| File name: | SetupProd_TeamsAddIn.exe |
| Full analysis: | https://app.any.run/tasks/ef18687b-a30c-4e66-bdaf-3a36b73a6773 |
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2024, 13:45:42 |
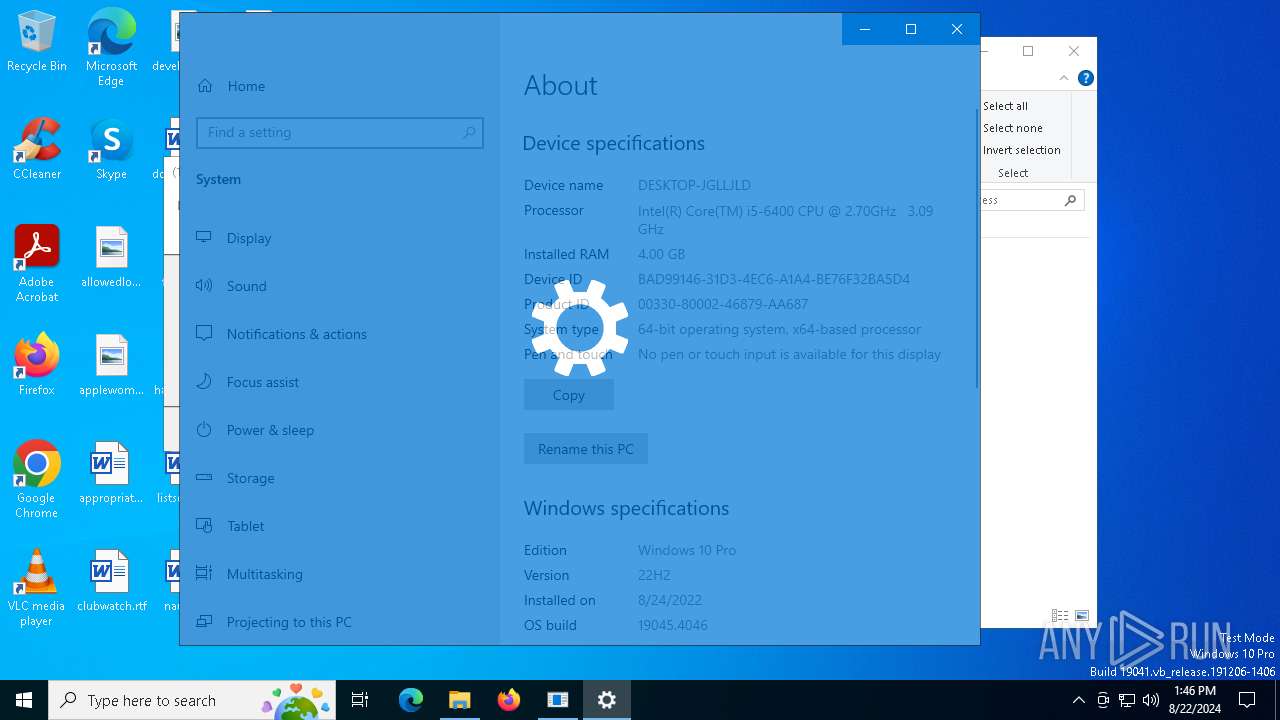
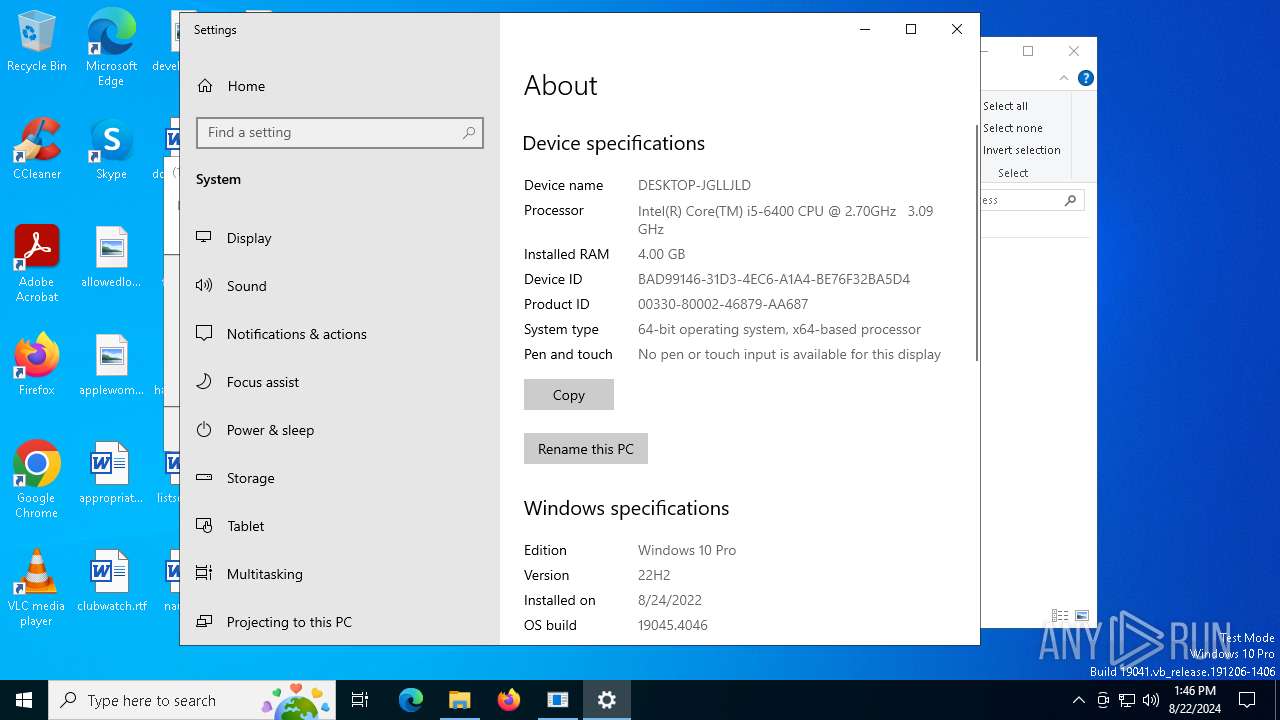
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F164D65666DCD14CCC2EFE7413234FA1 |
| SHA1: | 499922FE5D2296FA5F4CEC488F39AC489D68C6D2 |
| SHA256: | 84B04E0A98357EF9FF75884B13288CE8F35993CA025A1D996A1EA140A3A5A7CD |
| SSDEEP: | 3072:X1f8Yo9wu8tQ2uc5pmaE8Hbc/dKS2Jn91f32wx9M41ku+wMfZylcj/8F3fiL2W:XGYo9wWQHbPn9BBywEylcj/s0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- SetupProd_TeamsAddIn.exe (PID: 6740)
- dfsvc.exe (PID: 6800)
Process drops legitimate windows executable
- SetupProd_TeamsAddIn.exe (PID: 6740)
- dfsvc.exe (PID: 6800)
Searches for installed software
- SetupProd_TeamsAddIn.exe (PID: 6740)
Starts a Microsoft application from unusual location
- SetupProd_TeamsAddIn.exe (PID: 6740)
- SetupProd_TeamsAddIn.exe (PID: 6692)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 6800)
The process drops C-runtime libraries
- dfsvc.exe (PID: 6800)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 6800)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 6800)
Reads Internet Explorer settings
- dfsvc.exe (PID: 6800)
Checks Windows Trust Settings
- dfsvc.exe (PID: 6800)
INFO
Creates files or folders in the user directory
- dfsvc.exe (PID: 6800)
Disables trace logs
- dfsvc.exe (PID: 6800)
Checks supported languages
- dfsvc.exe (PID: 6800)
- SetupProd_TeamsAddIn.exe (PID: 6740)
Create files in a temporary directory
- SetupProd_TeamsAddIn.exe (PID: 6740)
- dfsvc.exe (PID: 6800)
Reads the machine GUID from the registry
- dfsvc.exe (PID: 6800)
Checks proxy server information
- dfsvc.exe (PID: 6800)
Reads Environment values
- dfsvc.exe (PID: 6800)
Reads the computer name
- dfsvc.exe (PID: 6800)
Manual execution by a user
- control.exe (PID: 320)
Dropped object may contain TOR URL's
- dfsvc.exe (PID: 6800)
Reads Microsoft Office registry keys
- control.exe (PID: 320)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 6800)
Reads the software policy settings
- dfsvc.exe (PID: 6800)
Reads security settings of Internet Explorer
- control.exe (PID: 320)
The process uses the downloaded file
- dfsvc.exe (PID: 6800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:30 03:39:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 74752 |
| InitializedDataSize: | 114688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2b03 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Support and Recovery Assistant for Office 365 |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| ProductName: | Microsoft Support and Recovery Assistant for Office 365 |
| ProductVersion: | 1.0.0.0 |
Total processes
136
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\WINDOWS\system32\control.exe" SYSTEM | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6692 | "C:\Users\admin\AppData\Local\Temp\SetupProd_TeamsAddIn.exe" | C:\Users\admin\AppData\Local\Temp\SetupProd_TeamsAddIn.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Support and Recovery Assistant for Office 365 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6740 | "C:\Users\admin\AppData\Local\Temp\SetupProd_TeamsAddIn.exe" | C:\Users\admin\AppData\Local\Temp\SetupProd_TeamsAddIn.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Support and Recovery Assistant for Office 365 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6764 | C:\WINDOWS\system32\rundll32.exe dfshim.dll, ShOpenVerbApplication https://outlookdiagnostics.azureedge.net/sarafiles/Microsoft.Sara.Prod.application?usergroup=Prod&Ring=Prod&symptomid=7DEB9E4F-B4CA-48C4-AA75-F21B4B25B888 | C:\Windows\SysWOW64\rundll32.exe | — | SetupProd_TeamsAddIn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6800 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
5 102
Read events
5 072
Write events
28
Delete events
2
Modification events
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: 0KBD8KTP5C12EA7GACZCV41Q | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: 0KBD8KTP5C12EA7GACZCV41Q | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: Y2QDQCEJMGPPMOTGRCGY87DJ | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0\StateManager |
| Operation: | write | Name: | StateStore_RandomString |
Value: MD4E7CBKND0LP8Q5OD4H5J1B | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6800) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
213
Suspicious files
13
Text files
283
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6800 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\W4CR2XAA.HLY\JEHTPOH3.VB8\SaraEULA.txt | text | |
MD5:A811F7A46C12ED29C5713A64F528569A | SHA256:30AFE28070DD647EFB545549CBDDCBBF9D40C7424BC93FECC8E7AE51A668D7EB | |||
| 6800 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\HONDLROR.RA5\YXXDBGTL.6E6.application | xml | |
MD5:31A29D900367BBBFA3044E4E96BF1050 | SHA256:8658BEBAF1B83D86C0162D418F96A9A39CDAFCB7C7B175A5C67EAC3EC9FBC962 | |||
| 6800 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A583E2A51BFBDC1E492A57B7C8325850 | binary | |
MD5:CB3B332B6265B65D251F47AE65990297 | SHA256:2799EDBD951DEE570D113BF322D3CE0A2AB8B3AF89AF290387001EC303A3FDEA | |||
| 6800 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\W4CR2XAA.HLY\JEHTPOH3.VB8\sara2.ico | image | |
MD5:64ABE480FD183A30B203DAAC7A523821 | SHA256:38FE914C14F96C6BECB22203D722E15036A49F78E085F339236BC7E18D6D3A06 | |||
| 6800 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\36AC0BE60E1243344AE145F746D881FE | binary | |
MD5:7AB1C9388AF861D4DE6FA89D5CD53288 | SHA256:B4D715088533C8D4B91604E951934EC0F0802F00B47C5E101739D1AC43FA24E3 | |||
| 6800 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\W4CR2XAA.HLY\JEHTPOH3.VB8\tools\x64\mrmapi.exe | executable | |
MD5:2B09ABEFDC84D46D10C2A83B0870F3D4 | SHA256:973DEE4EE73FDF7BC5815D7EDF3DDEE8E0C40B259BC1DCDE603B0BB3AE732CAA | |||
| 6800 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\W4CR2XAA.HLY\JEHTPOH3.VB8\Microsoft.IdentityModel.Clients.ActiveDirectory.WindowsForms.dll | executable | |
MD5:DAD75B06FCDBA45BC622BAF0582E806A | SHA256:C24A11C0E4AE4BD202DBC2002CBA4E29B18A5008063DCE2ABC922B7078E7519B | |||
| 6800 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0B8A20E1F3F4D73D52A19929F922C892 | der | |
MD5:0840F3C261E695105CD15C84EA85BEED | SHA256:F60632399A87485A7417DDF8B407DA66794C37347B3AA9E995EC389ECD091947 | |||
| 6740 | SetupProd_TeamsAddIn.exe | C:\Users\admin\AppData\Local\Temp\SaraSetup.log | binary | |
MD5:2F738E7D3917EEE7FFAD8E07FF54324B | SHA256:127689ED95C9A62E11B13D1E8CA471DB606D8A1605EA2107F6ED208B4A9CE905 | |||
| 6800 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\W4CR2XAA.HLY\JEHTPOH3.VB8\Microsoft.Sara.exe.manifest | xml | |
MD5:799138FA938158C52892B8F977207471 | SHA256:F39B77F6FA9D3995908B3EA5B71CEAC7A76FA36680A75B6D82880AF328079431 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
35
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5212 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6800 | dfsvc.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7020 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6800 | dfsvc.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
6800 | dfsvc.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_2010-07-06.crl | unknown | — | — | whitelisted |
1028 | SystemSettings.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1028 | SystemSettings.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6664 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3840 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3584 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6800 | dfsvc.exe | 152.199.19.160:443 | outlookdiagnostics.azureedge.net | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5212 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5212 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6800 | dfsvc.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
6800 | dfsvc.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
outlookdiagnostics.azureedge.net |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
SetupProd_TeamsAddIn.exe | Version verficiation success |
SetupProd_TeamsAddIn.exe | |
SetupProd_TeamsAddIn.exe | Current .net version is 533325 |
SetupProd_TeamsAddIn.exe | |
SetupProd_TeamsAddIn.exe | Fail to query SaraInstalled value |
SetupProd_TeamsAddIn.exe | |
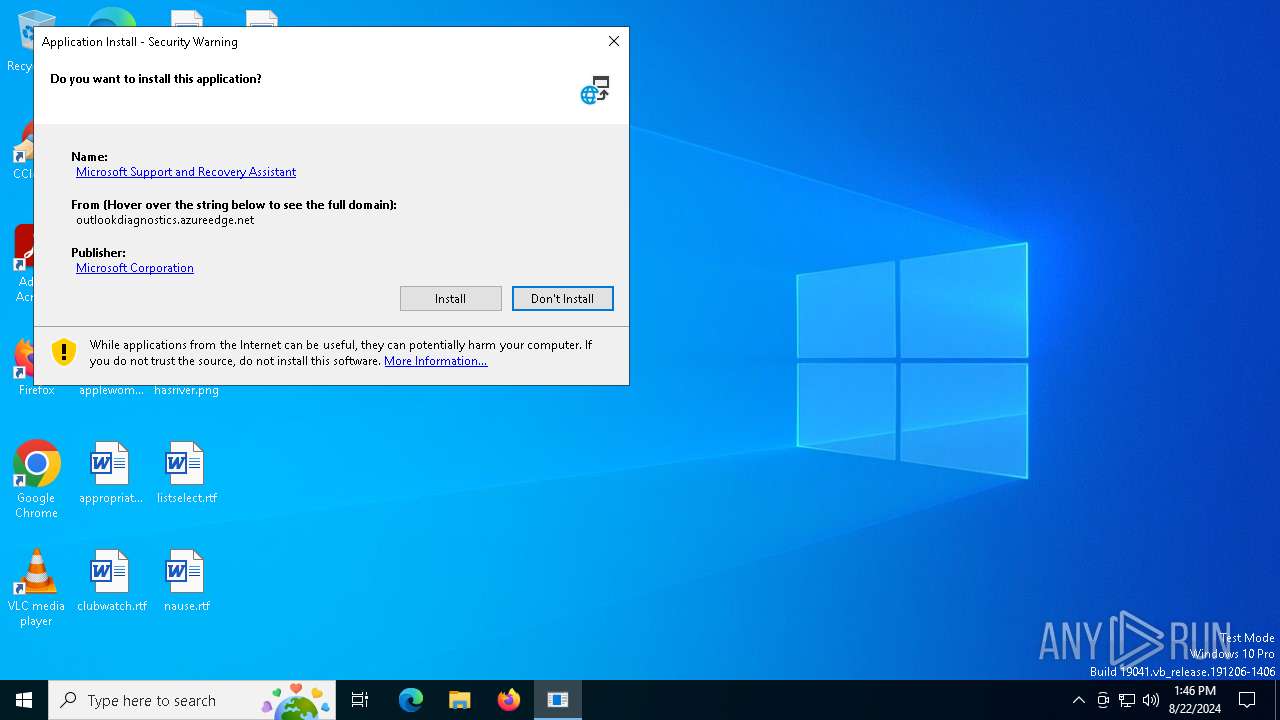
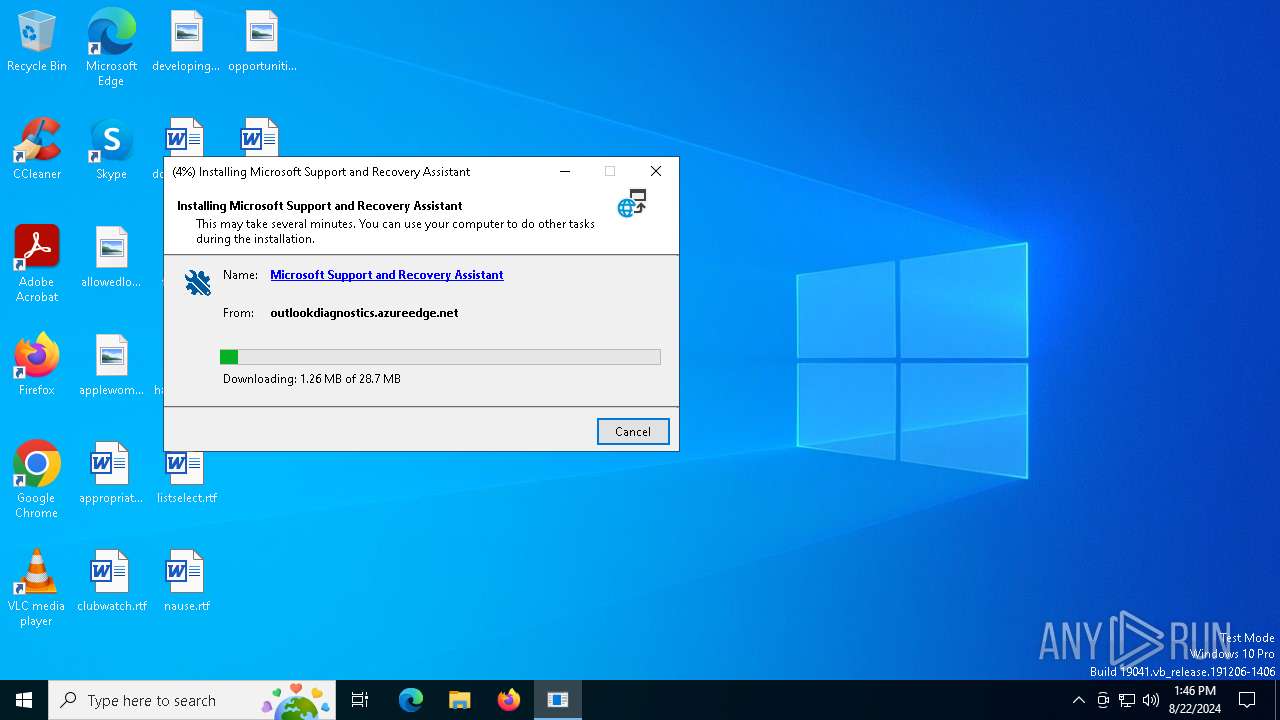
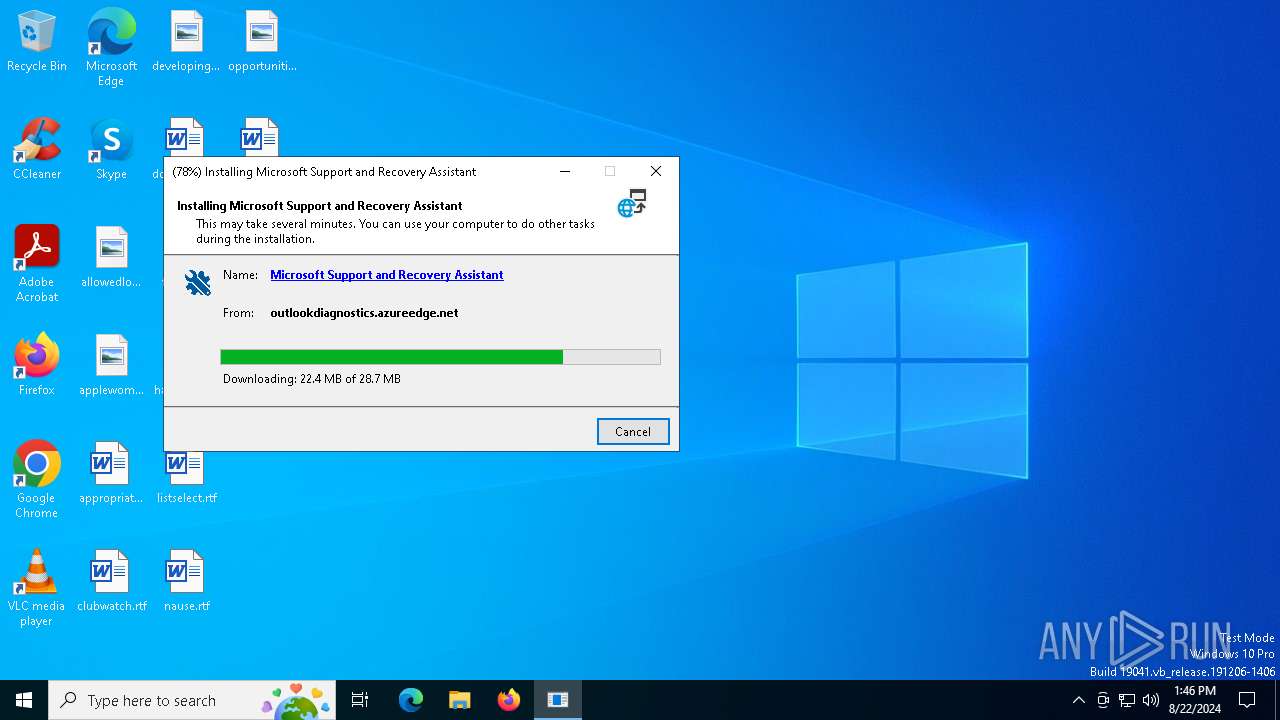
SetupProd_TeamsAddIn.exe | C:\WINDOWS\system32\rundll32.exe dfshim.dll, ShOpenVerbApplication https://outlookdiagnostics.azureedge.net/sarafiles/Microsoft.Sara.Prod.application?usergroup=Prod&Ring=Prod&symptomid=7DEB9E4F-B4CA-48C4-AA75-F21B4B25B888 |
SetupProd_TeamsAddIn.exe | |
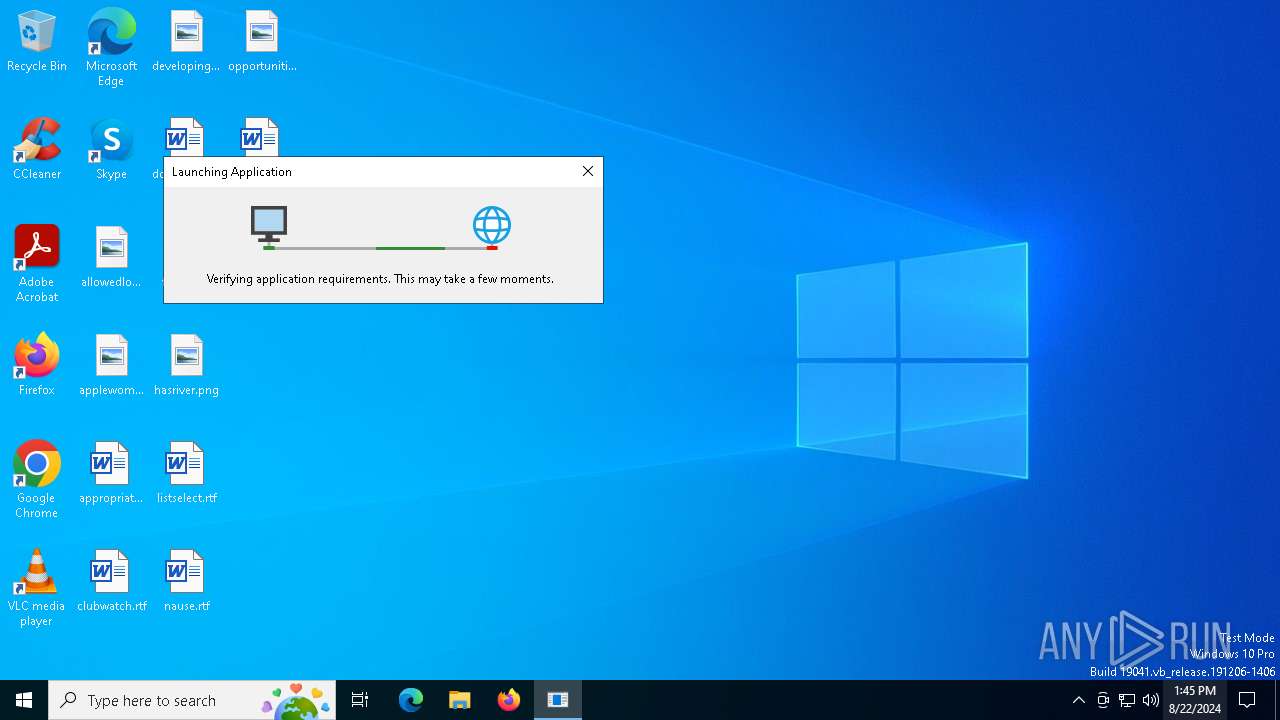
SetupProd_TeamsAddIn.exe | Start to install Office 365 Support and Recovery Assistant |
SetupProd_TeamsAddIn.exe | |