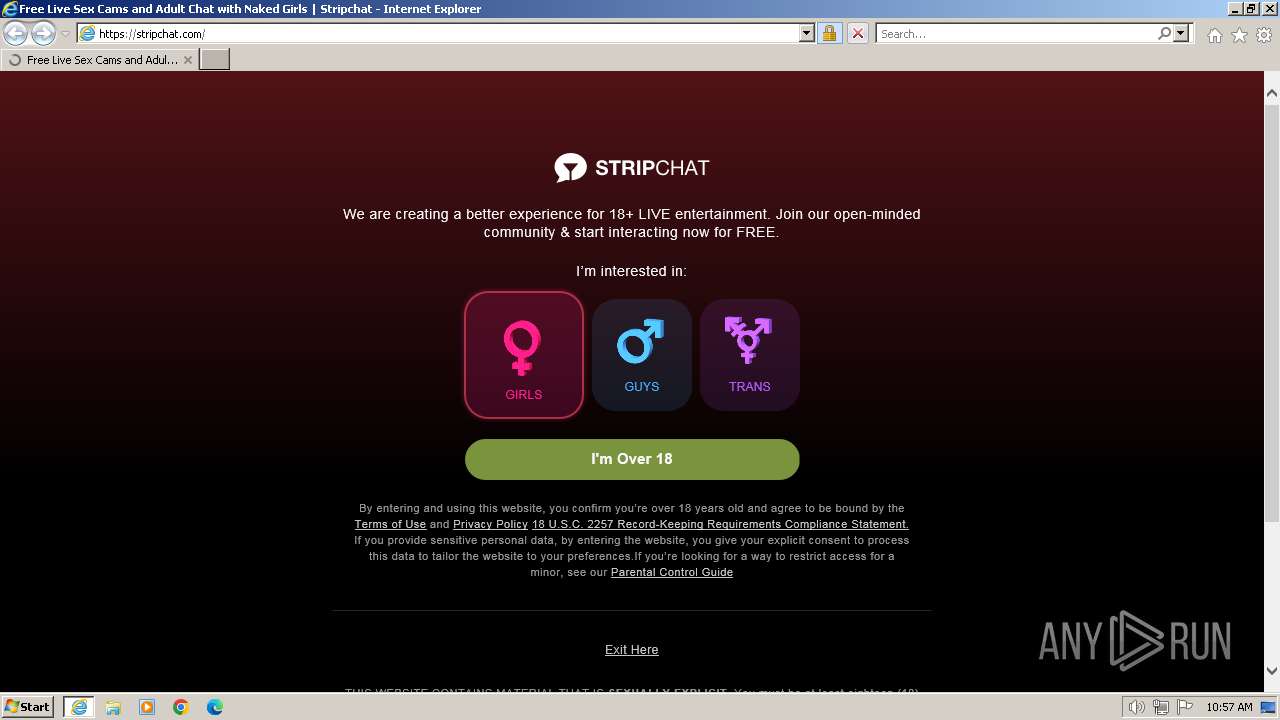
| URL: | http://stripchat.com/ |
| Full analysis: | https://app.any.run/tasks/b1391e36-ee74-4e86-968f-57b26fd002ab |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2024, 10:57:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 20CAF8885886D7D2667BF03F02C6F3E8 |
| SHA1: | 95460F2DB3DACB7CB21C25C3072F9DAE47790AD2 |
| SHA256: | 857F48BA4D858F3ECEF013A231A44912C7892AEAC6378508FC5A9F4DECF0158F |
| SSDEEP: | 3:N1KNRkaGKKn:CPKn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3864 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://stripchat.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3952 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3864 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
14 907
Read events
14 772
Write events
98
Delete events
37
Modification events
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31088436 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31088436 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
34
Suspicious files
7
Text files
135
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RJOMS42Z.txt | text | |
MD5:FC434F046A85C61A73A5F895E8A2EF79 | SHA256:319A1DD84ED8F852CD1B8A86FCBB5C9D274B6A49AD09DCD1530615EBD83C290A | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:BBE13E12932CDFE99ADDDC490D71024F | SHA256:CA78A403DD081AA51742EF8767127FE2B8DD811963E56F5A46301263F3FA72CF | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6HHL90I2.txt | text | |
MD5:DE62F7373109FF2C65F658A41C4AC6C0 | SHA256:7BA281823C78A64F01FB301AF6F3EF01D813392F4091BBD7026BBA5F09709457 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\9K51QSGA.txt | text | |
MD5:806D6AEC717200A739D9622CC587BAB5 | SHA256:BB301F131556D039263AE0AB17373982BFE0DB7A50CE8A1673AD317396C13BD4 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BBFPU3QL.txt | text | |
MD5:3C27D43E71430B0E9D338122FBD8859C | SHA256:A821C2378FF754CDC39EF3587071E6EA2955496629C2A67BDD56B04BC368BCE8 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\UFIFEWNB.txt | text | |
MD5:5EEB6CCC04FB0D96CF66B636C9F02DBB | SHA256:05FB2F194169213EDA501F3F1460A30A86CB023EF86FD9EC7C0B77A8C4002F07 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\OY2KE1LF.txt | text | |
MD5:6982B799B783D919C2BE70D85F543FE7 | SHA256:CC16F534C7C62E2BD26F06A95A6A876D3A85378BCA417279B984E7D9707B2874 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:CE807E63956547D53D7ED56A92D0D25D | SHA256:4889044B8038B174297B6FA463110A9448C4FFB7D030E65949977393B7795BD1 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BHOSI3FE.txt | text | |
MD5:F7F5E4301731F6159FF6E5D29C6F6577 | SHA256:598A80E6FC34194B76E2084AD0474F2059E5AF66FA637CA2E1185550737C1A59 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5WBLIOGU.txt | text | |
MD5:17EC1B499AEBFD0BE6EAB95F445AD46C | SHA256:CDFD5AB75226F9620BC29DE51005A8E053250BC65806D5B5EFFF0333BAFE0850 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
32
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3952 | iexplore.exe | GET | 301 | 104.18.63.126:80 | http://stripchat.com/ | unknown | — | — | unknown |
3952 | iexplore.exe | GET | 304 | 178.79.238.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?64db15c300a7b163 | unknown | — | — | unknown |
3952 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
3864 | iexplore.exe | GET | 304 | 178.79.238.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?96c8eb5dfc595a04 | unknown | — | — | unknown |
3864 | iexplore.exe | GET | 304 | 178.79.238.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bdc5ae628aaf0bd4 | unknown | — | — | unknown |
3864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
3864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0754c686571bd23f | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3952 | iexplore.exe | 104.18.63.126:80 | stripchat.com | CLOUDFLARENET | — | shared |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3952 | iexplore.exe | 104.18.63.126:443 | stripchat.com | CLOUDFLARENET | — | shared |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3952 | iexplore.exe | 178.79.238.128:80 | ctldl.windowsupdate.com | LLNW | FR | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3952 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3952 | iexplore.exe | 104.18.63.132:443 | assets.strpst.com | CLOUDFLARENET | — | shared |
3864 | iexplore.exe | 104.18.63.132:443 | assets.strpst.com | CLOUDFLARENET | — | shared |
3864 | iexplore.exe | 178.79.238.128:80 | ctldl.windowsupdate.com | LLNW | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stripchat.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
assets.strpst.com |
| unknown |
img.strpst.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |