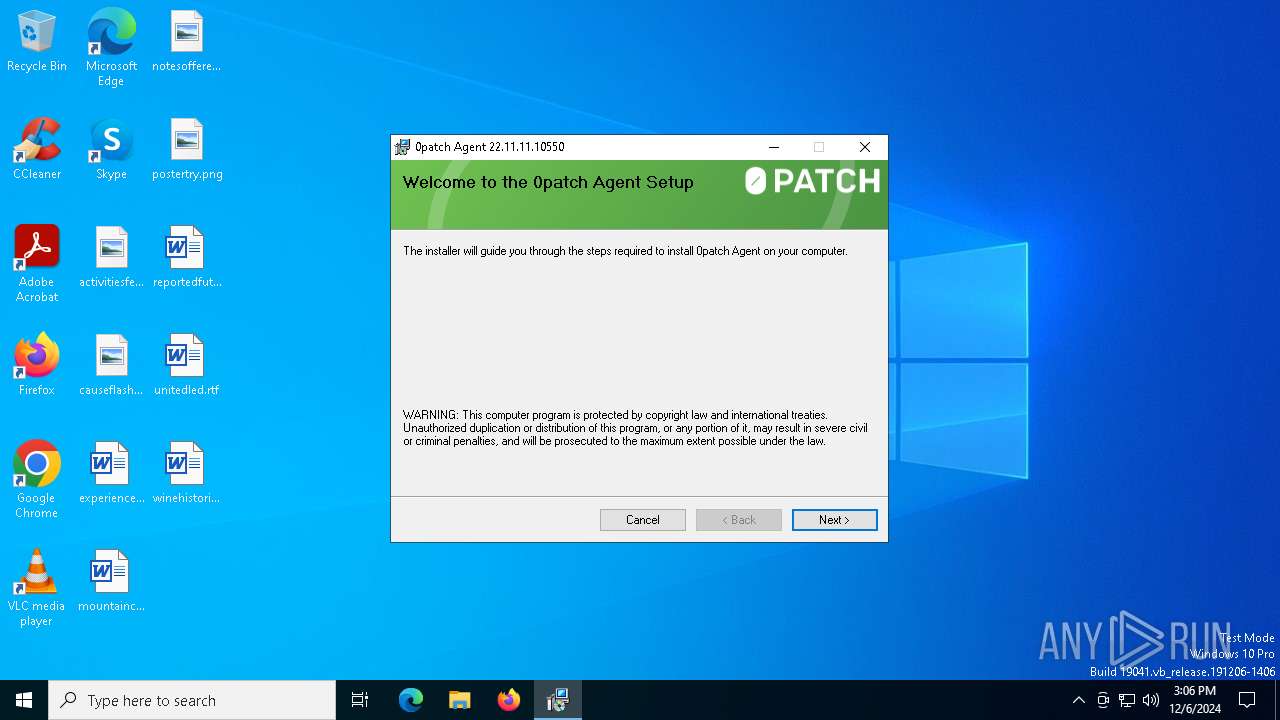
| File name: | 0PatchInstaller_22.11.11.10550.msi |
| Full analysis: | https://app.any.run/tasks/e273de07-50b6-4357-a52c-7a98aa7b040e |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2024, 15:05:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-msi |
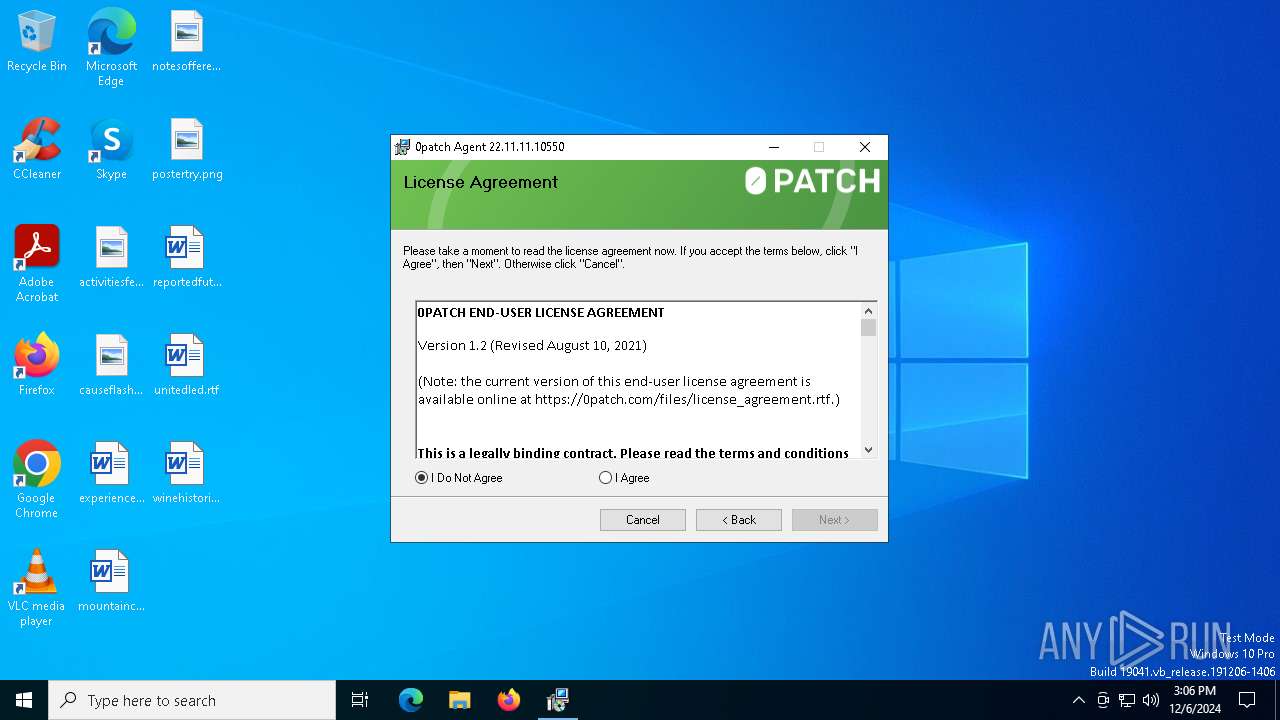
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Create Time/Date: Mon Jun 21 07:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;1033, Number of Pages: 200, Revision Number: {EBE261DB-A42F-49B4-82D5-9C81EC70227B}, Title: 0patch, Author: Acros Security, Comments: 0patch Agent, Number of Words: 2, Last Saved Time/Date: Fri Nov 11 08:11:23 2022, Last Printed: Fri Nov 11 08:11:23 2022 |
| MD5: | DD5C33A1874965AECC6AB4CBB4D401AE |
| SHA1: | 2532F1C99EAA87402CF1F64B0FF2EE3A18B1DFE7 |
| SHA256: | 856C1446329A8C70B72881A8E853352EDCBB06E3C32C57B0E4694BE36890BF86 |
| SSDEEP: | 98304:RGN4tDind42MDUNUiUSwX2IYn6V+ZIfbX0LYqEttAcoChFRpfXeBjVVnQEGX1eu6:jTNiS |
MALICIOUS
Application was injected by another process
- TrustedInstaller.exe (PID: 5464)
- WmiPrvSE.exe (PID: 6764)
- svchost.exe (PID: 1888)
- RuntimeBroker.exe (PID: 6636)
- svchost.exe (PID: 6900)
- backgroundTaskHost.exe (PID: 6300)
- backgroundTaskHost.exe (PID: 6276)
- svchost.exe (PID: 5076)
- svchost.exe (PID: 2992)
- svchost.exe (PID: 376)
- svchost.exe (PID: 3032)
- svchost.exe (PID: 1176)
- svchost.exe (PID: 1764)
- dllhost.exe (PID: 1816)
- TextInputHost.exe (PID: 5288)
- svchost.exe (PID: 3056)
- uhssvc.exe (PID: 2908)
- svchost.exe (PID: 812)
- svchost.exe (PID: 4200)
- UserOOBEBroker.exe (PID: 3004)
- svchost.exe (PID: 1340)
- svchost.exe (PID: 4456)
- RuntimeBroker.exe (PID: 5820)
- MoUsoCoreWorker.exe (PID: 4712)
- svchost.exe (PID: 3976)
- ApplicationFrameHost.exe (PID: 6108)
- dllhost.exe (PID: 5904)
- RuntimeBroker.exe (PID: 4960)
- dllhost.exe (PID: 5164)
- RuntimeBroker.exe (PID: 4676)
- SearchApp.exe (PID: 5064)
- StartMenuExperienceHost.exe (PID: 4896)
- svchost.exe (PID: 4436)
- ctfmon.exe (PID: 4268)
- svchost.exe (PID: 4168)
- svchost.exe (PID: 4176)
- svchost.exe (PID: 3668)
- svchost.exe (PID: 3160)
- svchost.exe (PID: 2952)
- sihost.exe (PID: 1712)
- dasHost.exe (PID: 3896)
- svchost.exe (PID: 2660)
- svchost.exe (PID: 3704)
- svchost.exe (PID: 3592)
- svchost.exe (PID: 3600)
- svchost.exe (PID: 2288)
- svchost.exe (PID: 3016)
- svchost.exe (PID: 3164)
- svchost.exe (PID: 4696)
- explorer.exe (PID: 4488)
