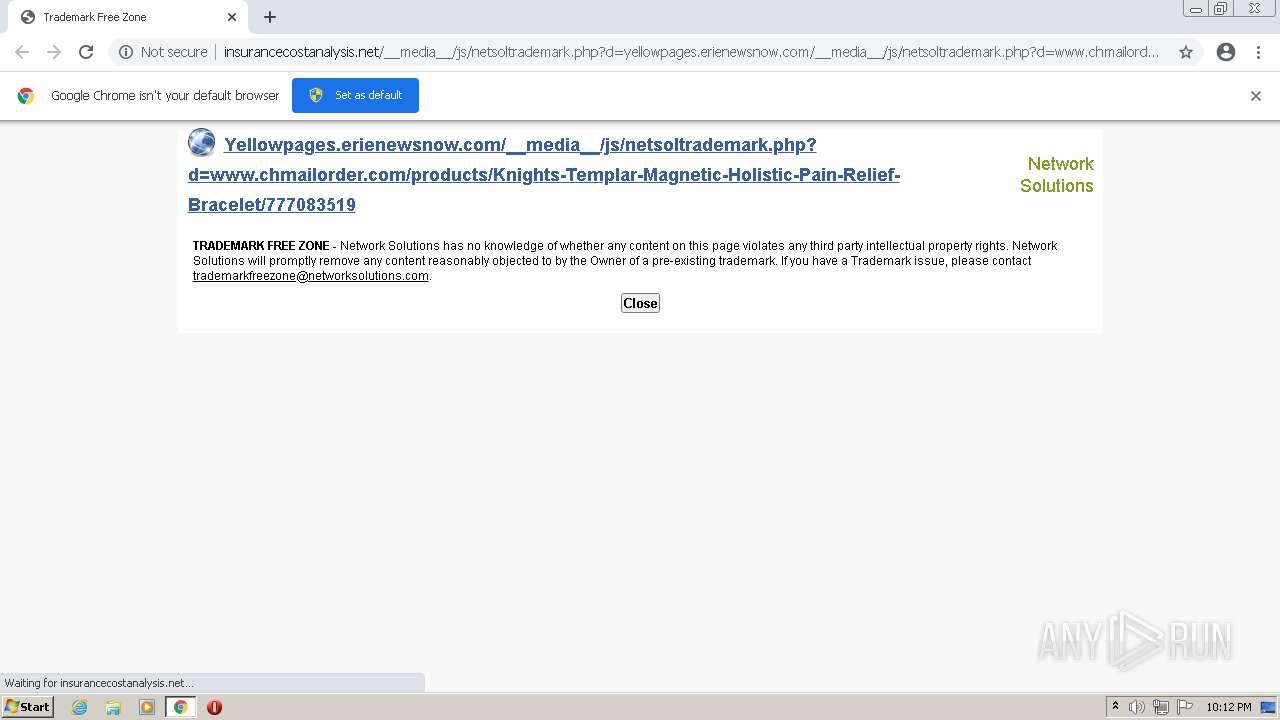
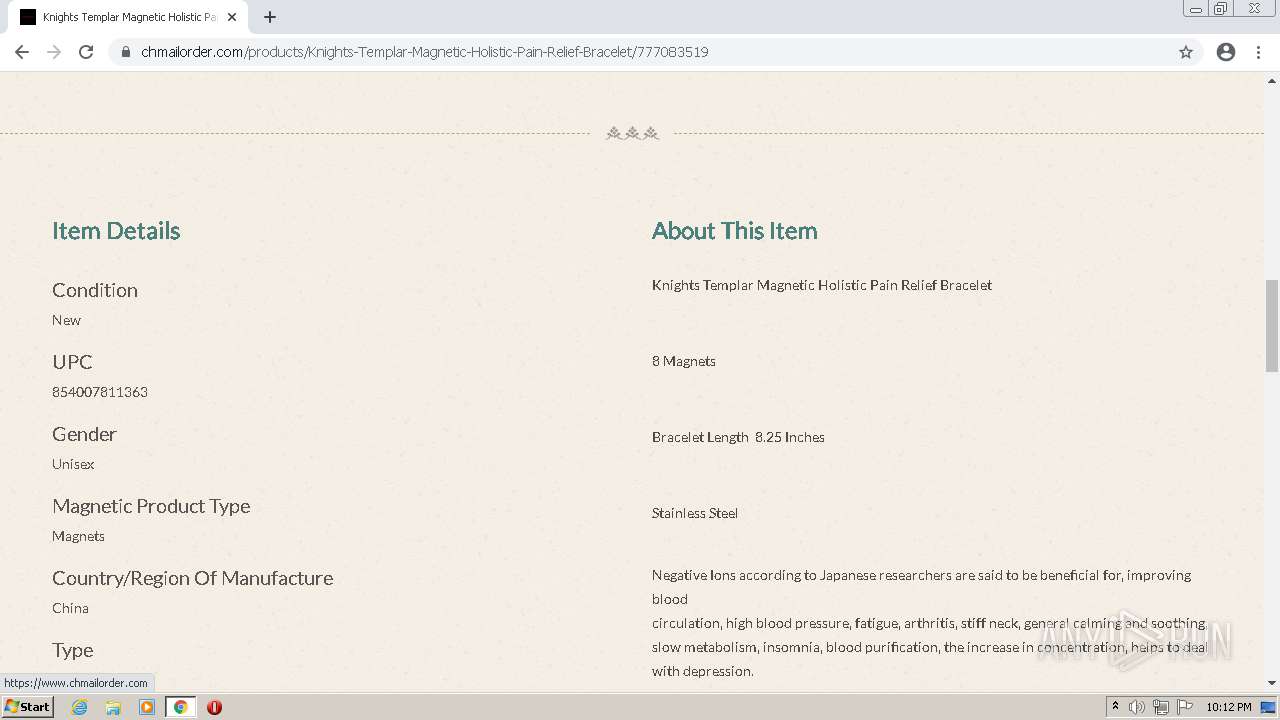
| URL: | http://insurancecostanalysis.net/__media__/js/netsoltrademark.php?d=yellowpages.erienewsnow.com/__media__/js/netsoltrademark.php?d=www.chmailorder.com%2Fproducts%2FKnights-Templar-Magnetic-Holistic-Pain-Relief-Bracelet%2F777083519 |
| Full analysis: | https://app.any.run/tasks/7470b208-a471-4a46-b9c7-b883deb75fab |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2021, 21:12:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 780990665493422612496C59AD52E9A3 |
| SHA1: | B3B2FCF81EA3187DC629DA610D5D91D6776AE119 |
| SHA256: | 85768F7111B8B851A5DDFF0CB4AF0BE4F86B206BFF20E53F82D74B2C5B64BD52 |
| SSDEEP: | 6:CQZHQxX9sJHHlLbKiXzhl9GWBzoo/XEuyugQFn:tZwxX9srLbZX93BBzfybqn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 1456)
Reads the computer name
- chrome.exe (PID: 1456)
- chrome.exe (PID: 824)
- chrome.exe (PID: 520)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 2272)
Reads the hosts file
- chrome.exe (PID: 1456)
- chrome.exe (PID: 520)
Checks supported languages
- chrome.exe (PID: 824)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 1456)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 520)
- chrome.exe (PID: 568)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2272)
Reads settings of System Certificates
- chrome.exe (PID: 520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1028 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1068 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://insurancecostanalysis.net/__media__/js/netsoltrademark.php?d=yellowpages.erienewsnow.com/__media__/js/netsoltrademark.php?d=www.chmailorder.com%2Fproducts%2FKnights-Templar-Magnetic-Holistic-Pain-Relief-Bracelet%2F777083519" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2872 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2808 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,11412537822406975521,14671072684930885297,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
7 720
Read events
7 664
Write events
56
Delete events
0
Modification events
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
15
Text files
56
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-612803C9-5B0.pma | — | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3eab53e9-c9c2-4165-b57c-cc799d0b1540.tmp | text | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\MANIFEST-000001 | binary | |
MD5:5AF87DFD673BA2115E2FCF5CFDB727AB | SHA256:F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4 | |||
| 3504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1c989e.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f06cb998-a768-4a1a-8cf8-89e6fc348d74.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1c989e.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
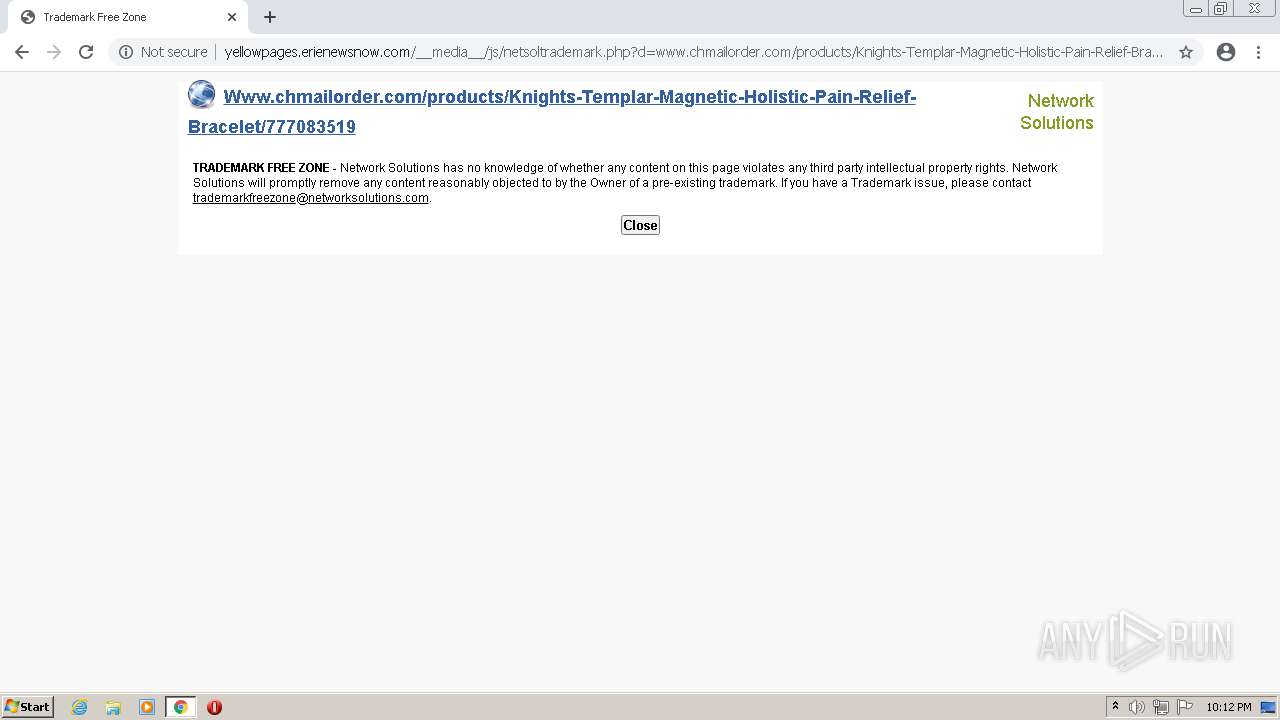
520 | chrome.exe | GET | 301 | 216.168.59.154:80 | http://www.chmailorder.com/products/Knights-Templar-Magnetic-Holistic-Pain-Relief-Bracelet/777083519 | US | — | — | unknown |
520 | chrome.exe | GET | 200 | 208.91.197.127:80 | http://insurancecostanalysis.net/__media__/js/netsoltrademark.php?d=yellowpages.erienewsnow.com/__media__/js/netsoltrademark.php?d=www.chmailorder.com%2Fproducts%2FKnights-Templar-Magnetic-Holistic-Pain-Relief-Bracelet%2F777083519 | VG | html | 1.71 Kb | malicious |
520 | chrome.exe | GET | 200 | 208.91.196.253:80 | http://nine.cdn-image.com/__media__/pics/451/netsol-logo.jpg | VG | image | 909 b | suspicious |
520 | chrome.exe | GET | 200 | 208.91.196.253:80 | http://nine.cdn-image.com/__media__/pics/451/netsol-logo.jpg | VG | image | 909 b | suspicious |
520 | chrome.exe | GET | 404 | 199.191.50.235:80 | http://yellowpages.erienewsnow.com/favicon.ico | VG | text | 30 b | unknown |
520 | chrome.exe | GET | 200 | 199.191.50.235:80 | http://yellowpages.erienewsnow.com/__media__/js/netsoltrademark.php?d=www.chmailorder.com/products/Knights-Templar-Magnetic-Holistic-Pain-Relief-Bracelet/777083519 | VG | html | 1.69 Kb | unknown |
520 | chrome.exe | GET | 404 | 208.91.197.127:80 | http://insurancecostanalysis.net/favicon.ico | VG | text | 30 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
520 | chrome.exe | 142.250.185.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
520 | chrome.exe | 208.91.196.253:80 | nine.cdn-image.com | Confluence Networks Inc | VG | suspicious |
520 | chrome.exe | 142.250.186.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
520 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
520 | chrome.exe | 199.191.50.235:80 | yellowpages.erienewsnow.com | Confluence Networks Inc | VG | unknown |
520 | chrome.exe | 216.168.59.154:80 | www.chmailorder.com | Digital Fortress, Inc. | US | unknown |
520 | chrome.exe | 216.168.59.154:443 | www.chmailorder.com | Digital Fortress, Inc. | US | unknown |
520 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
520 | chrome.exe | 142.250.185.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
520 | chrome.exe | 185.172.148.128:443 | assets.bonanzastatic.com | proinity GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
insurancecostanalysis.net |
| malicious |
accounts.google.com |
| shared |
nine.cdn-image.com |
| suspicious |
www.networksolutions.com |
| whitelisted |
yellowpages.erienewsnow.com |
| unknown |
ssl.gstatic.com |
| whitelisted |
www.chmailorder.com |
| unknown |
assets.bonanzastatic.com |
| malicious |
fonts.googleapis.com |
| whitelisted |