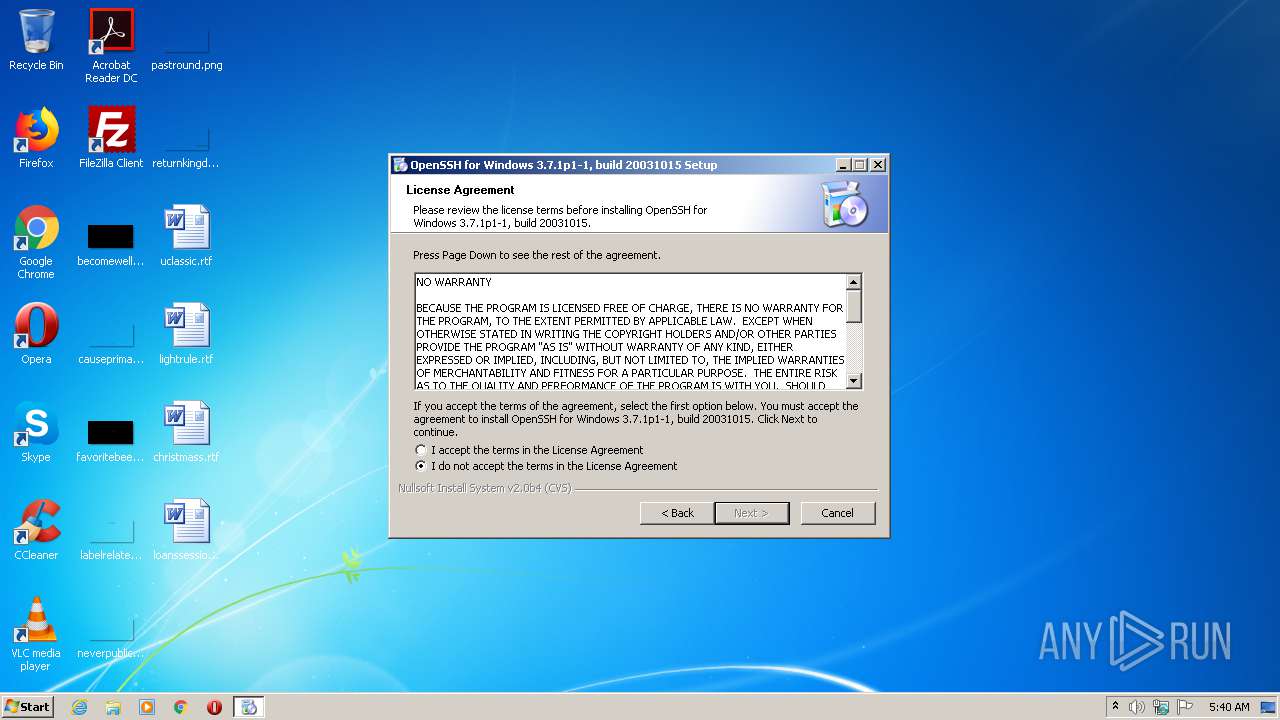
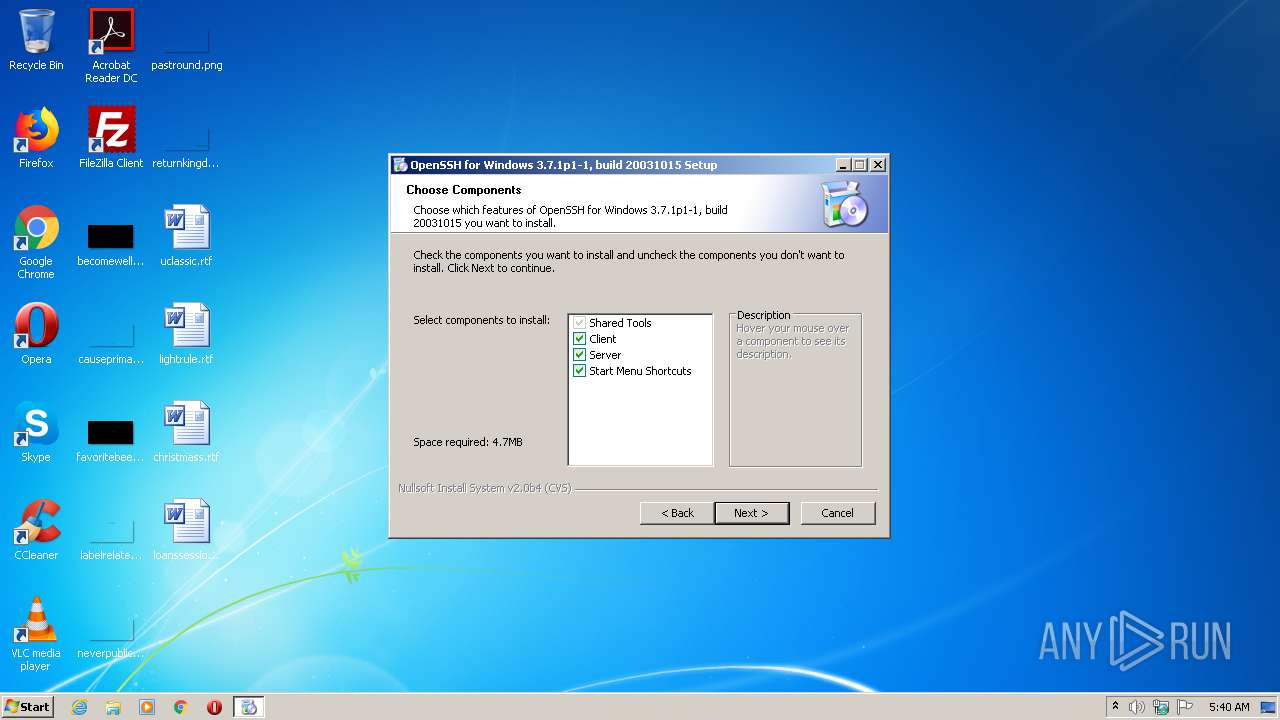
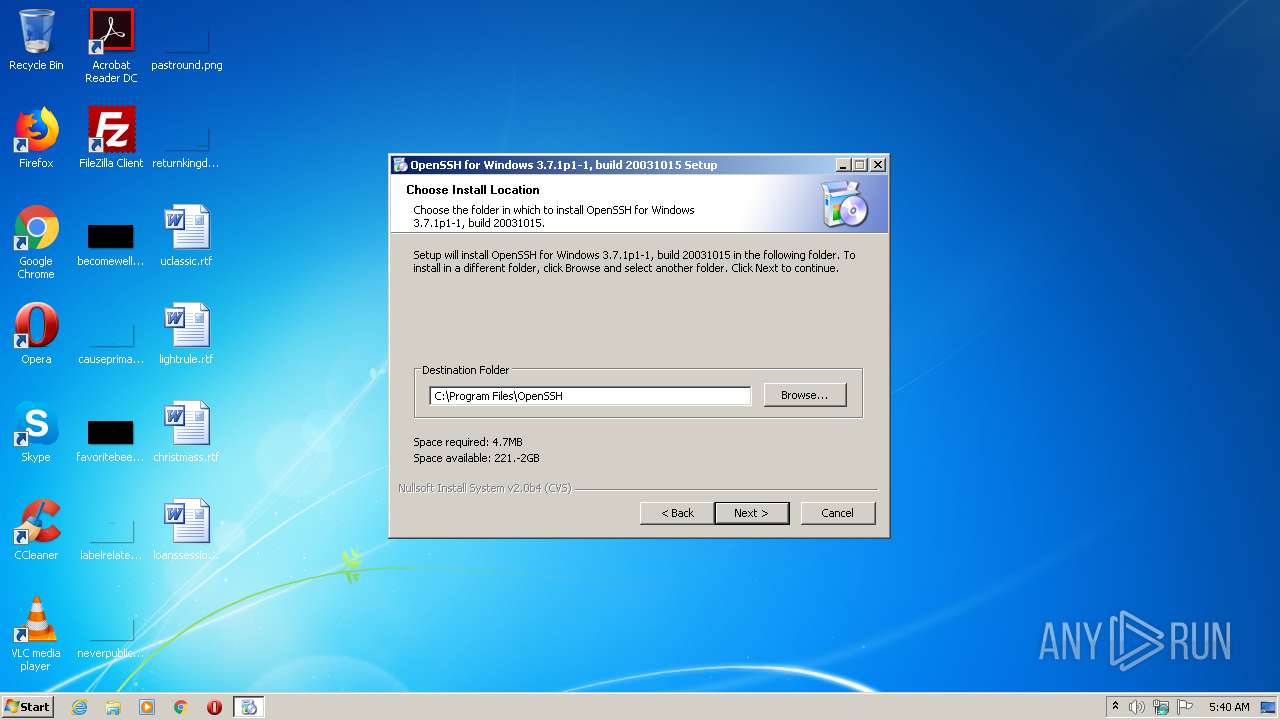
| File name: | setupssh371-20031015.exe |
| Full analysis: | https://app.any.run/tasks/6c5ed936-1449-4d4e-b6e4-12c44a97ae86 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2020, 04:39:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, Nullsoft Installer self-extracting archive |
| MD5: | 0380FCB2C057B62602045034333940D0 |
| SHA1: | E2448EB1EFF2A60DC018387252E0F24064D39C51 |
| SHA256: | 85057F5692180C9B2D65F7B5E37C8A4B111DEFD85A29B2B9A4932261B3A12D8E |
| SSDEEP: | 49152:84zmhY8cy41rqp+vBt19vnFg2i+JTbmoDz58UwumBOffdv:b4irZvBtXvFg2fJTn/5UBev |
MALICIOUS
Detects Cygwin installation
- setupssh371-20031015.exe (PID: 3760)
Loads dropped or rewritten executable
- ssh-keygen.exe (PID: 3544)
- setupssh371-20031015.exe (PID: 3760)
- ssh-keygen.exe (PID: 2620)
- ssh-keygen.exe (PID: 3596)
- cygrunsrv.exe (PID: 3228)
Application was dropped or rewritten from another process
- ns3134.tmp (PID: 3572)
- ssh-keygen.exe (PID: 3544)
- ns2A8C.tmp (PID: 2524)
- ssh-keygen.exe (PID: 3596)
- ns35BA.tmp (PID: 3528)
- ns3319.tmp (PID: 2516)
- ns3A12.tmp (PID: 1800)
- ns37EE.tmp (PID: 3868)
- cygrunsrv.exe (PID: 3228)
- ssh-keygen.exe (PID: 2620)
SUSPICIOUS
Executable content was dropped or overwritten
- setupssh371-20031015.exe (PID: 3760)
Starts application with an unusual extension
- setupssh371-20031015.exe (PID: 3760)
Creates files in the program directory
- ssh-keygen.exe (PID: 3544)
- ssh-keygen.exe (PID: 2620)
- ssh-keygen.exe (PID: 3596)
- setupssh371-20031015.exe (PID: 3760)
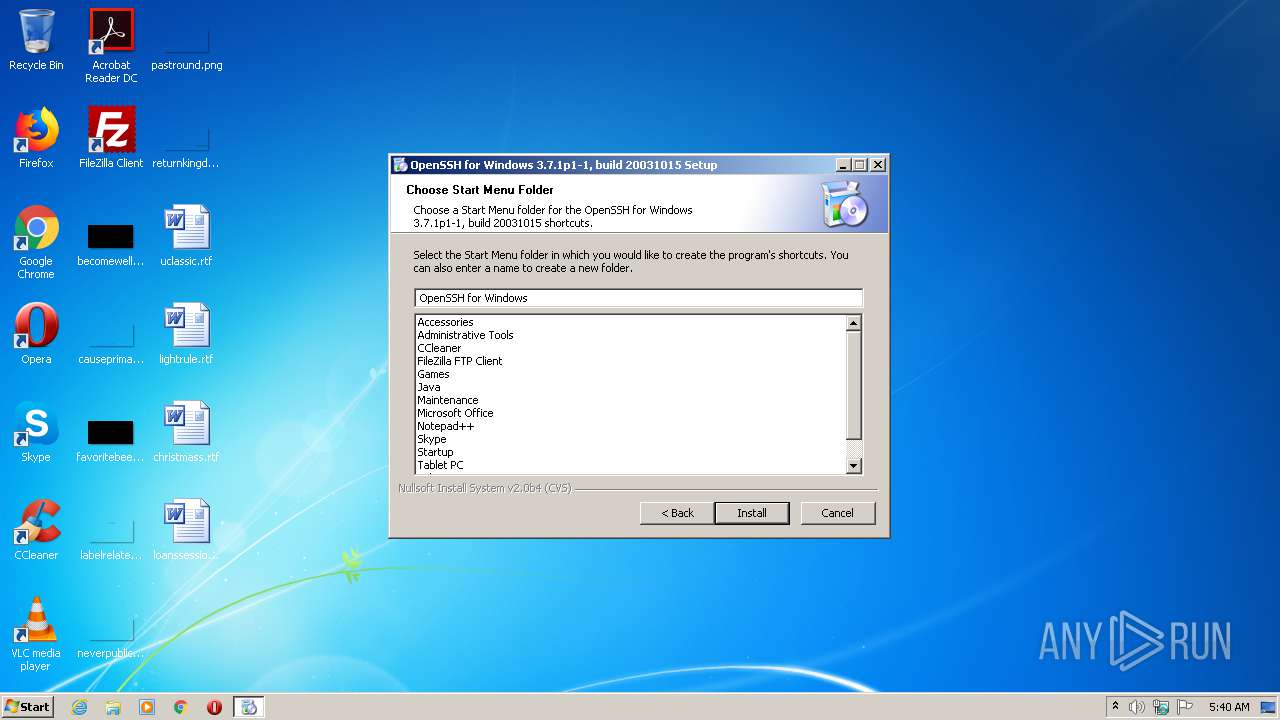
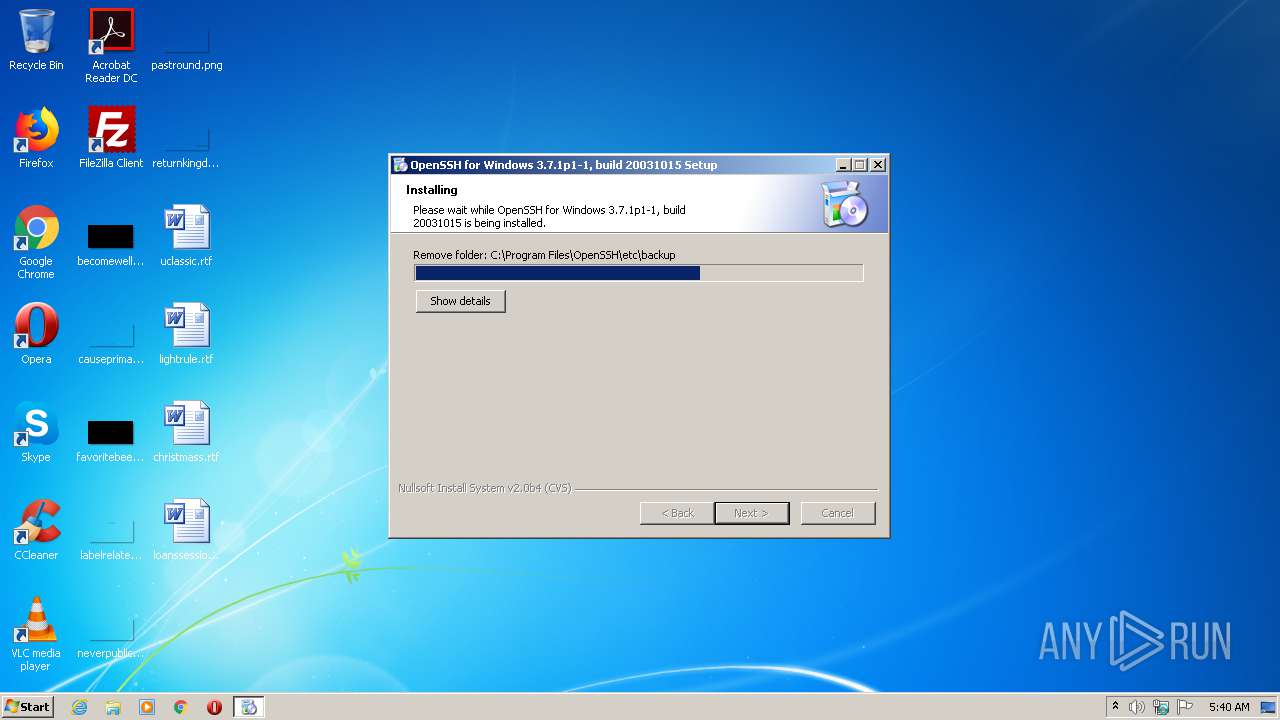
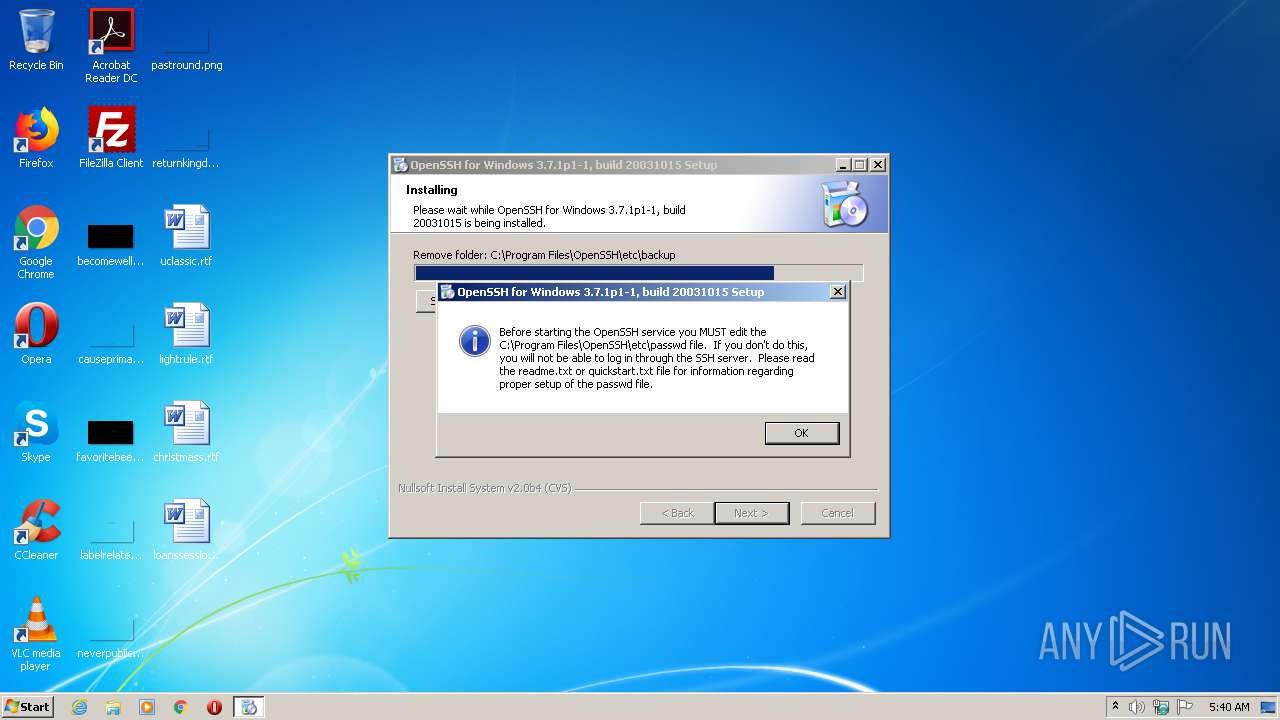
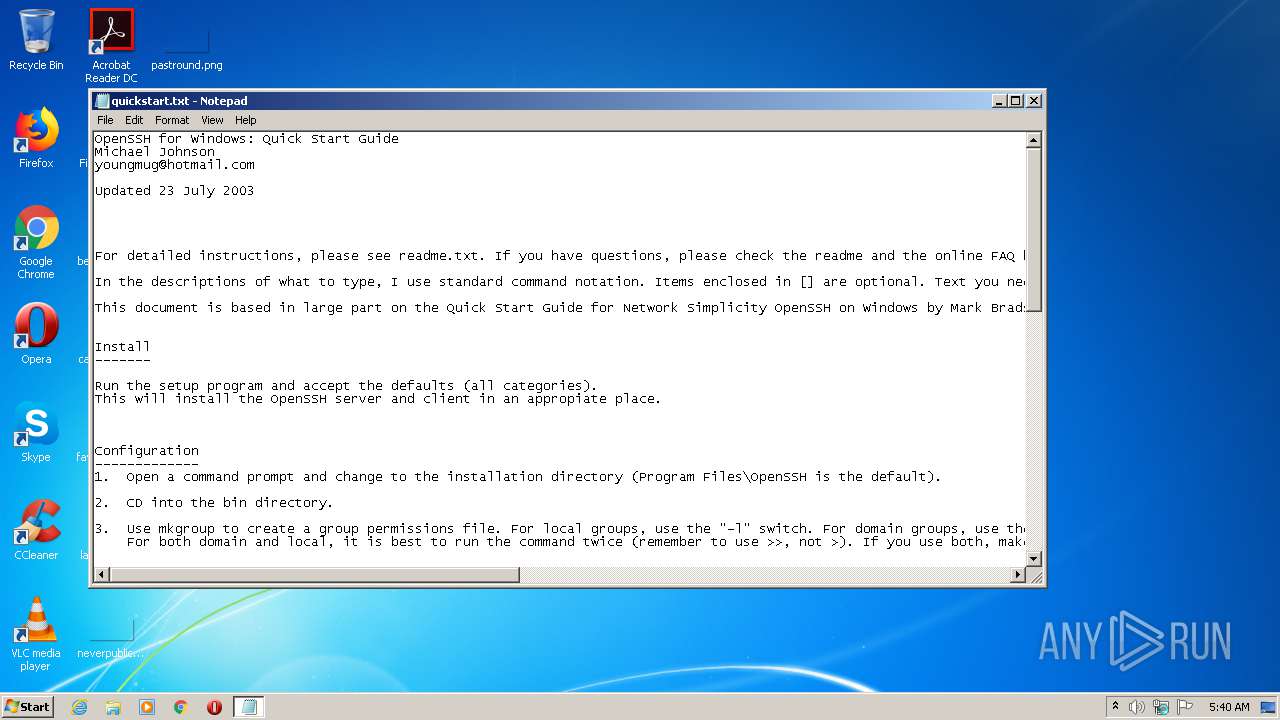
Creates a software uninstall entry
- setupssh371-20031015.exe (PID: 3760)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2003:09:23 22:04:25+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | 3837952 |
| EntryPoint: | 0x3aec30 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Sep-2003 20:04:25 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-Sep-2003 20:04:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x003A9000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x003AA000 | 0x00005000 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.82049 |
.rsrc | 0x003AF000 | 0x00007000 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.86466 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13905 | 540 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.34688 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 4.08356 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 6.5129 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.72198 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.61913 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.11499 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 5.62416 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 6.05238 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
56
Monitored processes
15
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1800 | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ns3A12.tmp C:\Program Files\OpenSSH\bin\cygrunsrv --install OpenSSHd --path /usr/sbin/sshd --args "-D" --dep "Tcpip" --stderr "/var/log/opensshd.log" --env "CYGWIN=binmode ntsec tty" --disp "OpenSSH Server" | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ns3A12.tmp | — | setupssh371-20031015.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2516 | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ns3319.tmp C:\Program Files\OpenSSH\bin\ssh-keygen.exe -t rsa -f /etc/ssh_host_rsa_key -N "" | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ns3319.tmp | — | setupssh371-20031015.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2524 | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ns2A8C.tmp C:\Program Files\OpenSSH\bin\ssh-keygen.exe -t dsa -f /etc/ssh_host_dsa_key -N "" | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ns2A8C.tmp | — | setupssh371-20031015.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2572 | cacls "C:\Program Files\OpenSSH" /E /T /G USER-PC\admin:F | C:\Windows\system32\cacls.exe | — | ns35BA.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\OpenSSH\bin\ssh-keygen.exe" -t rsa1 -f /etc/ssh_host_key -N "" | C:\Program Files\OpenSSH\bin\ssh-keygen.exe | — | ns3134.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2936 | cacls "C:\Program Files\OpenSSH" /E /T /G SYSTEM:F | C:\Windows\system32\cacls.exe | — | ns37EE.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\setupssh371-20031015.exe" | C:\Users\admin\AppData\Local\Temp\setupssh371-20031015.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\OpenSSH\bin\cygrunsrv" --install OpenSSHd --path /usr/sbin/sshd --args "-D" --dep "Tcpip" --stderr "/var/log/opensshd.log" --env "CYGWIN=binmode ntsec tty" --disp "OpenSSH Server" | C:\Program Files\OpenSSH\bin\cygrunsrv.exe | — | ns3A12.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3528 | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ns35BA.tmp cacls "C:\Program Files\OpenSSH" /E /T /G USER-PC\admin:F | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ns35BA.tmp | — | setupssh371-20031015.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3544 | "C:\Program Files\OpenSSH\bin\ssh-keygen.exe" -t dsa -f /etc/ssh_host_dsa_key -N "" | C:\Program Files\OpenSSH\bin\ssh-keygen.exe | — | ns2A8C.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
294
Read events
269
Write events
25
Delete events
0
Modification events
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Cygnus Solutions\Cygwin\Program Options |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Cygnus Solutions\Cygwin\mounts v2\/ |
| Operation: | write | Name: | native |
Value: C:\Program Files\OpenSSH | |||
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Cygnus Solutions\Cygwin\mounts v2\/ |
| Operation: | write | Name: | flags |
Value: 10 | |||
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Cygnus Solutions\Cygwin\mounts v2\/usr/bin |
| Operation: | write | Name: | native |
Value: C:\Program Files\OpenSSH/bin | |||
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Cygnus Solutions\Cygwin\mounts v2\/usr/bin |
| Operation: | write | Name: | flags |
Value: 10 | |||
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Cygnus Solutions\Cygwin\mounts v2\/home |
| Operation: | write | Name: | native |
Value: C:\Users\admin\AppData\Roaming\Microsoft | |||
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Cygnus Solutions\Cygwin\mounts v2\/home |
| Operation: | write | Name: | flags |
Value: 10 | |||
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | CYGWIN |
Value: tty | |||
| (PID) Process: | (3760) setupssh371-20031015.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | PATH |
Value: C:\ProgramData\Oracle\Java\javapath;%SystemRoot%\system32;%SystemRoot%;%SystemRoot%\System32\Wbem;%SYSTEMROOT%\System32\WindowsPowerShell\v1.0\;C:\Program Files\OpenSSH\bin | |||
| (PID) Process: | (3228) cygrunsrv.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\OpenSSHd\Parameters |
| Operation: | write | Name: | AppPath |
Value: /usr/sbin/sshd | |||
Executable files
40
Suspicious files
2
Text files
54
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3760 | setupssh371-20031015.exe | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3760 | setupssh371-20031015.exe | C:\Program Files\OpenSSH\bin\cygintl-2.dll | executable | |
MD5:1937654F5536A1DF5CE064BDBACBF59B | SHA256:CA618177D22DA0199B73183197FDD4FF4B103DEBA3AEBEF7CC5D8A02BD92A835 | |||
| 3760 | setupssh371-20031015.exe | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\InstallOptions.dll | executable | |
MD5:87728CB9E26FE22E2E829826A166982E | SHA256:16F100E89203E206802E945E8EC16DDD01C6A53B3E256C66140315CA644EF2EF | |||
| 3760 | setupssh371-20031015.exe | C:\Program Files\OpenSSH\bin\chown.exe | executable | |
MD5:2AC927C963FF7FAB4DE98C66870C0BB3 | SHA256:744567E95006D19FA6397F20B6949C2098BBFB0DF9791399B352AF1026AB2F46 | |||
| 3760 | setupssh371-20031015.exe | C:\Users\admin\AppData\Local\Temp\nsuEFB4.tmp\StartMenu.dll | executable | |
MD5:05662C9C0D124B4B57D33CA1A0A2C47E | SHA256:C835831ECC2E8D1D75CECD8270043F670F1AA8CC73BA2ED03299CD4F553FB235 | |||
| 3760 | setupssh371-20031015.exe | C:\Program Files\OpenSSH\bin\ssh-agent.exe | executable | |
MD5:509CAD6C4C5C48DF2C49F3BF16C874D1 | SHA256:279A207FC873CB5EA64A848B80609C40CFDCA39944071AEA156C03E68548D692 | |||
| 3760 | setupssh371-20031015.exe | C:\Program Files\OpenSSH\bin\ssh-keygen.exe | executable | |
MD5:A6D7E6A2081E22330566D82CD3016253 | SHA256:7C410A3480FAC95EC2D391C7BAC2DA1FF54ABFDF5BE674EC143197C54026CFD1 | |||
| 3760 | setupssh371-20031015.exe | C:\Program Files\OpenSSH\bin\cygiconv-2.dll | executable | |
MD5:7D5011DFAE2C3C025A65B9DFEC1AC3B2 | SHA256:051C9C71C6206C8CFB986F71D2F0112CF20186004495A44D38D72B2E70E83929 | |||
| 3760 | setupssh371-20031015.exe | C:\Program Files\OpenSSH\bin\chmod.exe | executable | |
MD5:1A0BFA6985CDF2EC9F251ED498CE95C5 | SHA256:0593F2020F361376E024EDB2DD082536C4639CBC3BFB234870DB3AD1C5108F14 | |||
| 3760 | setupssh371-20031015.exe | C:\Program Files\OpenSSH\bin\scp.exe | executable | |
MD5:EC3BF7B6D55AAF8ECF822FBFEDAA0104 | SHA256:7251F4CCBE6E7281007B3031E05FD25E4332D5E08F8D36F2B81F0E8470B0885F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report