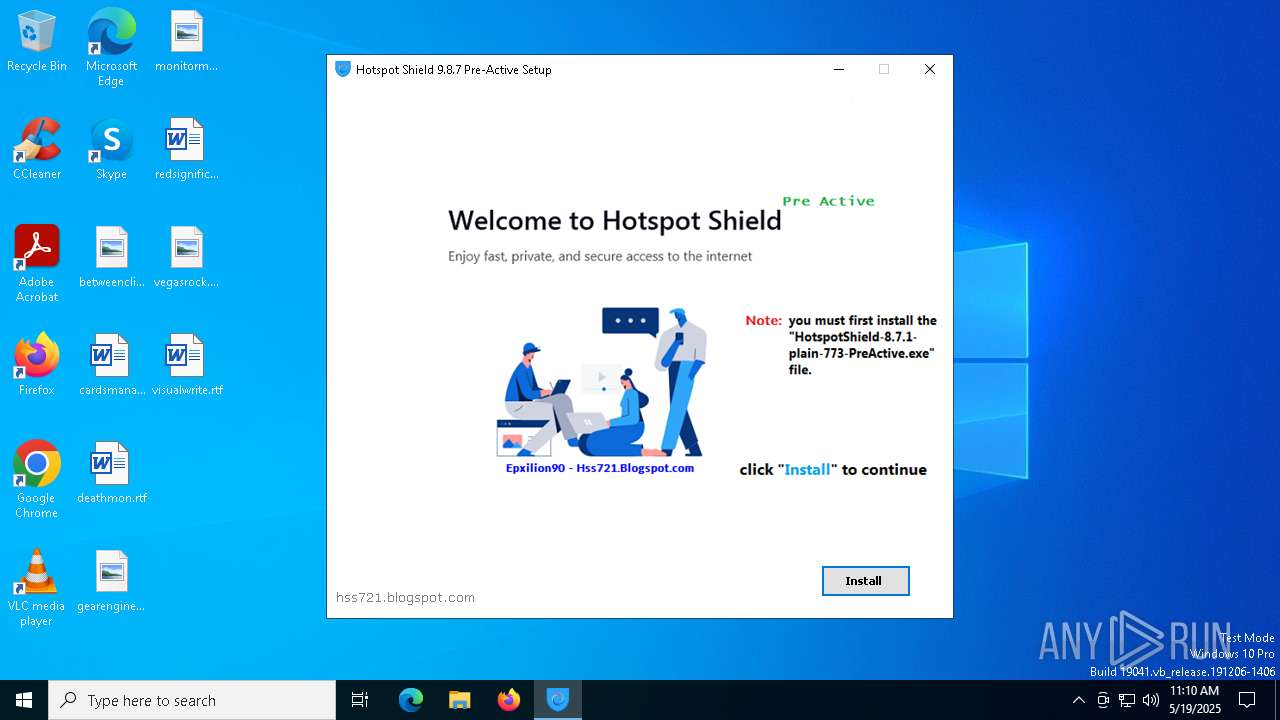
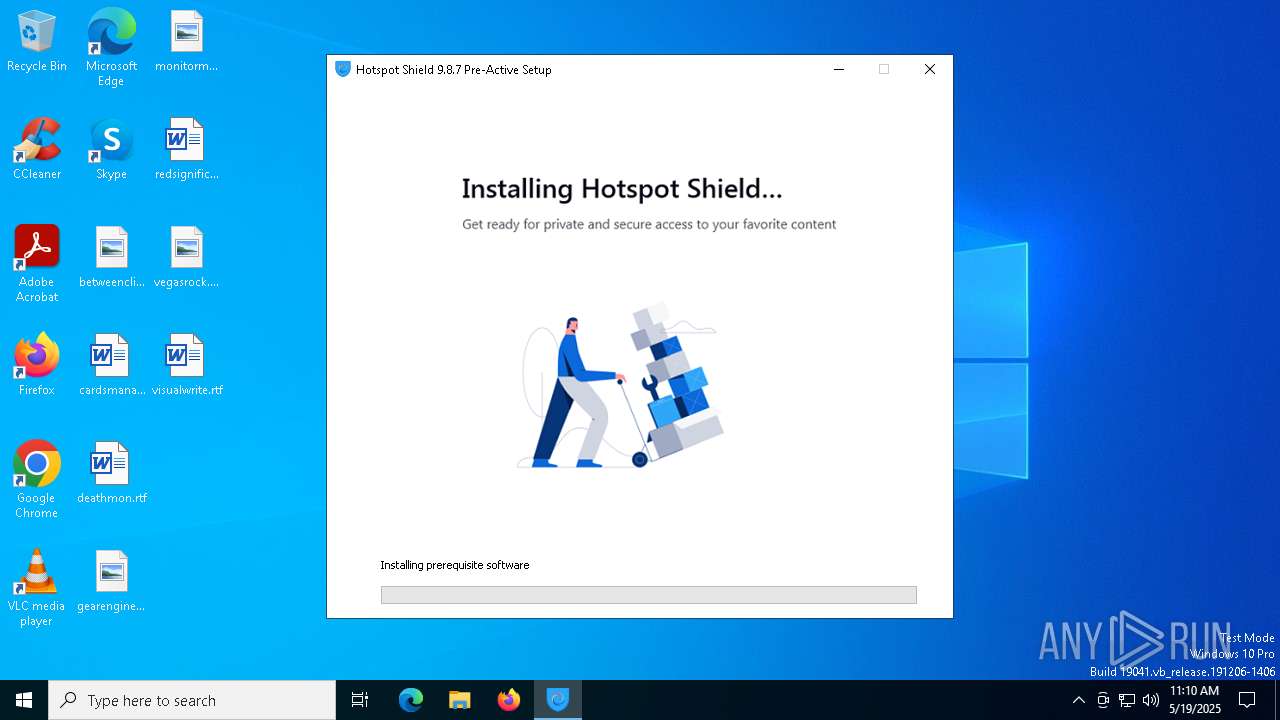
| File name: | HotspotShield-9.8.7-plain-773-PreActive.exe |
| Full analysis: | https://app.any.run/tasks/7e977313-523e-4083-a9c4-a223411fcd54 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 11:09:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 3D4C8BC415B5C96DDBA4DA8CB5ABFA6B |
| SHA1: | 6DDEEF50C7BAF52B3323D6265DD0E559DC2B05E2 |
| SHA256: | 856CE513C5E07D111907FCA6023D7341C9D3C934D281BFEC0C8E4FE16FC8971A |
| SSDEEP: | 49152:/3fLUDM36u8Q8d0D02b6Pw2wLEz3POgGNkAty5rodctrqdYrpupApSXxu2bijMZR:L377777771T |
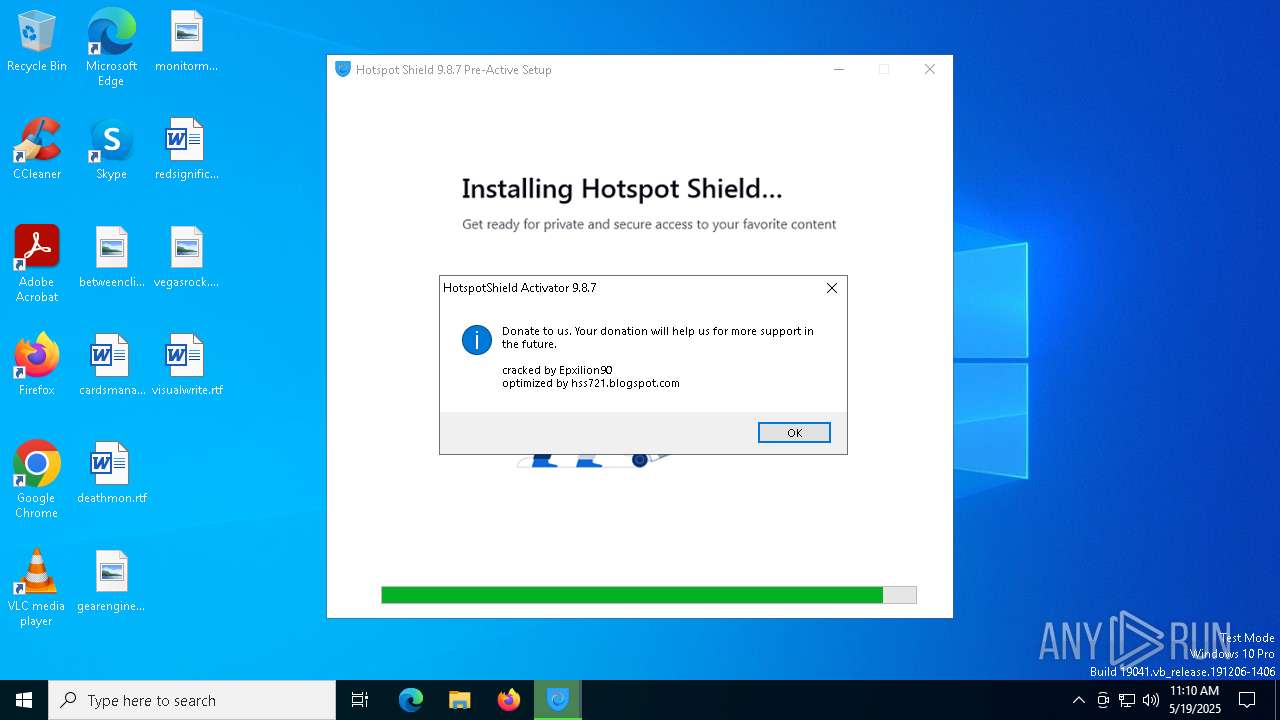
MALICIOUS
Executing a file with an untrusted certificate
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8040)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7576)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- cmw_srv.exe (PID: 1388)
- hsscp.exe (PID: 7372)
- hsscp.exe (PID: 5508)
- hsscp.exe (PID: 2108)
Changes the autorun value in the registry
- reg.exe (PID: 7896)
XORed URL has been found (YARA)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
SUSPICIOUS
Reads security settings of Internet Explorer
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- msiexec.exe (PID: 3176)
- tapinstall.exe (PID: 5552)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- cmw_srv.exe (PID: 1388)
- hsscp.exe (PID: 5508)
- MSI542B.tmp (PID: 516)
- hsscp.exe (PID: 2108)
Starts CMD.EXE for commands execution
- ftp.exe (PID: 7832)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 4224)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7880)
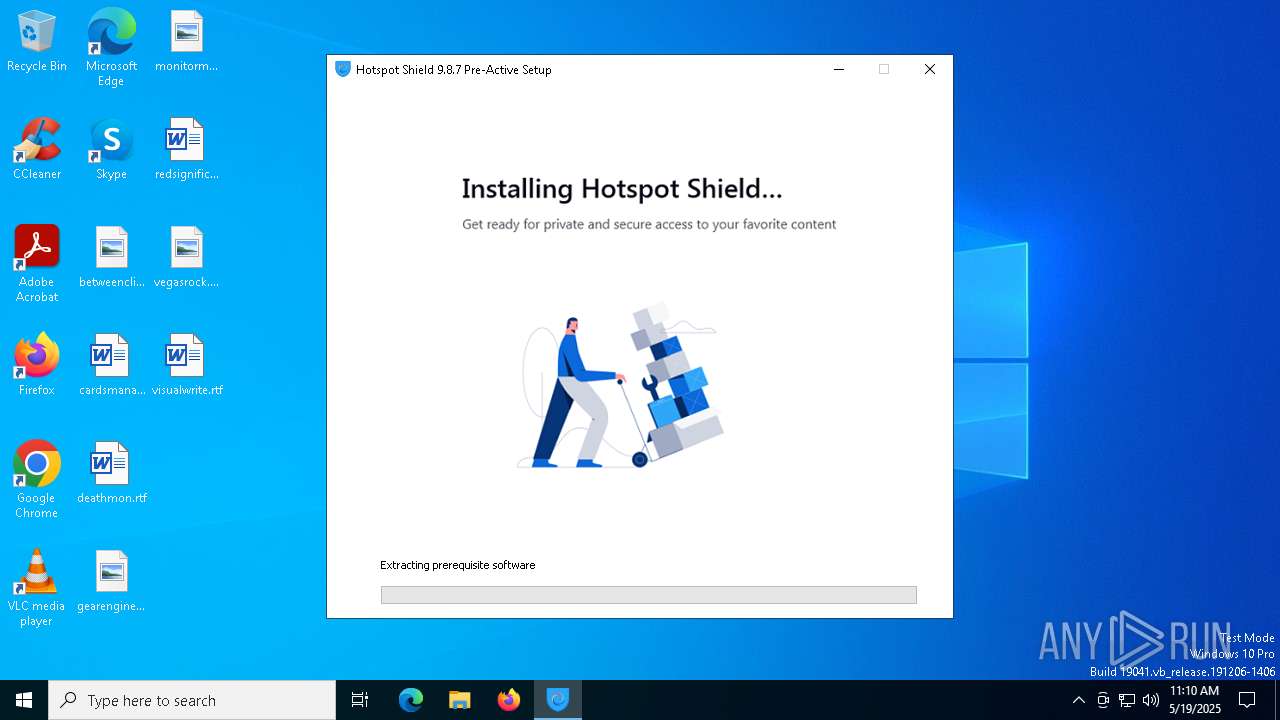
Executable content was dropped or overwritten
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7576)
- tap-windows-9.21.2.exe (PID: 5668)
- tap-windows-9.21.2.EXE (PID: 4164)
- tapinstall.exe (PID: 5552)
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 7212)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- cmw_srv.exe (PID: 1388)
The process checks if it is being run in the virtual environment
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 7932)
ADVANCEDINSTALLER mutex has been found
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
Reads the Windows owner or organization settings
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- msiexec.exe (PID: 8164)
Process drops legitimate windows executable
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- msiexec.exe (PID: 8164)
Malware-specific behavior (creating "System.dll" in Temp)
- tap-windows-9.21.2.EXE (PID: 4164)
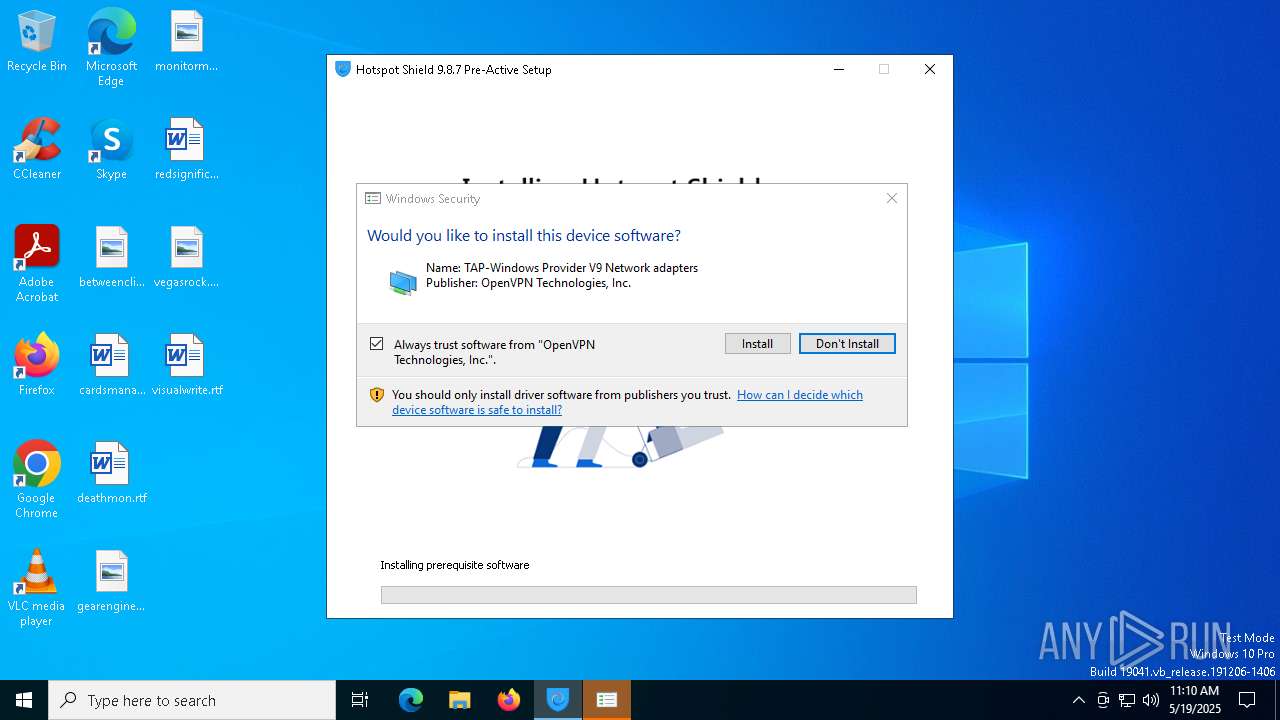
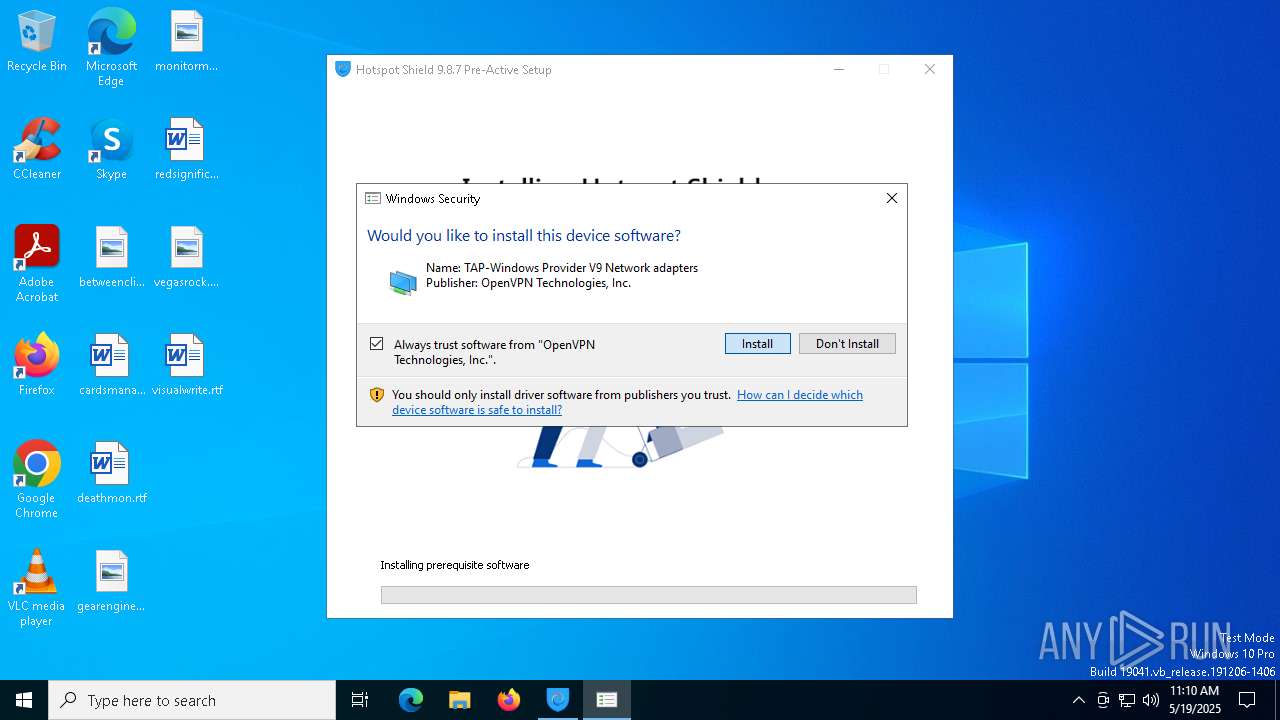
Drops a system driver (possible attempt to evade defenses)
- tap-windows-9.21.2.EXE (PID: 4164)
- tapinstall.exe (PID: 5552)
- drvinst.exe (PID: 6476)
- msiexec.exe (PID: 8164)
- drvinst.exe (PID: 7212)
The process creates files with name similar to system file names
- tap-windows-9.21.2.EXE (PID: 4164)
- msiexec.exe (PID: 8164)
Detects AdvancedInstaller (YARA)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
Creates files in the driver directory
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 7212)
There is functionality for taking screenshot (YARA)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
Creates or modifies Windows services
- drvinst.exe (PID: 7212)
Executes as Windows Service
- cmw_srv.exe (PID: 1388)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6272)
- cmd.exe (PID: 4224)
Starts application with an unusual extension
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
Executing commands from a ".bat" file
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 4224)
Application launched itself
- cmd.exe (PID: 4224)
- cmd.exe (PID: 6272)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
Creates a software uninstall entry
- tap-windows-9.21.2.EXE (PID: 4164)
INFO
Checks supported languages
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- msiexec.exe (PID: 8164)
- msiexec.exe (PID: 3176)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7576)
- tap-windows-9.21.2.exe (PID: 5668)
- tap-windows-9.21.2.EXE (PID: 4164)
- tapinstall.exe (PID: 3900)
- tapinstall.exe (PID: 5552)
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 7212)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- msiexec.exe (PID: 7536)
- msiexec.exe (PID: 7988)
- cmw_srv.exe (PID: 1388)
- hsscp.exe (PID: 5508)
- hsscp.exe (PID: 7372)
- hsscp.exe (PID: 2108)
- MSI542B.tmp (PID: 516)
Checks proxy server information
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
- MSI542B.tmp (PID: 516)
Reads the computer name
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- msiexec.exe (PID: 3176)
- msiexec.exe (PID: 8164)
- tapinstall.exe (PID: 5552)
- drvinst.exe (PID: 7212)
- drvinst.exe (PID: 6476)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- msiexec.exe (PID: 7536)
- msiexec.exe (PID: 7988)
- cmw_srv.exe (PID: 1388)
- hsscp.exe (PID: 7372)
- hsscp.exe (PID: 5508)
- MSI542B.tmp (PID: 516)
- tap-windows-9.21.2.exe (PID: 5668)
- hsscp.exe (PID: 2108)
The sample compiled with english language support
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- tap-windows-9.21.2.EXE (PID: 4164)
- tapinstall.exe (PID: 5552)
- drvinst.exe (PID: 6476)
- drvinst.exe (PID: 7212)
- msiexec.exe (PID: 8164)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
Creates files or folders in the user directory
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7576)
Create files in a temporary directory
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 7772)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- tap-windows-9.21.2.EXE (PID: 4164)
- tap-windows-9.21.2.exe (PID: 5668)
- tapinstall.exe (PID: 5552)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- MSI542B.tmp (PID: 516)
Reads security settings of Internet Explorer
- explorer.exe (PID: 8000)
- rundll32.exe (PID: 6700)
Reads the machine GUID from the registry
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- tapinstall.exe (PID: 5552)
- drvinst.exe (PID: 6476)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- msiexec.exe (PID: 8164)
- cmw_srv.exe (PID: 1388)
- hsscp.exe (PID: 7372)
- hsscp.exe (PID: 5508)
- hsscp.exe (PID: 2108)
Reads the software policy settings
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- tapinstall.exe (PID: 5552)
- drvinst.exe (PID: 6476)
- rundll32.exe (PID: 6700)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- msiexec.exe (PID: 8164)
- cmw_srv.exe (PID: 1388)
Reads Environment values
- msiexec.exe (PID: 3176)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 6324)
- msiexec.exe (PID: 7536)
- cmw_srv.exe (PID: 1388)
Process checks computer location settings
- msiexec.exe (PID: 3176)
- HotspotShield-9.8.7-plain-773-PreActive.exe (PID: 8088)
- MSI542B.tmp (PID: 516)
Creates files in the program directory
- tap-windows-9.21.2.EXE (PID: 4164)
- cmw_srv.exe (PID: 1388)
Adds/modifies Windows certificates
- drvinst.exe (PID: 6476)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8164)
Creates a software uninstall entry
- msiexec.exe (PID: 8164)
Reads product name
- cmw_srv.exe (PID: 1388)
Disables trace logs
- cmw_srv.exe (PID: 1388)
Local mutex for internet shortcut management
- MSI542B.tmp (PID: 516)
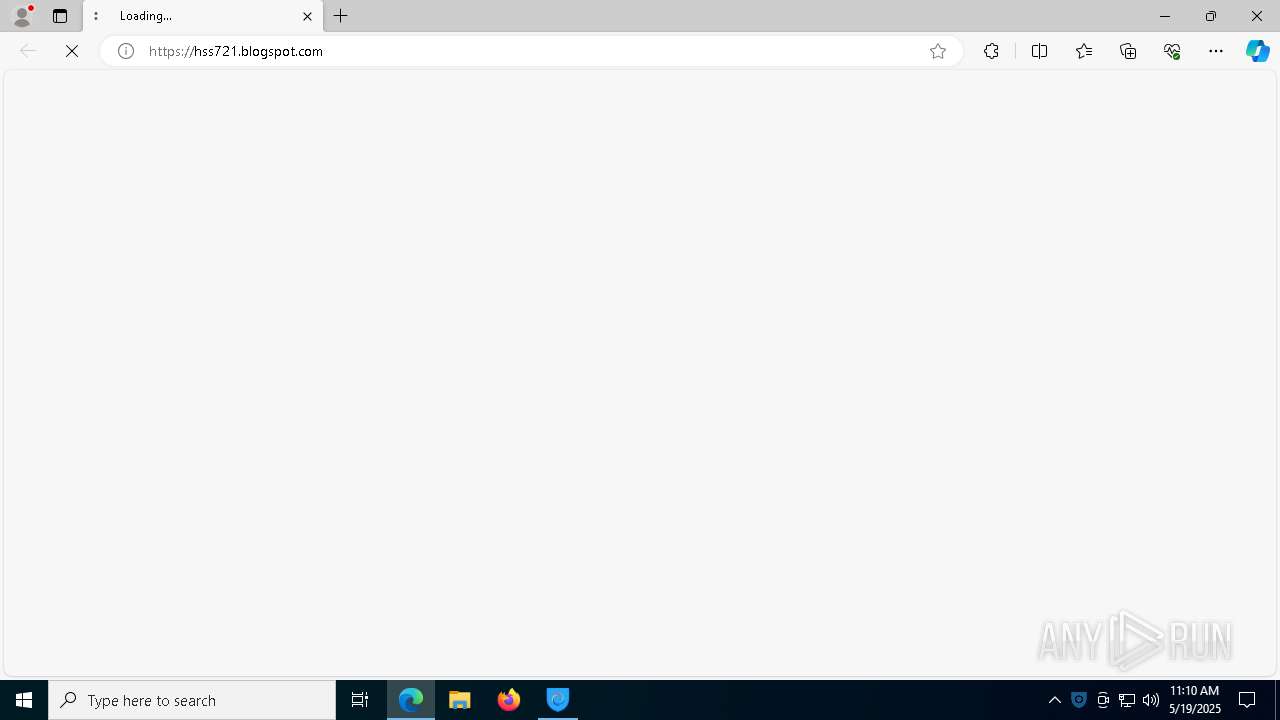
Manual execution by a user
- hsscp.exe (PID: 2108)
- msedge.exe (PID: 5744)
Application launched itself
- msedge.exe (PID: 5744)
- msedge.exe (PID: 1676)
- msedge.exe (PID: 8404)
.NET Reactor protector has been detected
- cmw_srv.exe (PID: 1388)
- hsscp.exe (PID: 5508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:10:28 18:53:37+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.3 |
| CodeSize: | 42643968 |
| InitializedDataSize: | 427520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x28a0a98 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.8.7.11577 |
| ProductVersionNumber: | 9.8.7.11577 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
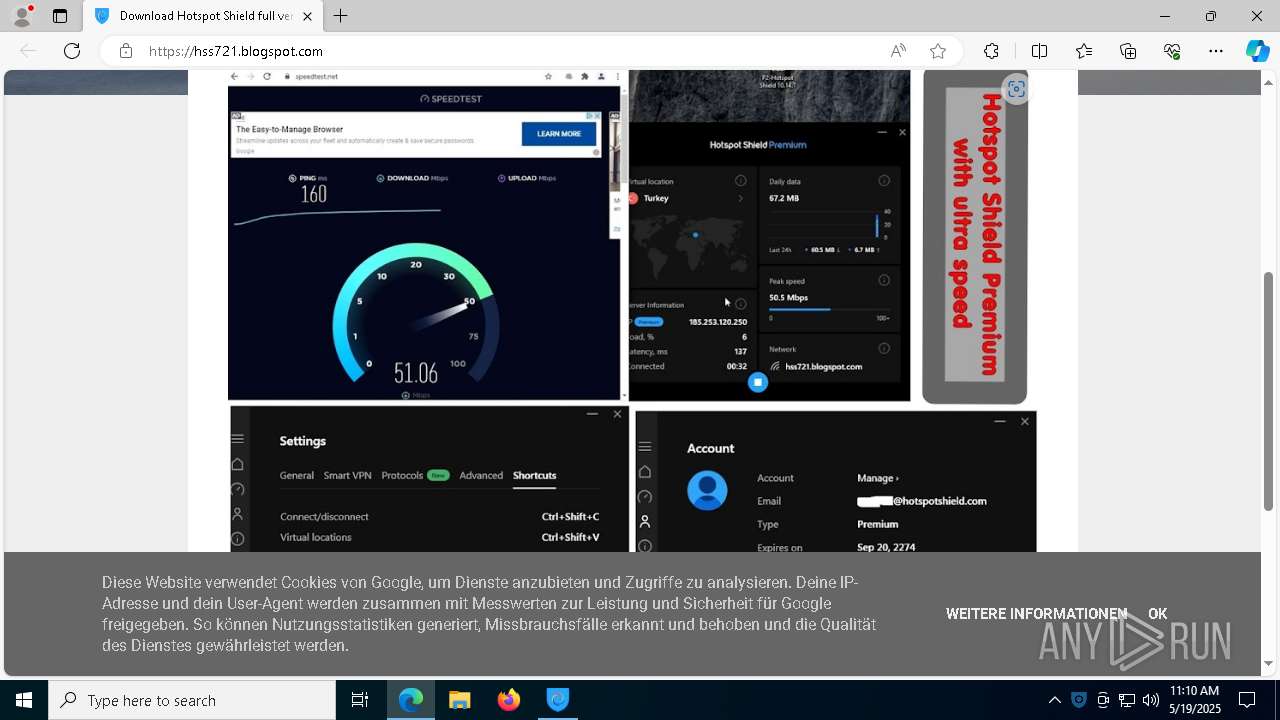
| CompanyName: | hss721.blogspot.com |
