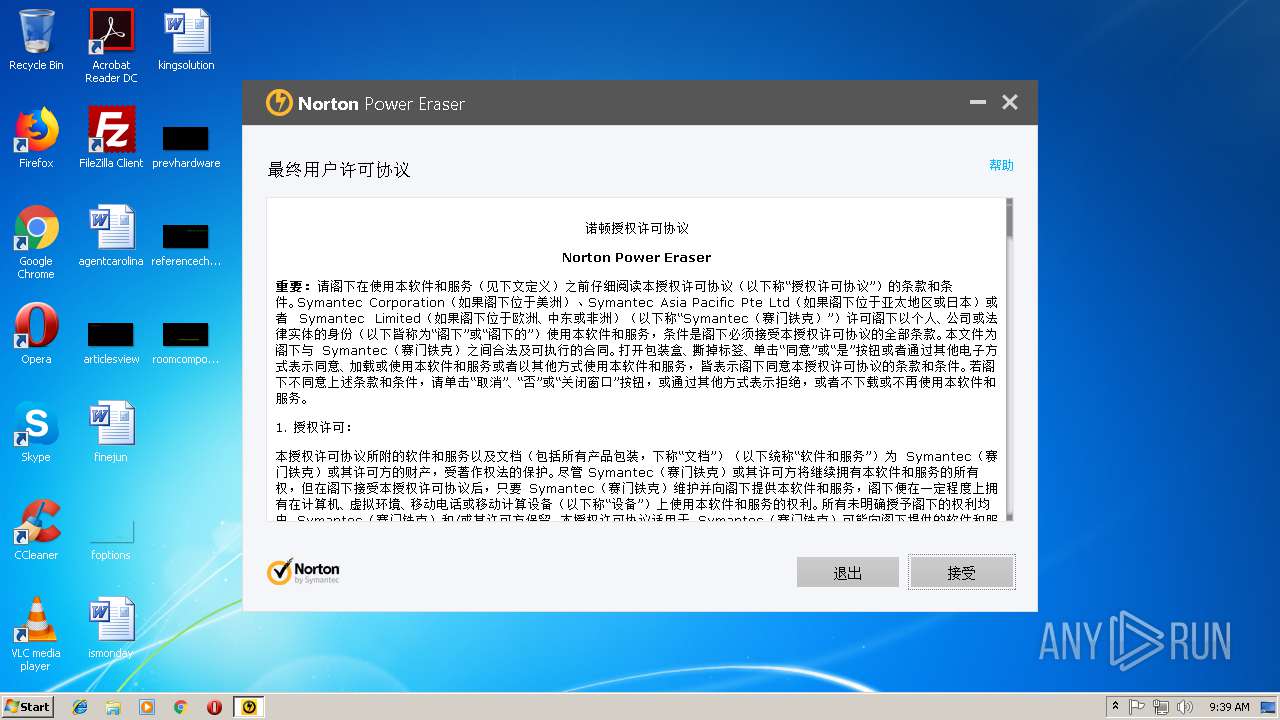
| File name: | Norton Power Eraser.exe |
| Full analysis: | https://app.any.run/tasks/b8bc4584-67e5-4819-b608-a2a53119ef33 |
| Verdict: | No threats detected |
| Analysis date: | September 24, 2018, 08:38:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C871DBA4C4DDF0A7D107D63D0C188D71 |
| SHA1: | 1F5873BC6B8D30E165C5841645AD672B4CADCD15 |
| SHA256: | 8568FEBB8F2E9D3CF0A9F6D99F368646153B5ABAF086415A61E77C882D6C0824 |
| SSDEEP: | 196608:LwM59nepxQxGotQ3JpcbwNsrqNnvyVIpEv90:9vbGotemtrqNnKV0q90 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- Norton Power Eraser.exe (PID: 2060)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:21 01:58:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 6126080 |
| InitializedDataSize: | 3404800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x40e42d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.3.0.24 |
| ProductVersionNumber: | 5.3.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Symantec Corporation |
| FileDescription: | Norton Power Eraser |
| FileVersion: | 5.3.0.24 |
| InternalName: | NPE |
| LegalCopyright: | Copyright (c) 1997-2018 Symantec Corporation |
| OriginalFileName: | NPE.exe |
| ProductName: | Norton Power Eraser |
| ProductVersion: | 5.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Apr-2018 23:58:00 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Symantec Corporation |
| FileDescription: | Norton Power Eraser |
| FileVersion: | 5.3.0.24 |
| InternalName: | NPE |
| LegalCopyright: | Copyright (c) 1997-2018 Symantec Corporation |
| OriginalFilename: | NPE.exe |
| ProductName: | Norton Power Eraser |
| ProductVersion: | 5.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000148 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 20-Apr-2018 23:58:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x005C8936 | 0x005C8A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.75249 |
IPPCODE | 0x005CA000 | 0x0000EF2B | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.28413 |
.rdata | 0x005D9000 | 0x00140D6C | 0x00140E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18424 |
.data | 0x0071A000 | 0x0003AD00 | 0x0002F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.24565 |
.gfids | 0x00755000 | 0x00000D98 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.95879 |
.tls | 0x00756000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00757000 | 0x0016BC78 | 0x0016BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.26457 |
.reloc | 0x008C3000 | 0x00061F90 | 0x00062000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65913 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.16991 | 2018 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.83854 | 19496 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.53695 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.68794 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.79893 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.90673 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.01681 | 2064 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 0.903812 | 36 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.46829 | 358 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.9382 | 514 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
ADVAPI32.dll (delay-loaded) |
COMCTL32.dll |
COMDLG32.dll |
CRYPT32.dll |
Cabinet.dll |
DNSAPI.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2060 | "C:\Users\admin\AppData\Local\Temp\Norton Power Eraser.exe" | C:\Users\admin\AppData\Local\Temp\Norton Power Eraser.exe | explorer.exe | ||||||||||||
User: admin Company: Symantec Corporation Integrity Level: HIGH Description: Norton Power Eraser Exit code: 0 Version: 5.3.0.24 Modules
| |||||||||||||||
| 3356 | "C:\Users\admin\AppData\Local\Temp\Norton Power Eraser.exe" | C:\Users\admin\AppData\Local\Temp\Norton Power Eraser.exe | — | explorer.exe | |||||||||||
User: admin Company: Symantec Corporation Integrity Level: MEDIUM Description: Norton Power Eraser Exit code: 3221226540 Version: 5.3.0.24 Modules
| |||||||||||||||
Total events
65
Read events
23
Write events
32
Delete events
10
Modification events
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\Norton Power Eraser.exe |
| Operation: | write | Name: | DumpType |
Value: 0 | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\Norton Power Eraser.exe |
| Operation: | write | Name: | DumpCount |
Value: 4 | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\Norton Power Eraser.exe |
| Operation: | write | Name: | DumpFlags |
Value: 0 | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\Norton Power Eraser.exe |
| Operation: | write | Name: | DumpFolder |
Value: C:\Users\admin\AppData\Local\NPE\LocalDumps | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\WMI\Autologger\NPETraceSession |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\WMI\Autologger\NPETraceSession |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\WMI\Autologger\NPETraceSession |
| Operation: | write | Name: | FileName |
Value: C:\Users\admin\AppData\Local\NPE\NPETraceSessionBoot.etl | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\WMI\Autologger\NPETraceSession |
| Operation: | write | Name: | Guid |
Value: {AABF8953-37E8-4872-A177-6DDFBCD83C01} | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\WMI\Autologger\NPETraceSession |
| Operation: | write | Name: | BufferSize |
Value: 64 | |||
| (PID) Process: | (2060) Norton Power Eraser.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\WMI\Autologger\NPETraceSession |
| Operation: | write | Name: | LogFileMode |
Value: 5 | |||
Executable files
0
Suspicious files
6
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2060 | Norton Power Eraser.exe | C:\Users\admin\AppData\Local\NPE\ErrMgmt\SQCLIENT.dat.log | — | |
MD5:— | SHA256:— | |||
| 2060 | Norton Power Eraser.exe | C:\ProgramData\Norton\{086A63F0-6B13-4F29-9695-134E7A01E963}\LC.INI | text | |
MD5:— | SHA256:— | |||
| 2060 | Norton Power Eraser.exe | C:\Users\admin\AppData\Local\NPE\ErrMgmt\SQCLIENT.dat | binary | |
MD5:— | SHA256:— | |||
| 2060 | Norton Power Eraser.exe | C:\Users\admin\AppData\Local\NPE\NPETraceSession.etl | etl | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2060 | Norton Power Eraser.exe | 52.234.215.129:443 | stats.norton.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stats.qalabs.symantec.com |
| unknown |
stats.norton.com |
| unknown |
Threats
Process | Message |
|---|---|
Norton Power Eraser.exe | unrecognized css selector at (res:smr_rules.css(899))
|