- svchost.exe (PID: 4000)
- svchost.exe (PID: 3824)
- svchost.exe (PID: 2256)
- svchost.exe (PID: 2944)
- svchost.exe (PID: 2920)
- OfficeClickToRun.exe (PID: 2884)
- svchost.exe (PID: 2892)
- svchost.exe (PID: 2528)
- svchost.exe (PID: 2816)
- svchost.exe (PID: 2852)
- svchost.exe (PID: 2748)
- spoolsv.exe (PID: 2652)
- svchost.exe (PID: 2500)
- svchost.exe (PID: 2372)
- svchost.exe (PID: 2360)
Runs injected code in another process
- 0patchServicex64.exe (PID: 6924)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6856)
- 0patchServicex64.exe (PID: 6924)
Process drops legitimate windows executable
- msiexec.exe (PID: 6364)
- TiWorker.exe (PID: 6384)
The process drops C-runtime libraries
- msiexec.exe (PID: 6364)
- TiWorker.exe (PID: 6384)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6364)
Checks Windows Trust Settings
- msiexec.exe (PID: 6364)
Executable content was dropped or overwritten
- TiWorker.exe (PID: 6384)
Creates or modifies Windows services
- 0patchServicex64.exe (PID: 6924)
INFO
Reads the computer name
- msiexec.exe (PID: 6364)
Checks supported languages
- msiexec.exe (PID: 6364)
- msiexec.exe (PID: 3820)
- SearchApp.exe (PID: 5064)
- 0patchScanner.exe (PID: 6892)
- StartMenuExperienceHost.exe (PID: 4896)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1752)
- RuntimeBroker.exe (PID: 6636)
- explorer.exe (PID: 4488)
Reads the software policy settings
- msiexec.exe (PID: 1752)
- SearchApp.exe (PID: 5064)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- msiexec.exe (PID: 6364)
Creates files in the program directory
- MoUsoCoreWorker.exe (PID: 4712)
Manages system restore points
- SrTasks.exe (PID: 5096)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6364)
Creates a software uninstall entry
- msiexec.exe (PID: 6364)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 4896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| Pages: | 200 |
| RevisionNumber: | {EBE261DB-A42F-49B4-82D5-9C81EC70227B} |
| Title: | 0patch |
| Subject: | - |
| Author: | Acros Security |
| Keywords: | - |
| Comments: | 0patch Agent |
| Words: | 2 |
| ModifyDate: | 2022:11:11 08:11:23 |
| LastPrinted: | 2022:11:11 08:11:23 |
Total processes
143
Monitored processes
76
Malicious processes
3
Suspicious processes
65
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | C:\WINDOWS\System32\svchost.exe -k LocalSystemNetworkRestricted -p -s WdiSystemHost | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | C:\WINDOWS\System32\svchost.exe -k LocalSystemNetworkRestricted -p -s StorSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s wlidsvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1340 | C:\WINDOWS\system32\svchost.exe -k LocalSystemNetworkRestricted -p -s PcaSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | sihost.exe | C:\Windows\System32\sihost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Shell Infrastructure Host Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\0PatchInstaller_22.11.11.10550.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | C:\WINDOWS\system32\svchost.exe -k UnistackSvcGroup | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1816 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1888 | C:\WINDOWS\System32\svchost.exe -k netsvcs -p -s NetSetupSvc | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s LanmanServer | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
50 771
Read events
49 884
Write events
767
Delete events
120
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000802CC |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000502F2 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (1340) svchost.exe | Key: | \REGISTRY\A\{16e72e64-c637-8373-8dae-ab0cd8ece97a}\Root\InventoryDevicePnp |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (1340) svchost.exe | Key: | \REGISTRY\A\{16e72e64-c637-8373-8dae-ab0cd8ece97a}\Root\InventoryDevicePnp\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1340) svchost.exe | Key: | \REGISTRY\A\{16e72e64-c637-8373-8dae-ab0cd8ece97a}\Root\InventoryDeviceContainer |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (1340) svchost.exe | Key: | \REGISTRY\A\{16e72e64-c637-8373-8dae-ab0cd8ece97a}\Root\InventoryDeviceContainer\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1340) svchost.exe | Key: | \REGISTRY\A\{16e72e64-c637-8373-8dae-ab0cd8ece97a}\Root\InventoryDriverBinary |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (1340) svchost.exe | Key: | \REGISTRY\A\{16e72e64-c637-8373-8dae-ab0cd8ece97a}\Root\InventoryDriverBinary\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1340) svchost.exe | Key: | \REGISTRY\A\{16e72e64-c637-8373-8dae-ab0cd8ece97a}\Root\InventoryDeviceMediaClass |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (1340) svchost.exe | Key: | \REGISTRY\A\{16e72e64-c637-8373-8dae-ab0cd8ece97a}\Root\InventoryDeviceMediaClass\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
24
Suspicious files
64
Text files
29
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6364 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\Internet Explorer\DOMStore\ZWUI0EBX\www.bing[1].xml | text | |
MD5:D9A849506C173A22152980859AF06260 | SHA256:BDAAD3549EF9679273270C19D4C0F3059100303BFACEE4F6BF4E173921064CCF | |||
| 4488 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 1176 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:043565B7C83BFD884EB1FDE2E7CCDCC5 | SHA256:80A1700DD6E600A6B8FA4A0F2A118778C903D2966690103D7E582407FB447126 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | der | |
MD5:D442044A53369945A1B439699B53E0F1 | SHA256:CD130CAE82ABF8D0F12305B1742F2BA2D227163A8DA79A3DE87E6F4FFC76F1B3 | |||
| 1752 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\357F04AD41BCF5FE18FCB69F60C6680F_A21E1CE1973D5BD726AB7CC8073919AA | binary | |
MD5:5578B44278C68116CE9181295461245E | SHA256:57F34542083A7CC4FDAC7C8534385C05EA28EDA302EBA385EB551C1CA001722B | |||
| 1752 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:FEC3A2B0EC605CC15FAF19CC50DD51E4 | SHA256:BF3A942E60D90CCF4856C72AF0CE04059C51D88A79DE218B489B73D243BD157E | |||
| 1176 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:055934ED65A3BC03940BB217377A4602 | SHA256:F45A5125ADBB62EC734253C795EA563B20238C5708EDD4D6911A5E98B0583890 | |||
| 4712 | MoUsoCoreWorker.exe | C:\ProgramData\USOPrivate\UpdateStore\store.db-journal | binary | |
MD5:474F22BAF113A66CBCA875827A09CD55 | SHA256:FE51339AF52FEC4CFDFDD86D34C7C70E533256A0446C9CAC3602C0ECE2829755 | |||
| 6364 | msiexec.exe | C:\Windows\Installer\MSIB3D2.tmp | binary | |
MD5:51F9C39DD4F6955910B047C220F1F25F | SHA256:F8B4C4B91883168461417D0666D2FEEC10D2EEFA6533AC8F0BA2DB3224F561F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
34
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.183:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1752 | msiexec.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
1752 | msiexec.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDAK8vM6%2B4NE6wqJS%2BQ%3D%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6628 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6300 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6628 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6072 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.183:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1752 | msiexec.exe | 151.101.2.133:80 | ocsp.globalsign.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |