| File name: | QEQAppLocal.exe |
| Full analysis: | https://app.any.run/tasks/9cd5fdd6-176a-4bc4-a40a-e3c255851268 |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 17:16:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 37EA0110BE8156E0203D57A2F19FEE33 |
| SHA1: | CE3DB68D337D03FEE4EA5912D7C550A9E92541B2 |
| SHA256: | 853116F6C21DA769CFD8C6D54BC64098A67946C9107207226304EE0762B81A5A |
| SSDEEP: | 98304:wSr+JX+KUn5EAi7V/0cygMd2LC/tCOnF09788CP9GwJMLh2z3y1yroMKf3SQZmhV:nIzbZ5vcHgcqANEErWnz74x |
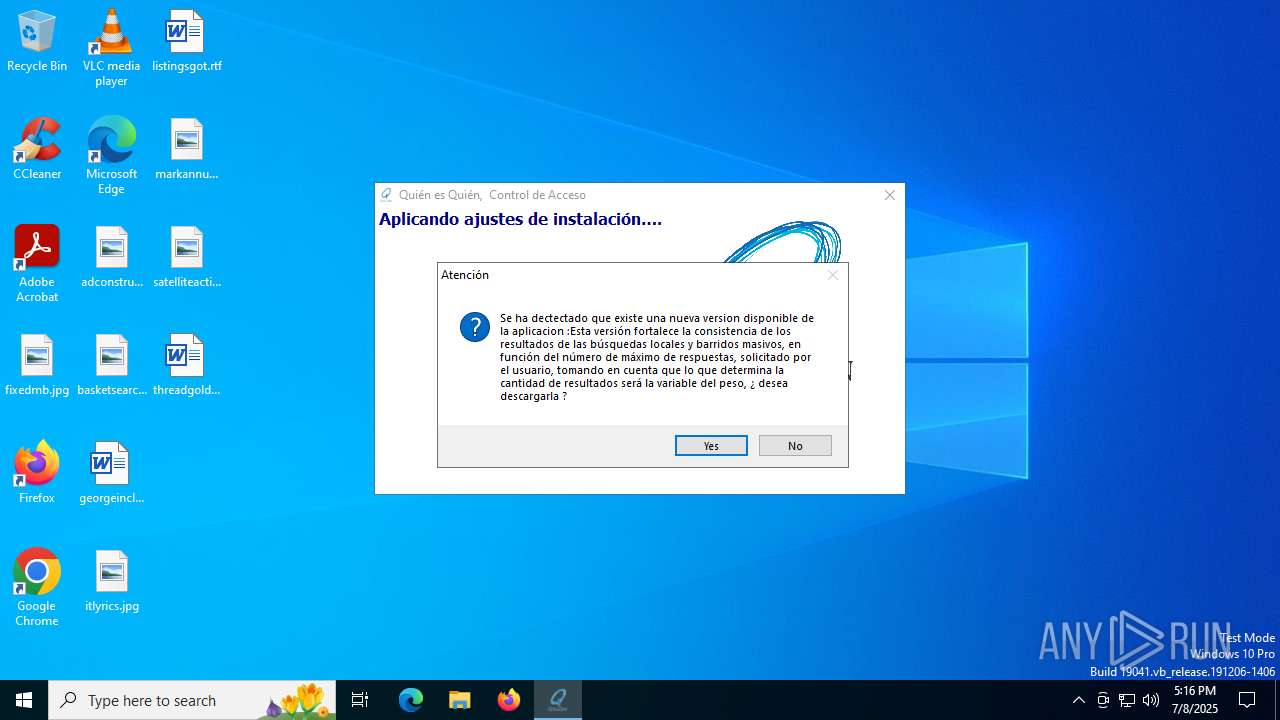
MALICIOUS
Starts NET.EXE for service management
- net.exe (PID: 5628)
- QEQAppLocal.tmp (PID: 3860)
SUSPICIOUS
Executable content was dropped or overwritten
- QEQAppLocal.exe (PID: 2972)
- QEQAppLocal.exe (PID: 2076)
- QEQAppLocal.tmp (PID: 3860)
Reads security settings of Internet Explorer
- QEQAppLocal.tmp (PID: 2780)
- PDownPepsMkt.exe (PID: 6256)
Reads the Windows owner or organization settings
- QEQAppLocal.tmp (PID: 3860)
Uses NETSH.EXE to add a firewall rule or allowed programs
- QEQAppLocal.tmp (PID: 3860)
Creates file in the systems drive root
- mysqld-nt.exe (PID: 1324)
Executes as Windows Service
- mysqld-nt.exe (PID: 1324)
Reads Microsoft Outlook installation path
- PDownPepsMkt.exe (PID: 6256)
Reads Internet Explorer settings
- PDownPepsMkt.exe (PID: 6256)
INFO
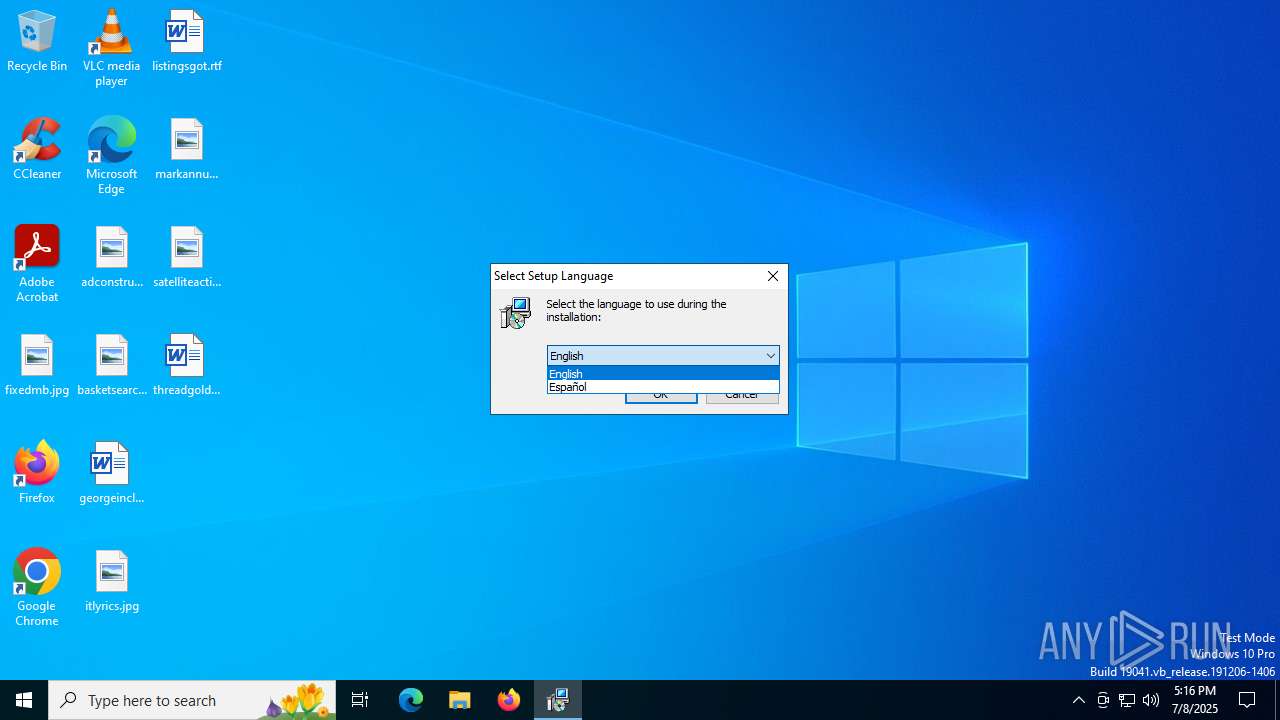
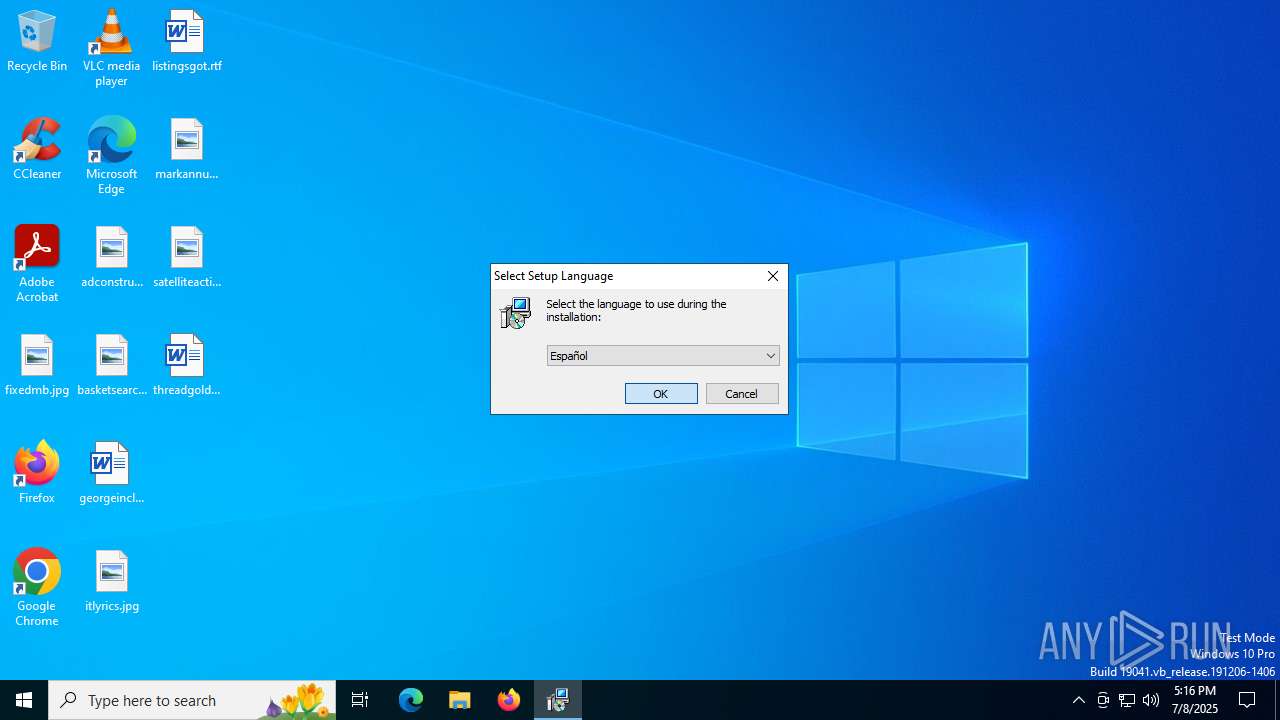
Checks supported languages
- QEQAppLocal.exe (PID: 2972)
- QEQAppLocal.tmp (PID: 2780)
- QEQAppLocal.exe (PID: 2076)
- QEQAppLocal.tmp (PID: 3860)
- mysqld-nt.exe (PID: 4576)
- mysqld-nt.exe (PID: 1324)
- PDownPepsMkt.exe (PID: 6256)
Create files in a temporary directory
- QEQAppLocal.exe (PID: 2972)
- QEQAppLocal.exe (PID: 2076)
- QEQAppLocal.tmp (PID: 3860)
Reads the computer name
- QEQAppLocal.tmp (PID: 2780)
- QEQAppLocal.tmp (PID: 3860)
- mysqld-nt.exe (PID: 4576)
- mysqld-nt.exe (PID: 1324)
- PDownPepsMkt.exe (PID: 6256)
Process checks computer location settings
- QEQAppLocal.tmp (PID: 2780)
Detects InnoSetup installer (YARA)
- QEQAppLocal.exe (PID: 2972)
- QEQAppLocal.tmp (PID: 2780)
- QEQAppLocal.tmp (PID: 3860)
- QEQAppLocal.exe (PID: 2076)
Compiled with Borland Delphi (YARA)
- QEQAppLocal.tmp (PID: 2780)
- QEQAppLocal.tmp (PID: 3860)
The sample compiled with english language support
- QEQAppLocal.tmp (PID: 3860)
The sample compiled with portuguese language support
- QEQAppLocal.tmp (PID: 3860)
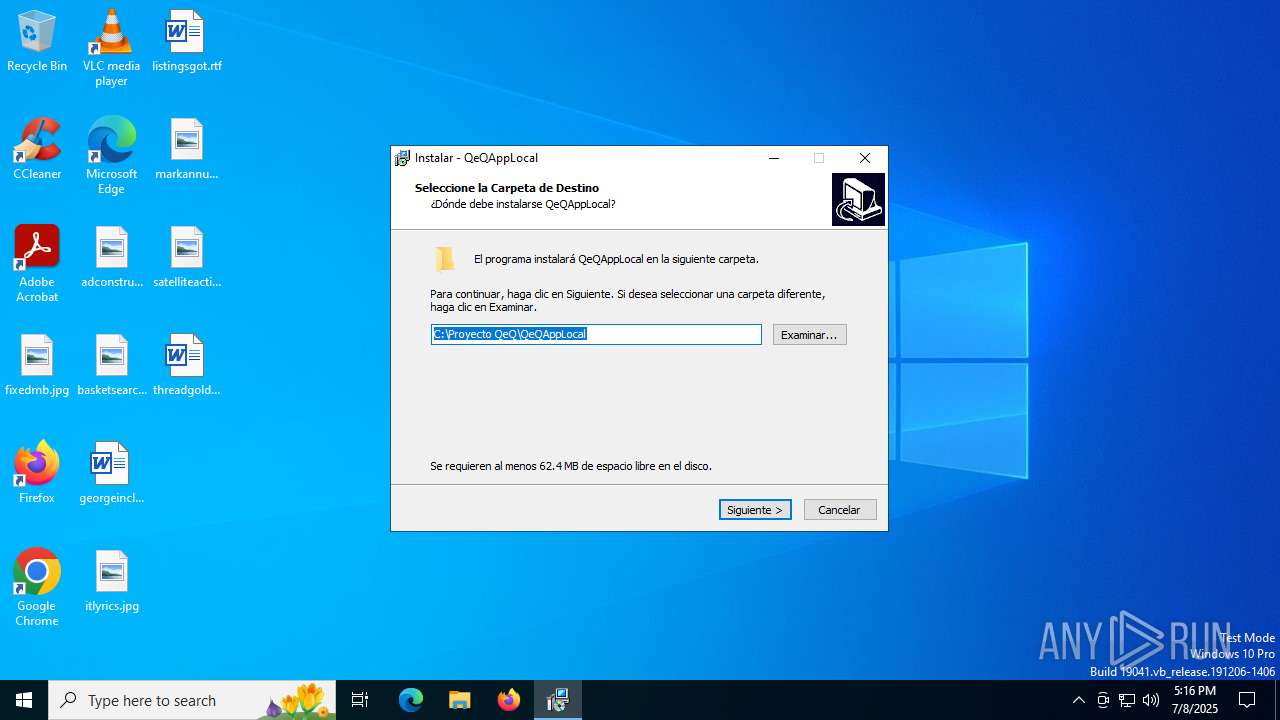
Creates files in the program directory
- QEQAppLocal.tmp (PID: 3860)
Creates a software uninstall entry
- QEQAppLocal.tmp (PID: 3860)
Creates files or folders in the user directory
- PDownPepsMkt.exe (PID: 6256)
Checks proxy server information
- PDownPepsMkt.exe (PID: 6256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Cyberfish |
| FileDescription: | QeQAppLocal Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | QeQAppLocal |
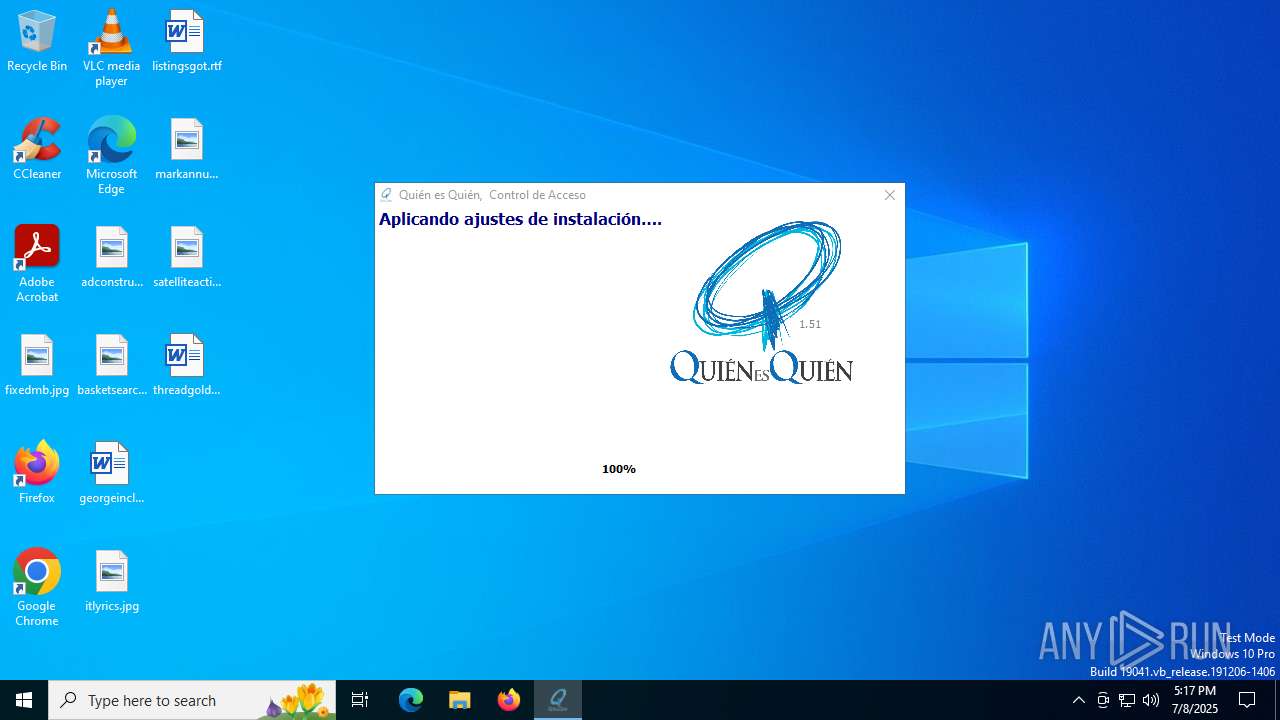
| ProductVersion: | 1.5 |
Total processes
154
Monitored processes
18
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\mysql\bin\mysqld-nt.exe MySQL | C:\mysql\bin\mysqld-nt.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Modules
| |||||||||||||||
| 1524 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | mysqld-nt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Local\Temp\QEQAppLocal.exe" /SPAWNWND=$8023C /NOTIFYWND=$70374 | C:\Users\admin\AppData\Local\Temp\QEQAppLocal.exe | QEQAppLocal.tmp | ||||||||||||
User: admin Company: Cyberfish Integrity Level: HIGH Description: QeQAppLocal Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\AppData\Local\Temp\is-66USP.tmp\QEQAppLocal.tmp" /SL5="$70374,14049967,57856,C:\Users\admin\AppData\Local\Temp\QEQAppLocal.exe" | C:\Users\admin\AppData\Local\Temp\is-66USP.tmp\QEQAppLocal.tmp | — | QEQAppLocal.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2972 | "C:\Users\admin\AppData\Local\Temp\QEQAppLocal.exe" | C:\Users\admin\AppData\Local\Temp\QEQAppLocal.exe | — | explorer.exe | |||||||||||
User: admin Company: Cyberfish Integrity Level: MEDIUM Description: QeQAppLocal Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3000 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3860 | "C:\Users\admin\AppData\Local\Temp\is-NAO96.tmp\QEQAppLocal.tmp" /SL5="$1202BA,14049967,57856,C:\Users\admin\AppData\Local\Temp\QEQAppLocal.exe" /SPAWNWND=$8023C /NOTIFYWND=$70374 | C:\Users\admin\AppData\Local\Temp\is-NAO96.tmp\QEQAppLocal.tmp | — | QEQAppLocal.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
3 011
Read events
2 982
Write events
29
Delete events
0
Modification events
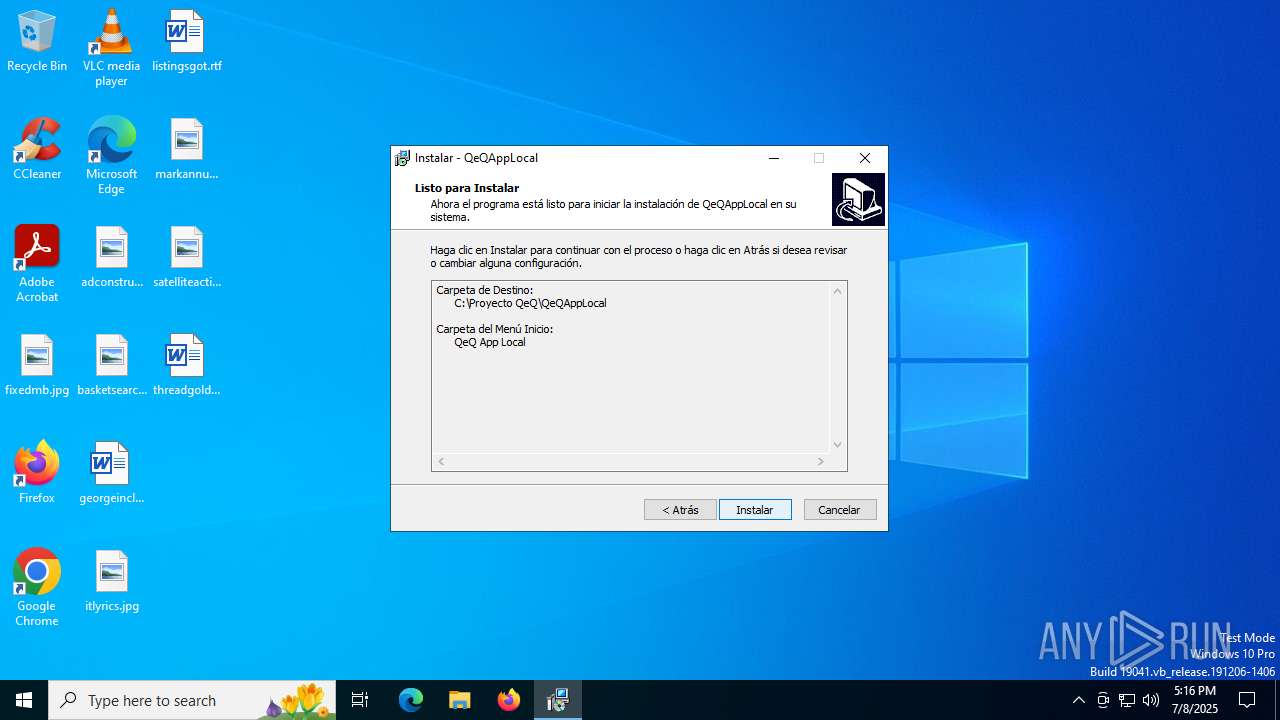
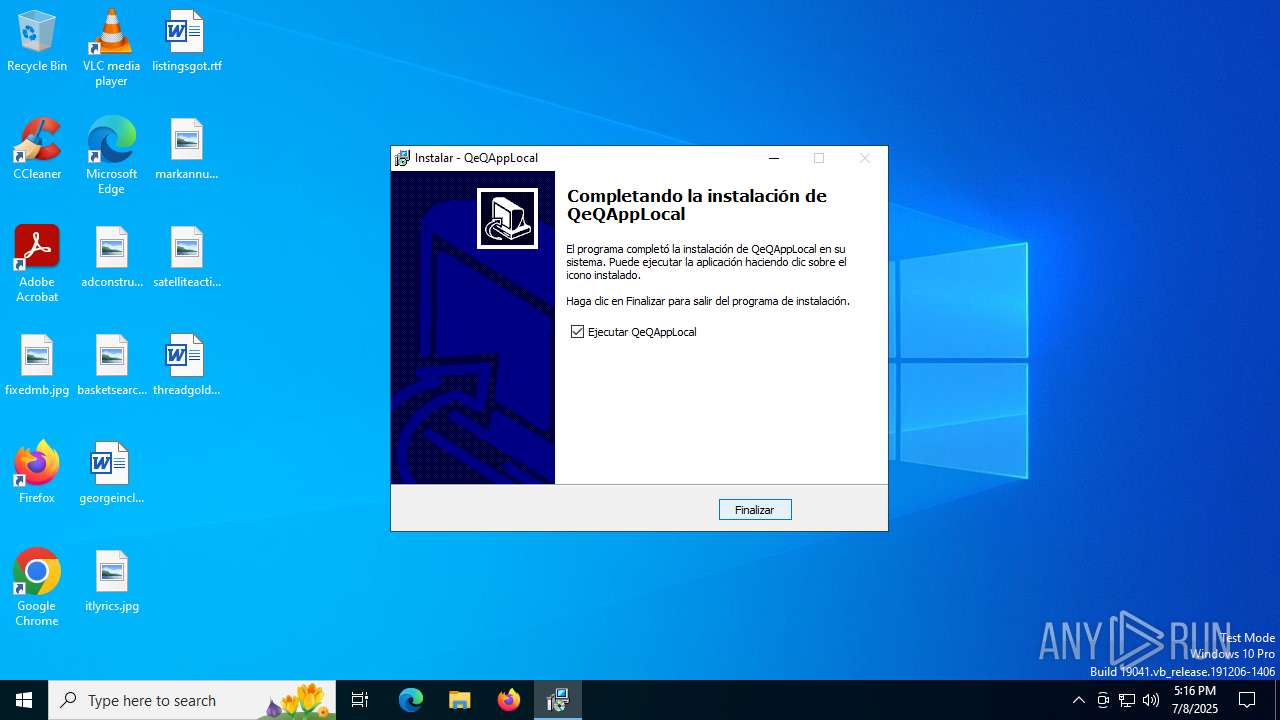
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (a) | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Proyecto QeQ\QeQAppLocal | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Proyecto QeQ\QeQAppLocal\ | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: QeQ App Local | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
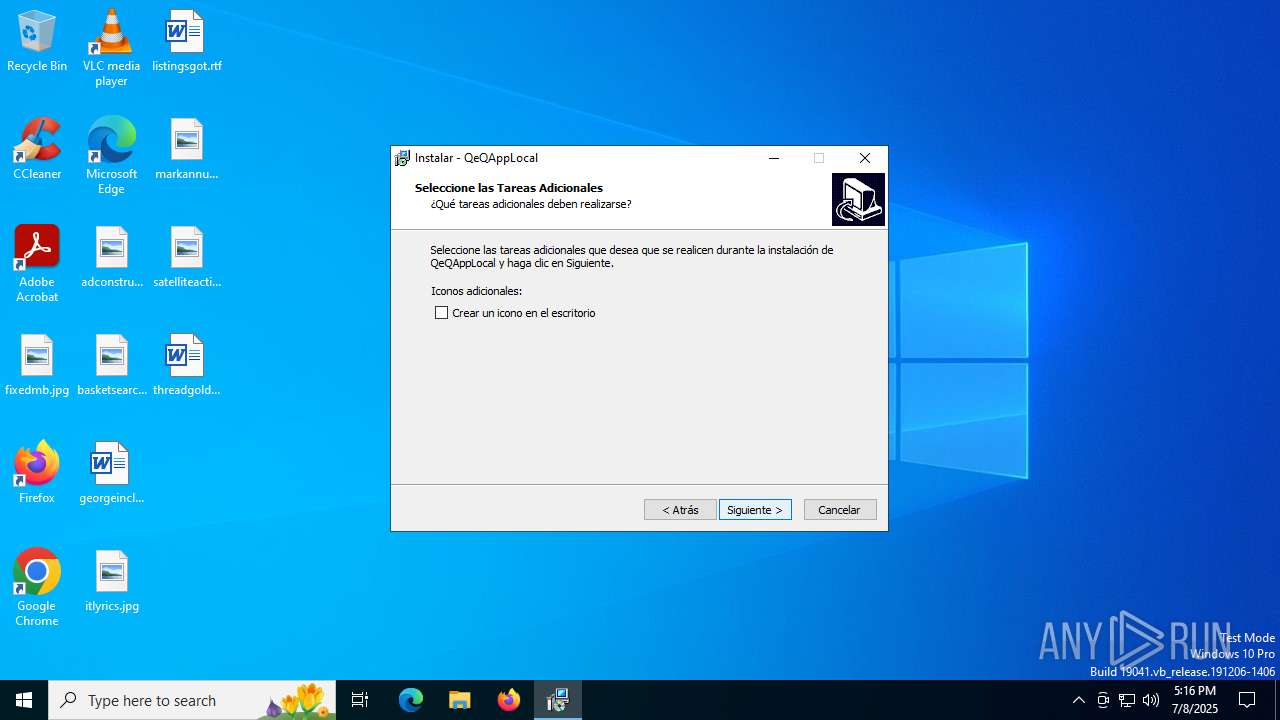
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: desktopicon | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: spanish | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | DisplayName |
Value: QeQAppLocal versión 1.5 | |||
| (PID) Process: | (3860) QEQAppLocal.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{254F2425-B3EF-4650-9354-B8A2B18F8680}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Proyecto QeQ\QeQAppLocal\unins000.exe" | |||
Executable files
25
Suspicious files
64
Text files
73
Unknown types
84
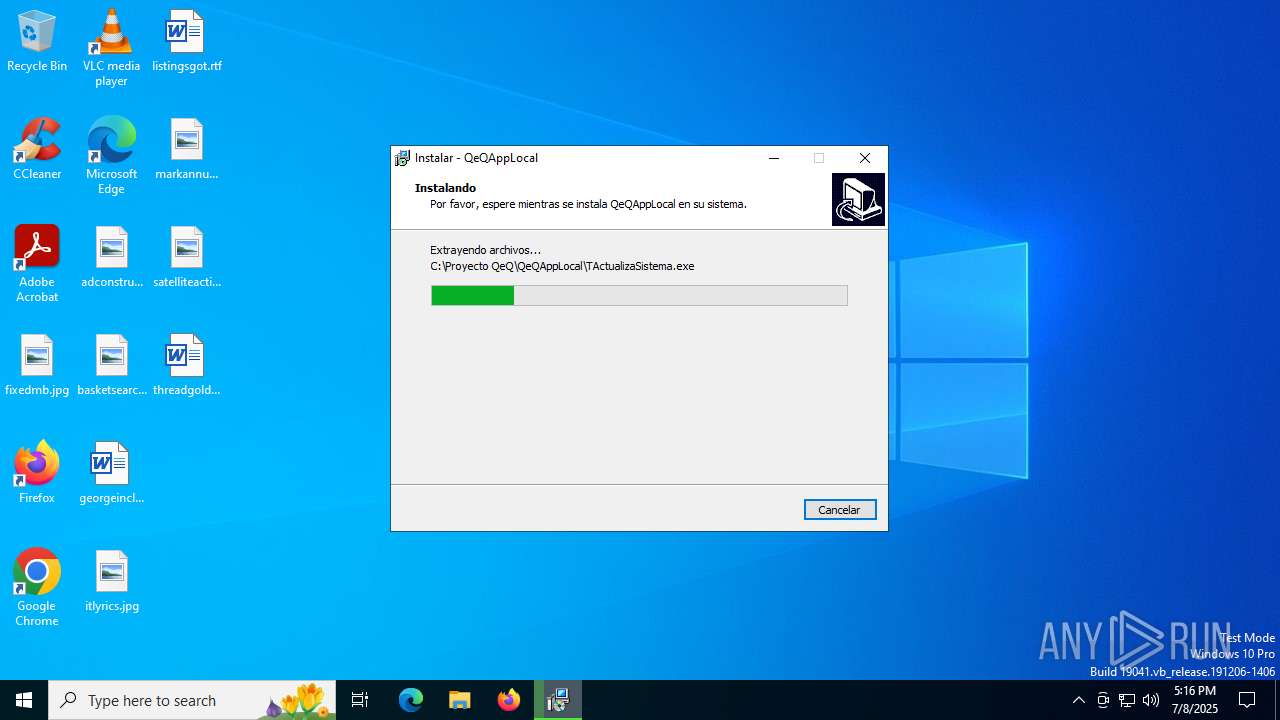
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | QEQAppLocal.exe | C:\Users\admin\AppData\Local\Temp\is-66USP.tmp\QEQAppLocal.tmp | executable | |
MD5:832DAB307E54AA08F4B6CDD9B9720361 | SHA256:CC783A04CCBCA4EDD06564F8EC88FE5A15F1E3BB26CEC7DE5E090313520D98F3 | |||
| 3860 | QEQAppLocal.tmp | C:\Proyecto QeQ\QeQAppLocal\is-KMB4A.tmp | image | |
MD5:B5F7F2914A7E7266641BA6727E39F749 | SHA256:92FCAF10F58821F8FEE0B9E729B8D5A29313640D73A00AEFB8DDB7713A91A552 | |||
| 3860 | QEQAppLocal.tmp | C:\Users\admin\AppData\Local\Temp\is-KRCGJ.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 3860 | QEQAppLocal.tmp | C:\Proyecto QeQ\QeQAppLocal\is-SHKEC.tmp | executable | |
MD5:49C61652B91FD630B8CA098AD4209786 | SHA256:BCF31604FEF4A2EA0444782A72B5880F0FC5FCB188F21040DB4711FD5B8871D3 | |||
| 3860 | QEQAppLocal.tmp | C:\Proyecto QeQ\QeQAppLocal\unins000.exe | executable | |
MD5:49C61652B91FD630B8CA098AD4209786 | SHA256:BCF31604FEF4A2EA0444782A72B5880F0FC5FCB188F21040DB4711FD5B8871D3 | |||
| 3860 | QEQAppLocal.tmp | C:\Proyecto QeQ\QeQAppLocal\is-N9B10.tmp | executable | |
MD5:02CCC9D77BB706B11106943064D5995E | SHA256:C365F452BEECEEC34F892E88F9A080B9BC565CB45AC89E667E8FE996B4D670CF | |||
| 3860 | QEQAppLocal.tmp | C:\Proyecto QeQ\QeQAppLocal\dbxdrivers.ini | ini | |
MD5:0815FB38505DC1985A63CB8D3B8A3B50 | SHA256:3154117F76BC8DDD6D9036CB438B18FE2B56A5D97DBB2B5CE9D1E39C305987B7 | |||
| 3860 | QEQAppLocal.tmp | C:\Proyecto QeQ\QeQAppLocal\TActualizaSistema.exe | executable | |
MD5:02CCC9D77BB706B11106943064D5995E | SHA256:C365F452BEECEEC34F892E88F9A080B9BC565CB45AC89E667E8FE996B4D670CF | |||
| 3860 | QEQAppLocal.tmp | C:\Proyecto QeQ\QeQAppLocal\is-51FI4.tmp | compressed | |
MD5:4C65106871B5DB741C1AA37466F379F2 | SHA256:D86DF9A42E9CB97E8A7D49EFCEF93C6657B0DD52489B59F990606ABE9F6A413D | |||
| 3860 | QEQAppLocal.tmp | C:\Proyecto QeQ\QeQAppLocal\is-6QK54.tmp | text | |
MD5:0A890043F6B7319DC36072480AA543DB | SHA256:36C10E7234D27D6898D47DE620C3B96B4F651551966FBA82451904609B978419 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
26
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6320 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3944 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3944 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6256 | PDownPepsMkt.exe | GET | 200 | 142.250.185.238:80 | http://maps.google.com/maps/api/js?sensor=true | unknown | — | — | whitelisted |
6256 | PDownPepsMkt.exe | GET | 200 | 3.224.119.20:80 | http://www.qeq.mx/datos/xport/QeQCryptU.zip | unknown | — | — | unknown |
6256 | PDownPepsMkt.exe | GET | 200 | 3.224.119.20:80 | http://qeq.mx/datos/qws/qsis?var1=usis&var2=qsis&tipo=1&campo=id&cond=1 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6788 | RUXIMICS.exe | 52.185.211.133:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6320 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6320 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |