| File name: | ldplayer_ens_2091_ld.exe |
| Full analysis: | https://app.any.run/tasks/ce9e4eaf-f94a-485e-966d-9d5104adadb2 |
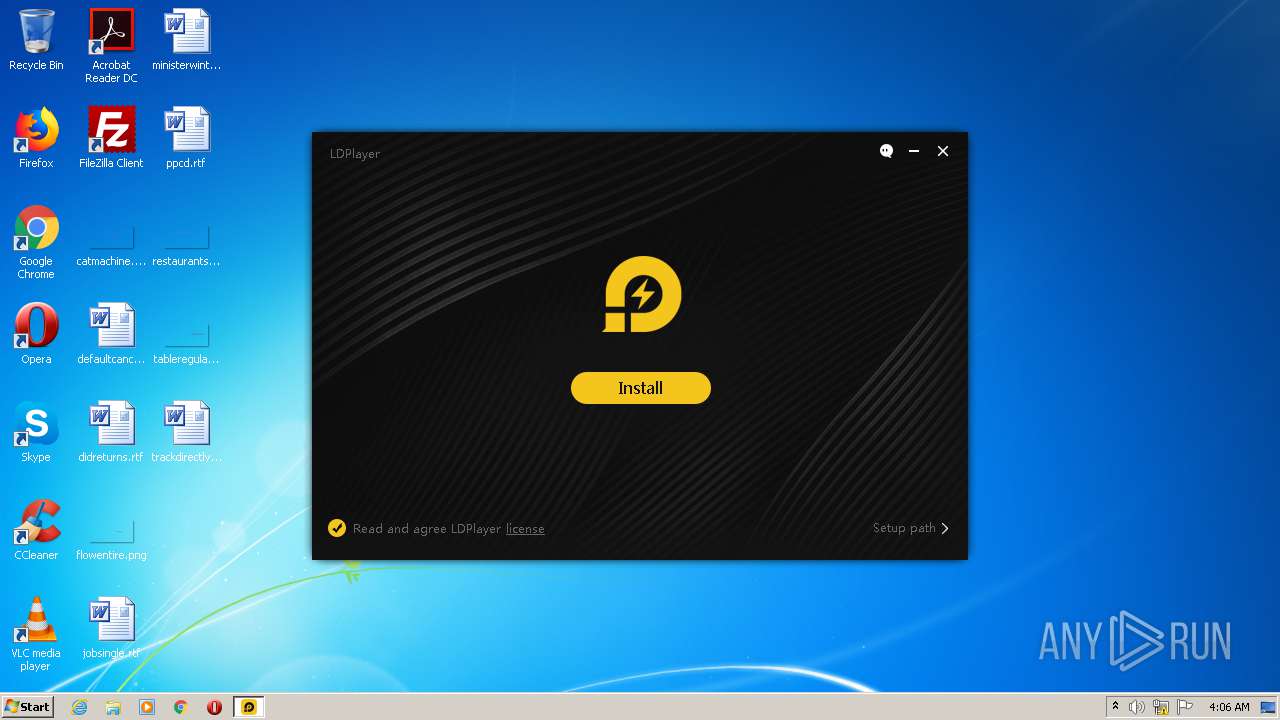
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2020, 03:06:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EFB4091D14D7869793D801A917E37A9F |
| SHA1: | 9704466842A61D603F77D4F6FB993BC8ED3F7472 |
| SHA256: | 84BD7E9CB26C863CAB40E582A51E2F619CD0B10928890C3A1B3F9E50F45B42F4 |
| SSDEEP: | 49152:rDeKTnQc9mzmF49DUjAbDiYFpIyzQR9sXafgkDFMVR9C1UhPJXMK701hOHZbebbS:GYQimz19g8FphzrBiCV2Hs |
MALICIOUS
Actions looks like stealing of personal data
- ldplayer_ens_2091_ld.exe (PID: 2492)
Loads dropped or rewritten executable
- ldplayer_ens_2091_ld.exe (PID: 2492)
SUSPICIOUS
Creates files in the user directory
- ldplayer_ens_2091_ld.exe (PID: 2492)
Executable content was dropped or overwritten
- ldplayer_ens_2091_ld.exe (PID: 2492)
Reads Environment values
- ldplayer_ens_2091_ld.exe (PID: 2492)
Reads Internet Cache Settings
- ldplayer_ens_2091_ld.exe (PID: 2492)
Reads internet explorer settings
- ldplayer_ens_2091_ld.exe (PID: 2492)
Creates files in the program directory
- ldplayer_ens_2091_ld.exe (PID: 2492)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:27 11:58:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 869888 |
| InitializedDataSize: | 2110976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9f2e8 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Traditional) |
| CharacterSet: | Unicode |
| CompanyName: | XUANZHI INTERNATIONAL CO., LIMITED |
| FileDescription: | LDPlayer |
| FileVersion: | 1.0.0 |
| InternalName: | ldplayerinst.exe |
| LegalCopyright: | Copyright (C) 2016 |
| OriginalFileName: | ldplayerinst.exe |
| ProductName: | LDPlayer |
| ProductVersion: | 1.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Jul-2020 09:58:39 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | XUANZHI INTERNATIONAL CO., LIMITED |
| FileDescription: | LDPlayer |
| FileVersion: | 1.0.0 |
| InternalName: | ldplayerinst.exe |
| LegalCopyright: | Copyright (C) 2016 |
| OriginalFilename: | ldplayerinst.exe |
| ProductName: | LDPlayer |
| ProductVersion: | 1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Jul-2020 09:58:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000D446A | 0x000D4600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54993 |
.rdata | 0x000D6000 | 0x00036F06 | 0x00037000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08976 |
.data | 0x0010D000 | 0x0000E288 | 0x00005800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93137 |
.rsrc | 0x0011C000 | 0x001B1C30 | 0x001B1E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.27007 |
.reloc | 0x002CE000 | 0x0000C220 | 0x0000C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.57594 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06216 | 651 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0.773327 | 304 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 0.746345 | 176 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 3.831 | 1640 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 3.97057 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 3.46461 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 2.11169 | 72 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 3.2232 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 3.24731 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 2.8258 | 270376 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2492 | "C:\Users\admin\AppData\Local\Temp\ldplayer_ens_2091_ld.exe" | C:\Users\admin\AppData\Local\Temp\ldplayer_ens_2091_ld.exe | explorer.exe | ||||||||||||
User: admin Company: XUANZHI INTERNATIONAL CO., LIMITED Integrity Level: HIGH Description: LDPlayer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 3044 | "C:\Users\admin\AppData\Local\Temp\ldplayer_ens_2091_ld.exe" | C:\Users\admin\AppData\Local\Temp\ldplayer_ens_2091_ld.exe | — | explorer.exe | |||||||||||
User: admin Company: XUANZHI INTERNATIONAL CO., LIMITED Integrity Level: MEDIUM Description: LDPlayer Exit code: 3221226540 Version: 1.0.0 Modules
| |||||||||||||||
Total events
464
Read events
443
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E407080003001A00030006001F001D0100000000 | |||
| (PID) Process: | (2492) ldplayer_ens_2091_ld.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
3
Suspicious files
2
Text files
80
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\Fusion_ld2\Fusion.dl | — | |
MD5:— | SHA256:— | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\00193464.log | — | |
MD5:— | SHA256:— | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\Fusion_ld2\Fusion.dll | binary | |
MD5:— | SHA256:— | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\nsd165181241388\css\main.css | text | |
MD5:9B27E2A266FE15A3AABFE635C29E8923 | SHA256:166AA42BC5216C5791388847AE114EC0671A0D97B9952D14F29419B8BE3FB23F | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\nsd165181241388\css\sdk-ui\browse.css | text | |
MD5:6009D6E864F60AEA980A9DF94C1F7E1C | SHA256:5EF48A8C8C3771B4F233314D50DD3B5AFDCD99DD4B74A9745C8FE7B22207056D | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\nsd165181241388\csshover3.htc | html | |
MD5:52FA0DA50BF4B27EE625C80D36C67941 | SHA256:E37E99DDFC73AC7BA774E23736B2EF429D9A0CB8C906453C75B14C029BDD5493 | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\nsd165181241388\css\sdk-ui\button.css | text | |
MD5:37E1FF96E084EC201F0D95FEEF4D5E94 | SHA256:8E806F5B94FC294E918503C8053EF1284E4F4B1E02C7DA4F4635E33EC33E0534 | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\Fusion_ld2\funsion.zip | compressed | |
MD5:— | SHA256:— | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\nsd165181241388\css\sdk-ui\images\progress-bg2.png | image | |
MD5:B582D9A67BFE77D523BA825FD0B9DAE3 | SHA256:AB4EEB3EA1EEF4E84CB61ECCB0BA0998B32108D70B3902DF3619F4D9393F74C3 | |||
| 2492 | ldplayer_ens_2091_ld.exe | C:\Users\admin\AppData\Local\Temp\nsd165181241388\images\Loader.gif | image | |
MD5:57CA1A2085D82F0574E3EF740B9A5EAD | SHA256:476A7B1085CC64DE1C0EB74A6776FA8385D57EB18774F199DF83FC4D7BBCC24E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2492 | ldplayer_ens_2091_ld.exe | POST | 200 | 52.212.91.170:80 | http://ww42.fubediddnetefa.com/ | IE | — | — | malicious |
2492 | ldplayer_ens_2091_ld.exe | POST | 200 | 52.209.200.29:80 | http://secure.fubediddnetefa.com/ | IE | binary | 767 Kb | malicious |
2492 | ldplayer_ens_2091_ld.exe | GET | 200 | 172.217.16.206:80 | http://www.google-analytics.com/collect?v=1&t=event&tid=UA-134765723-1&cid=72a64af6fe11aec591f7beeb2b99b756&ec=app&ea=download_run&el=1&ev=100&z=41 | US | image | 35 b | whitelisted |
2492 | ldplayer_ens_2091_ld.exe | GET | 200 | 34.252.94.12:80 | http://ww42.fubediddnetefa.com/ | IE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.16.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2492 | ldplayer_ens_2091_ld.exe | 13.226.156.173:80 | d2janltnicv7uh.cloudfront.net | — | US | unknown |
— | — | 34.252.94.12:80 | ww42.fubediddnetefa.com | Amazon.com, Inc. | IE | malicious |
2492 | ldplayer_ens_2091_ld.exe | 13.226.155.44:80 | encdn.ldmnq.com | — | US | unknown |
2492 | ldplayer_ens_2091_ld.exe | 52.212.91.170:80 | ww42.fubediddnetefa.com | Amazon.com, Inc. | IE | malicious |
2492 | ldplayer_ens_2091_ld.exe | 52.209.200.29:80 | secure.fubediddnetefa.com | Amazon.com, Inc. | IE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
encdn.ldmnq.com |
| shared |
d2janltnicv7uh.cloudfront.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ww42.fubediddnetefa.com |
| malicious |
secure.fubediddnetefa.com |
| malicious |