| File name: | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe |
| Full analysis: | https://app.any.run/tasks/e9725cad-f233-433b-a77d-7ed38deda19f |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2025, 10:41:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 2 sections |
| MD5: | 1598018E92980E7B5B66607A379CA918 |
| SHA1: | F3D71DE85BF2DD5D5EF05B59CA64B7D168ADBA20 |
| SHA256: | 85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 |
| SSDEEP: | 98304:jAzf0y62Iee/P8oJ0Uq8v7jeSGoYSrL4KcBfQx+60jLwMr97q9xbZT6FeQ0UHYlN:k+1JJ7F0QM60jrgZT6Fd0dFZuZGePDa1 |
MALICIOUS
Changes the autorun value in the registry
- 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe (PID: 3364)
- smss.exe (PID: 2216)
- winlogon.exe (PID: 2736)
- services.exe (PID: 6068)
- lsass.exe (PID: 5572)
- inetinfo.exe (PID: 5320)
Create files in the Startup directory
- smss.exe (PID: 2216)
BRONTOK has been detected (SURICATA)
- inetinfo.exe (PID: 5320)
SUSPICIOUS
The process creates files with name similar to system file names
- 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe (PID: 3364)
Starts itself from another location
- 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe (PID: 3364)
- smss.exe (PID: 2216)
Executable content was dropped or overwritten
- 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe (PID: 3364)
- smss.exe (PID: 2216)
Reads security settings of Internet Explorer
- inetinfo.exe (PID: 5320)
Drops a file with a rarely used extension (PIF)
- smss.exe (PID: 2216)
Checks Windows Trust Settings
- inetinfo.exe (PID: 5320)
INFO
Checks supported languages
- 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe (PID: 3364)
- smss.exe (PID: 2216)
- winlogon.exe (PID: 2736)
- services.exe (PID: 6068)
- lsass.exe (PID: 5572)
- inetinfo.exe (PID: 5320)
Failed to create an executable file in Windows directory
- 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe (PID: 3364)
- smss.exe (PID: 2216)
- winlogon.exe (PID: 2736)
- services.exe (PID: 6068)
- lsass.exe (PID: 5572)
- inetinfo.exe (PID: 5320)
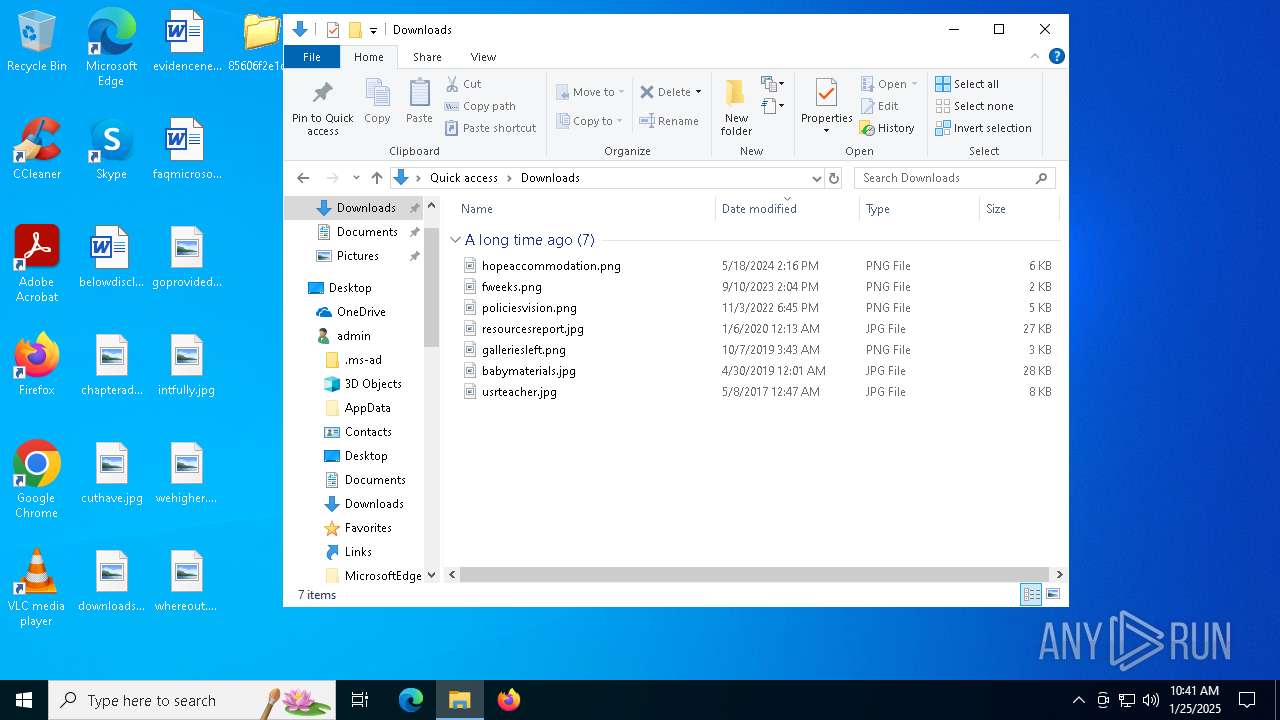
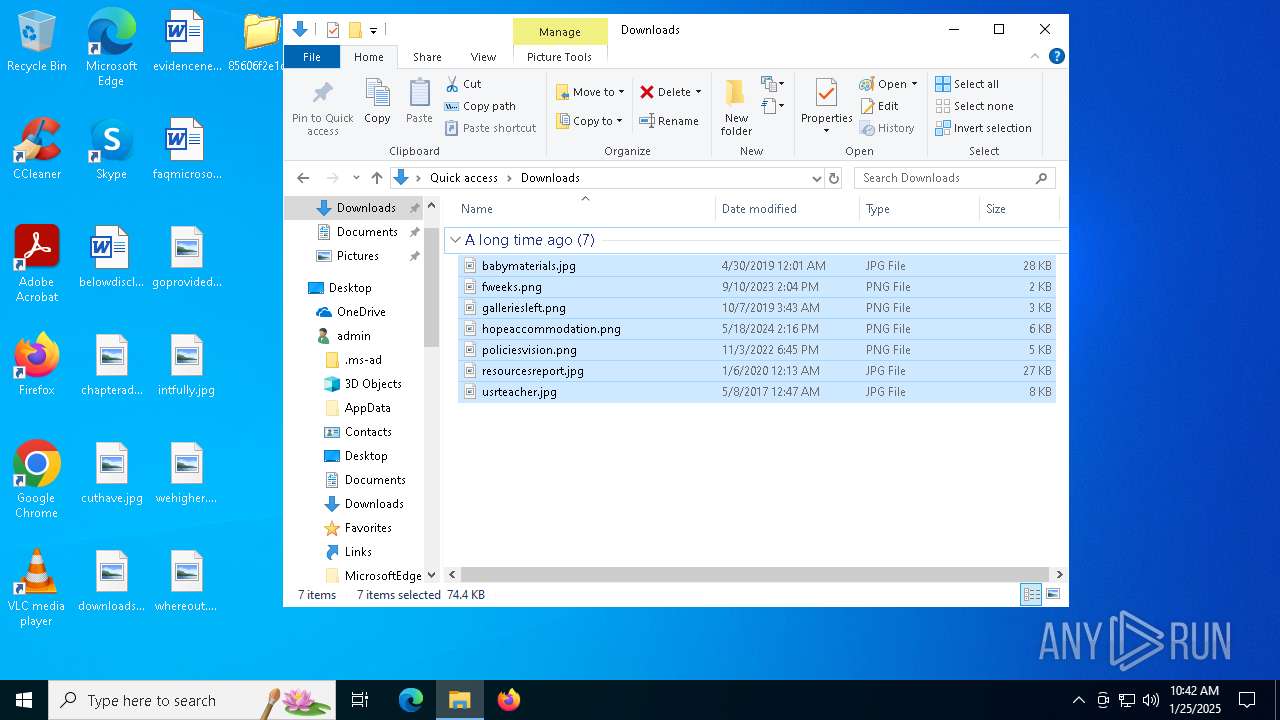
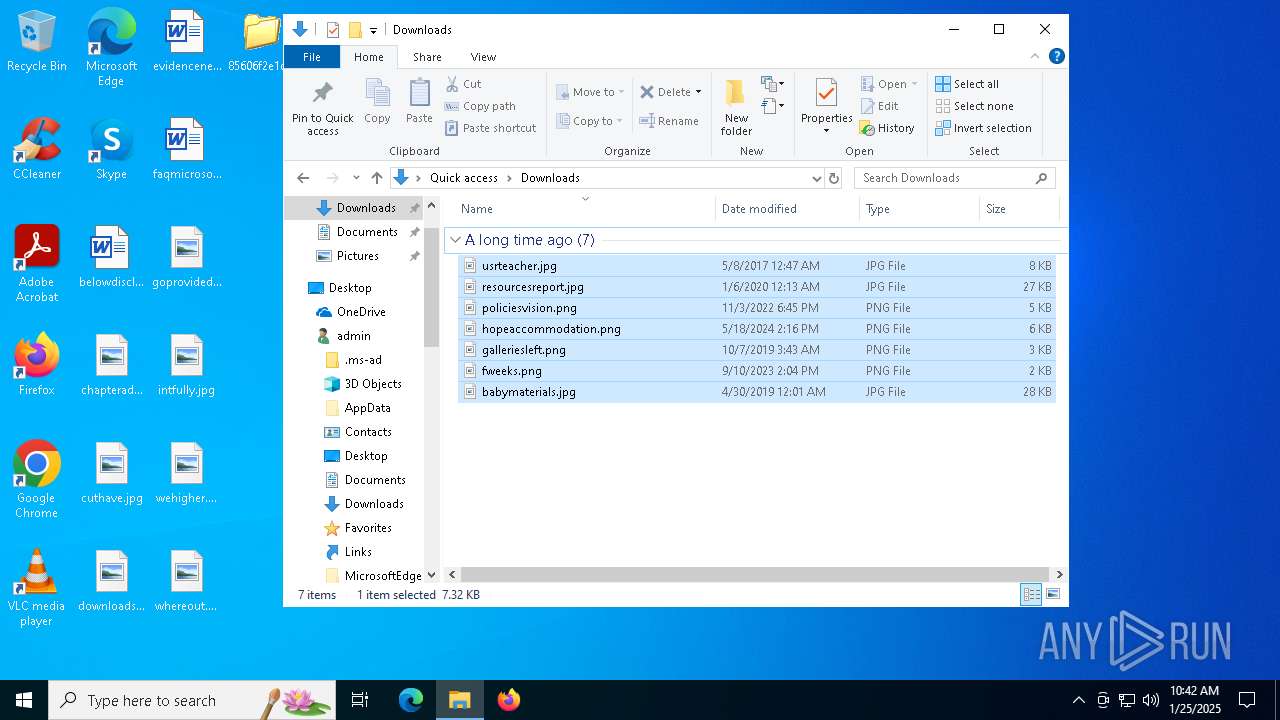
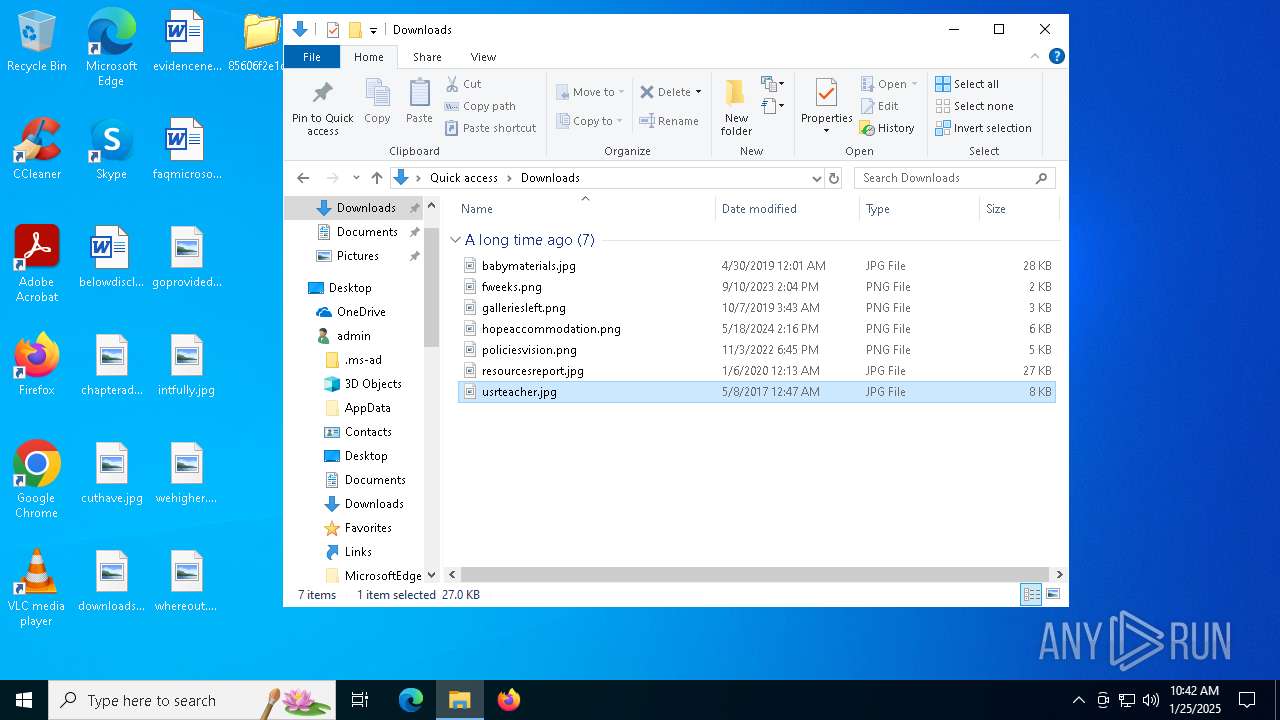
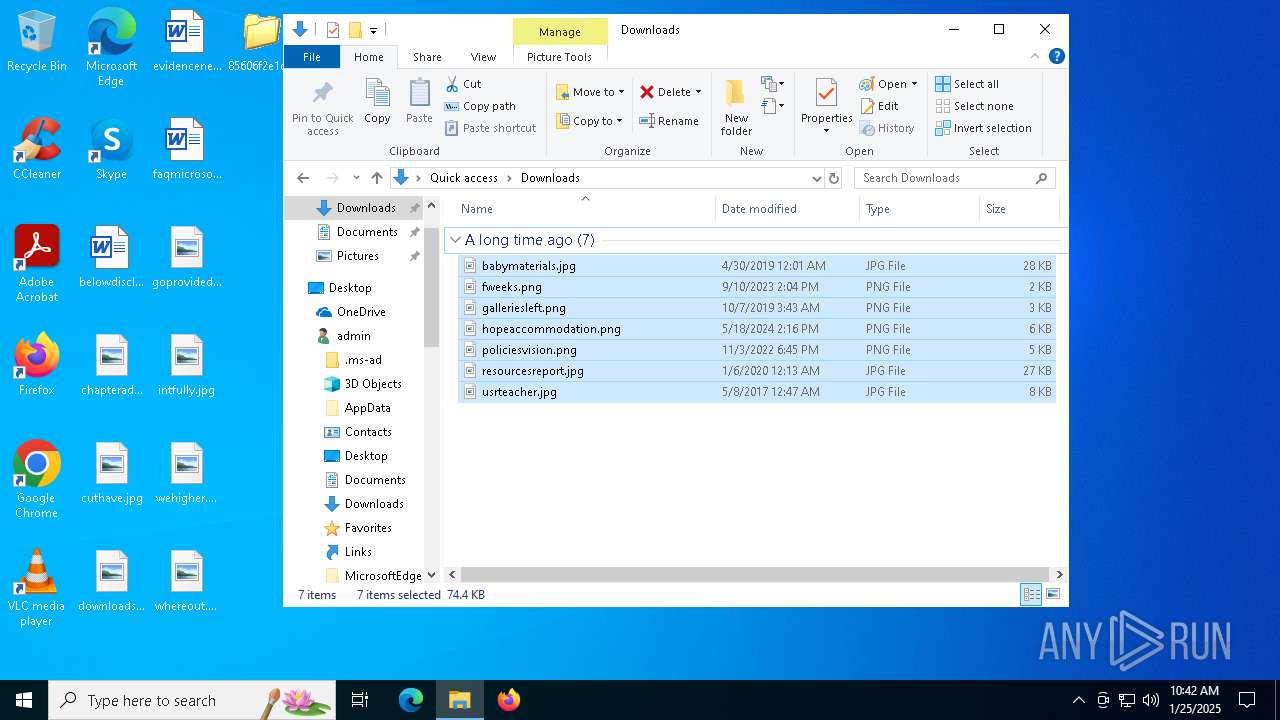
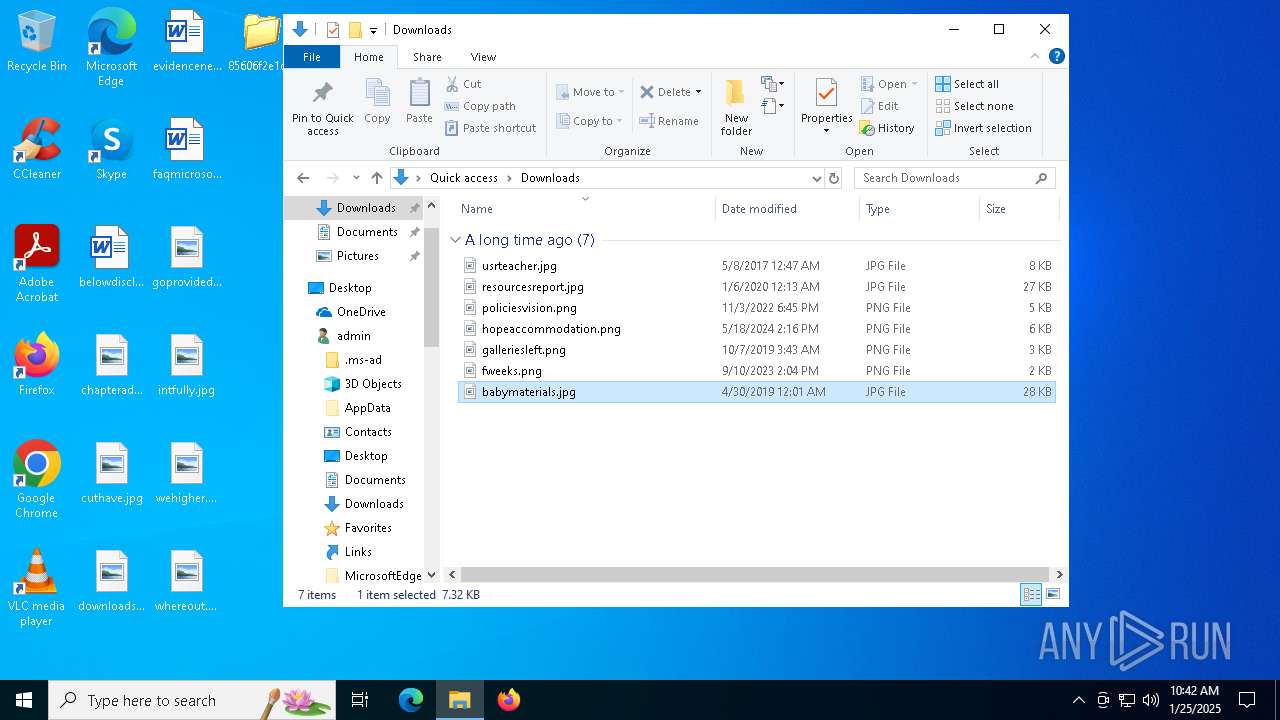
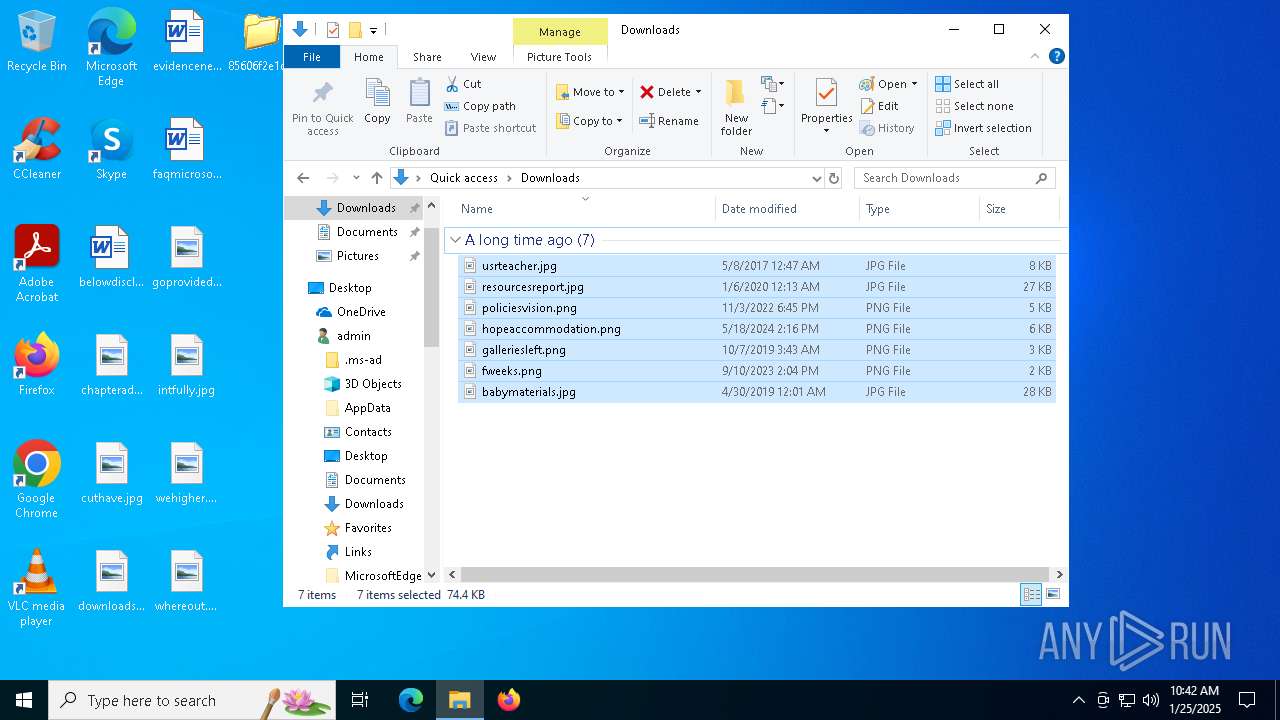
Creates files or folders in the user directory
- 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe (PID: 3364)
- smss.exe (PID: 2216)
- inetinfo.exe (PID: 5320)
Create files in a temporary directory
- 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe (PID: 3364)
- smss.exe (PID: 2216)
- winlogon.exe (PID: 2736)
- services.exe (PID: 6068)
- lsass.exe (PID: 5572)
- inetinfo.exe (PID: 5320)
Reads the computer name
- inetinfo.exe (PID: 5320)
Checks proxy server information
- inetinfo.exe (PID: 5320)
Reads the software policy settings
- inetinfo.exe (PID: 5320)
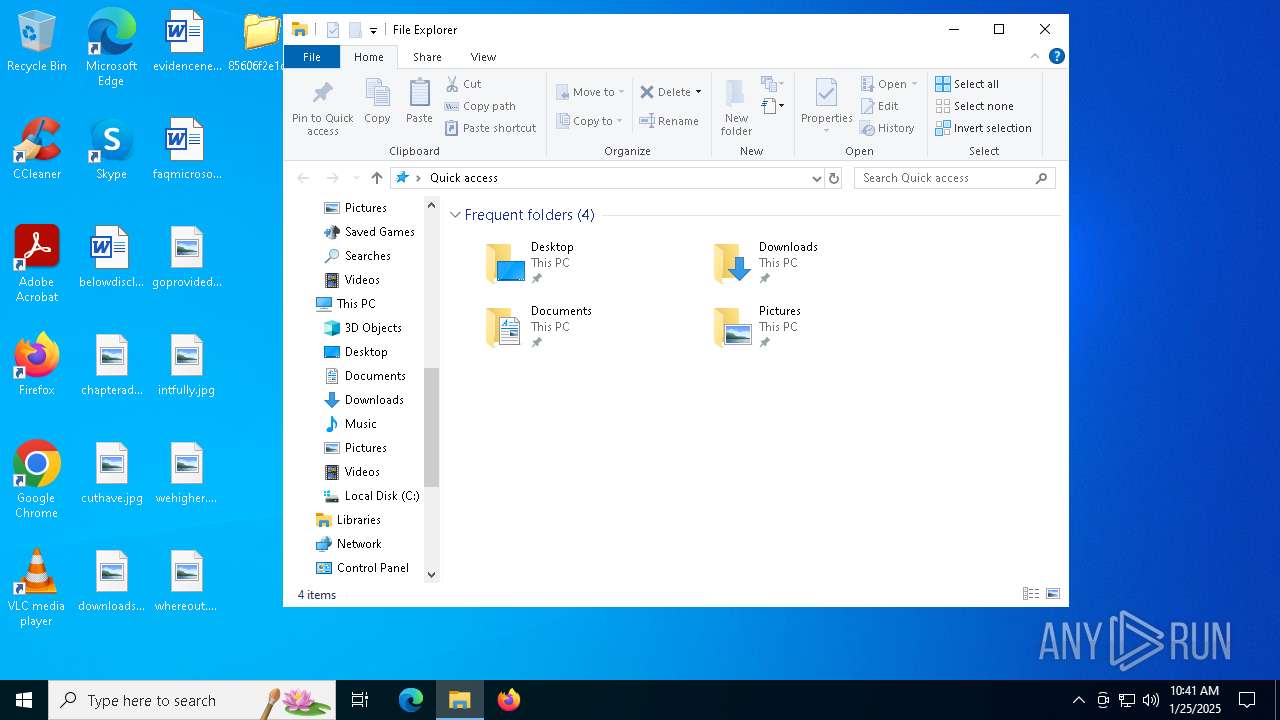
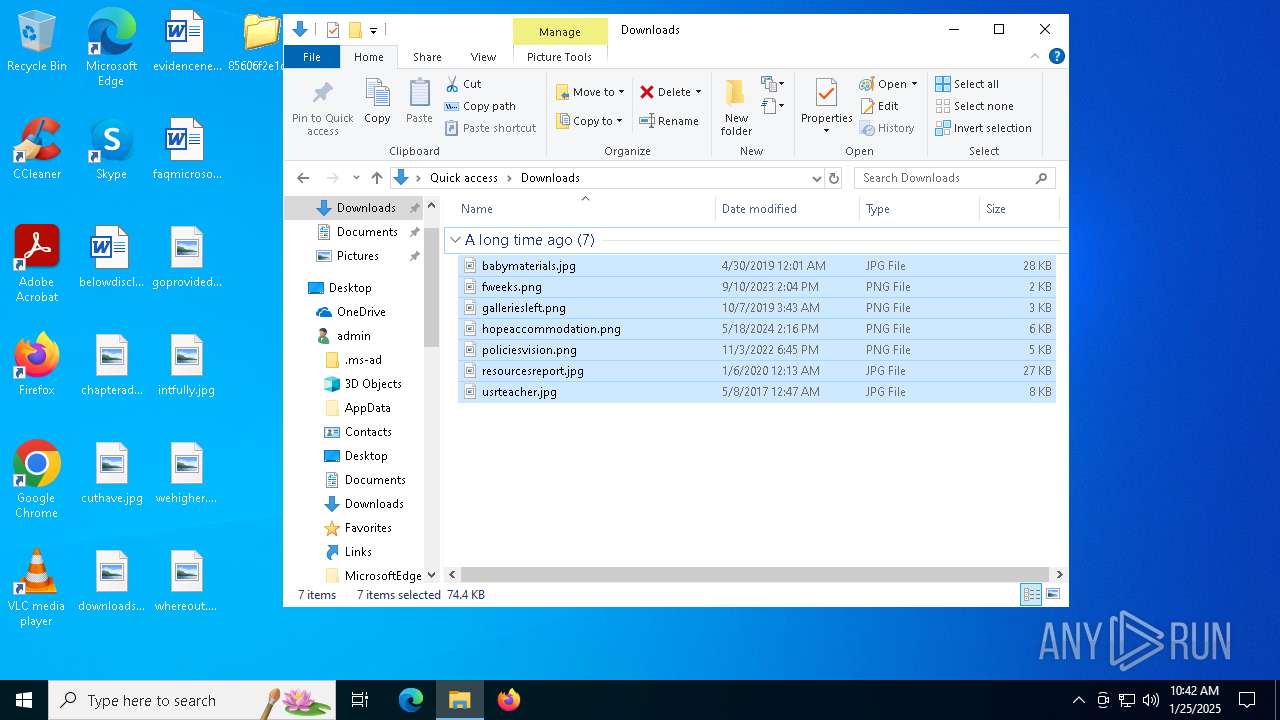
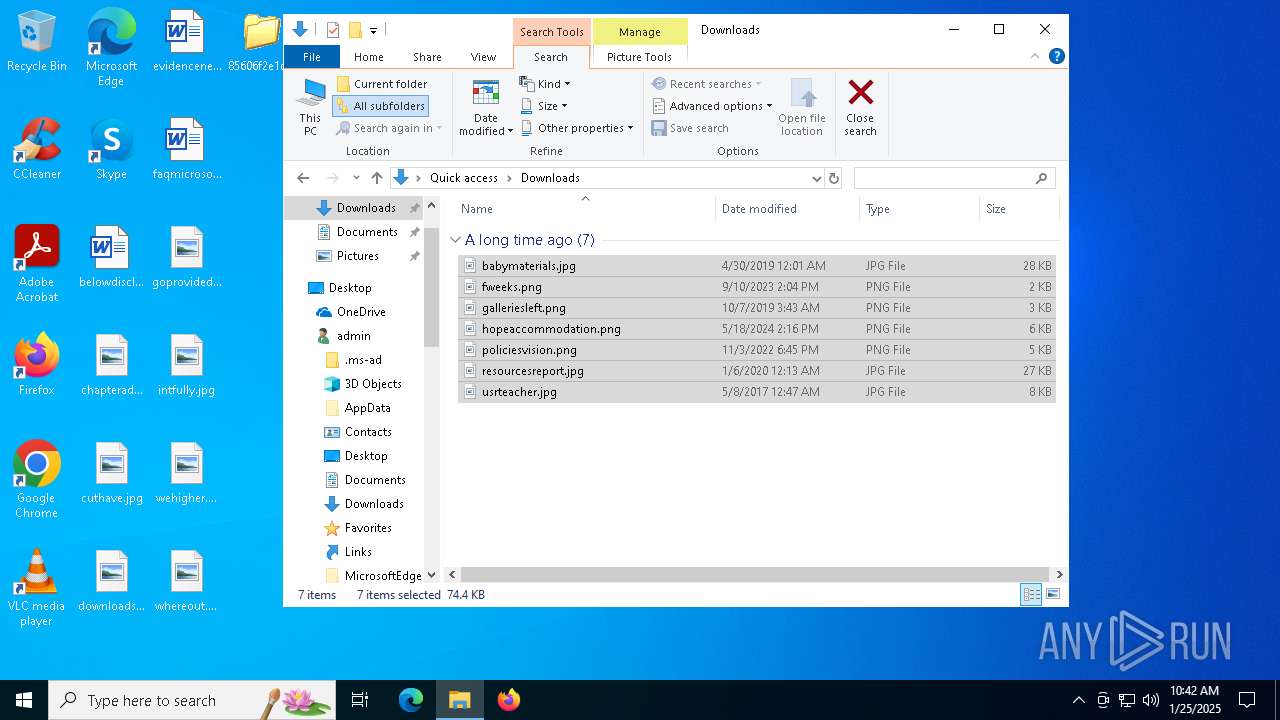
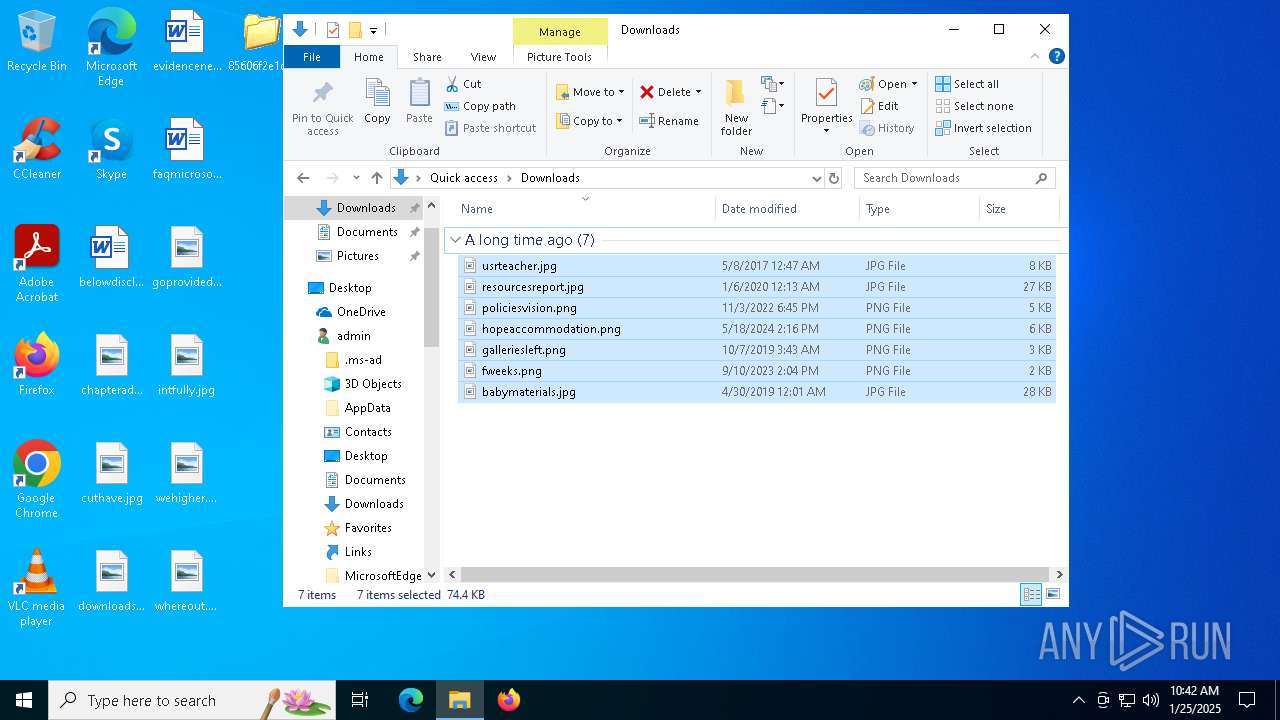
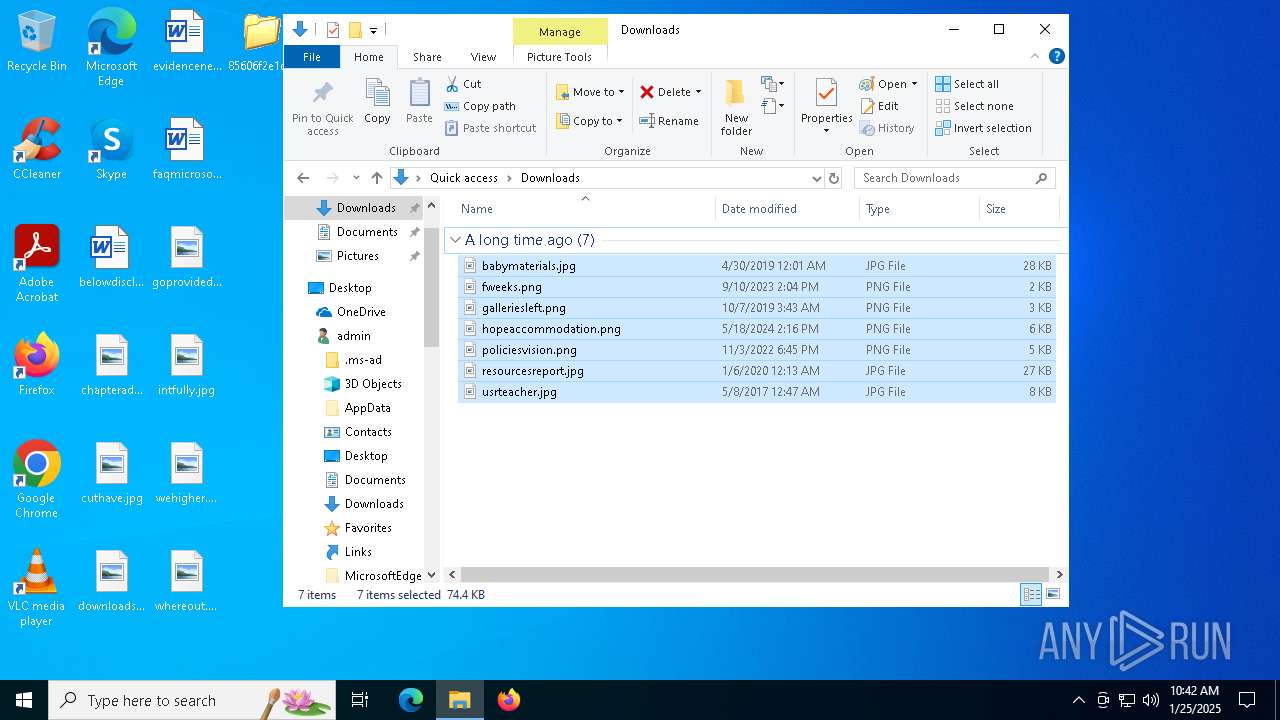
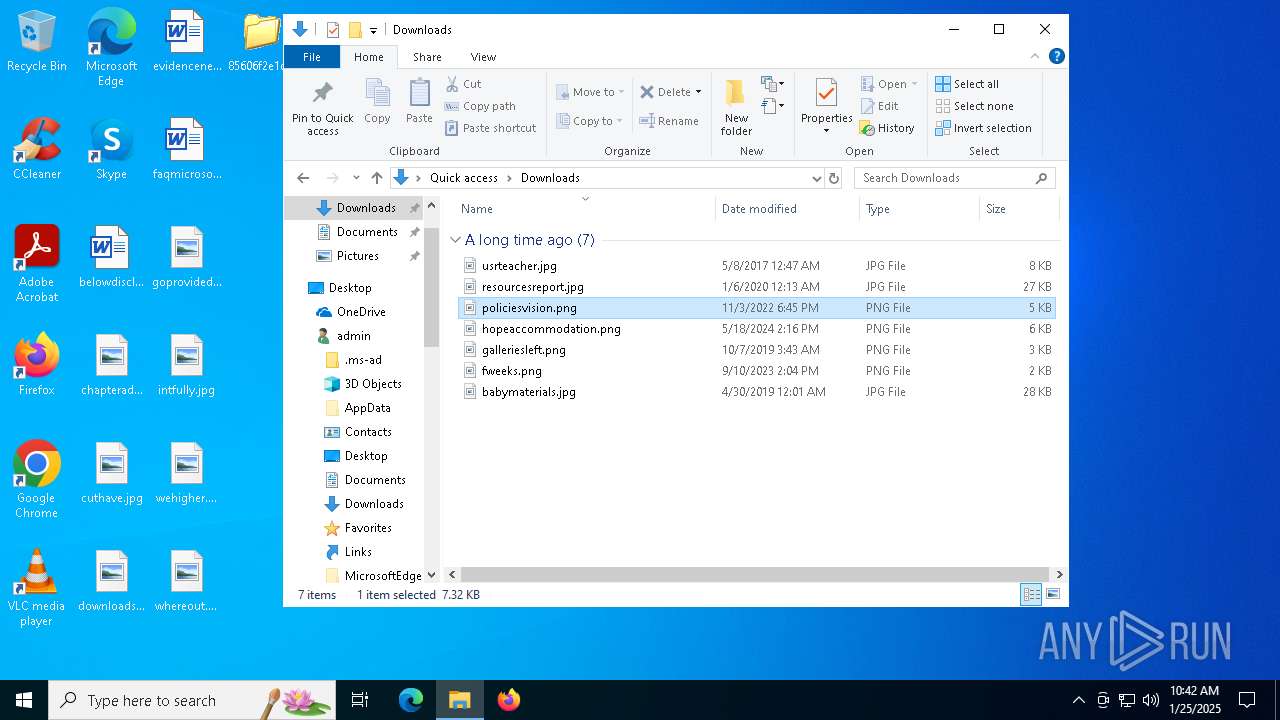
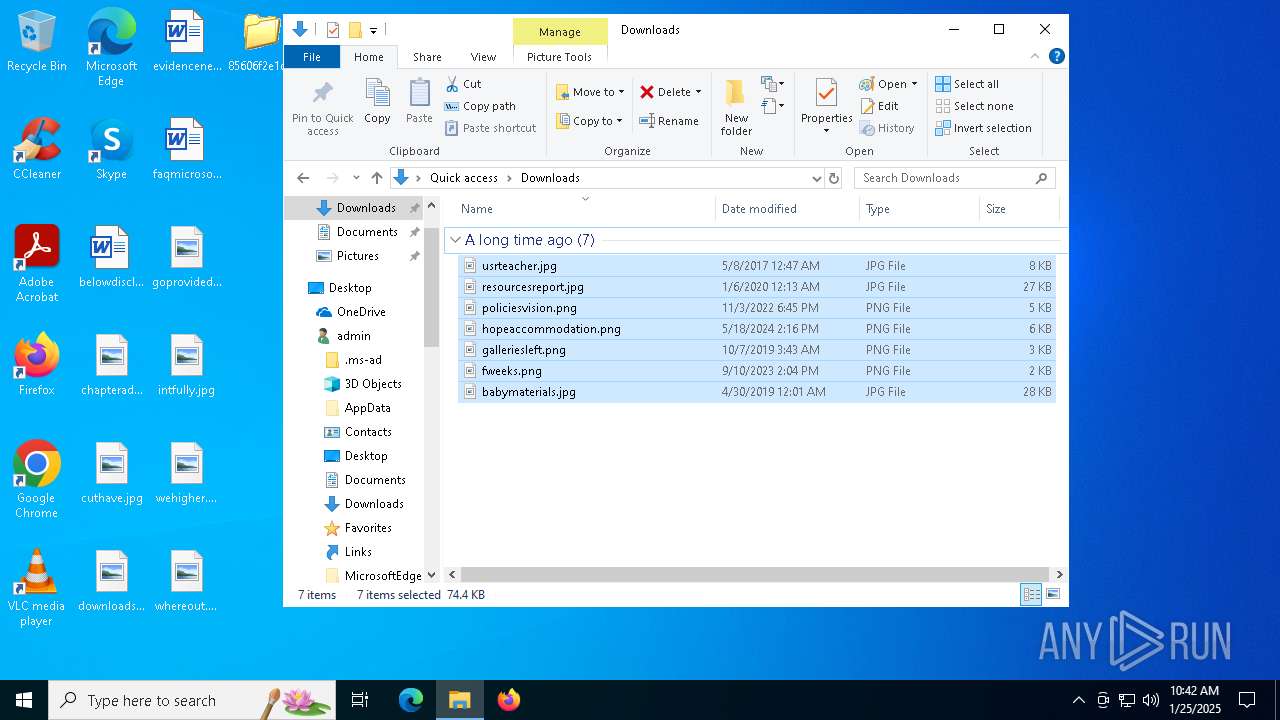
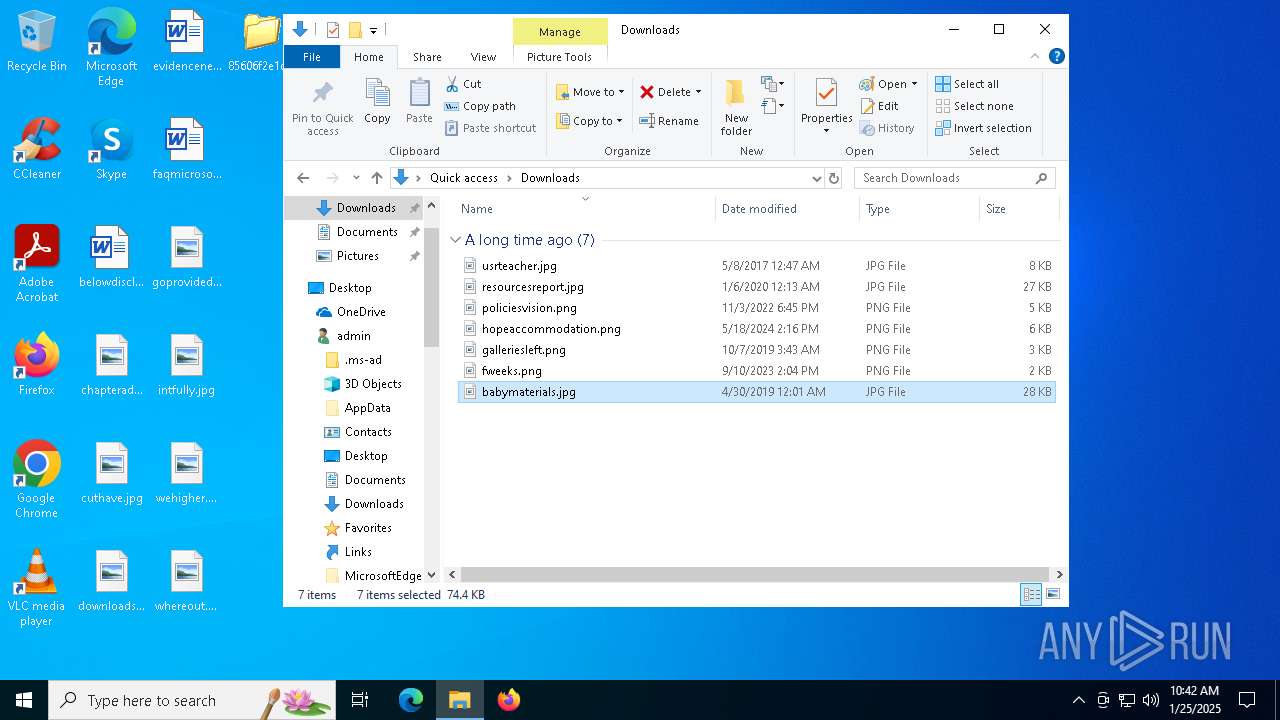
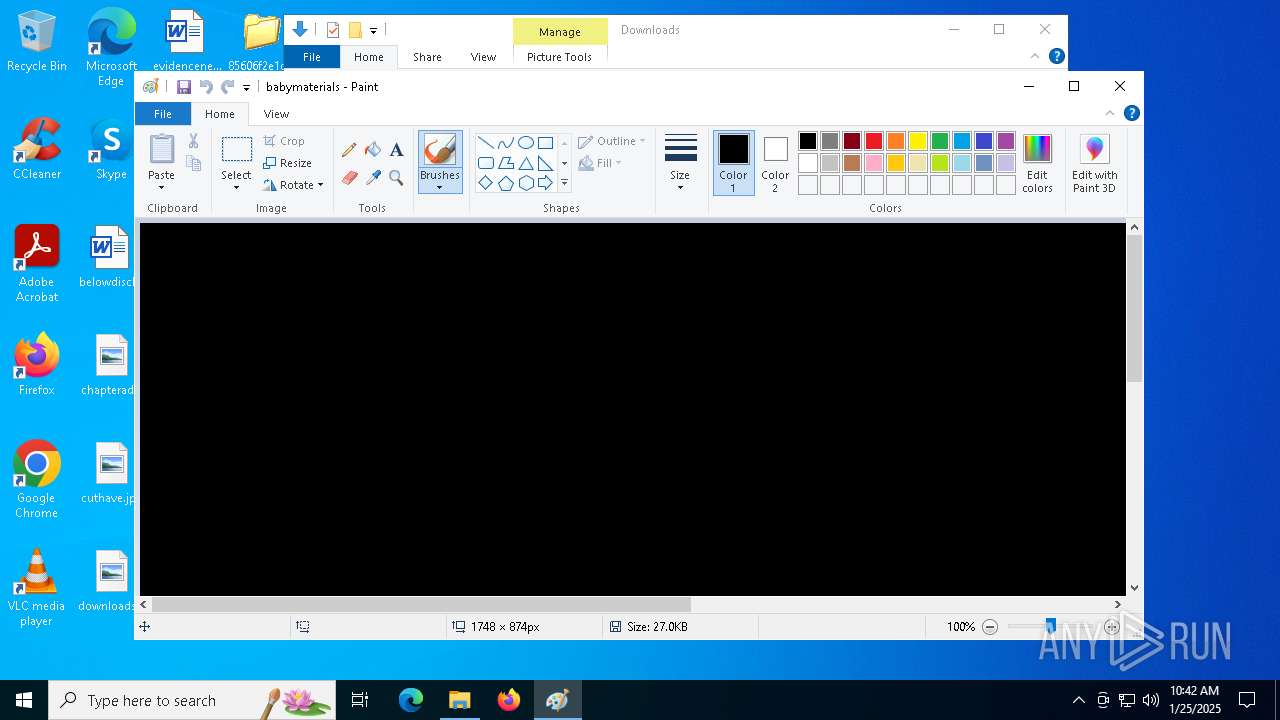
Manual execution by a user
- mspaint.exe (PID: 5256)
Reads the machine GUID from the registry
- inetinfo.exe (PID: 5320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Mew compressed Win32 Executable (88.8) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 512 |
