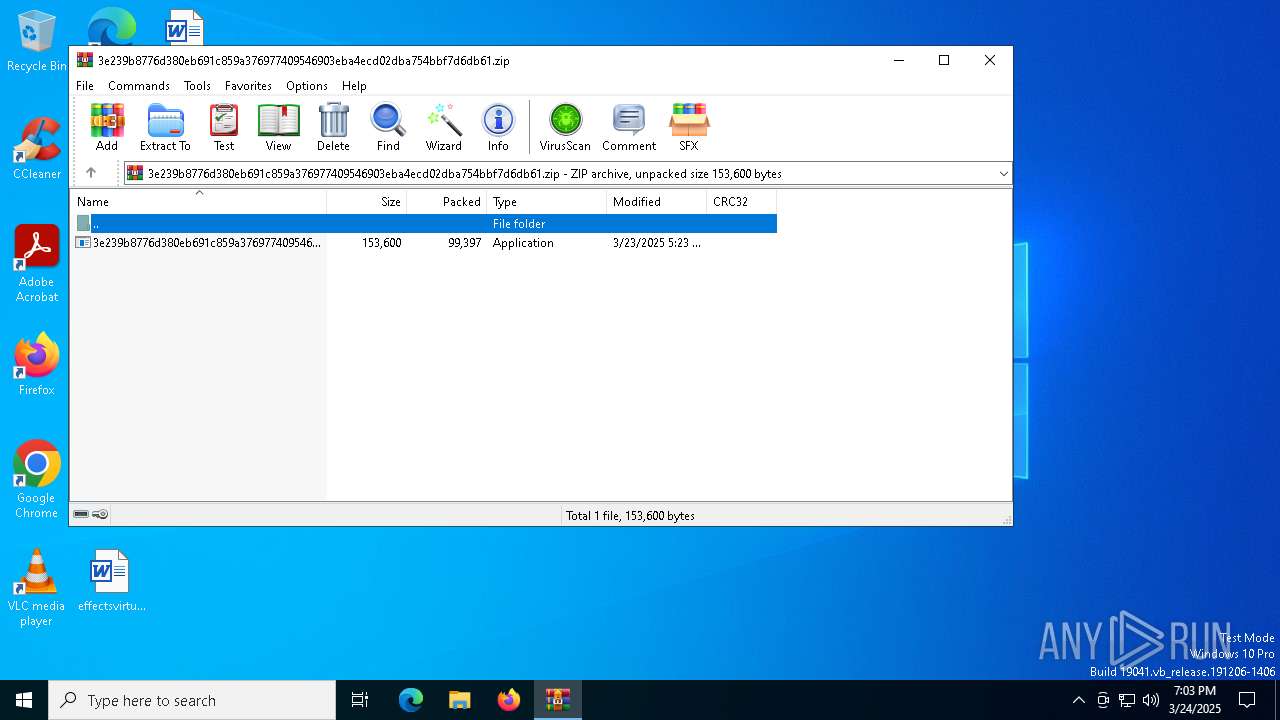
| File name: | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.zip |
| Full analysis: | https://app.any.run/tasks/e9048a41-3cfd-4e5e-97d9-12e4c32213ac |
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | March 24, 2025, 19:03:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 256A5E50FC64289A6A38A1B0052AF12F |
| SHA1: | 3D2B8E82CE239AE1842FB71C99E4A5F9EDBA2936 |
| SHA256: | 84FA579A94BE8C050B9EE9D92623BDECDCEFB31330AD8EEA6AFC13EC37CEB154 |
| SSDEEP: | 3072:OFS3pfk5aUw6BWeZDiWJtTUfCbdxz3nSBxtQo0l+q:OSNk5agQeZDiWJt6+xzXKTQo0l+q |
MALICIOUS
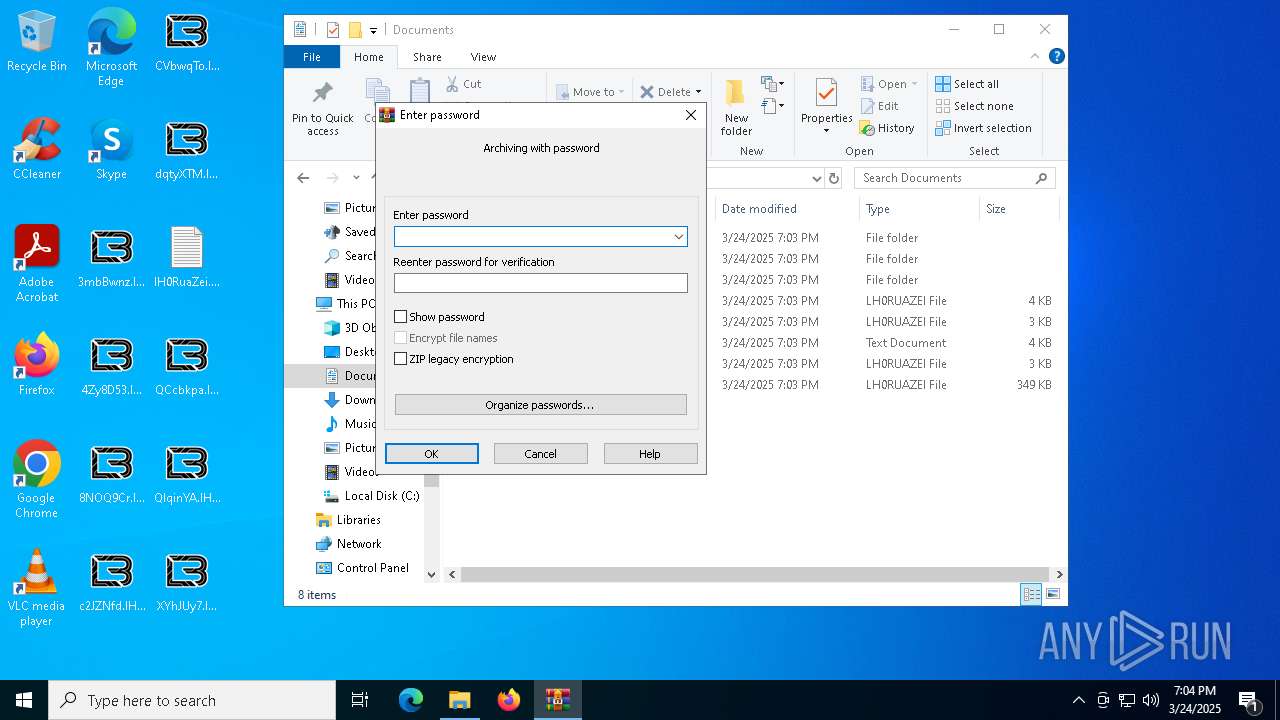
Generic archive extractor
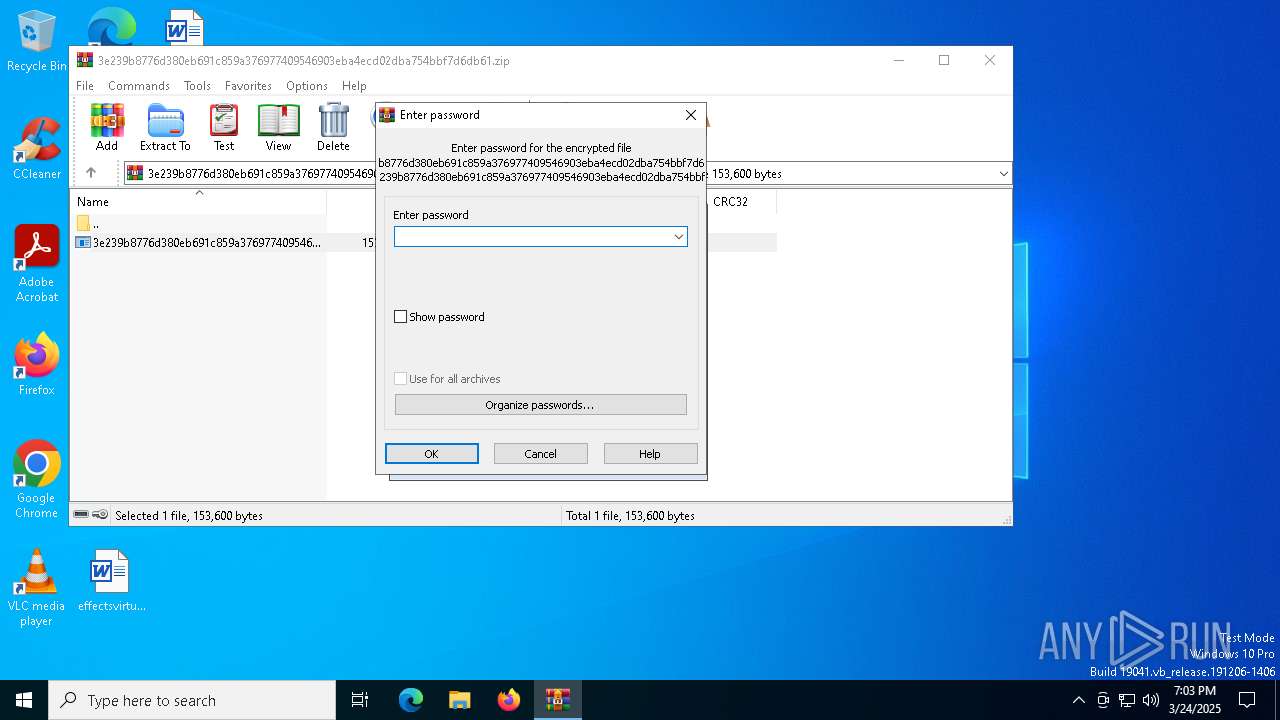
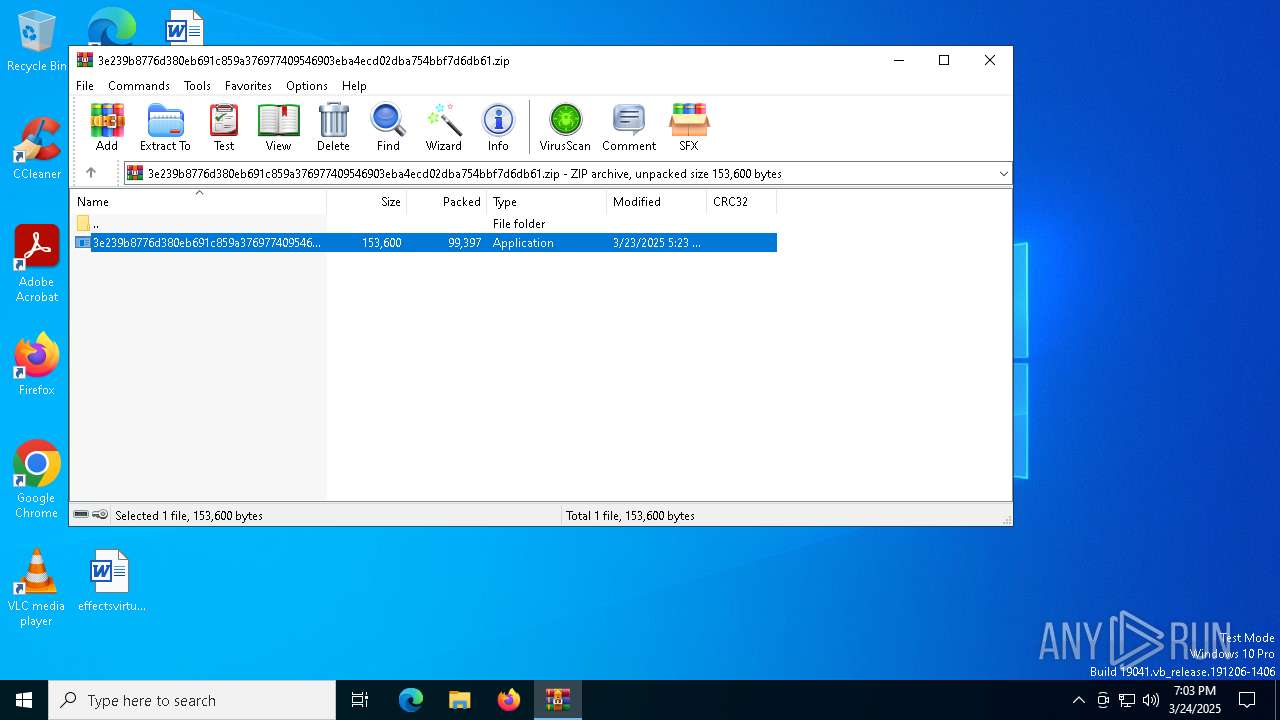
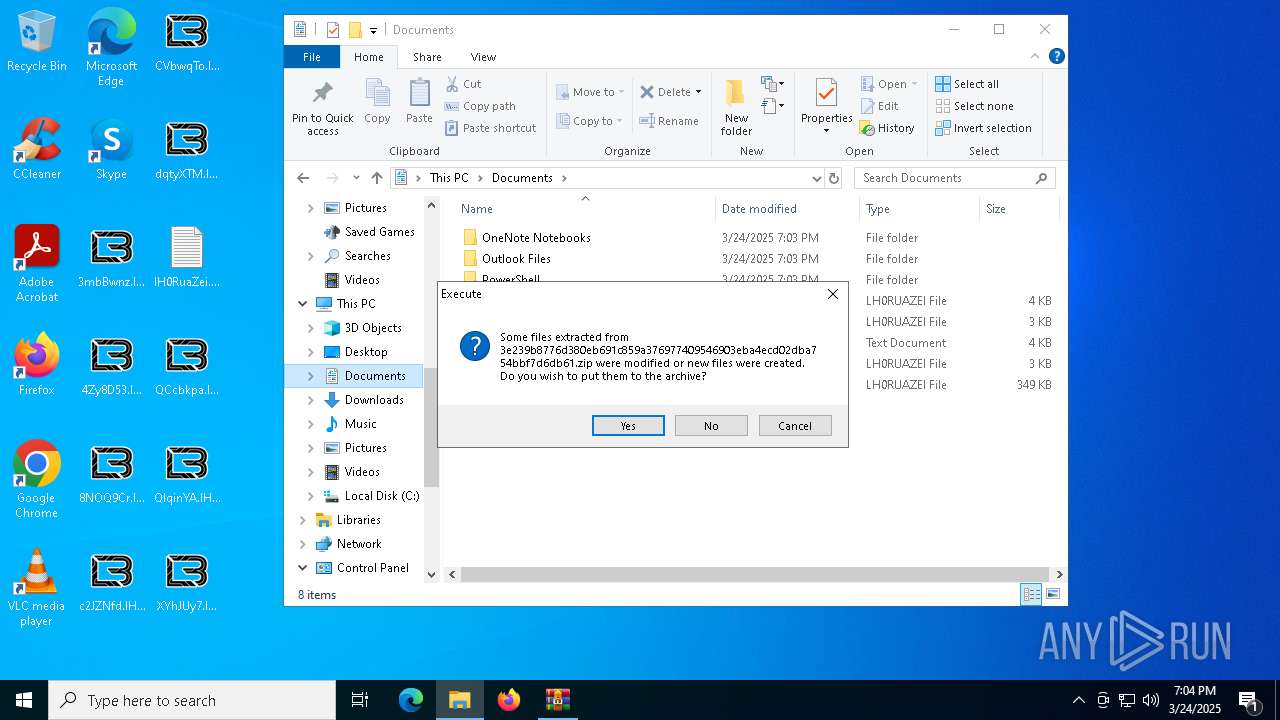
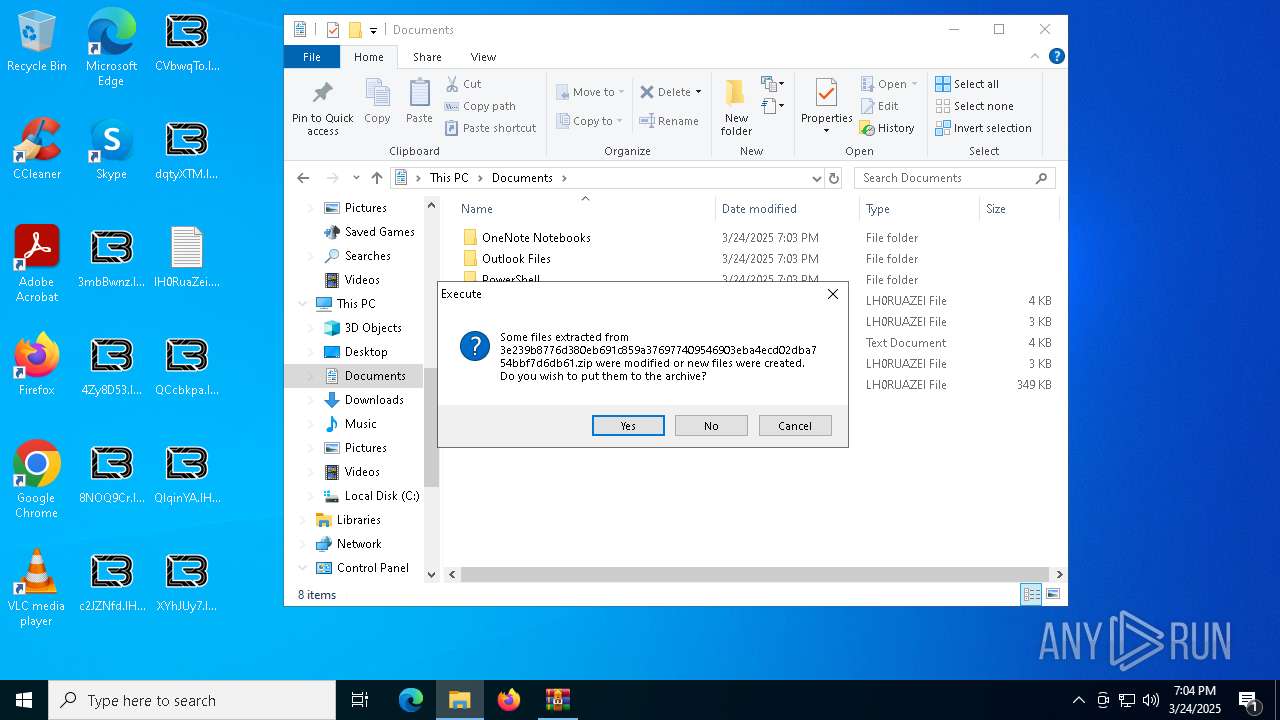
- WinRAR.exe (PID: 7412)
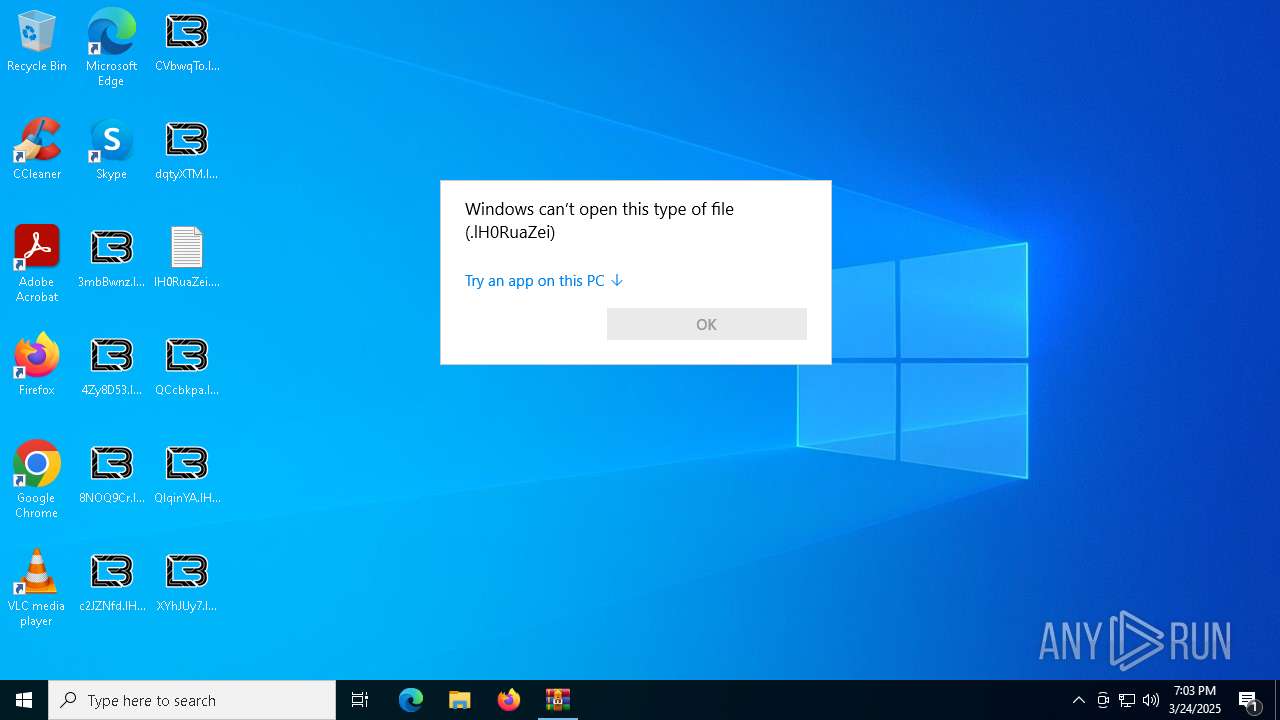
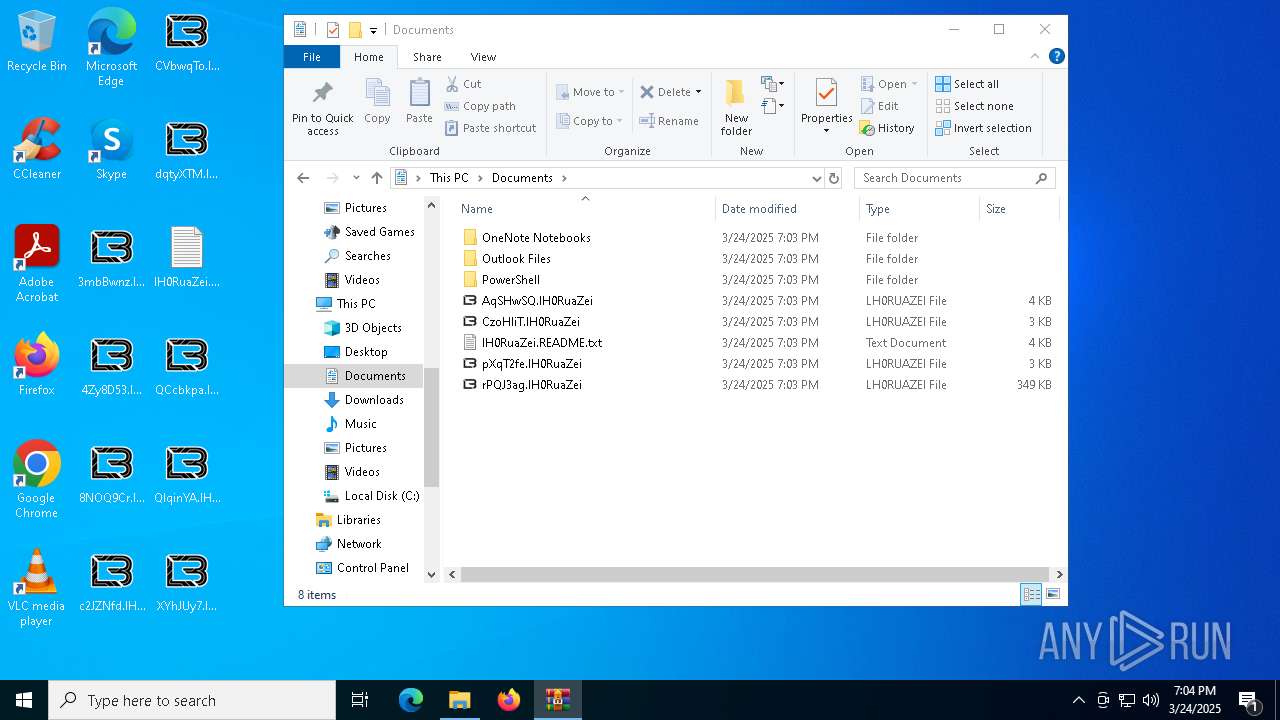
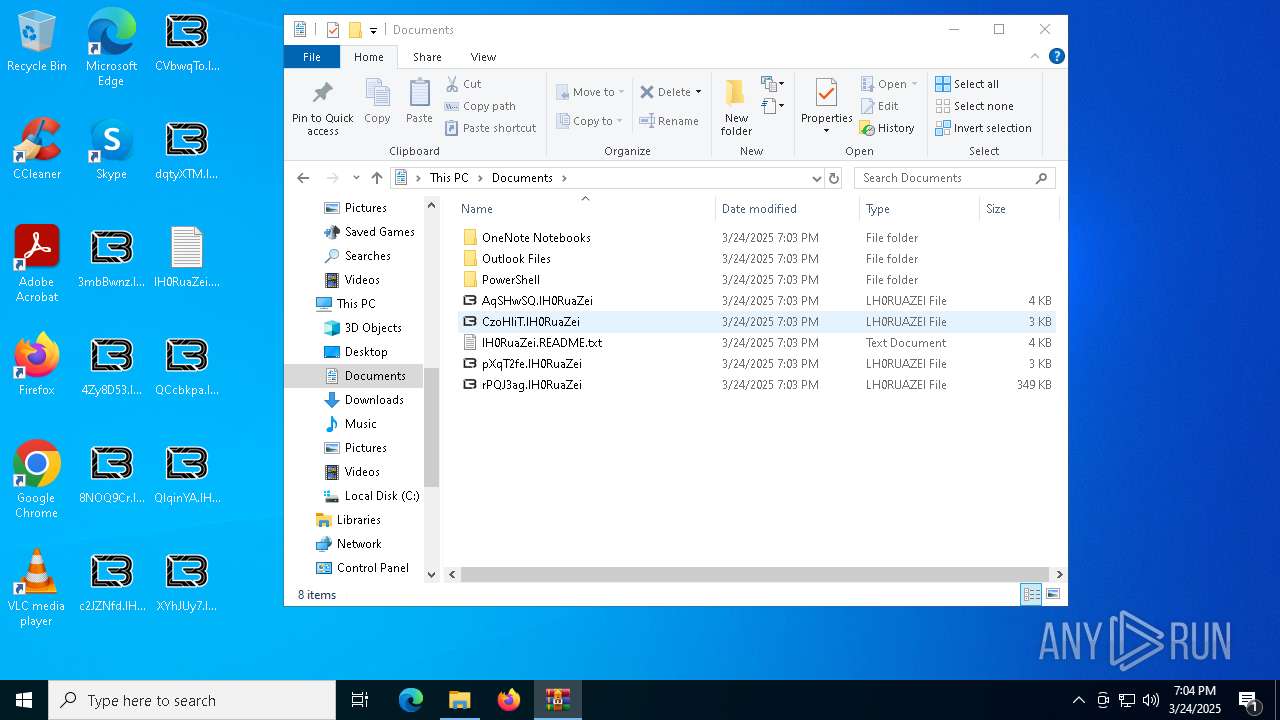
RANSOMWARE has been detected
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 6264)
[YARA] LockBit is detected
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 6264)
Actions looks like stealing of personal data
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 6264)
Known privilege escalation attack
- dllhost.exe (PID: 7376)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7412)
Write to the desktop.ini file (may be used to cloak folders)
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 6264)
There is functionality for taking screenshot (YARA)
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 6264)
INFO
Checks supported languages
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 1676)
- SearchApp.exe (PID: 6040)
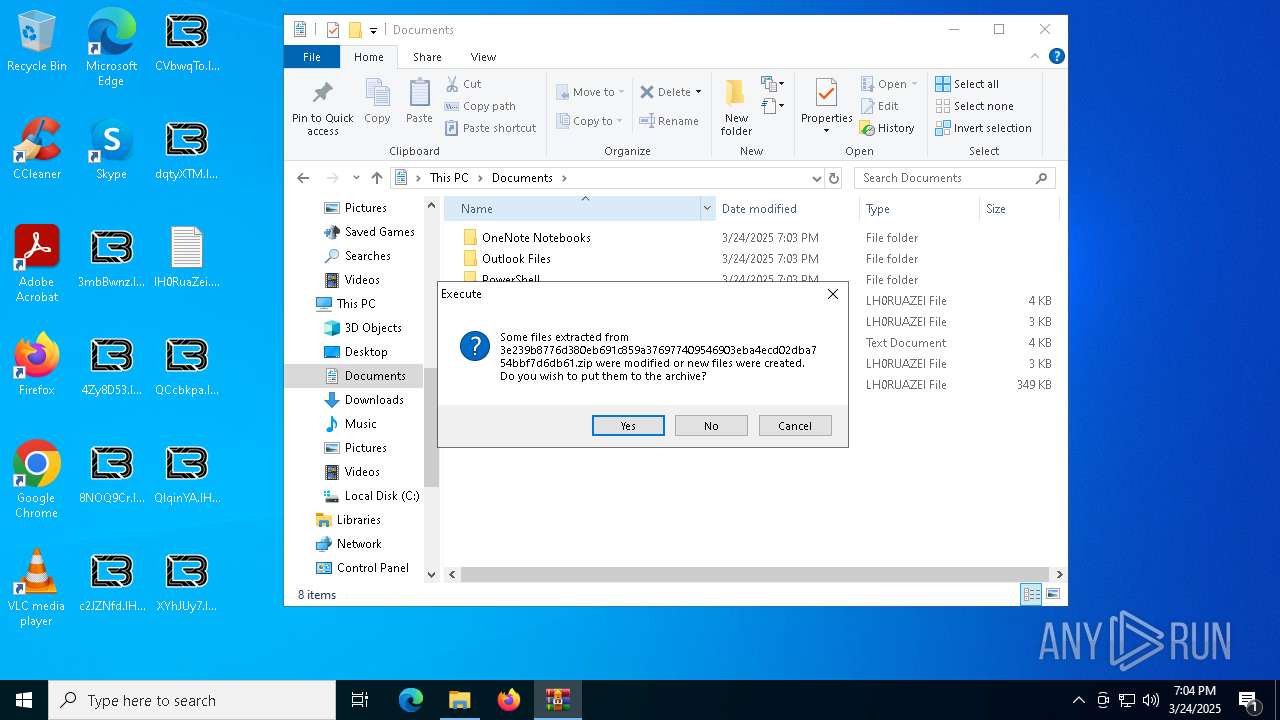
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7412)
Reads the machine GUID from the registry
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 1676)
Creates files in the program directory
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 6264)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7764)
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 6264)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7764)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7764)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7764)
Create files in a temporary directory
- 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe (PID: 6264)
Process checks computer location settings
- SearchApp.exe (PID: 6040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:03:23 05:23:14 |
| ZipCRC: | 0x932956c5 |
| ZipCompressedSize: | 99397 |
| ZipUncompressedSize: | 153600 |
| ZipFileName: | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe |
Total processes
152
Monitored processes
15
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb7412.30829\3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb7412.30829\3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4776 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6040 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb7412.30829\3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb7412.30829\3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6744 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6964 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7376 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7412 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7600 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7612 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 248
Read events
9 174
Write events
73
Delete events
1
Modification events
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7376) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
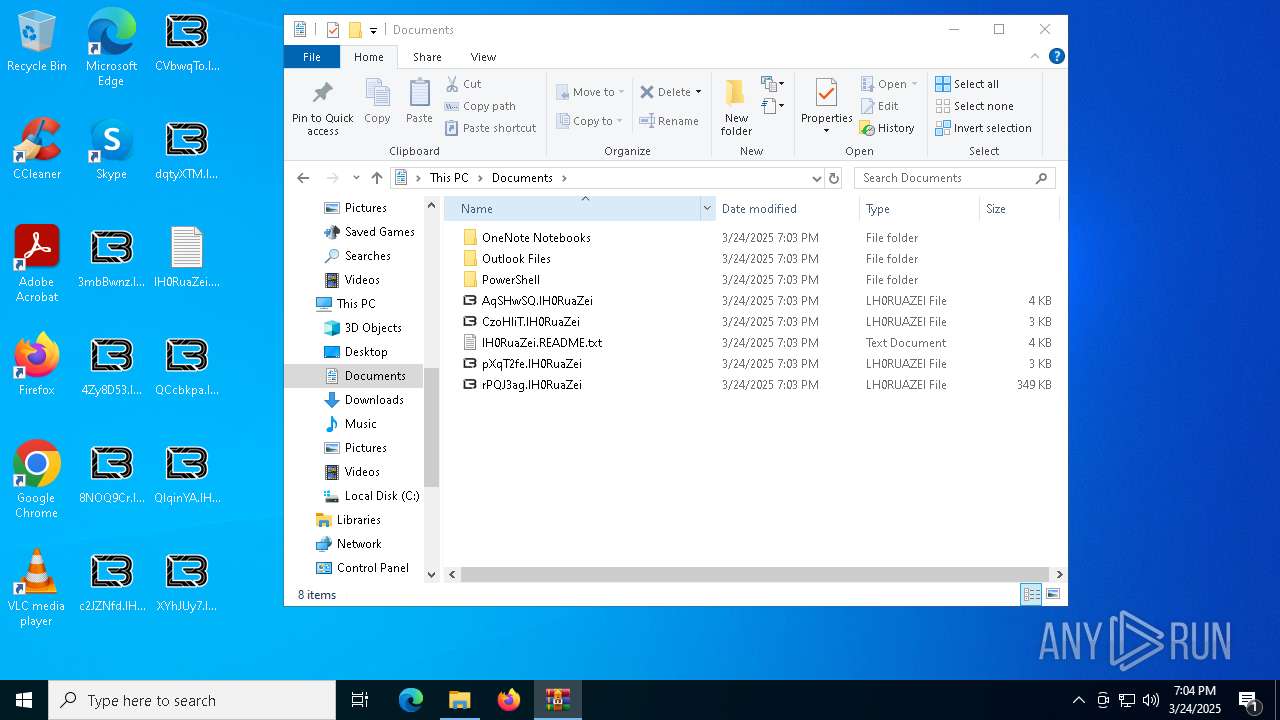
Executable files
16
Suspicious files
1 387
Text files
1 479
Unknown types
0
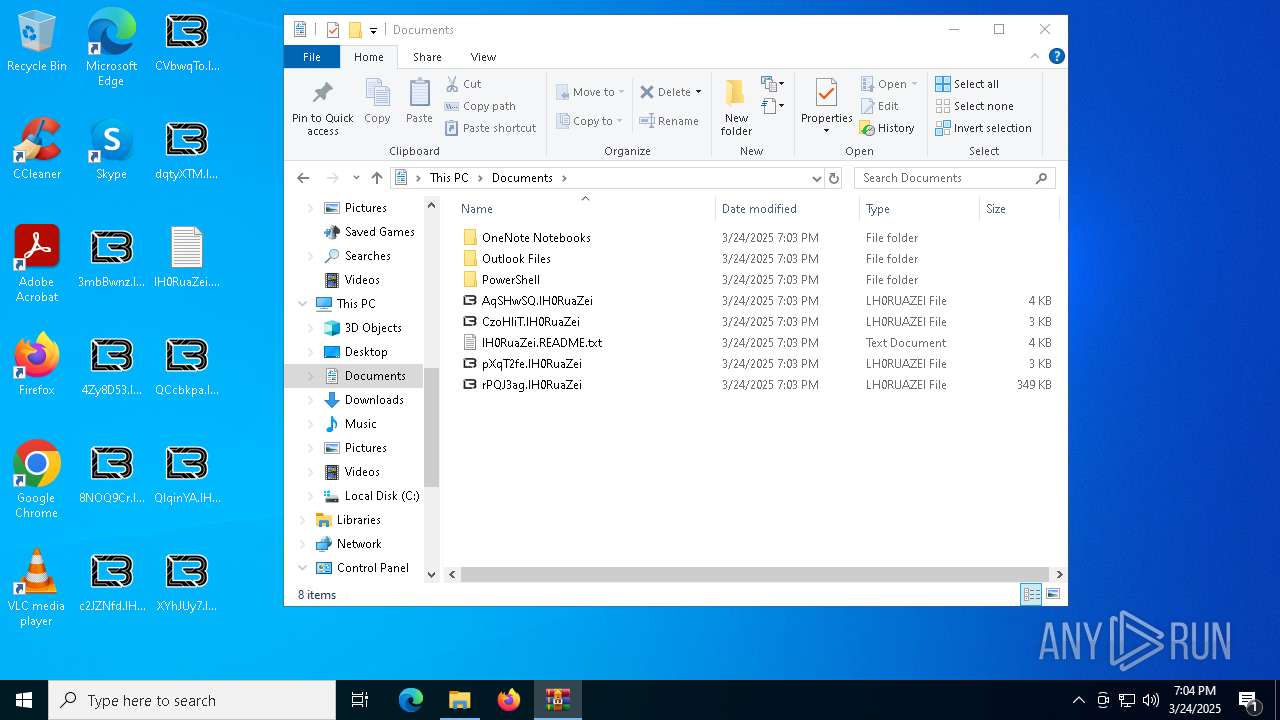
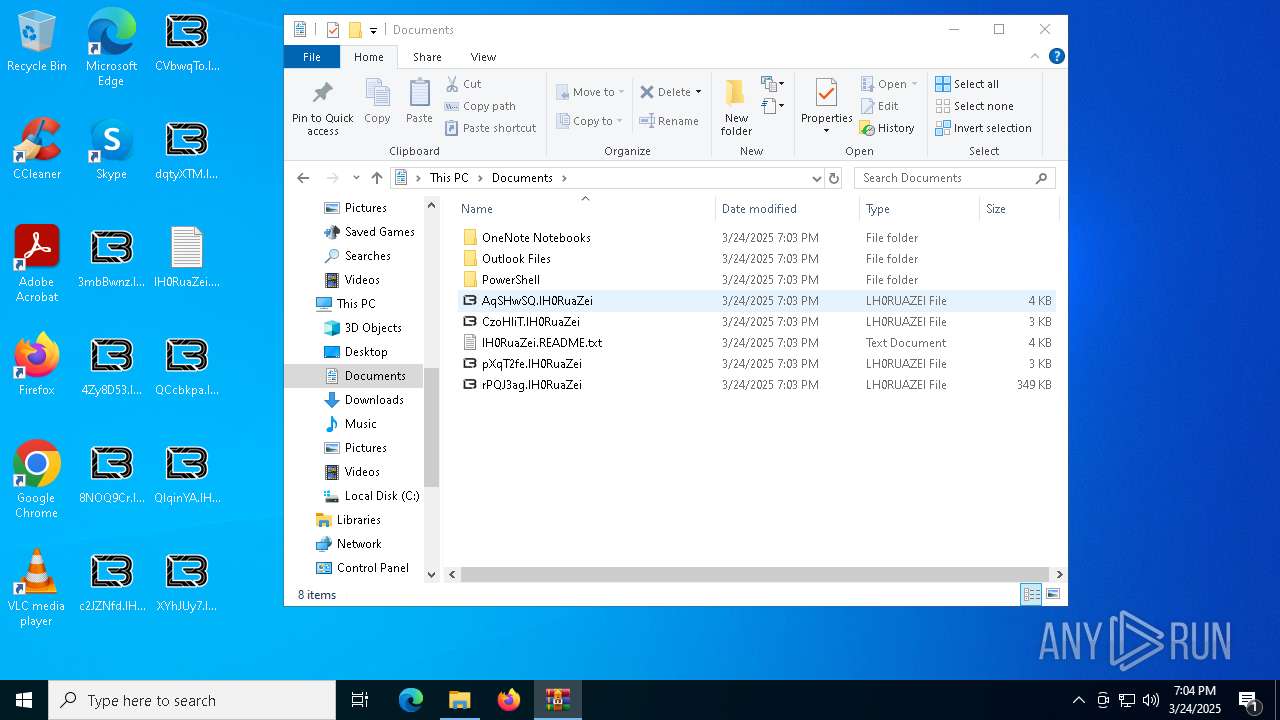
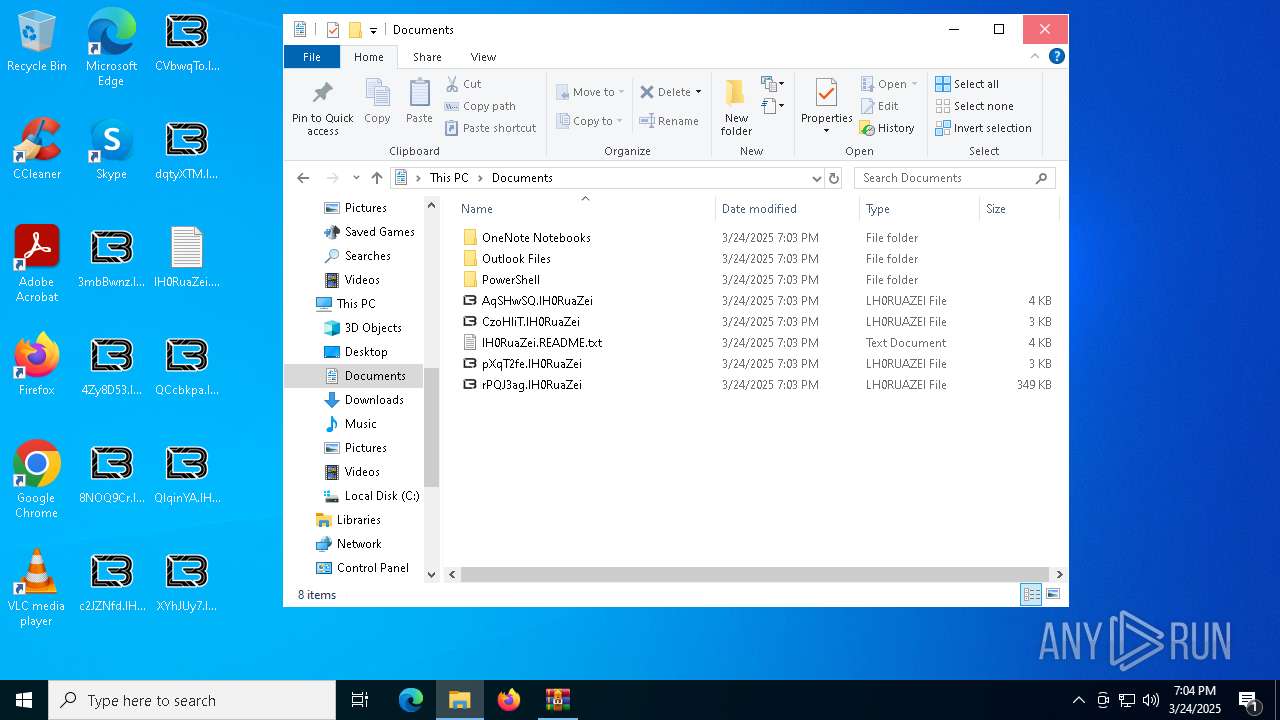
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\$Recycle.Bin\S-1-5-18\HHHHHHHHHHH | binary | |
MD5:E5044AD748A0D7664C5C66EDA08EC617 | SHA256:B1B86AA59FB05F3E663529316A7202E8C0DF9DB4490657C1AE2EA2878F6C2CE4 | |||
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\$Recycle.Bin\S-1-5-18\GGGGGGGGGGG | binary | |
MD5:E5044AD748A0D7664C5C66EDA08EC617 | SHA256:B1B86AA59FB05F3E663529316A7202E8C0DF9DB4490657C1AE2EA2878F6C2CE4 | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7412.30829\3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | executable | |
MD5:222EAB3F409F97B1A3442411676CA689 | SHA256:3E239B8776D380EB691C859A376977409546903EBA4ECD02DBA754BBF7D6DB61 | |||
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\$Recycle.Bin\S-1-5-18\JJJJJJJJJJJ | binary | |
MD5:E5044AD748A0D7664C5C66EDA08EC617 | SHA256:B1B86AA59FB05F3E663529316A7202E8C0DF9DB4490657C1AE2EA2878F6C2CE4 | |||
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\$Recycle.Bin\S-1-5-18\DDDDDDDDDDD | binary | |
MD5:E5044AD748A0D7664C5C66EDA08EC617 | SHA256:B1B86AA59FB05F3E663529316A7202E8C0DF9DB4490657C1AE2EA2878F6C2CE4 | |||
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\$Recycle.Bin\S-1-5-18\BBBBBBBBBBB | binary | |
MD5:E5044AD748A0D7664C5C66EDA08EC617 | SHA256:B1B86AA59FB05F3E663529316A7202E8C0DF9DB4490657C1AE2EA2878F6C2CE4 | |||
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\$Recycle.Bin\S-1-5-18\KKKKKKKKKKK | binary | |
MD5:E5044AD748A0D7664C5C66EDA08EC617 | SHA256:B1B86AA59FB05F3E663529316A7202E8C0DF9DB4490657C1AE2EA2878F6C2CE4 | |||
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\$Recycle.Bin\S-1-5-18\LLLLLLLLLLL | binary | |
MD5:E5044AD748A0D7664C5C66EDA08EC617 | SHA256:B1B86AA59FB05F3E663529316A7202E8C0DF9DB4490657C1AE2EA2878F6C2CE4 | |||
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\ProgramData\lH0RuaZei.ico | image | |
MD5:88D9337C4C9CFE2D9AFF8A2C718EC76B | SHA256:95E059EF72686460884B9AEA5C292C22917F75D56FE737D43BE440F82034F438 | |||
| 6264 | 3e239b8776d380eb691c859a376977409546903eba4ecd02dba754bbf7d6db61.exe | C:\$Recycle.Bin\S-1-5-18\AAAAAAAAAAA | binary | |
MD5:E5044AD748A0D7664C5C66EDA08EC617 | SHA256:B1B86AA59FB05F3E663529316A7202E8C0DF9DB4490657C1AE2EA2878F6C2CE4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
28
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6040 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7756 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7920 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7764 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7756 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |