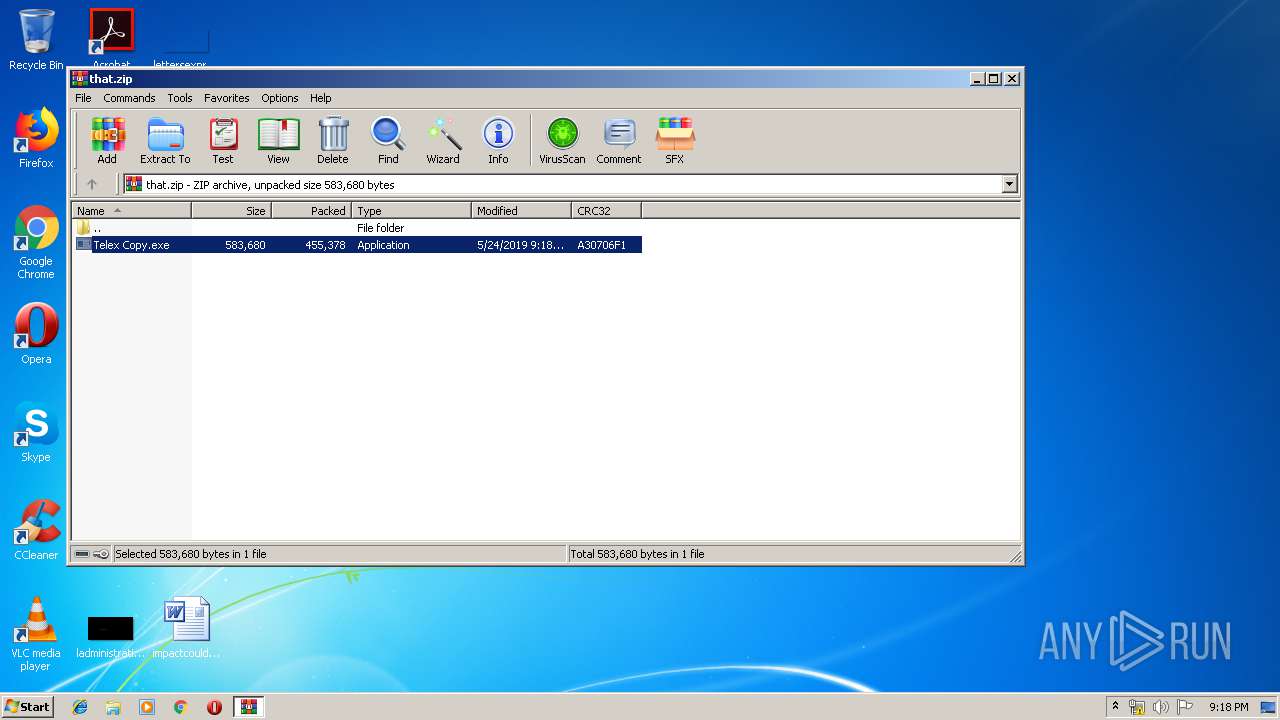
| File name: | that.zip |
| Full analysis: | https://app.any.run/tasks/2820e393-2c2f-4c30-a69c-53825ac8e9f7 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 20:17:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
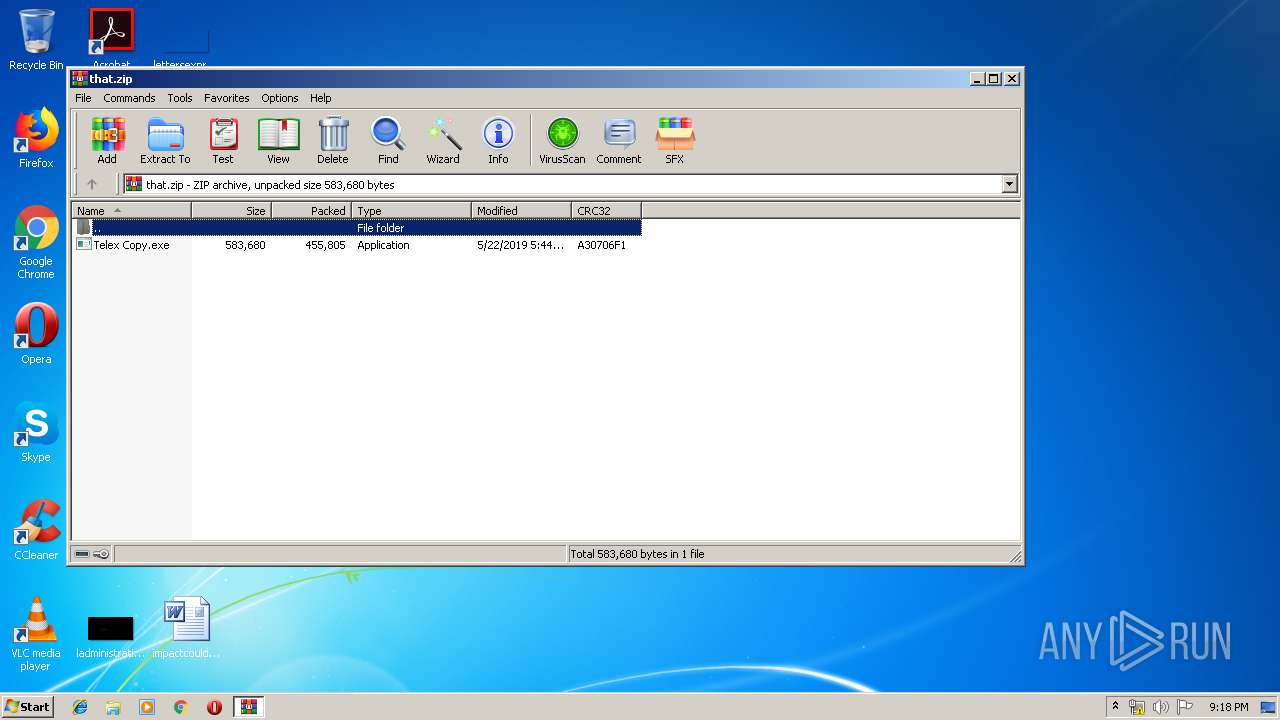
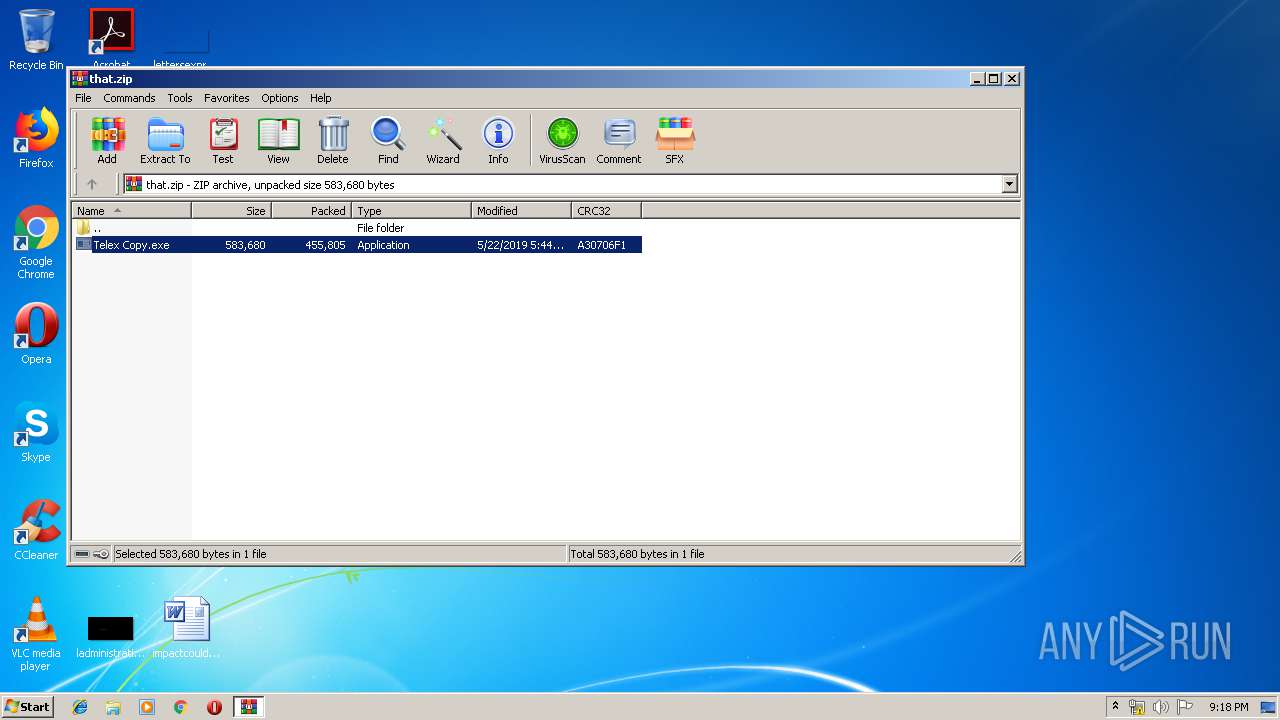
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 132C6C2ED14AB90437EA8CFDDB4FB2D5 |
| SHA1: | 24B6DF3C680552D676117373D41B4408300C1DCD |
| SHA256: | 85525B45B6B86C879C8235839AE49C0F1CA8FDABC753A486B527D4F14823D328 |
| SSDEEP: | 12288:TlGnTz+ptjD3DCn5R+Brn8cYcxTCQkw2zMb:ZGwtjzOn3mr8emQk/Qb |
MALICIOUS
Application was dropped or rewritten from another process
- Telex Copy.exe (PID: 2404)
- DFGHJ.exe (PID: 3372)
- DFGHJ.exe (PID: 3448)
Writes to a start menu file
- cmd.exe (PID: 1444)
Changes the autorun value in the registry
- DFGHJ.exe (PID: 3372)
- DFGHJ.exe (PID: 3448)
Actions looks like stealing of personal data
- DFGHJ.exe (PID: 3448)
SUSPICIOUS
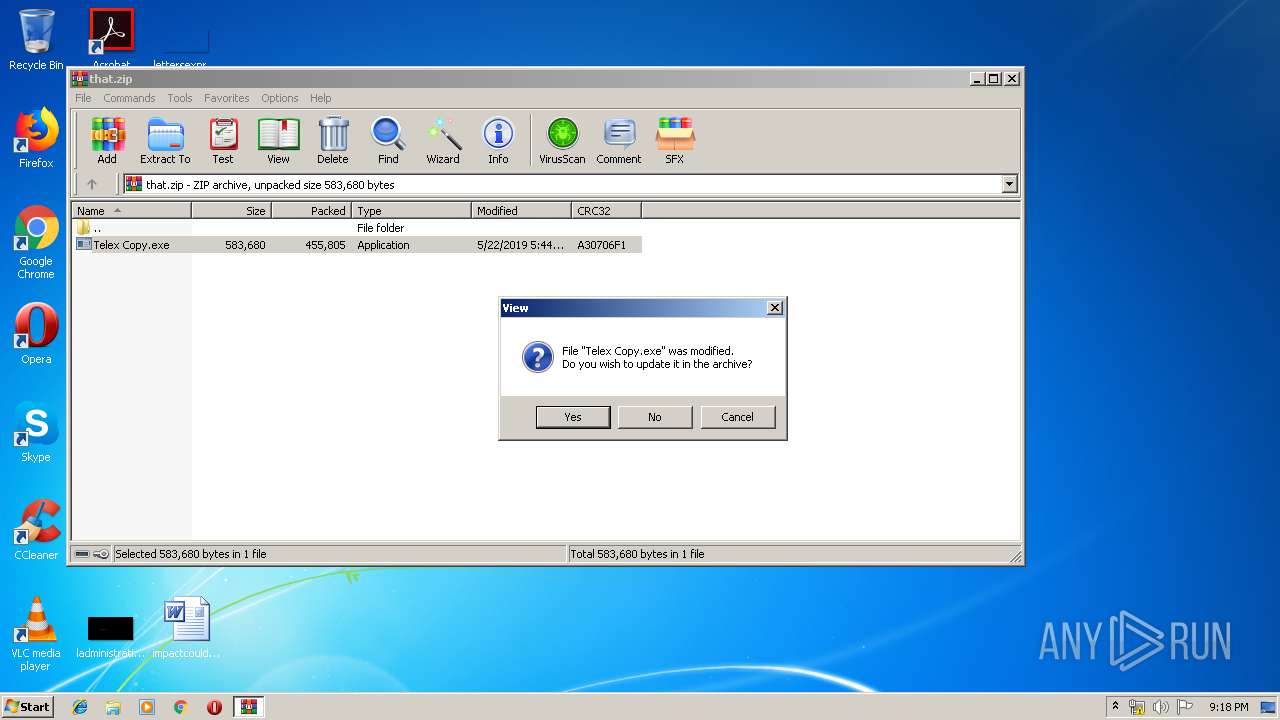
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3312)
- cmd.exe (PID: 1444)
- DFGHJ.exe (PID: 3448)
Starts CMD.EXE for commands execution
- Telex Copy.exe (PID: 2404)
- DFGHJ.exe (PID: 3372)
Creates files in the user directory
- cmd.exe (PID: 1444)
- DFGHJ.exe (PID: 3448)
Application launched itself
- DFGHJ.exe (PID: 3372)
Reads Windows Product ID
- DFGHJ.exe (PID: 3448)
Cleans NTFS data-stream (Zone Identifier)
- DFGHJ.exe (PID: 3448)
Reads Environment values
- DFGHJ.exe (PID: 3448)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3312)
- cmd.exe (PID: 1444)
- DFGHJ.exe (PID: 3448)
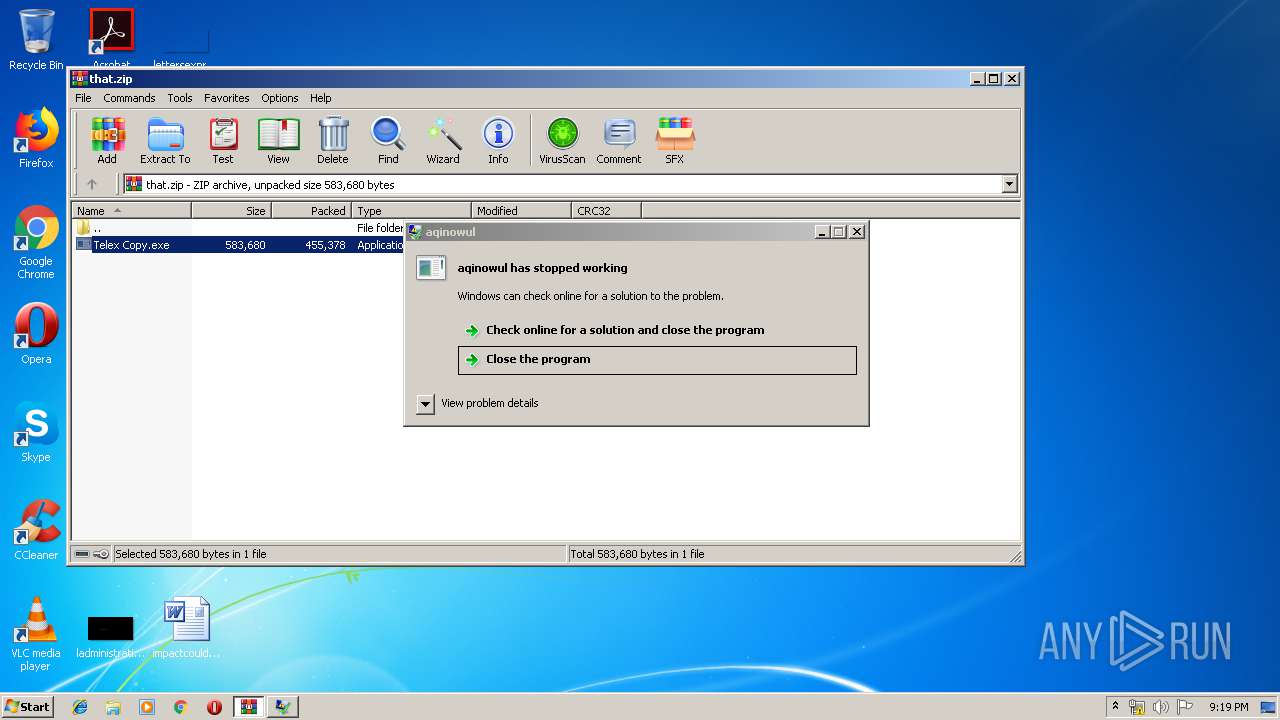
Application was crashed
- DFGHJ.exe (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:22 17:44:12 |
| ZipCRC: | 0xa30706f1 |
| ZipCompressedSize: | 455805 |
| ZipUncompressedSize: | 583680 |
| ZipFileName: | Telex Copy.exe |
Total processes
50
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.9927\Telex Copy.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | Telex Copy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1444 | "C:\Windows\System32\cmd.exe" /c copy "C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.9927\Telex Copy.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe" | C:\Windows\System32\cmd.exe | Telex Copy.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1532 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | DFGHJ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1820 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.9927\Telex Copy.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | Telex Copy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2404 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.9927\Telex Copy.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.9927\Telex Copy.exe | — | WinRAR.exe | |||||||||||
User: admin Company: ovumufeliqoxepetozuw Integrity Level: MEDIUM Description: aqinowul Exit code: 0 Version: 4.6.8.9 Modules
| |||||||||||||||
| 3244 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | DFGHJ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3312 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\that.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3372 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe | cmd.exe | ||||||||||||
User: admin Company: ovumufeliqoxepetozuw Integrity Level: MEDIUM Description: aqinowul Exit code: 3762504530 Version: 4.6.8.9 Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe | DFGHJ.exe | ||||||||||||
User: admin Company: ovumufeliqoxepetozuw Integrity Level: MEDIUM Description: aqinowul Exit code: 0 Version: 4.6.8.9 Modules
| |||||||||||||||
| 4028 | "C:\Windows\System32\cmd.exe" /c, "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe" | C:\Windows\System32\cmd.exe | — | Telex Copy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3762504530 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
734
Read events
705
Write events
29
Delete events
0
Modification events
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\that.zip | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3312) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rzi_3312.13538 | — | |
MD5:— | SHA256:— | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3312.9927\Telex Copy.exe | executable | |
MD5:— | SHA256:— | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\that.zip | compressed | |
MD5:— | SHA256:— | |||
| 1444 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\DFGHJ.exe | executable | |
MD5:— | SHA256:— | |||
| 3448 | DFGHJ.exe | C:\Users\admin\AppData\Local\Temp\636943295788262500_6a07240e-c132-45ab-957d-840d156f3c46.db | sqlite | |
MD5:— | SHA256:— | |||
| 3448 | DFGHJ.exe | C:\Users\admin\AppData\Roaming\NewApp\NewApp.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report