| FileDescription: | Hotspot Shield 9.8.7 Pre-Active |
| FileVersion: | 9.8.7.11577 |
| InternalName: | HotspotShield-9.8.7-plain-773-PreActive |
| LegalCopyright: | Copyright (C) 2020 hss721.blogspot.com |
| OriginalFileName: | HotspotShield-9.8.7-plain-773-PreActive.exe |
| ProductName: | Hotspot Shield 9.8.7 Pre-Active |
| ProductVersion: | 9.8.7.11577 |
Total processes
234
Monitored processes
101
Malicious processes
9
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Users\admin\AppData\Local\Temp\MSI542B.tmp" https://hss721.blogspot.com | C:\Users\admin\AppData\Local\Temp\MSI542B.tmp | — | HotspotShield-9.8.7-plain-773-PreActive.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: HIGH Description: File that launches another file Exit code: 0 Version: 17.0.0.0 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=6104 --field-trial-handle=2320,i,5926588401530243880,3780909861146239205,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3688 --field-trial-handle=2320,i,5926588401530243880,3780909861146239205,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6308 --field-trial-handle=2320,i,5926588401530243880,3780909861146239205,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 840 | C:\WINDOWS\System32\attrib.exe -r "C:\Users\admin\AppData\Local\Temp\EXE545B.bat" | C:\Windows\SysWOW64\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | C:\WINDOWS\System32\attrib.exe -r "\\?\C:\Users\admin\AppData\Roaming\HSS721~1.COM\HOTSPO~1.115\install\LOCKHO~1.MSI" | C:\Windows\SysWOW64\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4300 --field-trial-handle=2320,i,5926588401530243880,3780909861146239205,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3516 --field-trial-handle=2320,i,5926588401530243880,3780909861146239205,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Hotspot Shield\9.8.7\bin\cmw_srv.exe" | C:\Program Files (x86)\Hotspot Shield\9.8.7\bin\cmw_srv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Pango Inc. Integrity Level: SYSTEM Description: Hss.Service.Application Version: 9.8.7.11577 Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5456 --field-trial-handle=2320,i,5926588401530243880,3780909861146239205,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
50 137
Read events
49 724
Write events
394
Delete events
19
Modification events
| (PID) Process: | (7772) HotspotShield-9.8.7-plain-773-PreActive.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7772) HotspotShield-9.8.7-plain-773-PreActive.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7772) HotspotShield-9.8.7-plain-773-PreActive.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7772) HotspotShield-9.8.7-plain-773-PreActive.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7896) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | HotspotUpdater |
Value: C:\Users\admin\AppData\Local\Temp\HotspotUpdater.exe | |||
| (PID) Process: | (5552) tapinstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (7212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\tap0901 |
| Operation: | write | Name: | Owners |
Value: oem1.inf | |||
| (PID) Process: | (7212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Setup\PnpLockdownFiles\%SystemRoot%/System32/drivers/tap0901.sys |
| Operation: | write | Name: | Owners |
Value: oem1.inf | |||
| (PID) Process: | (7212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\DRIVERS\DriverDatabase\DriverPackages\oemvista.inf_amd64_a572b7f20c402d28\Descriptors\tap0901 |
| Operation: | write | Name: | Configuration |
Value: tap0901.ndi | |||
| (PID) Process: | (7212) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\DRIVERS\DriverDatabase\DriverPackages\oemvista.inf_amd64_a572b7f20c402d28\Descriptors\tap0901 |
| Operation: | write | Name: | Manufacturer |
Value: %provider% | |||
Executable files
158
Suspicious files
282
Text files
98
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7772 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\HotspotUpdater.exe | — | |
MD5:— | SHA256:— | |||
| 8088 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Roaming\hss721.blogspot.com\Hotspot Shield 9.8.7 Pre-Active 9.8.7.11577\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 7772 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\__temp_cmd.txt | binary | |
MD5:67177A32985B6AF1A43880460C6D430E | SHA256:CEB114EDA7FE4DA47B1533F745A23EB78BDFF4D590283478A500247666CAF9EA | |||
| 8088 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\MSIE6ED.tmp | executable | |
MD5:C39DAEBA173815516C180CA4361F7895 | SHA256:A34BD87A23349BD52B8B0F25154235B90B698986C8849E101B7E40D11D48E4DC | |||
| 8088 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_8088\hss.ico | image | |
MD5:4B47AB834B9B551F473B4AC20720968C | SHA256:74FA67B7F6D7D915D66BFF3AA8C254B964F89AA32020DBDD562596D9E65E7DD7 | |||
| 7772 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\HotspotShield-9.8.7-plain-773-PreActive.exe | executable | |
MD5:E7FF4977EA73D84AAF8E5DE447489F20 | SHA256:17B9F275942054333847E4584D794ED7429AD83B72038FF20E04161332095460 | |||
| 8088 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\MSIE68C.tmp | executable | |
MD5:C39DAEBA173815516C180CA4361F7895 | SHA256:A34BD87A23349BD52B8B0F25154235B90B698986C8849E101B7E40D11D48E4DC | |||
| 8088 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\MSIE6BC.tmp | executable | |
MD5:C39DAEBA173815516C180CA4361F7895 | SHA256:A34BD87A23349BD52B8B0F25154235B90B698986C8849E101B7E40D11D48E4DC | |||
| 8088 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\shiE580.tmp | executable | |
MD5:84A34BF3486F7B9B7035DB78D78BDD1E | SHA256:F85911C910B660E528D2CF291BAA40A92D09961996D6D84E7A53A7095C7CD96E | |||
| 8088 | HotspotShield-9.8.7-plain-773-PreActive.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_8088\i001upd.png | binary | |
MD5:9E3D2DA837304D1E277568820BEA4841 | SHA256:DD4042BA64B4864526BF816035CC135C22FF125983EDC0D7A7481AFEB8633620 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
89
DNS requests
102
