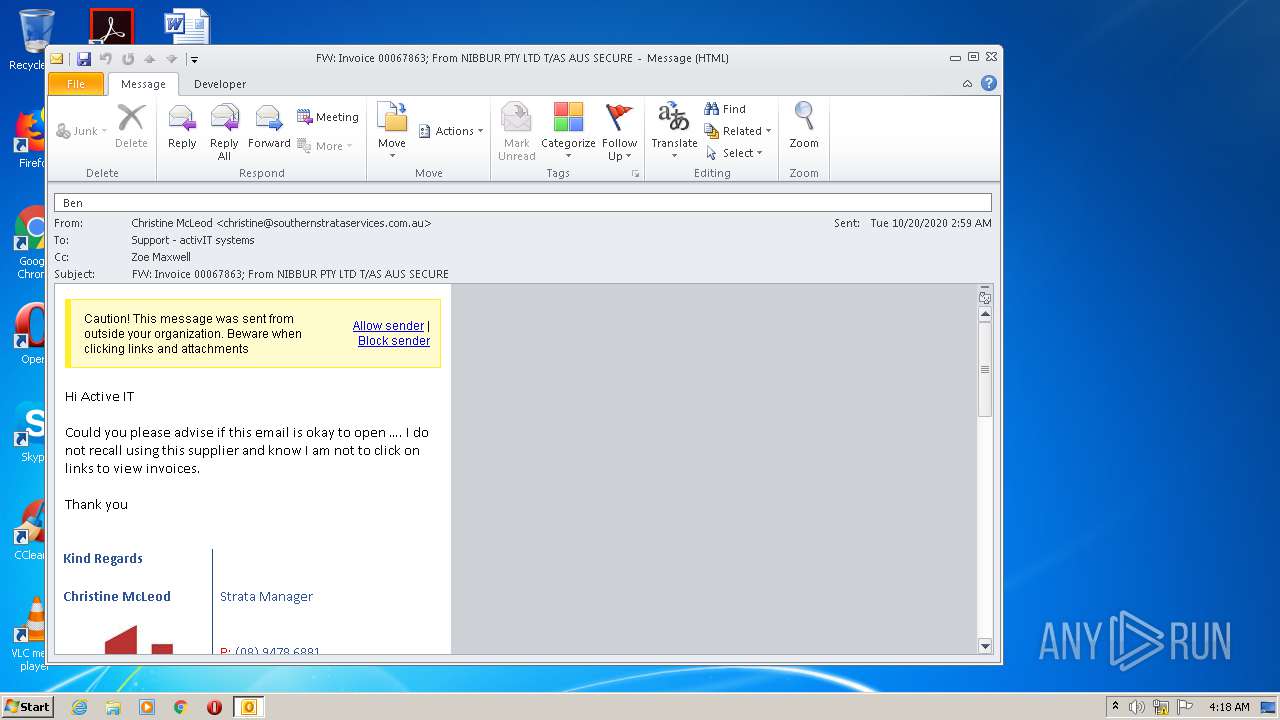
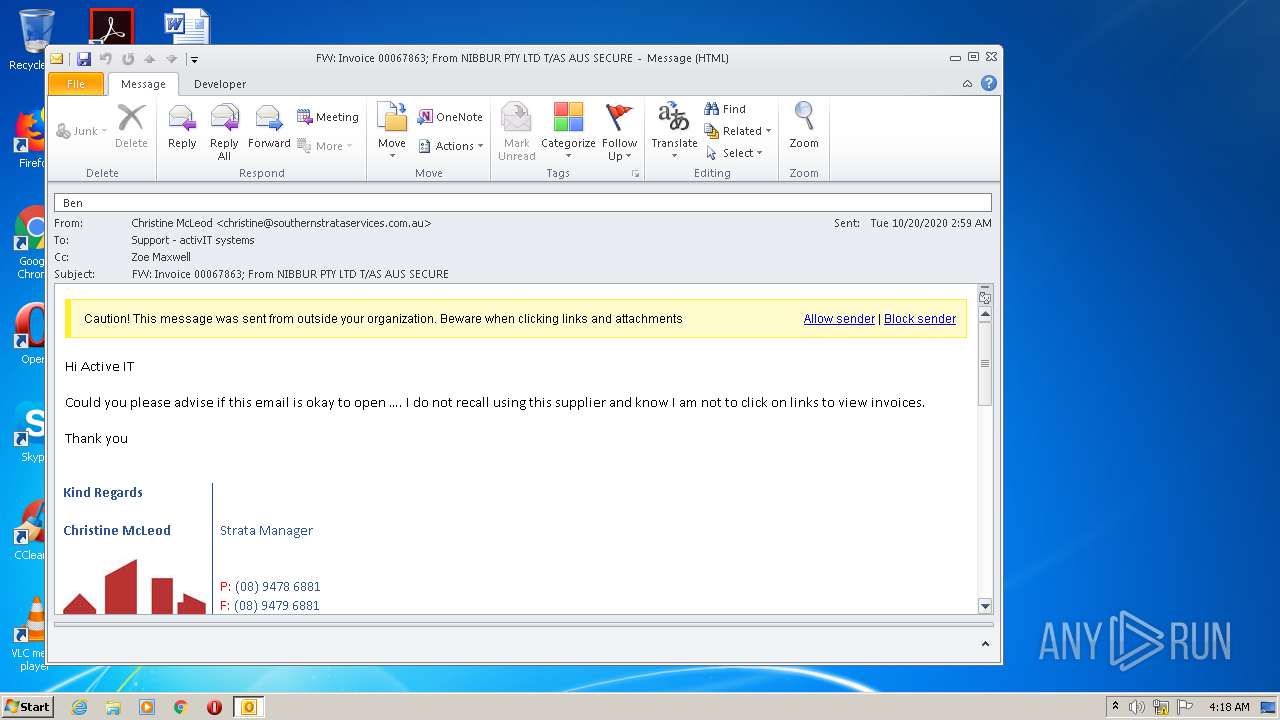
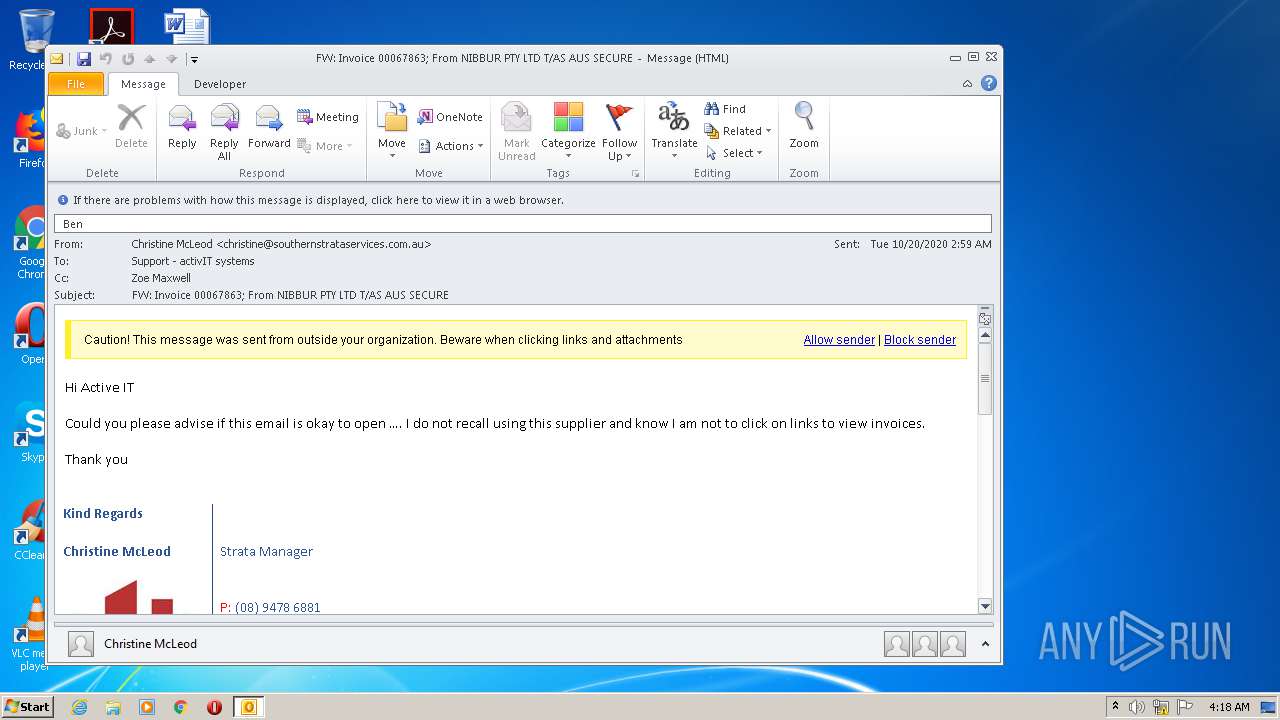
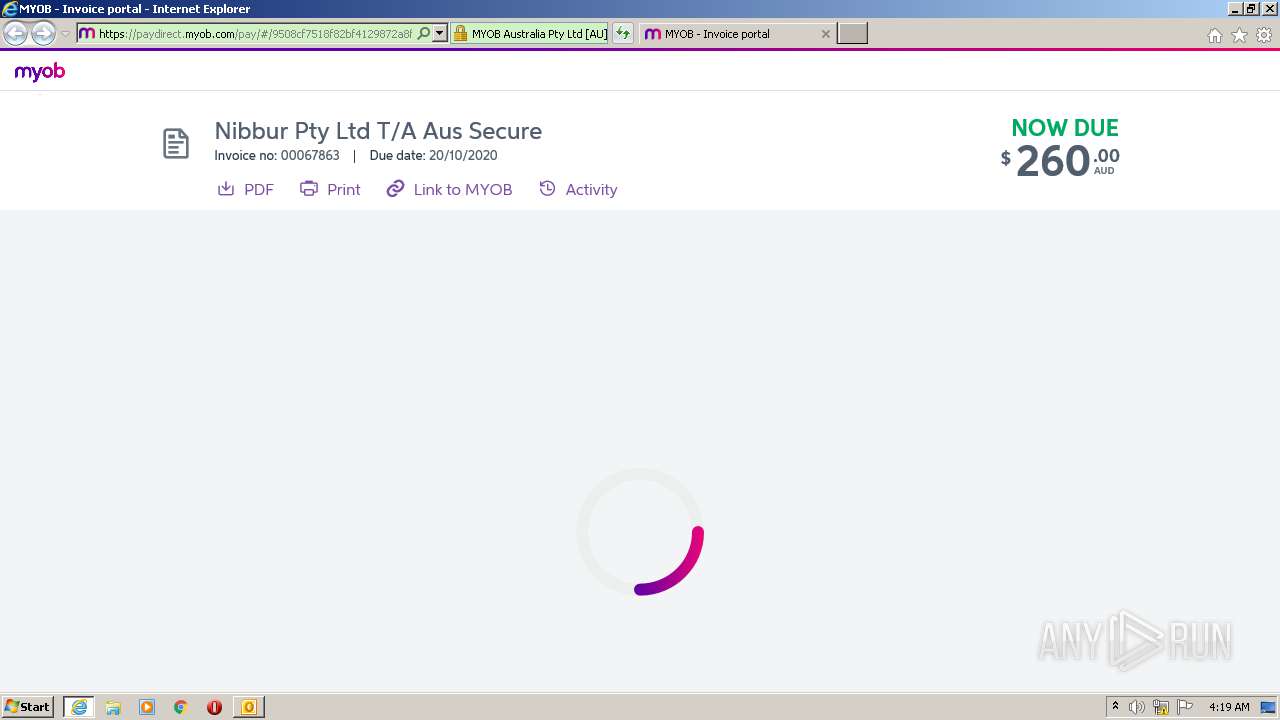
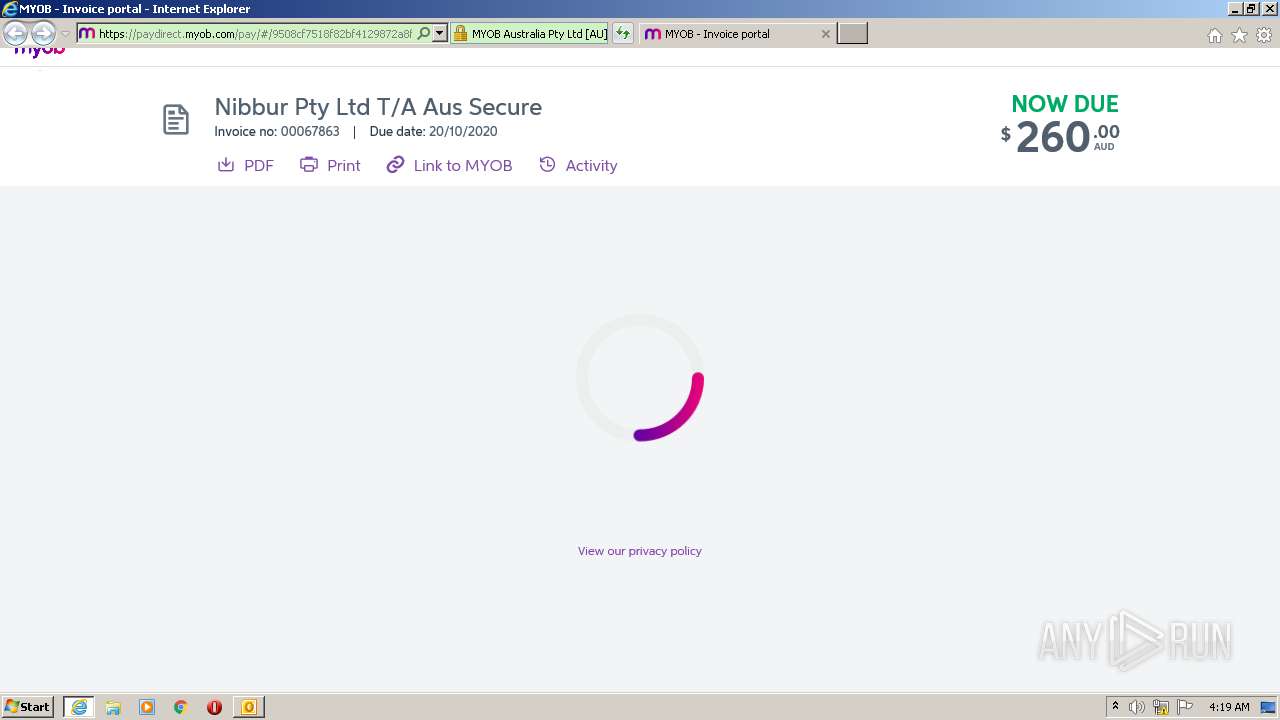
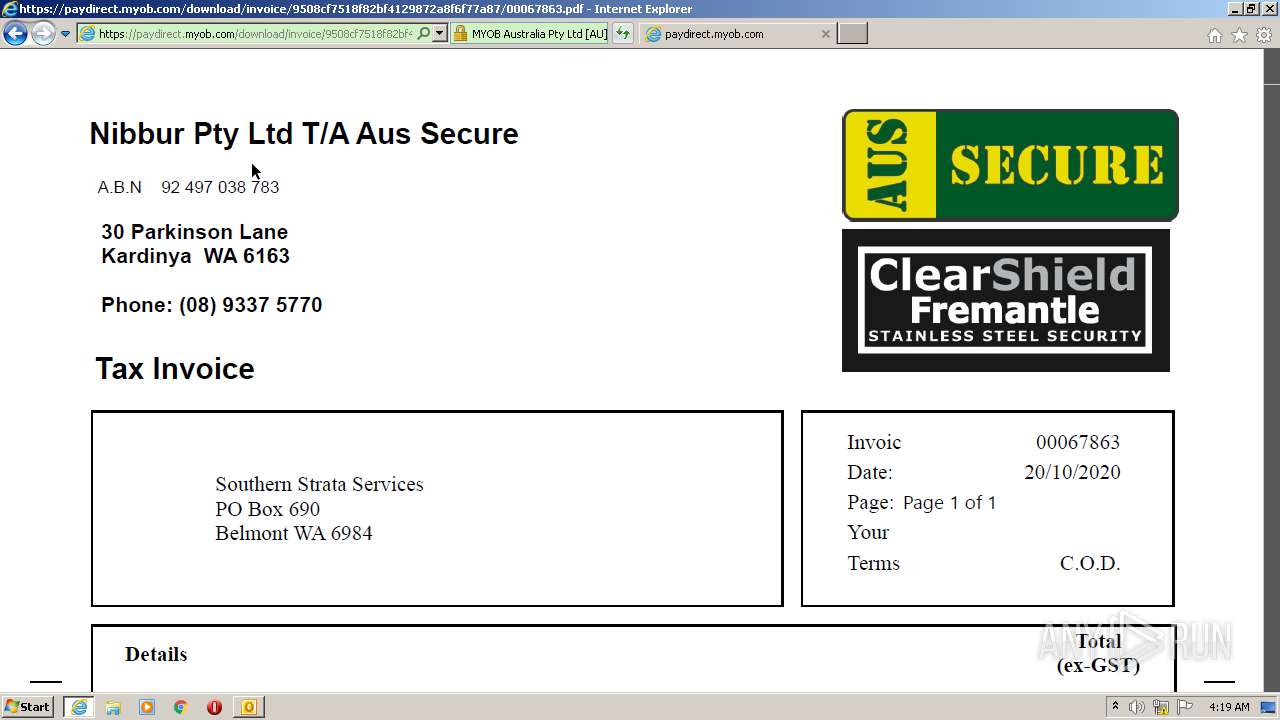
| File name: | FW_ Invoice 00067863_ From NIBBUR PTY LTD T_AS AUS SECURE.msg |
| Full analysis: | https://app.any.run/tasks/2fd1a015-8d41-4309-8f8f-3874f8b9951d |
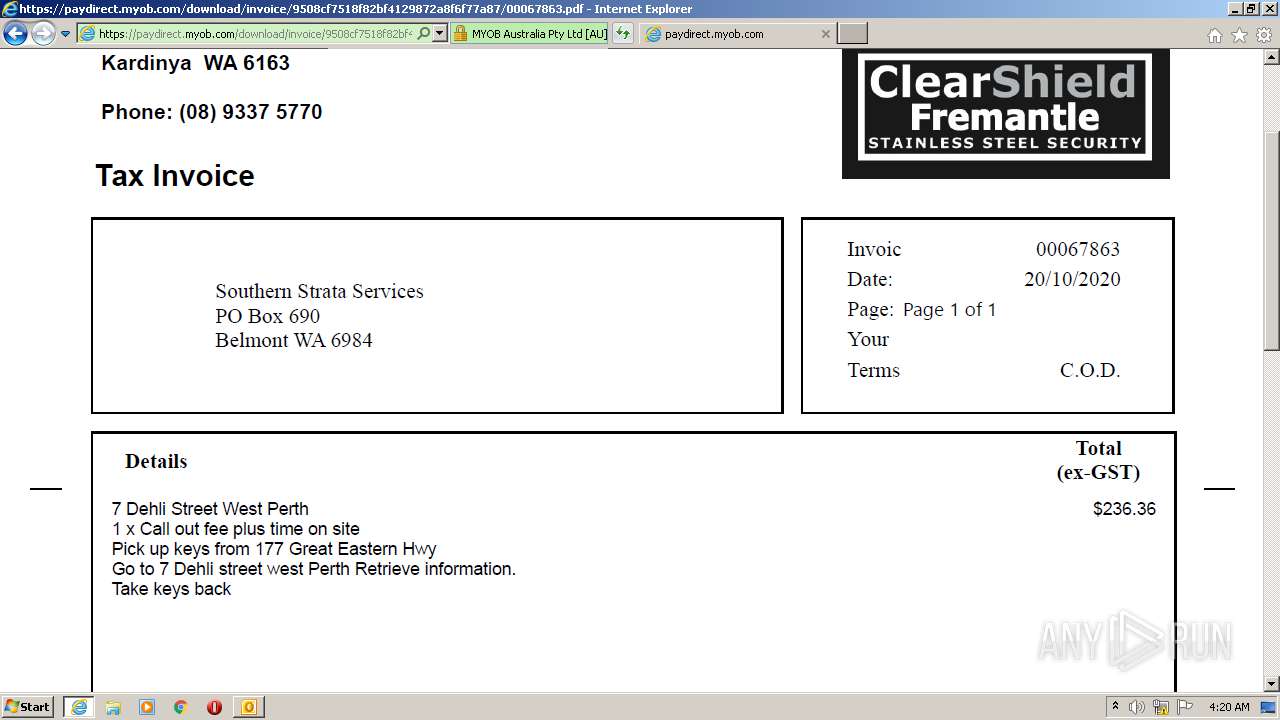
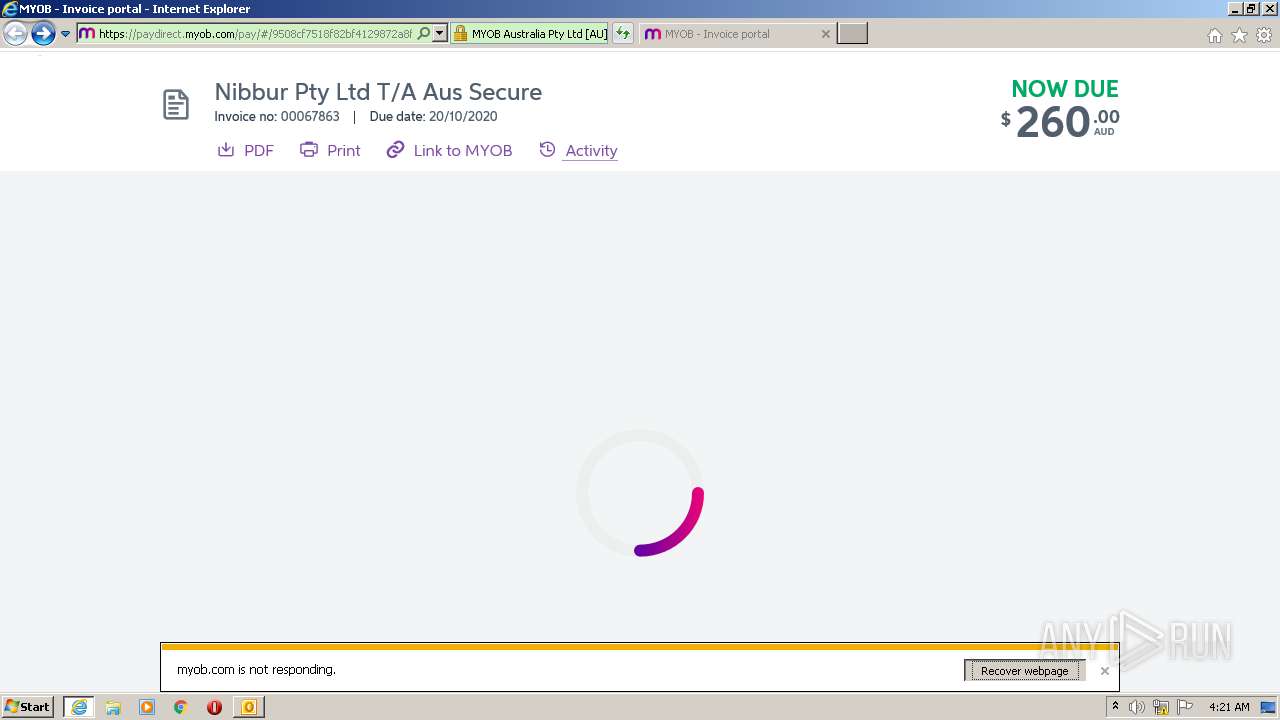
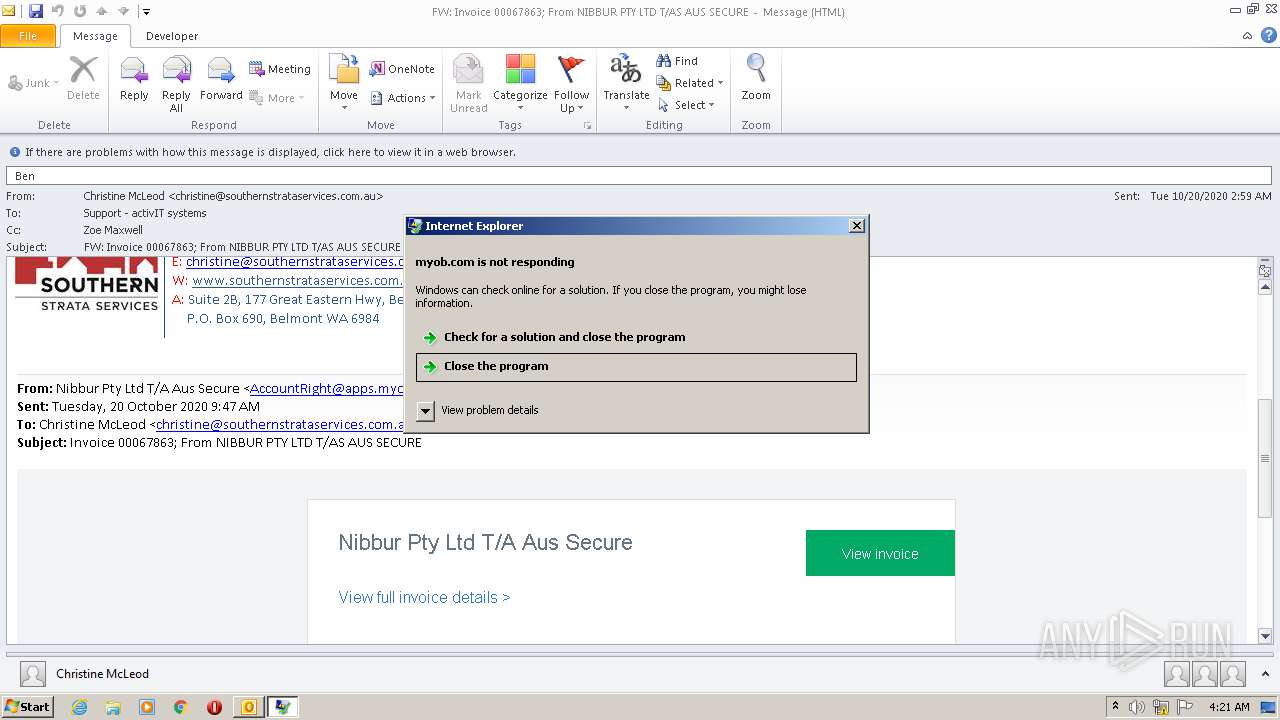
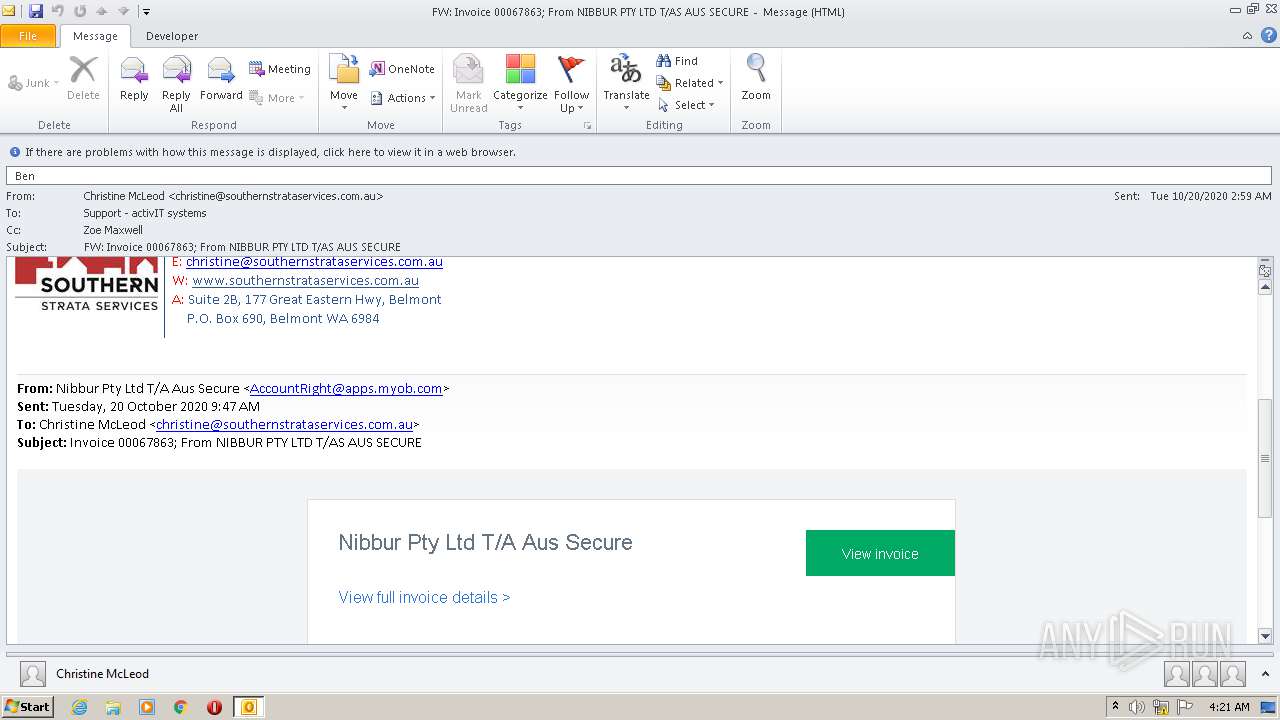
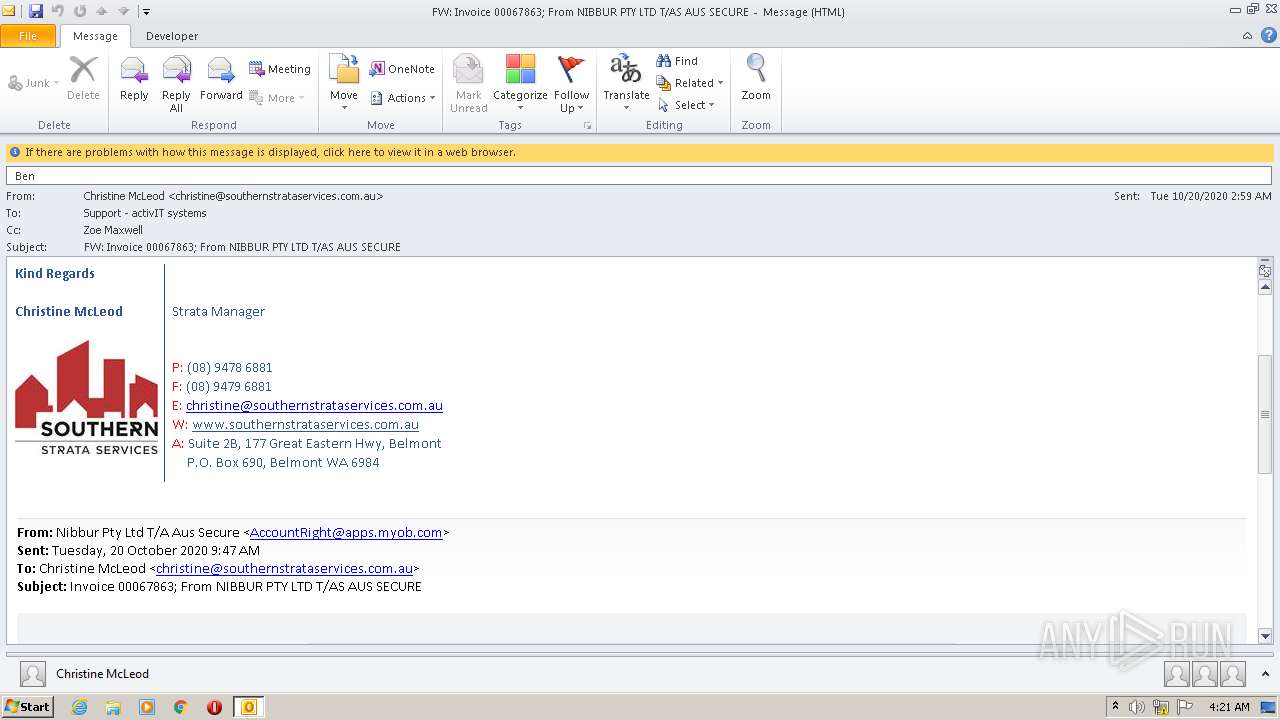
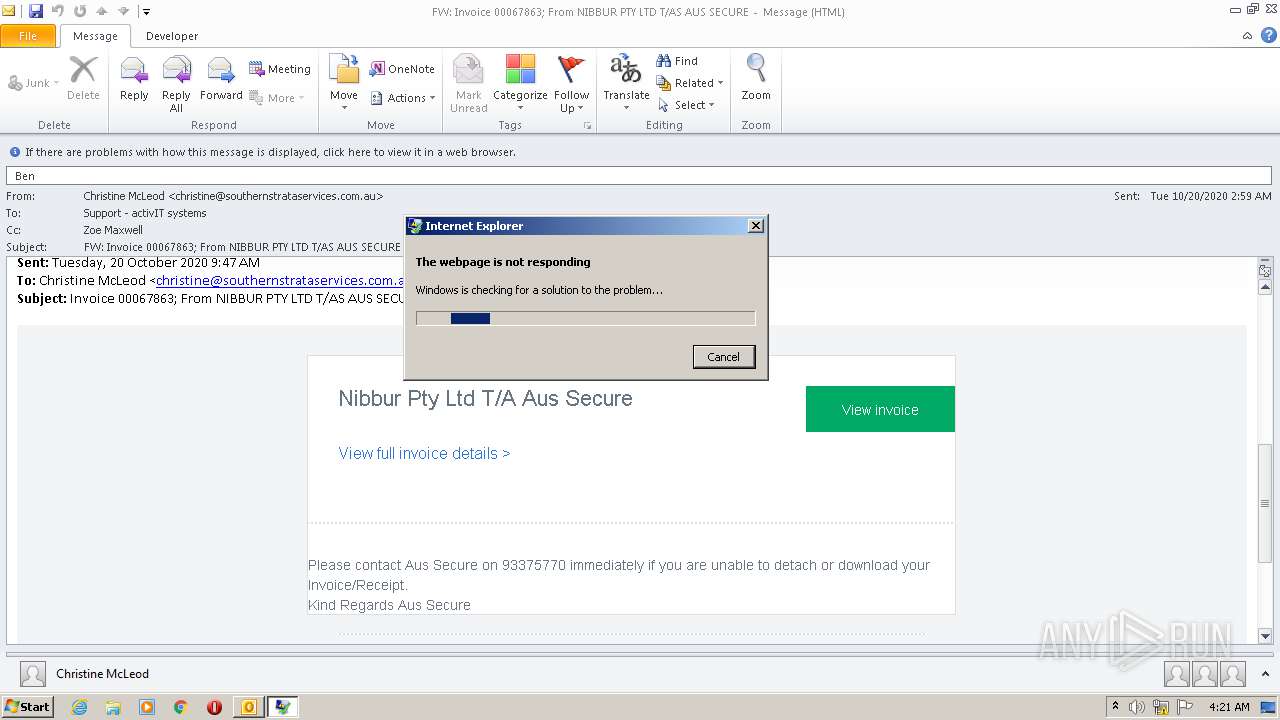
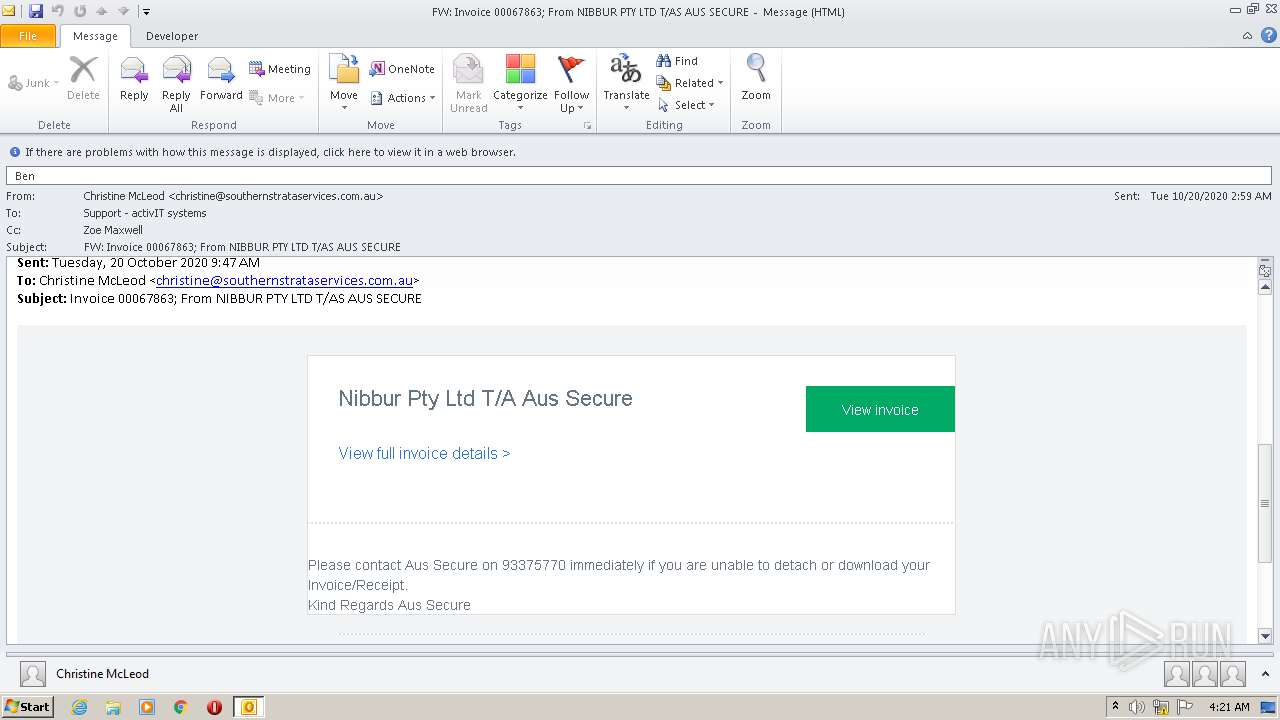
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 03:18:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 9CB404B82DFF11864AE399FEB44CD498 |
| SHA1: | 8D5AE055CA5DB1B1FD6E4EF279D7A7A2083227B0 |
| SHA256: | 859E9EDB60114E8B883EB38B16AFB522F3708704BE928AAC46491FED3ACEE610 |
| SSDEEP: | 3072:V1e68rilaQOniT78cOTVifqXJ+SkkQDfmXBCv2DHgd1:D8YTQ1ifoCv27gd1 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2572)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 2592)
- MsiExec.exe (PID: 3852)
SUSPICIOUS
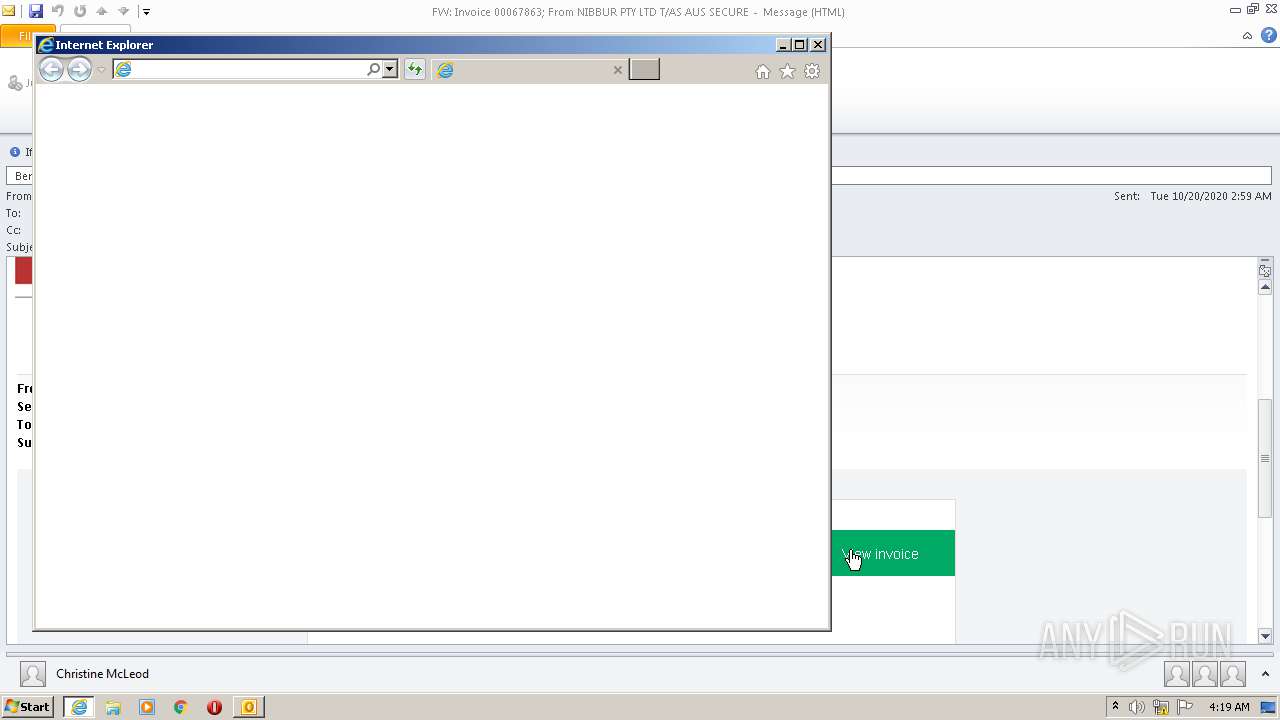
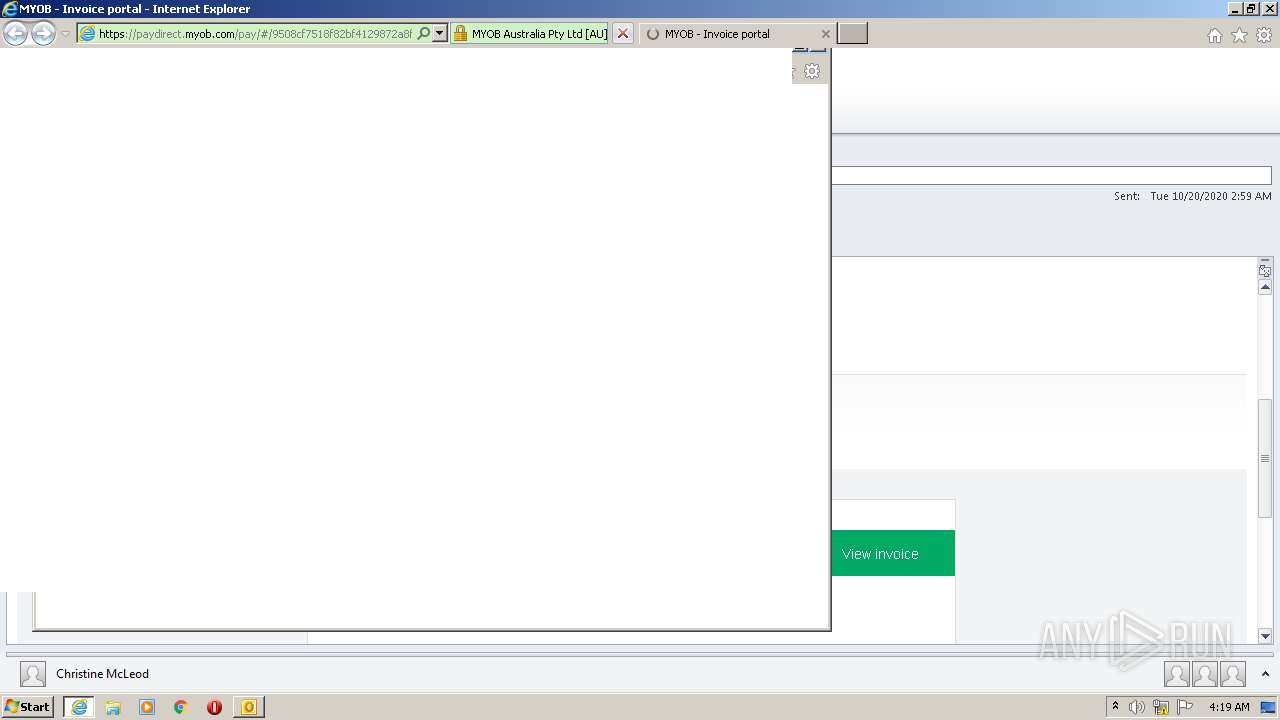
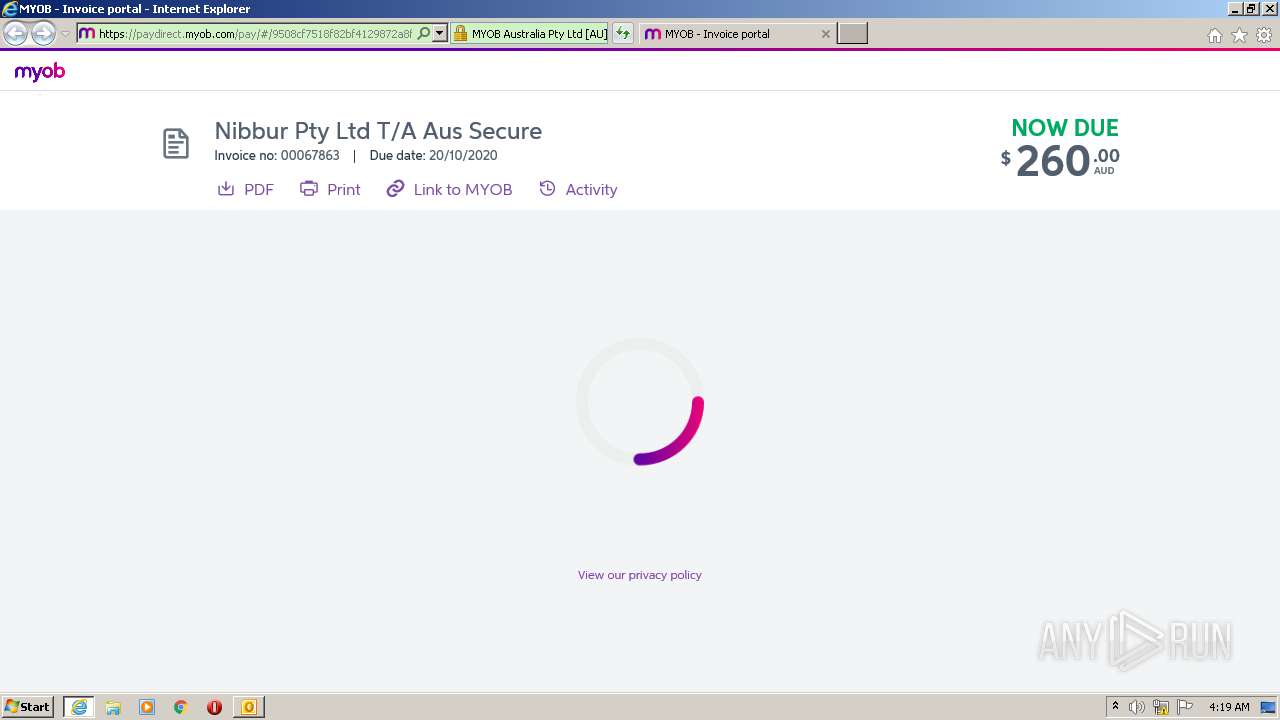
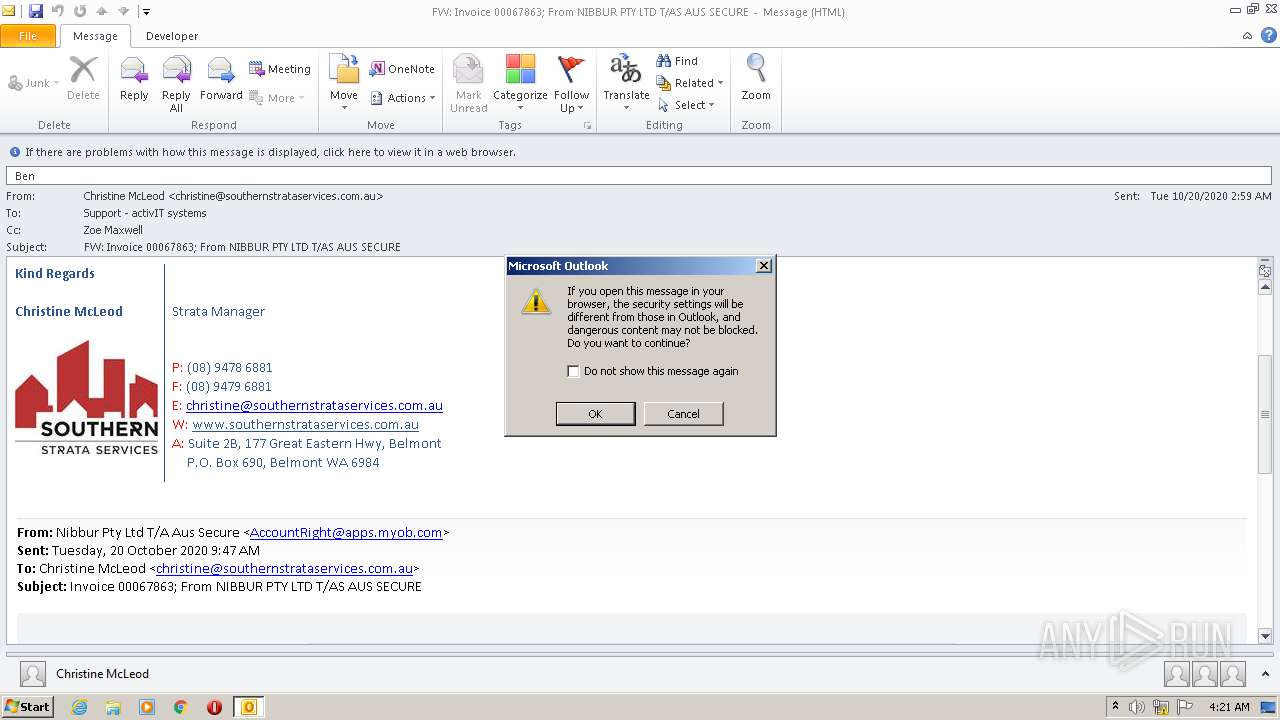
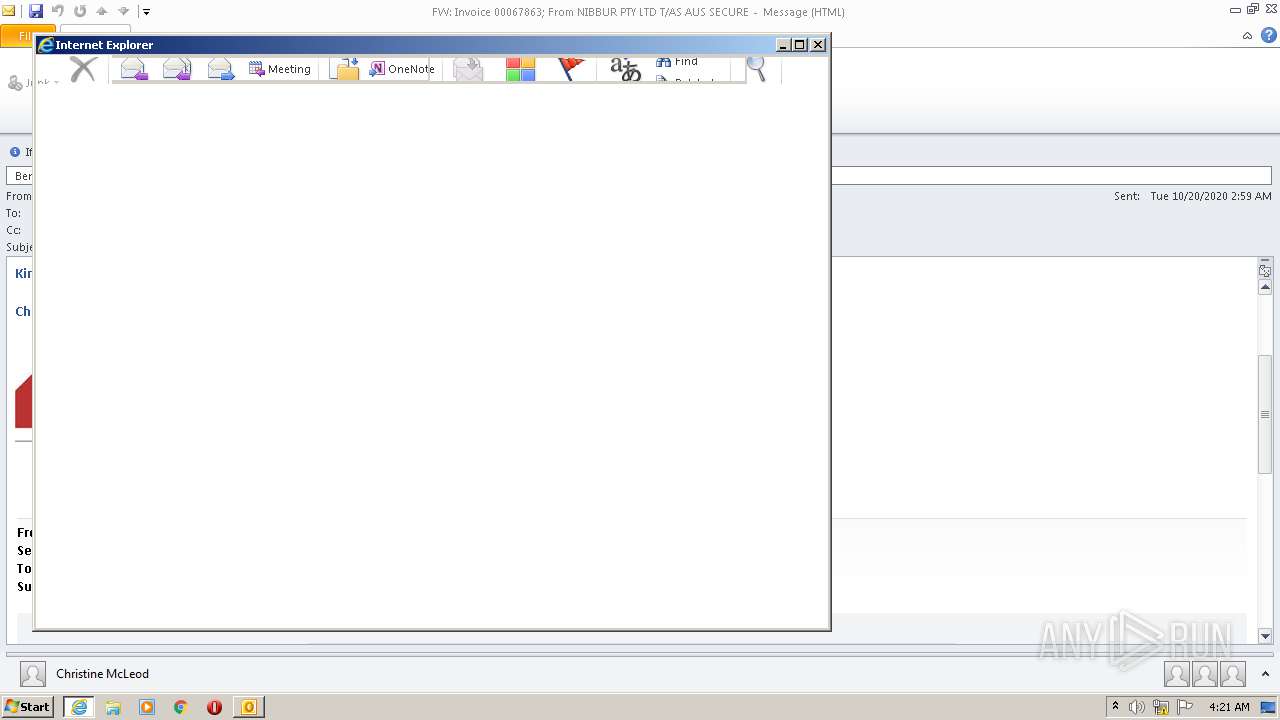
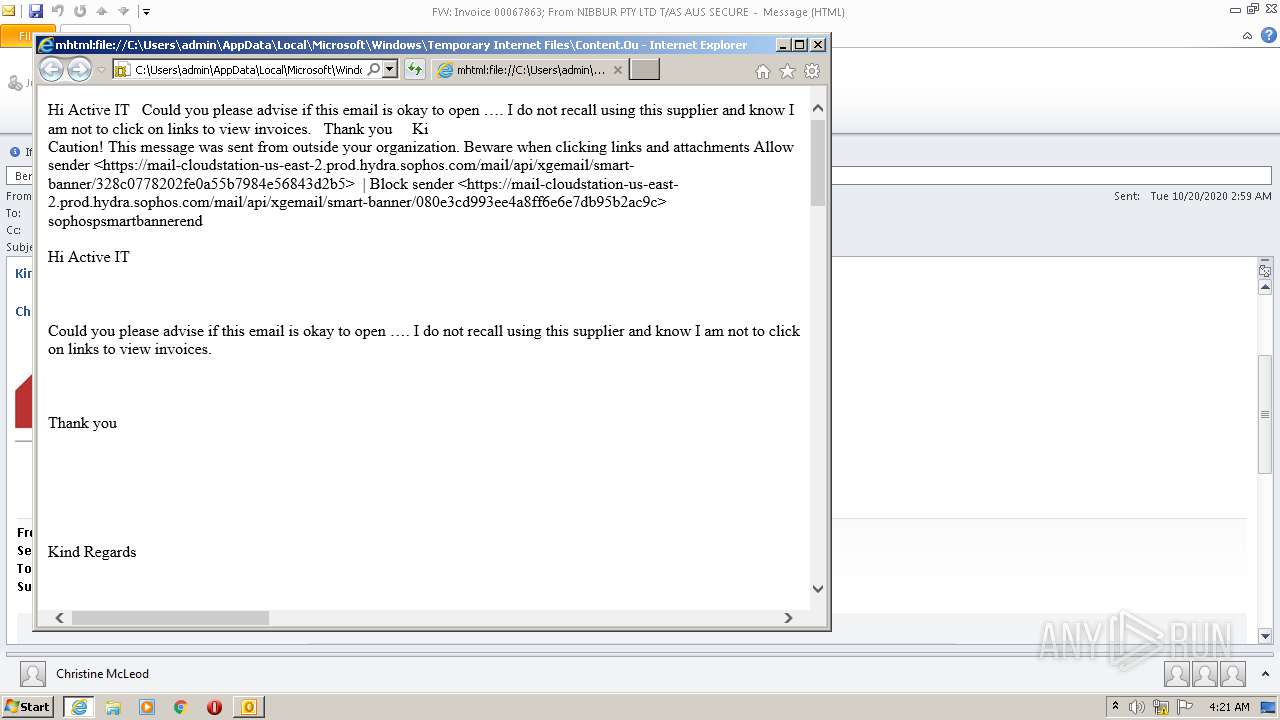
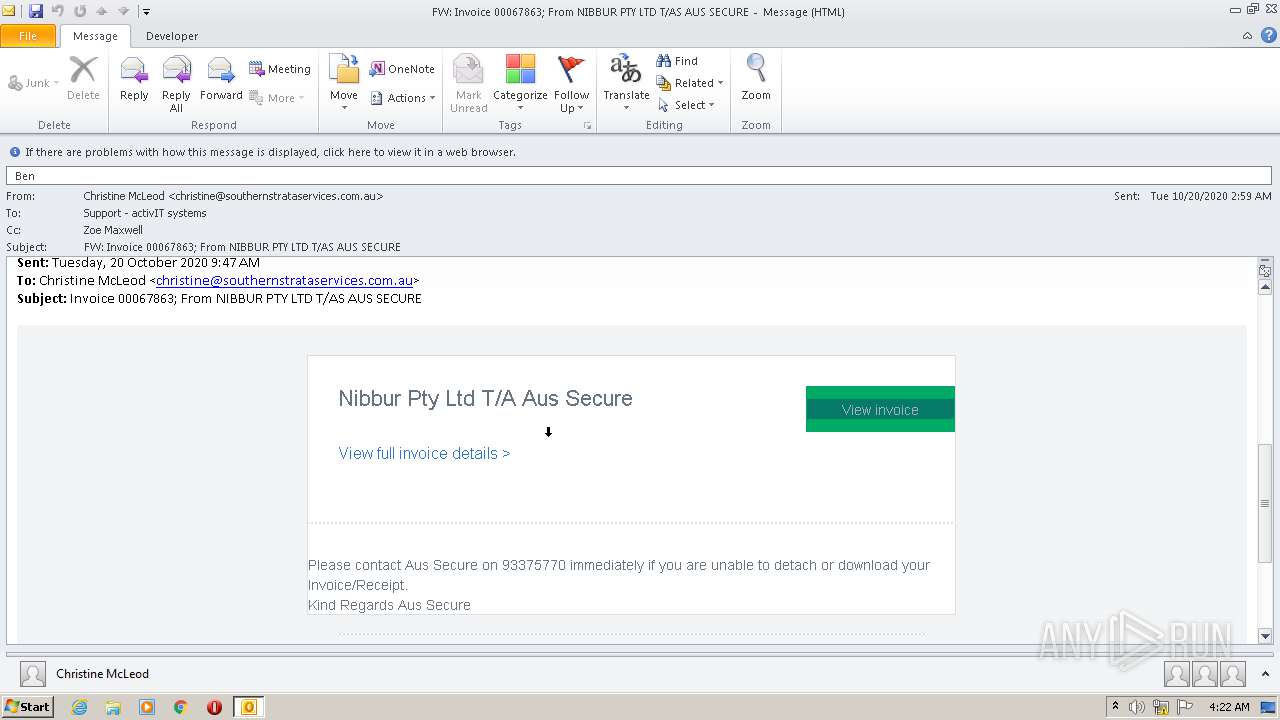
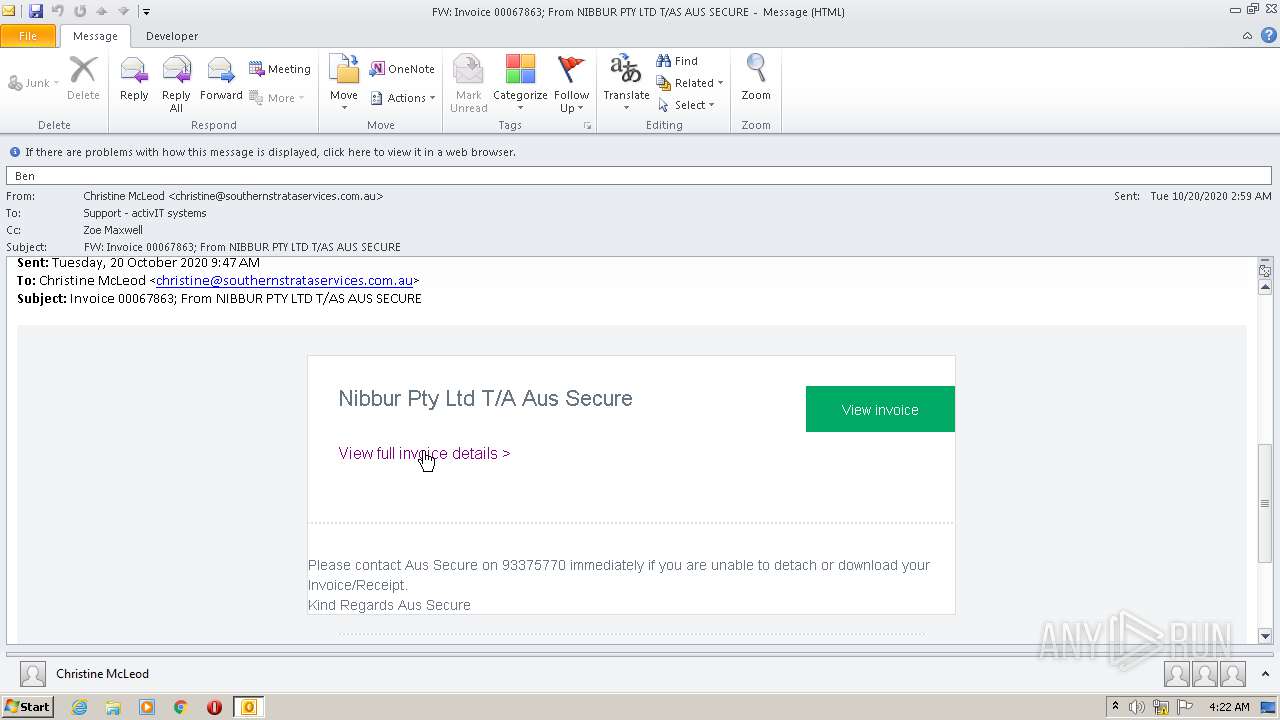
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2572)
Creates files in the program directory
- AdobeARM.exe (PID: 2448)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 2448)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2572)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2572)
- iexplore.exe (PID: 2908)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 3508)
- AcroRd32.exe (PID: 1288)
- iexplore.exe (PID: 3528)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2572)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 2908)
- AcroRd32.exe (PID: 3896)
- AcroRd32.exe (PID: 1288)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 1948)
- iexplore.exe (PID: 3528)
Application launched itself
- iexplore.exe (PID: 3508)
- AcroRd32.exe (PID: 1288)
- RdrCEF.exe (PID: 2604)
- iexplore.exe (PID: 3380)
- iexplore.exe (PID: 2748)
- msiexec.exe (PID: 3332)
Reads settings of System Certificates
- iexplore.exe (PID: 2908)
- iexplore.exe (PID: 3508)
- AcroRd32.exe (PID: 1288)
- iexplore.exe (PID: 3528)
- msiexec.exe (PID: 3332)
Changes internet zones settings
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3380)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3508)
Reads internet explorer settings
- iexplore.exe (PID: 2908)
- iexplore.exe (PID: 3528)
- iexplore.exe (PID: 1948)
Changes settings of System certificates
- iexplore.exe (PID: 3508)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 1288)
Reads the hosts file
- RdrCEF.exe (PID: 2604)
Creates files in the program directory
- msiexec.exe (PID: 3332)
Creates a software uninstall entry
- msiexec.exe (PID: 3332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
61
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1104 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2604.0.866657104\23435961" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 3221226356 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 2908 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | iexplore.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 2908 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3380 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3489660927 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\FW_ Invoice 00067863_ From NIBBUR PTY LTD T_AS AUS SECURE.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2592 | C:\Windows\system32\MsiExec.exe -Embedding CF51A442D0038189FC0EA522A312DB17 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
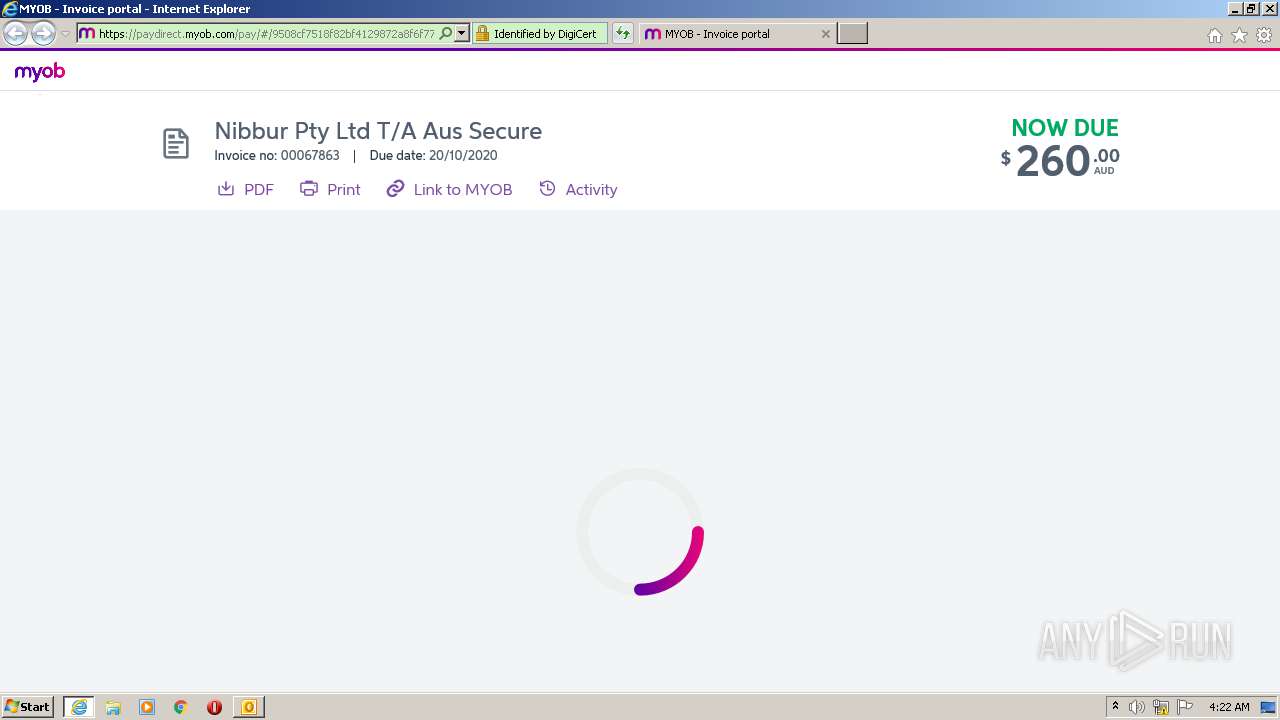
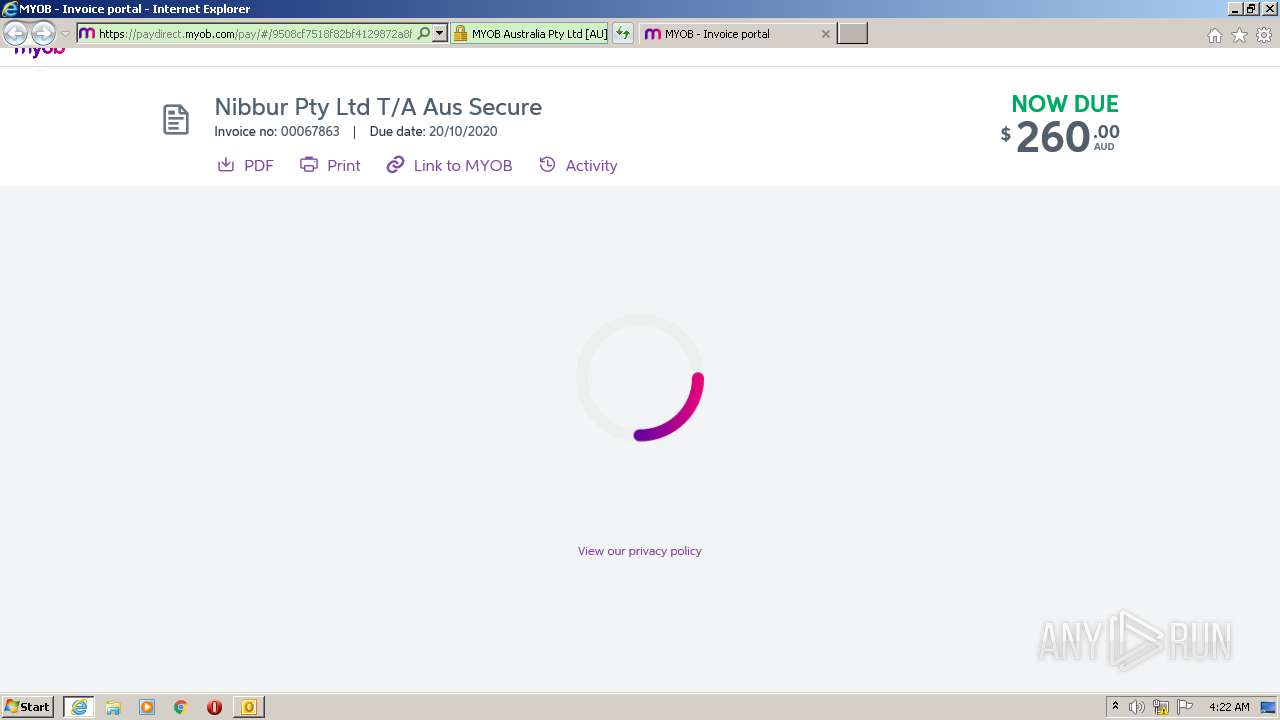
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" https://us-east-2.protection.sophos.com/?d=myob.com&u=aHR0cHM6Ly9wYXlkaXJlY3QubXlvYi5jb20vcGF5LyMvOTUwOGNmNzUxOGY4MmJmNDEyOTg3MmE4ZjZmNzdhODc_c291cmNlPWVtYWlsLXZpZXcmdHlwZT1pbnZvaWNl&e=Y2hyaXN0aW5lQHNvdXRoZXJuc3RyYXRhc2VydmljZXMuY29tLmF1&t=R3VFOExXWWREMWJuMkZKbFVvWHJiR2UxVFpVSk5mSjAyY0djaTRPU2UzUT0=&h=e1329d54d4e040fd9c2fa5f1dd0009a2 | C:\Program Files\Internet Explorer\iexplore.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3508 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 497
Read events
5 572
Write events
879
Delete events
46
Modification events
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
2
Suspicious files
84
Text files
103
Unknown types
64
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR41A1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2572 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | binary | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabB8D5.tmp | — | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarB8D6.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4530F665.dat | image | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
| 2908 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
73
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2572 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2908 | iexplore.exe | GET | 200 | 13.35.253.20:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEALiUkureckjj7MJj36f730%3D | US | der | 471 b | whitelisted |
2908 | iexplore.exe | GET | 200 | 13.35.253.148:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2908 | iexplore.exe | GET | 200 | 13.35.253.20:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEALiUkureckjj7MJj36f730%3D | US | der | 471 b | whitelisted |
2908 | iexplore.exe | GET | 200 | 13.35.253.148:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 13.35.253.97:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 13.35.253.97:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2908 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEA335eBNi%2BLljjzzi8IS7mc%3D | US | der | 471 b | whitelisted |
2908 | iexplore.exe | GET | 200 | 13.35.253.148:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2908 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2572 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2908 | iexplore.exe | 13.35.253.148:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
2908 | iexplore.exe | 13.35.253.185:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
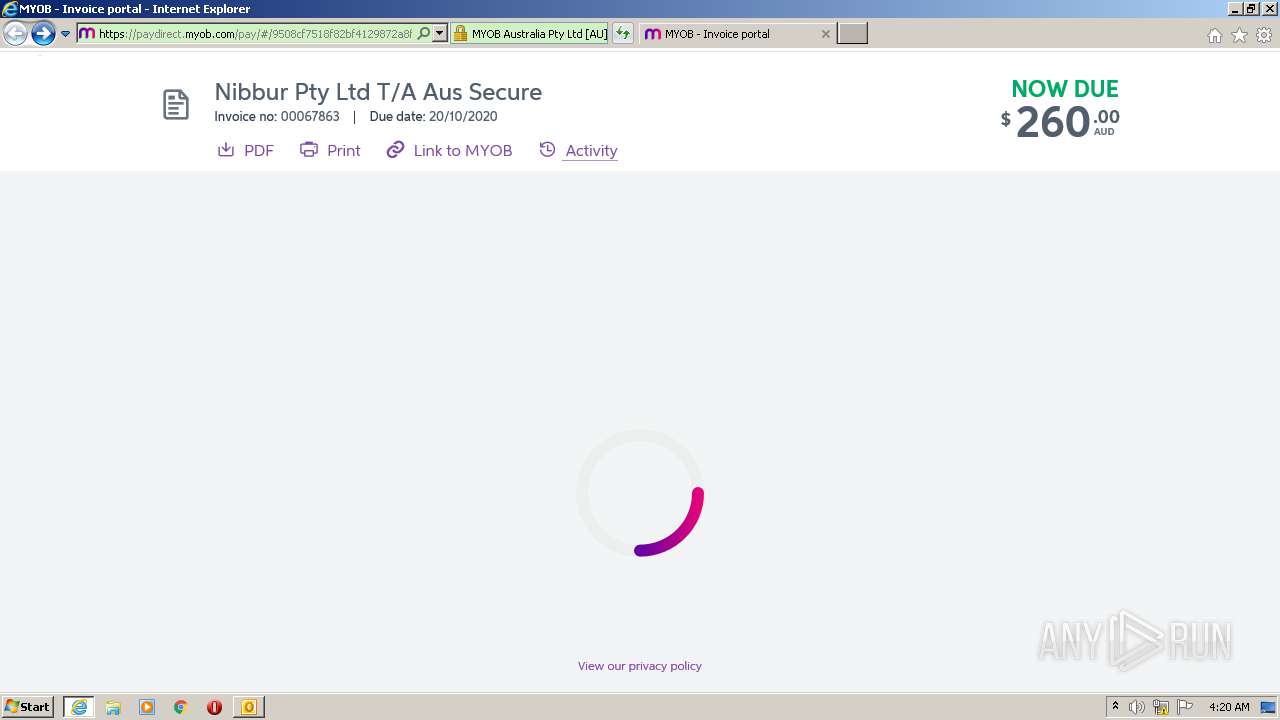
2908 | iexplore.exe | 99.86.7.15:443 | paydirect.myob.com | AT&T Services, Inc. | US | suspicious |
2908 | iexplore.exe | 13.35.253.20:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
2908 | iexplore.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2908 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2908 | iexplore.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3508 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2908 | iexplore.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
us-east-2.protection.sophos.com |
| shared |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
paydirect.myob.com |
| shared |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |