| File name: | LOCKY_YKCOL.vbs |
| Full analysis: | https://app.any.run/tasks/e5299002-eec1-4a6a-bdf1-00042a99eeb0 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 19:03:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | C5013B49AE6E44142D189BA8A189B8FC |
| SHA1: | 25C763440AE3B7A42F59873F92BB876D130E2AA7 |
| SHA256: | 84C32E68B97A68142D8828BF937639CC5F3399698319A01A574C5326A5E2D679 |
| SSDEEP: | 192:Ubf6LGn2D89MKxSQIHkBSv+r27QUeRU0uLalJQXnqUz:UL67D8KESQykAv827QUeRU0uLalJQXbz |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- WScript.exe (PID: 3384)
Checks supported languages
- WScript.exe (PID: 3384)
Creates files in the user directory
- WScript.exe (PID: 3384)
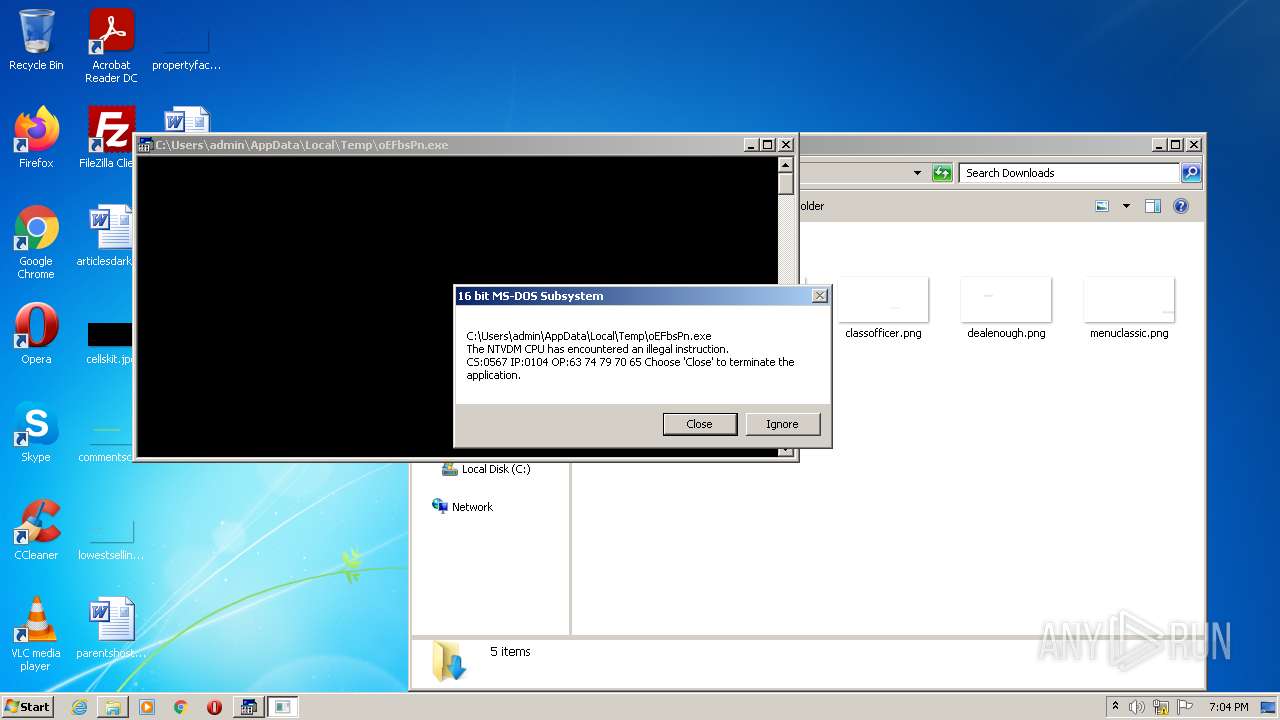
Executes application which crashes
- WScript.exe (PID: 3384)
INFO
Checks supported languages
- ntvdm.exe (PID: 1172)
Checks Windows Trust Settings
- WScript.exe (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1172 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3384 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\LOCKY_YKCOL.vbs" | C:\Windows\System32\WScript.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
1 034
Read events
1 004
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3384) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\2FDDOP0K.txt | text | |
MD5:— | SHA256:— | |||
| 3384 | WScript.exe | C:\Users\admin\AppData\Local\Temp\oEFbsPn.exe | html | |
MD5:— | SHA256:— | |||
| 1172 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsC8FB.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 1172 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsC8EA.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | WScript.exe | GET | 200 | 199.59.243.200:80 | http://billdickeymasonry.com/KJSkjdhf? | US | html | 1.02 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3384 | WScript.exe | 199.59.243.200:80 | billdickeymasonry.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
belloisetropical.com |
| malicious |
tertrodefordown.info |
| unknown |
dns.msftncsi.com |
| shared |
billdickeymasonry.com |
| malicious |