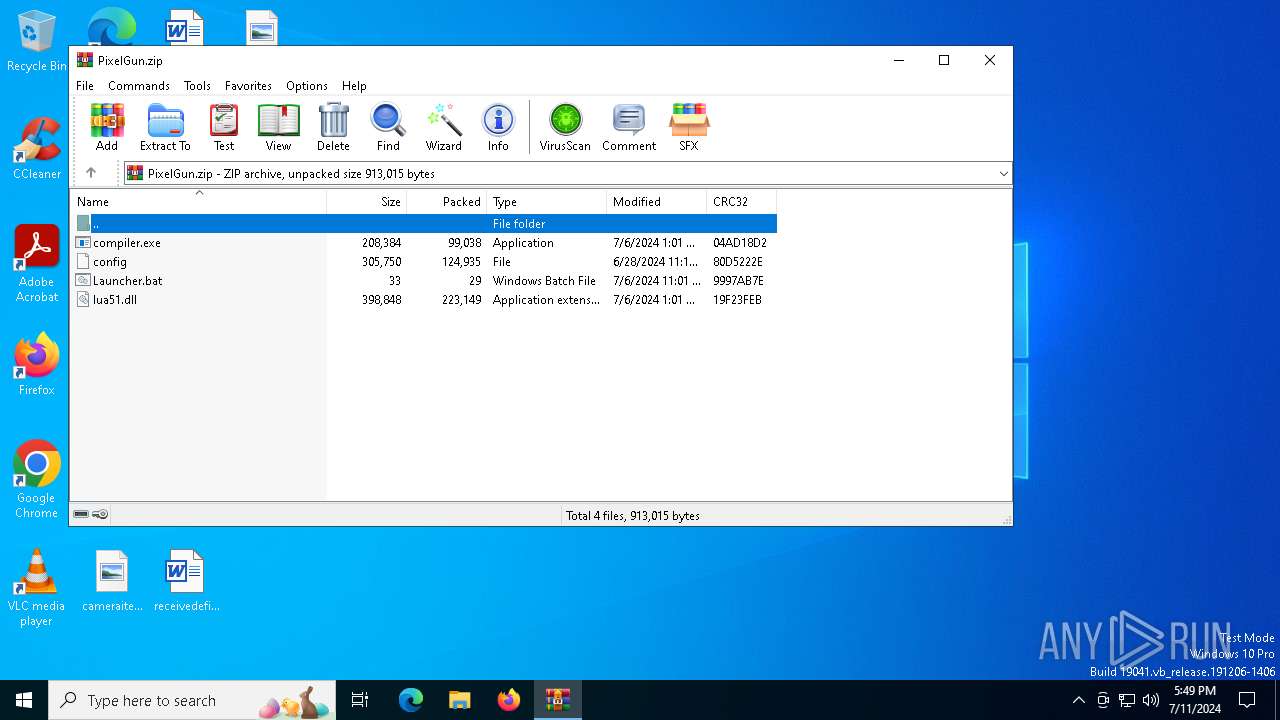
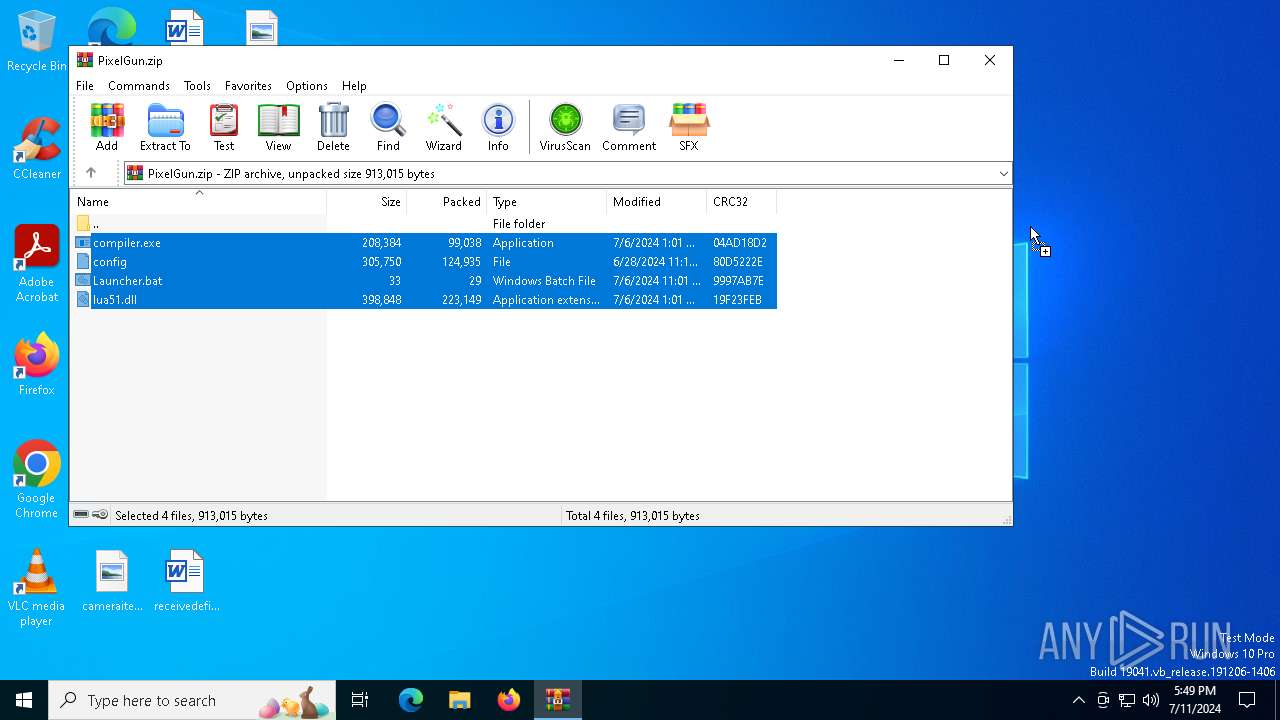
| download: | /user-attachments/files/16115758/PixelGun.zip |
| Full analysis: | https://app.any.run/tasks/cff024dc-18a7-4443-bf84-e494739da323 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2024, 17:49:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 0258C63C60E757AC21A52FD180C4EC40 |
| SHA1: | 430FBD78403517F8A0634BC269C43FA362FDC8C6 |
| SHA256: | 85261CA4C6D2DA6A9A2F6B655CBF60CB1C10C6FEB4023B0F45695893734A05DD |
| SSDEEP: | 24576:HRBRLhiI577Dbof12Bv/vtAjpNy4eeYcF+JYsH:HRBRLhiI5vDbof12Bv/vtAjpNy4eeYcy |
MALICIOUS
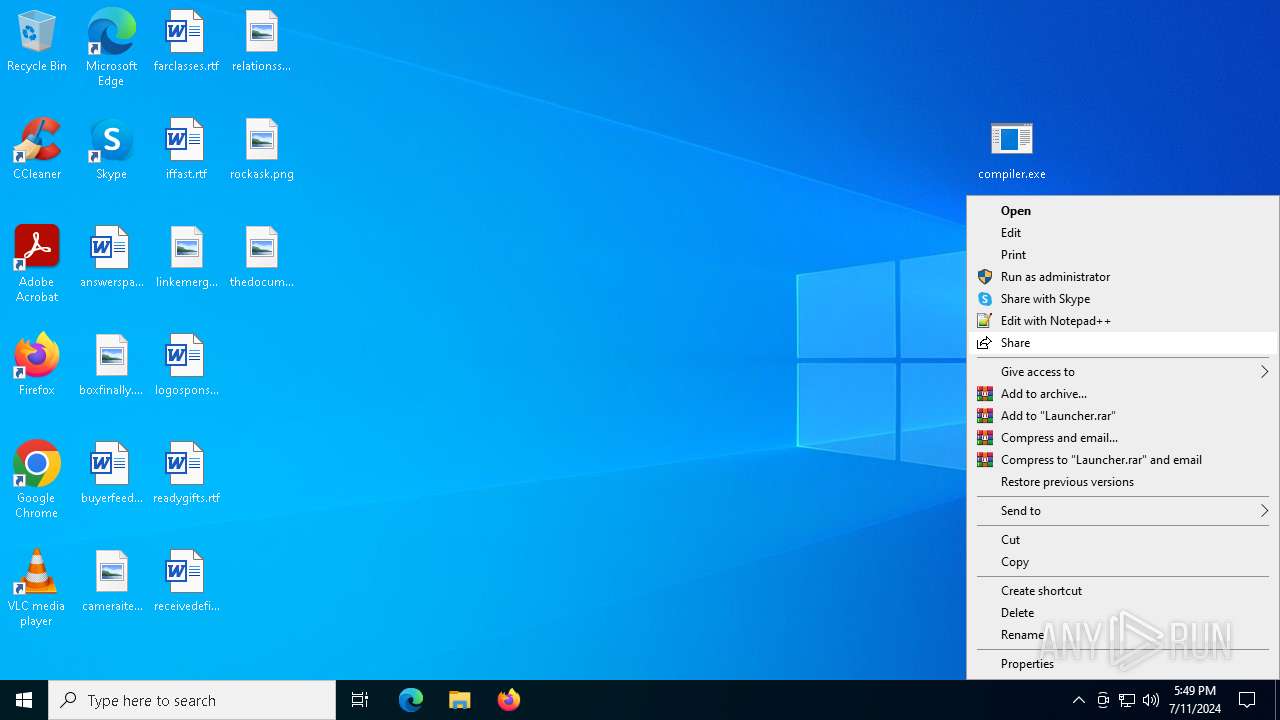
Drops the executable file immediately after the start
- WinRAR.exe (PID: 452)
SUSPICIOUS
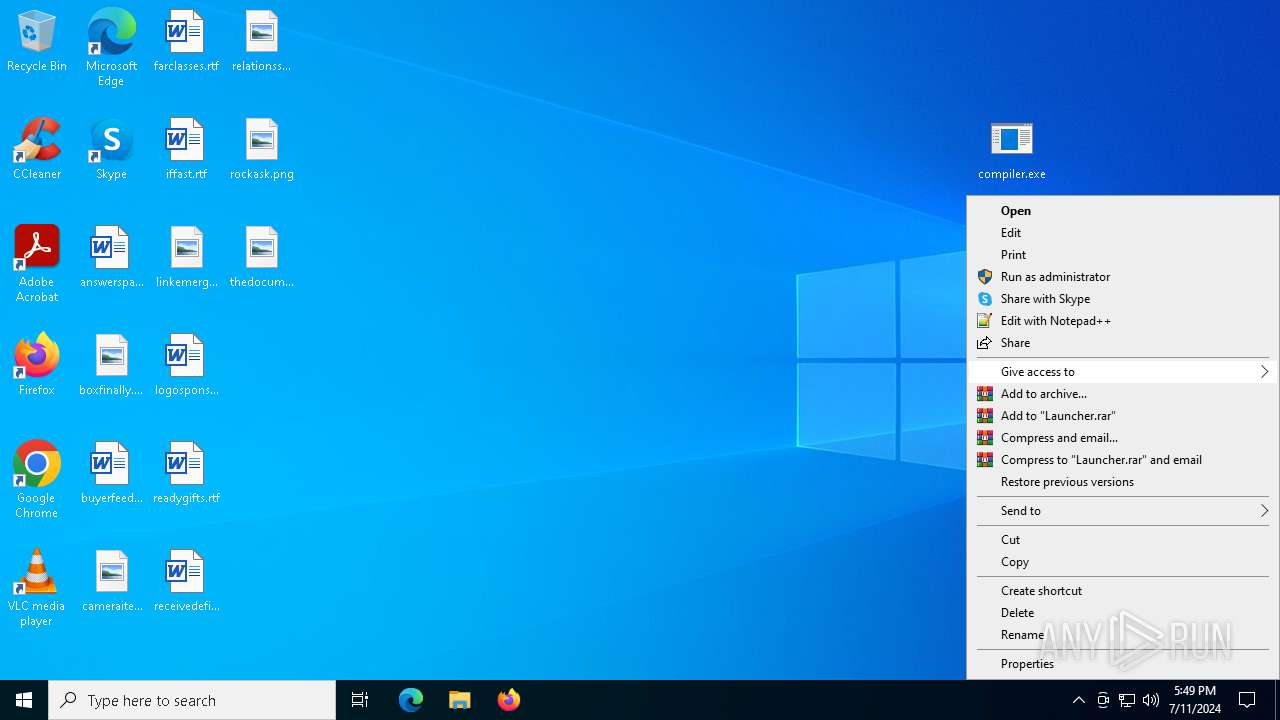
Checks Windows Trust Settings
- compiler.exe (PID: 2888)
- compiler.exe (PID: 3840)
Checks for external IP
- compiler.exe (PID: 2888)
- compiler.exe (PID: 3840)