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7908 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7908 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6036 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747700362&P2=404&P3=2&P4=a0rwUbOoblqRAfNpOGCrCKc8UnJrJNHtzYzwQ%2bxQXG8kkyJo%2fvIoikDTnfMoWV0AdevnW34PQ8Sx4oc47Owvmw%3d%3d | unknown | — | — | whitelisted |
6036 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747700362&P2=404&P3=2&P4=a0rwUbOoblqRAfNpOGCrCKc8UnJrJNHtzYzwQ%2bxQXG8kkyJo%2fvIoikDTnfMoWV0AdevnW34PQ8Sx4oc47Owvmw%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6036 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747700362&P2=404&P3=2&P4=a0rwUbOoblqRAfNpOGCrCKc8UnJrJNHtzYzwQ%2bxQXG8kkyJo%2fvIoikDTnfMoWV0AdevnW34PQ8Sx4oc47Owvmw%3d%3d | unknown | — | — | whitelisted |
6036 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747700362&P2=404&P3=2&P4=a0rwUbOoblqRAfNpOGCrCKc8UnJrJNHtzYzwQ%2bxQXG8kkyJo%2fvIoikDTnfMoWV0AdevnW34PQ8Sx4oc47Owvmw%3d%3d | unknown | — | — | whitelisted |
6036 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747700362&P2=404&P3=2&P4=a0rwUbOoblqRAfNpOGCrCKc8UnJrJNHtzYzwQ%2bxQXG8kkyJo%2fvIoikDTnfMoWV0AdevnW34PQ8Sx4oc47Owvmw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1912 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.22:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7452 | svchost.exe | 95.100.186.9:443 | go.microsoft.com | AKAMAI-AS | FR | whitelisted |
7908 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7908 | SIHClient.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
qwrfcvbnj7825xjefygdjssjdh.io |
| unknown |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.hsselite.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2040 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2040 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2040 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2040 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO OpenDrive Cloud Storage Domain in DNS Lookup (od .lk) |