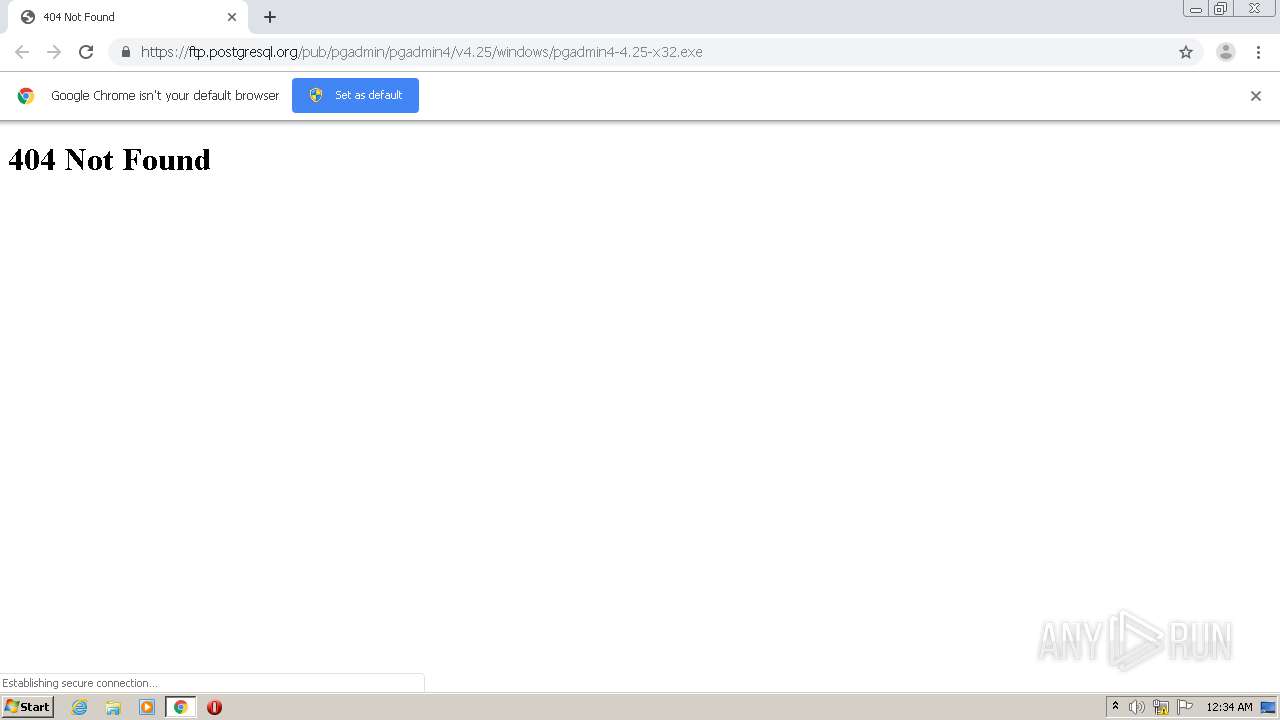
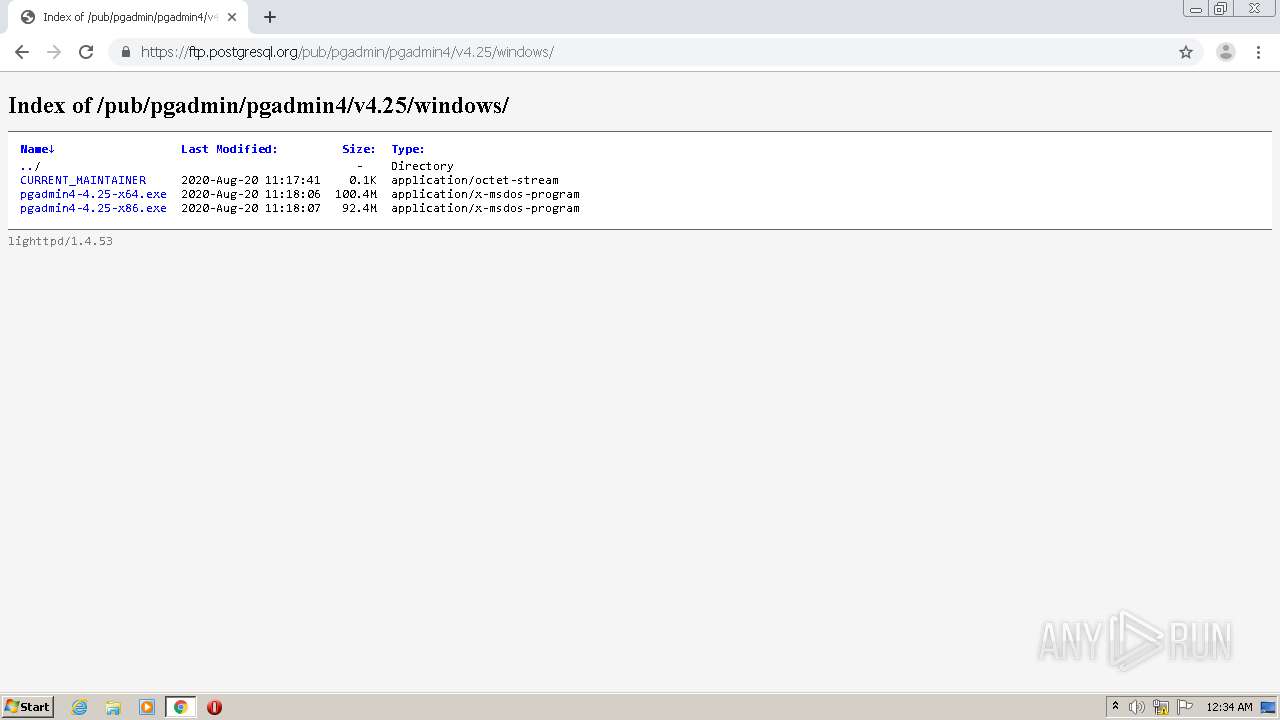
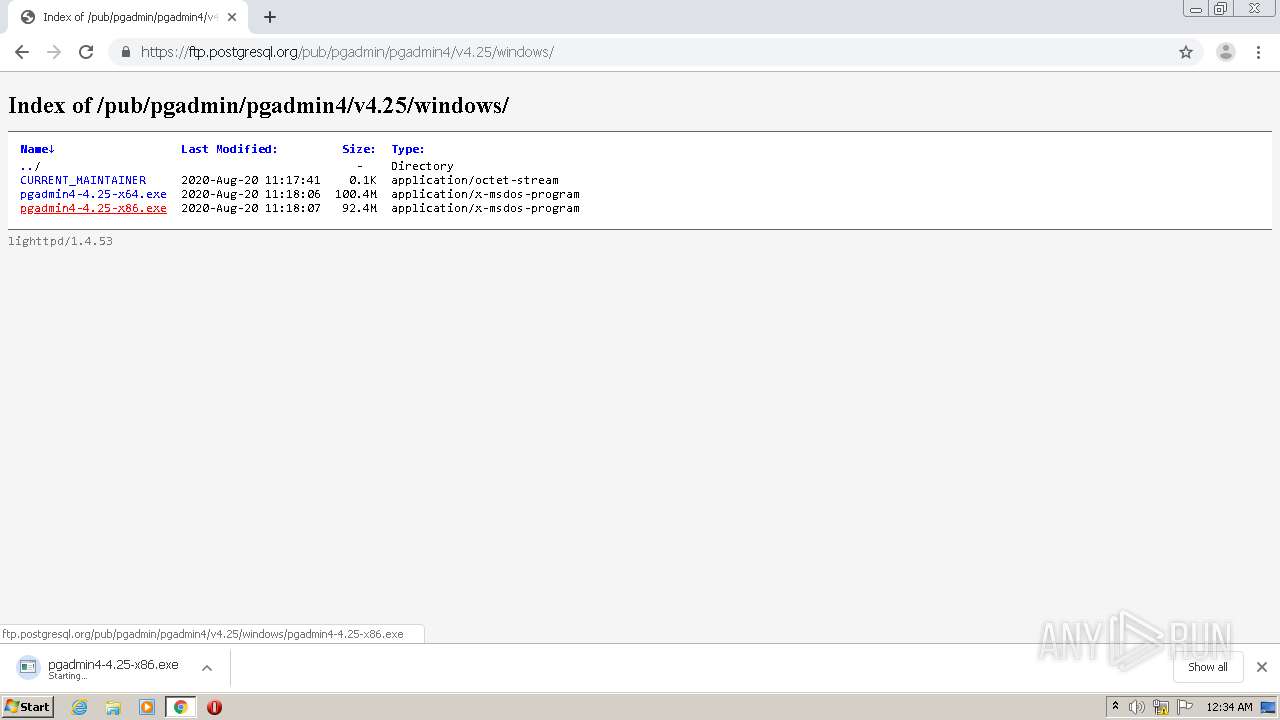
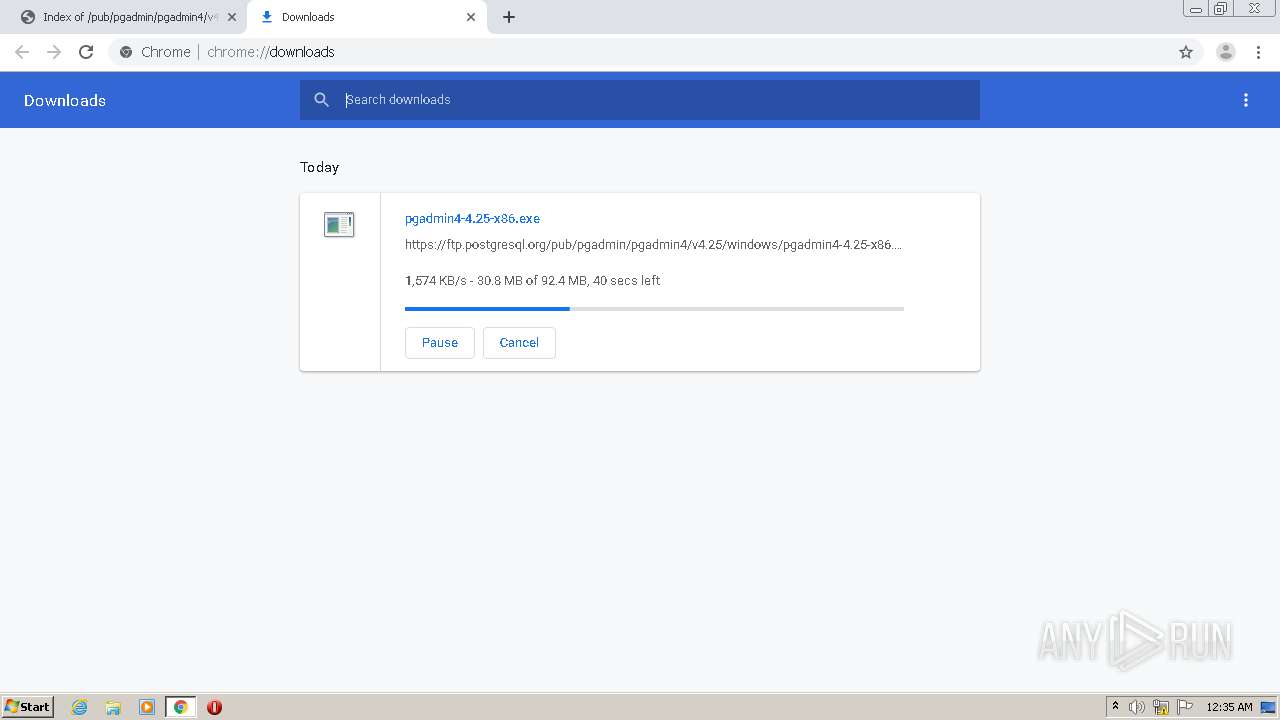
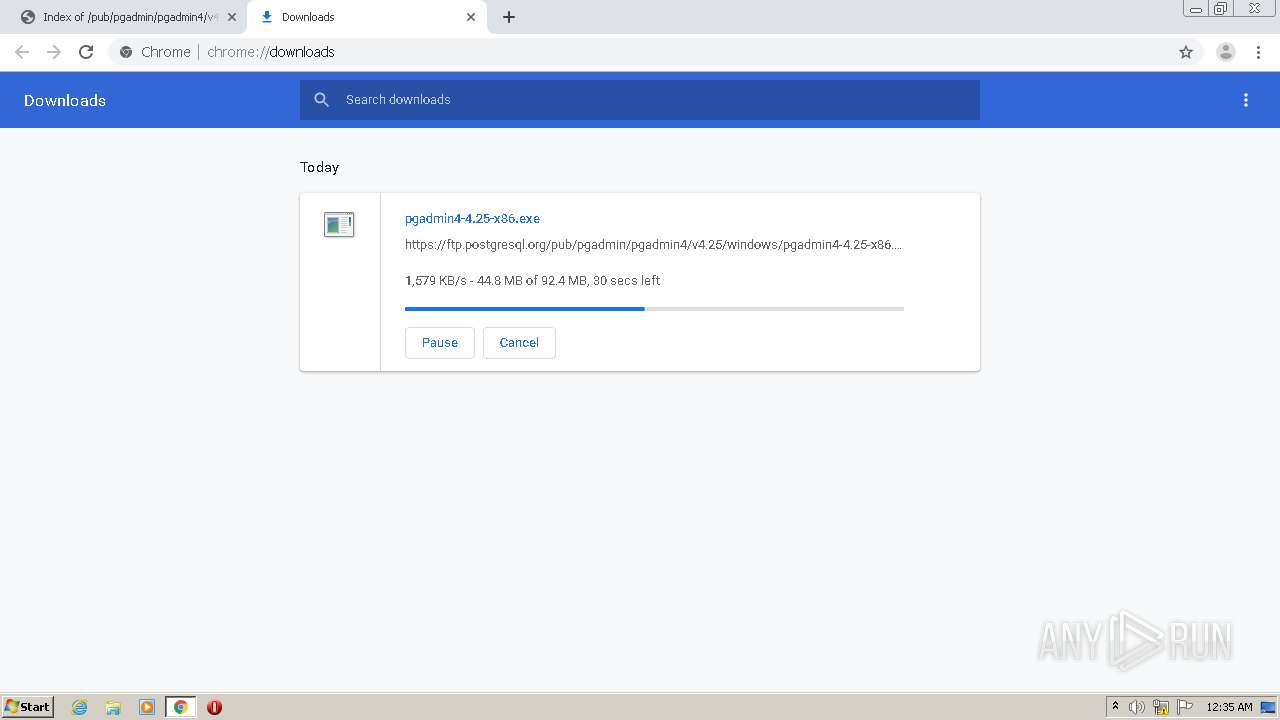
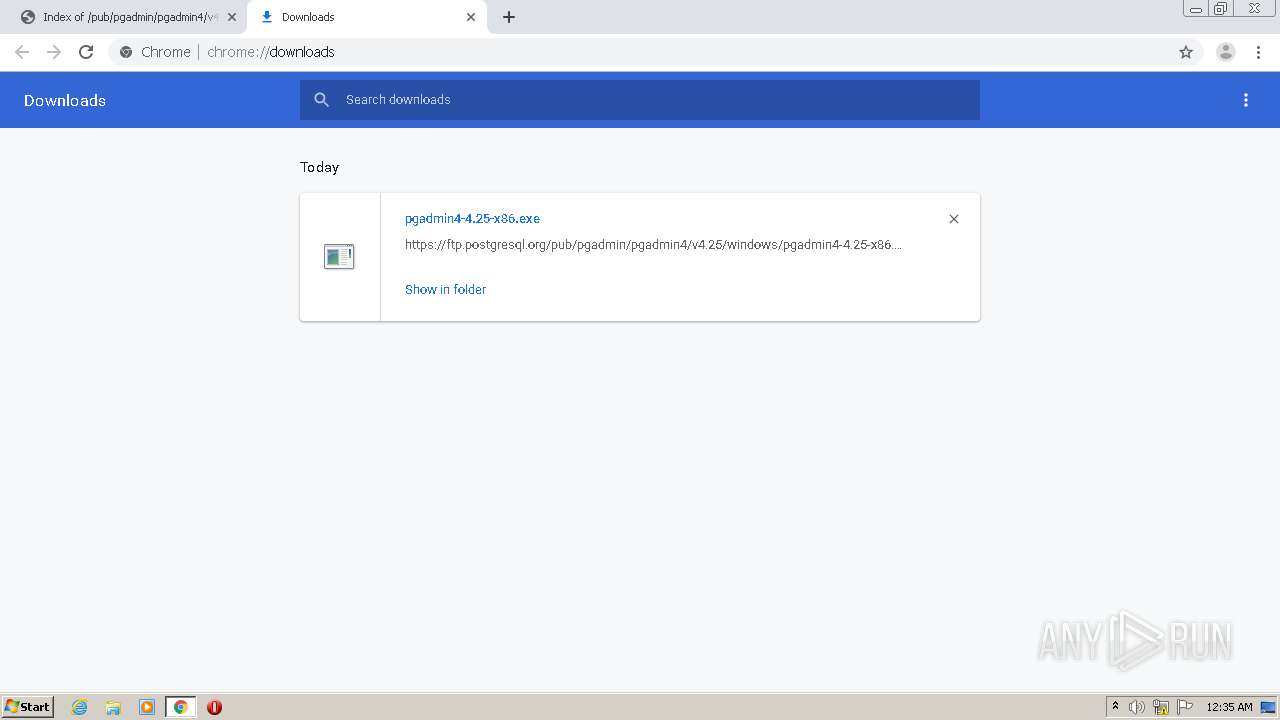
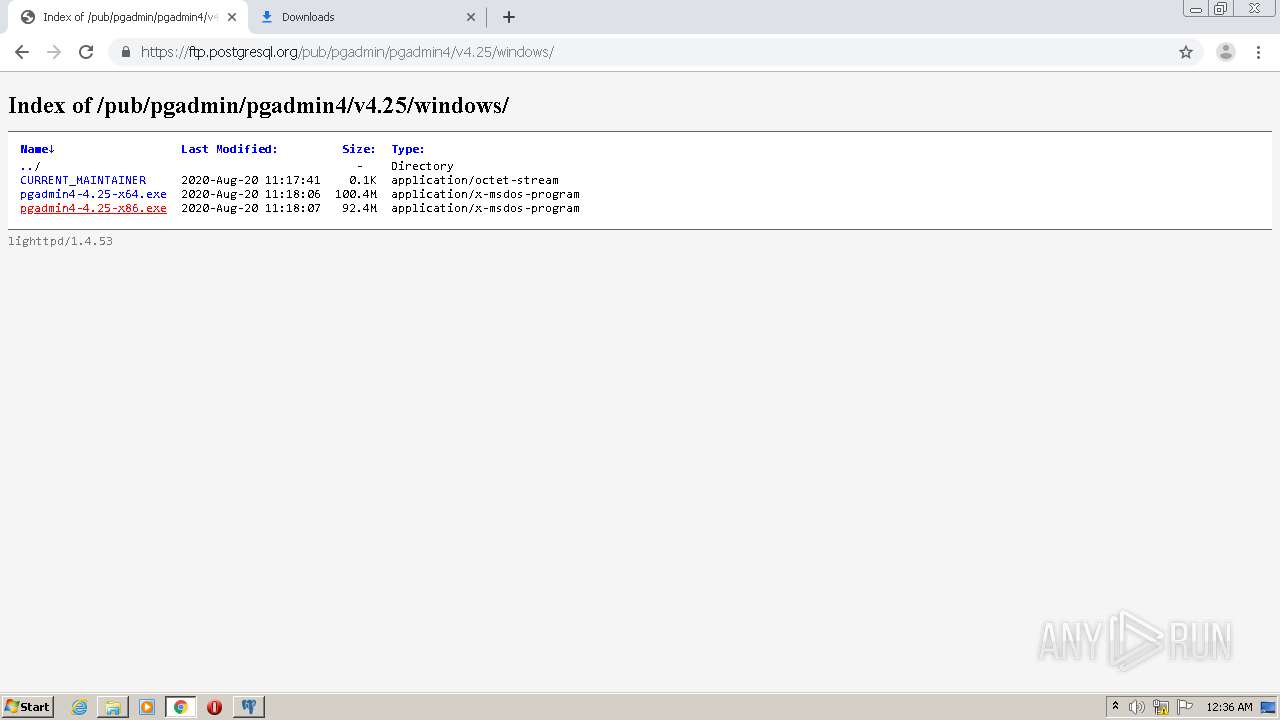
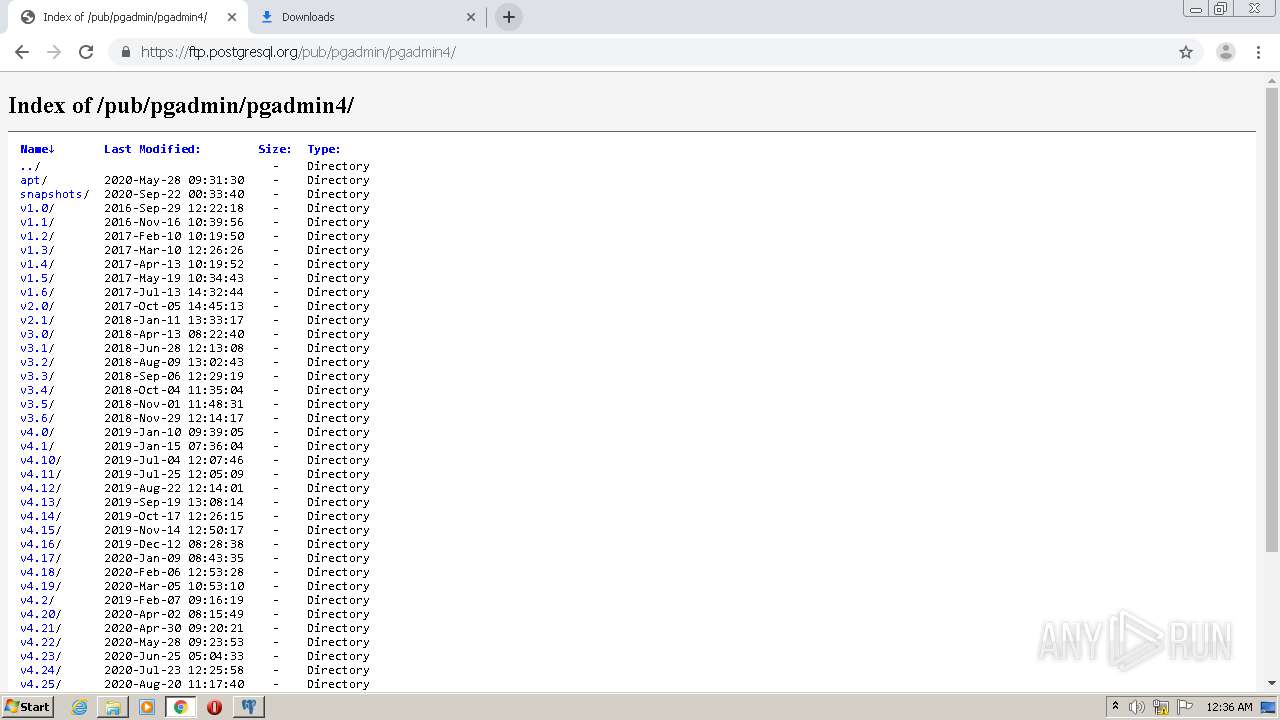
| URL: | https://ftp.postgresql.org/pub/pgadmin/pgadmin4/v4.25/windows/pgadmin4-4.25-x32.exe |
| Full analysis: | https://app.any.run/tasks/2a0ed992-0007-4f6f-b602-a983505f8896 |
| Verdict: | Malicious activity |
| Analysis date: | September 22, 2020, 23:34:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0F79A124F445896B9D04DEFC90516A2F |
| SHA1: | 85DBF9D784CB4019D8A6E869D9A50D16BB908891 |
| SHA256: | 855E6E2E4BF3AD25DD99BD3082E5C2AF00FAA8F3F4CD1CEA653827FC7B1D76F0 |
| SSDEEP: | 3:N8pLdCXAWVSKroEBx5oxcXn1KACmKQIOLNn:2pLde50oxKxcXAnmKQIkN |
MALICIOUS
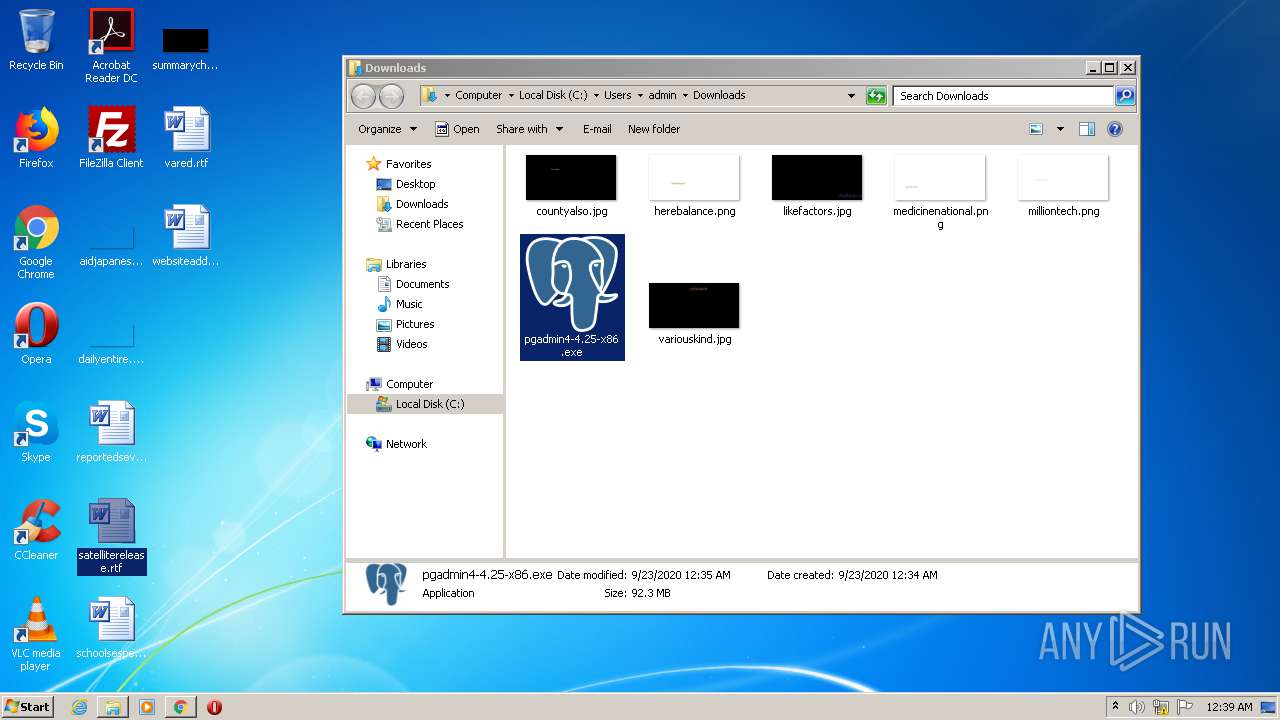
Application was dropped or rewritten from another process
- pgadmin4-4.25-x86.exe (PID: 1896)
- pgadmin4-4.25-x86.exe (PID: 2332)
- vcredist_x86.exe (PID: 2208)
- vcredist_x86.exe (PID: 1148)
- pgAdmin4.exe (PID: 1872)
- pgAdmin4.exe (PID: 2796)
Loads dropped or rewritten executable
- pgAdmin4.exe (PID: 1872)
- vcredist_x86.exe (PID: 1148)
- pgAdmin4.exe (PID: 2796)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2824)
- pgadmin4-4.25-x86.exe (PID: 1896)
- pgadmin4-4.25-x86.exe (PID: 2332)
- vcredist_x86.exe (PID: 1148)
- pgadmin4-4.25-x86.tmp (PID: 2340)
Reads the Windows organization settings
- pgadmin4-4.25-x86.tmp (PID: 2340)
Reads Windows owner or organization settings
- pgadmin4-4.25-x86.tmp (PID: 2340)
Application launched itself
- vcredist_x86.exe (PID: 2208)
Loads Python modules
- pgAdmin4.exe (PID: 1872)
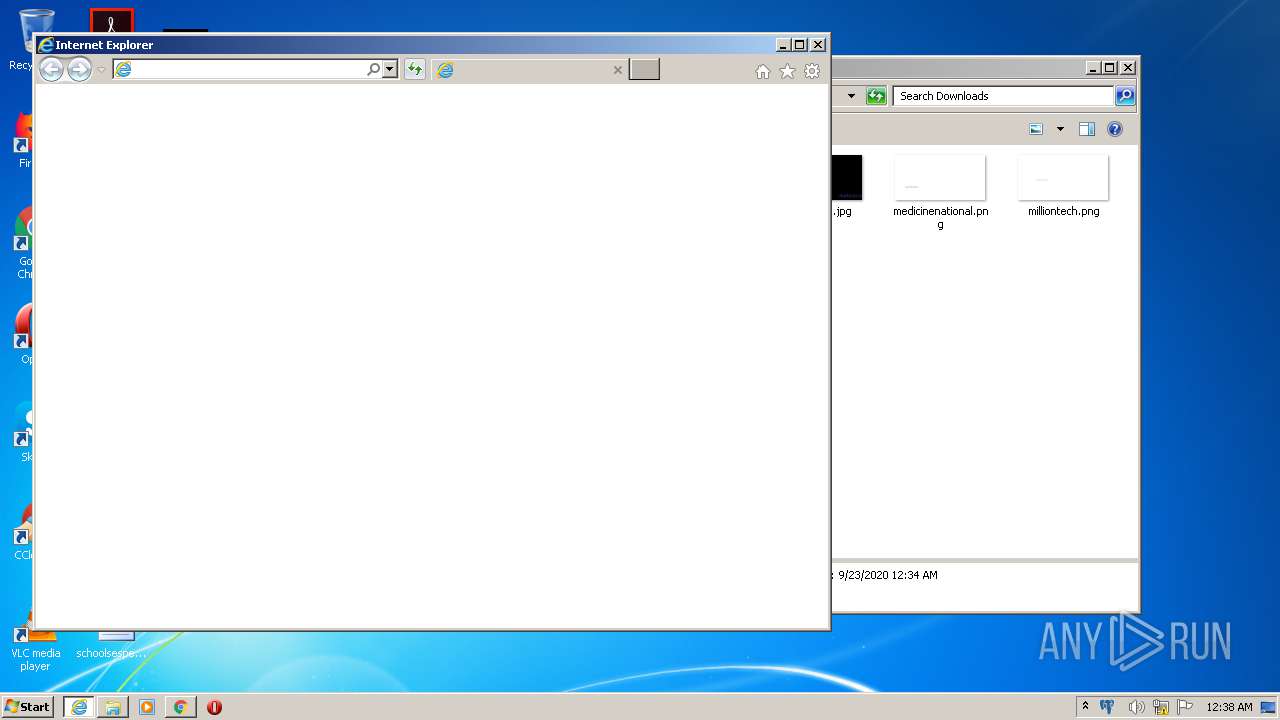
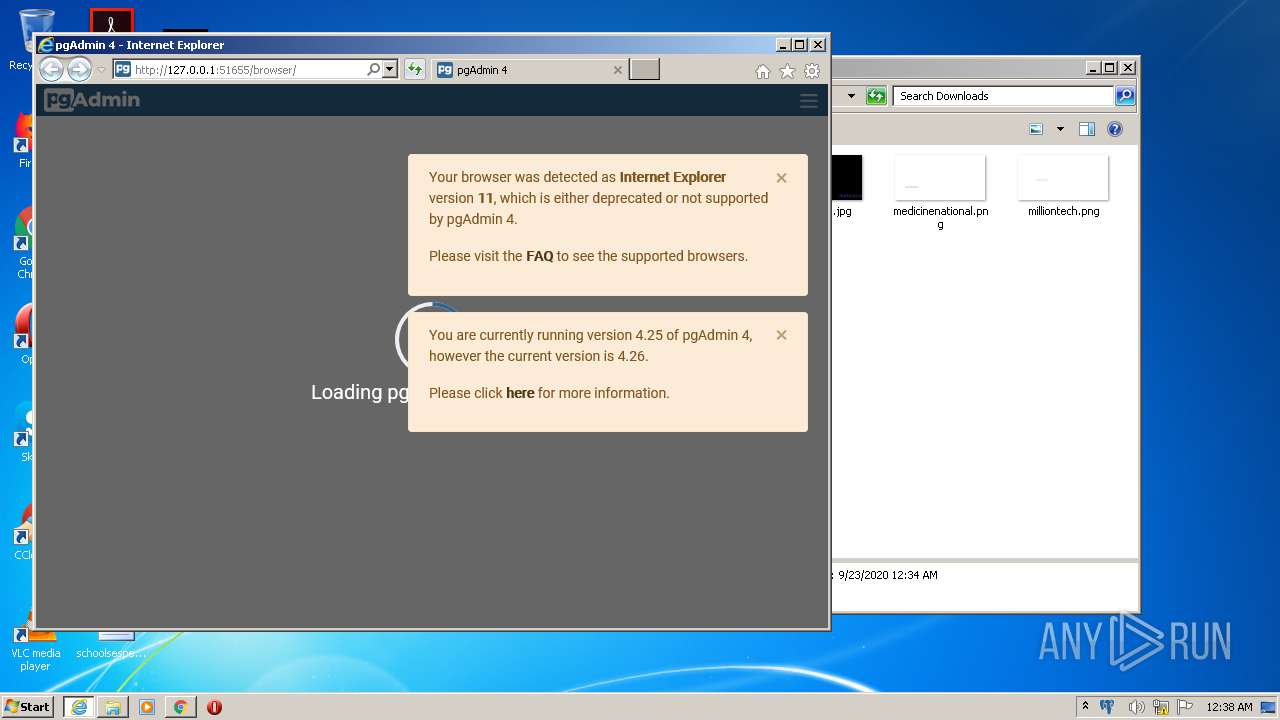
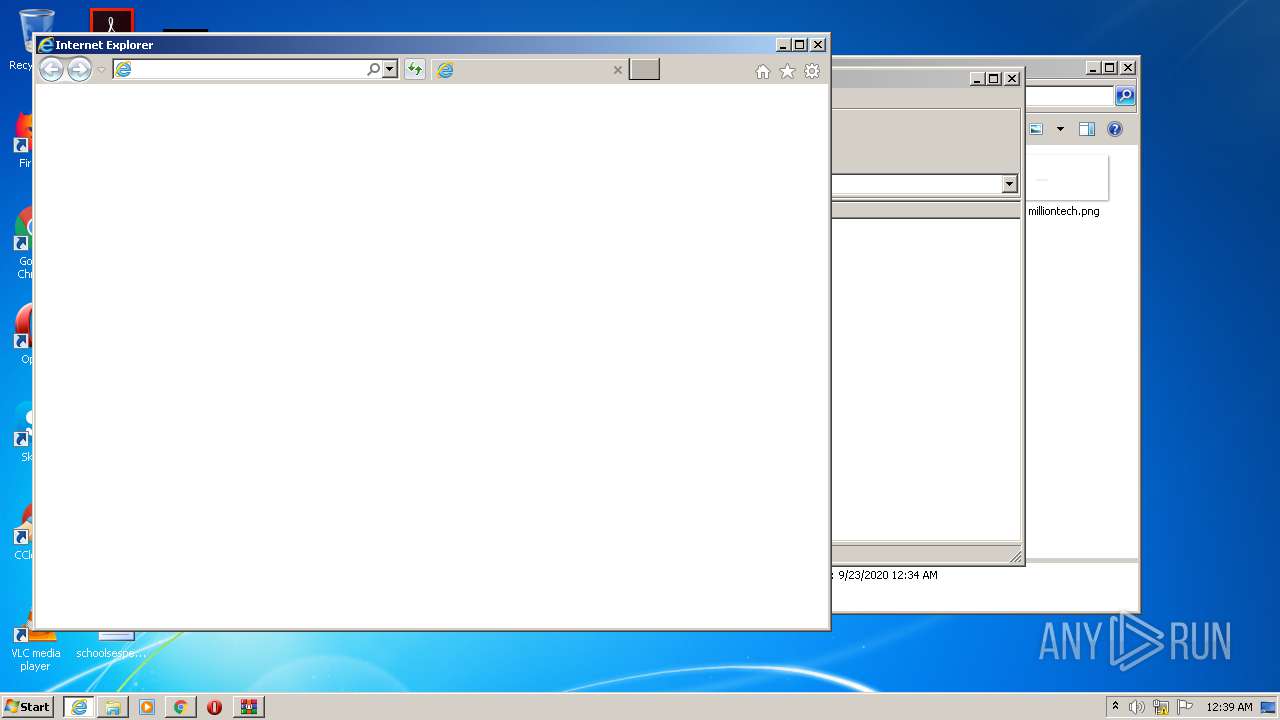
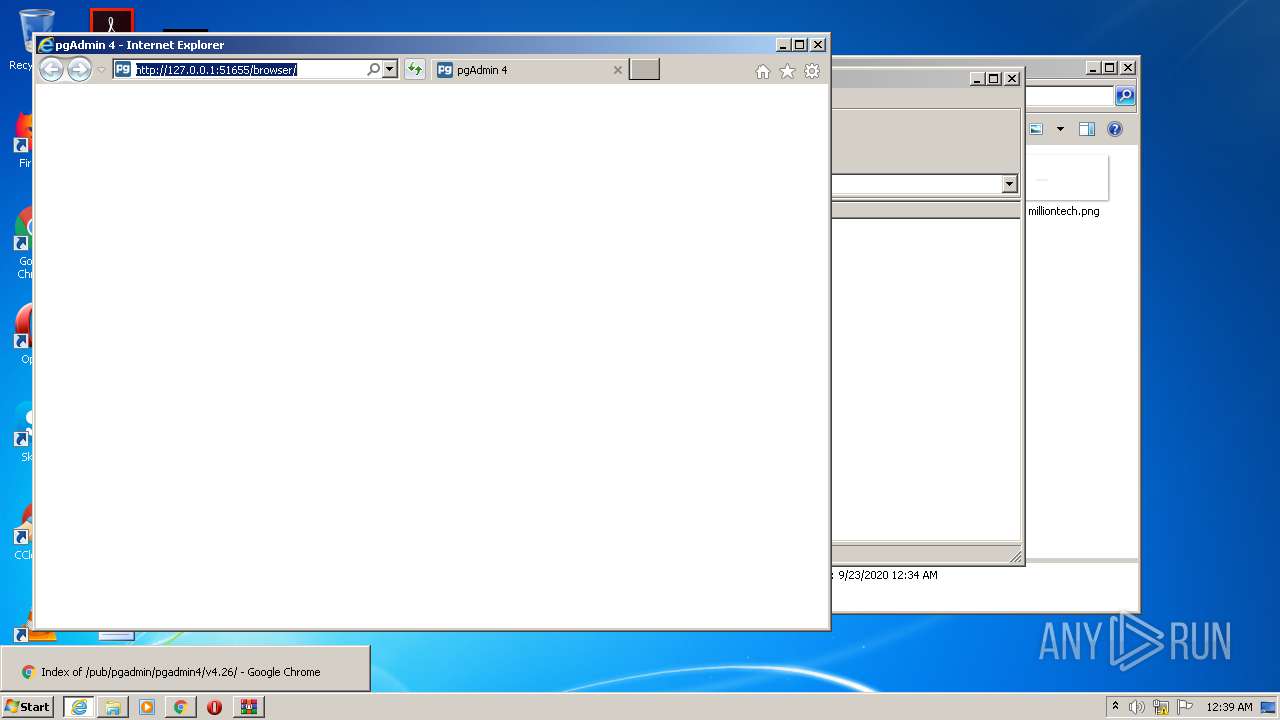
Starts Internet Explorer
- pgAdmin4.exe (PID: 1872)
- pgAdmin4.exe (PID: 2796)
Searches for installed software
- vcredist_x86.exe (PID: 1148)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2824)
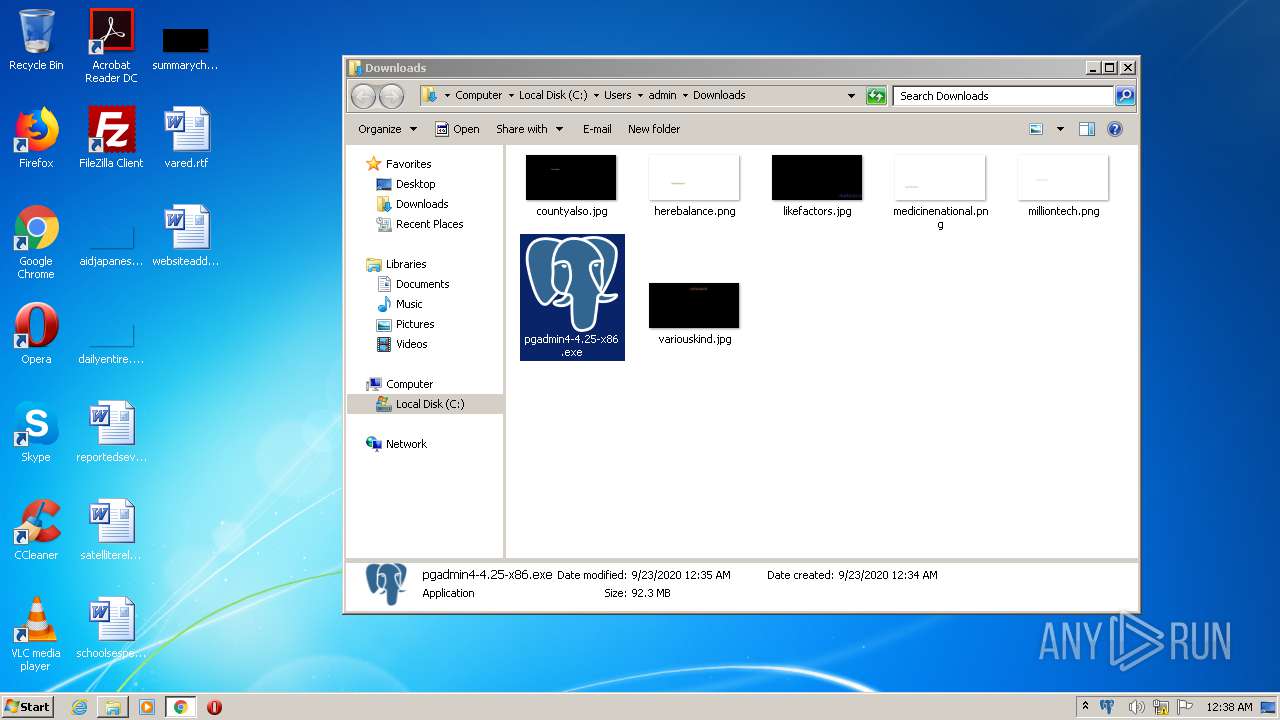
Creates files in the user directory
- pgAdmin4.exe (PID: 1872)
INFO
Reads the hosts file
- chrome.exe (PID: 2824)
- chrome.exe (PID: 696)
Reads Internet Cache Settings
- chrome.exe (PID: 2824)
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 3856)
Reads settings of System Certificates
- chrome.exe (PID: 696)
- pgAdmin4.exe (PID: 1872)
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 2572)
- chrome.exe (PID: 2824)
Application was dropped or rewritten from another process
- pgadmin4-4.25-x86.tmp (PID: 2816)
- pgadmin4-4.25-x86.tmp (PID: 2340)
Dropped object may contain Bitcoin addresses
- pgadmin4-4.25-x86.tmp (PID: 2340)
Creates a software uninstall entry
- pgadmin4-4.25-x86.tmp (PID: 2340)
Application launched itself
- chrome.exe (PID: 2824)
- iexplore.exe (PID: 3856)
- iexplore.exe (PID: 2120)
Changes internet zones settings
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3856)
Reads internet explorer settings
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 3560)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2120)
Changes settings of System certificates
- iexplore.exe (PID: 2120)
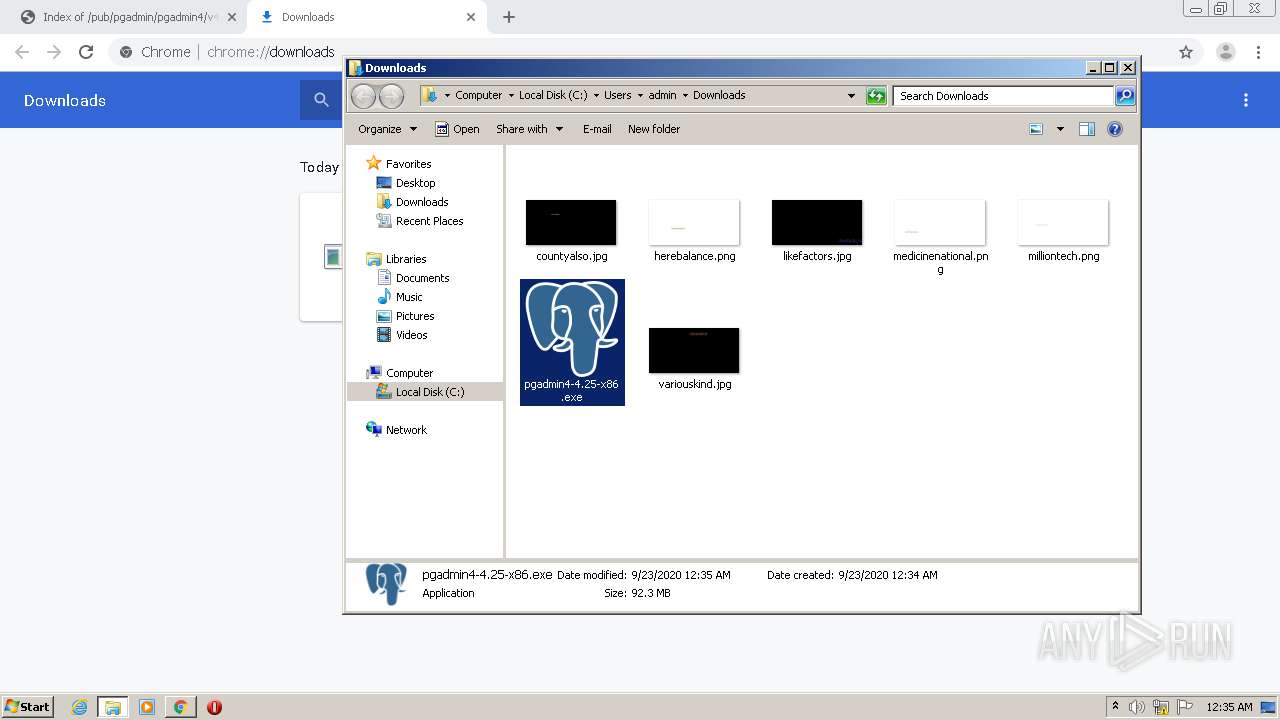
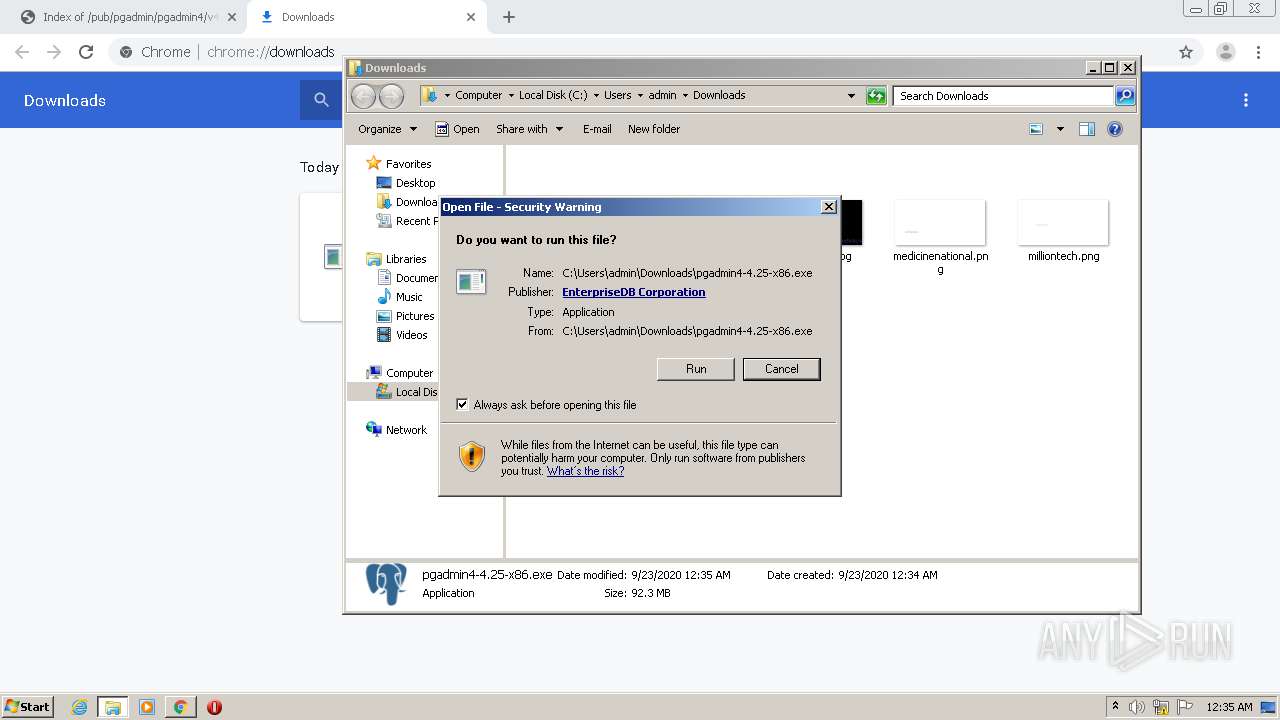
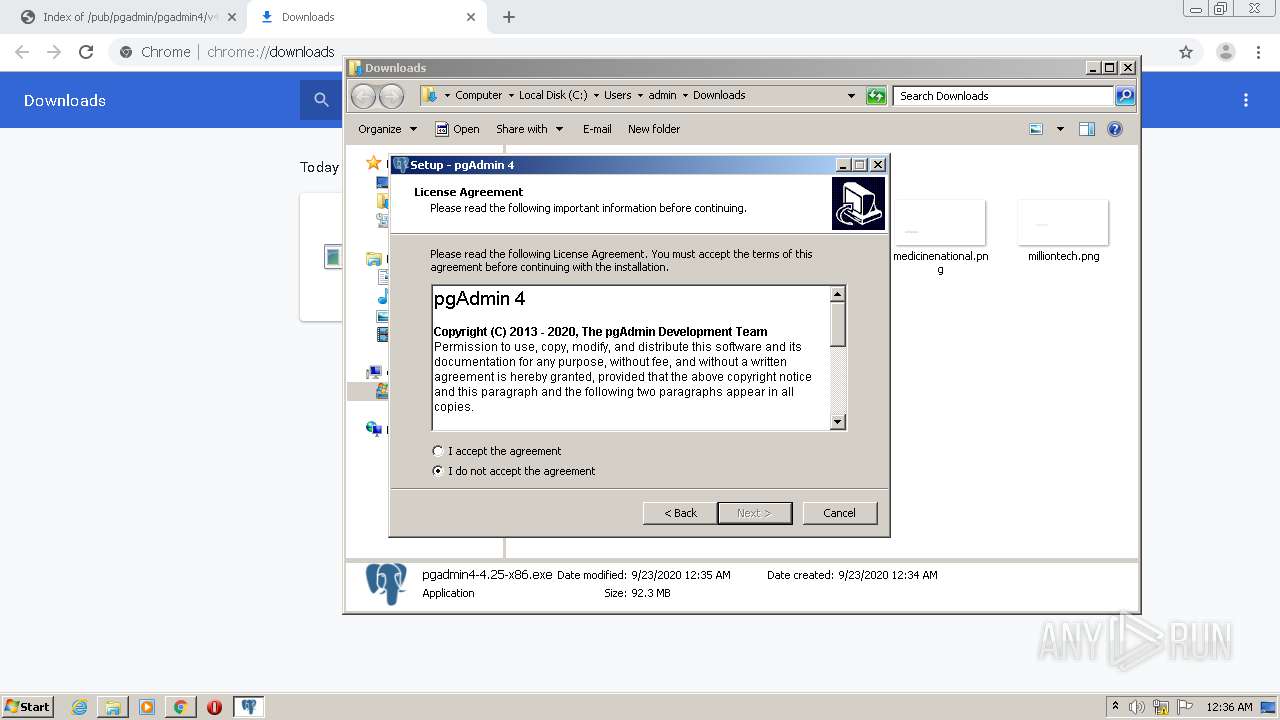
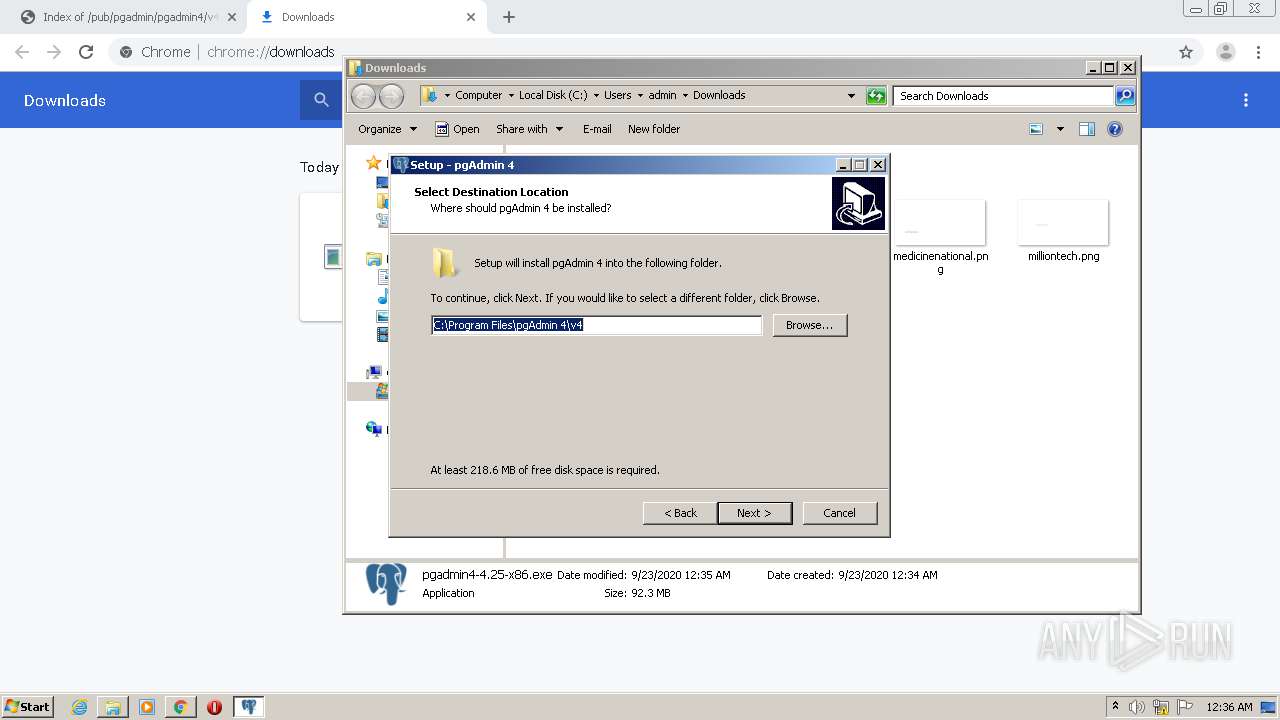
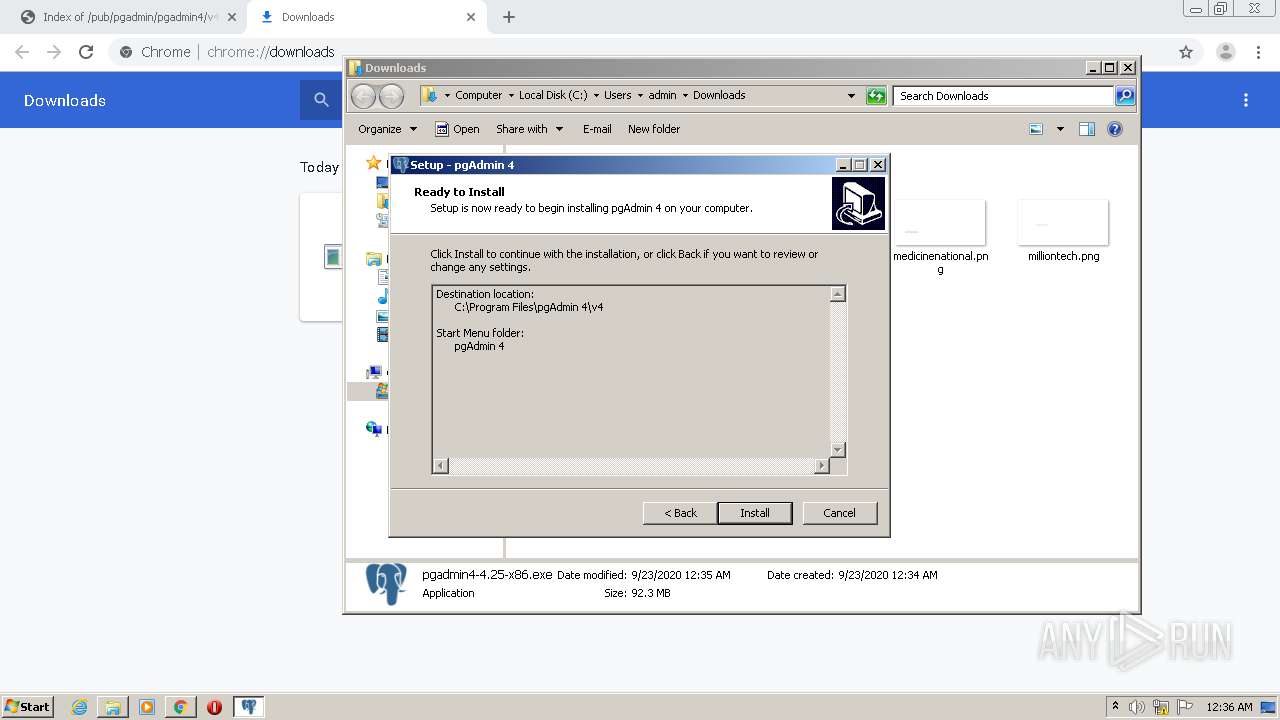
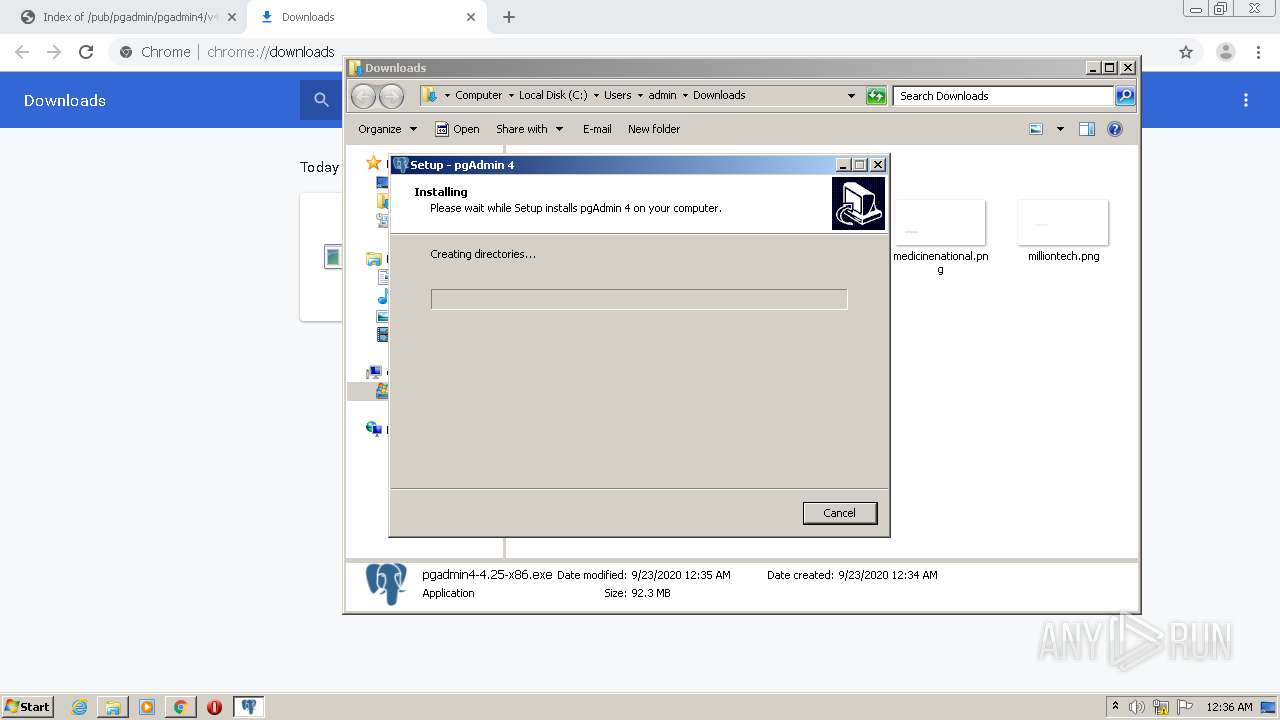
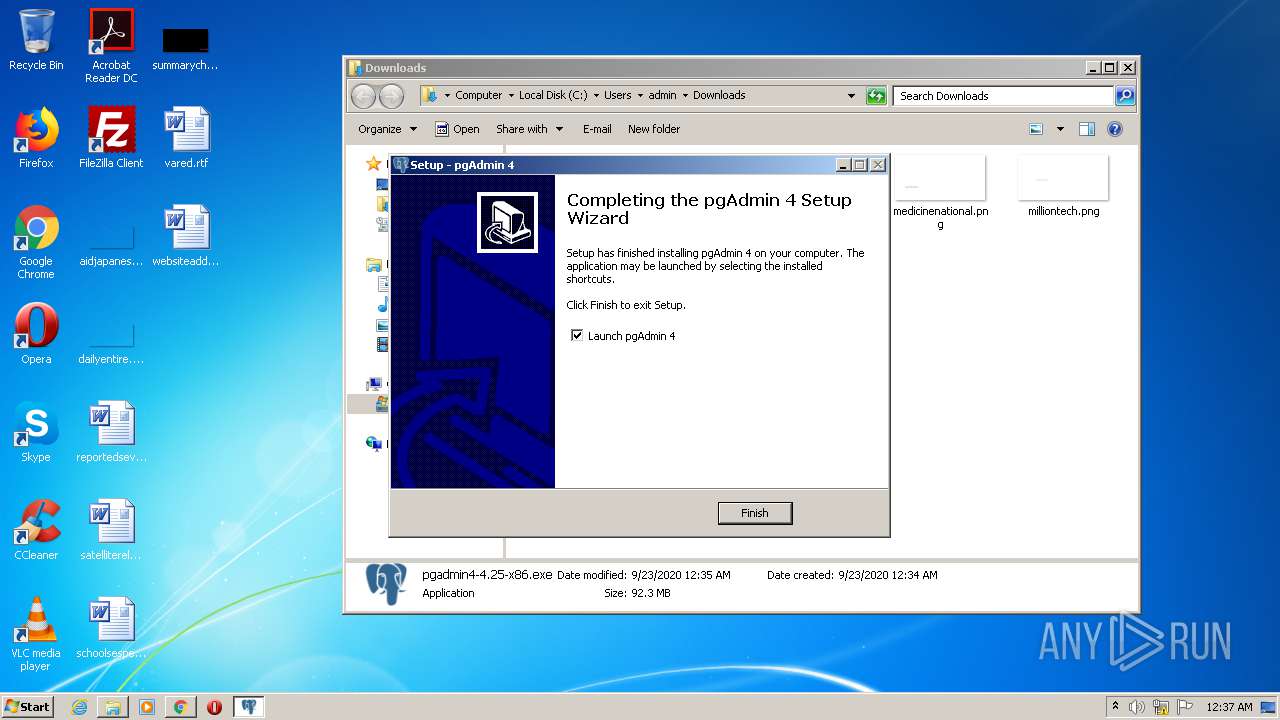
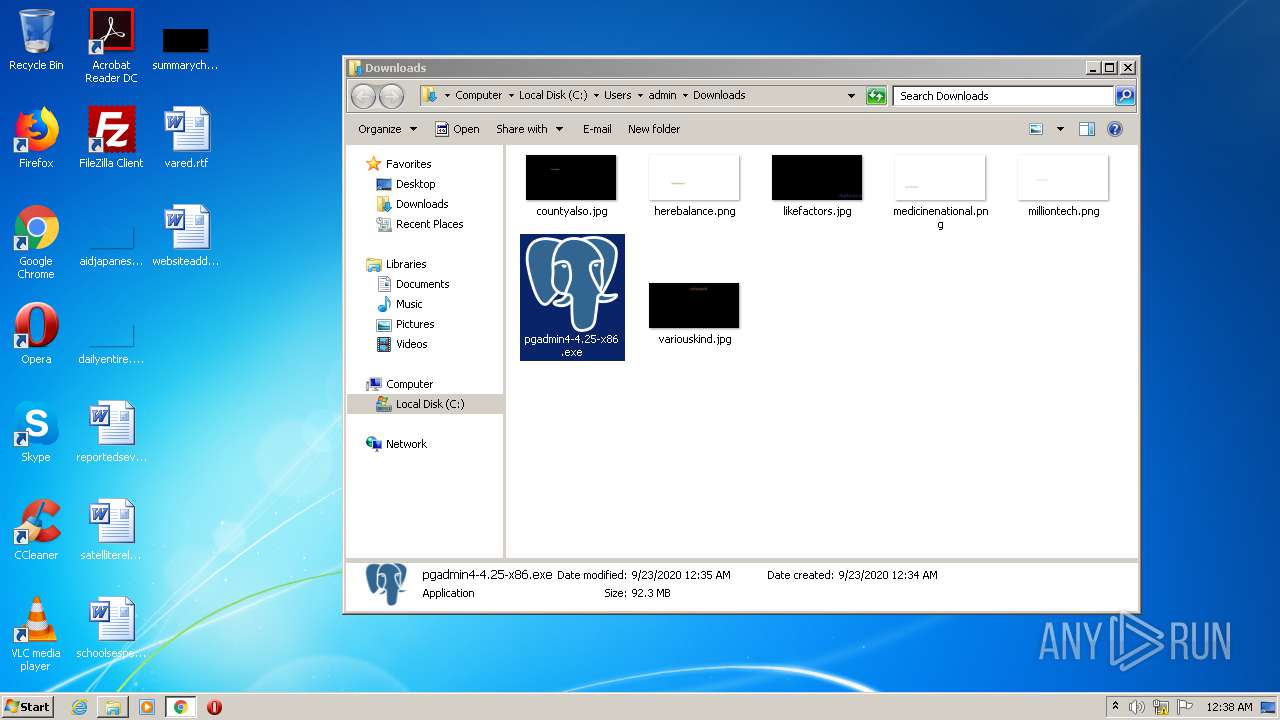
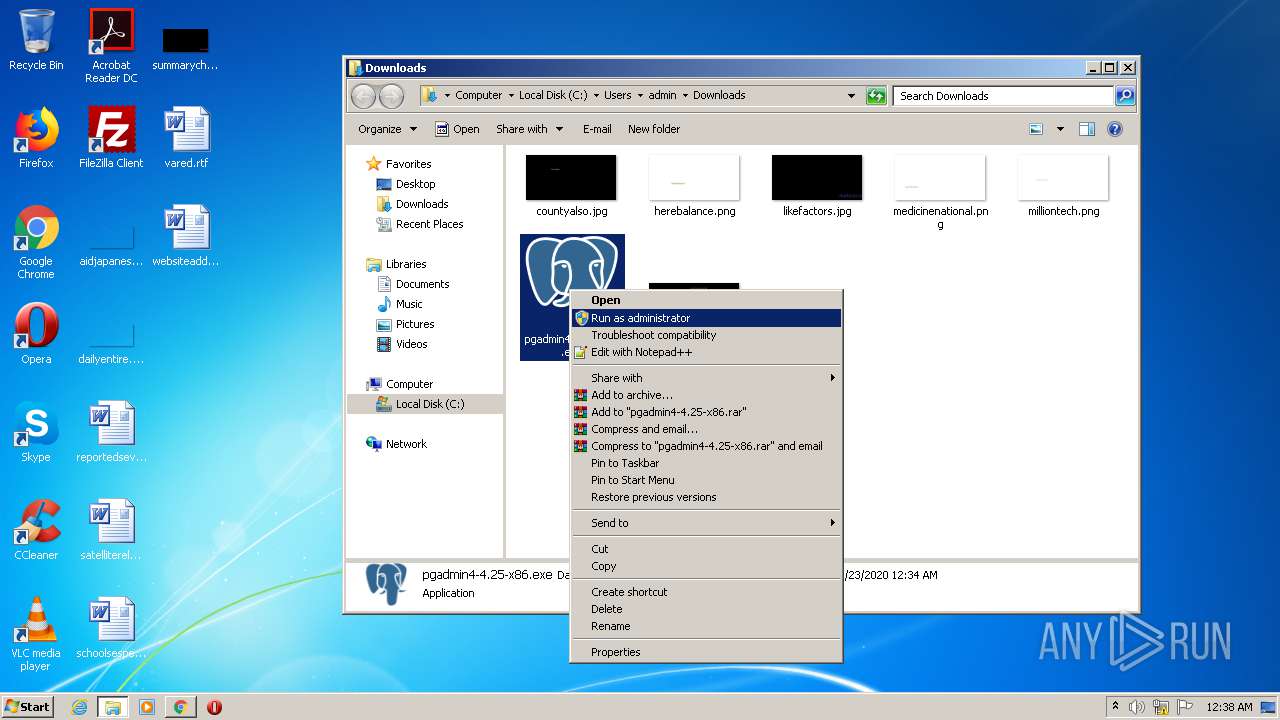
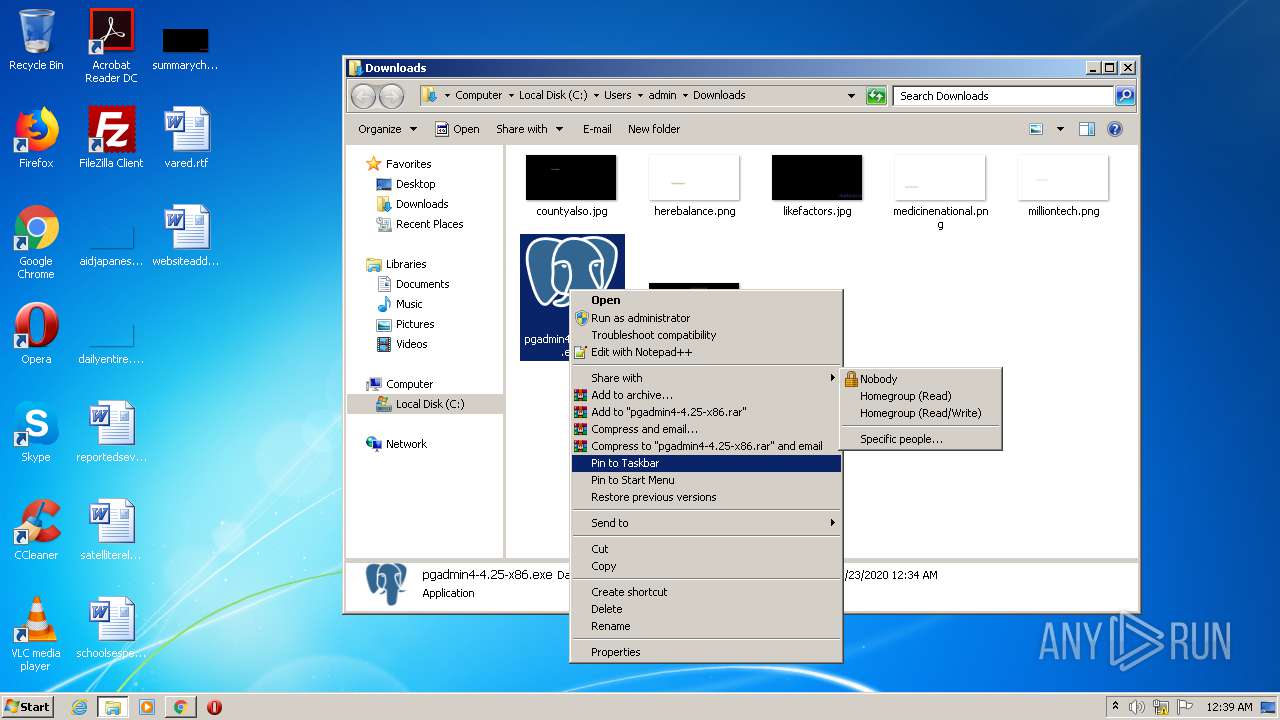
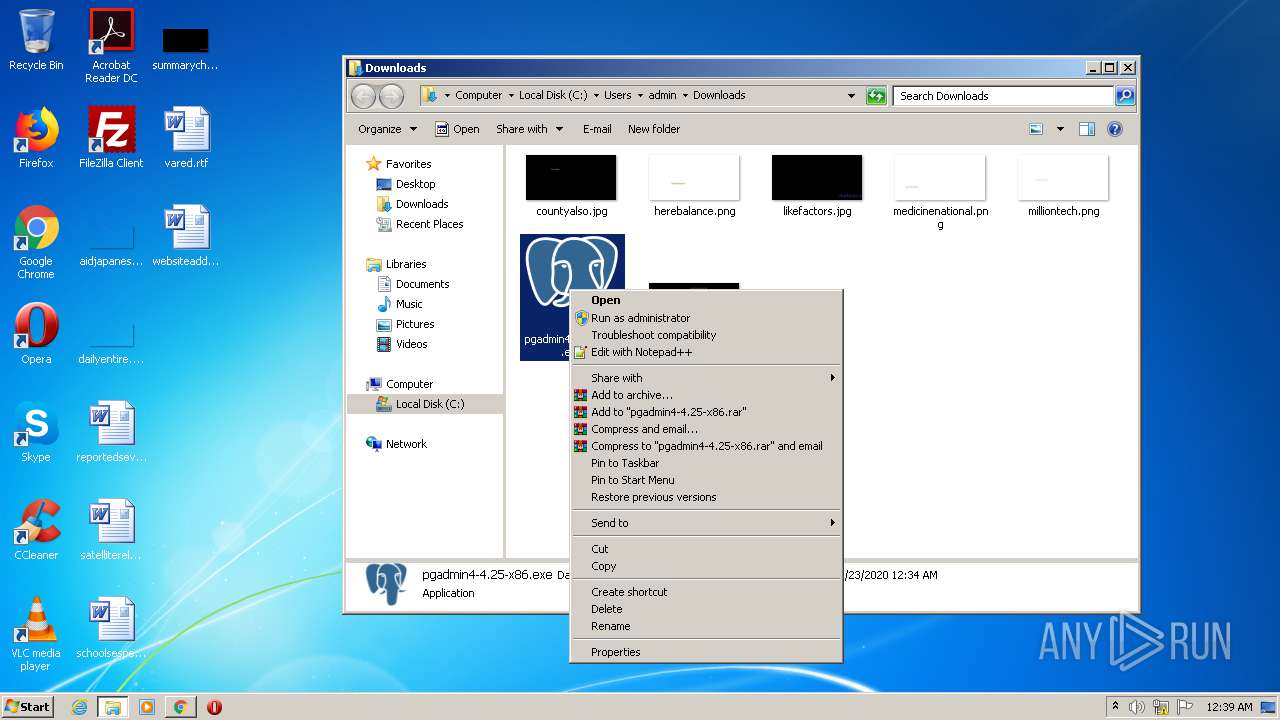
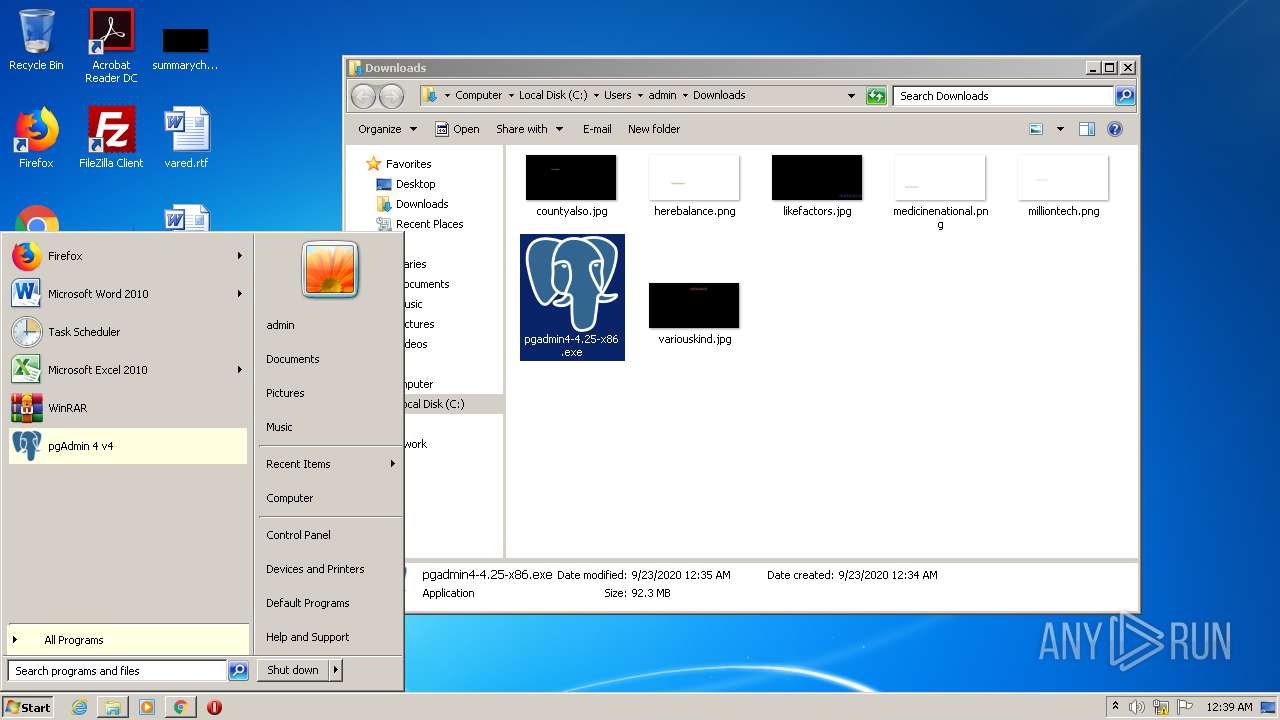
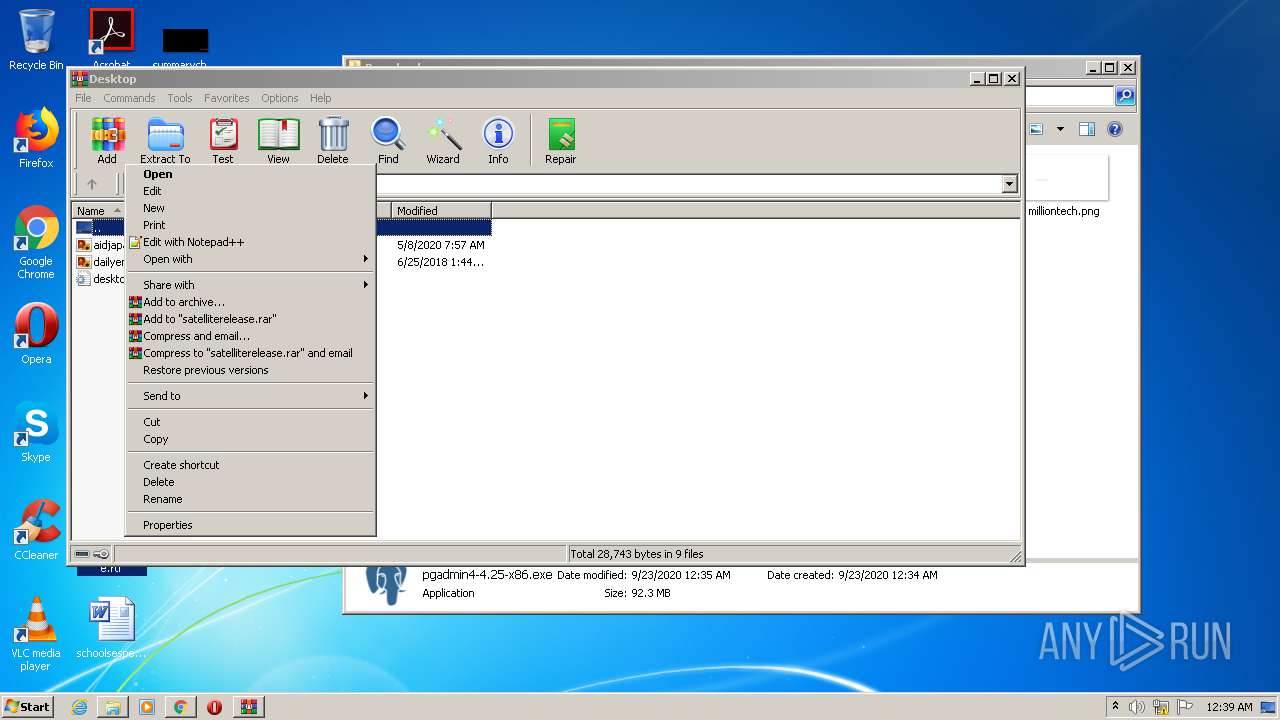
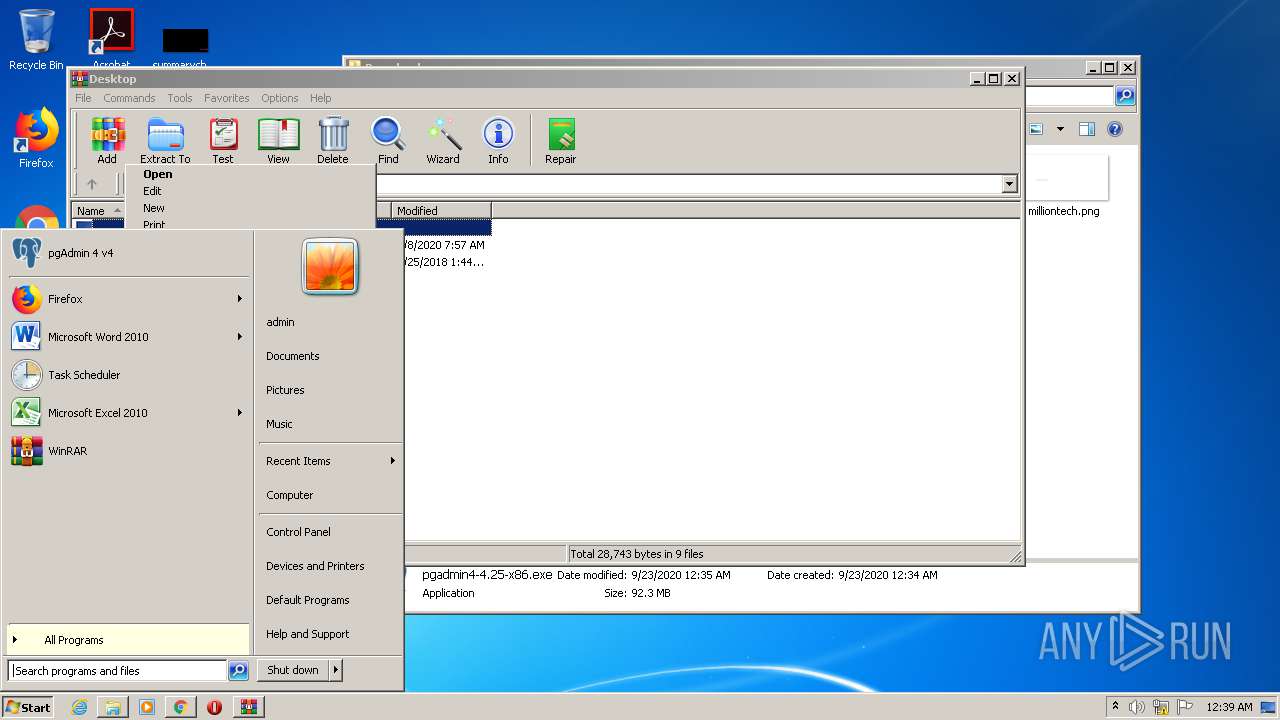
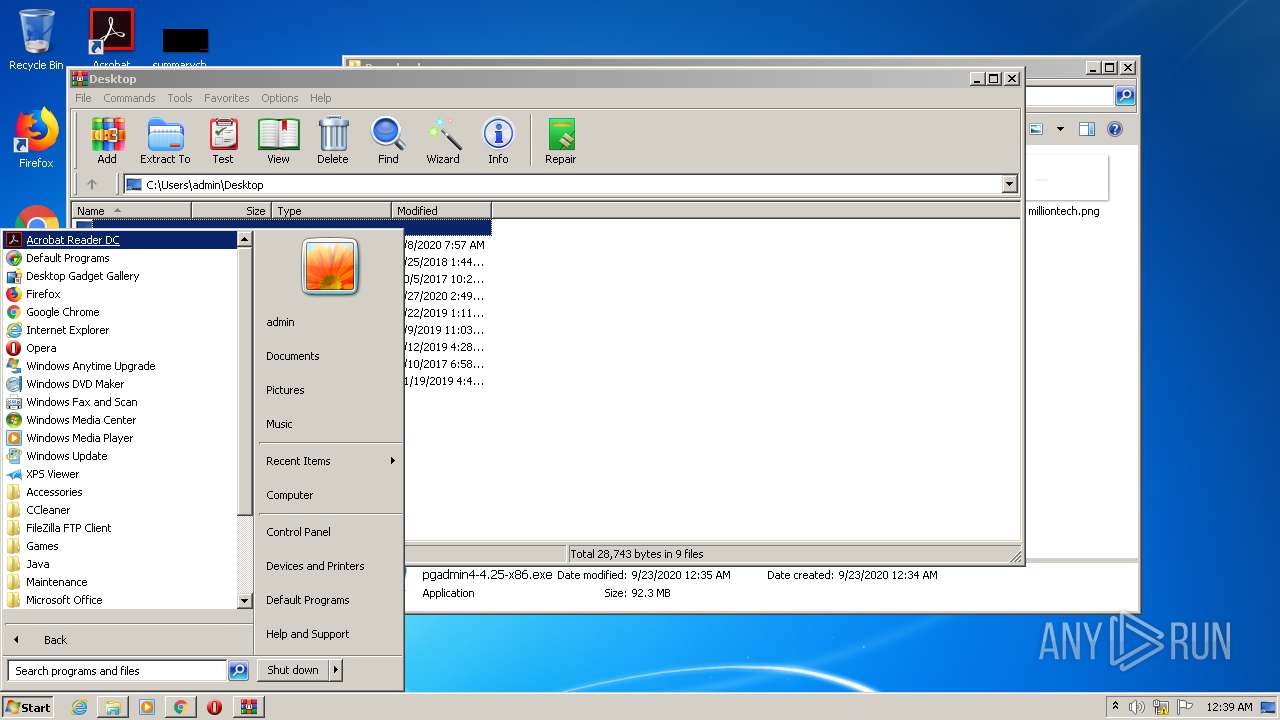
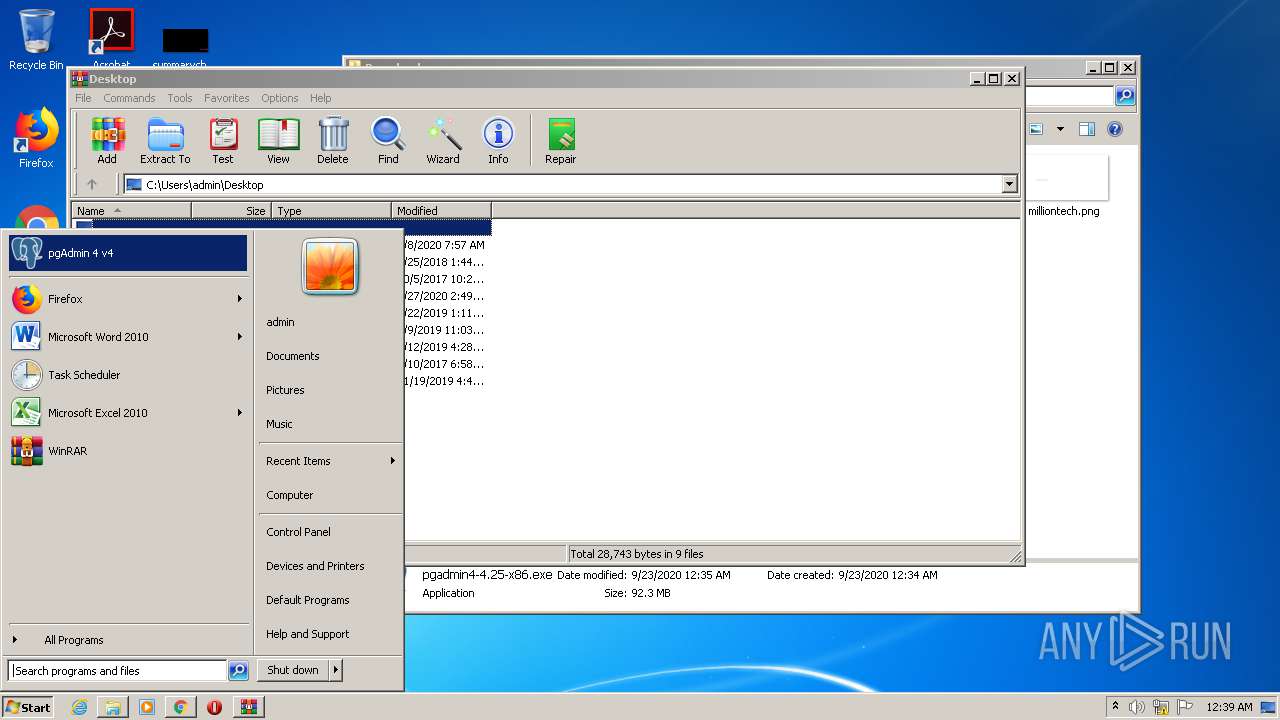
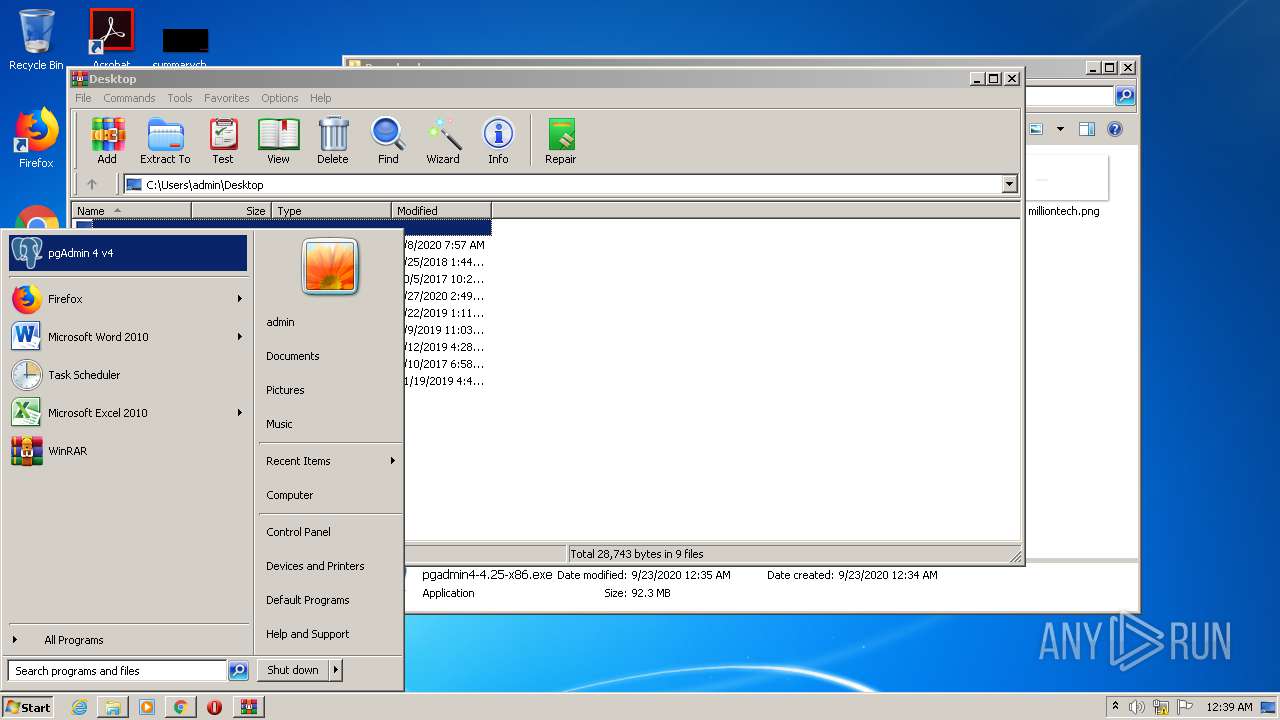
Manual execution by user
- pgadmin4-4.25-x86.exe (PID: 1896)
- WinRAR.exe (PID: 2216)
- pgAdmin4.exe (PID: 2796)
Creates files in the user directory
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2572)
Creates files in the program directory
- pgadmin4-4.25-x86.tmp (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
32
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,132305823032164972,14329379369277643433,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14276527241597116374 --mojo-platform-channel-handle=1504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,132305823032164972,14329379369277643433,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18333063208461454116 --mojo-platform-channel-handle=3424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\pgAdmin 4\v4\installer\vcredist_x86.exe" /passive /verysilent /norestart -burn.unelevated BurnPipe.{EB475F94-2FD3-47AC-8B92-F49743E89697} {4C1FDDF6-6772-4588-B1D3-C792A2EC3962} 2208 | C:\Program Files\pgAdmin 4\v4\installer\vcredist_x86.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.24215 Exit code: 1638 Version: 14.0.24215.1 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,132305823032164972,14329379369277643433,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13573119614441306587 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
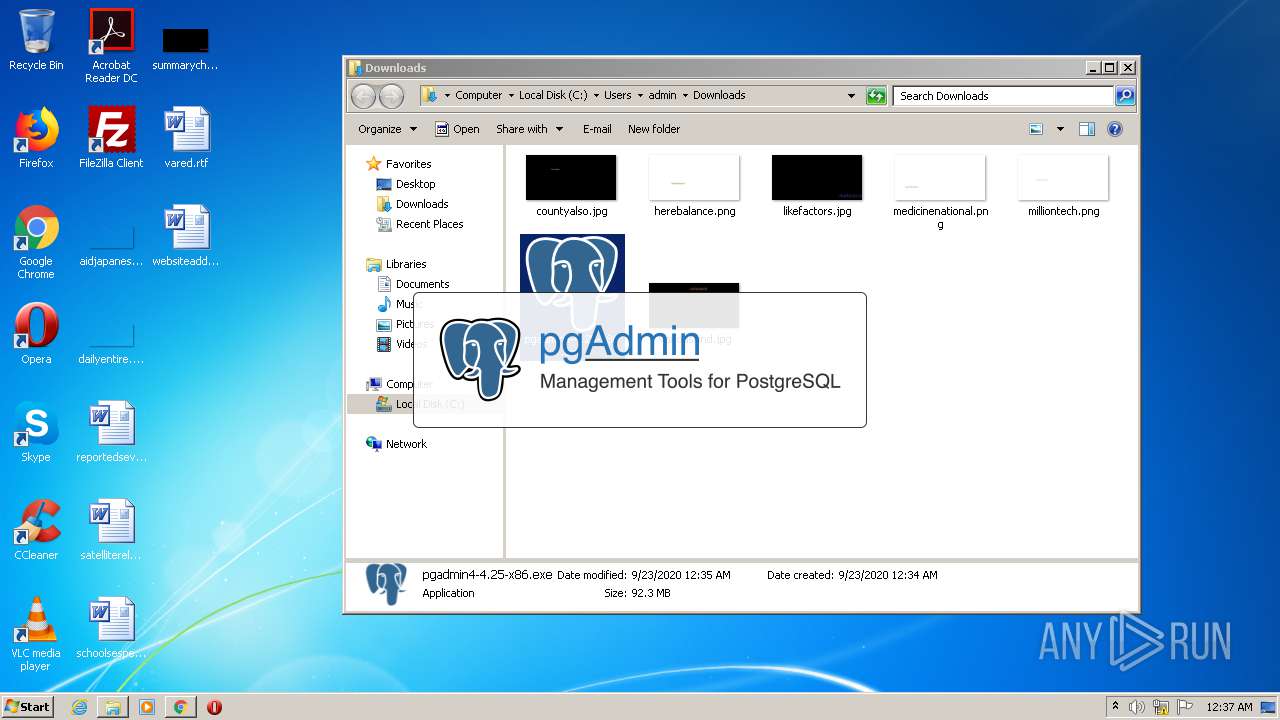
| 1872 | "C:\Program Files\pgAdmin 4\v4\runtime\pgAdmin4.exe" | C:\Program Files\pgAdmin 4\v4\runtime\pgAdmin4.exe | pgadmin4-4.25-x86.tmp | ||||||||||||
User: admin Company: The pgAdmin Development Team Integrity Level: HIGH Description: pgAdmin 4 Desktop Runtime Exit code: 0 Version: 4.25.0.0 Modules
| |||||||||||||||
| 1896 | "C:\Users\admin\Downloads\pgadmin4-4.25-x86.exe" | C:\Users\admin\Downloads\pgadmin4-4.25-x86.exe | explorer.exe | ||||||||||||
User: admin Company: The pgAdmin Development Team Integrity Level: MEDIUM Description: pgAdmin 4 Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Internet Explorer\iexplore.exe" http://127.0.0.1:51655/?key=c99a45f2-5685-49bf-85fa-c4dfc0e4b4a1 | C:\Program Files\Internet Explorer\iexplore.exe | pgAdmin4.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,132305823032164972,14329379369277643433,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16495313998219609517 --mojo-platform-channel-handle=3964 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\pgAdmin 4\v4\installer\\vcredist_x86.exe" /passive /verysilent /norestart | C:\Program Files\pgAdmin 4\v4\installer\vcredist_x86.exe | — | pgadmin4-4.25-x86.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.24215 Exit code: 1638 Version: 14.0.24215.1 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\WinRAR\WinRAR.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
3 407
Read events
3 104
Write events
287
Delete events
16
Modification events
| (PID) Process: | (2488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2824-13245291283840375 |
Value: 259 | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
130
Suspicious files
255
Text files
6 526
Unknown types
1 896
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4a1c541b-b47e-4629-8f82-3dadd0f73b63.tmp | — | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF26e44c.TMP | text | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF26e48b.TMP | text | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF26e650.TMP | — | |
MD5:— | SHA256:— | |||
| 2824 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF26e44c.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
31
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
696 | chrome.exe | GET | 200 | 74.125.100.136:80 | http://r2---sn-5hnedn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=85.203.44.130&mm=28&mn=sn-5hnedn7e&ms=nvh&mt=1600817655&mv=m&mvi=2&pl=26&shardbypass=yes | US | crx | 834 Kb | whitelisted |
696 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2120 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2120 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
696 | chrome.exe | 172.217.18.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
696 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
696 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
696 | chrome.exe | 172.217.21.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
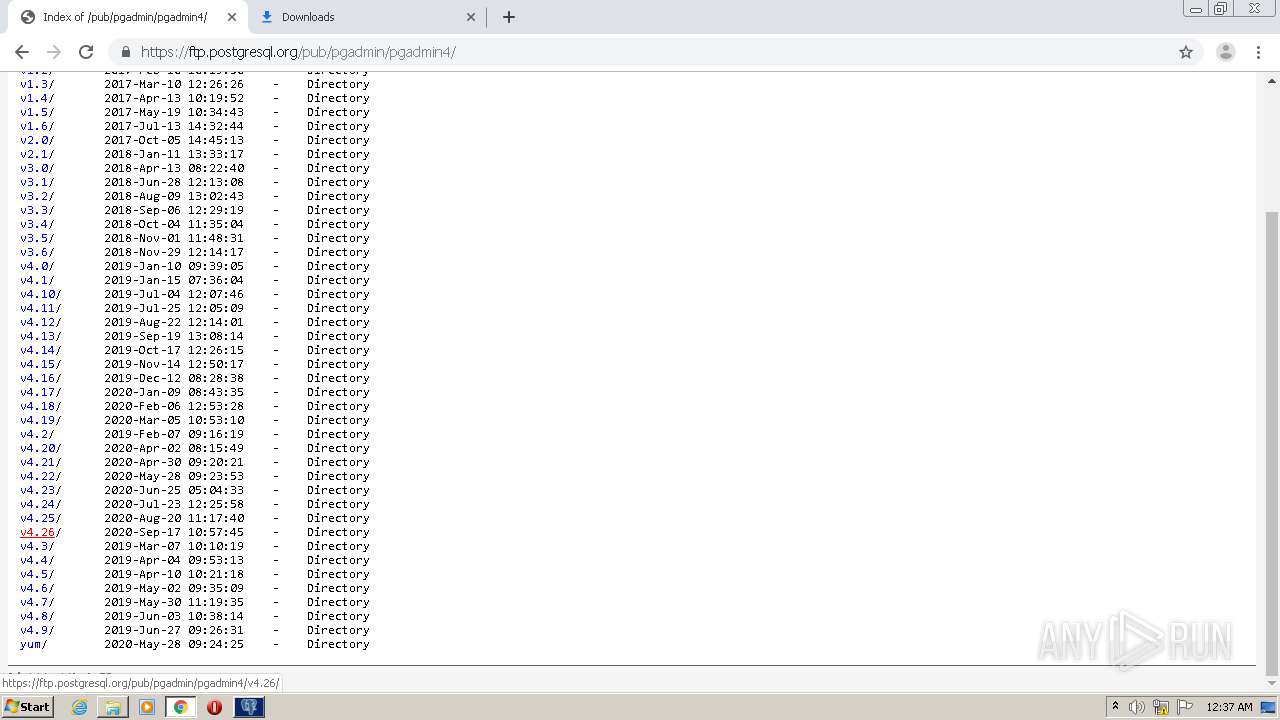
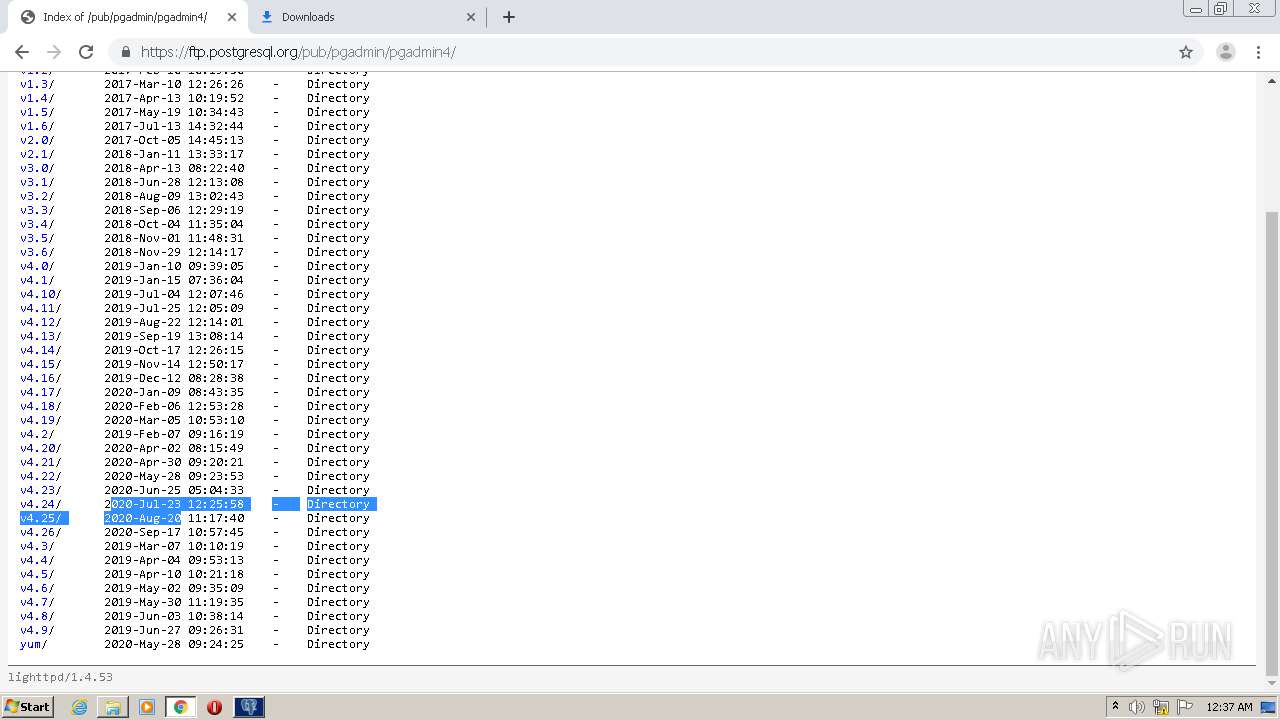
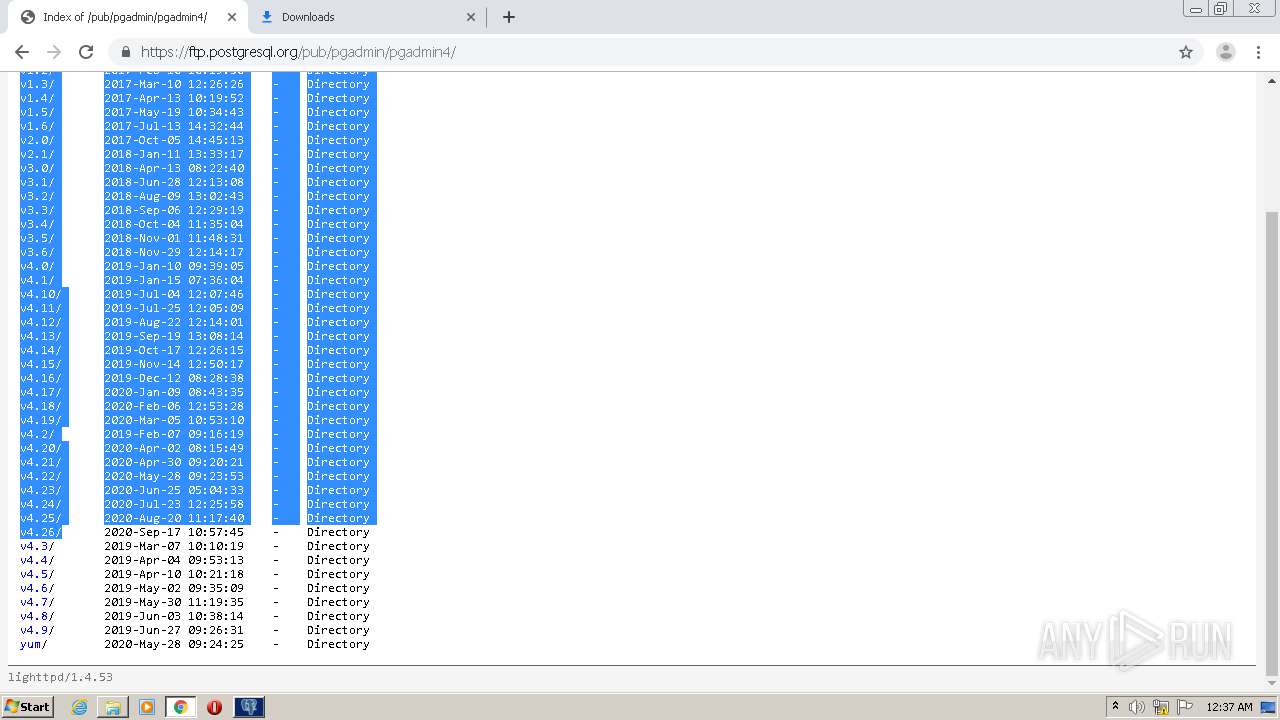
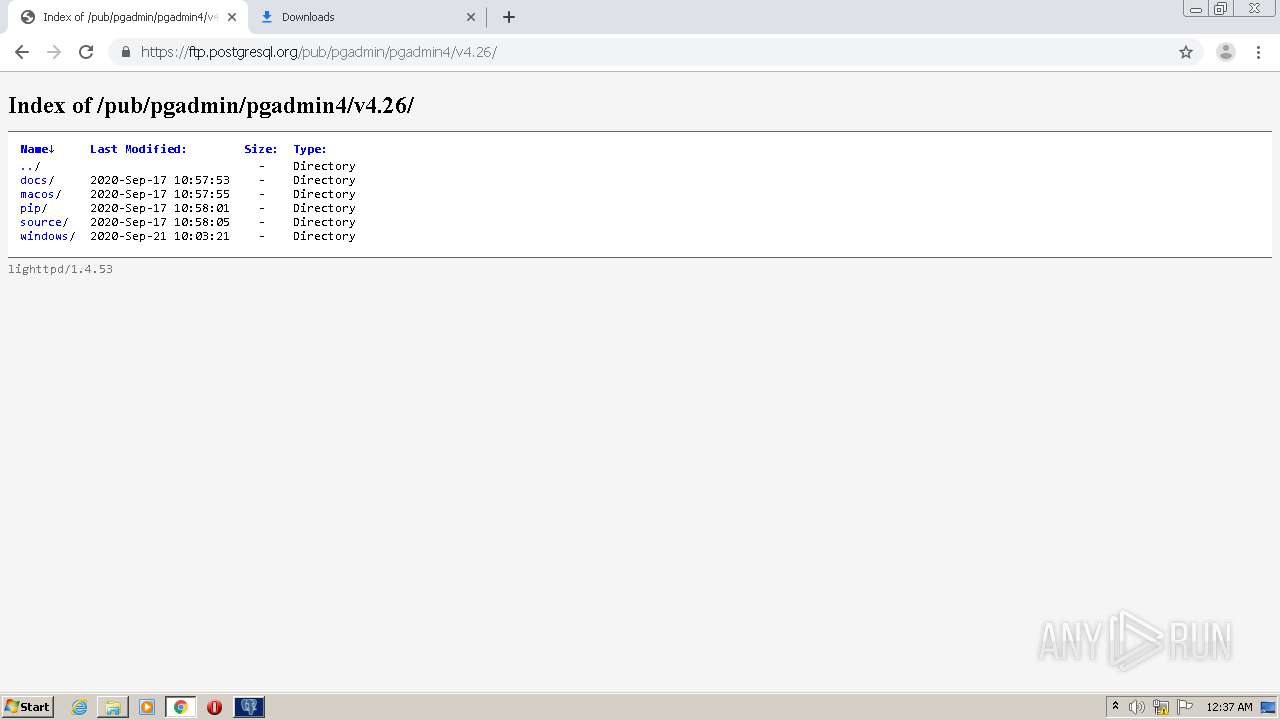
696 | chrome.exe | 147.75.85.69:443 | ftp.postgresql.org | Packet Host, Inc. | US | unknown |
696 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
696 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
696 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
696 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ftp.postgresql.org |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-5hnedn7e.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
pgAdmin4.exe | QCoreApplication::applicationFilePath: Please instantiate the QApplication object first
|
pgAdmin4.exe | QCoreApplication::applicationFilePath: Please instantiate the QApplication object first
|
pgAdmin4.exe | Shared memory segment name: "pgadmin4-admin-719075f6f0e13177672464b6b9001dcb-shmem"
|
pgAdmin4.exe | Semaphore name: "pgadmin4-admin-719075f6f0e13177672464b6b9001dcb-sema"
|
pgAdmin4.exe | Python path: "C:/Program Files/pgAdmin 4/v4/venv/Lib/site-packages;C:/Program Files/pgAdmin 4/v4/venv/DLLs;C:/Program Files/pgAdmin 4/v4/venv/Lib"
Python Home: "C:/Program Files/pgAdmin 4/v4/venv"
|
pgAdmin4.exe | Webapp path: "C:/Program Files/pgAdmin 4/v4/web/pgAdmin4.py"
|
pgAdmin4.exe | Failed to connect to the server: "Connection refused" - request URL: "http://127.0.0.1:51655/misc/ping?key=c99a45f2-5685-49bf-85fa-c4dfc0e4b4a1" .
|
pgAdmin4.exe | Failed to connect to the server: "Connection refused" - request URL: "http://127.0.0.1:51655/misc/ping?key=c99a45f2-5685-49bf-85fa-c4dfc0e4b4a1" .
|
pgAdmin4.exe | Failed to connect to the server: "Connection refused" - request URL: "http://127.0.0.1:51655/misc/ping?key=c99a45f2-5685-49bf-85fa-c4dfc0e4b4a1" .
|
pgAdmin4.exe | Failed to connect to the server: "Connection refused" - request URL: "http://127.0.0.1:51655/misc/ping?key=c99a45f2-5685-49bf-85fa-c4dfc0e4b4a1" .
|