Connects to the server without a host name
- compiler.exe (PID: 2888)
Reads security settings of Internet Explorer
- compiler.exe (PID: 2888)
- compiler.exe (PID: 3840)
INFO
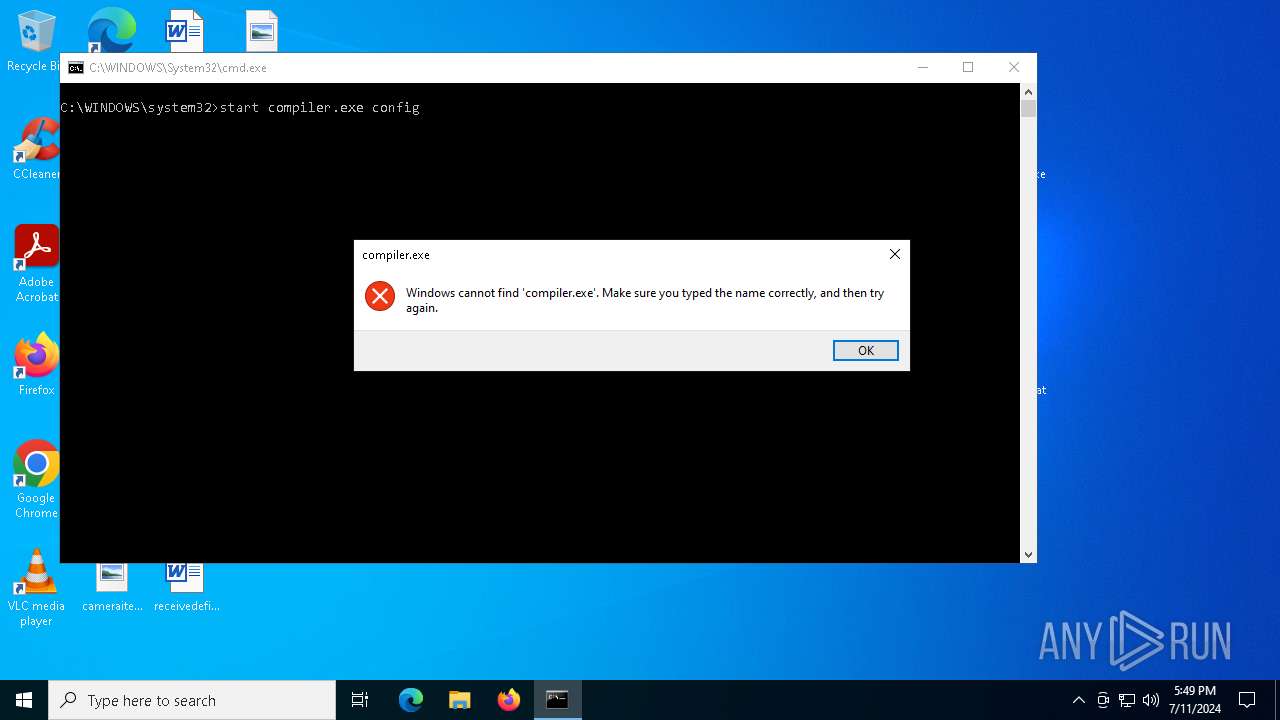
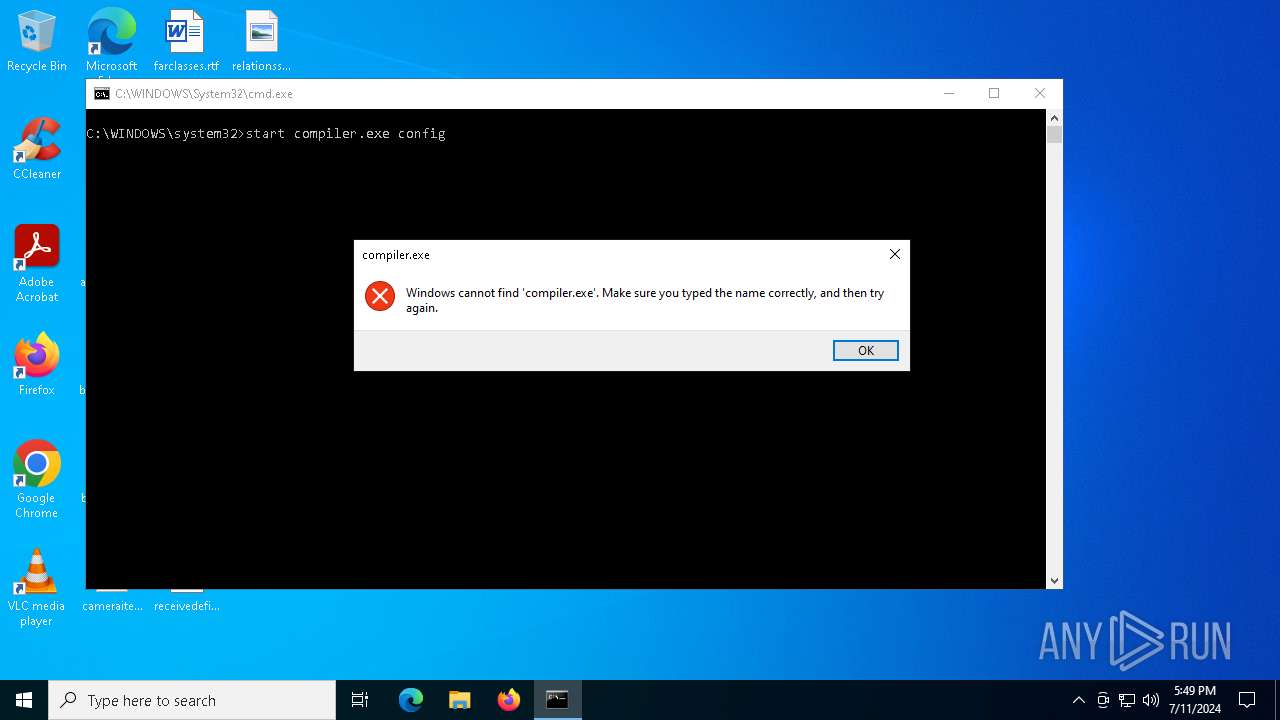
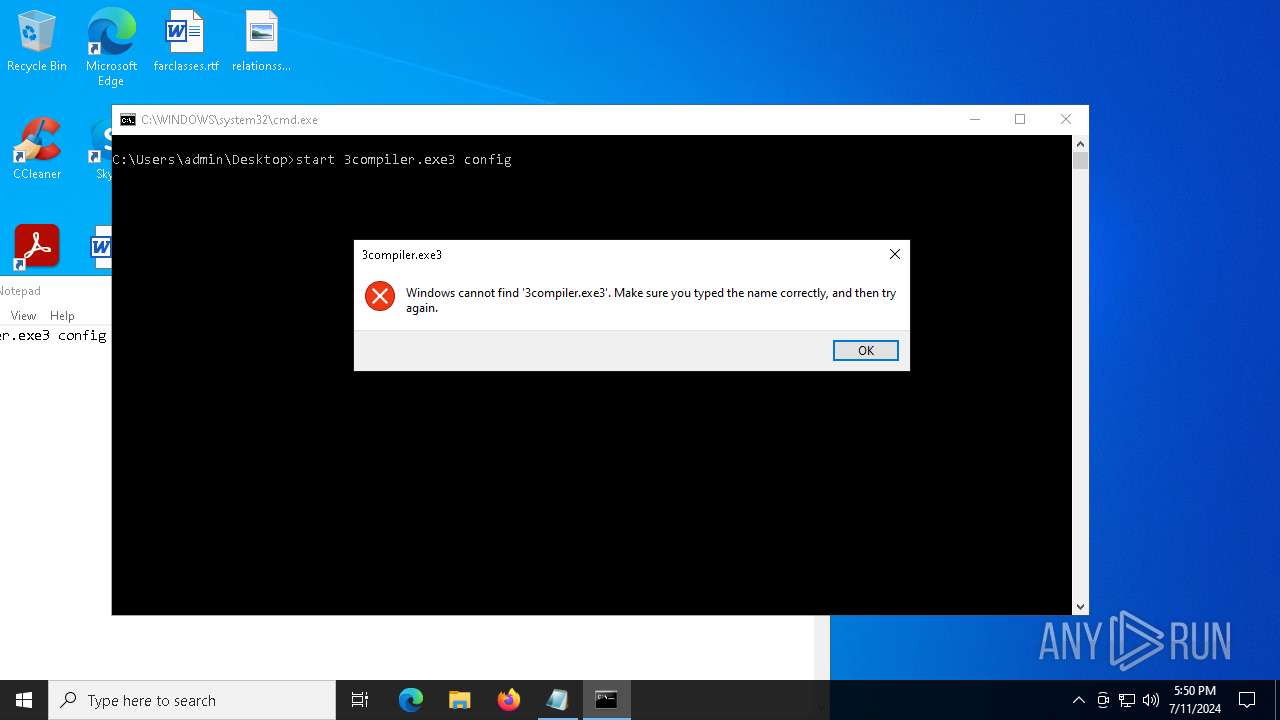
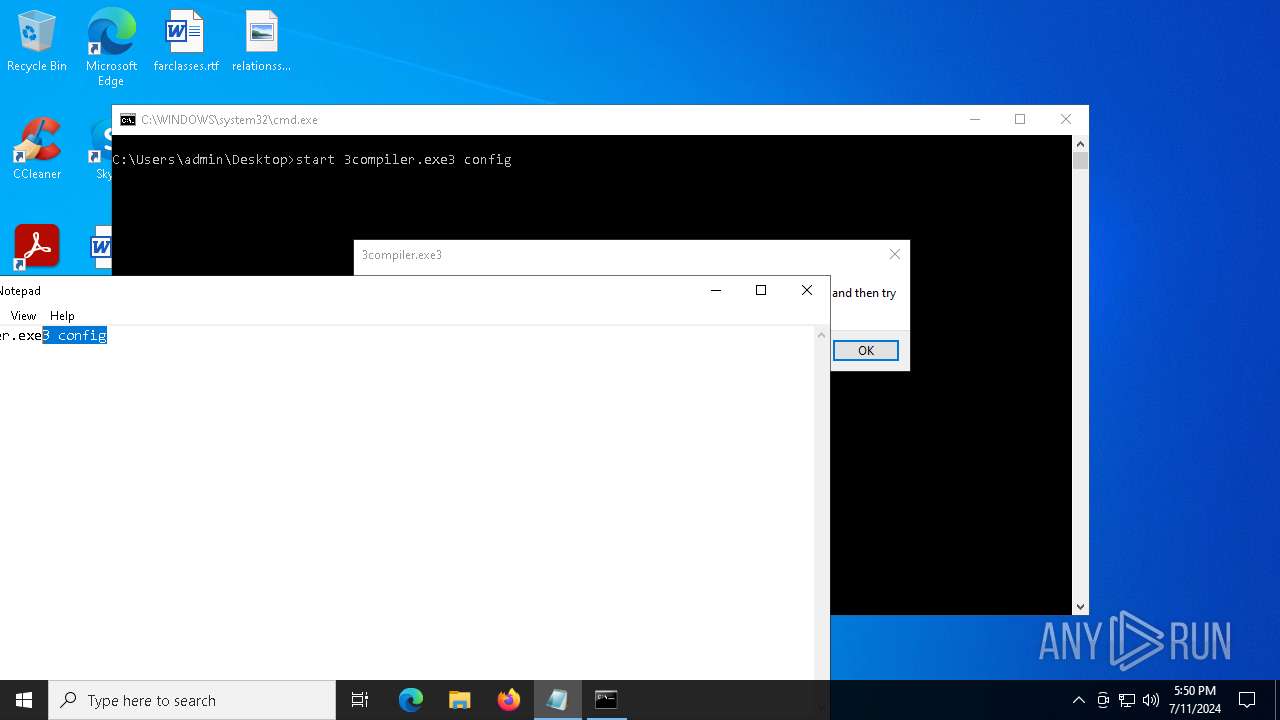
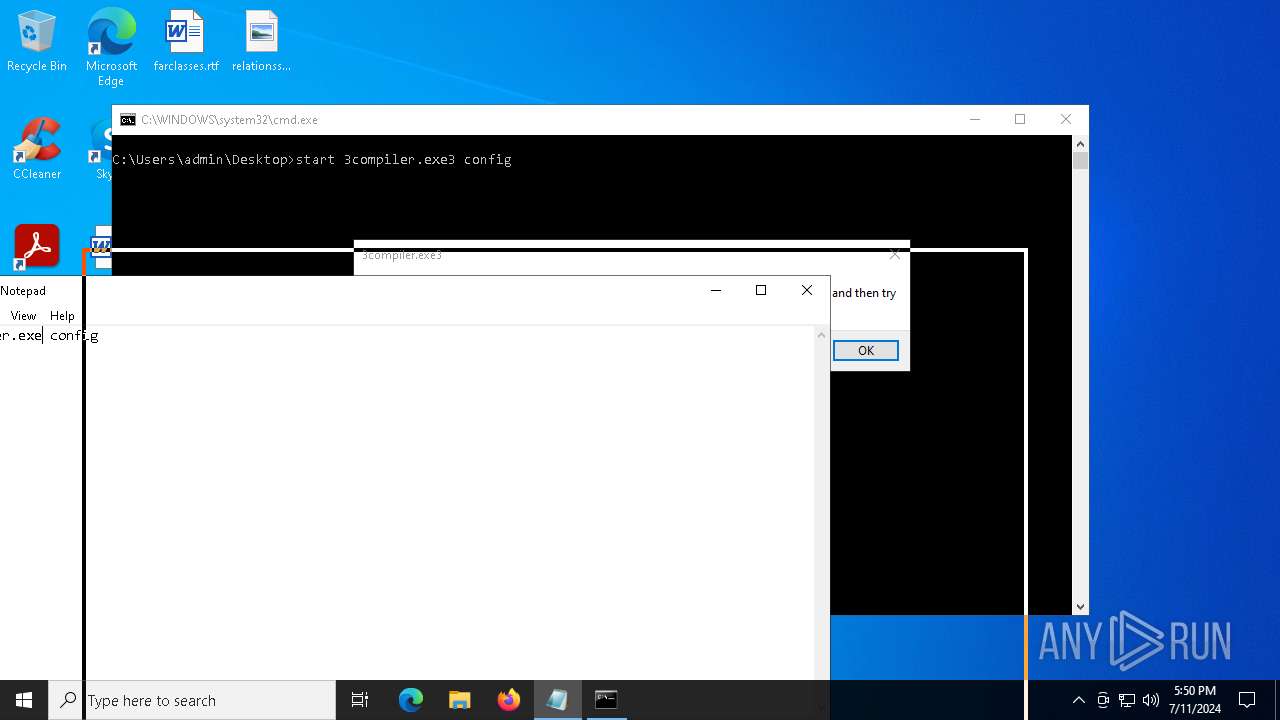
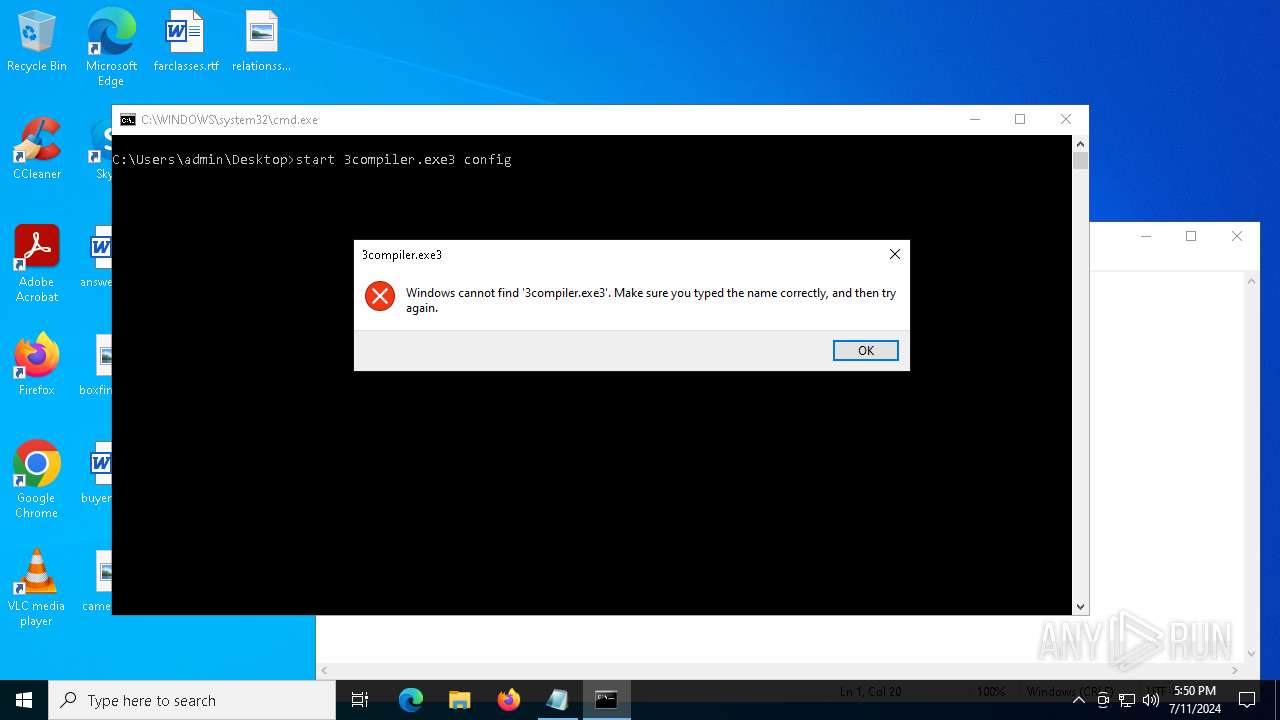
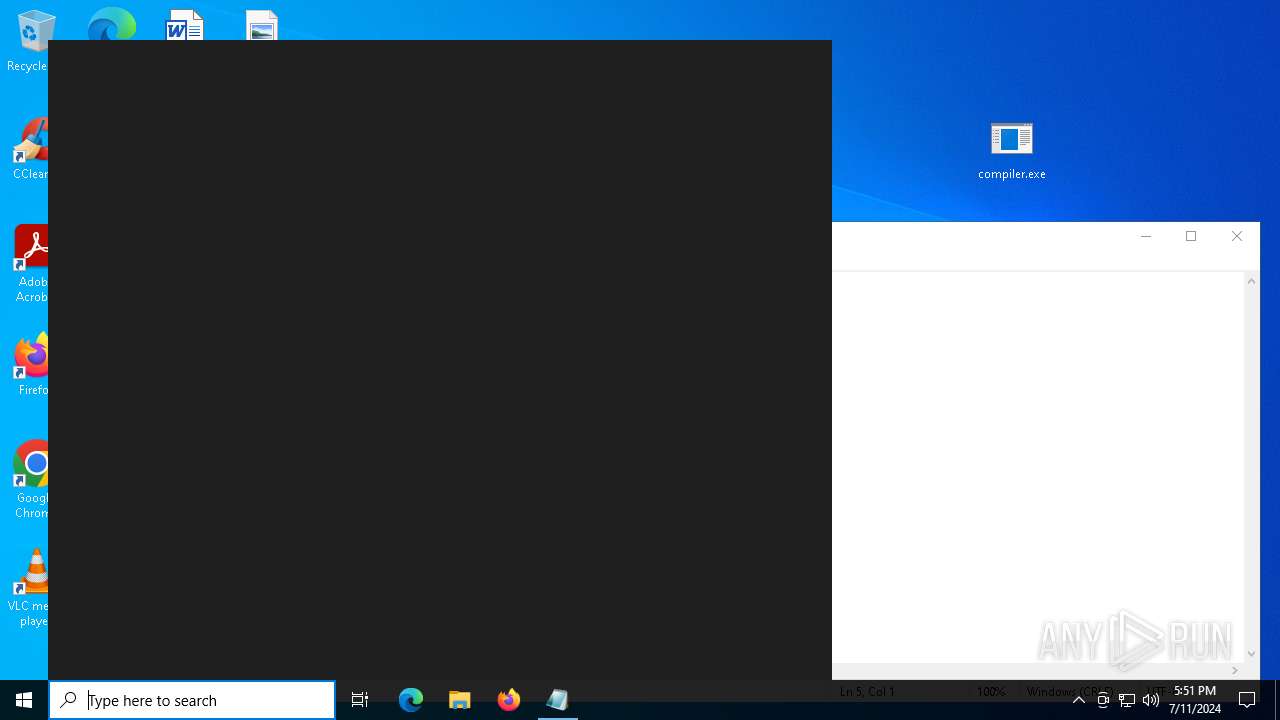
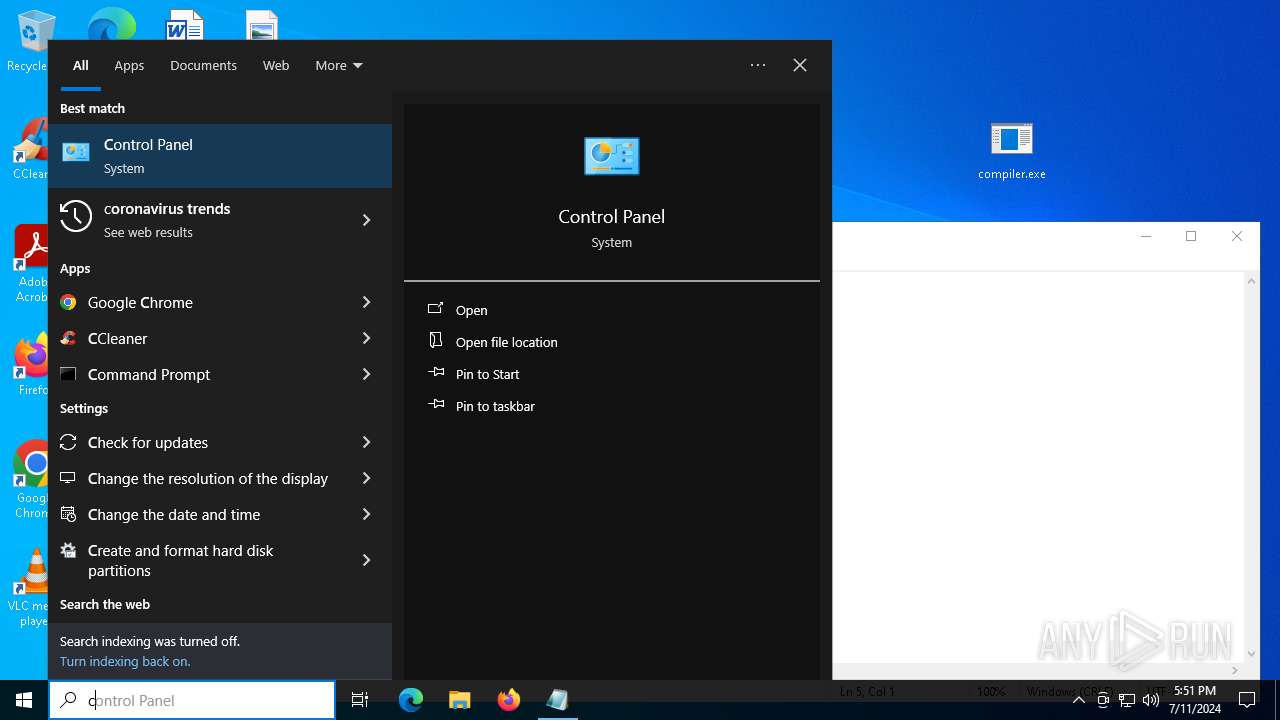
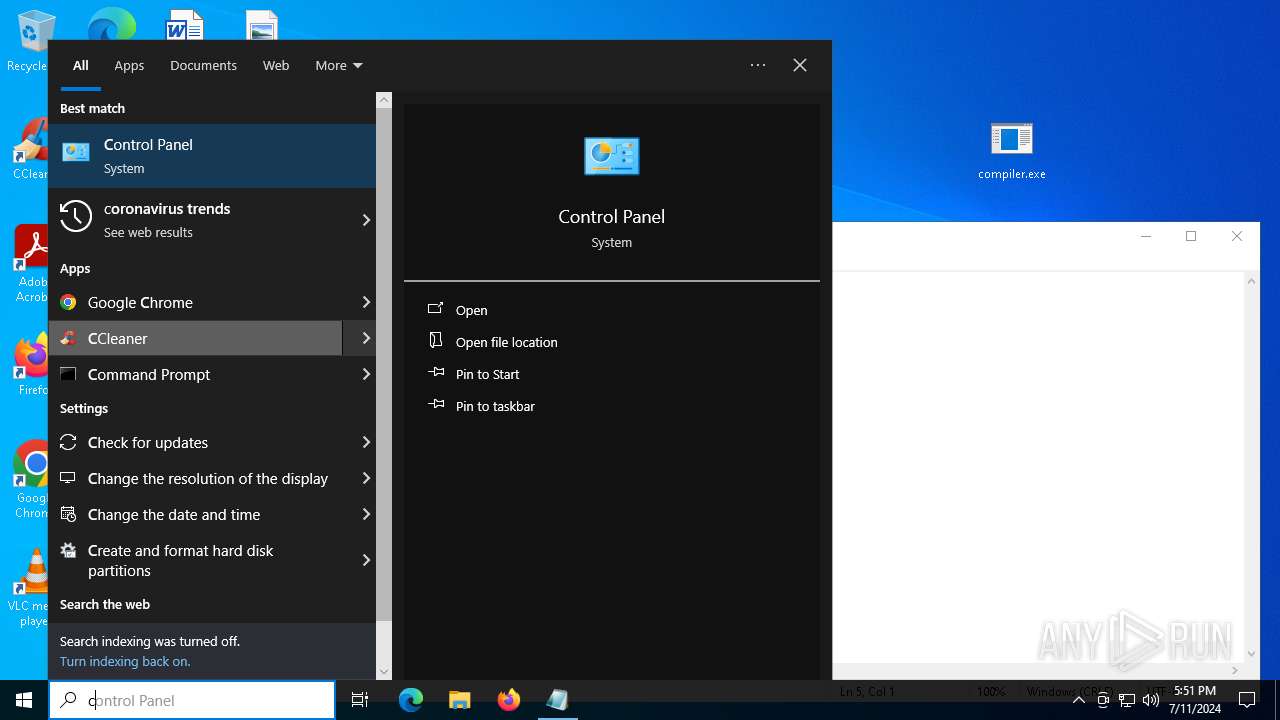
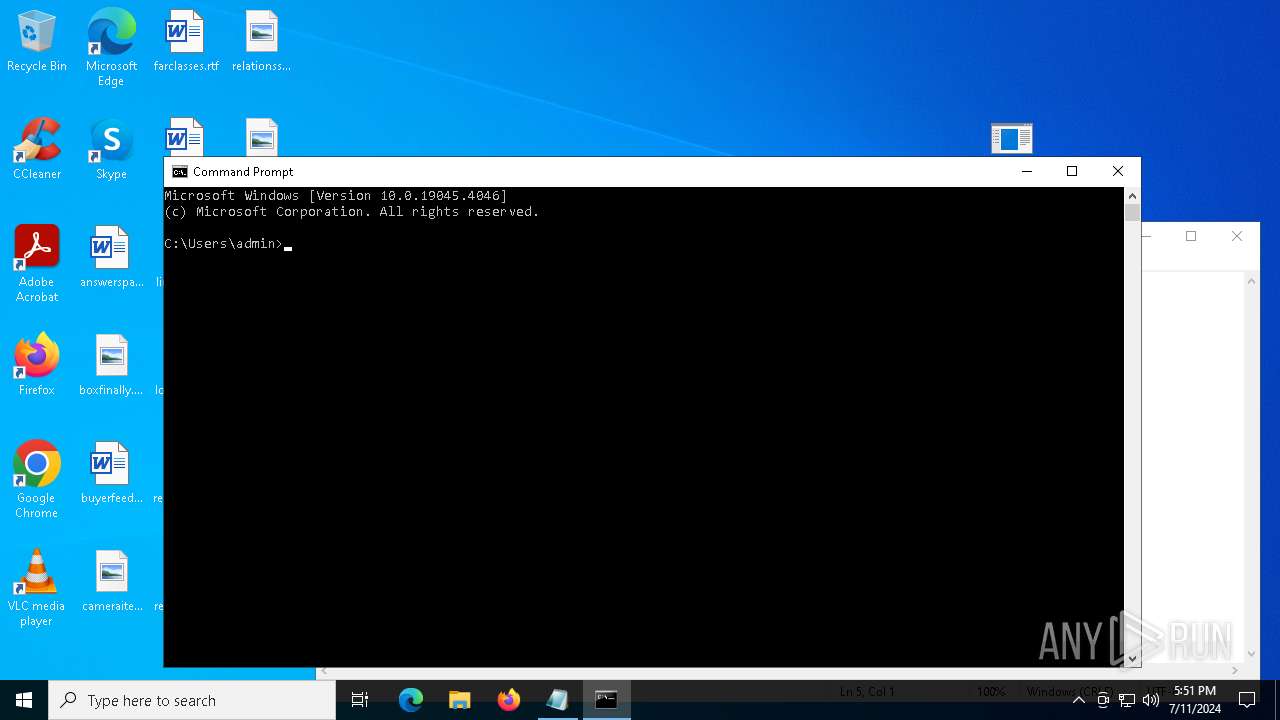
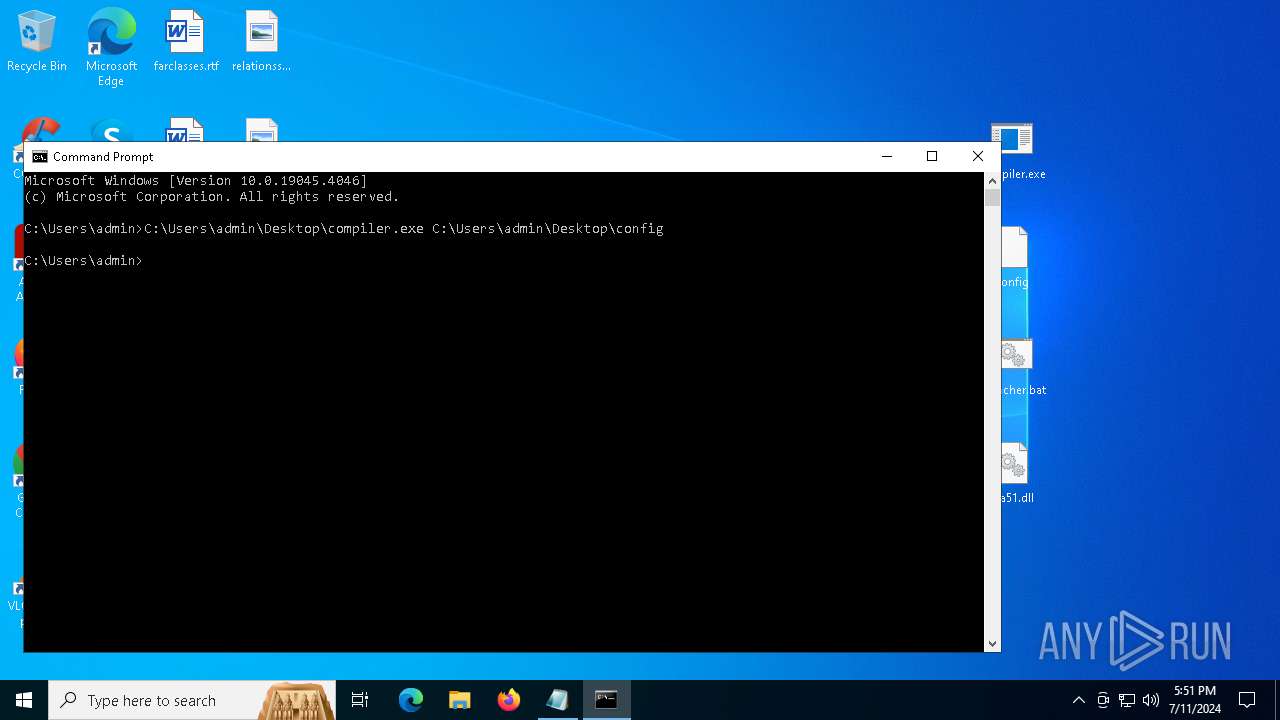
Manual execution by a user
- compiler.exe (PID: 3596)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 5224)
- cmd.exe (PID: 4052)
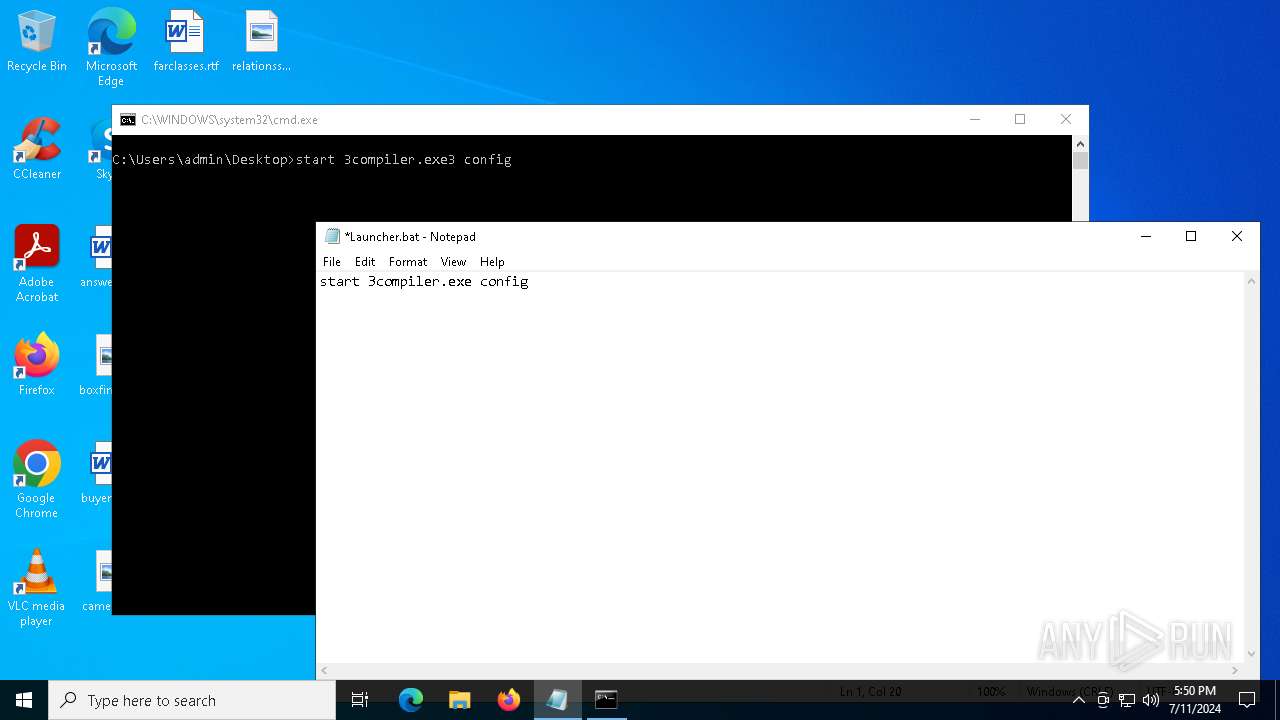
- notepad.exe (PID: 3580)
- cmd.exe (PID: 6520)
- cmd.exe (PID: 4800)
Creates files or folders in the user directory
- compiler.exe (PID: 2888)
- compiler.exe (PID: 3840)
Reads the computer name
- compiler.exe (PID: 2888)
- compiler.exe (PID: 3840)
Reads the software policy settings
- compiler.exe (PID: 2888)
- slui.exe (PID: 6408)
- compiler.exe (PID: 3840)
- slui.exe (PID: 3512)
Reads security settings of Internet Explorer
- notepad.exe (PID: 3580)
Reads the machine GUID from the registry
- compiler.exe (PID: 2888)
- compiler.exe (PID: 3840)
Checks proxy server information
- slui.exe (PID: 3512)
- compiler.exe (PID: 3840)
- compiler.exe (PID: 2888)
Checks supported languages
- compiler.exe (PID: 3840)
- compiler.exe (PID: 3596)
- compiler.exe (PID: 2888)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:07:06 04:01:44 |
| ZipCRC: | 0x04ad18d2 |
| ZipCompressedSize: | 99038 |
| ZipUncompressedSize: | 208384 |
| ZipFileName: | compiler.exe |
Total processes
162
Monitored processes
18
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 452 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\PixelGun.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
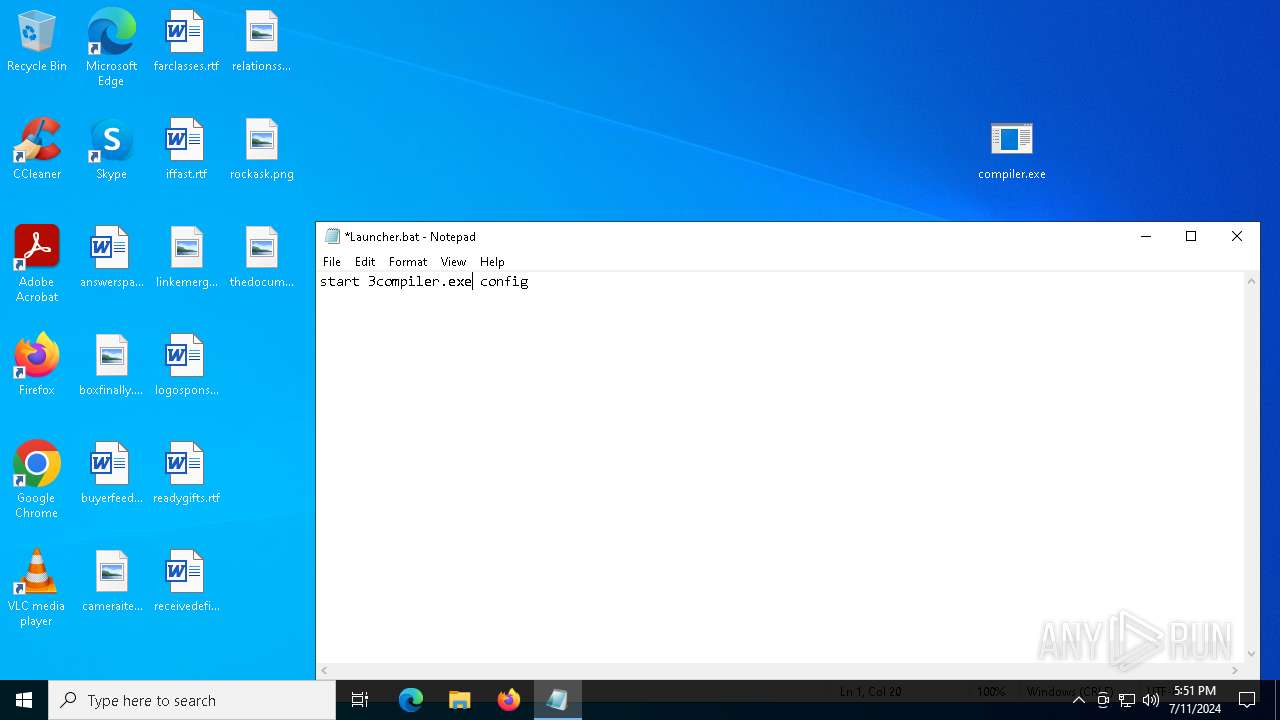
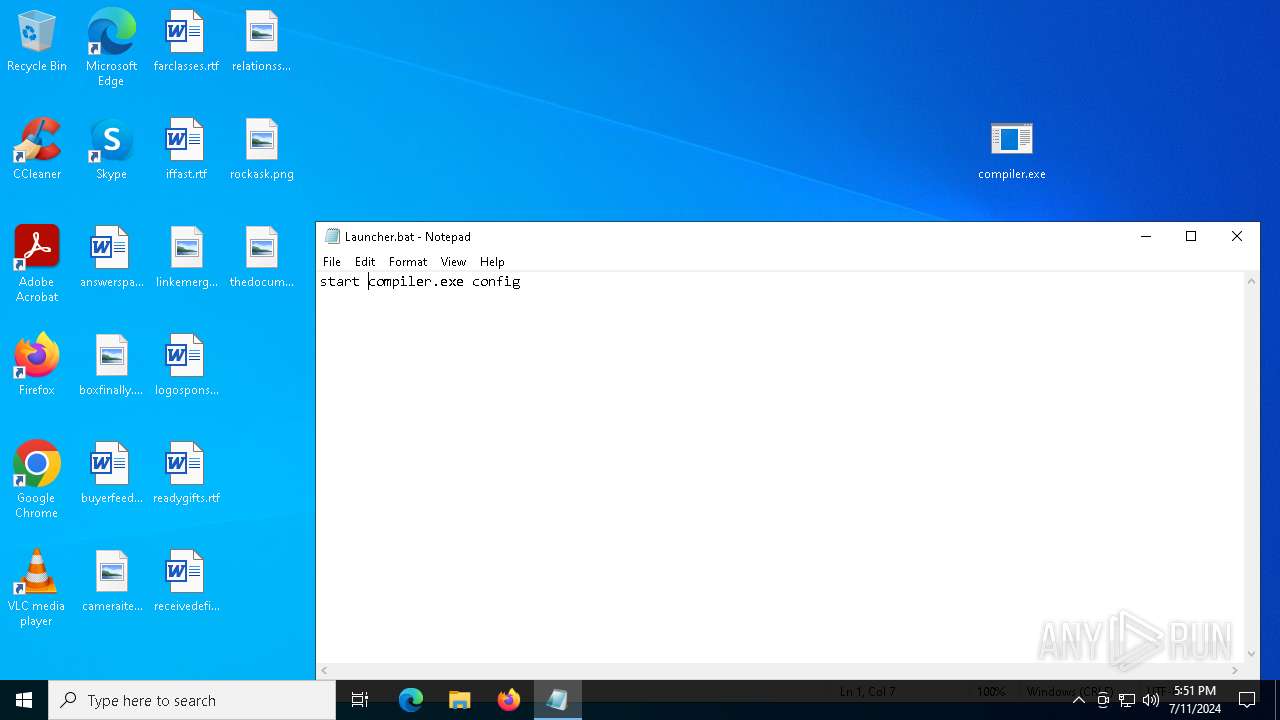
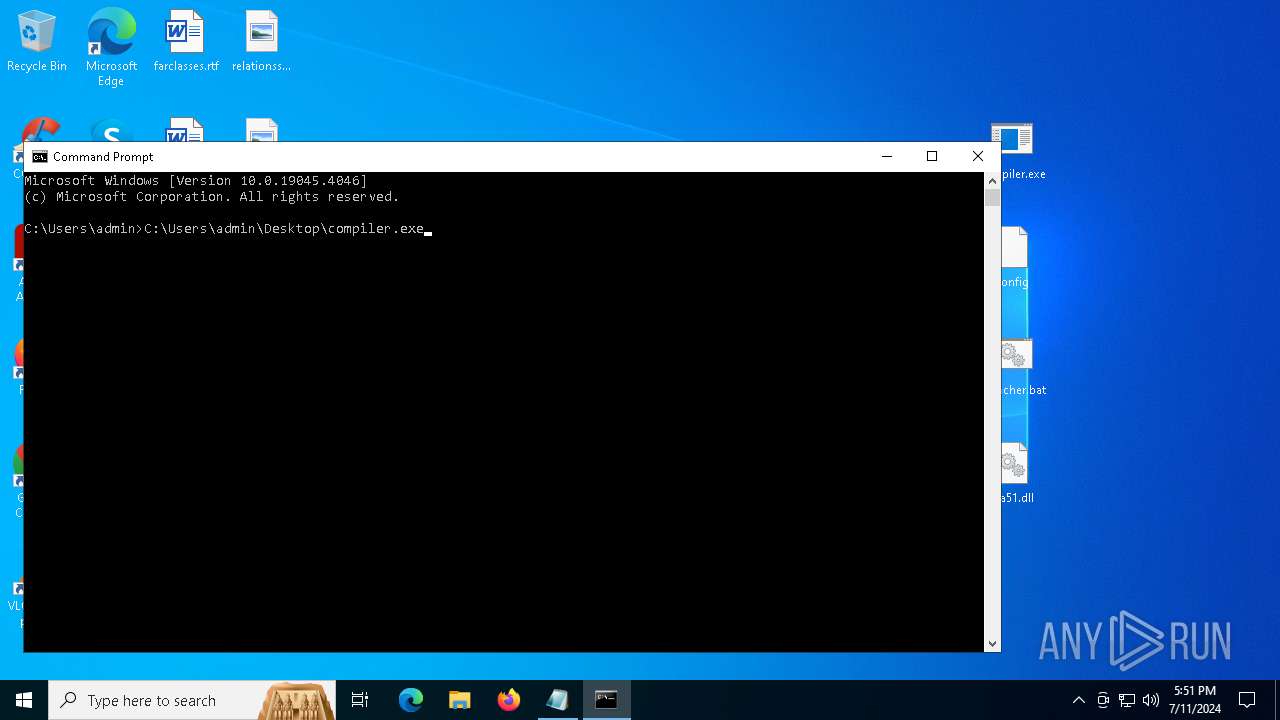
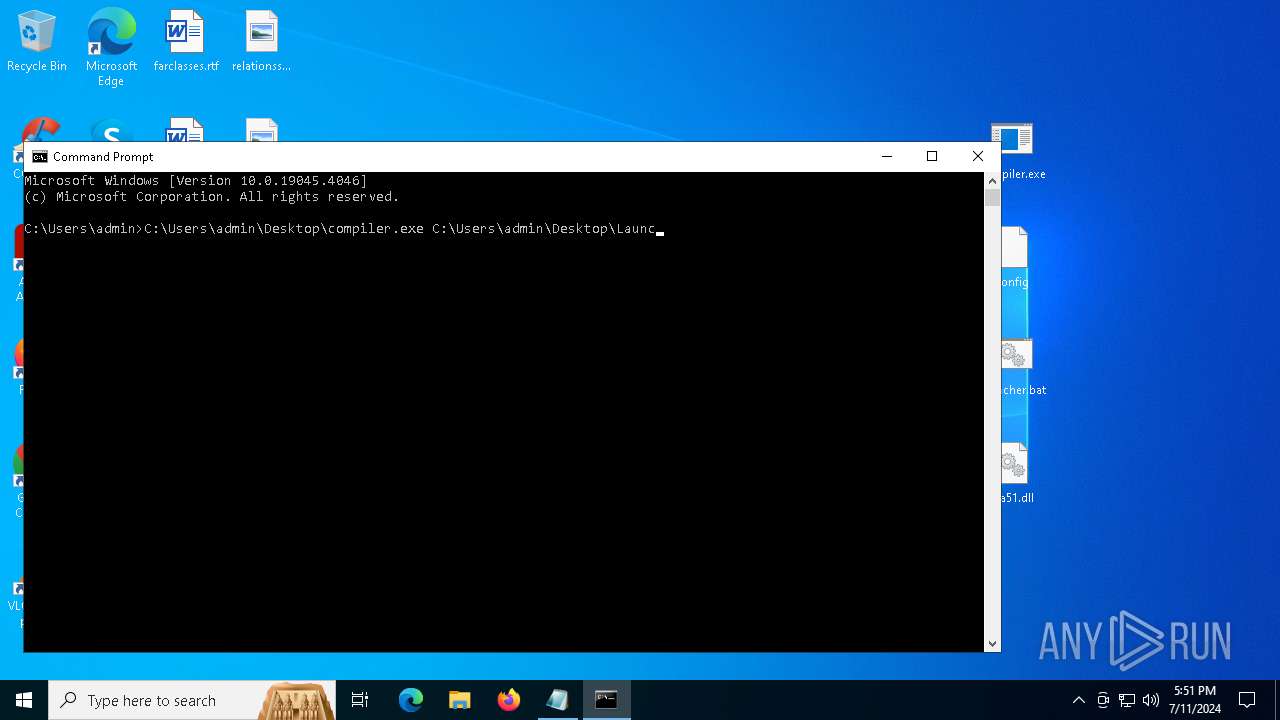
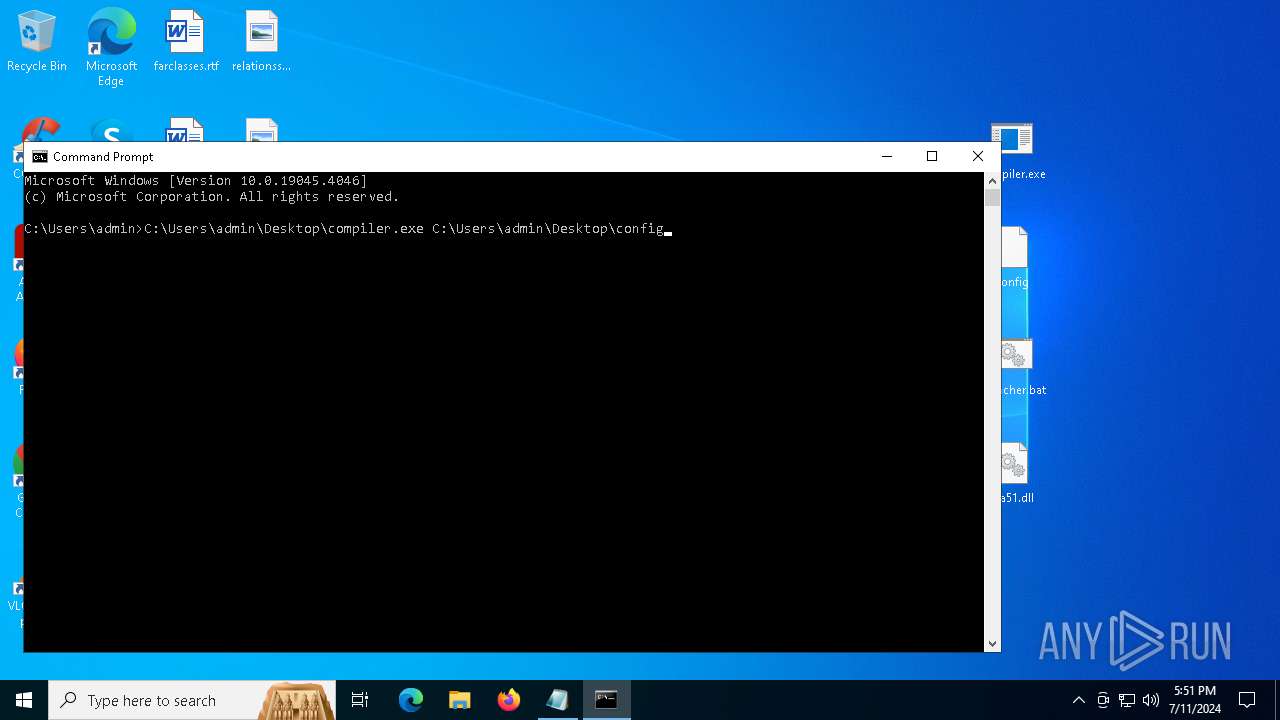
| 2888 | compiler.exe config | C:\Users\admin\Desktop\compiler.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3512 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
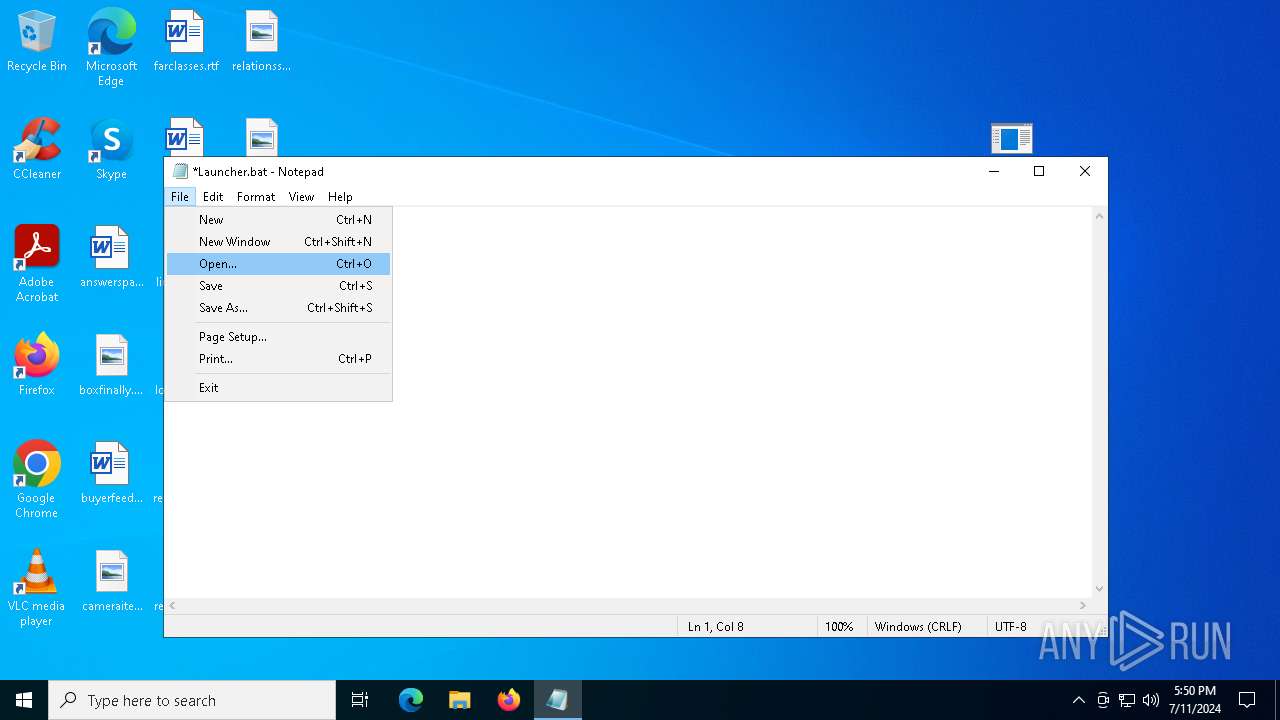
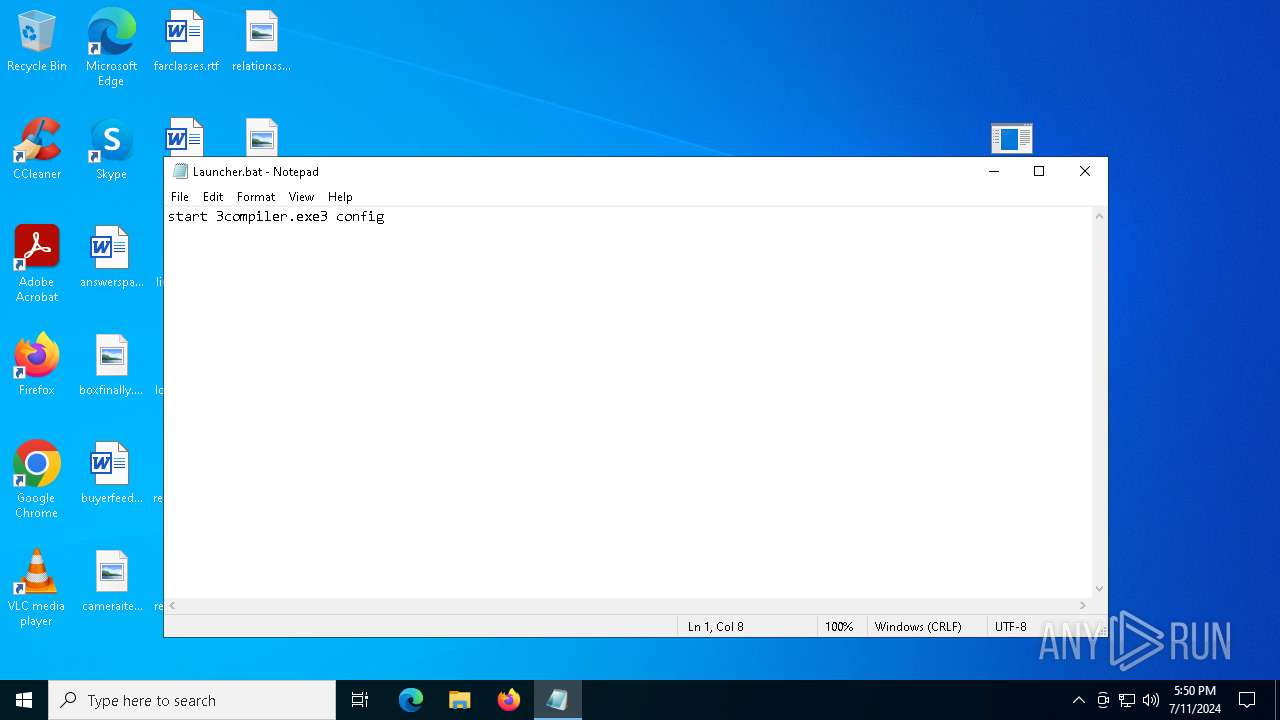
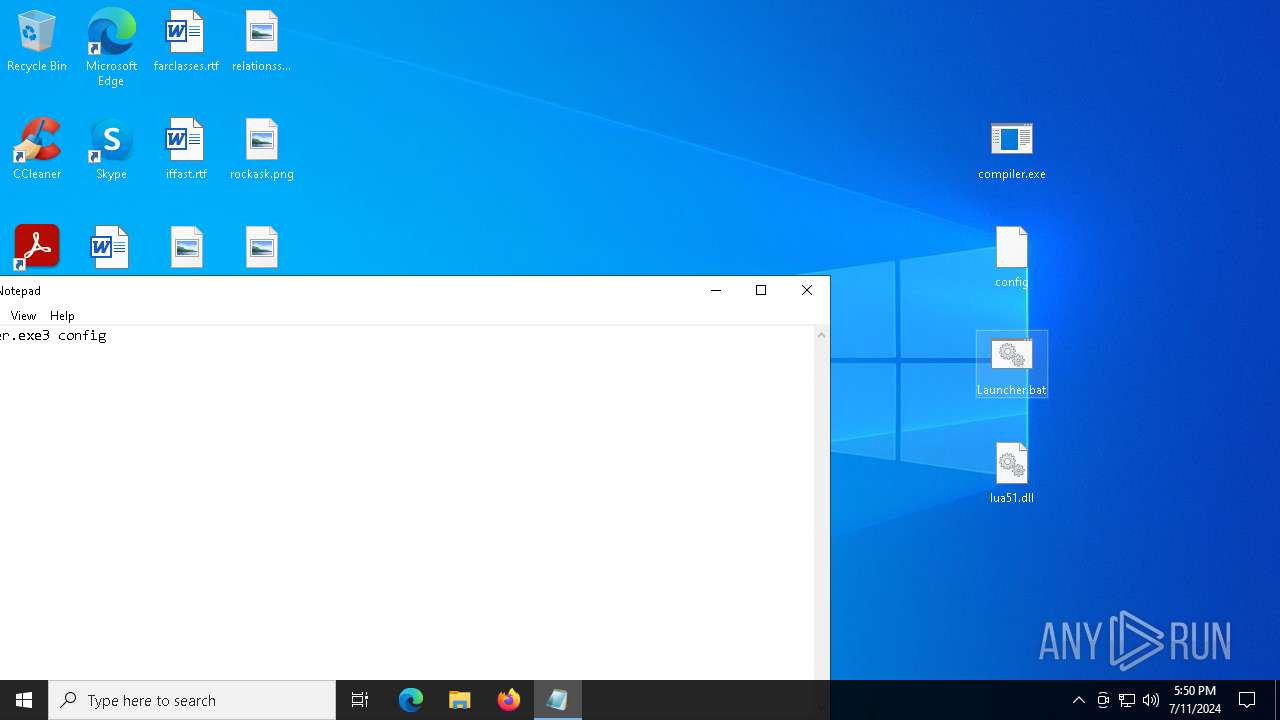
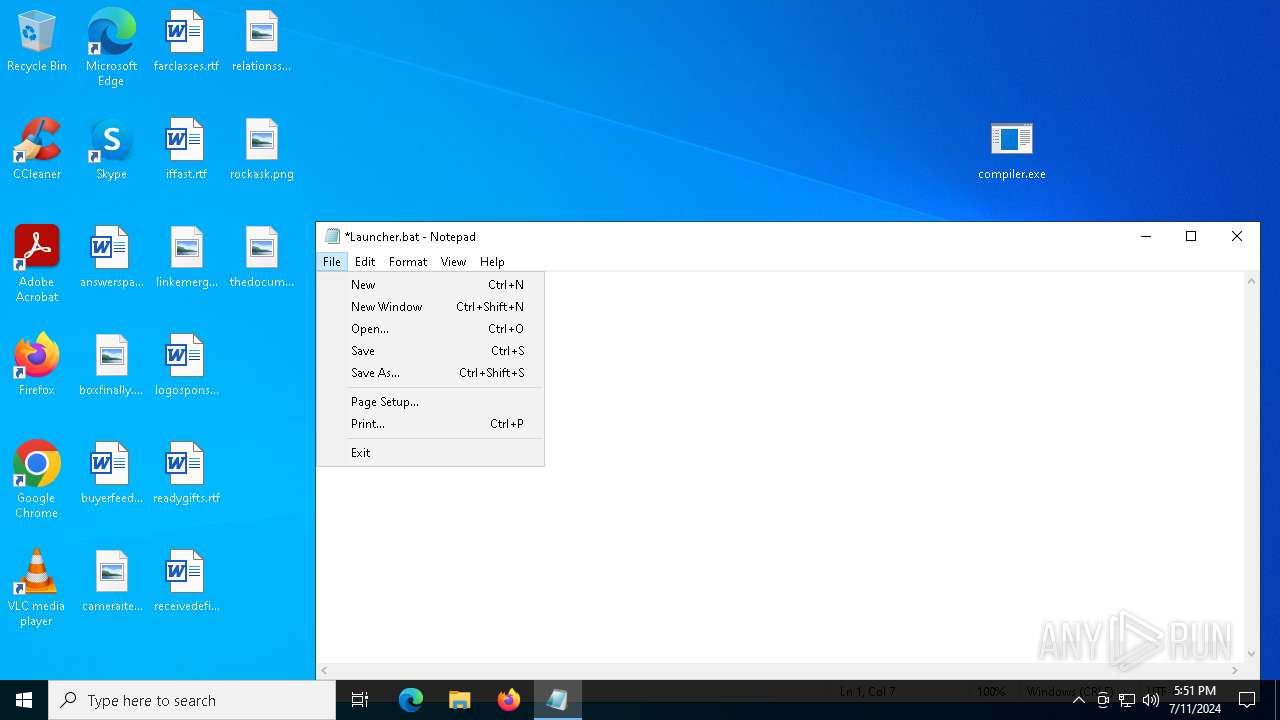
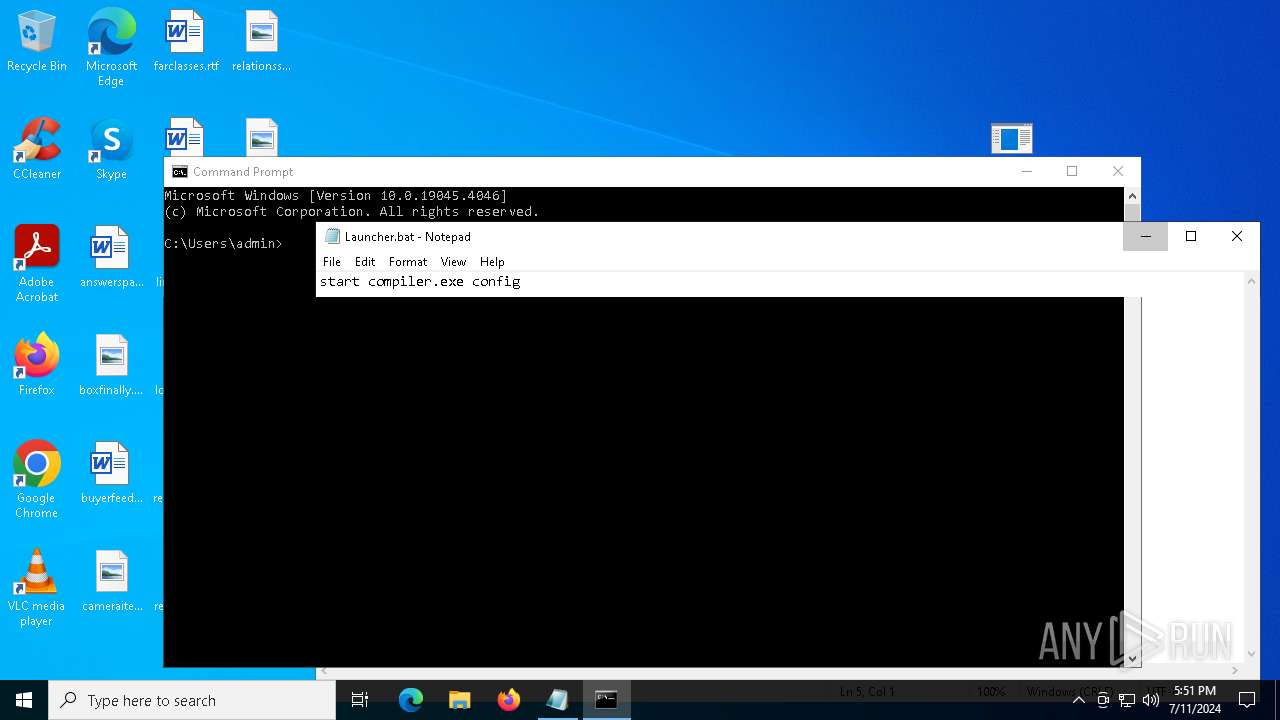
| 3580 | "C:\WINDOWS\System32\NOTEPAD.EXE" C:\Users\admin\Desktop\Launcher.bat | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3596 | "C:\Users\admin\Desktop\compiler.exe" | C:\Users\admin\Desktop\compiler.