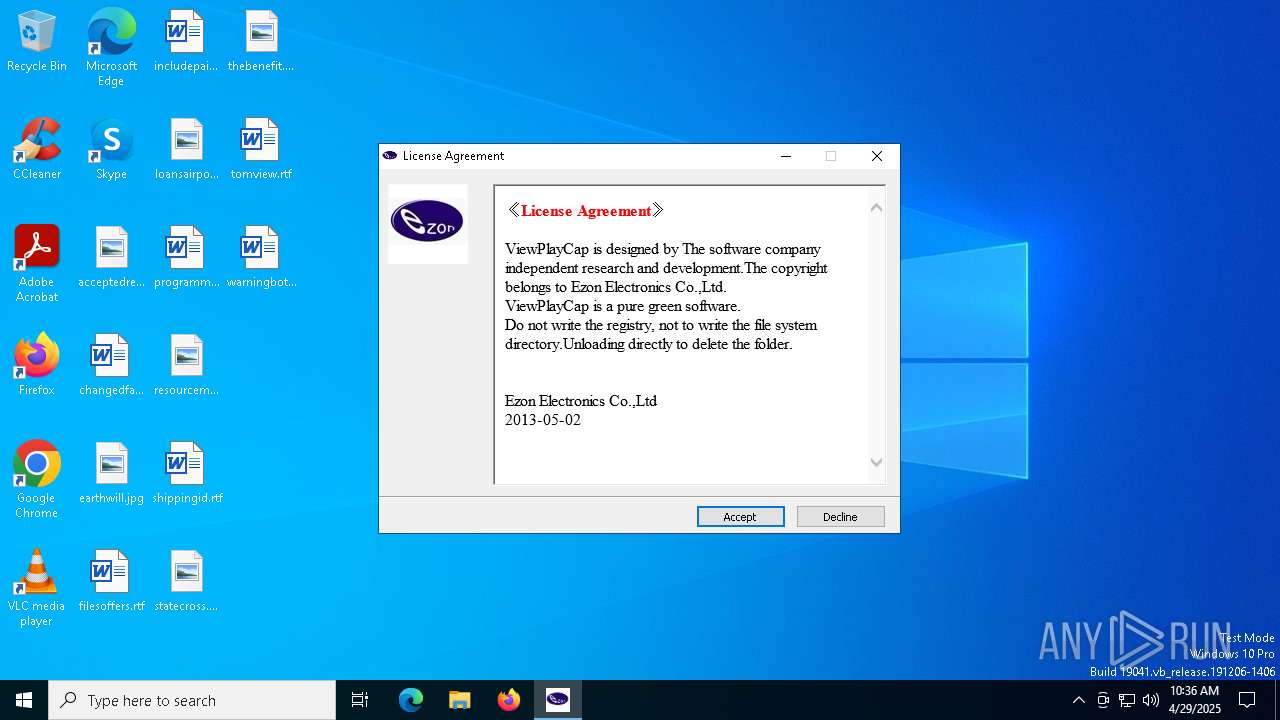
| File name: | ViewPlay.exe |
| Full analysis: | https://app.any.run/tasks/ff6eaf0a-1c41-4292-8c35-6732492535bb |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 10:36:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive, 5 sections |
| MD5: | BCDD8DA242AC5BE6D2A7D86A13BE812F |
| SHA1: | 8F516DEC702165E3EB2182C6D78702C893E7EC66 |
| SHA256: | 85309B4A5739A95743A0DB87A17A9458F14D84AB2CCE2EE46FFD0C63C6E1DE7F |
| SSDEEP: | 49152:Z6SUk/6KkQaQFl7vw7x/Y5WZFPiALcjVKrN5VVnv:Ut8kQa60/JPiALcjVKZ5Hv |
MALICIOUS
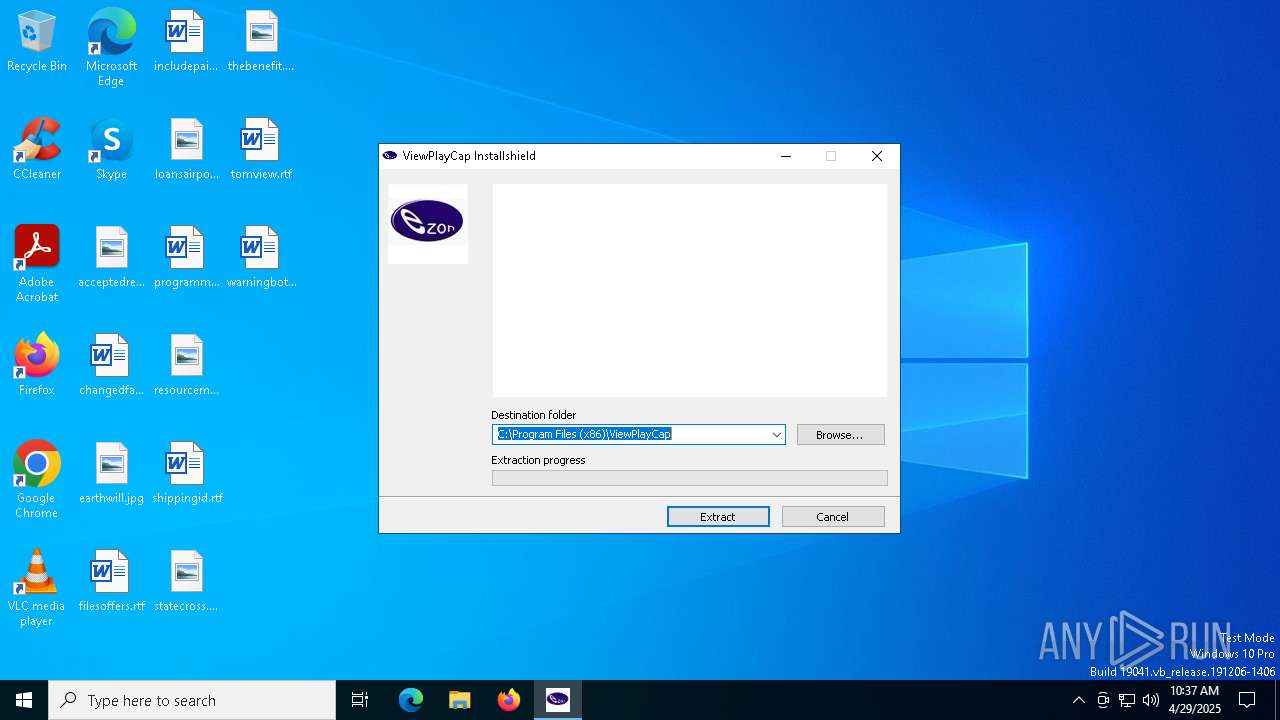
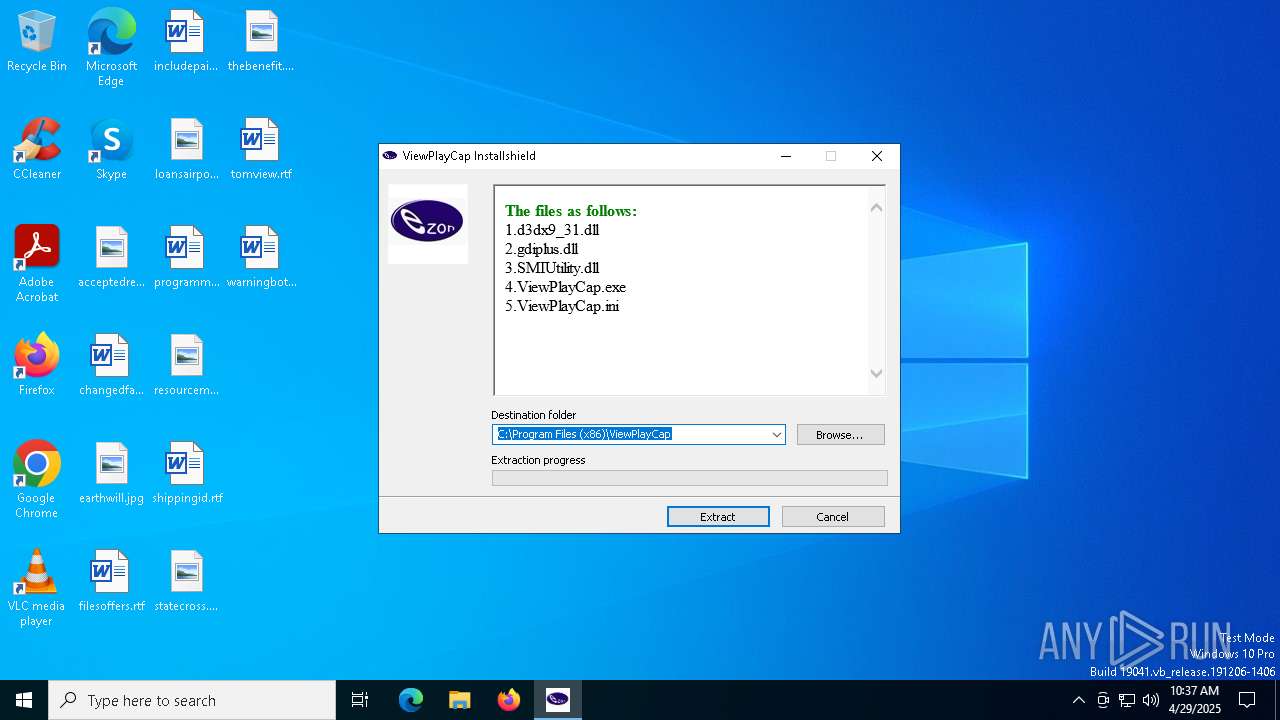
SFX dropper has been detected
- ViewPlay.exe (PID: 6640)
SUSPICIOUS
Reads Microsoft Outlook installation path
- ViewPlay.exe (PID: 6640)
Reads security settings of Internet Explorer
- ViewPlay.exe (PID: 6640)
There is functionality for taking screenshot (YARA)
- ViewPlay.exe (PID: 6640)
Reads Internet Explorer settings
- ViewPlay.exe (PID: 6640)
Application launched itself
- ViewPlay.exe (PID: 6640)
Process drops legitimate windows executable
- ViewPlay.exe (PID: 680)
Executable content was dropped or overwritten
- ViewPlay.exe (PID: 680)
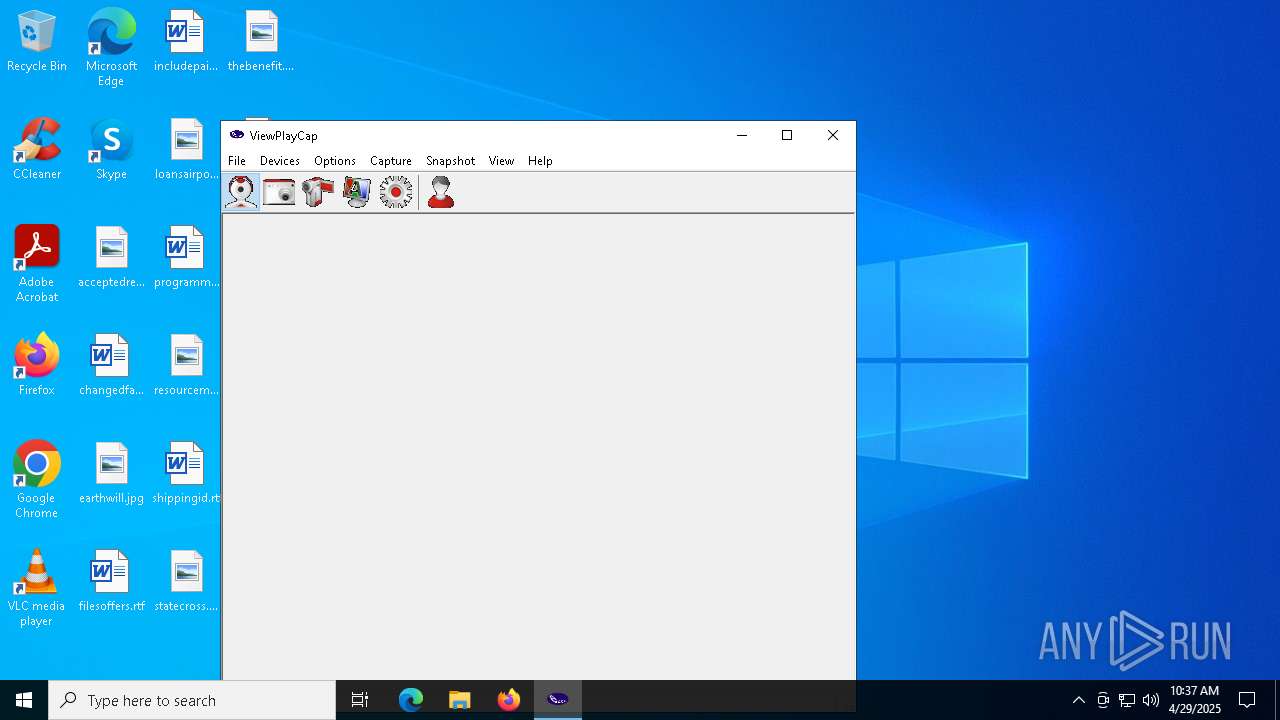
Executes application which crashes
- ViewPlayCap.exe (PID: 1660)
INFO
Checks supported languages
- ViewPlay.exe (PID: 6640)
- ViewPlay.exe (PID: 680)
- ViewPlayCap.exe (PID: 1660)
- ViewPlayCap.exe (PID: 1164)
Checks proxy server information
- ViewPlay.exe (PID: 6640)
Reads the computer name
- ViewPlay.exe (PID: 6640)
- ViewPlay.exe (PID: 680)
- ViewPlayCap.exe (PID: 1164)
- ViewPlayCap.exe (PID: 1660)
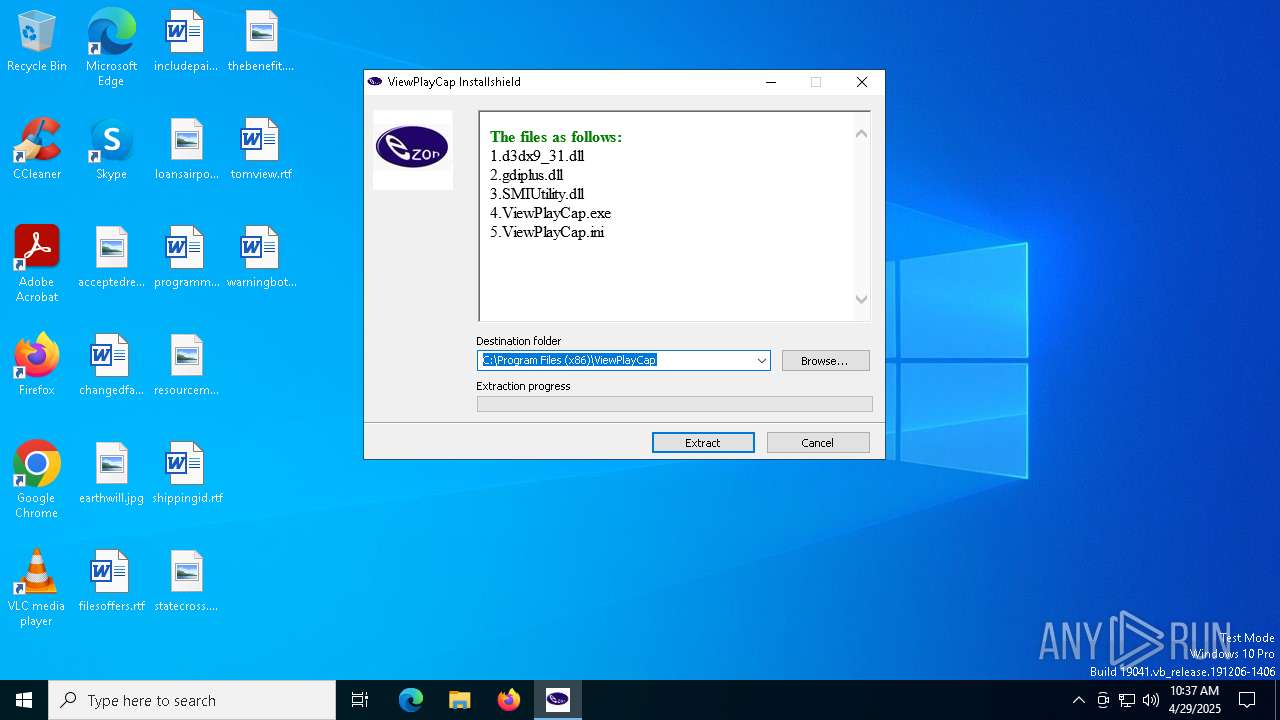
Creates files in the program directory
- ViewPlay.exe (PID: 680)
The sample compiled with english language support
- ViewPlay.exe (PID: 680)
Process checks computer location settings
- ViewPlay.exe (PID: 6640)
The sample compiled with chinese language support
- ViewPlay.exe (PID: 680)
Creates files or folders in the user directory
- ViewPlay.exe (PID: 680)
- WerFault.exe (PID: 208)
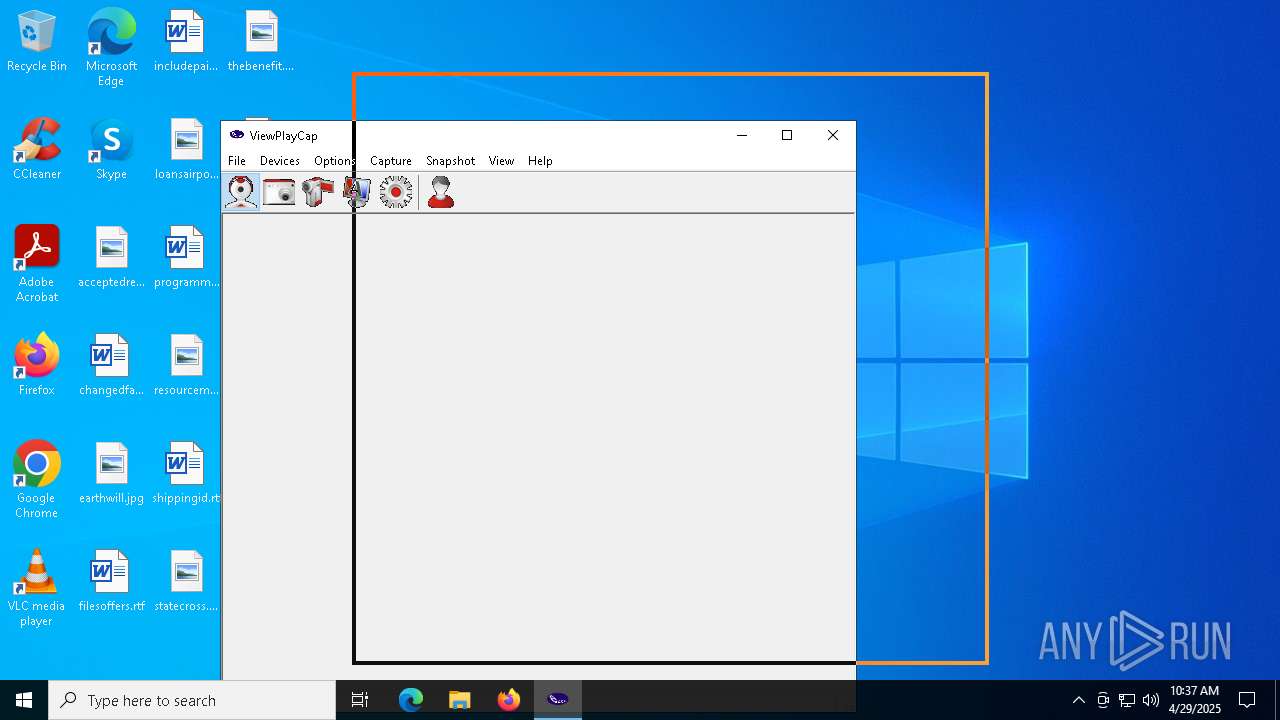
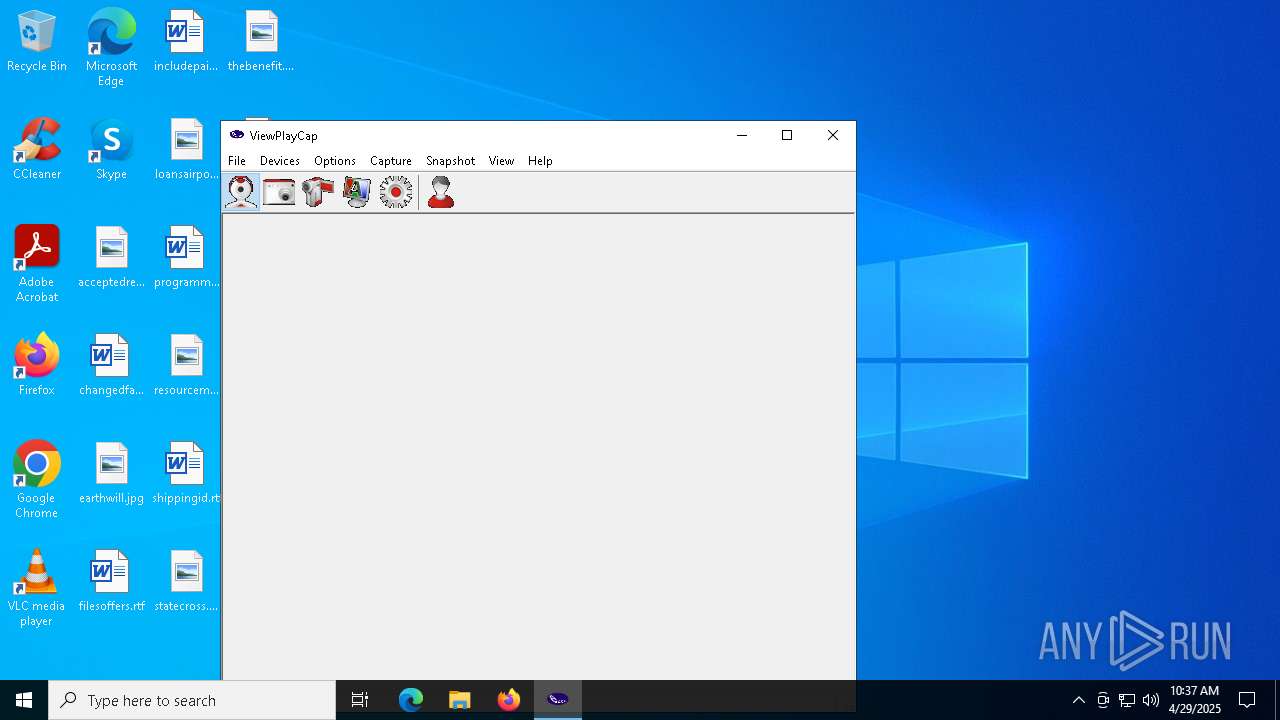
Manual execution by a user
- ViewPlayCap.exe (PID: 1660)
- ViewPlayCap.exe (PID: 1164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:09 13:19:49+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 74752 |
| InitializedDataSize: | 104448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xac87 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
138
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1660 -s 1464 | C:\Windows\SysWOW64\WerFault.exe | — | ViewPlayCap.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Users\admin\AppData\Local\Temp\ViewPlay.exe" -el -s2 "-dC:\Program Files (x86)\ViewPlayCap" "-p" "-sp" | C:\Users\admin\AppData\Local\Temp\ViewPlay.exe | ViewPlay.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\ViewPlayCap\ViewPlayCap.exe" | C:\Program Files (x86)\ViewPlayCap\ViewPlayCap.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: ViewPlayCap Exit code: 0 Version: 3, 0, 0, 0 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\ViewPlayCap\ViewPlayCap.exe" | C:\Program Files (x86)\ViewPlayCap\ViewPlayCap.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: ViewPlayCap Exit code: 3221225485 Version: 3, 0, 0, 0 Modules
| |||||||||||||||
| 1760 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3132 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | "C:\Users\admin\AppData\Local\Temp\ViewPlay.exe" | C:\Users\admin\AppData\Local\Temp\ViewPlay.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 591
Read events
3 574
Write events
16
Delete events
1
Modification events
| (PID) Process: | (6640) ViewPlay.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6640) ViewPlay.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6640) ViewPlay.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
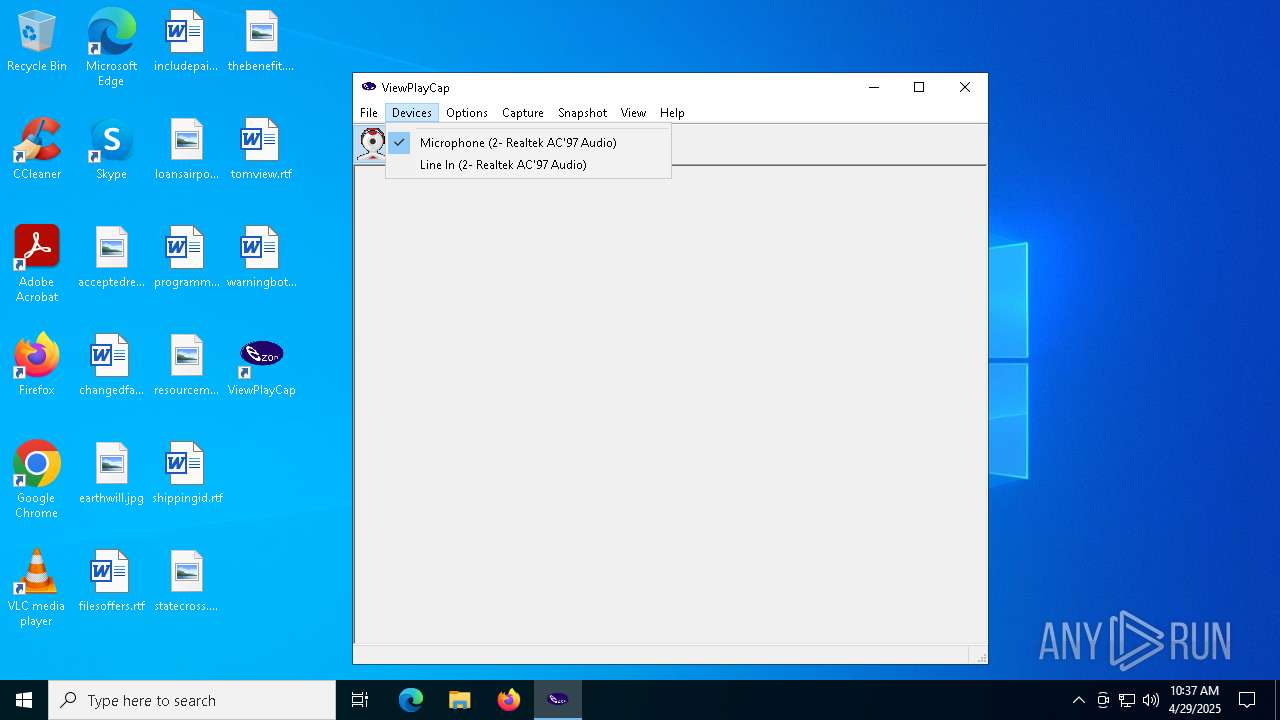
| (PID) Process: | (1660) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\wave:{05B02C95-C55A-499C-A533-120810B973DF} |
| Operation: | write | Name: | FriendlyName |
Value: Microphone (2- Realtek AC'97 Audio) | |||
| (PID) Process: | (1660) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\wave:{05B02C95-C55A-499C-A533-120810B973DF} |
| Operation: | write | Name: | CLSID |
Value: {E30629D2-27E5-11CE-875D-00608CB78066} | |||
| (PID) Process: | (1660) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\wave:{05B02C95-C55A-499C-A533-120810B973DF} |
| Operation: | write | Name: | FilterData |
Value: 02000000000020000000000000000000 | |||
| (PID) Process: | (1660) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\wave:{05B02C95-C55A-499C-A533-120810B973DF} |
| Operation: | write | Name: | EndpointId |
Value: {0.0.1.00000000}.{05b02c95-c55a-499c-a533-120810b973df} | |||
| (PID) Process: | (1660) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\wave:{05B02C95-C55A-499C-A533-120810B973DF} |
| Operation: | write | Name: | EndpointGuid |
Value: {05B02C95-C55A-499C-A533-120810B973DF} | |||
| (PID) Process: | (1660) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\wave:{05B02C95-C55A-499C-A533-120810B973DF} |
| Operation: | write | Name: | WaveInId |
Value: 0 | |||
| (PID) Process: | (1660) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\wave:{05B02C95-C55A-499C-A533-120810B973DF} |
| Operation: | write | Name: | ClassManagerFlags |
Value: 2 | |||
Executable files
7
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 208 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_ViewPlayCap.exe_11d84f274cb5656db53d3a3bd7d654e145427ef_1061ad56_00b3f6ca-bb69-40ab-80e4-2a3fac1508cc\Report.wer | — | |
MD5:— | SHA256:— | |||
| 208 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER2E71.tmp.WERInternalMetadata.xml | binary | |
MD5:F10A22165B905033403DC5D530ABEF2F | SHA256:DE90242D555BF50AFD94695D8068983B3F4FF97BF50384FB84118E76EF2F4270 | |||
| 1164 | ViewPlayCap.exe | C:\Program Files (x86)\ViewPlayCap\ViewPlayCap.ini | text | |
MD5:C31F2FC37B7BDC4C252A501E56761047 | SHA256:CCCD7EA56F0FDBE1FA3F25F760F959E098548F0F81662FE67B8AF39815372313 | |||
| 680 | ViewPlay.exe | C:\Program Files (x86)\ViewPlayCap\SMIUtility.dll | executable | |
MD5:AEA0D6ACC43D8915A7887D91F690813B | SHA256:1EE6C041276CD5B1A3E14B2A833982DC6F9197694E0F1CD3F55453655427AD40 | |||
| 680 | ViewPlay.exe | C:\Program Files (x86)\ViewPlayCap\gdiplus.dll | executable | |
MD5:4D328694BB516E46D2D184950D94433F | SHA256:8199452AF9E5289C126D0FF9D99F2302C52861EC49008702B7F95D64D316383C | |||
| 680 | ViewPlay.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\ViewPlayCap.lnk | binary | |
MD5:EFAE7536BF4208263A075307F6227449 | SHA256:88E0A604696A5F8C0A8CD02C8768C79C31041F6C8A2744A2E955947FBF19EDA5 | |||
| 680 | ViewPlay.exe | C:\Users\admin\Desktop\ViewPlayCap.lnk | binary | |
MD5:747824D69EB0483C5D348EB06607A096 | SHA256:CE77CCEE8A915827E1BFBB0355269098E256683F28E06A4F916BF0D7EA8B9300 | |||
| 680 | ViewPlay.exe | C:\Program Files (x86)\ViewPlayCap\ViewPlayCap.ini | text | |
MD5:C31F2FC37B7BDC4C252A501E56761047 | SHA256:CCCD7EA56F0FDBE1FA3F25F760F959E098548F0F81662FE67B8AF39815372313 | |||
| 680 | ViewPlay.exe | C:\Program Files (x86)\ViewPlayCap\d3dx9_31.dll | executable | |
MD5:797E24743937D67D69F28F2CF5052EE8 | SHA256:E2065619FE6EB0034833B1DC0369DEB4A6EDC3110E38A1132EEAFCF430C578A5 | |||
| 208 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER2EB0.tmp.xml | xml | |
MD5:E804A987FB8F84105C45110F557C7834 | SHA256:11F700CBFCA090CD8AEBD0C5F30B399315F4CC456D4BAC783FDE76E9382AE4B0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.40:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2384 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2384 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.40:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |