| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/50db1bb9-bdb9-40d9-b592-8510fb580080 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 17:54:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | BCDD8DA242AC5BE6D2A7D86A13BE812F |
| SHA1: | 8F516DEC702165E3EB2182C6D78702C893E7EC66 |
| SHA256: | 85309B4A5739A95743A0DB87A17A9458F14D84AB2CCE2EE46FFD0C63C6E1DE7F |
| SSDEEP: | 49152:Z6SUk/6KkQaQFl7vw7x/Y5WZFPiALcjVKrN5VVnv:Ut8kQa60/JPiALcjVKZ5Hv |
MALICIOUS
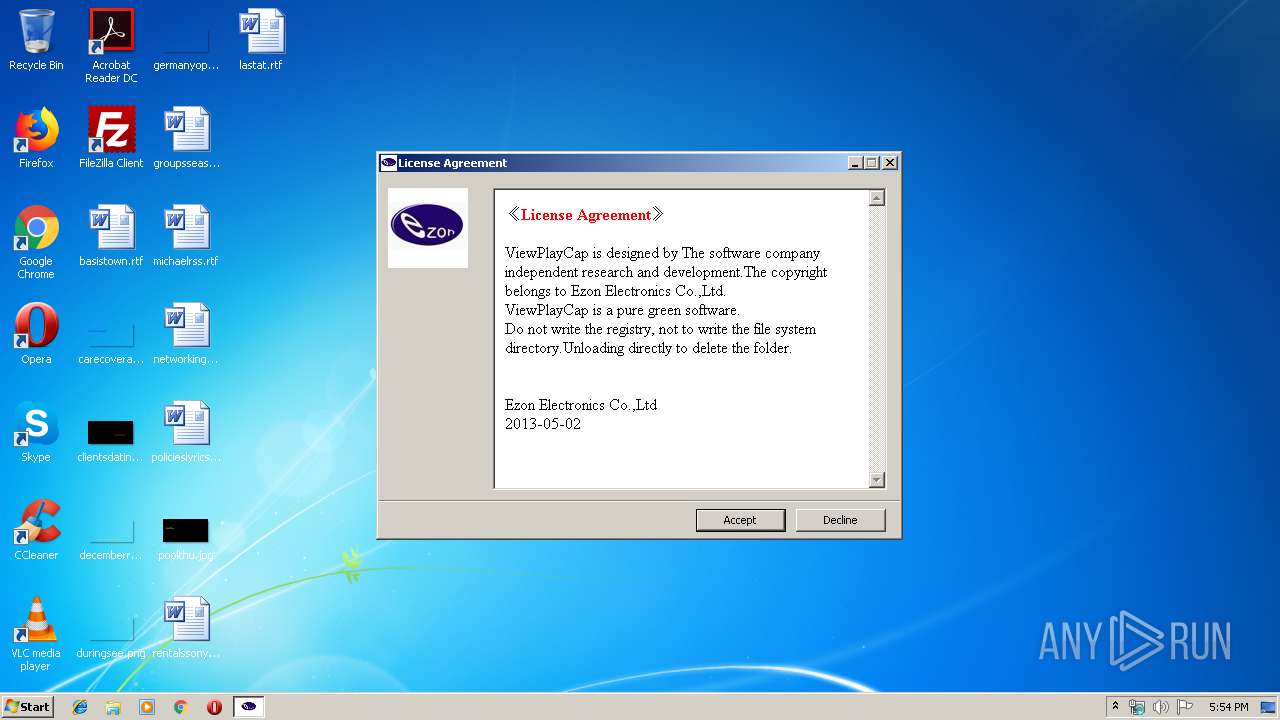
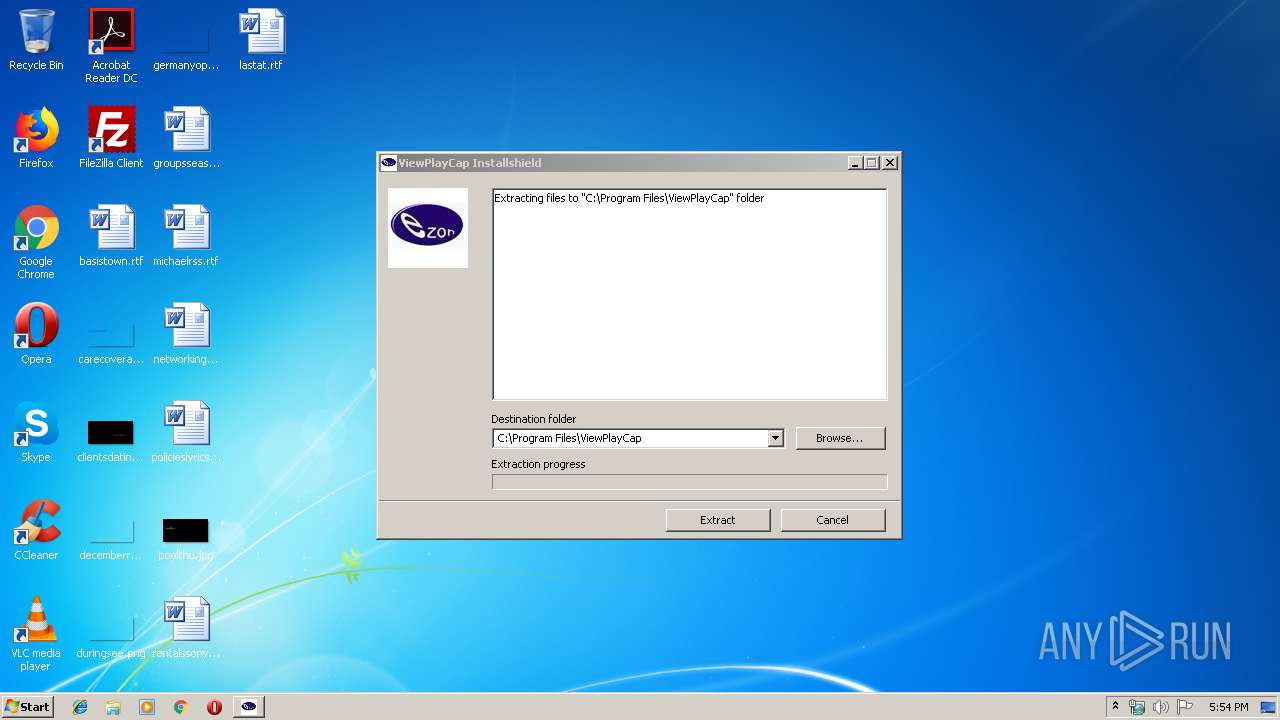
Loads dropped or rewritten executable
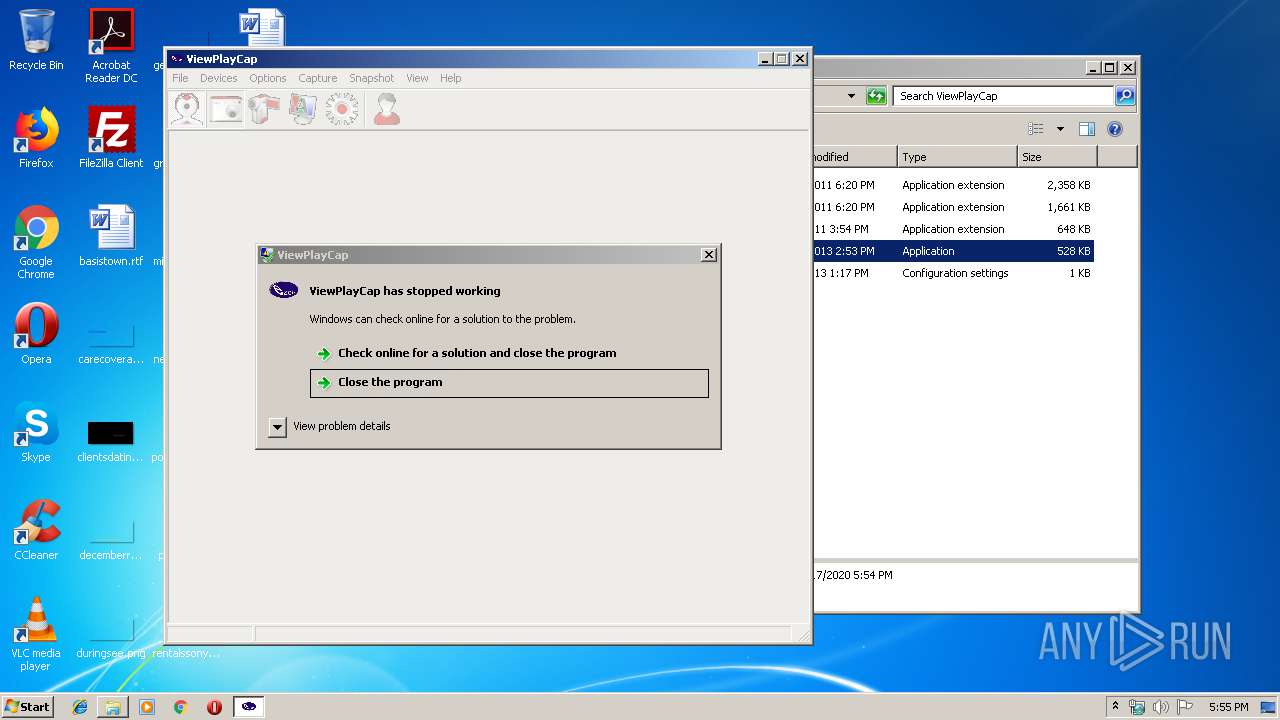
- WerFault.exe (PID: 788)
- ViewPlayCap.exe (PID: 1248)
Application was dropped or rewritten from another process
- ViewPlayCap.exe (PID: 1248)
SUSPICIOUS
Reads internet explorer settings
- setup.exe (PID: 516)
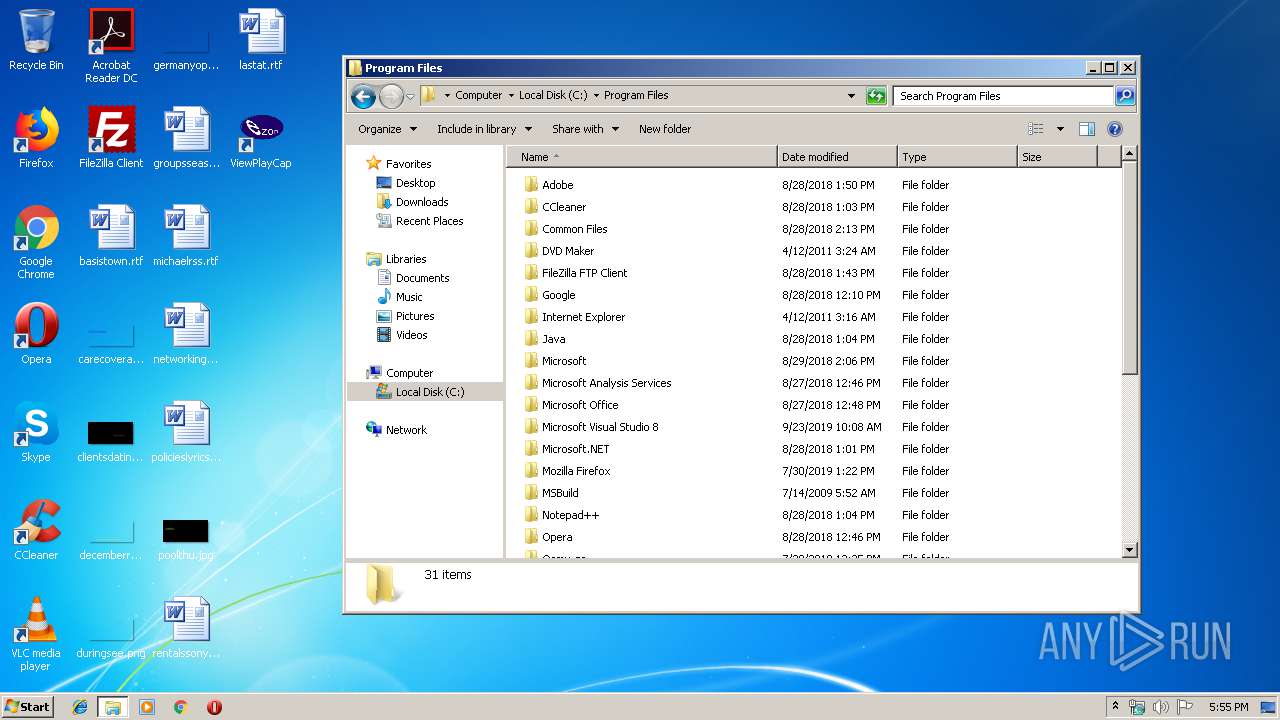
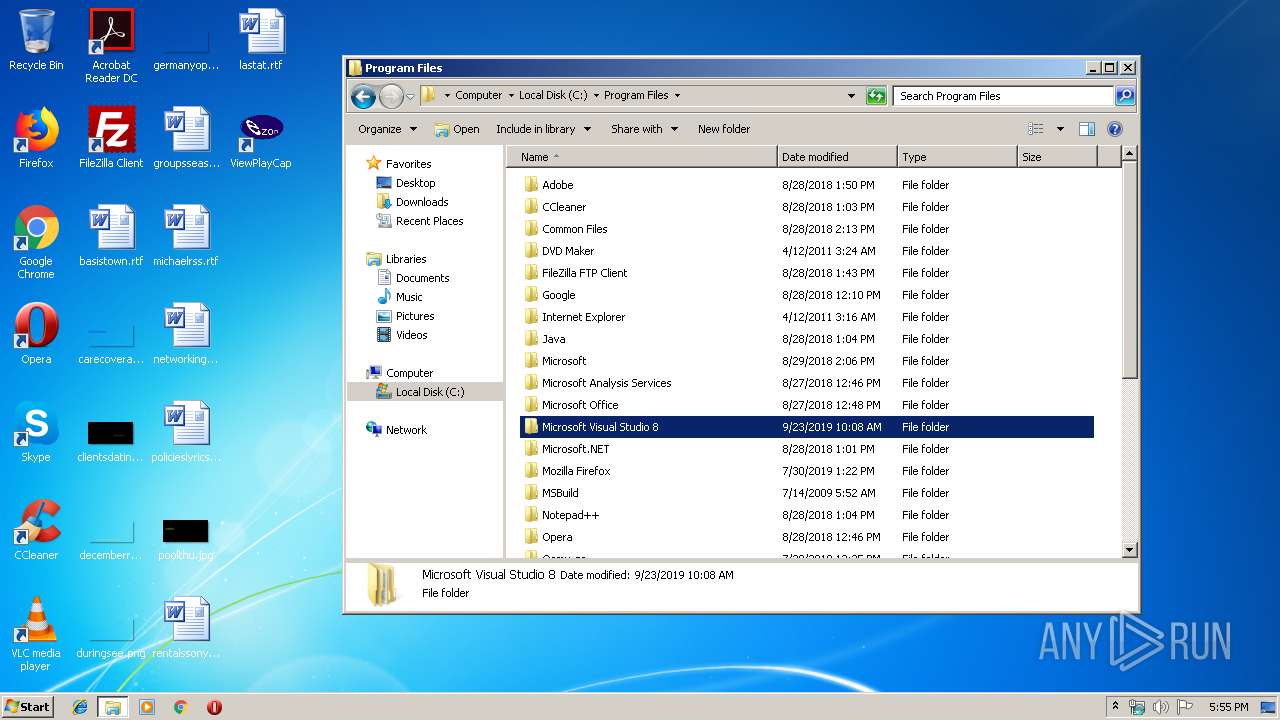
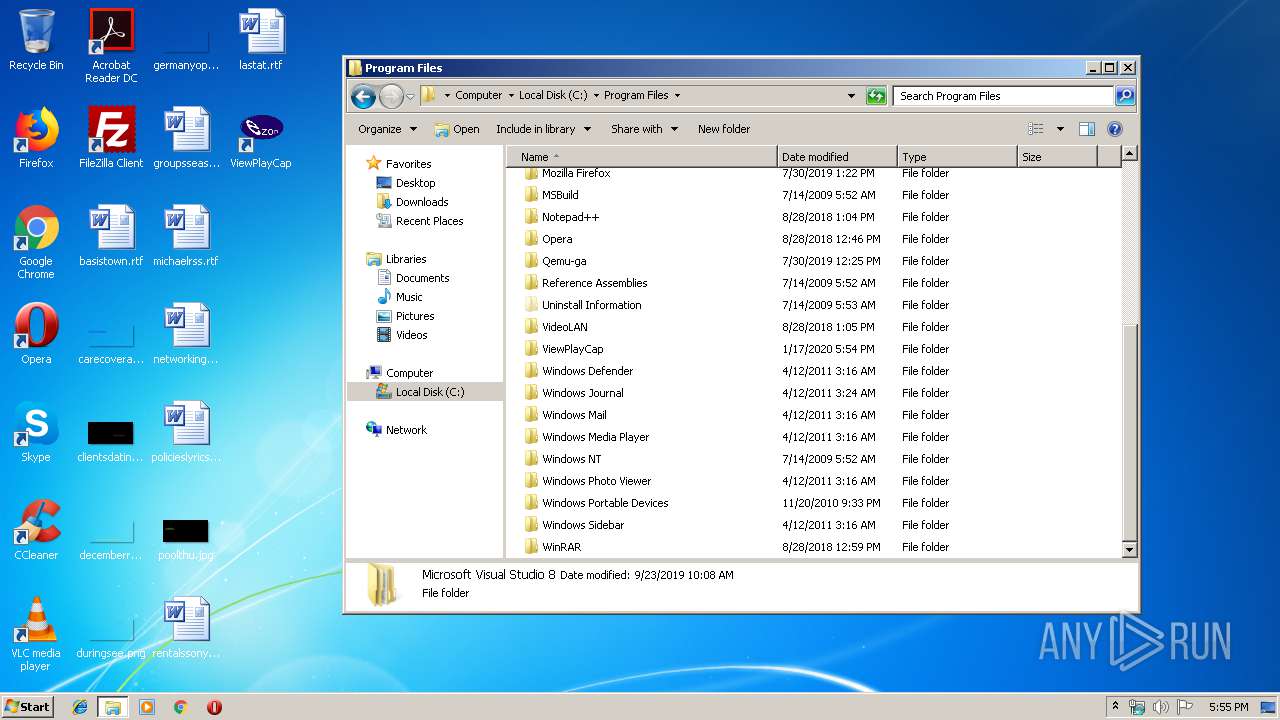
Creates files in the program directory
- setup.exe (PID: 3932)
Application launched itself
- setup.exe (PID: 516)
Creates files in the user directory
- setup.exe (PID: 3932)
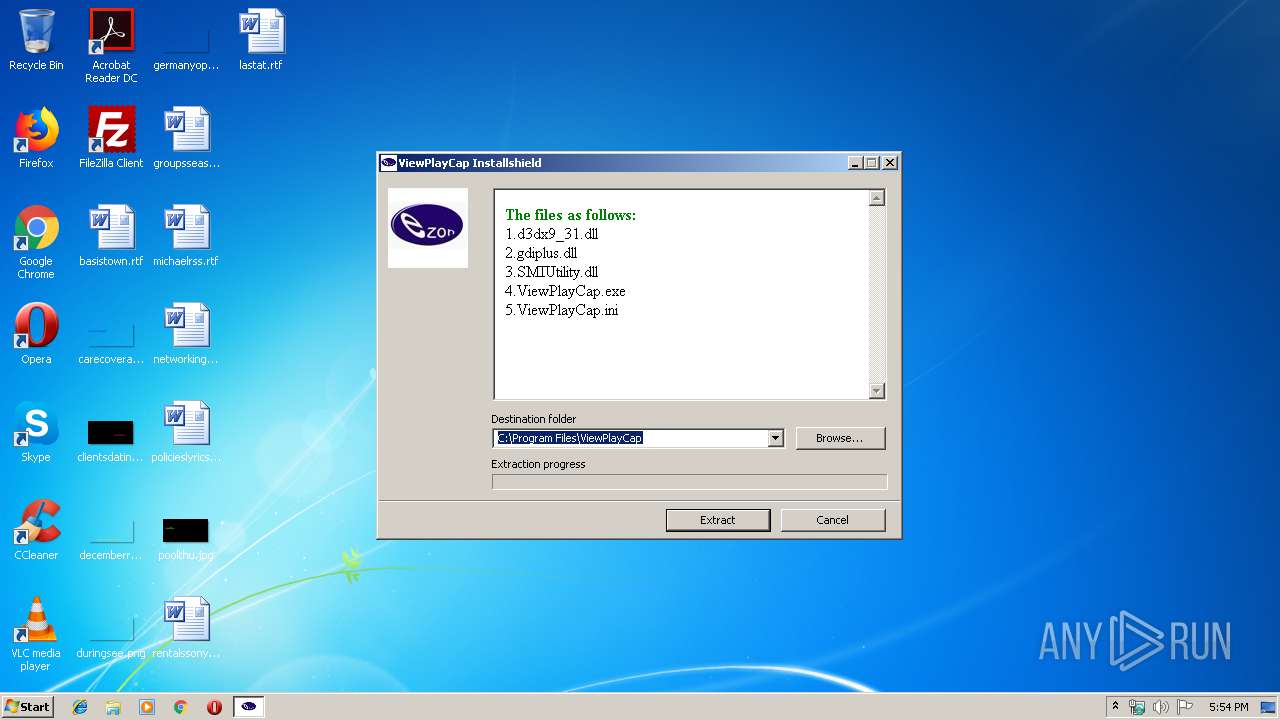
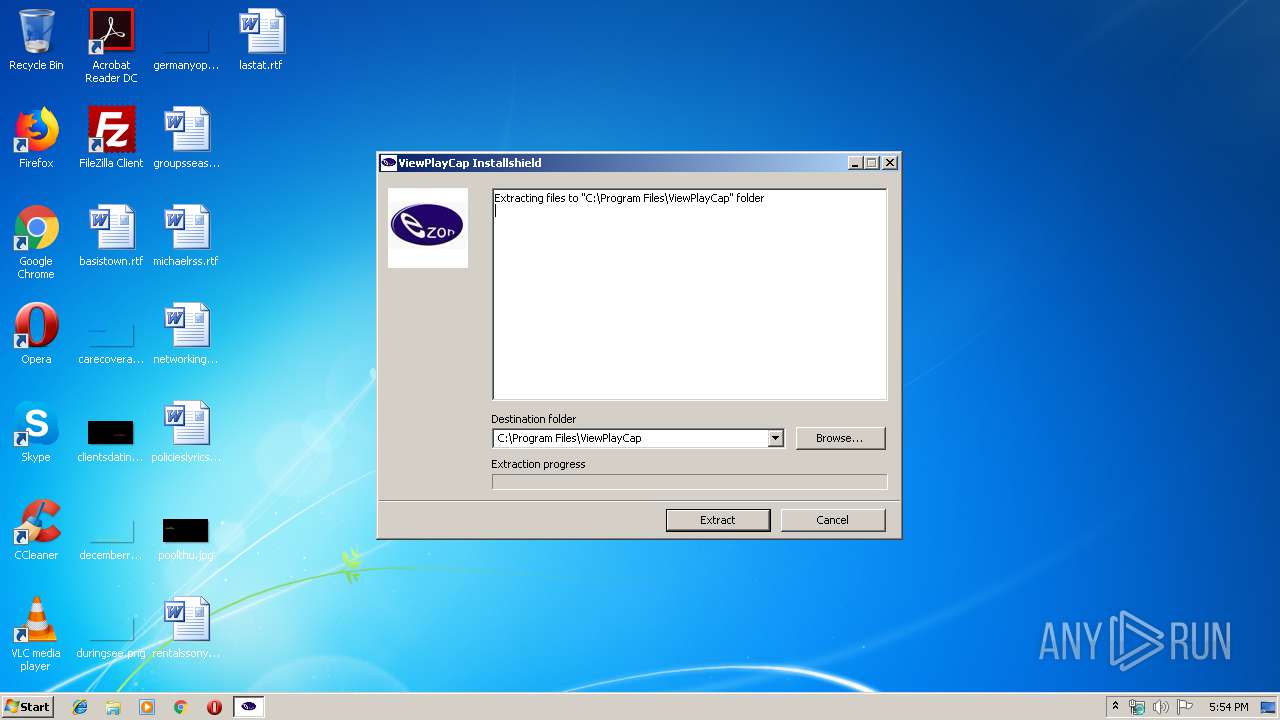
Executable content was dropped or overwritten
- setup.exe (PID: 3932)
INFO
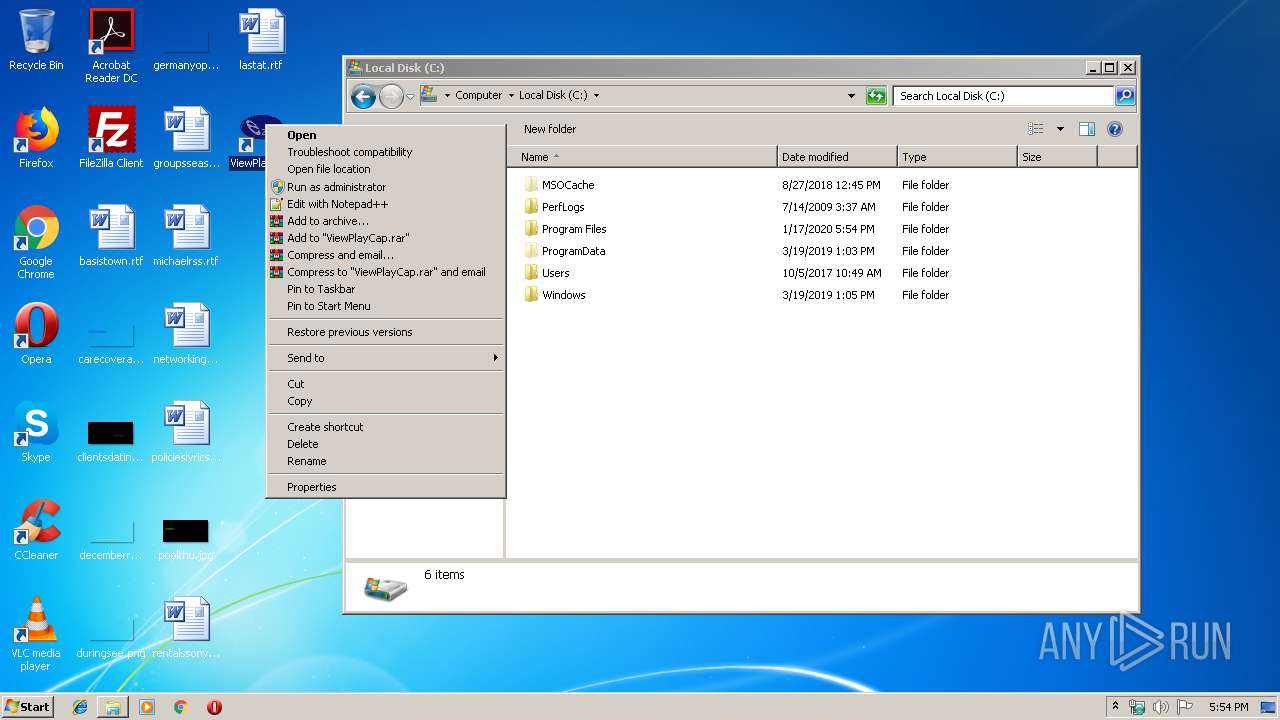
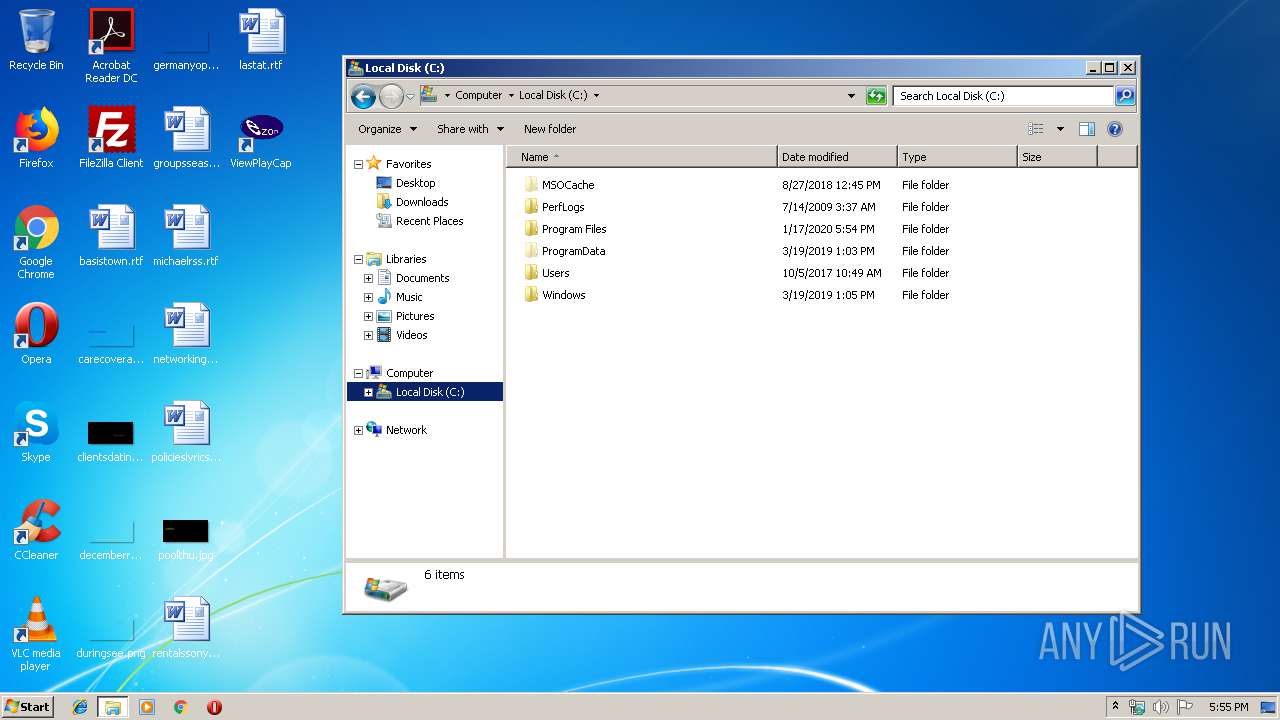
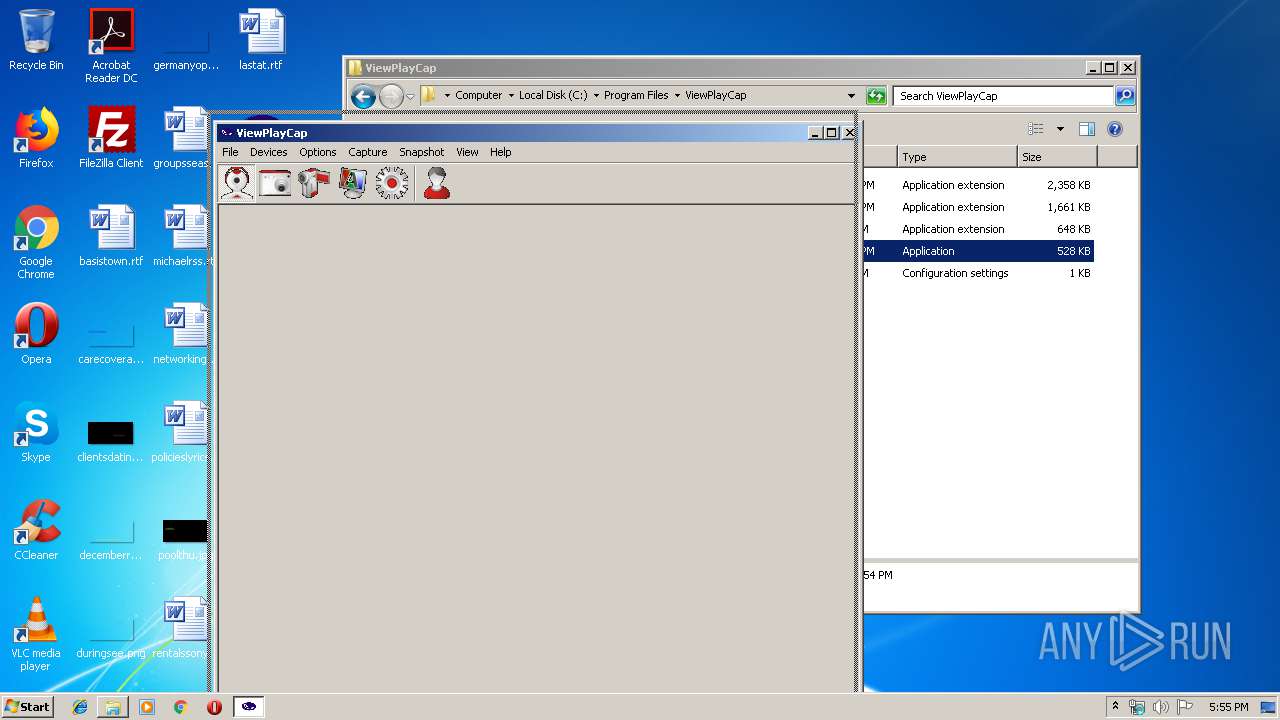
Manual execution by user
- explorer.exe (PID: 2848)
- ViewPlayCap.exe (PID: 1248)
- opera.exe (PID: 4028)
Creates files in the user directory
- opera.exe (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:06:09 15:19:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 74752 |
| InitializedDataSize: | 104448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xac87 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jun-2012 13:19:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Jun-2012 13:19:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001231E | 0x00012400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55555 |
.rdata | 0x00014000 | 0x00001D15 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99401 |
.data | 0x00016000 | 0x00017724 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.54914 |
.CRT | 0x0002E000 | 0x00000020 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.394141 |
.rsrc | 0x0002F000 | 0x000175B0 | 0x00017600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.54887 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.24143 | 556 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.26996 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.16254 | 776 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.06352 | 380 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 2.33959 | 102 | Latin 1 / Western European | English - United States | RT_STRING |
100 | 1.98048 | 20 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
101 | 4.74885 | 19240 | Latin 1 / Western European | Process Default Language | RT_BITMAP |
ASKNEXTVOL | 3.42597 | 646 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
46
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 788 | C:\Windows\system32\WerFault.exe -u -p 1248 -s 740 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
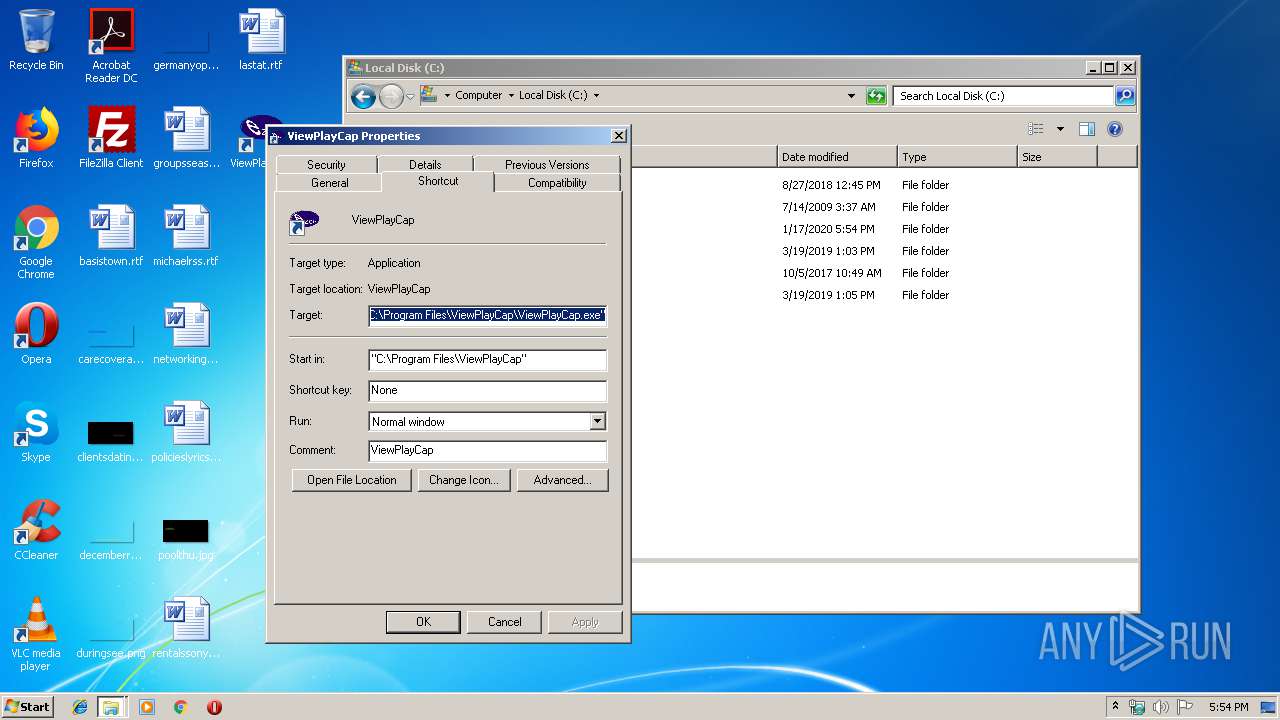
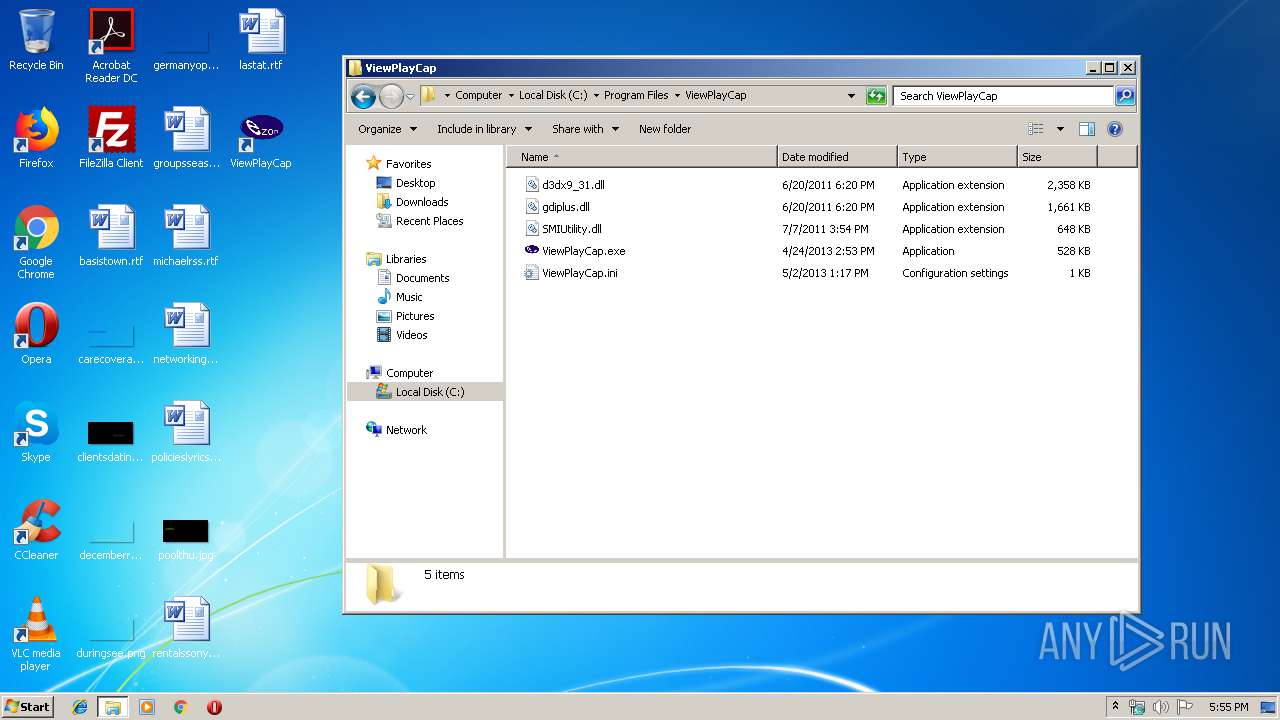
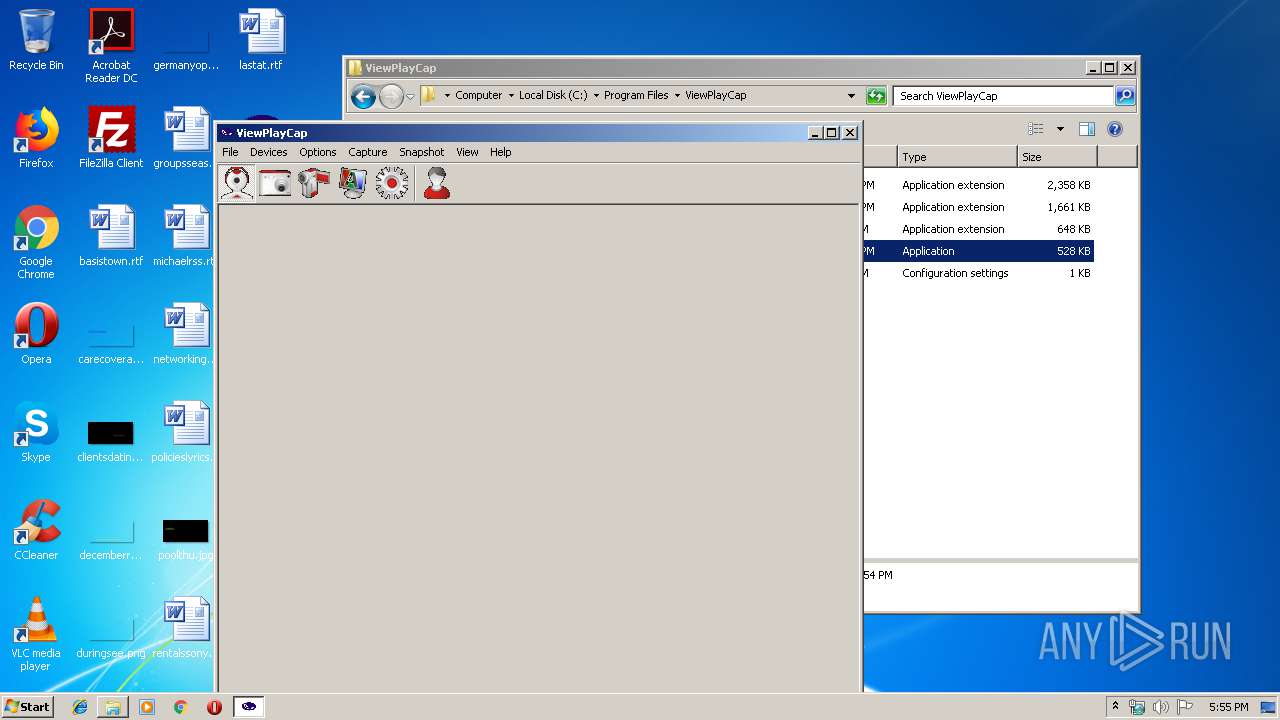
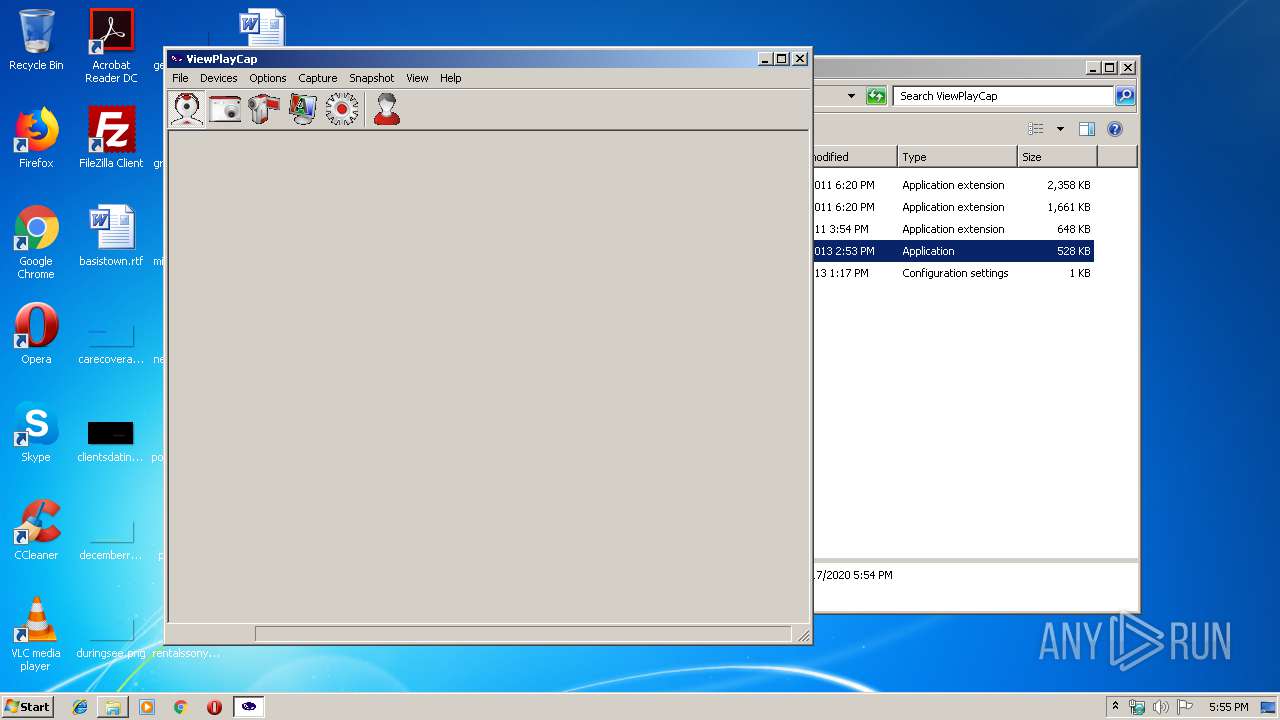
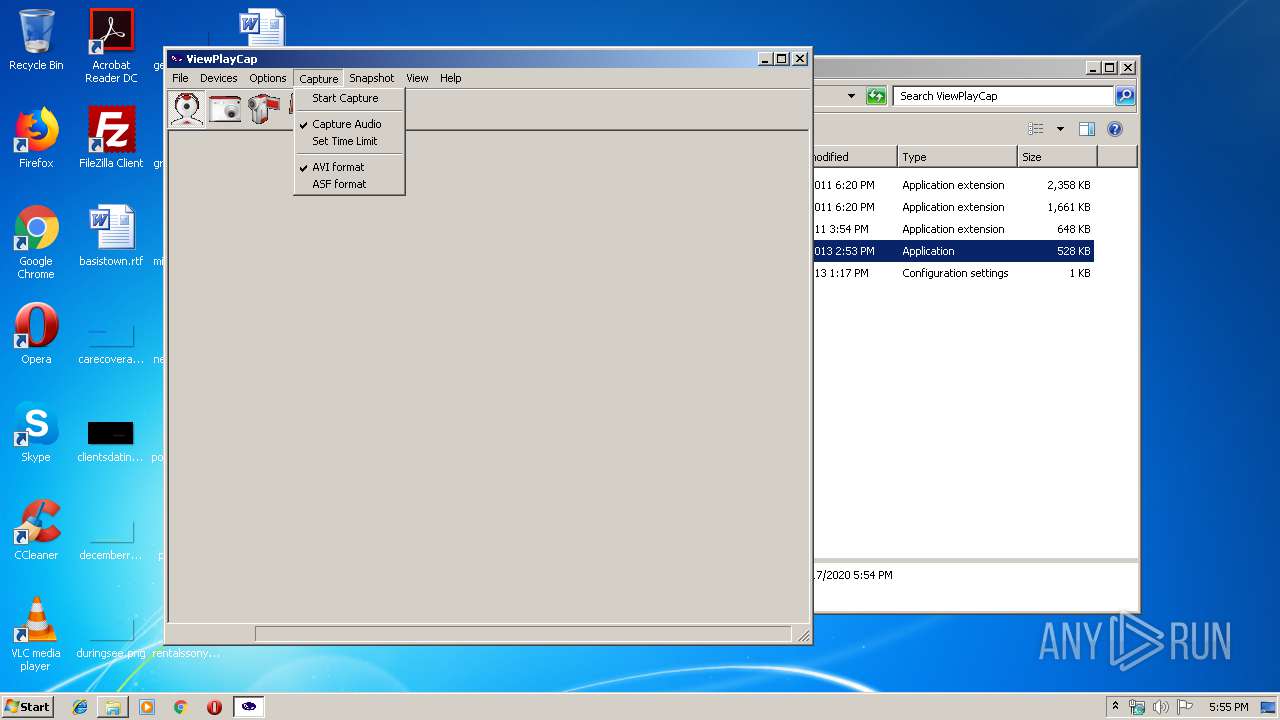
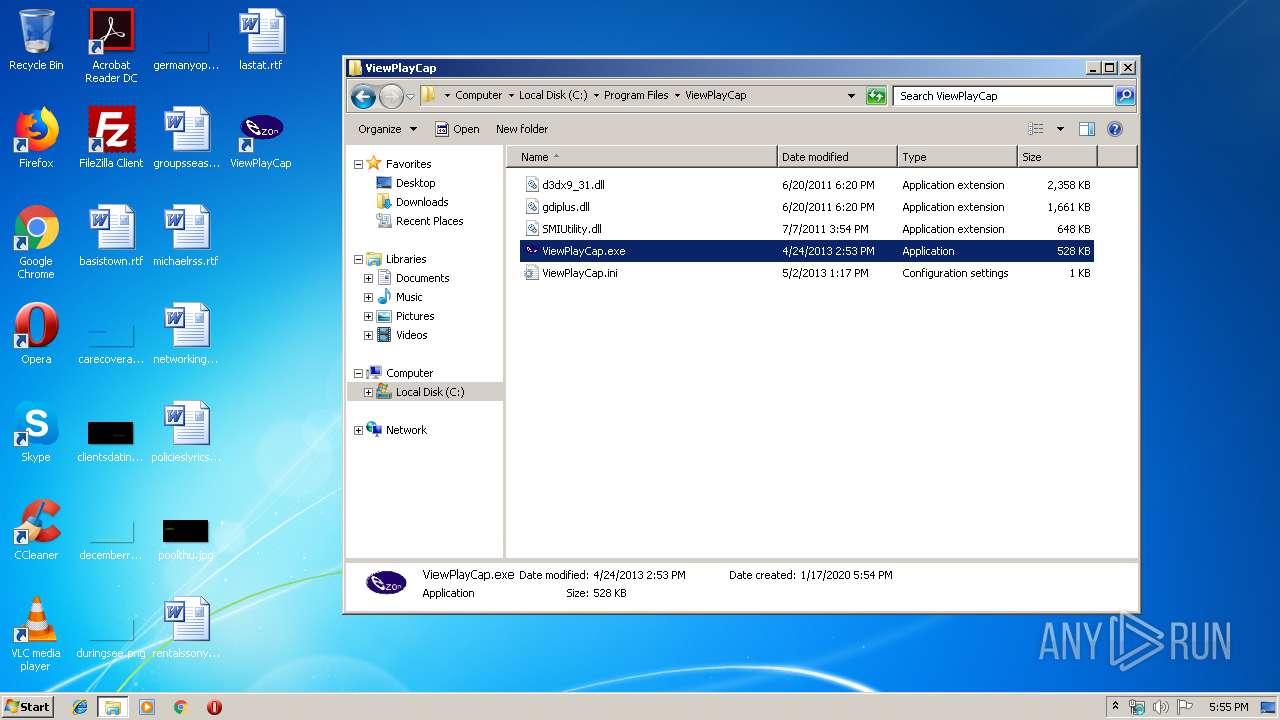
| 1248 | "C:\Program Files\ViewPlayCap\ViewPlayCap.exe" | C:\Program Files\ViewPlayCap\ViewPlayCap.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: ViewPlayCap Exit code: 3221225485 Version: 3, 0, 0, 0 Modules
| |||||||||||||||
| 2848 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3932 | "C:\Users\admin\AppData\Local\Temp\setup.exe" -el -s2 "-dC:\Program Files\ViewPlayCap" "-p" "-sp" | C:\Users\admin\AppData\Local\Temp\setup.exe | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4028 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
746
Read events
726
Write events
20
Delete events
0
Modification events
| (PID) Process: | (516) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (516) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1248) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: ViewPlayCap.exe | |||
| (PID) Process: | (1248) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | FriendlyName |
Value: Microphone (Realtek AC'97 Audio | |||
| (PID) Process: | (1248) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | CLSID |
Value: {E30629D2-27E5-11CE-875D-00608CB78066} | |||
| (PID) Process: | (1248) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | FilterData |
Value: 02000000000020000000000000000000 | |||
| (PID) Process: | (1248) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | WaveInId |
Value: 0 | |||
| (PID) Process: | (1248) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Microphone (Realtek AC'97 Audio |
| Operation: | write | Name: | ClassManagerFlags |
Value: 2 | |||
| (PID) Process: | (1248) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Line In (Realtek AC'97 Audio) |
| Operation: | write | Name: | FriendlyName |
Value: Line In (Realtek AC'97 Audio) | |||
| (PID) Process: | (1248) ViewPlayCap.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\ActiveMovie\devenum\{33D9A762-90C8-11D0-BD43-00A0C911CE86}\Line In (Realtek AC'97 Audio) |
| Operation: | write | Name: | CLSID |
Value: {E30629D2-27E5-11CE-875D-00608CB78066} | |||
Executable files
4
Suspicious files
6
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4028 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr83CC.tmp | — | |
MD5:— | SHA256:— | |||
| 4028 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr83FC.tmp | — | |
MD5:— | SHA256:— | |||
| 3932 | setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\ViewPlayCap.lnk | lnk | |
MD5:— | SHA256:— | |||
| 788 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\ViewPlayCap.exe.1248.dmp | dmp | |
MD5:— | SHA256:— | |||
| 4028 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 4028 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 4028 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 788 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_ViewPlayCap.exe_11d84f274cb5656db53d3a3bd7d654e145427ef_032e6101\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 3932 | setup.exe | C:\Users\admin\Desktop\ViewPlayCap.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3932 | setup.exe | C:\Program Files\ViewPlayCap\ViewPlayCap.ini | ini | |
MD5:C31F2FC37B7BDC4C252A501E56761047 | SHA256:CCCD7EA56F0FDBE1FA3F25F760F959E098548F0F81662FE67B8AF39815372313 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
ViewPlayCap.exe | SMI_GetVIDPIDByIdx:CheckSMInterfacePointer failed!idx=0
|
ViewPlayCap.exe | SMI_GetVIDPIDByIdx:CheckSMInterfacePointer failed!idx=0
|
ViewPlayCap.exe | No Video Input Device
|