUpdater\137.0.7129.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\137.0.7129.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=137.0.7129.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x1447e50,0x1447e5c,0x1447e68 | C:\Program Files (x86)\Google\GoogleUpdater\137.0.7129.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater (x86) Exit code: 0 Version: 137.0.7129.0 Modules
| |||||||||||||||
Total events
33 692
Read events
33 361
Write events
297
Delete events
34
Modification events
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6644) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000DC9F47DA1EB4DB01 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (3332) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientState\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | pv |
Value: 137.0.7129.0 | |||
| (PID) Process: | (3332) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{534F5323-3569-4F42-919D-1E1CF93E5BF6} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
55
Suspicious files
296
Text files
78
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10d35f.TMP | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10d340.TMP | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10d36f.TMP | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10d36f.TMP | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10d36f.TMP | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
82
DNS requests
77
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6876 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
6876 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6876 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAtQzyRrJj79hacpMVFY8%2F8%3D | unknown | — | — | whitelisted |
8048 | updater.exe | GET | 200 | 172.217.16.195:80 | http://o.pki.goog/we2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEQDQZgpWpezrXAmFnbj86J49 | unknown | — | — | whitelisted |
8048 | updater.exe | GET | 200 | 216.58.206.35:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
8048 | updater.exe | GET | 200 | 216.58.206.35:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7324 | chrome.exe | 142.250.185.142:443 | www.android.com | GOOGLE | US | whitelisted |
6876 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7324 | chrome.exe | 142.250.102.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7324 | chrome.exe | 216.58.206.33:443 | lh3.googleusercontent.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.android.com |
| whitelisted |
accounts.google.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
Process | Message |
|---|---|
nearby_config.exe | W0423 07:11:26.152756 7496 registry.cc:333] Unable to read registry value HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\NearbyShare\vendor_id, status: 2
|
nearby_config.exe | I0423 07:11:26.152349 7496 win32_utils.cc:49] GetThreadPreferredUILanguages() returns: en-US
|
nearby_config.exe | I0423 07:11:26.152523 7496 main.cc:347] GetPreferredLanguages() returns: 2 languages. nearby::localization::InitializeL10n returns: en
|
nearby_config.exe | I0423 07:11:26.158766 7496 main.cc:373] GetCommonStartMenuPath: common start menu path is C:\ProgramData\Microsoft\Windows\Start Menu
|
nearby_config.exe | I0423 07:11:26.158889 7496 main.cc:373] GetCommonStartMenuPath: common start menu path is C:\ProgramData\Microsoft\Windows\Start Menu
|
nearby_config.exe | I0423 07:11:26.158843 7496 main.cc:380] DeleteCommonStartMenuShortcut: Deleting common start menu shortcut.
|
nearby_config.exe | I0423 07:11:26.163503 7496 main.cc:412] CreateCommonStartMenuShortcut: Creating common start menu shortcut.
|
nearby_config.exe | I0423 07:11:26.163614 7496 main.cc:421] CreateCommonStartMenuShortcut: shortcut_path is C:\ProgramData\Microsoft\Windows\Start Menu\Quick Share.lnk, target_path is C:\Program Files\Google\NearbyShare\nearby_share.exe
|
nearby_config.exe | I0423 07:11:26.206118 7496 main.cc:503] Nearby configuration Done
|
nearby_config.exe | I0423 07:11:38.713755 4448 win32_utils.cc:49] GetThreadPreferredUILanguages() returns: en-US
|