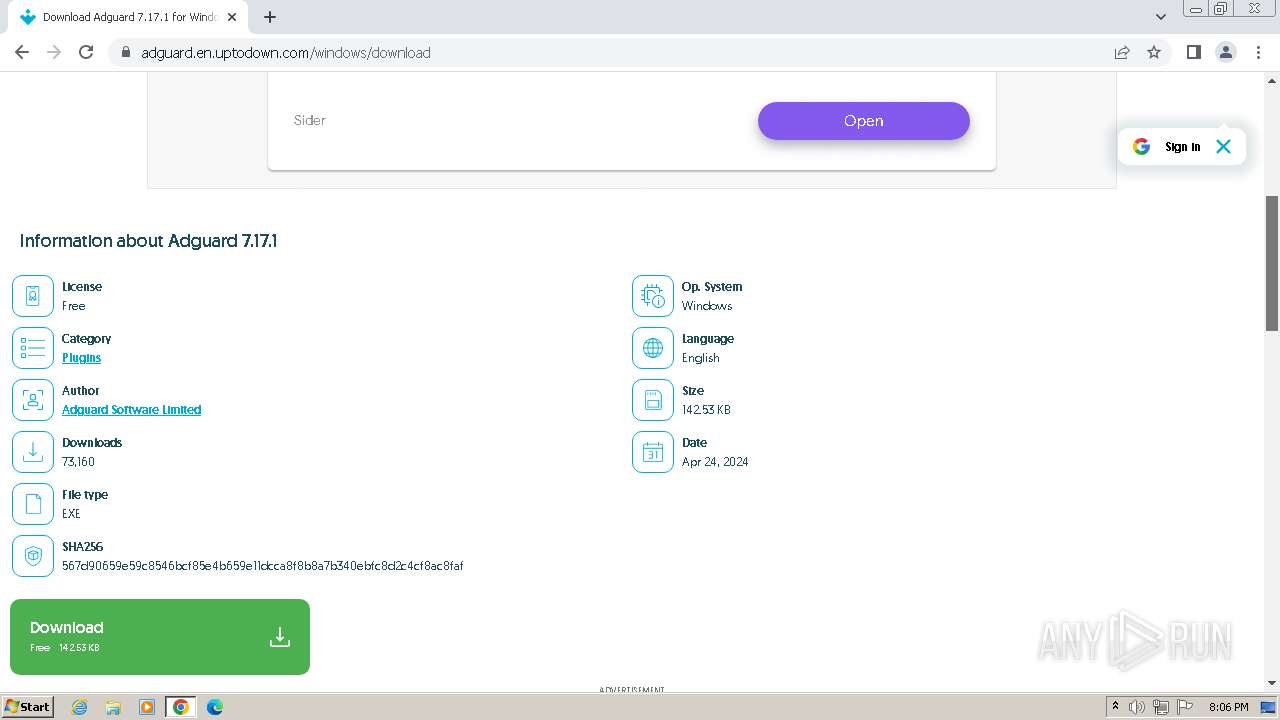
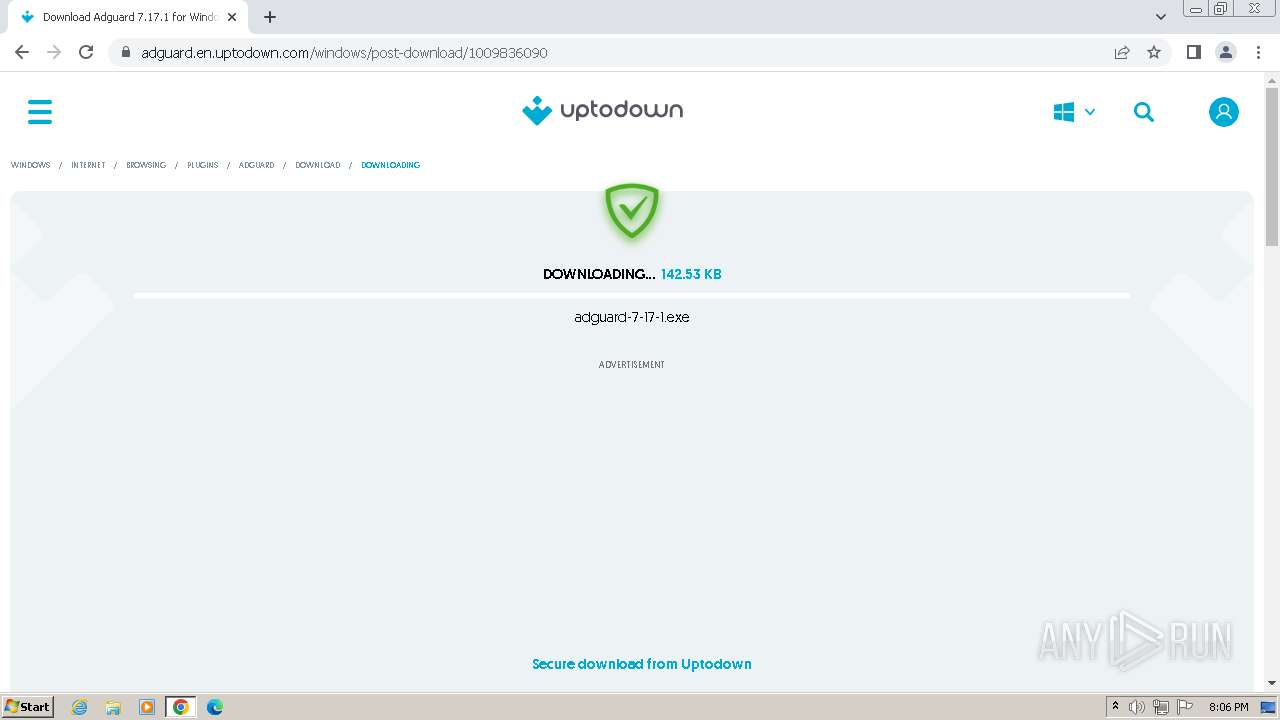
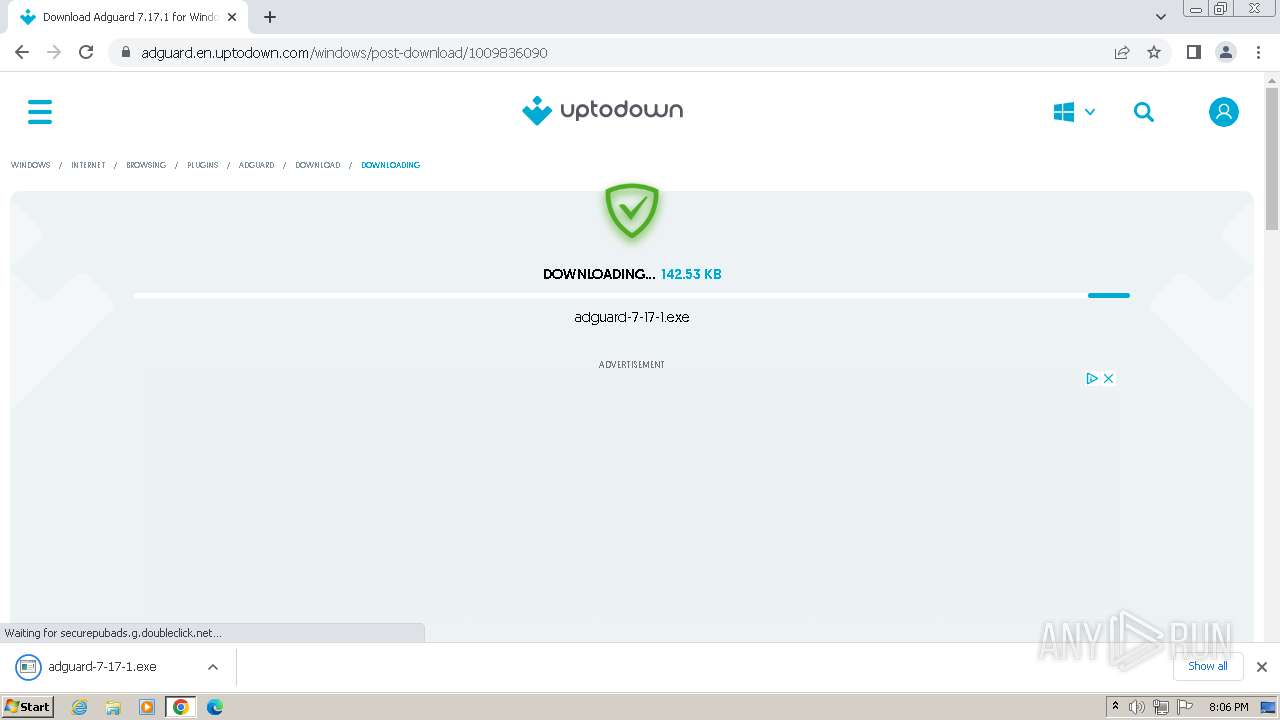
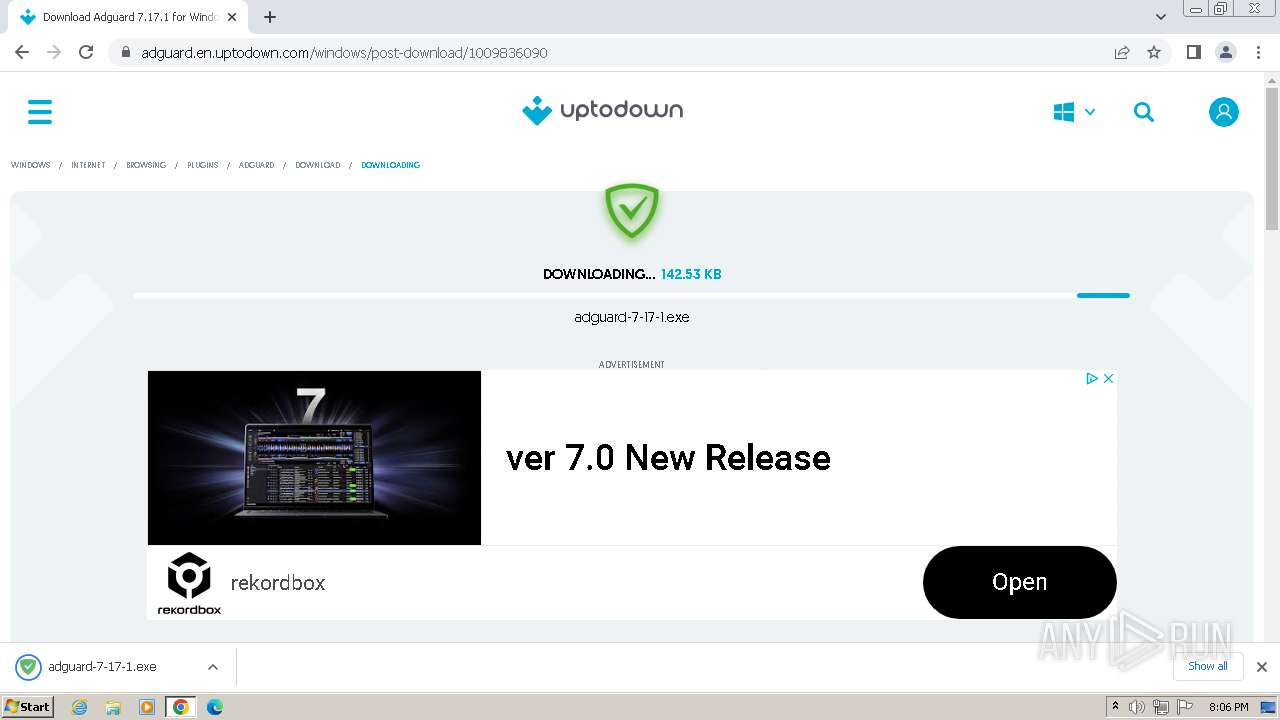
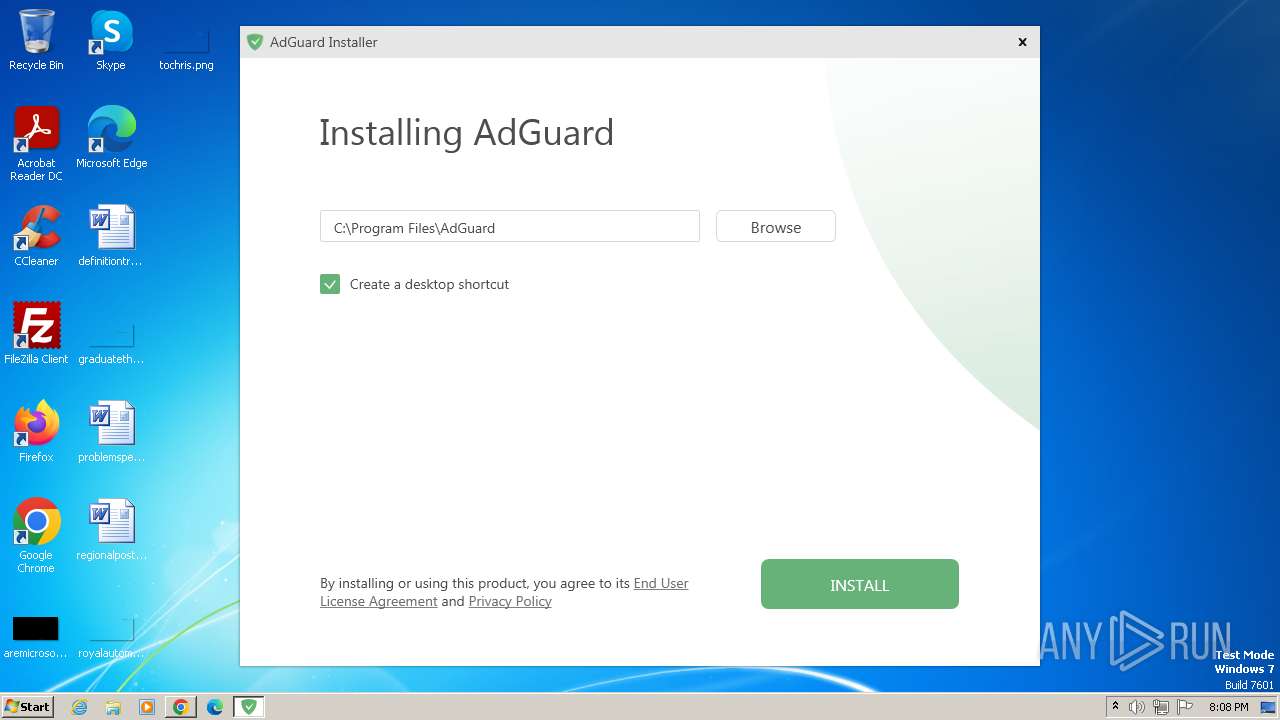
| URL: | https://adguard.en.uptodown.com/windows |
| Full analysis: | https://app.any.run/tasks/4e8fc219-6a55-456c-9393-5f88986547d5 |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2024, 19:06:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EBE44D1933F9A8E4E58F9626303168C3 |
| SHA1: | 1886A803284DEFE356AE43A4DD1BE0D38075D787 |
| SHA256: | 84AC7B14BF70EE9E7D538B80D1E92DF1DE6BB959673CAB031EBD7C8C44668EC5 |
| SSDEEP: | 3:N8pxokVsbd3SMm:2TFU3Sf |
MALICIOUS
Drops the executable file immediately after the start
- setup.exe (PID: 3948)
- adgSetup.exe (PID: 2624)
- setup.exe (PID: 3804)
- AdguardSvc.exe (PID: 2632)
- msiexec.exe (PID: 948)
Starts NET.EXE for service management
- cmd.exe (PID: 3320)
- net.exe (PID: 3504)
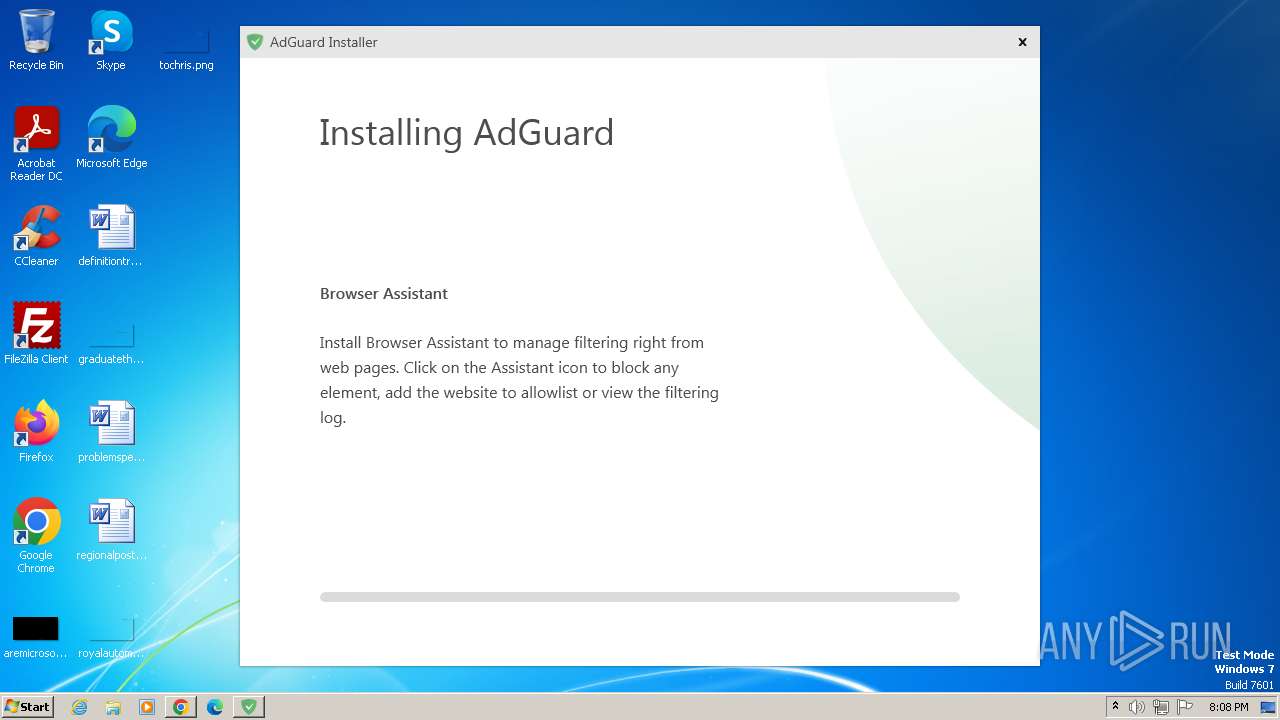
SUSPICIOUS
Executable content was dropped or overwritten
- setup.exe (PID: 3804)
- setup.exe (PID: 3948)
- adgSetup.exe (PID: 2624)
- rundll32.exe (PID: 2924)
- rundll32.exe (PID: 2316)
- rundll32.exe (PID: 2284)
- rundll32.exe (PID: 3008)
- rundll32.exe (PID: 2376)
- AdguardSvc.exe (PID: 2632)
- rundll32.exe (PID: 1372)
Process drops legitimate windows executable
- setup.exe (PID: 3804)
- rundll32.exe (PID: 2924)
- rundll32.exe (PID: 2316)
- rundll32.exe (PID: 3008)
- msiexec.exe (PID: 948)
- rundll32.exe (PID: 2284)
- rundll32.exe (PID: 2376)
- rundll32.exe (PID: 1372)
Starts itself from another location
- setup.exe (PID: 3804)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 4080)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 2376)
- AdguardSvc.exe (PID: 2632)
Executes as Windows Service
- AdguardSvc.exe (PID: 2632)
Drops a system driver (possible attempt to evade defenses)
- AdguardSvc.exe (PID: 2632)
Starts SC.EXE for service management
- setup.exe (PID: 3804)
- AdguardSvc.exe (PID: 2632)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 2316)
- cmd.exe (PID: 1108)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 2540)
- cmd.exe (PID: 2696)
- cmd.exe (PID: 1928)
INFO
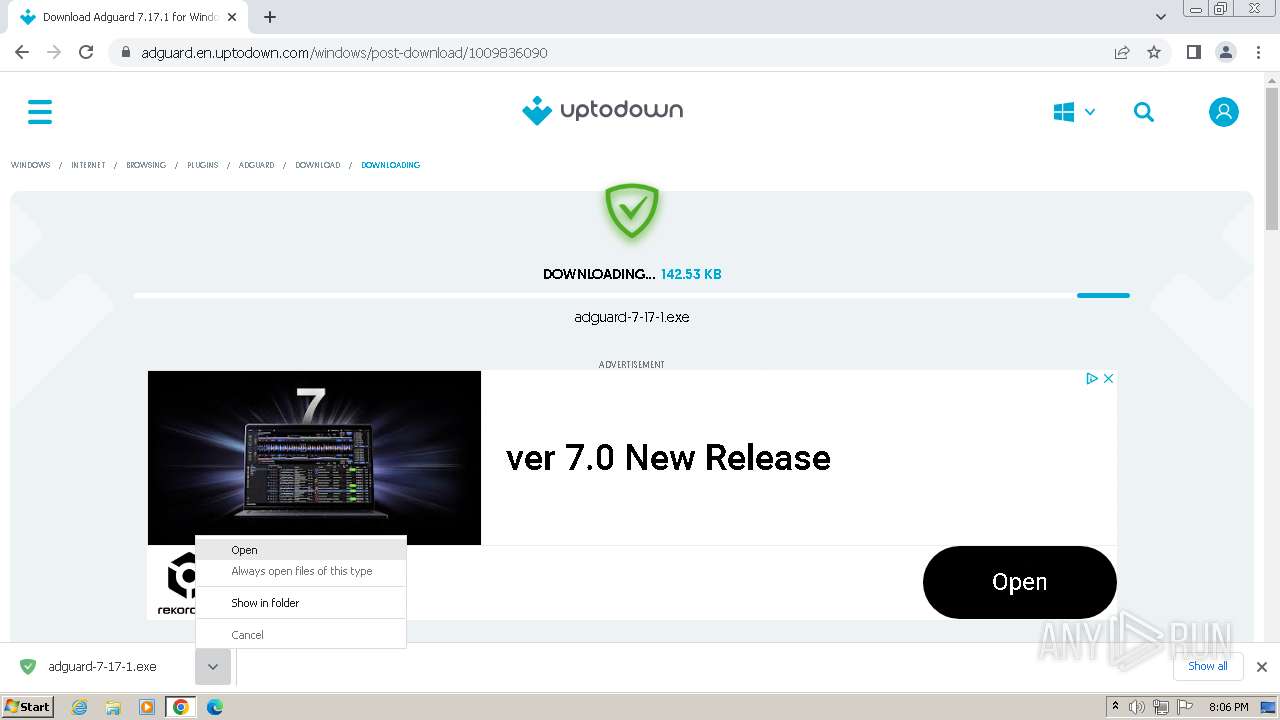
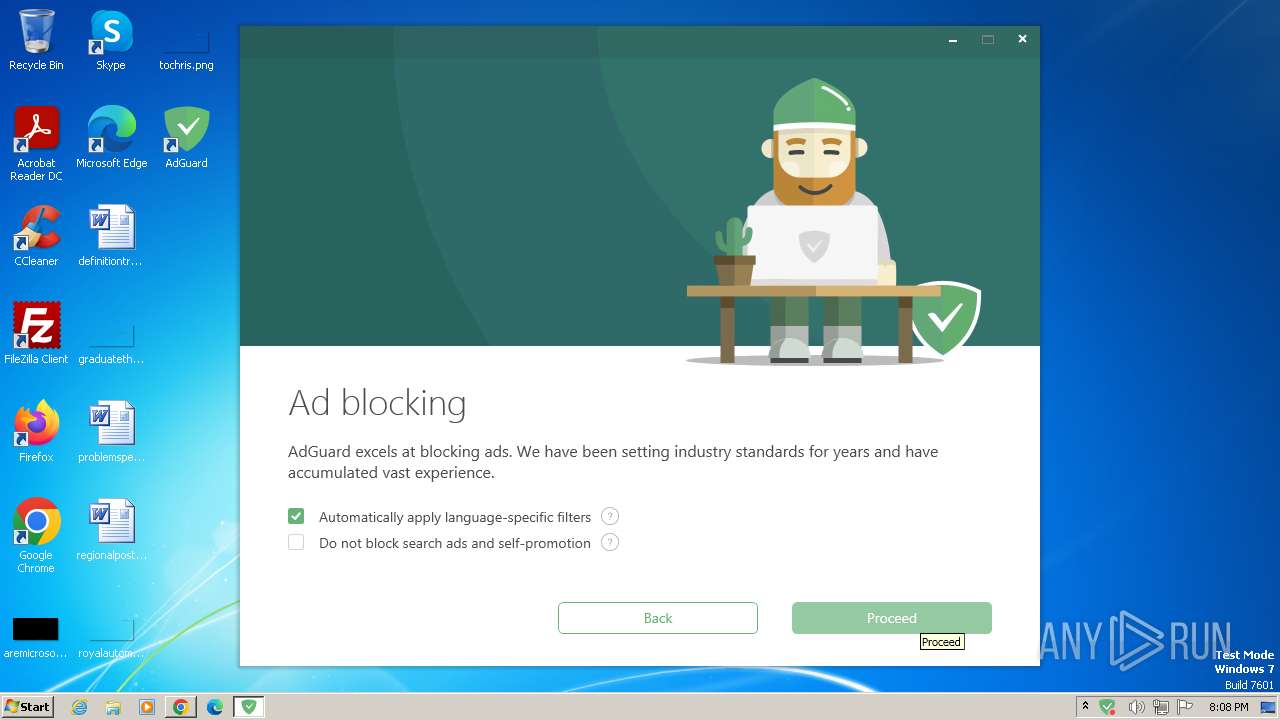
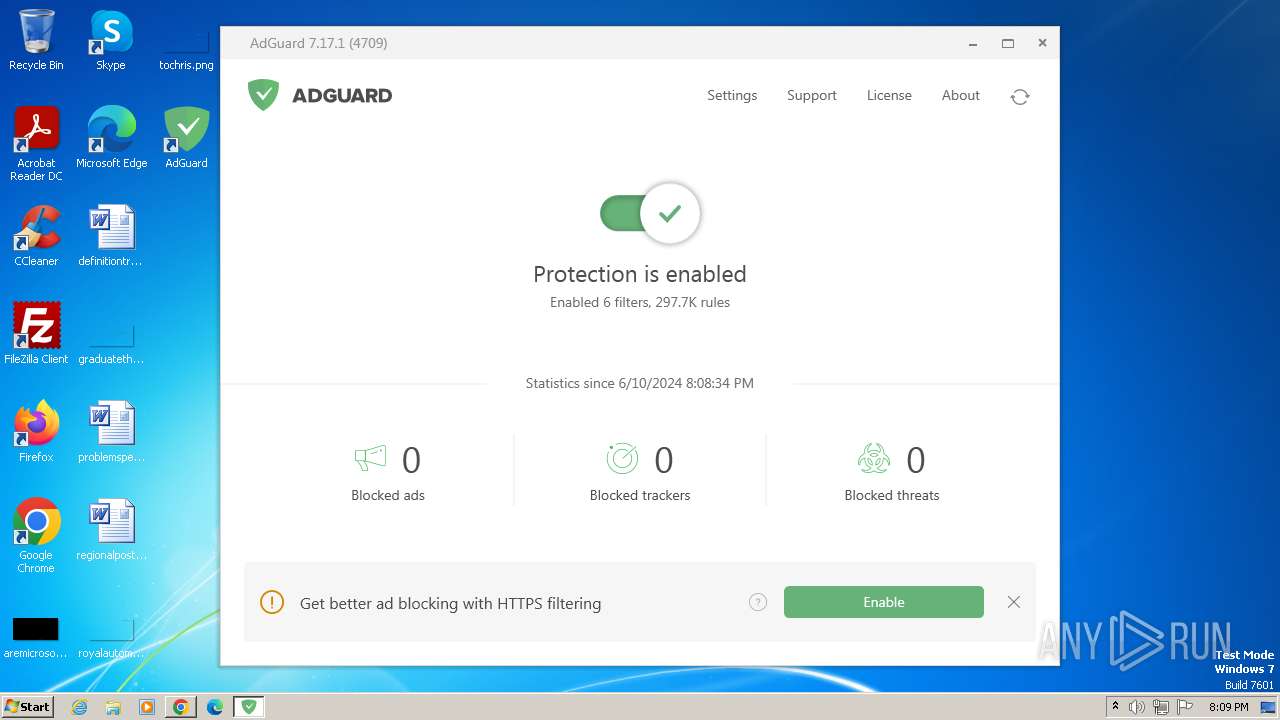
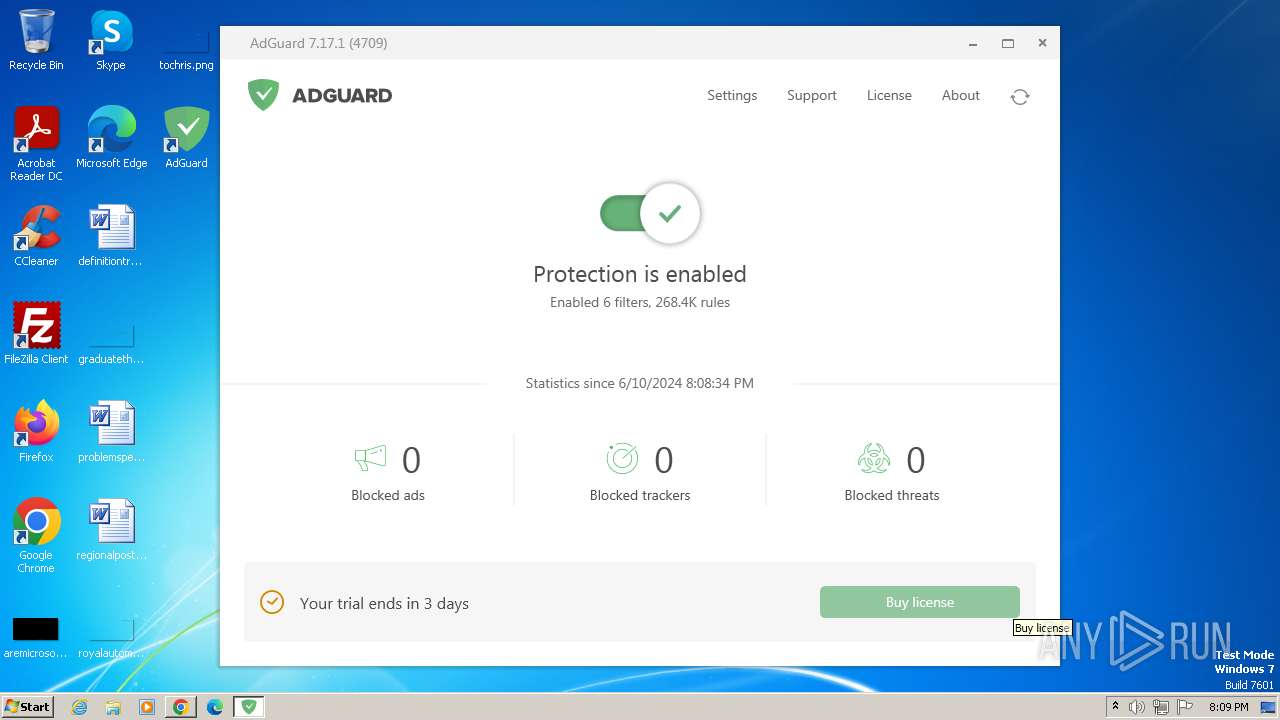
Manual execution by a user
- wmpnscfg.exe (PID: 2556)
- Adguard.exe (PID: 928)
Checks supported languages
- wmpnscfg.exe (PID: 2556)
Reads the computer name
- wmpnscfg.exe (PID: 2556)
Drops the executable file immediately after the start
- chrome.exe (PID: 3988)
- rundll32.exe (PID: 2924)
- rundll32.exe (PID: 2316)
- rundll32.exe (PID: 3008)
- rundll32.exe (PID: 2284)
- rundll32.exe (PID: 2376)
- rundll32.exe (PID: 1372)
- chrome.exe (PID: 1800)
The process uses the downloaded file
- chrome.exe (PID: 2696)
Executable content was dropped or overwritten
- chrome.exe (PID: 3988)
- msiexec.exe (PID: 948)
- chrome.exe (PID: 1800)
Application launched itself
- chrome.exe (PID: 3988)
- msiexec.exe (PID: 948)
Dropped object may contain TOR URL's
- msiexec.exe (PID: 948)
- AdguardSvc.exe (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
123
Monitored processes
68
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1512 --field-trial-handle=1172,i,16424367918586551558,2206180156520087558,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=1996 --field-trial-handle=1172,i,16424367918586551558,2206180156520087558,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 368 | "ie4uinit.exe" -ClearIconCache | C:\Windows\System32\ie4uinit.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2004 --field-trial-handle=1172,i,16424367918586551558,2206180156520087558,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1272 --field-trial-handle=1172,i,16424367918586551558,2206180156520087558,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 848 | "sc" sdshow "Adguard Service" | C:\Windows\System32\sc.exe | — | AdguardSvc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3036 --field-trial-handle=1172,i,16424367918586551558,2206180156520087558,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 928 | "C:\Program Files\AdGuard\Adguard.exe" | C:\Program Files\AdGuard\Adguard.exe | — | explorer.exe | |||||||||||
User: admin Company: Adguard Software Limited Integrity Level: MEDIUM Description: AdGuard for Windows Version: 7.17.4709.0 | |||||||||||||||
| 948 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3320 --field-trial-handle=1172,i,16424367918586551558,2206180156520087558,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
10 011
Read events
9 920
Write events
85
Delete events
6
Modification events
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
251
Suspicious files
363
Text files
123
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1033c4.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF103aa9.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1033d3.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF104b05.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
93
DNS requests
142
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 217.20.57.22:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?223c9450285bf91b | unknown | — | — | unknown |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
— | — | GET | 200 | 2.19.105.18:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
— | — | GET | 301 | 195.181.175.15:80 | http://static.adtidy.org/windows/setup.exe | unknown | — | — | unknown |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
— | — | GET | 301 | 195.181.170.19:80 | http://static.adguard.com/installer.v1.0.json | unknown | — | — | unknown |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3988 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
748 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | unknown |
748 | chrome.exe | 151.101.195.52:443 | adguard.en.uptodown.com | FASTLY | US | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
748 | chrome.exe | 151.101.67.52:443 | adguard.en.uptodown.com | FASTLY | US | unknown |
748 | chrome.exe | 142.250.184.232:443 | www.googletagmanager.com | GOOGLE | US | unknown |
748 | chrome.exe | 104.22.74.216:443 | btloader.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
adguard.en.uptodown.com |
| unknown |
stc.utdstc.com |
| unknown |
geo.cookie-script.com |
| unknown |
img.utdstc.com |
| whitelisted |
btloader.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
scripts.ssm.codes |
| unknown |
www.google-analytics.com |
| whitelisted |
api.btloader.com |
| whitelisted |