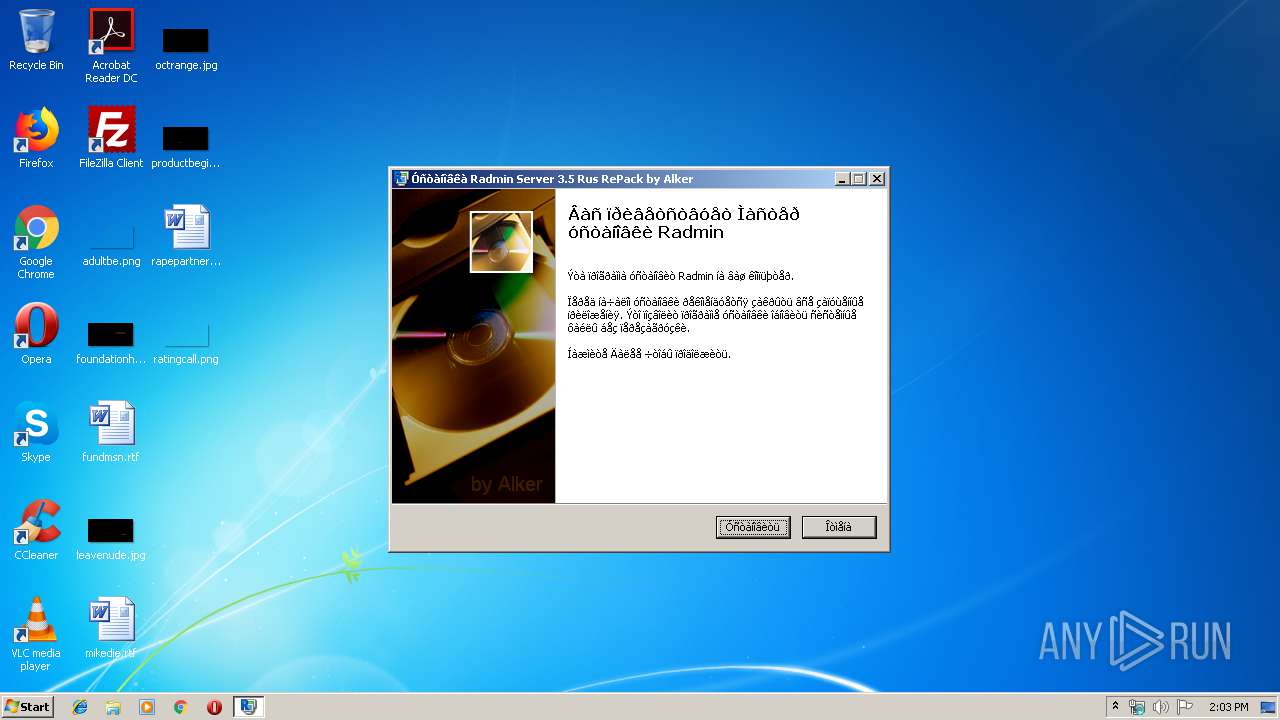
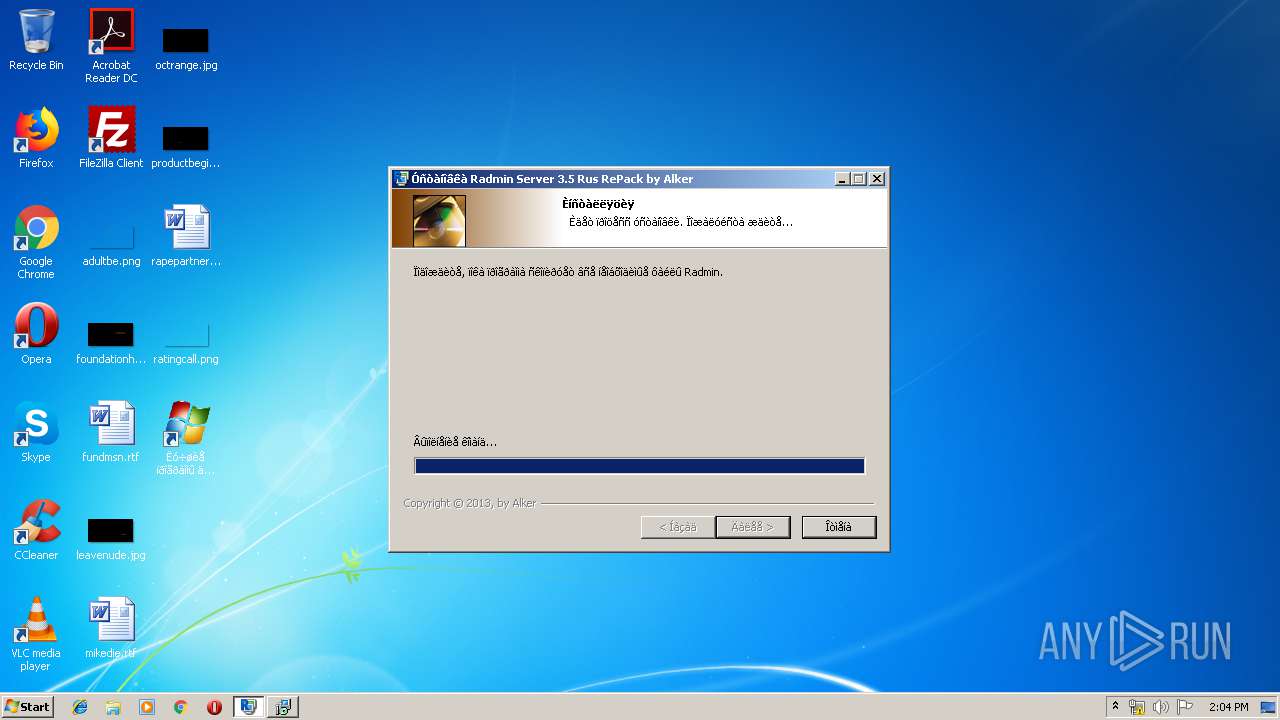
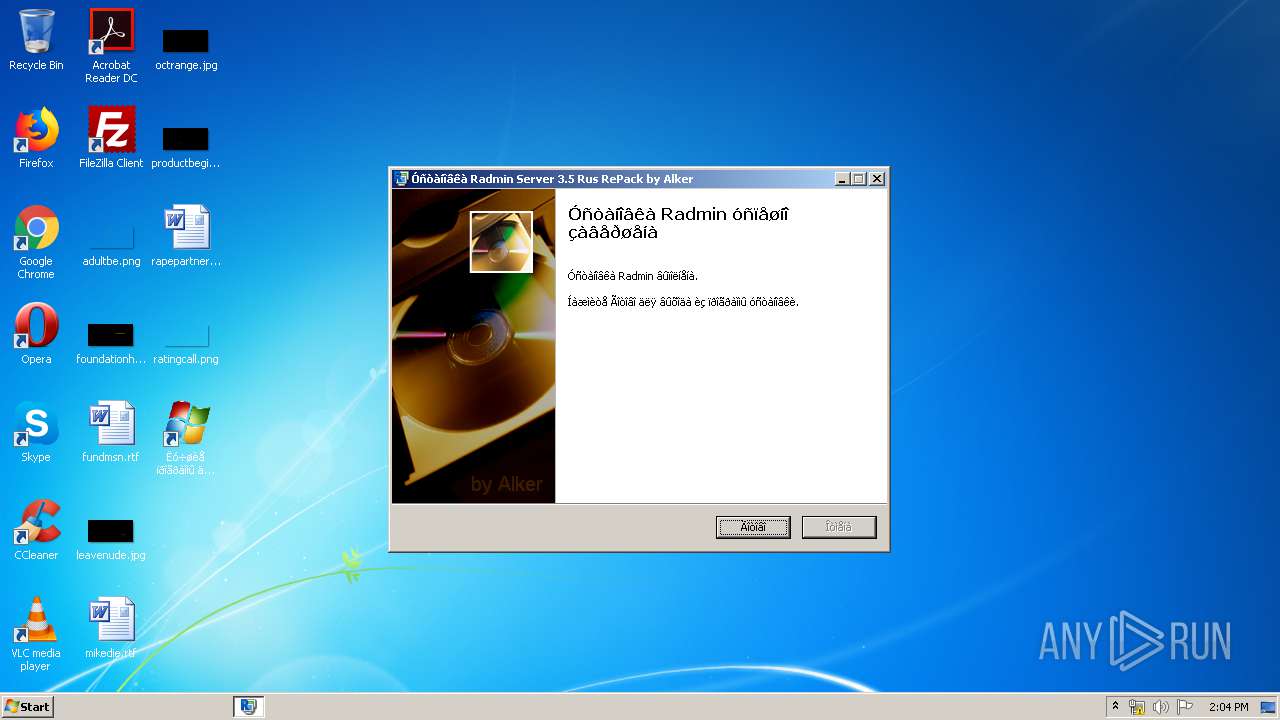
| File name: | Radmin Server 3.5 Rus RePack V3 by Alker .exe |
| Full analysis: | https://app.any.run/tasks/4f5f6418-d6a5-43d1-ab4f-4b18cdf66960 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 14:02:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F95BD8F18D6C6AB06CC9174AEFD897AE |
| SHA1: | B16ABE64CC5C2E60E97A60556EDABCB6BC0326F3 |
| SHA256: | 8539BF4BF6EA3E6D312EAAEB82D46F672E0CDC4EC49B5AEFFC43AC47F3AB63A5 |
| SSDEEP: | 98304:bXz+FBXH7zACtXfHgEtYx2eR5YW+8dwIwUKaRMu2at4jz0Sefr7aG2zAhaExCmM:LKFBX78CVgam2q5VdRpKI4JiHP2zMawI |
MALICIOUS
Application was dropped or rewritten from another process
- rsetup.exe (PID: 2840)
- rsetup.exe (PID: 1536)
- rsetup.exe (PID: 2556)
- RServer3.exe (PID: 1884)
- FamItrfc.Exe (PID: 2780)
- FamItrfc.Exe (PID: 2400)
Changes settings of System certificates
- rsetup.exe (PID: 1536)
Loads dropped or rewritten executable
- RServer3.exe (PID: 1884)
- FamItrfc.Exe (PID: 2780)
- FamItrfc.Exe (PID: 2400)
SUSPICIOUS
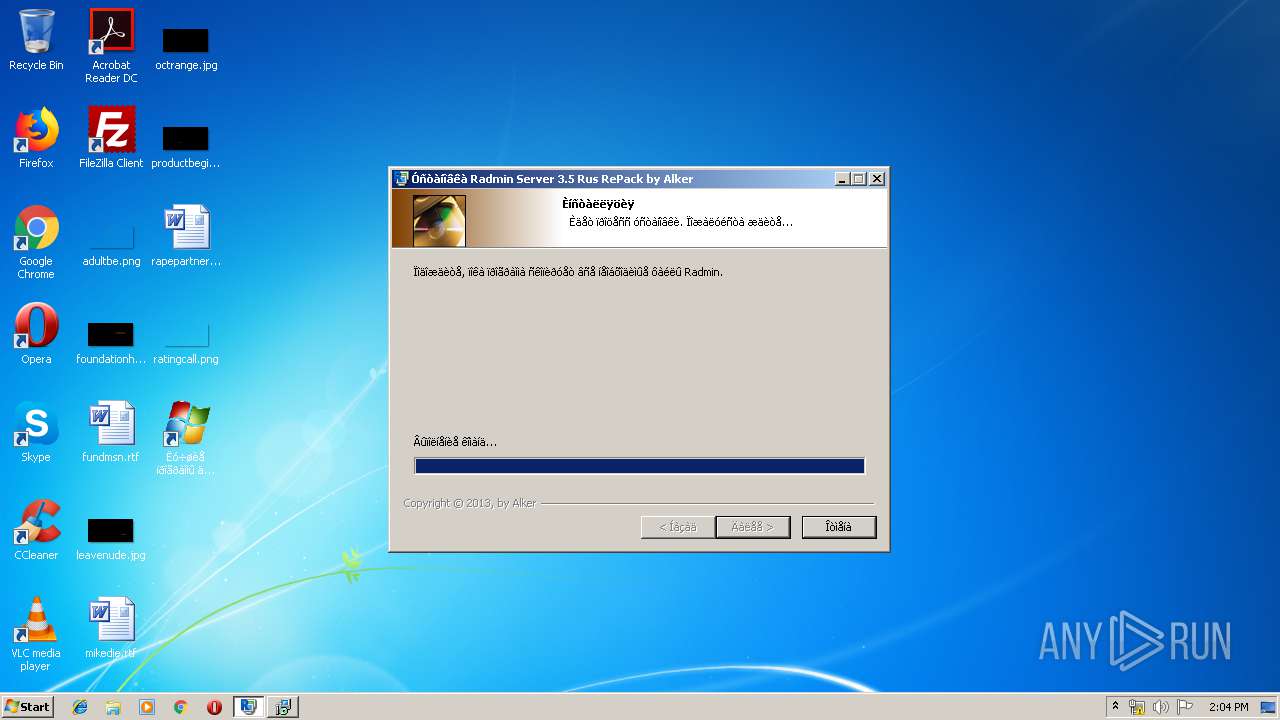
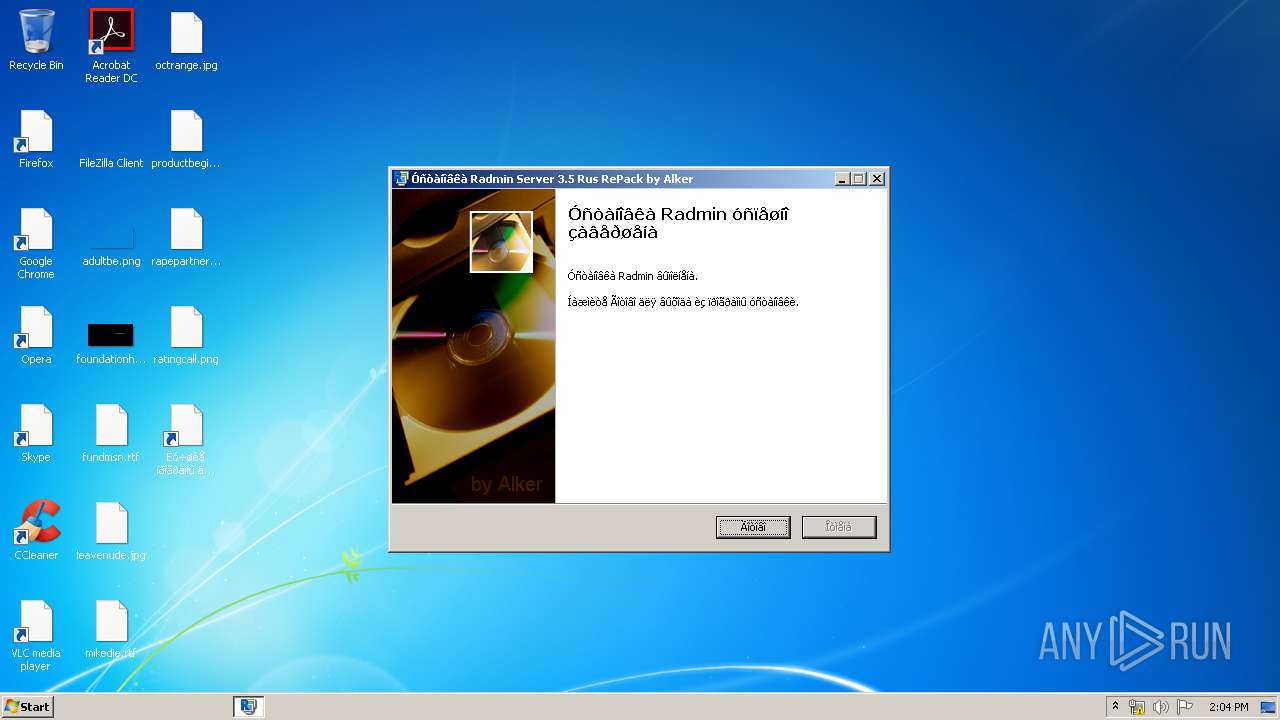
Creates a software uninstall entry
- Radmin Server 3.5 Rus RePack V3 by Alker .exe (PID: 3924)
Executed as Windows Service
- vssvc.exe (PID: 2968)
- RServer3.exe (PID: 1884)
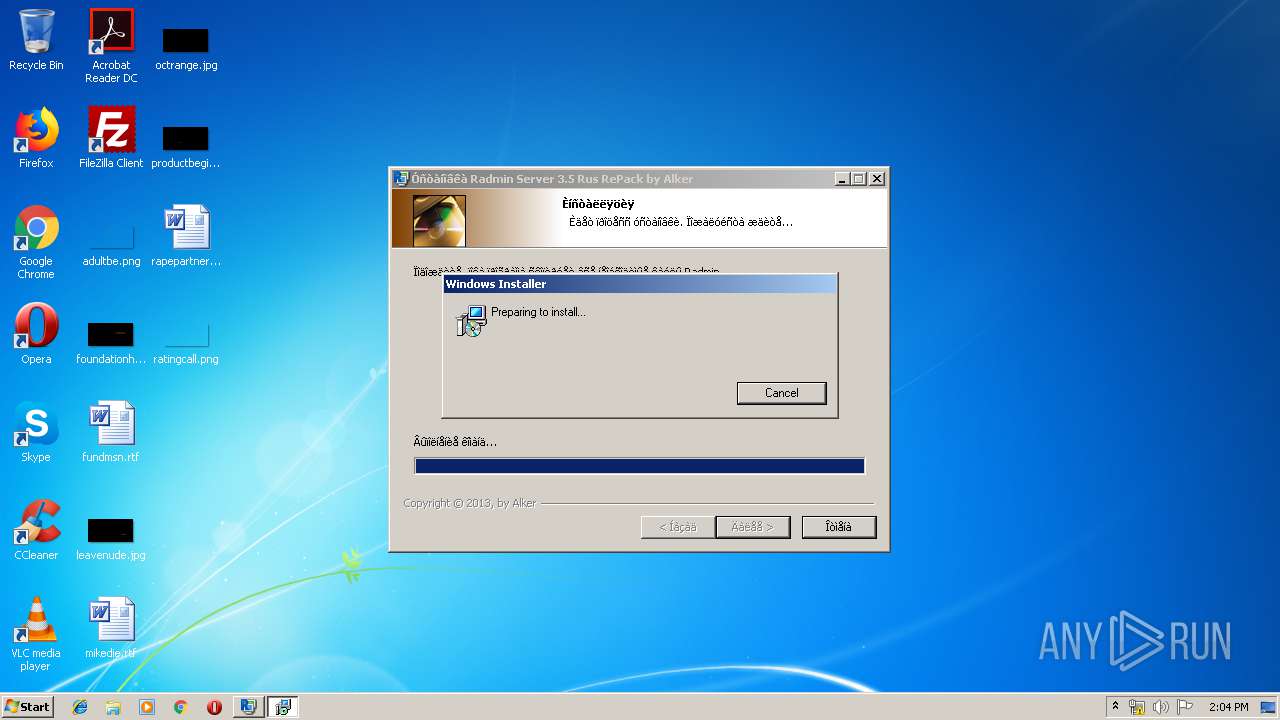
Starts Microsoft Installer
- Radmin Server 3.5 Rus RePack V3 by Alker .exe (PID: 3924)
Creates files in the program directory
- Radmin Server 3.5 Rus RePack V3 by Alker .exe (PID: 3924)
Executable content was dropped or overwritten
- Radmin Server 3.5 Rus RePack V3 by Alker .exe (PID: 3924)
- MsiExec.exe (PID: 2612)
- msiexec.exe (PID: 1780)
- rsetup.exe (PID: 1536)
- DrvInst.exe (PID: 1344)
- DrvInst.exe (PID: 3188)
Creates files in the Windows directory
- Radmin Server 3.5 Rus RePack V3 by Alker .exe (PID: 3924)
- msiexec.exe (PID: 1780)
- DrvInst.exe (PID: 1344)
- DrvInst.exe (PID: 3188)
- RServer3.exe (PID: 1884)
Creates files in the user directory
- msiexec.exe (PID: 1780)
Adds / modifies Windows certificates
- rsetup.exe (PID: 1536)
Executed via COM
- DrvInst.exe (PID: 1344)
- DrvInst.exe (PID: 3188)
- iexplore.exe (PID: 2284)
Removes files from Windows directory
- DrvInst.exe (PID: 3188)
- DrvInst.exe (PID: 1344)
Creates files in the driver directory
- DrvInst.exe (PID: 1344)
- DrvInst.exe (PID: 3188)
Uses NETSH.EXE for network configuration
- MsiExec.exe (PID: 2612)
Starts CMD.EXE for commands execution
- Radmin Server 3.5 Rus RePack V3 by Alker .exe (PID: 3924)
Application launched itself
- FamItrfc.Exe (PID: 2780)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2676)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2968)
Searches for installed software
- msiexec.exe (PID: 1780)
Application launched itself
- msiexec.exe (PID: 1780)
- iexplore.exe (PID: 2284)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2612)
Creates a software uninstall entry
- msiexec.exe (PID: 1780)
Reads Internet Cache Settings
- iexplore.exe (PID: 2644)
- iexplore.exe (PID: 2284)
Changes internet zones settings
- iexplore.exe (PID: 2284)
Reads internet explorer settings
- iexplore.exe (PID: 2644)
Creates files in the user directory
- iexplore.exe (PID: 2644)
- iexplore.exe (PID: 2284)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2644)
Reads settings of System Certificates
- iexplore.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (49.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (16.2) |
| .scr | | | Windows screen saver (14.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 52224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
| CompanyName: | Famatech Corp. |
| FileDescription: | Radmin 3.5 Installation |
| FileVersion: | 3.5 |
| LegalCopyright: | Famatech Corp. |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Famatech Corp. |
| FileDescription: | Radmin 3.5 Installation |
| FileVersion: | 3.5 |
| LegalCopyright: | Famatech Corp. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59438 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88549 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00006DD8 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.34257 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 3.25122 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.64635 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 4.16001 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 5.9217 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 3.84573 | 1640 | UNKNOWN | UNKNOWN | RT_ICON |
55 | 5.81414 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
56 | 5.33143 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
57 | 4.86658 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
58 | 4.72998 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
66
Monitored processes
19
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | netsh advfirewall firewall add rule name="Radmin Server 3" dir=in action=allow program="C:\Windows\system32\rserver30\rserver3.exe" enable=yes profile=any | C:\Windows\system32\netsh.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 976 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rserv35rus\rserv35ru.msi" /qb | C:\Windows\System32\msiexec.exe | — | Radmin Server 3.5 Rus RePack V3 by Alker .exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{5dac22b1-1a4f-3a68-a9dd-d97b424c140f}\mirrorv3.inf" "0" "60bbf019f" "000003C4" "WinSta0\Default" "0000052C" "208" "c:\windows\system32\rserver30" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | "C:\Windows\system32\rserver30\rsetup.exe" /intsetup | C:\Windows\system32\rserver30\rsetup.exe | MsiExec.exe | ||||||||||||
User: admin Company: Famatech Corp. Integrity Level: HIGH Description: Radmin Setup Helper Exit code: 1 Version: 3, 5, 0, 0 Modules
| |||||||||||||||
| 1780 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1884 | "C:\Windows\system32\rserver30\RServer3.exe" /service | C:\Windows\system32\rserver30\RServer3.exe | services.exe | ||||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin Server Exit code: 0 Version: 3, 5, 0, 0 Modules
| |||||||||||||||
| 2188 | REG ADD "HKLM\SOFTWARE\Radmin\v3.0\Server" /f /v "LicenseText" /t REG_SZ /d "A1KER special license" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Users\admin\AppData\Local\Temp\Radmin Server 3.5 Rus RePack V3 by Alker .exe" | C:\Users\admin\AppData\Local\Temp\Radmin Server 3.5 Rus RePack V3 by Alker .exe | — | explorer.exe | |||||||||||
User: admin Company: Famatech Corp. Integrity Level: MEDIUM Description: Radmin 3.5 Installation Exit code: 3221226540 Version: 3.5 Modules
| |||||||||||||||
| 2400 | "C:\Windows\system32\rserver30\FamItrfc.Exe" | C:\Windows\system32\rserver30\FamItrfc.Exe | — | FamItrfc.Exe | |||||||||||
User: admin Company: Famatech Corp. Integrity Level: MEDIUM Description: Radmin component Exit code: 0 Version: 3,4,0,1205 Modules
| |||||||||||||||
Total events
1 894
Read events
1 329
Write events
548
Delete events
17
Modification events
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Radmin\v3.0\Server |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Radmin\v3.0\Server |
| Operation: | write | Name: | LicenseText |
Value: A1KER special license | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Radmin\v3.0\Server |
| Operation: | write | Name: | HideTrayIcon |
Value: 0 | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Radmin\v3.0\Shared\Parameters |
| Operation: | write | Name: | AutoSelectLangId |
Value: 00000000 | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Radmin\v3.0\Shared\Parameters |
| Operation: | write | Name: | LangId |
Value: 19040000 | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall |
| Operation: | write | Name: | DisplayName |
Value: | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall |
| Operation: | write | Name: | DisplayVersion |
Value: 3.5 | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall |
| Operation: | write | Name: | VersionMajor |
Value: 3 | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall |
| Operation: | write | Name: | VersionMinor |
Value: 5 | |||
| (PID) Process: | (3924) Radmin Server 3.5 Rus RePack V3 by Alker .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall |
| Operation: | write | Name: | Publisher |
Value: Famatech Corp. | |||
Executable files
42
Suspicious files
27
Text files
177
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | Radmin Server 3.5 Rus RePack V3 by Alker .exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 3924 | Radmin Server 3.5 Rus RePack V3 by Alker .exe | C:\Users\admin\AppData\Local\Temp\Rserv35rus\rserv35ru.msi | — | |
MD5:— | SHA256:— | |||
| 1780 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1780 | msiexec.exe | C:\Windows\Installer\3af300.msi | — | |
MD5:— | SHA256:— | |||
| 1780 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabF449.tmp | — | |
MD5:— | SHA256:— | |||
| 1780 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarF44A.tmp | — | |
MD5:— | SHA256:— | |||
| 1780 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabF479.tmp | — | |
MD5:— | SHA256:— | |||
| 1780 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarF47A.tmp | — | |
MD5:— | SHA256:— | |||
| 1780 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabF585.tmp | — | |
MD5:— | SHA256:— | |||
| 1780 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarF586.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
42
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
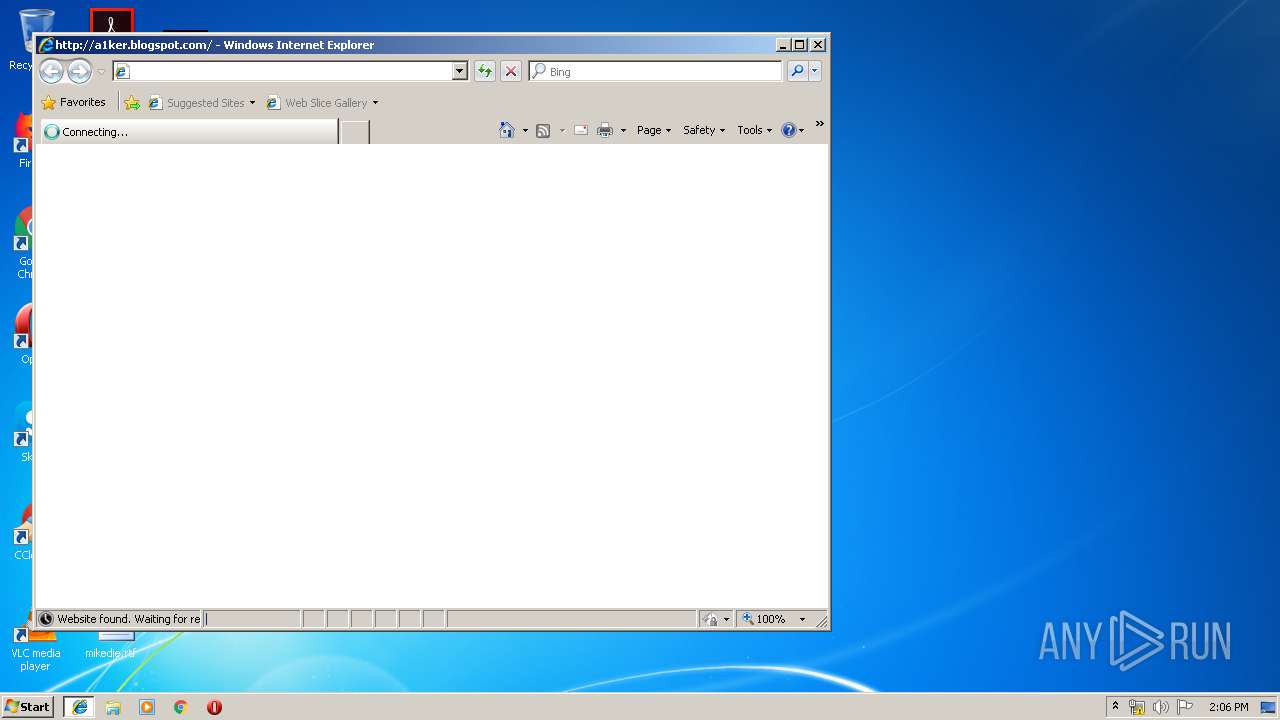
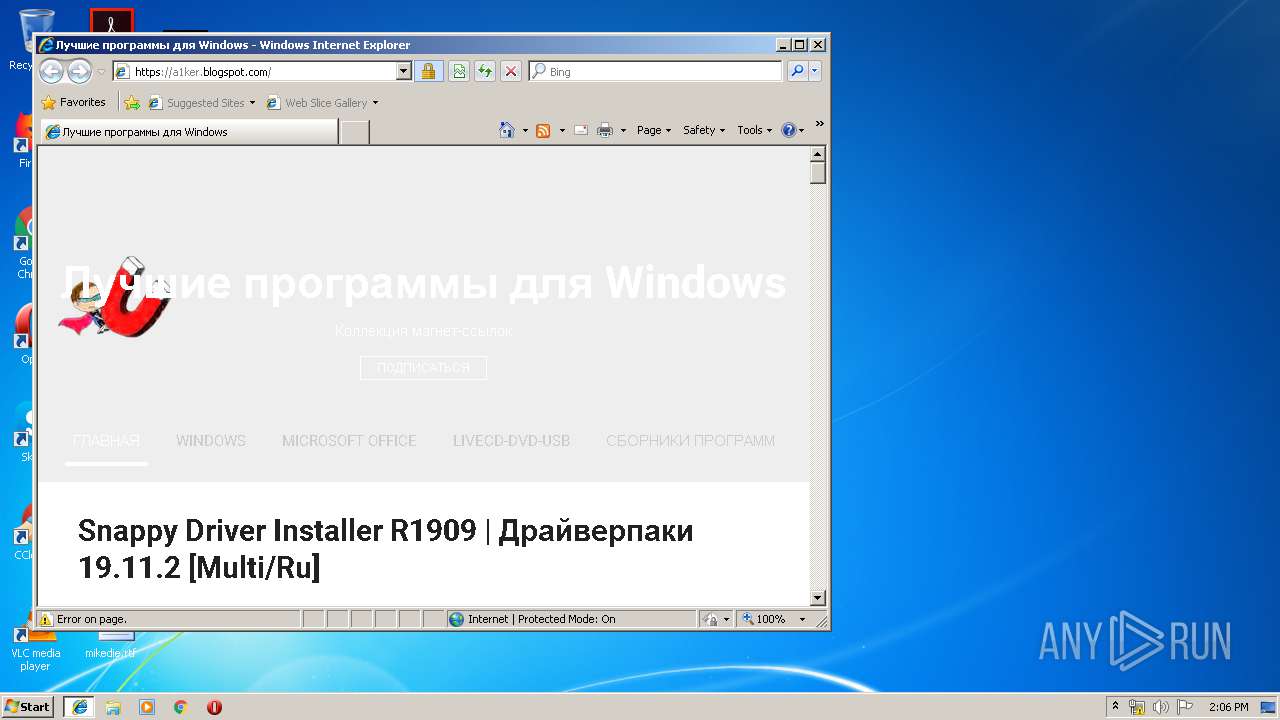
2644 | iexplore.exe | GET | 302 | 172.217.16.161:80 | http://a1ker.blogspot.ru/ | US | html | 175 b | whitelisted |
2284 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2644 | iexplore.exe | GET | 301 | 172.217.16.161:80 | http://a1ker.blogspot.com/ | US | html | 175 b | whitelisted |
1780 | msiexec.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2644 | iexplore.exe | 172.217.21.201:443 | www.blogger.com | Google Inc. | US | whitelisted |
2284 | iexplore.exe | 172.217.16.161:443 | a1ker.blogspot.ru | Google Inc. | US | whitelisted |
2284 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2644 | iexplore.exe | 172.217.16.161:80 | a1ker.blogspot.ru | Google Inc. | US | whitelisted |
1780 | msiexec.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2644 | iexplore.exe | 172.217.16.161:443 | a1ker.blogspot.ru | Google Inc. | US | whitelisted |
2644 | iexplore.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2644 | iexplore.exe | 172.217.21.193:443 | 4.bp.blogspot.com | Google Inc. | US | whitelisted |
2644 | iexplore.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2644 | iexplore.exe | 213.180.204.194:443 | translate.yandex.net | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
www.bing.com |
| whitelisted |
a1ker.blogspot.ru |
| whitelisted |
a1ker.blogspot.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
4.bp.blogspot.com |
| whitelisted |
1.bp.blogspot.com |
| whitelisted |
www.blogger.com |
| shared |
2.bp.blogspot.com |
| whitelisted |
Threats
Process | Message |
|---|---|
RServer3.exe | %n%n%n%n%n%n%n%n%n |