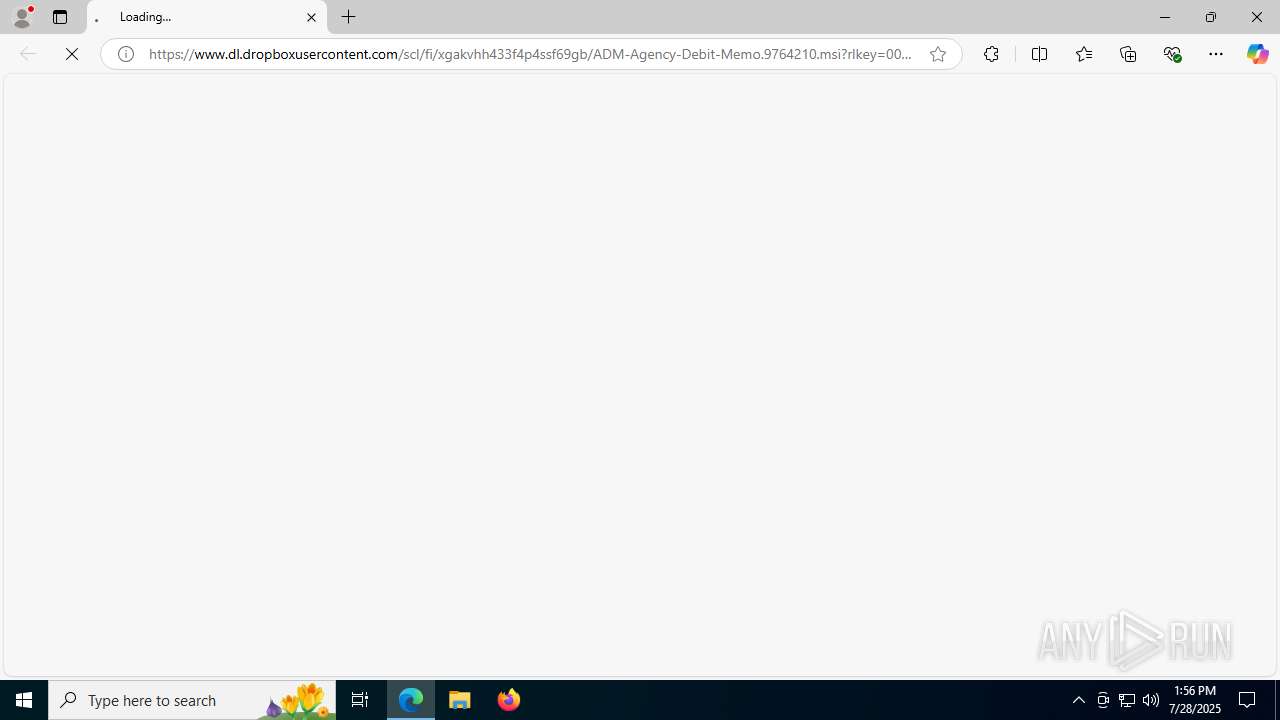
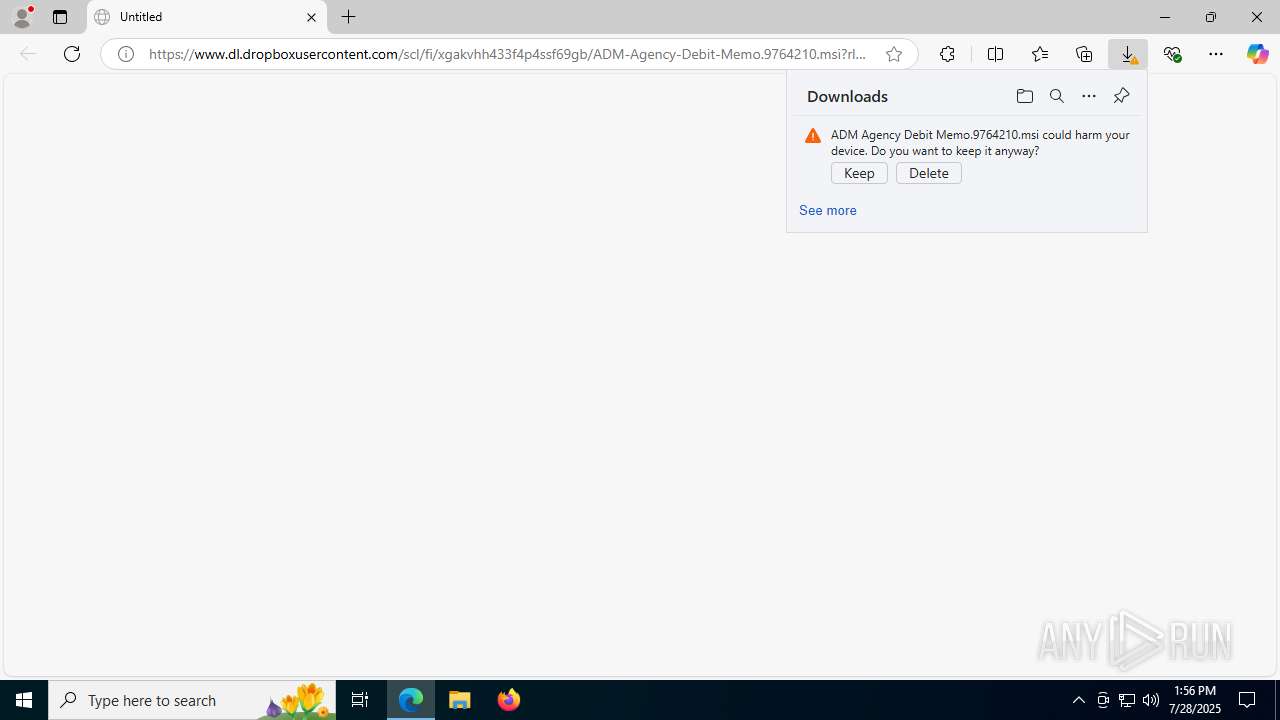
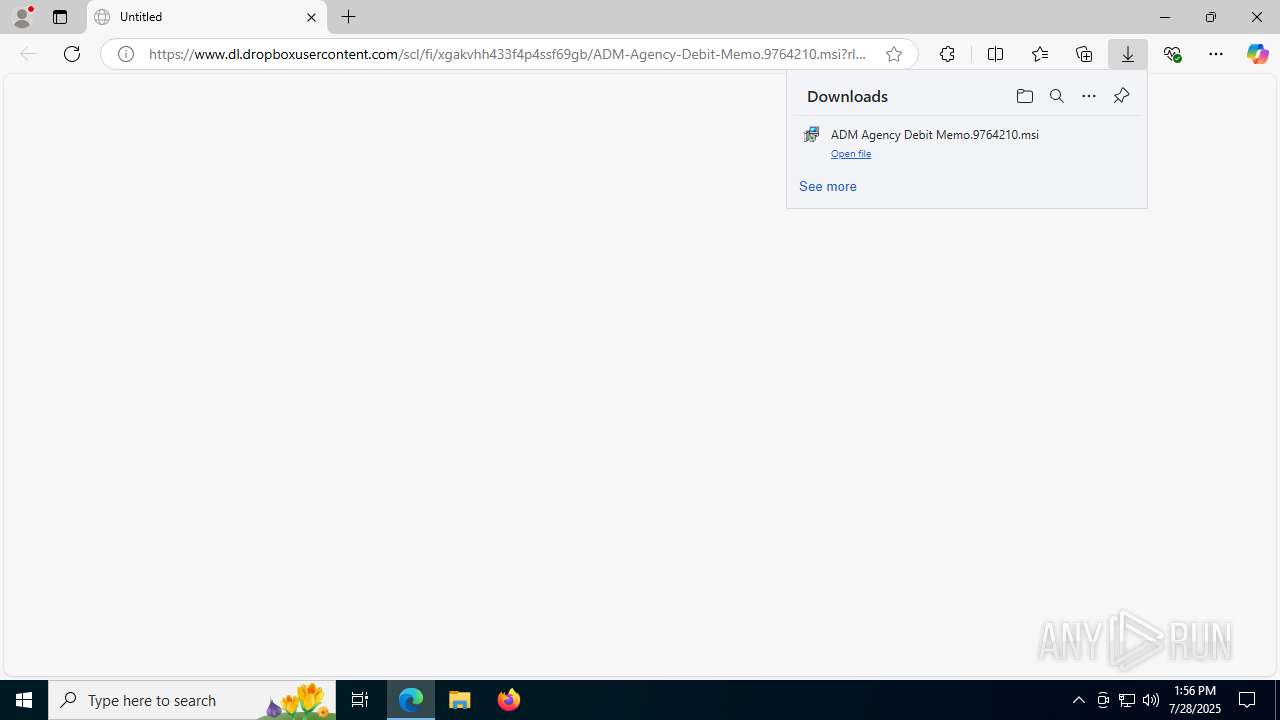
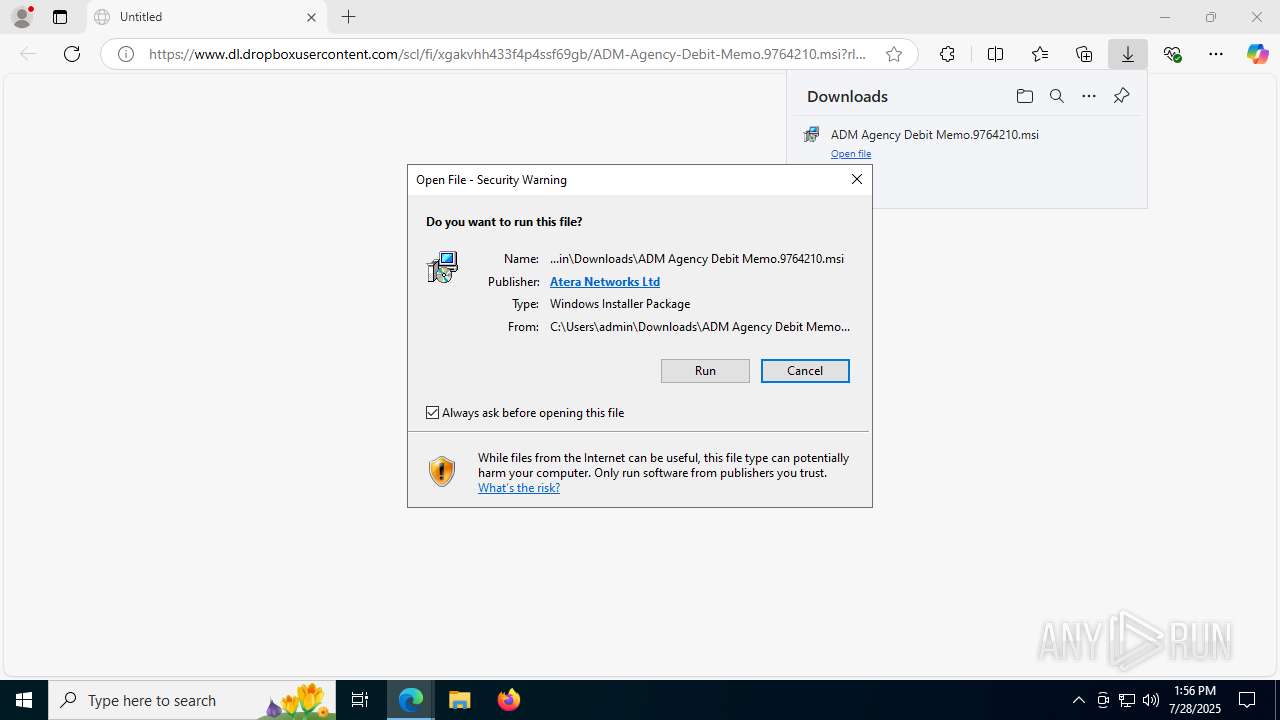
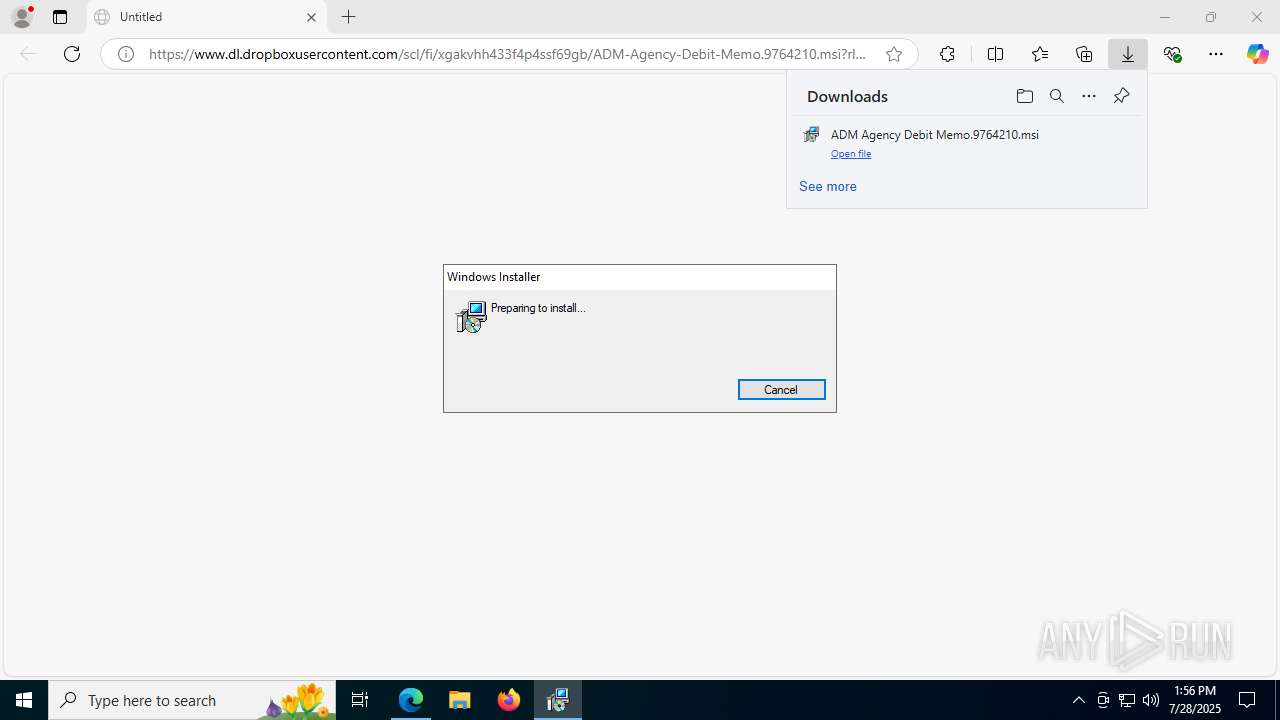
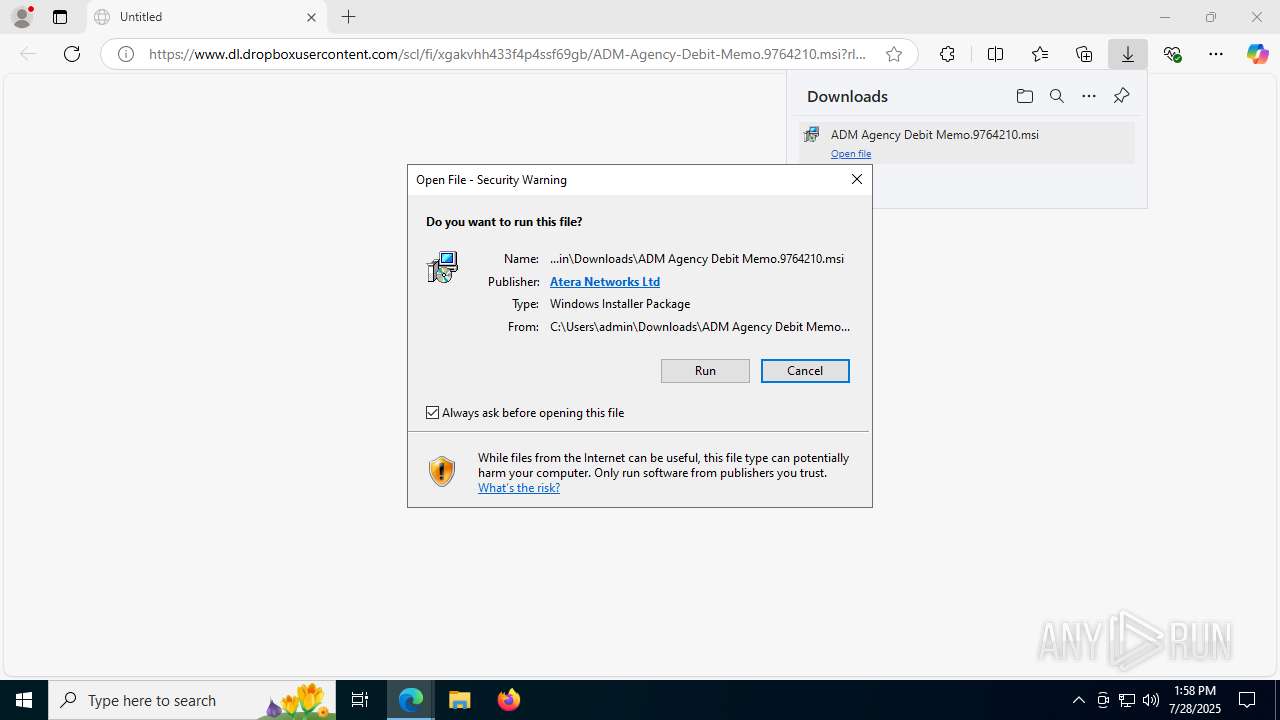
| URL: | https://www.dl.dropboxusercontent.com/scl/fi/xgakvhh433f4p4ssf69gb/ADM-Agency-Debit-Memo.9764210.msi?rlkey=00wjsz1zltz7ks20yds3wio9q&st=abnjce5t&dl=0 |
| Full analysis: | https://app.any.run/tasks/b2226636-ffad-4fb7-95cc-634eb79adc54 |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2025, 13:56:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0B77C76CCE6E8CAB7DE5EFC7D46BCFC3 |
| SHA1: | D7DFCE8685FA99184135BA2257B0C22A883BEA89 |
| SHA256: | 855B0BD344457FA038681753D310792D1138EEEDC4DC046E806011139AD8100D |
| SSDEEP: | 3:N8DSLDcvALtGTU6hAHlTzHKnCALLx9oGjqHMaXlcY/Hm4cg+xPXiYV:2OLDFGlAHlTzsDLntpa1cYLcVXi4 |
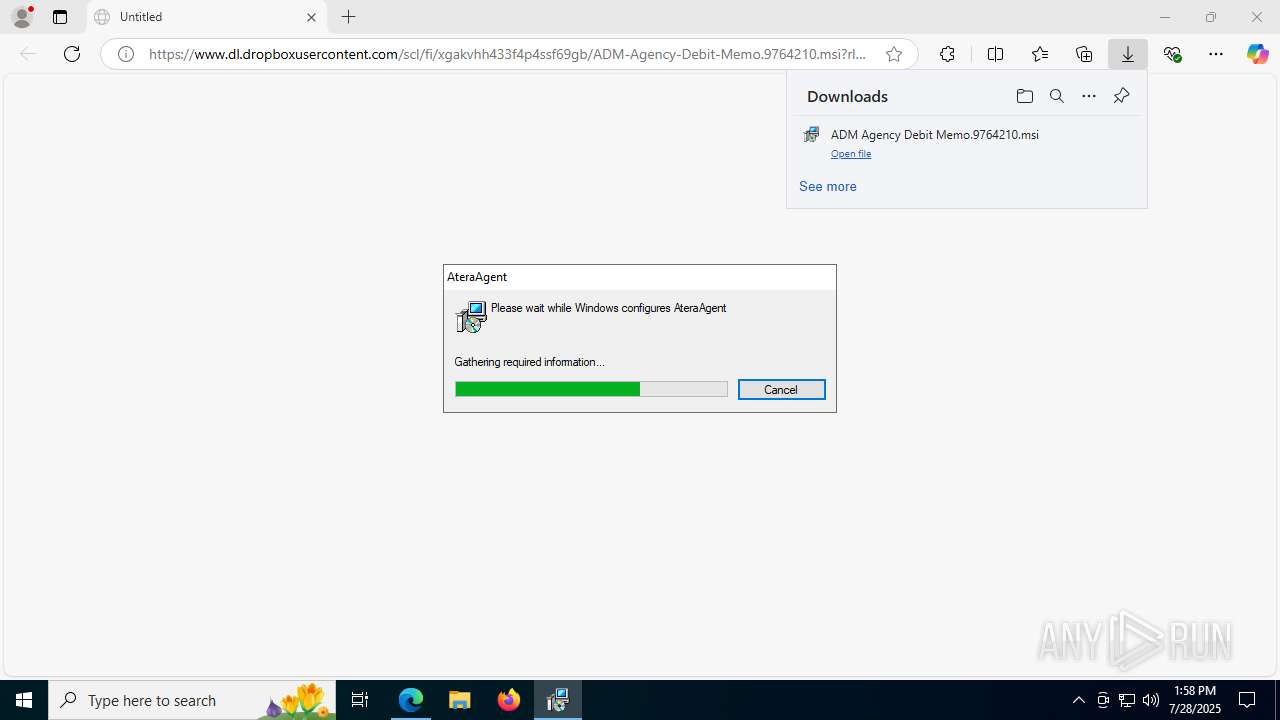
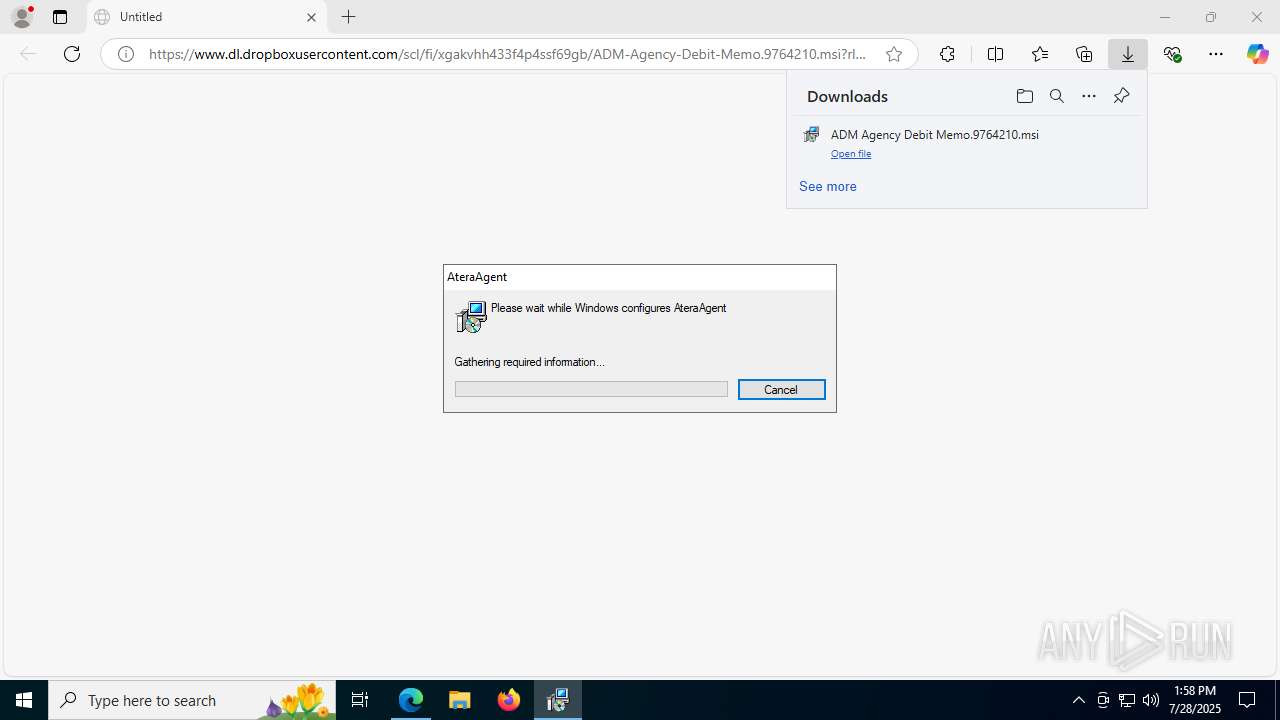
MALICIOUS
Starts NET.EXE for service management
- msiexec.exe (PID: 188)
- net.exe (PID: 4080)
- msiexec.exe (PID: 7648)
- net.exe (PID: 7660)
SUSPICIOUS
Process drops legitimate windows executable
- msedge.exe (PID: 3760)
- msedge.exe (PID: 2972)
- msiexec.exe (PID: 7856)
- AteraAgent.exe (PID: 7372)
Executes as Windows Service
- VSSVC.exe (PID: 7908)
- AteraAgent.exe (PID: 7372)
- AteraAgent.exe (PID: 6360)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7856)
Executable content was dropped or overwritten
- rundll32.exe (PID: 1976)
- rundll32.exe (PID: 6228)
- rundll32.exe (PID: 7756)
- AteraAgent.exe (PID: 7372)
- rundll32.exe (PID: 7360)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 188)
- msiexec.exe (PID: 7648)
Potential Corporate Privacy Violation
- rundll32.exe (PID: 1976)
- AteraAgent.exe (PID: 7372)
- AgentPackageAgentInformation.exe (PID: 7812)
- AteraAgent.exe (PID: 6360)
ATERAAGENT has been detected
- AteraAgent.exe (PID: 4020)
- AteraAgent.exe (PID: 7372)
- AteraAgent.exe (PID: 1872)
- AteraAgent.exe (PID: 6360)
Reads security settings of Internet Explorer
- AteraAgent.exe (PID: 4020)
- AteraAgent.exe (PID: 7372)
- AteraAgent.exe (PID: 1872)
- AteraAgent.exe (PID: 6360)
Reads the date of Windows installation
- AteraAgent.exe (PID: 7372)
- AteraAgent.exe (PID: 6360)
Restarts service on failure
- sc.exe (PID: 1232)
- sc.exe (PID: 8056)
Starts SC.EXE for service management
- AteraAgent.exe (PID: 7372)
- AteraAgent.exe (PID: 6360)
INFO
Application launched itself
- msedge.exe (PID: 2972)
Checks supported languages
- identity_helper.exe (PID: 7588)
- msiexec.exe (PID: 7856)
- msiexec.exe (PID: 7268)
- msiexec.exe (PID: 188)
- AteraAgent.exe (PID: 4020)
- AteraAgent.exe (PID: 7372)
- AgentPackageAgentInformation.exe (PID: 7812)
- AgentPackageAgentInformation.exe (PID: 7848)
- msiexec.exe (PID: 516)
- AteraAgent.exe (PID: 1872)
- msiexec.exe (PID: 7648)
- AteraAgent.exe (PID: 6360)
Reads the computer name
- identity_helper.exe (PID: 7588)
- msiexec.exe (PID: 7856)
- msiexec.exe (PID: 188)
- msiexec.exe (PID: 7268)
- AteraAgent.exe (PID: 4020)
- AteraAgent.exe (PID: 7372)
- AgentPackageAgentInformation.exe (PID: 7812)
- AgentPackageAgentInformation.exe (PID: 7848)
- msiexec.exe (PID: 516)
- msiexec.exe (PID: 7648)
- AteraAgent.exe (PID: 1872)
- AteraAgent.exe (PID: 6360)
Reads Environment values
- identity_helper.exe (PID: 7588)
- AteraAgent.exe (PID: 7372)
- AteraAgent.exe (PID: 4020)
- AgentPackageAgentInformation.exe (PID: 7812)
- AteraAgent.exe (PID: 1872)
- AgentPackageAgentInformation.exe (PID: 7848)
- AteraAgent.exe (PID: 6360)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3112)
Executable content was dropped or overwritten
- msedge.exe (PID: 2972)
- msedge.exe (PID: 3760)
- msiexec.exe (PID: 7856)
Reads the software policy settings
- msiexec.exe (PID: 3112)
- msiexec.exe (PID: 7856)
- rundll32.exe (PID: 1976)
- AteraAgent.exe (PID: 4020)
- AteraAgent.exe (PID: 7372)
- rundll32.exe (PID: 7360)
- AgentPackageAgentInformation.exe (PID: 7812)
- AgentPackageAgentInformation.exe (PID: 7848)
- AteraAgent.exe (PID: 1872)
- AteraAgent.exe (PID: 6360)
- slui.exe (PID: 5496)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2972)
Manages system restore points
- SrTasks.exe (PID: 3800)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7856)
- AteraAgent.exe (PID: 4020)
- AteraAgent.exe (PID: 7372)
- AgentPackageAgentInformation.exe (PID: 7812)
- AgentPackageAgentInformation.exe (PID: 7848)
- AteraAgent.exe (PID: 1872)
- AteraAgent.exe (PID: 6360)
The sample compiled with english language support
- rundll32.exe (PID: 7756)
- rundll32.exe (PID: 1976)
- rundll32.exe (PID: 6228)
- rundll32.exe (PID: 7360)
Create files in a temporary directory
- rundll32.exe (PID: 7756)
- rundll32.exe (PID: 1976)
- rundll32.exe (PID: 6228)
- rundll32.exe (PID: 7360)
Checks proxy server information
- rundll32.exe (PID: 1976)
- rundll32.exe (PID: 7360)
- slui.exe (PID: 5496)
Disables trace logs
- rundll32.exe (PID: 1976)
- AteraAgent.exe (PID: 7372)
- rundll32.exe (PID: 7360)
- AgentPackageAgentInformation.exe (PID: 7848)
- AgentPackageAgentInformation.exe (PID: 7812)
- AteraAgent.exe (PID: 6360)
Creates a software uninstall entry
- msiexec.exe (PID: 7856)
Creates files in the program directory
- AteraAgent.exe (PID: 4020)
- AteraAgent.exe (PID: 7372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
208
Monitored processes
67
Malicious processes
3
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\Windows\syswow64\MsiExec.exe -Embedding 83E69DC8358787C2F7E361002CB2EA5D E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | C:\WINDOWS\system32\net1 STOP AteraAgent | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | C:\Windows\syswow64\MsiExec.exe -Embedding 96CAC28BD3AF2BC3865ECFC74E661DFB | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2684,i,1298117884328818703,822774511681152456,262144 --variations-seed-version --mojo-platform-channel-handle=2680 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc43bcf208,0x7ffc43bcf214,0x7ffc43bcf220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6916,i,1298117884328818703,822774511681152456,262144 --variations-seed-version --mojo-platform-channel-handle=7568 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1232 | "C:\Windows\System32\sc.exe" failure AteraAgent reset= 600 actions= restart/25000 | C:\Windows\System32\sc.exe | — | AteraAgent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1872 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe" /i /IntegratorLogin="abidkhan07873@gmail.com" /CompanyId="1" /IntegratorLoginUI="" /CompanyIdUI="" /FolderId="" /AccountId="001Q300000UkJb8IAF" /AgentId="" | C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe | msiexec.exe | ||||||||||||
User: admin Company: ATERA Networks Ltd. Integrity Level: MEDIUM Description: AteraAgent Exit code: 0 Version: 1.8.7.2 Modules
| |||||||||||||||
| 1976 | rundll32.exe "C:\WINDOWS\Installer\MSI76FC.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1668875 6 AlphaControlAgentInstallation!AlphaControlAgentInstallation.CustomActions.ReportMsiStart | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
38 260
Read events
37 868
Write events
357
Delete events
35
Modification events
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EF955AF193992F00 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524868 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D06C0F25-863A-45D6-9B9C-DDF2BEAA2B7B} | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (2972) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
45
Suspicious files
252
Text files
78
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18db86.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18db86.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18db76.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18dba5.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18dba5.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18dbc5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
79
DNS requests
67
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3760 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:7iU43b1F-AHjoaFn4uF3hlrhozhAt8t5BwrPzqHqI3E&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6832 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2972 | msedge.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
2972 | msedge.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7768 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2972 | msedge.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAnTy%2FhDMohv9omwS69%2Fdow%3D | unknown | — | — | whitelisted |
7768 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4020 | AteraAgent.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2232 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3760 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3760 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3760 | msedge.exe | 162.125.66.15:443 | www.dl.dropboxusercontent.com | DROPBOX | DE | whitelisted |
3760 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3760 | msedge.exe | 2.23.227.199:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.dl.dropboxusercontent.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1976 | rundll32.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7372 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7372 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7372 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
7372 | AteraAgent.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7812 | AgentPackageAgentInformation.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |
7812 | AgentPackageAgentInformation.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Possible Atera Remote Access Software Domain observed in TLS SNI (agent-api .atera .com) |