| InitializedDataSize: | - |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2f47b |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
134
Monitored processes
14
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | C:\Users\admin\AppData\Local\smss.exe | C:\Users\admin\AppData\Local\smss.exe | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2736 | C:\Users\admin\AppData\Local\winlogon.exe | C:\Users\admin\AppData\Local\winlogon.exe | smss.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | at.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\Desktop\85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe" | C:\Users\admin\Desktop\85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3848 | at 17:08 /every:M,T,W,Th,F,S,Su "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Brengkolang.com" | C:\Windows\SysWOW64\at.exe | — | smss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Schedule service command line interface Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3984 | at /delete /y | C:\Windows\SysWOW64\at.exe | — | smss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Schedule service command line interface Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3988 | explorer.exe | C:\Windows\SysWOW64\explorer.exe | — | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4160 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | at.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 504
Read events
5 495
Write events
9
Delete events
0
Modification events
| (PID) Process: | (3364) 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tok-Cirrhatus |
Value: "C:\Users\admin\AppData\Local\smss.exe" | |||
| (PID) Process: | (2216) smss.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tok-Cirrhatus |
Value: "C:\Users\admin\AppData\Local\smss.exe" | |||
| (PID) Process: | (2736) winlogon.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tok-Cirrhatus |
Value: "C:\Users\admin\AppData\Local\smss.exe" | |||
| (PID) Process: | (6068) services.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tok-Cirrhatus |
Value: "C:\Users\admin\AppData\Local\smss.exe" | |||
| (PID) Process: | (5572) lsass.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tok-Cirrhatus |
Value: "C:\Users\admin\AppData\Local\smss.exe" | |||
| (PID) Process: | (5320) inetinfo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tok-Cirrhatus |
Value: "C:\Users\admin\AppData\Local\smss.exe" | |||
| (PID) Process: | (5320) inetinfo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5320) inetinfo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5320) inetinfo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
8
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | C:\Users\admin\AppData\Local\csrss.exe | executable | |
MD5:1598018E92980E7B5B66607A379CA918 | SHA256:85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 | |||
| 3364 | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | C:\Users\admin\AppData\Local\smss.exe | executable | |
MD5:1598018E92980E7B5B66607A379CA918 | SHA256:85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 | |||
| 3364 | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | C:\Users\admin\AppData\Local\inetinfo.exe | executable | |
MD5:1598018E92980E7B5B66607A379CA918 | SHA256:85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 | |||
| 2216 | smss.exe | C:\Users\admin\AppData\Local\winlogon.exe | executable | |
MD5:1598018E92980E7B5B66607A379CA918 | SHA256:85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 | |||
| 2216 | smss.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Brengkolang.com | executable | |
MD5:1598018E92980E7B5B66607A379CA918 | SHA256:85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 | |||
| 2216 | smss.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Empty.pif | executable | |
MD5:1598018E92980E7B5B66607A379CA918 | SHA256:85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 | |||
| 3364 | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | C:\Users\admin\AppData\Local\lsass.exe | executable | |
MD5:1598018E92980E7B5B66607A379CA918 | SHA256:85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 | |||
| 3364 | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | C:\Users\admin\AppData\Local\services.exe | executable | |
MD5:1598018E92980E7B5B66607A379CA918 | SHA256:85606F2E1D2C281310193BC7FA1395FDC09A6035DE5AC4862DA4E58F0619A975 | |||
| 2216 | smss.exe | C:\Users\admin\AppData\Local\Temp\~DFC542258C3F40A402.TMP | binary | |
MD5:21AD241025D25AB23409AF09F08AE339 | SHA256:9A5863E376429AFAFE8D06DAC4089C337EA263BDEE7395E2B7DEAF52A52F31CD | |||
| 3364 | 85606f2e1d2c281310193bc7fa1395fdc09a6035de5ac4862da4e58f0619a975.exe | C:\Users\admin\AppData\Local\Temp\~DF27C3C24D70C01D74.TMP | binary | |
MD5:21AD241025D25AB23409AF09F08AE339 | SHA256:9A5863E376429AFAFE8D06DAC4089C337EA263BDEE7395E2B7DEAF52A52F31CD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1480 | RUXIMICS.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1480 | RUXIMICS.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5320 | inetinfo.exe | GET | 301 | 76.223.84.192:80 | http://www.geocities.com/sblsji1/IN12SDSDWVLML.txt | unknown | — | — | whitelisted |
— | — | GET | 200 | 87.248.119.251:443 | https://www.yahoo.com/ | unknown | text | 4 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5892 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1480 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.204.157:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1480 | RUXIMICS.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1480 | RUXIMICS.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.geocities.com |
| whitelisted |
www.yahoo.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5320 | inetinfo.exe | A Network Trojan was detected | ET MALWARE Brontok User-Agent Detected (Brontok.A3 Browser) |