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3840 | C:\Users\admin\Desktop\compiler.exe C:\Users\admin\Desktop\config | C:\Users\admin\Desktop\compiler.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4052 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Launcher.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4800 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Launcher.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 175
Read events
13 131
Write events
44
Delete events
0
Modification events
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PixelGun.zip | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
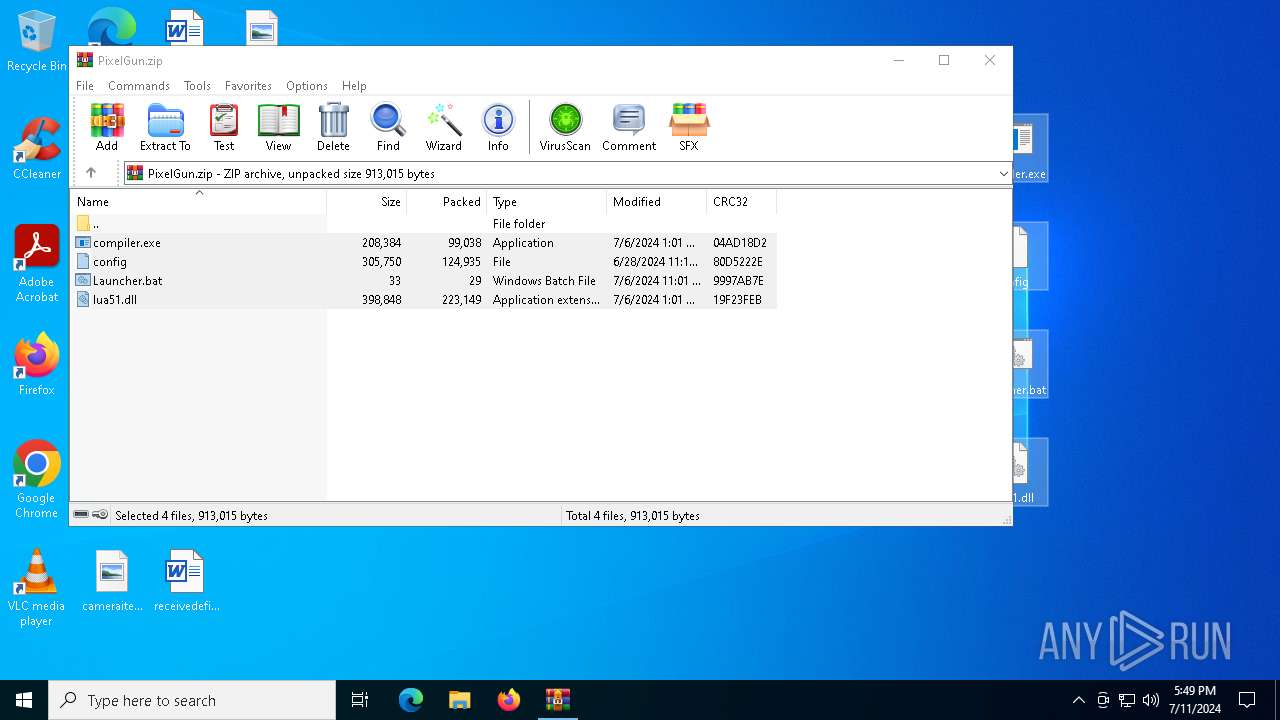
Executable files
2
Suspicious files
4
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 452 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa452.47887\config | text | |
MD5:4AD602C68EB3AA4C84C73834E653605F | SHA256:AA2AC19E959BECA447E34DA002CC63149C208D8427BB8631344EA069F4BBCCBA | |||
| 452 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa452.47887\lua51.dll | executable | |
MD5:6BDA32CF1EA270B6D2E8E7B07DE8B1EE | SHA256:569245D4921E9DA20AB946CA8BC3F6E38E8319CE69296EA227133C3252DB966D | |||
| 2888 | compiler.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\json[1].json | binary | |
MD5:39C3A98170FC9A01DD5B3D716F94B308 | SHA256:9D9A6DEE02529B469CEDCF5C17BF05F503B7351C0C2CC373D1C875EFD617BC3D | |||
| 452 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa452.47887\compiler.exe | executable | |
MD5:38AC56927ACC81BCD95289A96A89A522 | SHA256:677782E0750DEFF17AFE2CF56EC4EAC1182833143C1FE3E8CEB705502FB7CB5A | |||
| 2888 | compiler.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:C076E917EAA6DD7AD5166D7F80687716 | SHA256:E78E6CF2D647A4014499C1818A52595322F1C47102556191711E7E9CFE462D5C | |||
| 3840 | compiler.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\json[1].json | binary | |
MD5:39C3A98170FC9A01DD5B3D716F94B308 | SHA256:9D9A6DEE02529B469CEDCF5C17BF05F503B7351C0C2CC373D1C875EFD617BC3D | |||
| 2888 | compiler.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | der | |
MD5:CA41F63AAAA9EFC35C10C40EDCC3C136 | SHA256:C5B936A87B2850820C050B76930690A8D8D3BC15BB3DA637E9B7F048AFF89E4B | |||
| 452 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa452.47887\Launcher.bat | text | |
MD5:6287E562F249E3713E12136A1FFBD8FA | SHA256:D76B5184C7FE293578AEC681B64D1A72EEC44E28342655F1BF2DCF120F6B7708 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
94
DNS requests
27
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2340 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2340 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2888 | compiler.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2888 | compiler.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | shared |
3688 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6628 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6152 | SIHClient.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6152 | SIHClient.exe | GET | 200 | 2.18.97.123:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2056 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2448 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2340 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4656 | SearchApp.exe | 92.123.104.37:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2340 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2340 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
ip-api.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2888 | compiler.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2168 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3840 | compiler.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2168 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |