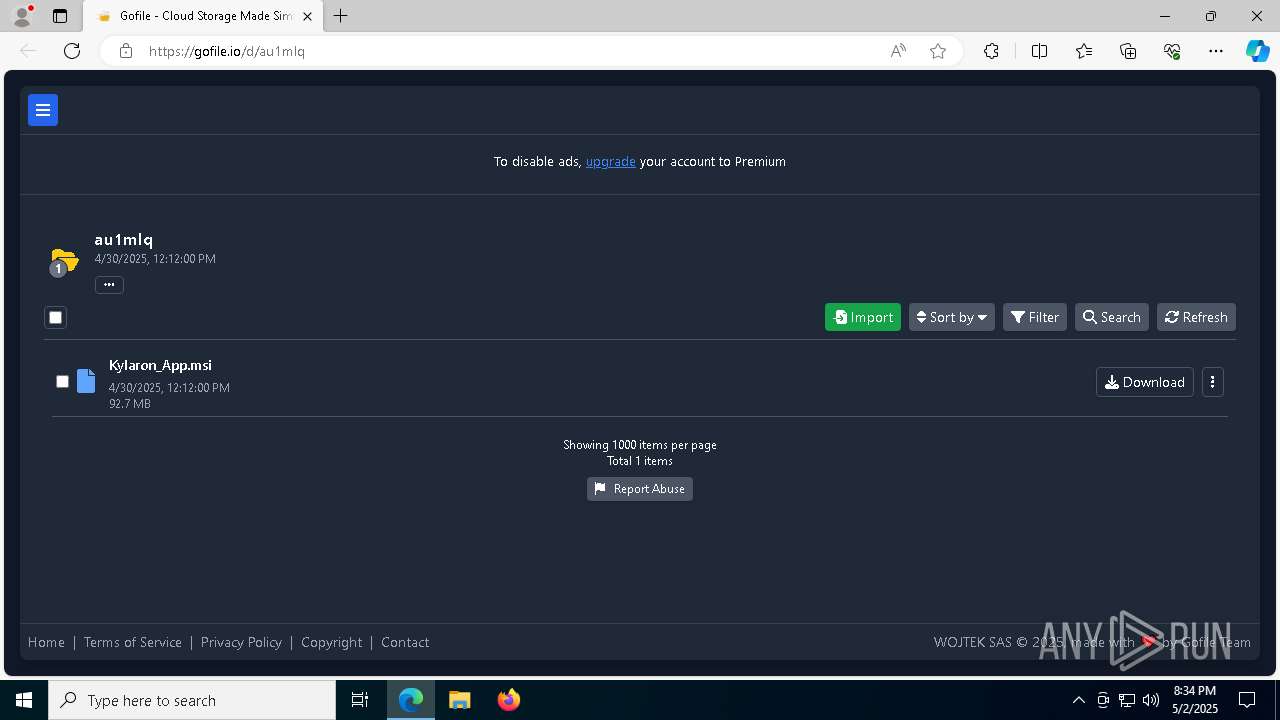
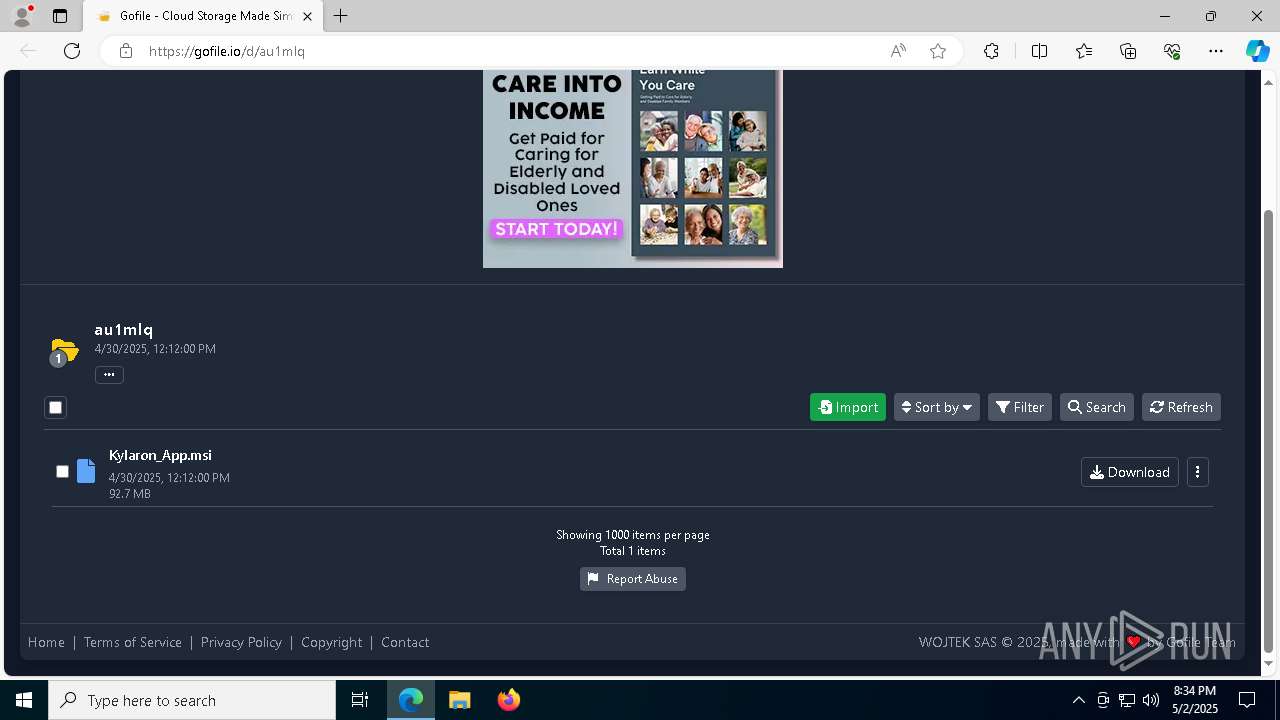
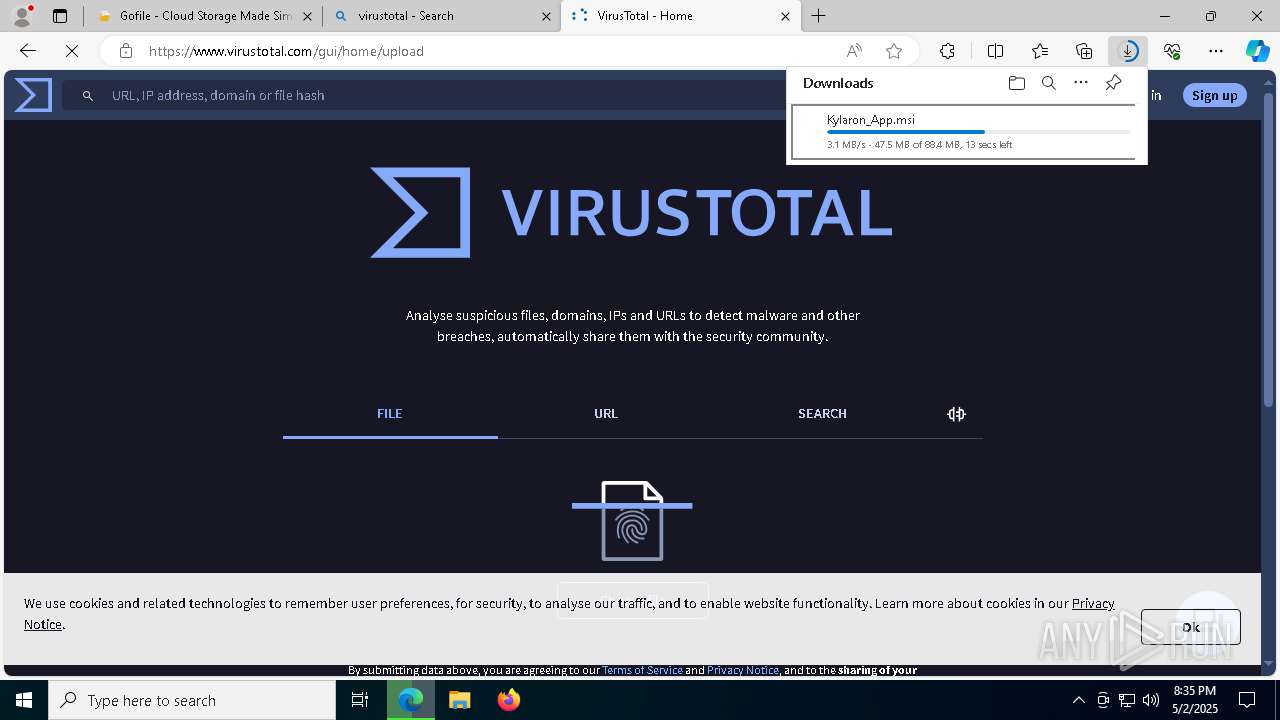
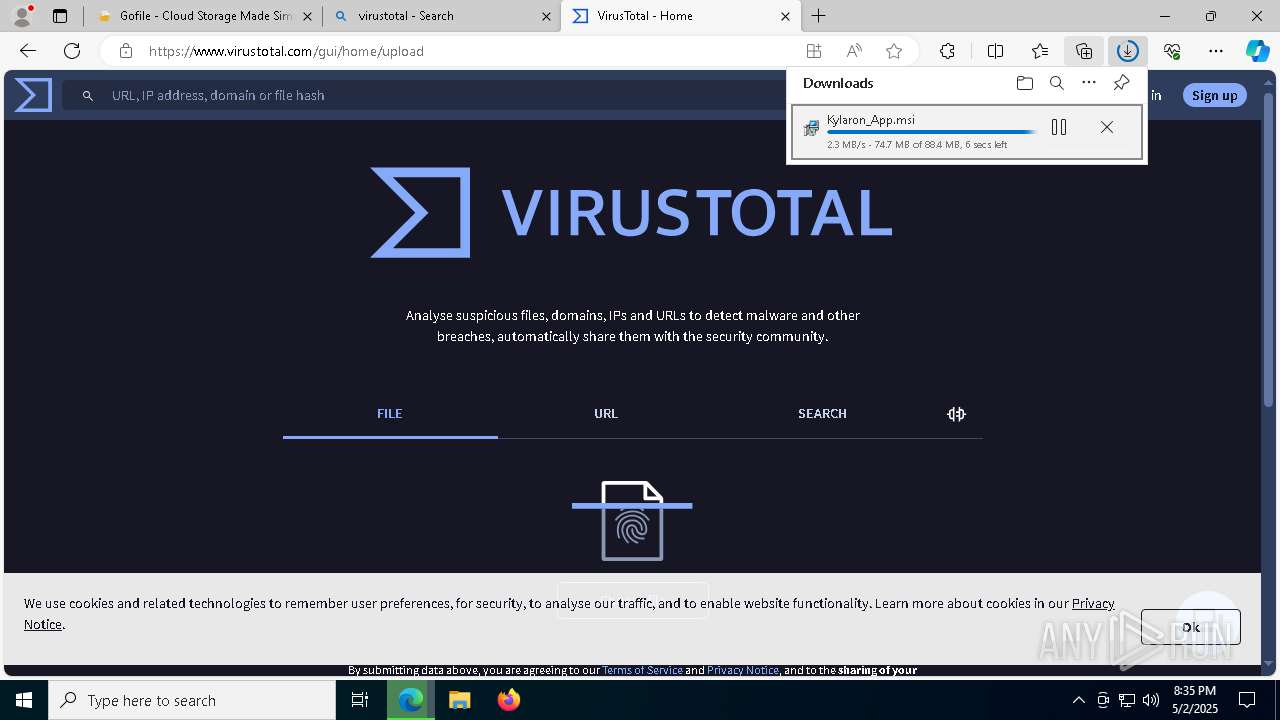
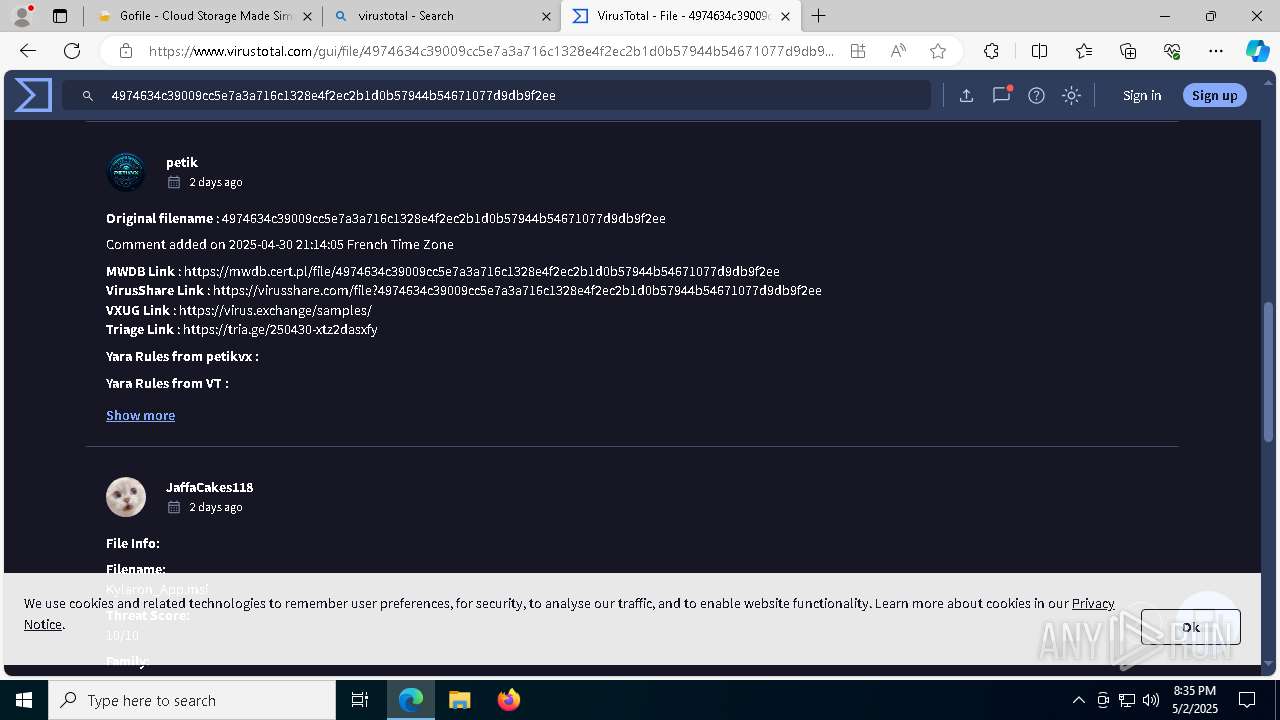
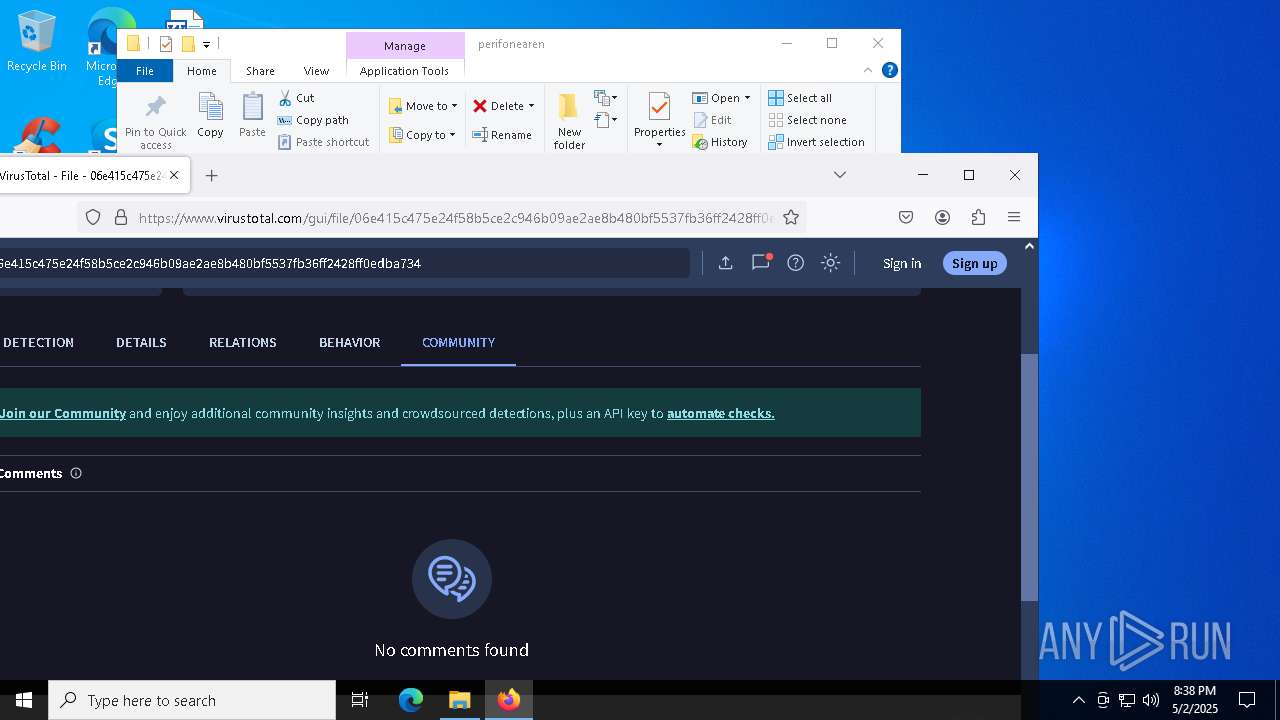
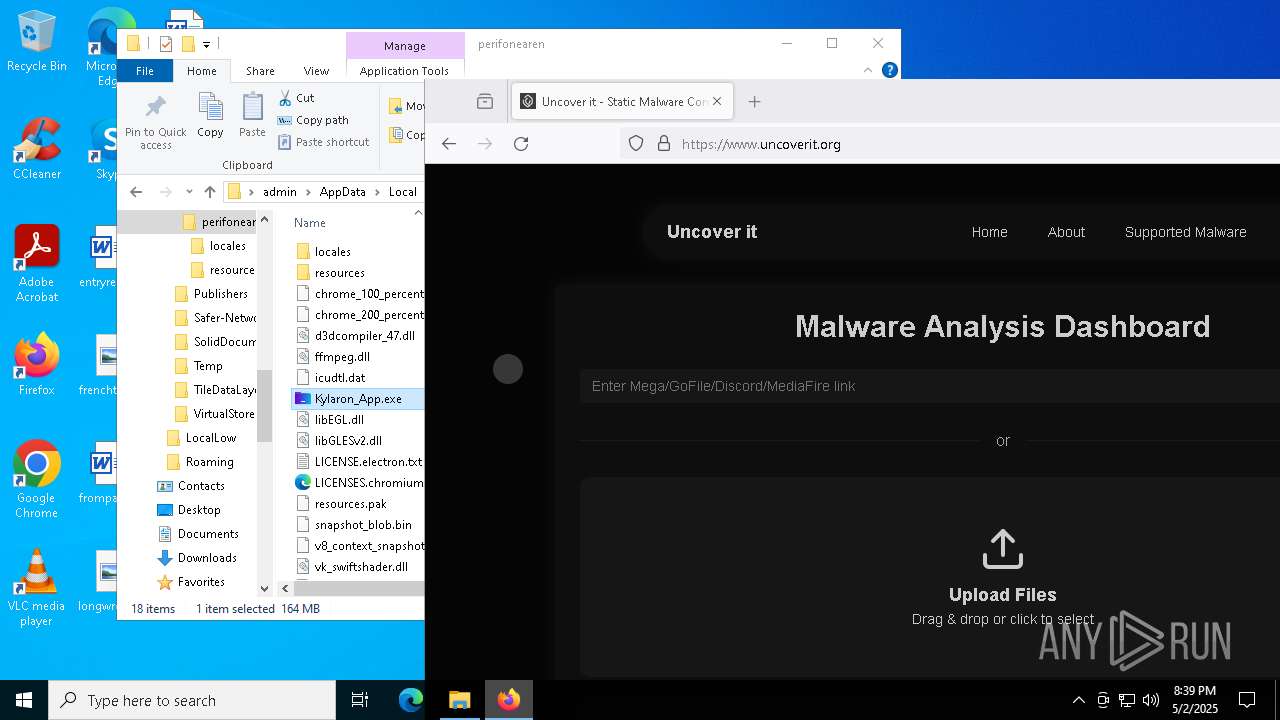
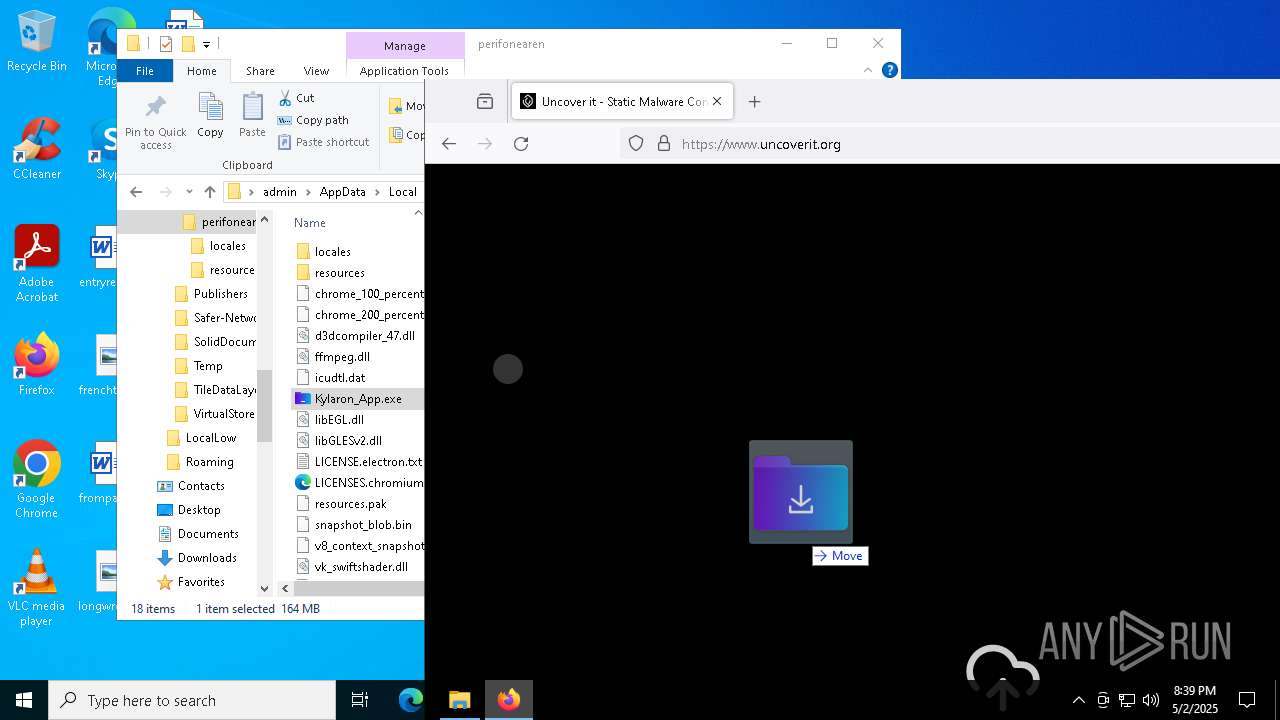
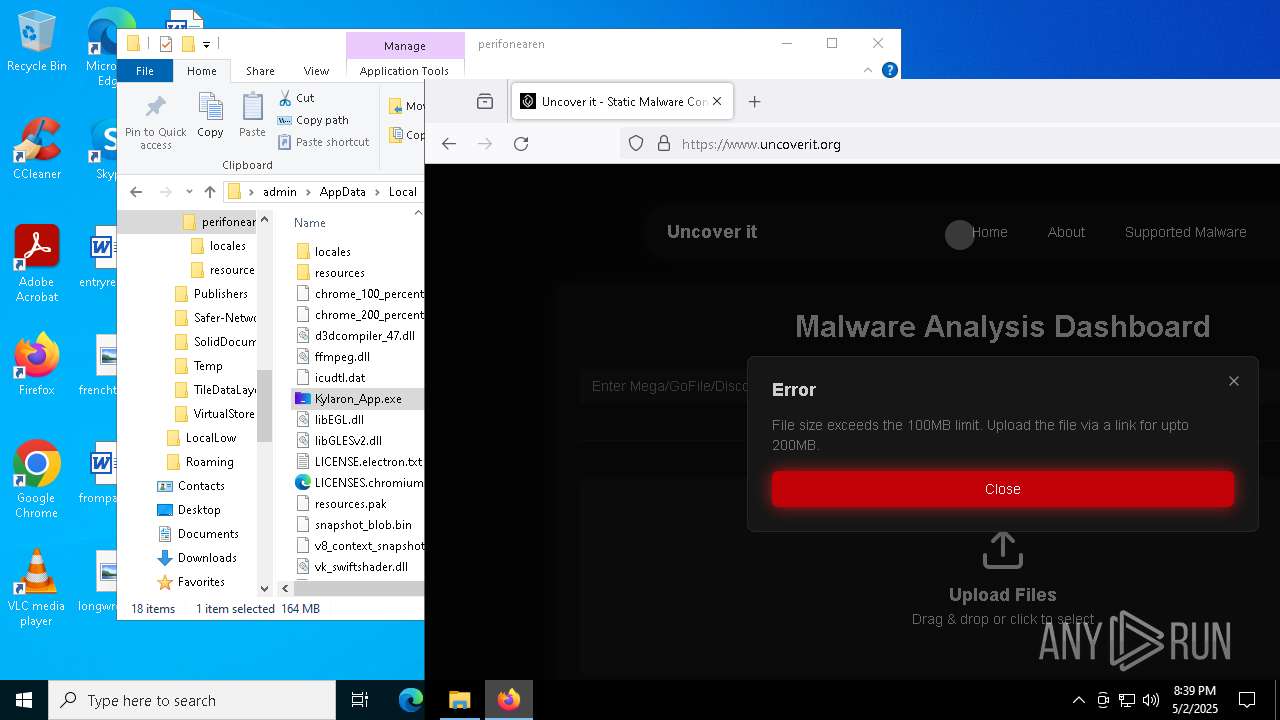
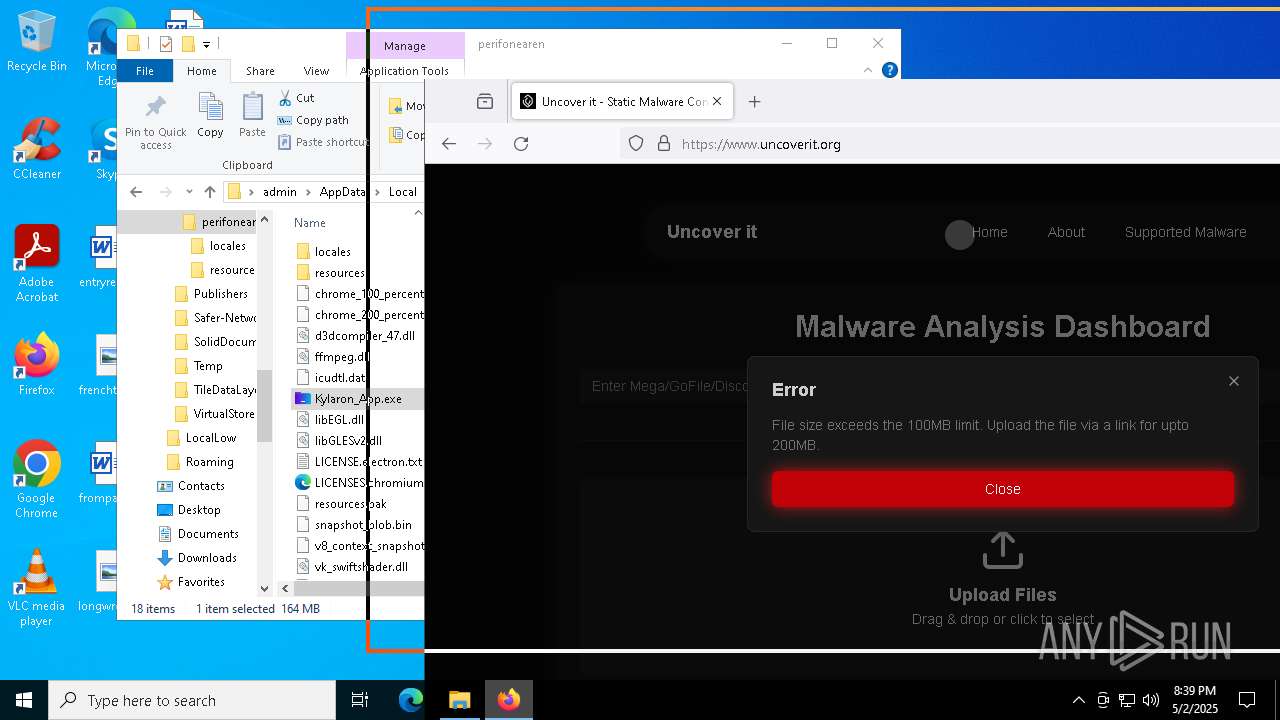
| URL: | https://gofile.io/d/au1mlq |
| Full analysis: | https://app.any.run/tasks/85e59715-da8d-4834-9e1a-b6e99e75a43a |
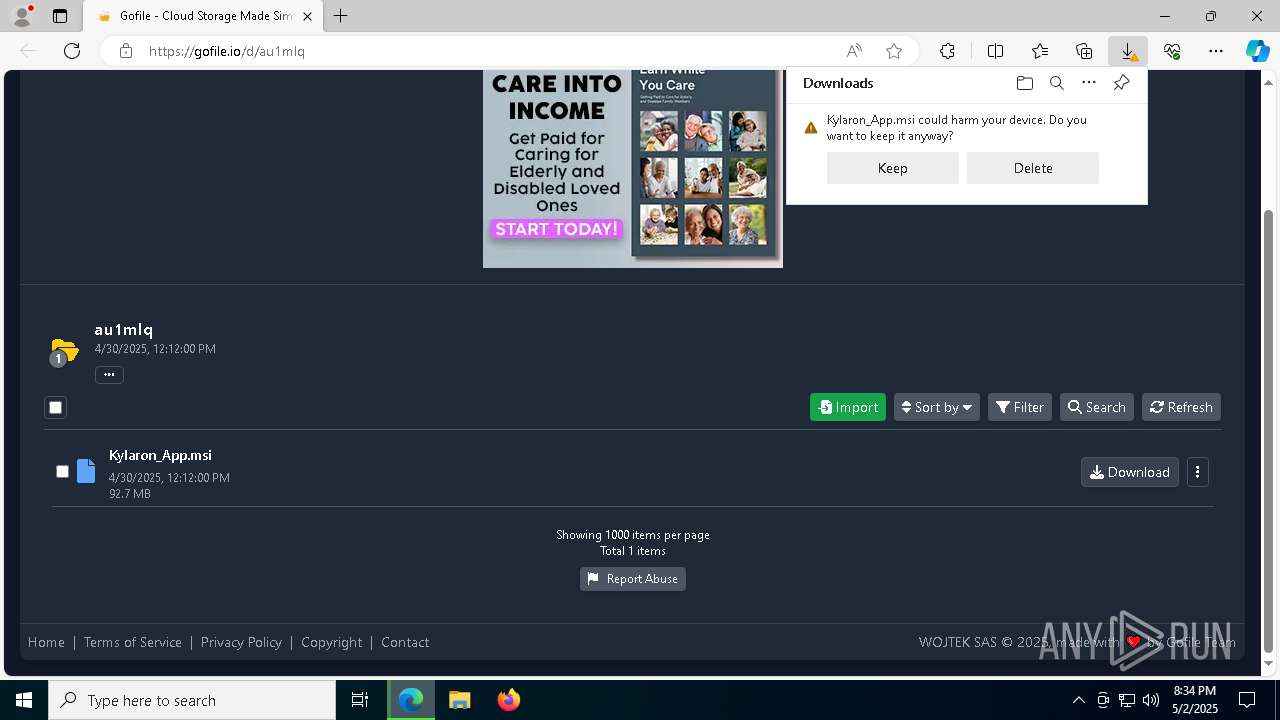
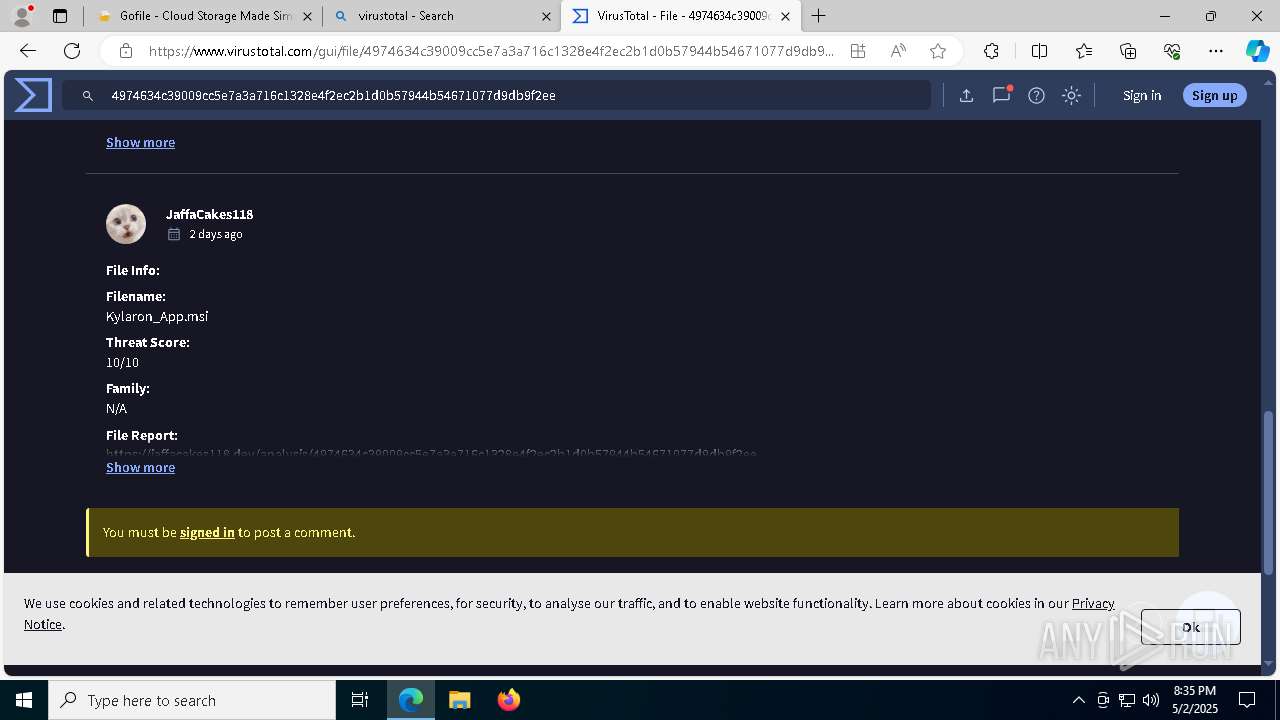
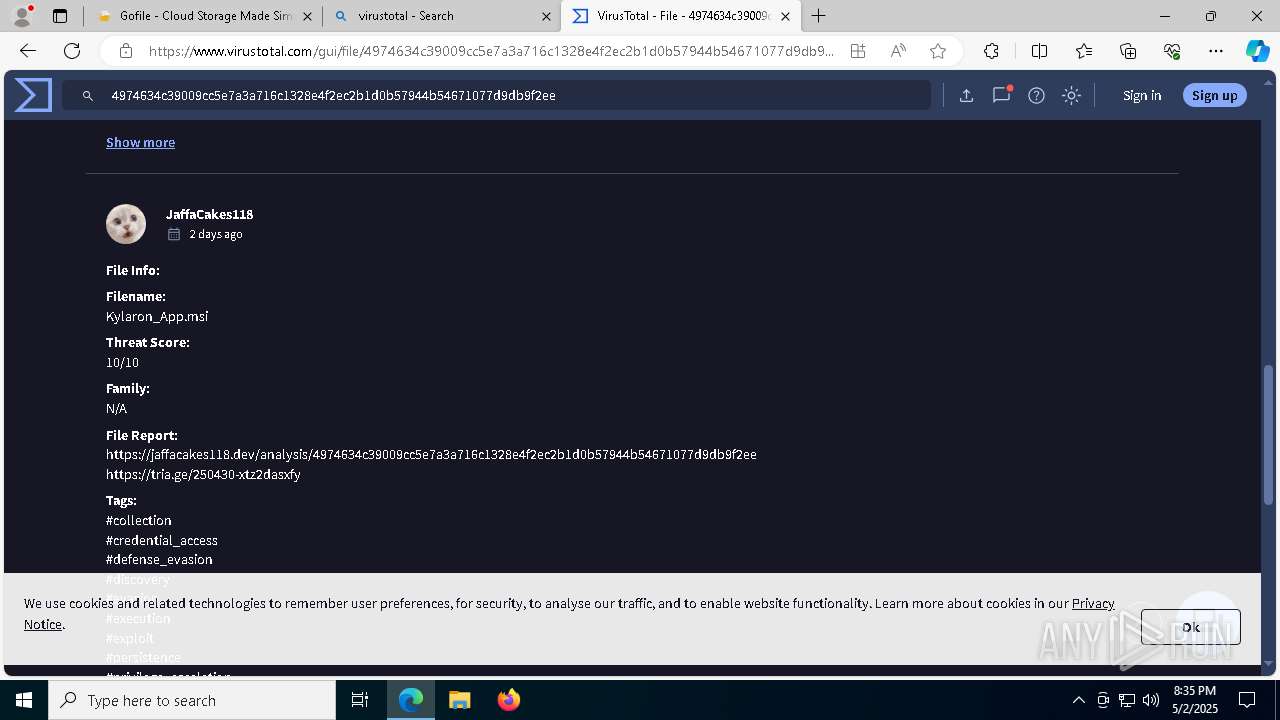
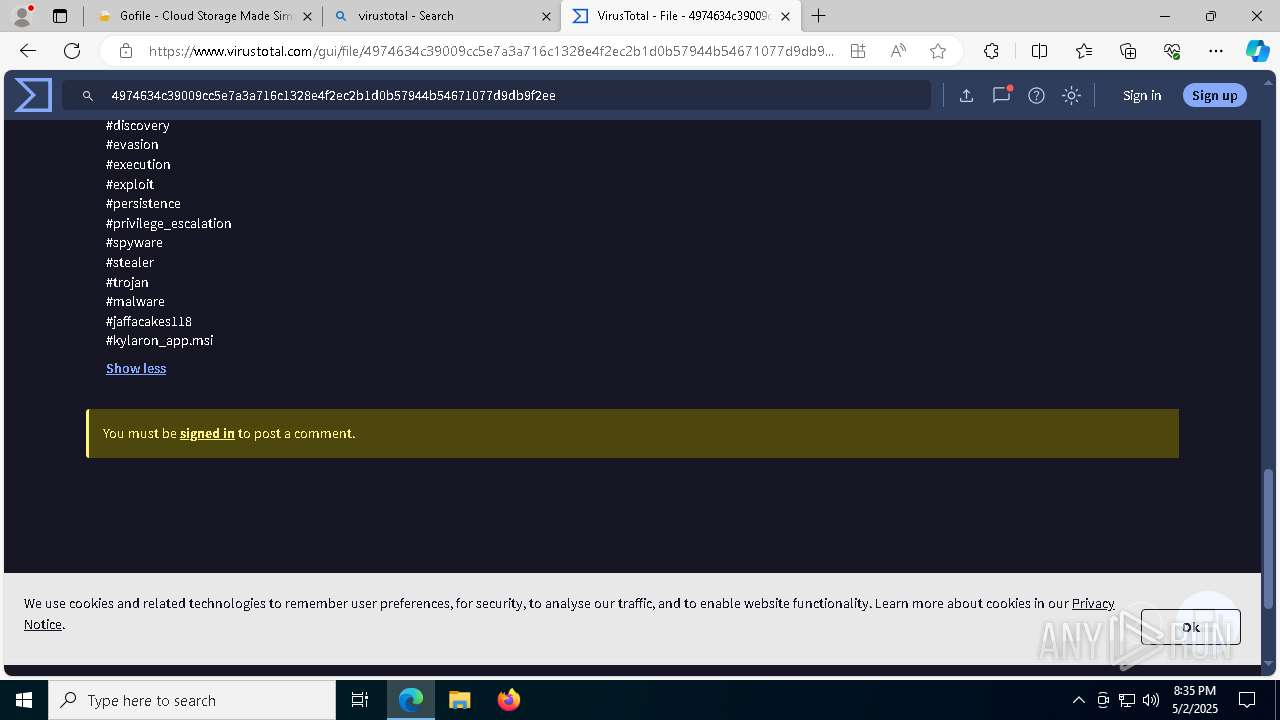
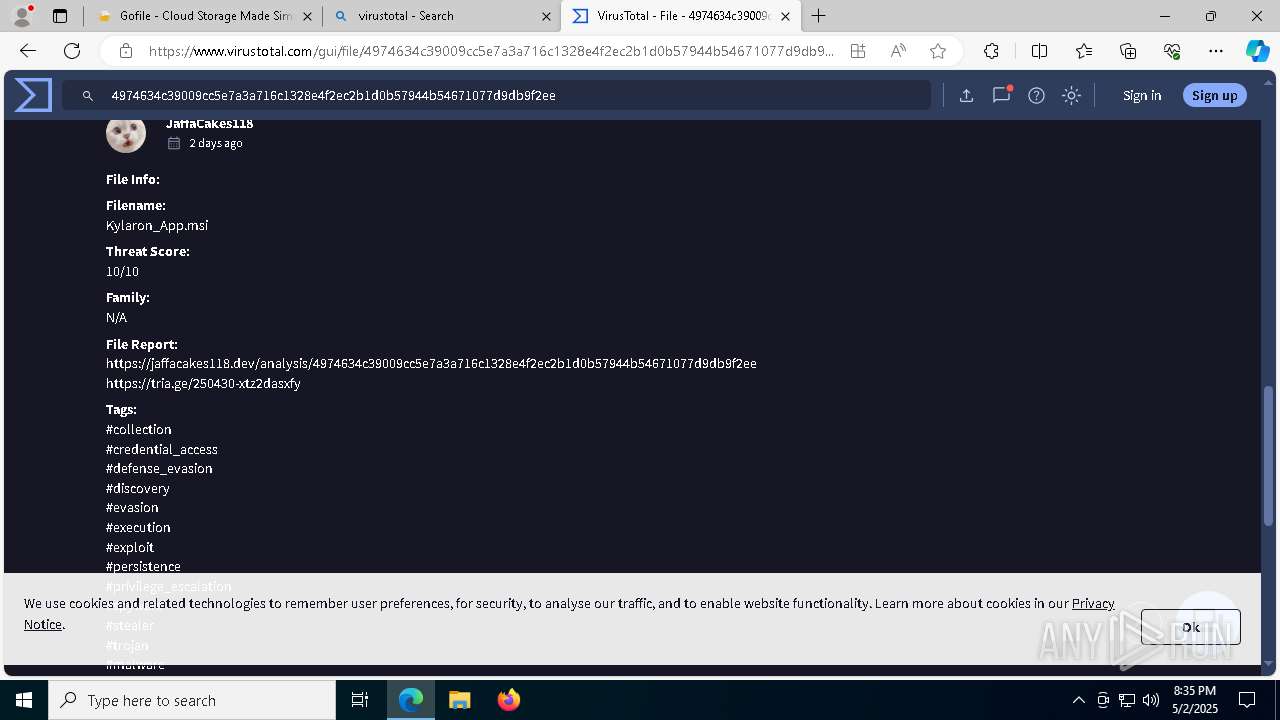
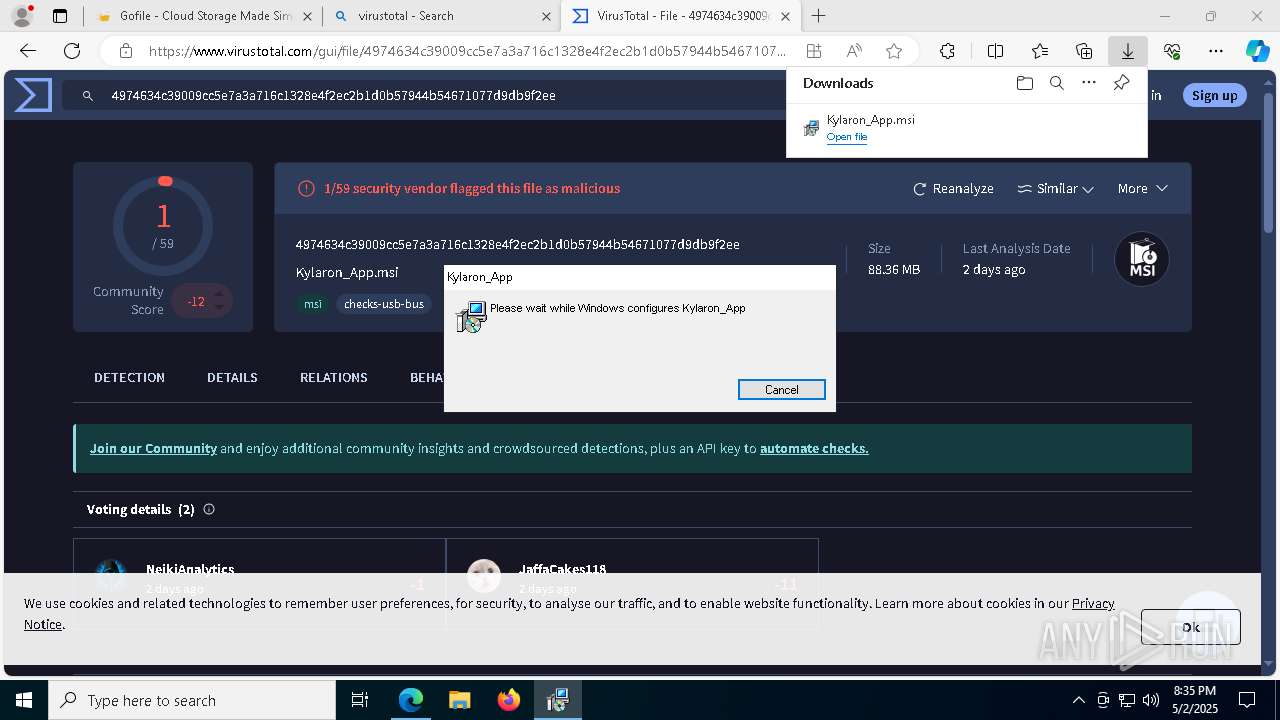
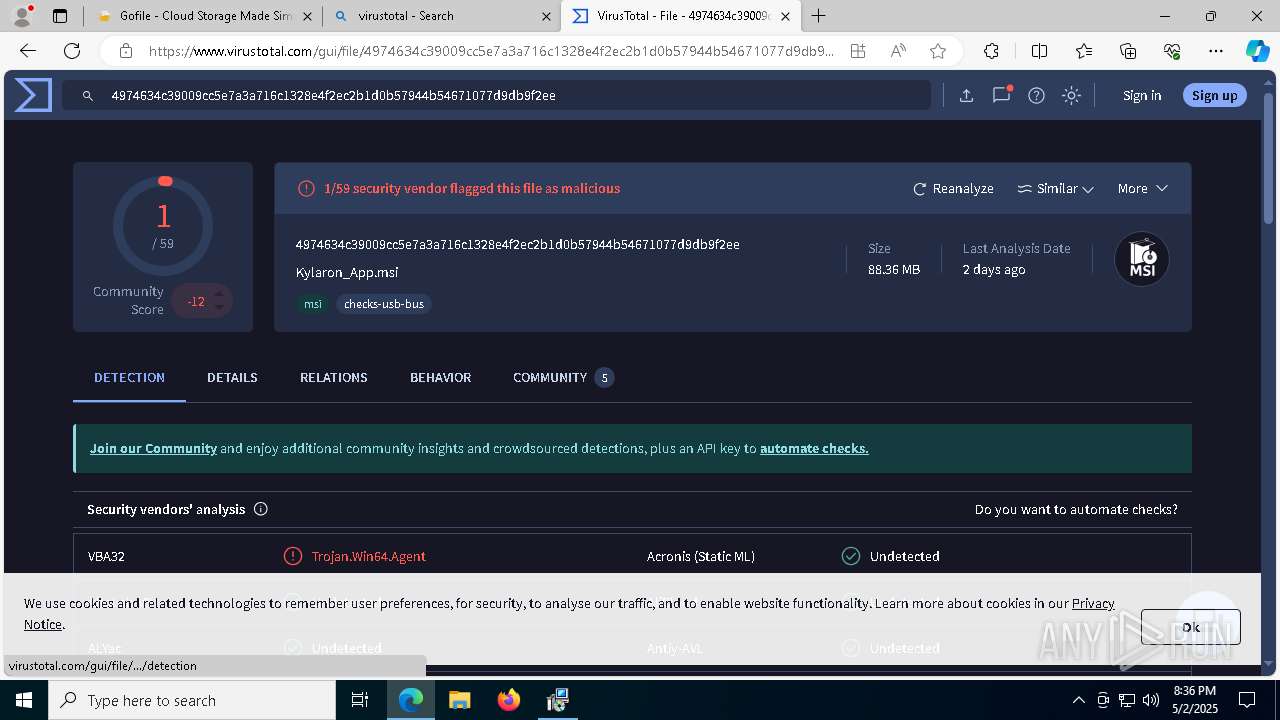
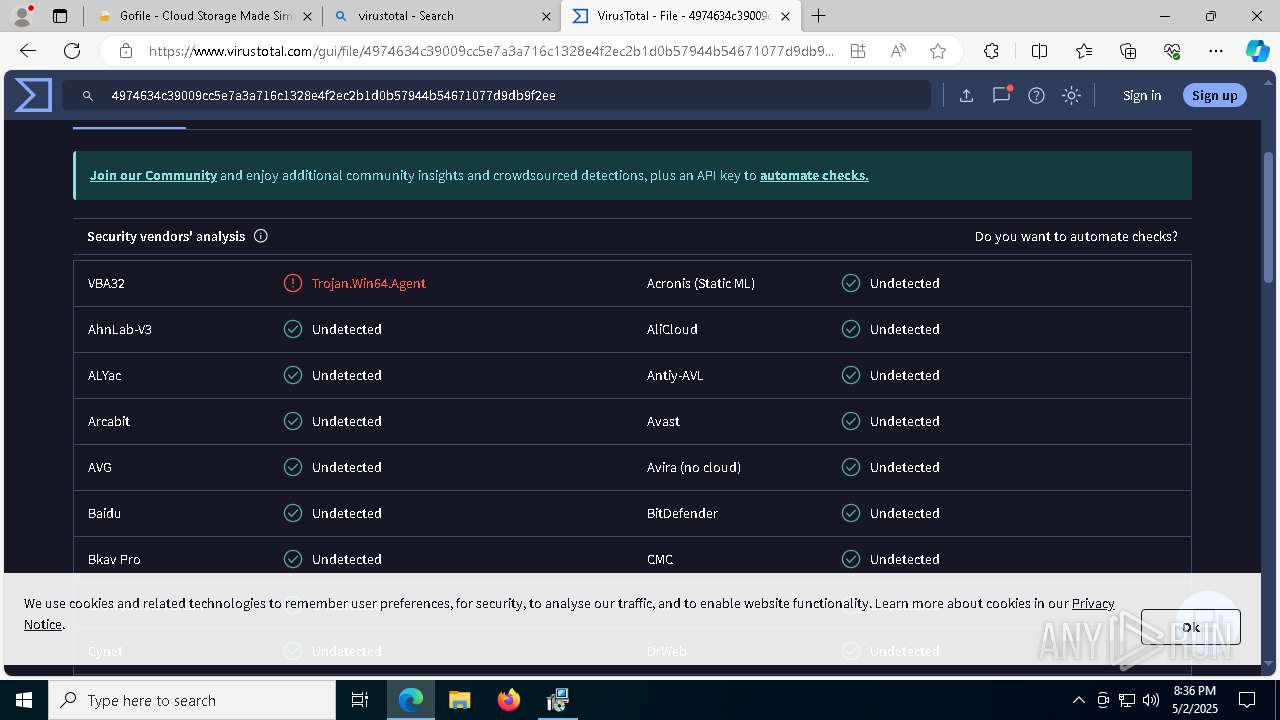
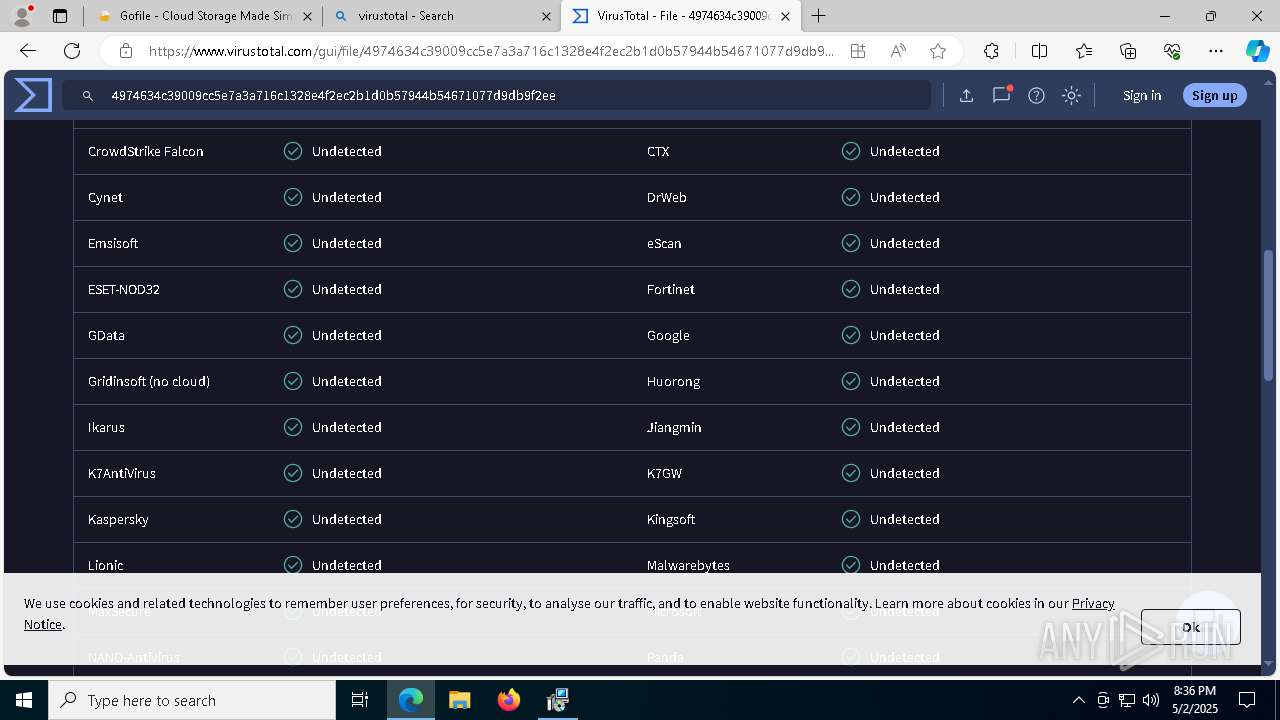
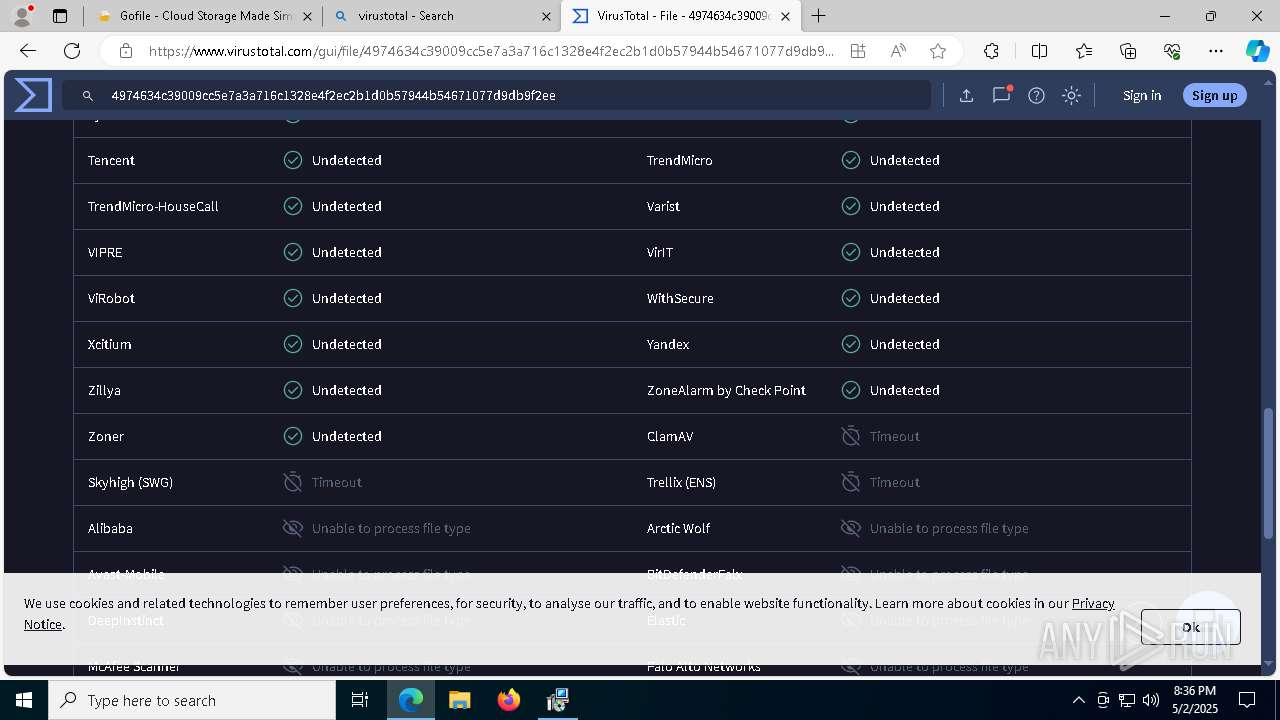
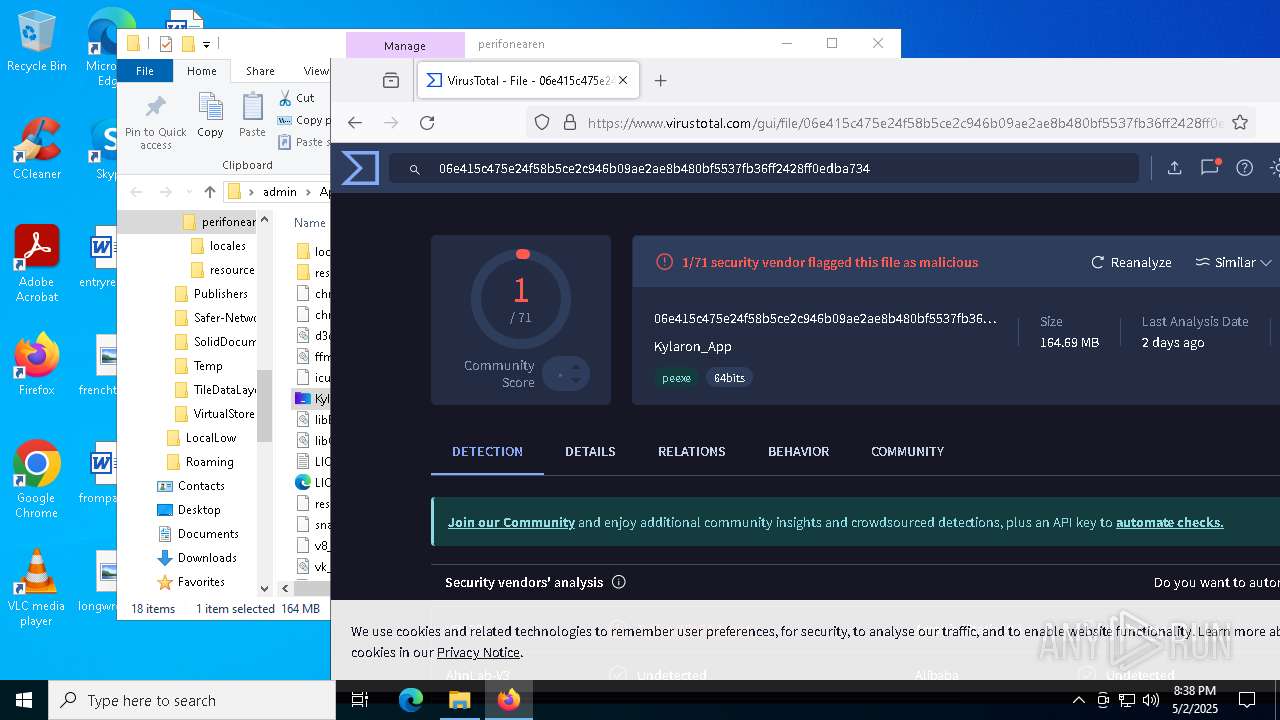
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2025, 20:34:36 |
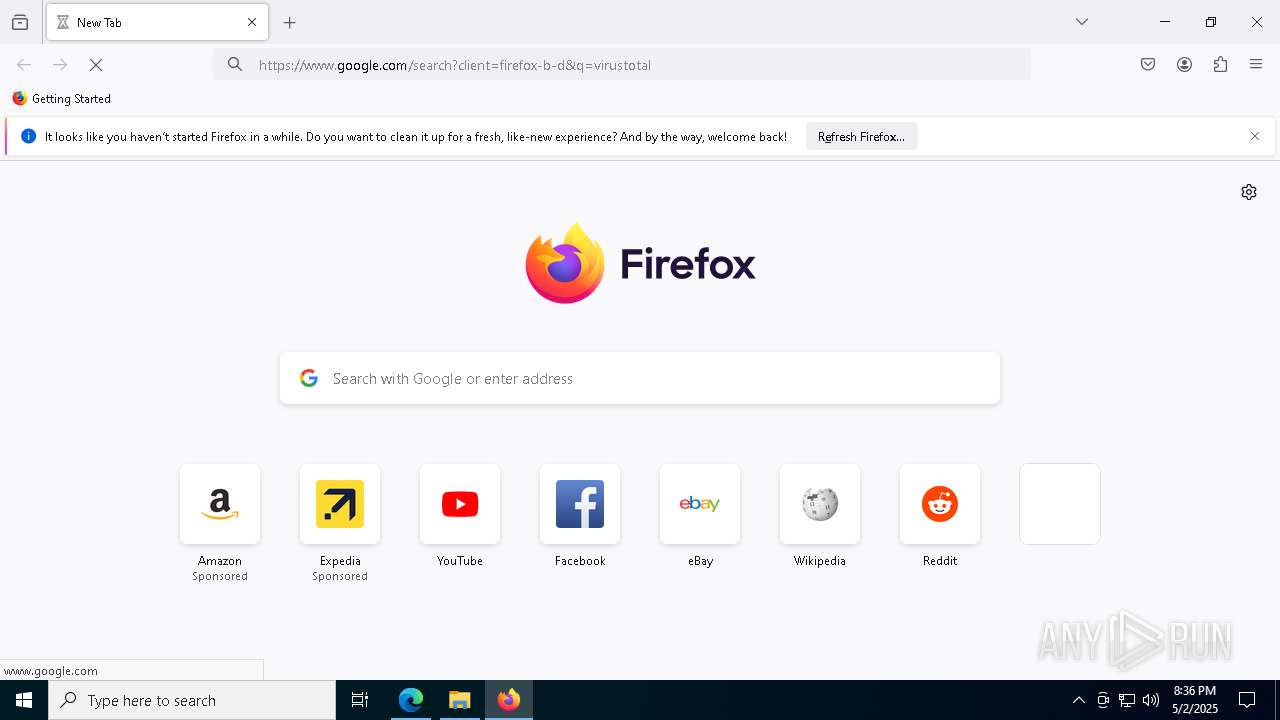
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
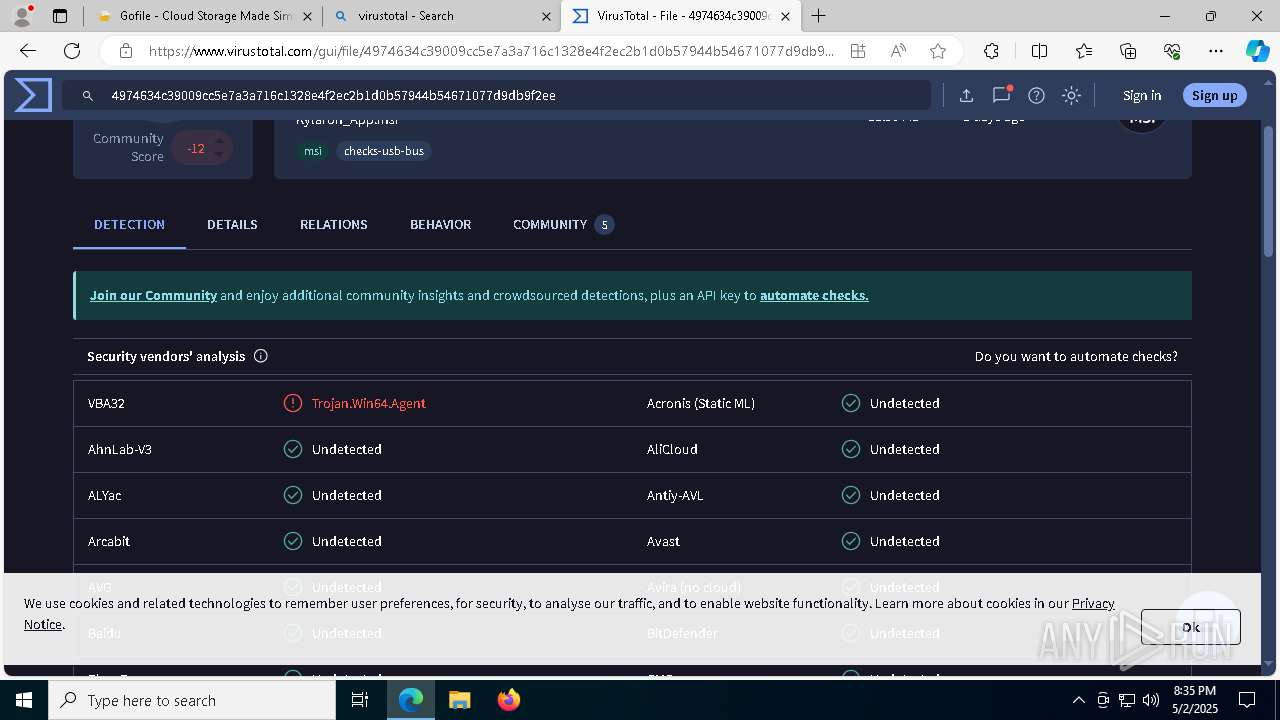
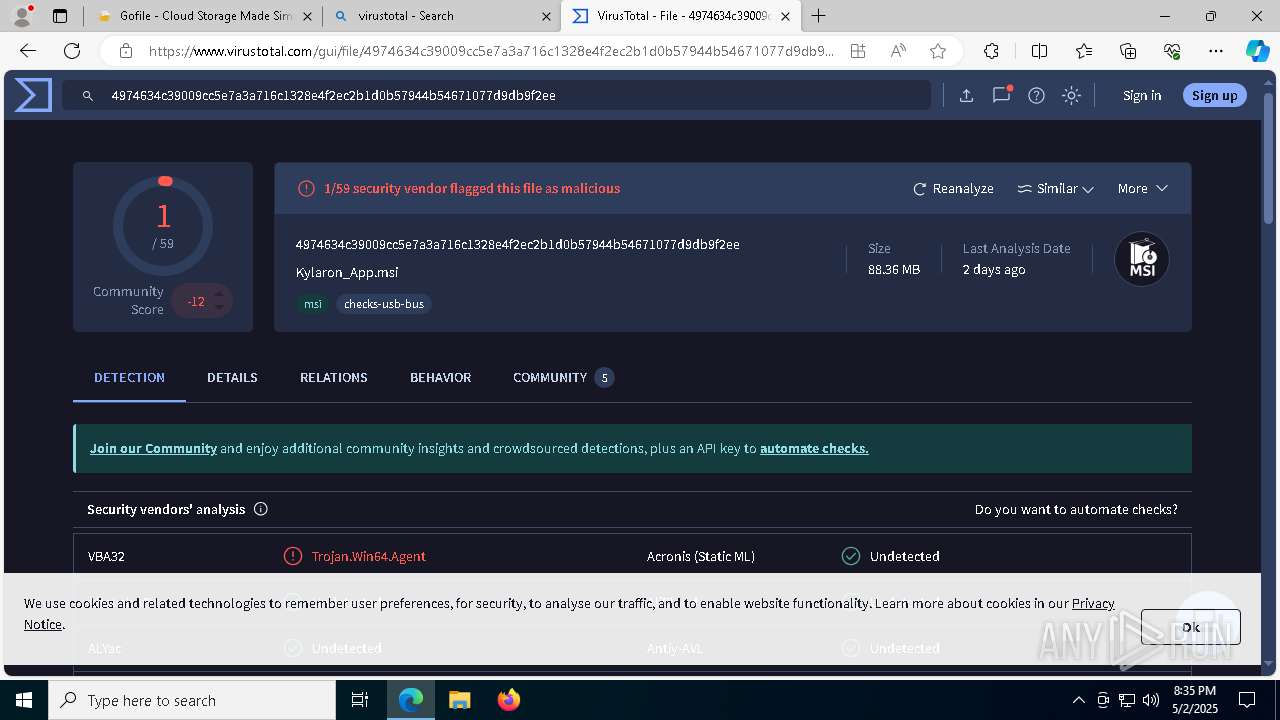
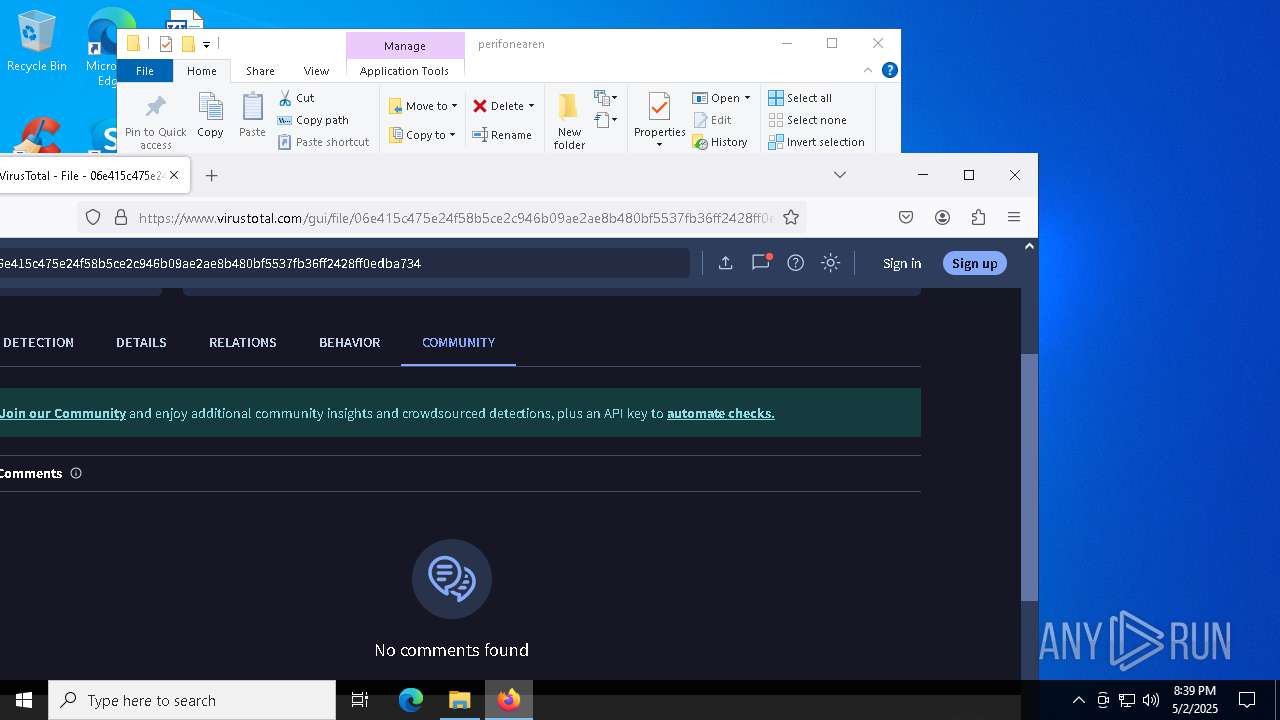
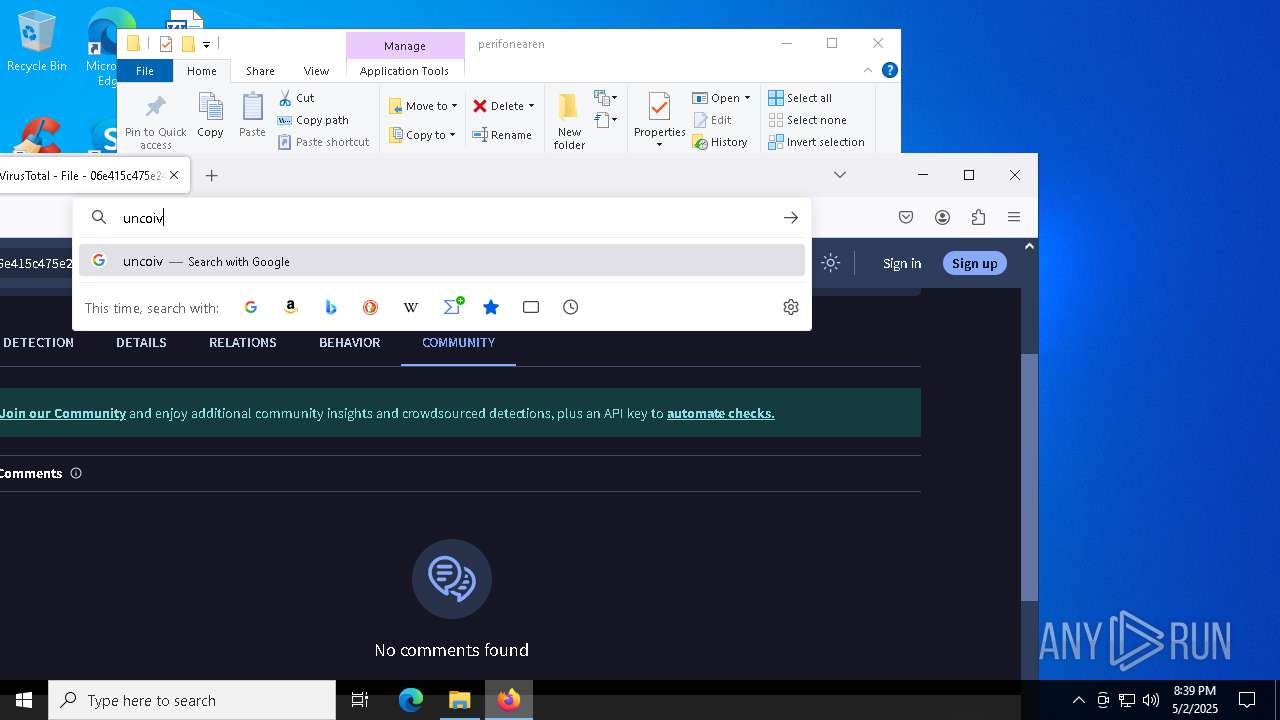
| MD5: | DC09DA8EA994D1E7ADBC7FCE1148308B |
| SHA1: | 86010912ACDF10F77A80E314F89FA78123DA5265 |
| SHA256: | 84AB2ACB879B3E28483C1E06A365C399F13B53DBB0BFE177AECC3A5C9FD8EF81 |
| SSDEEP: | 3:N8rxL1un:2ZEn |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 9832)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 10024)
Changes Windows Defender settings
- cmd.exe (PID: 9948)
Changes settings for real-time protection
- powershell.exe (PID: 8968)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 8588)
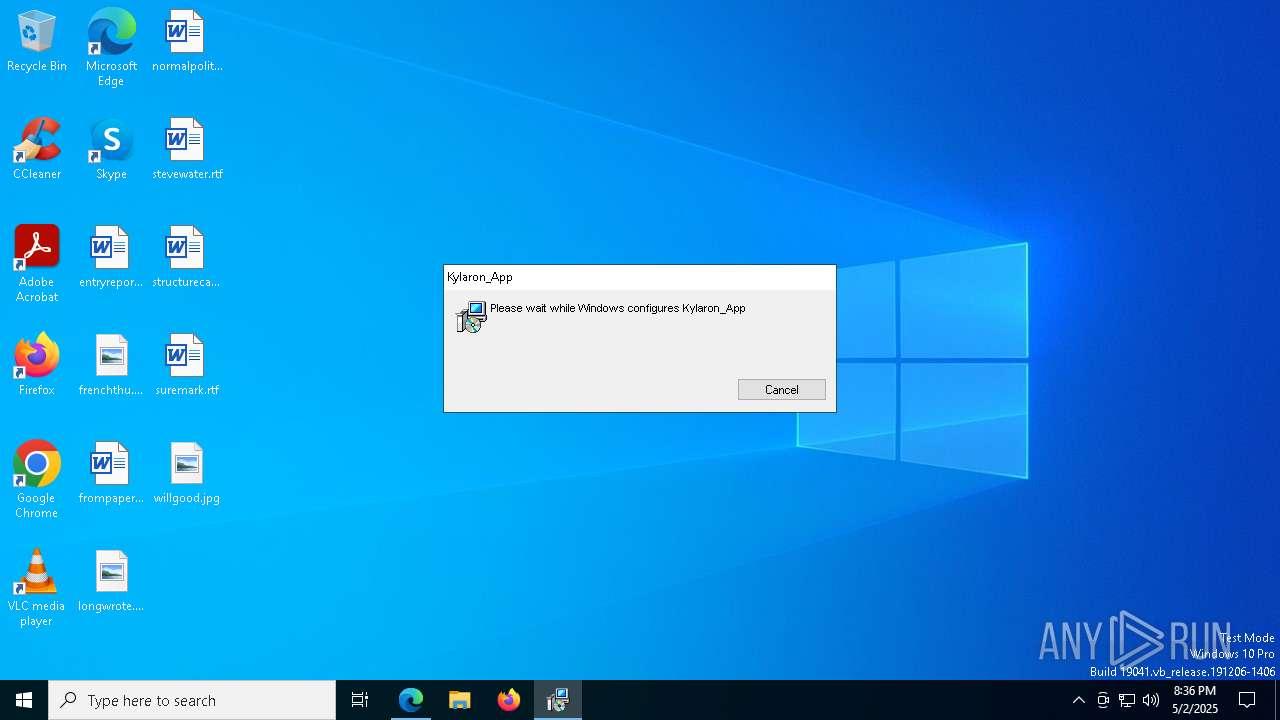
Process drops legitimate windows executable
- msiexec.exe (PID: 8596)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 3192)
- net.exe (PID: 2780)
- cmd.exe (PID: 8648)
- net.exe (PID: 10192)
- cmd.exe (PID: 9196)
- net.exe (PID: 10212)
- net.exe (PID: 8308)
- cmd.exe (PID: 10060)
- cmd.exe (PID: 2104)
- net.exe (PID: 7232)
- cmd.exe (PID: 7520)
- net.exe (PID: 8128)
- net.exe (PID: 7820)
- net.exe (PID: 7924)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 9224)
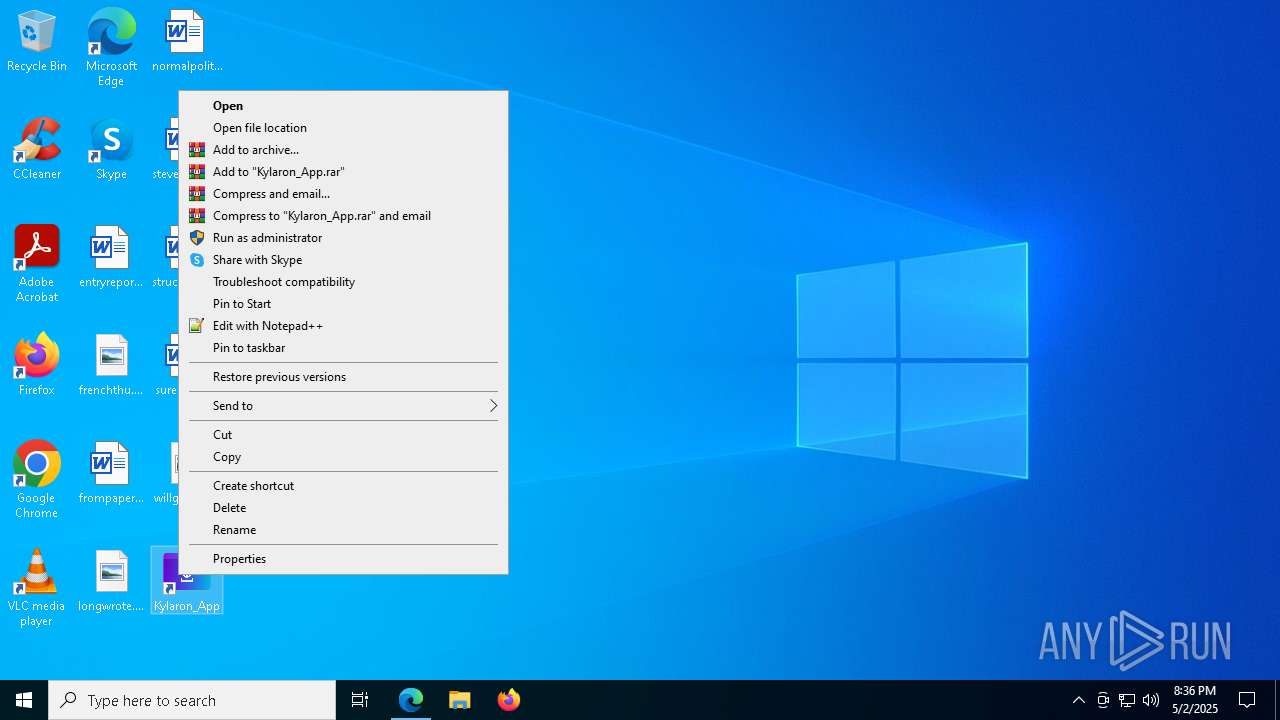
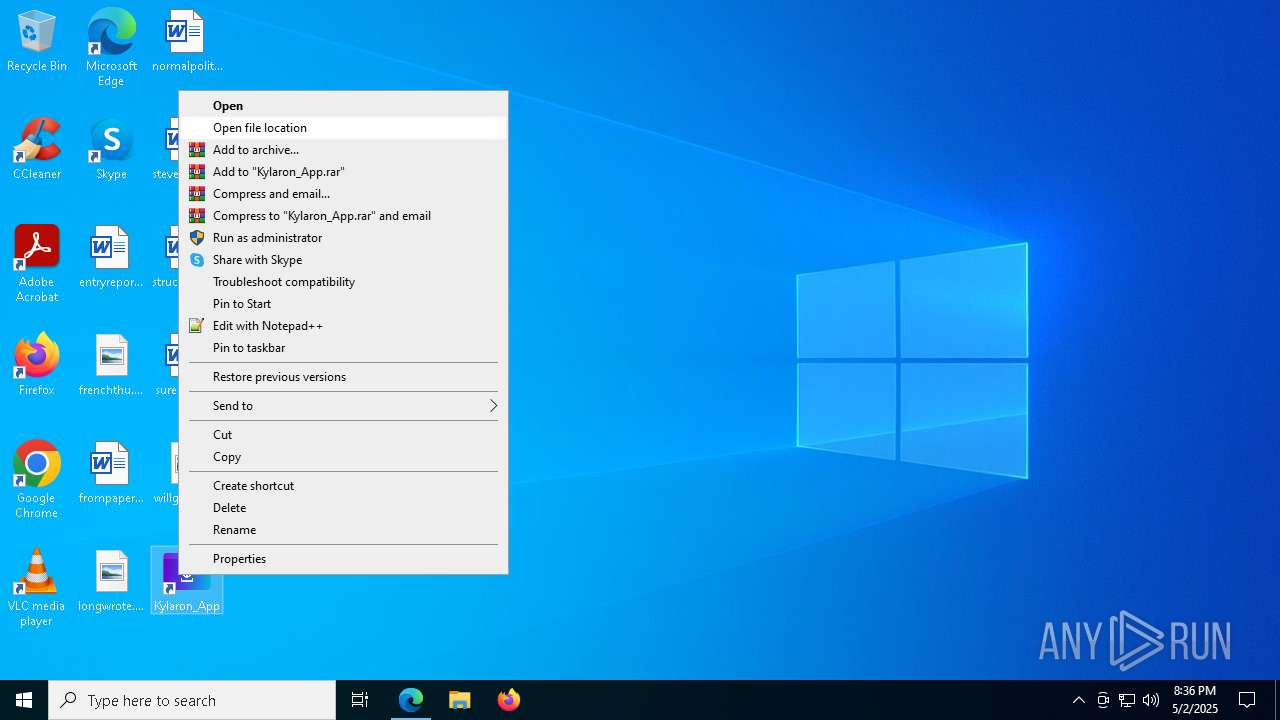
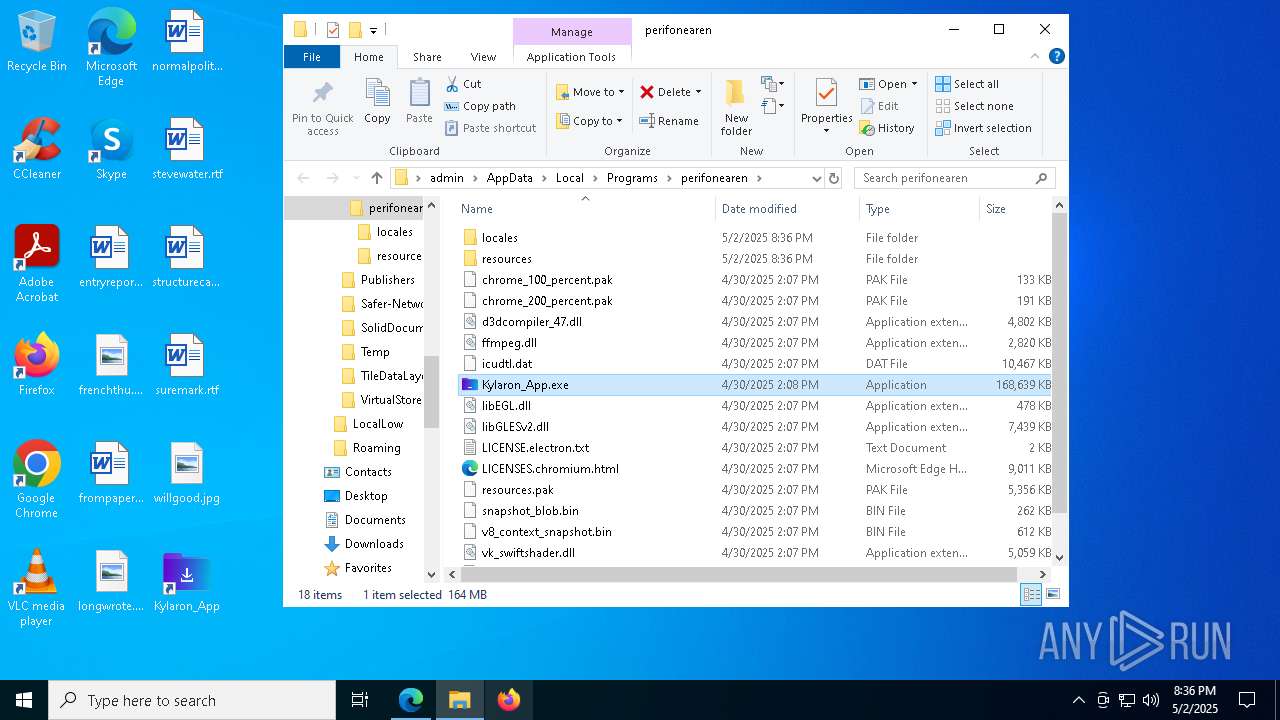
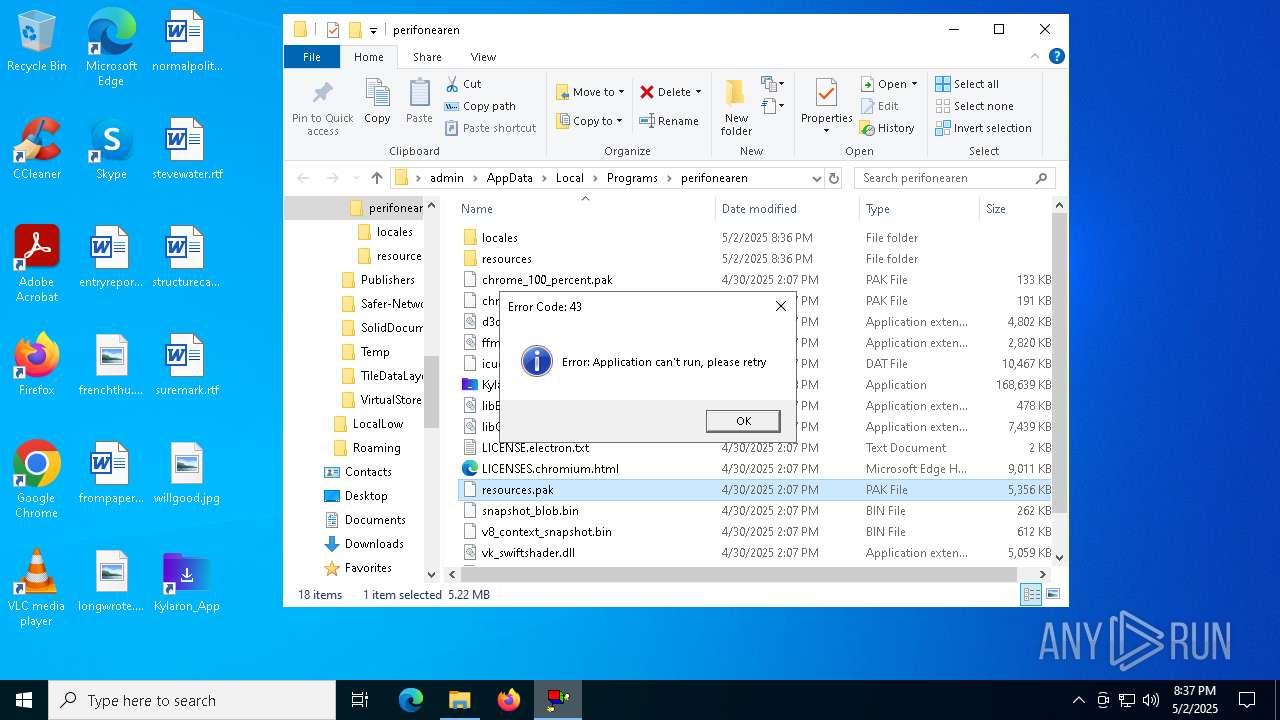
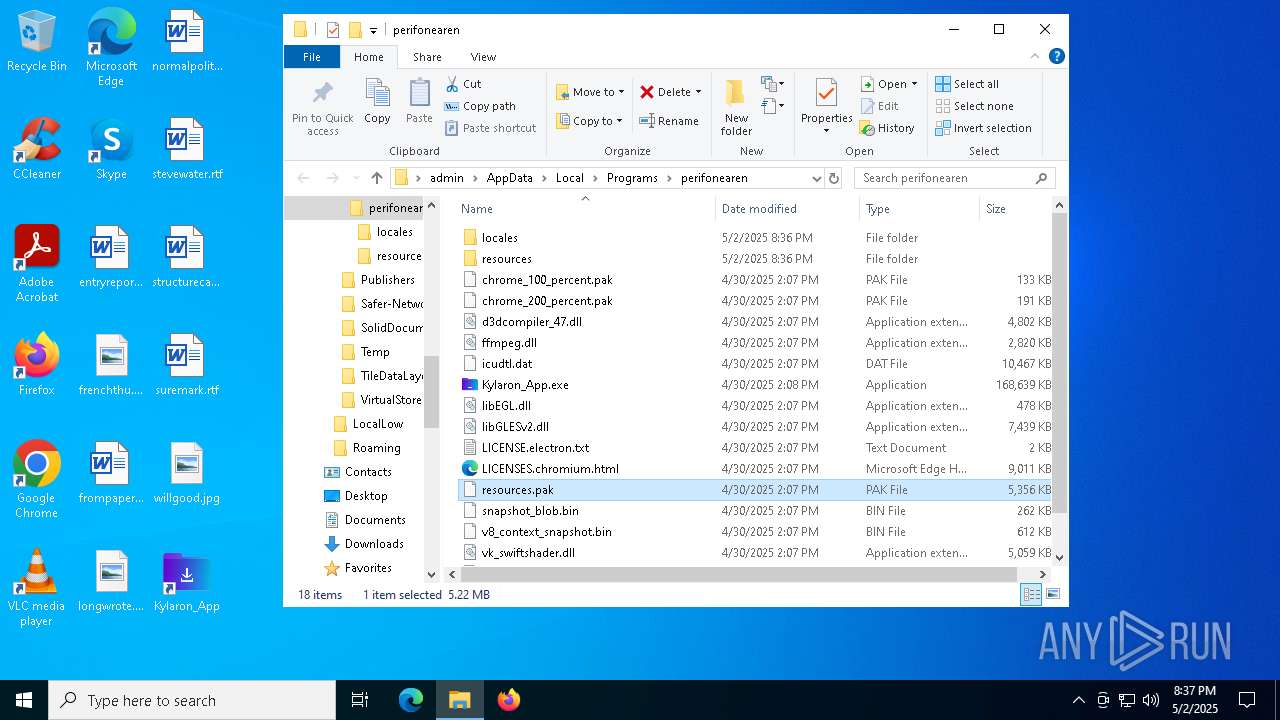
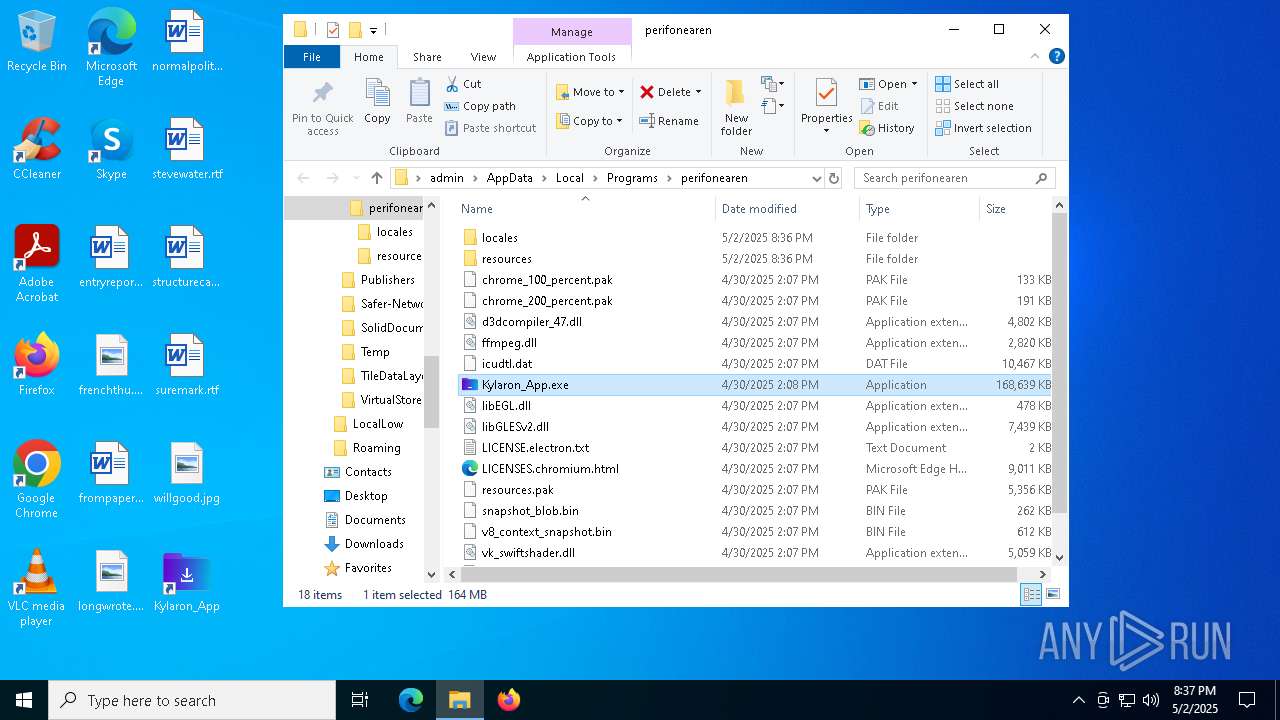
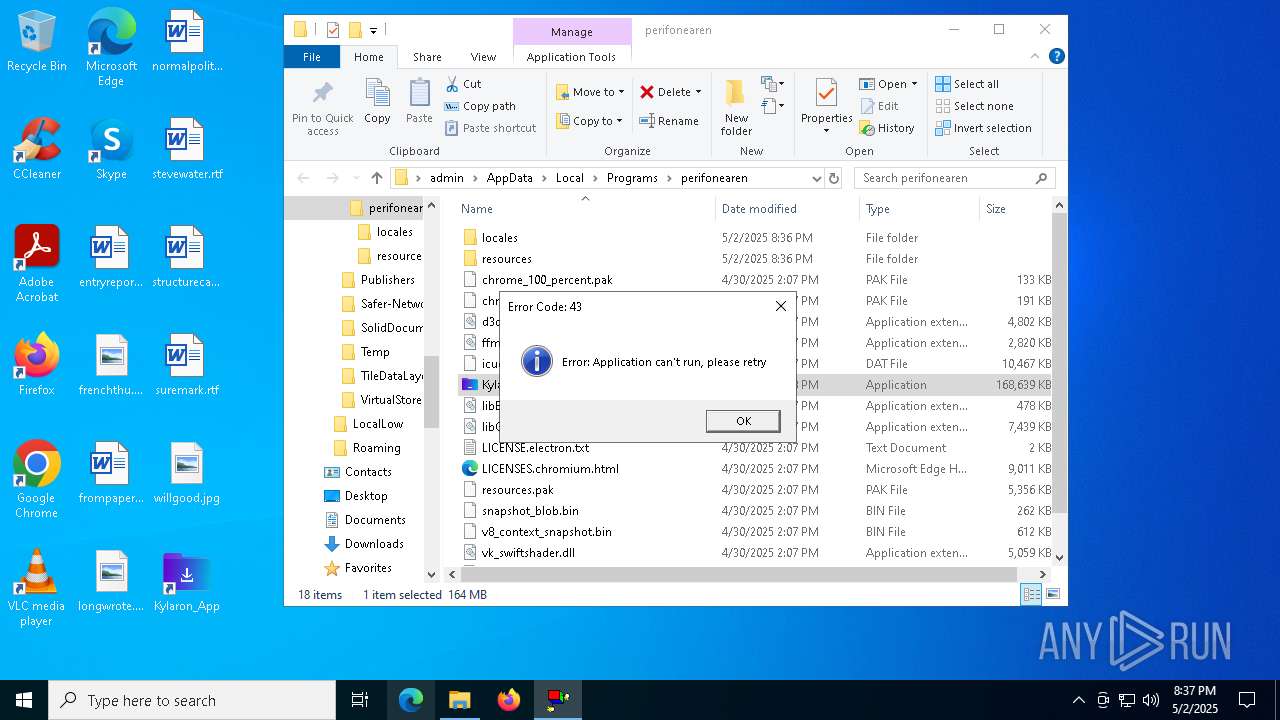
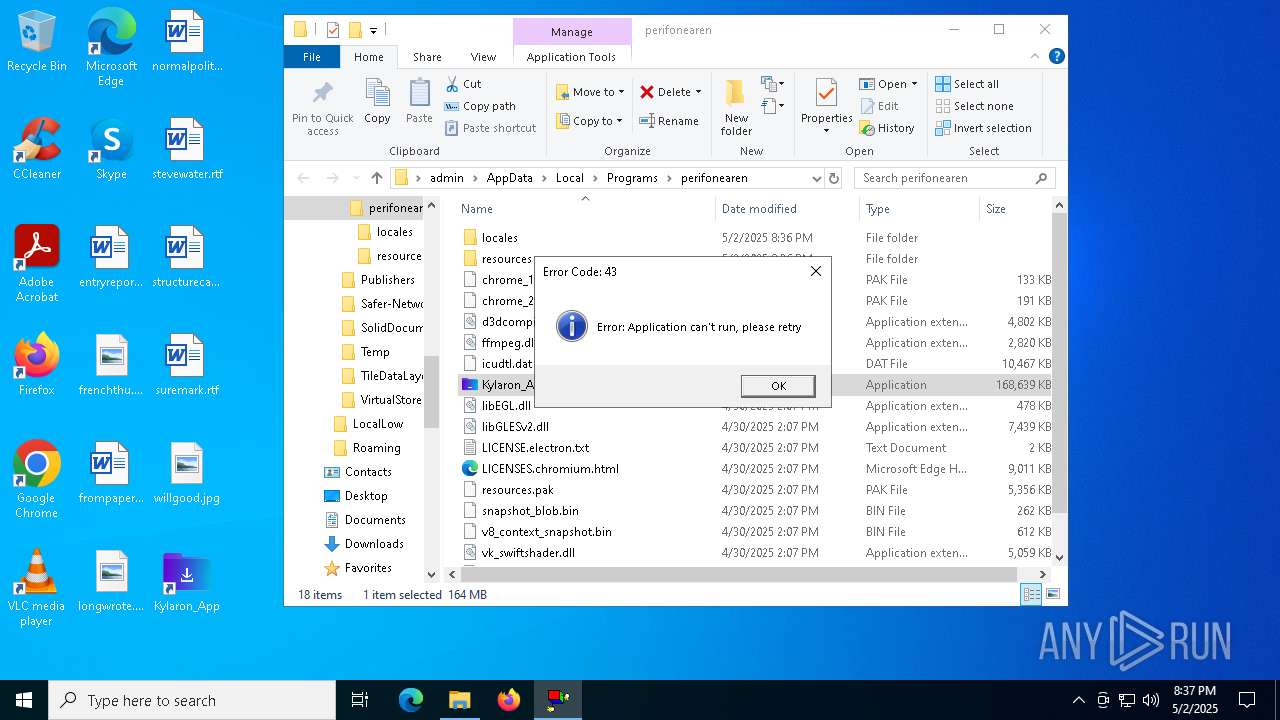
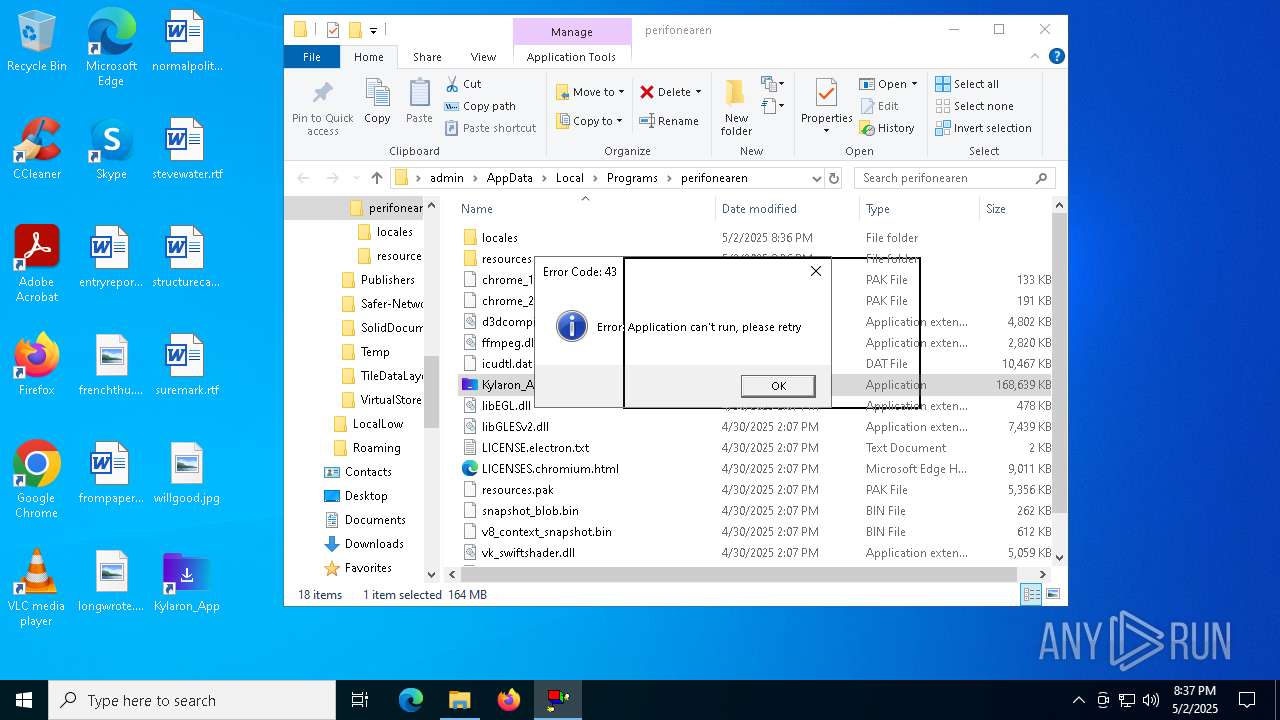
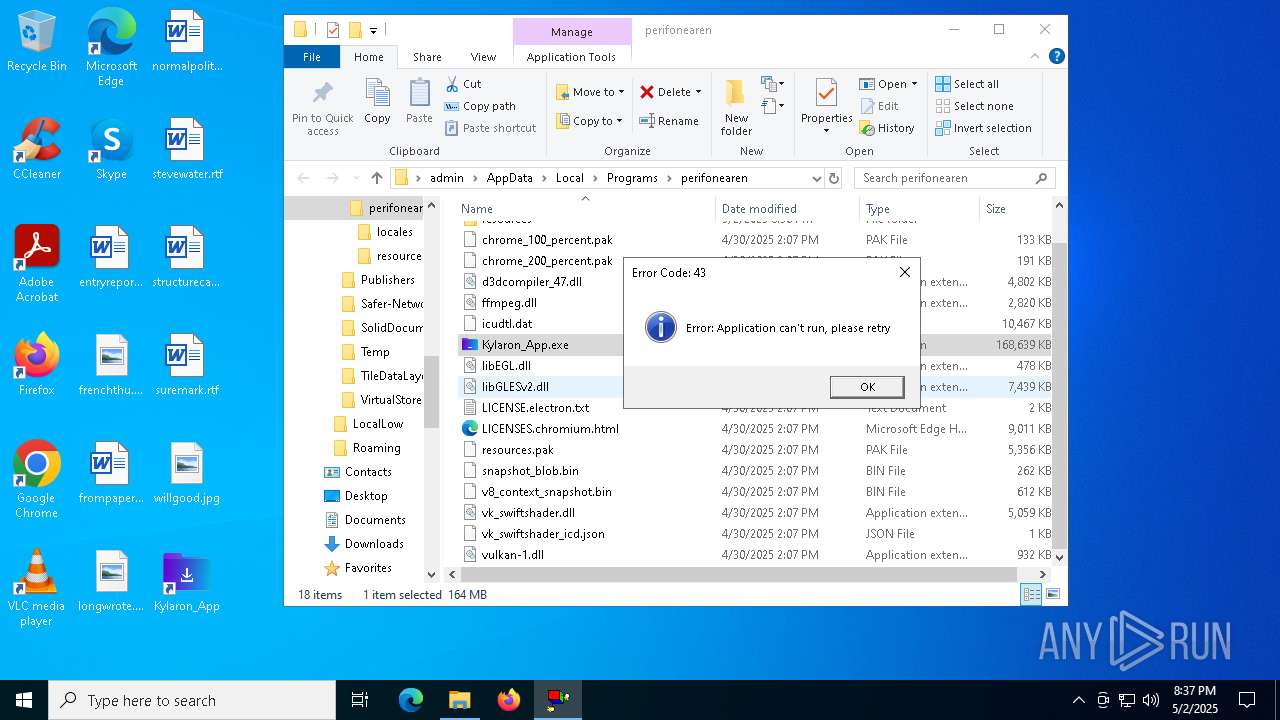
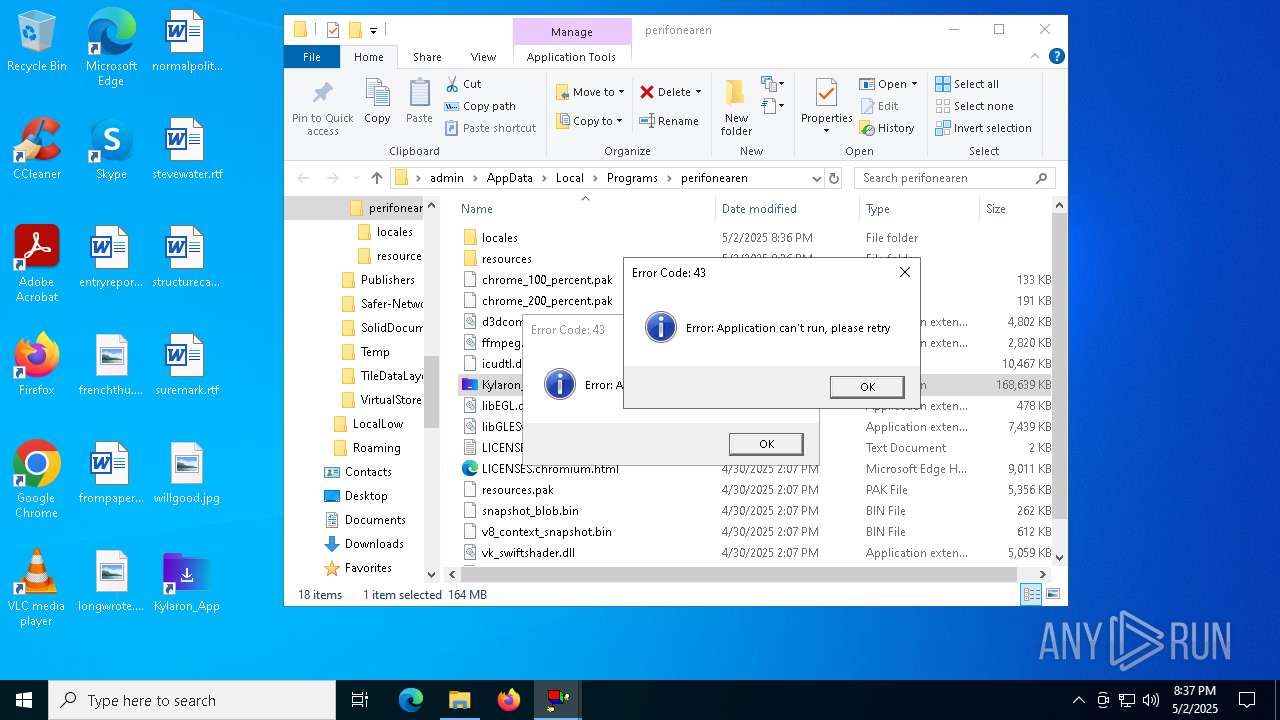
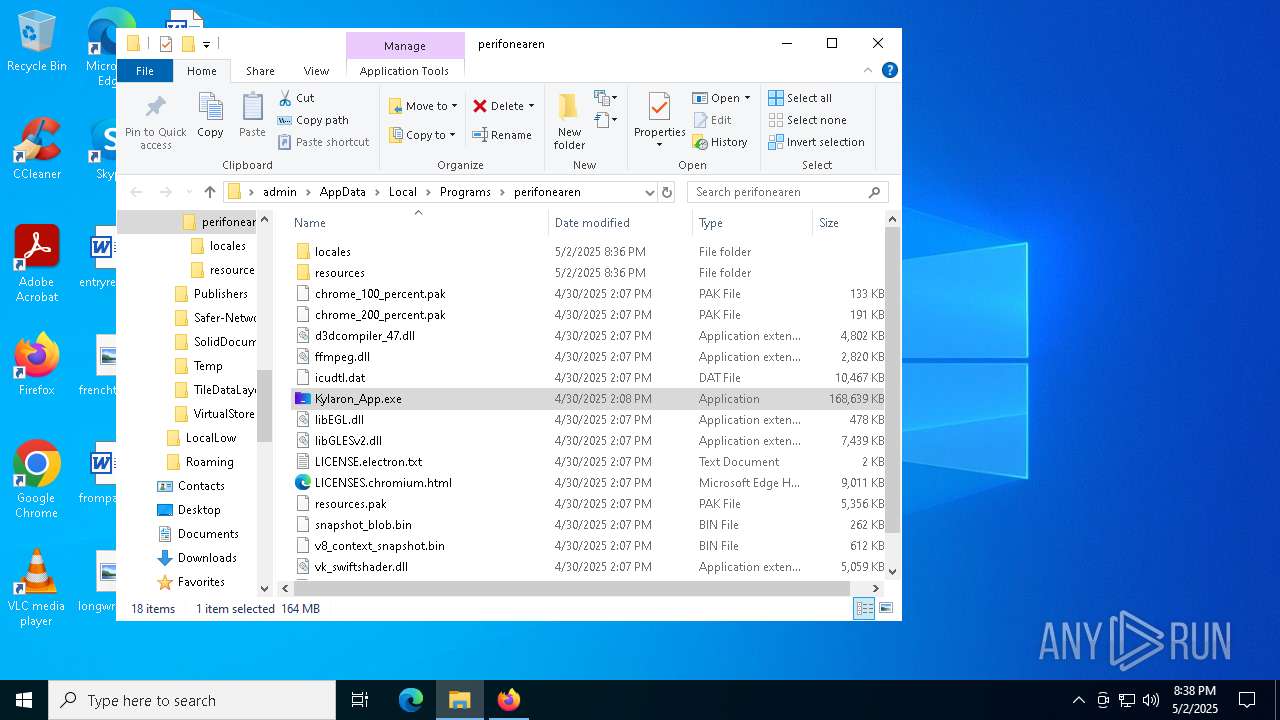
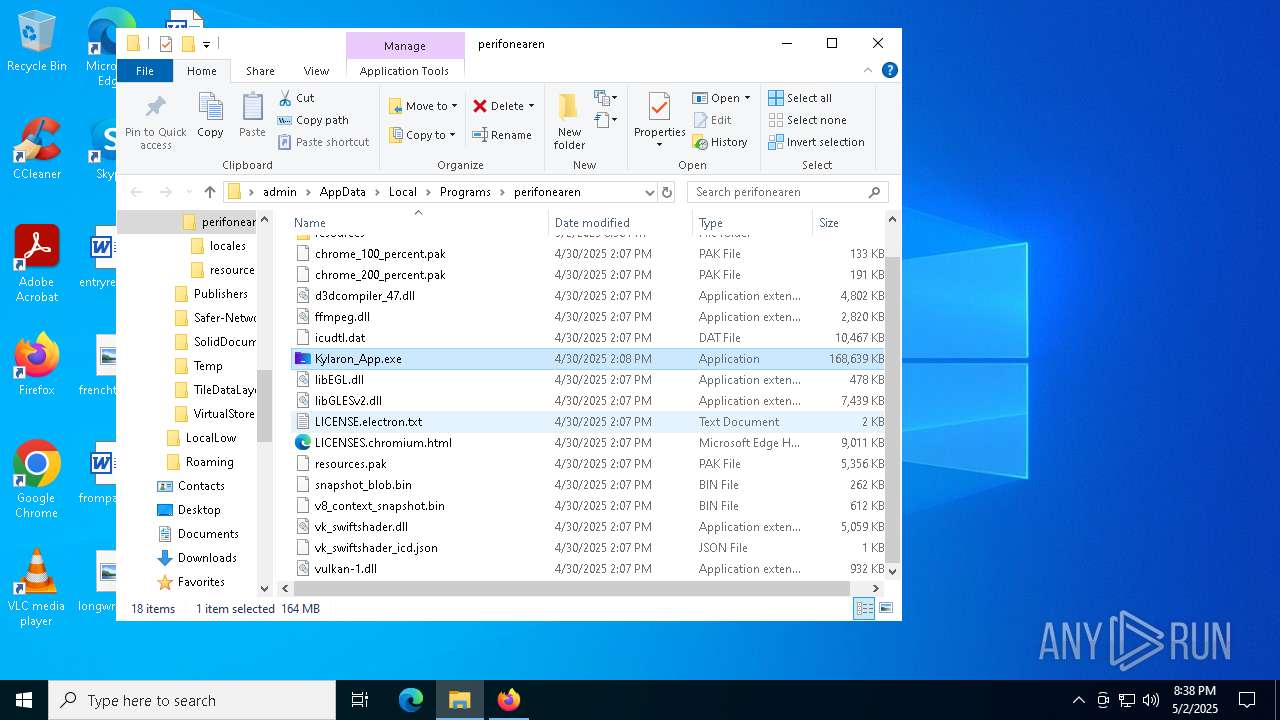
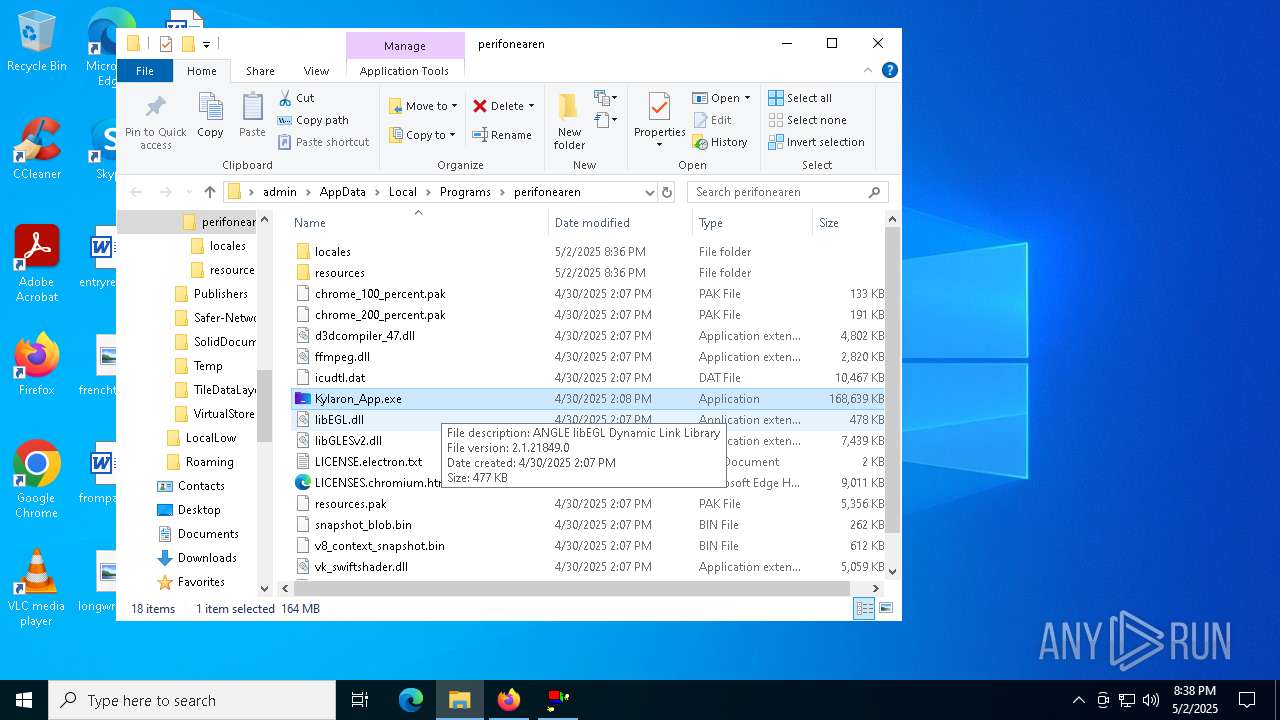
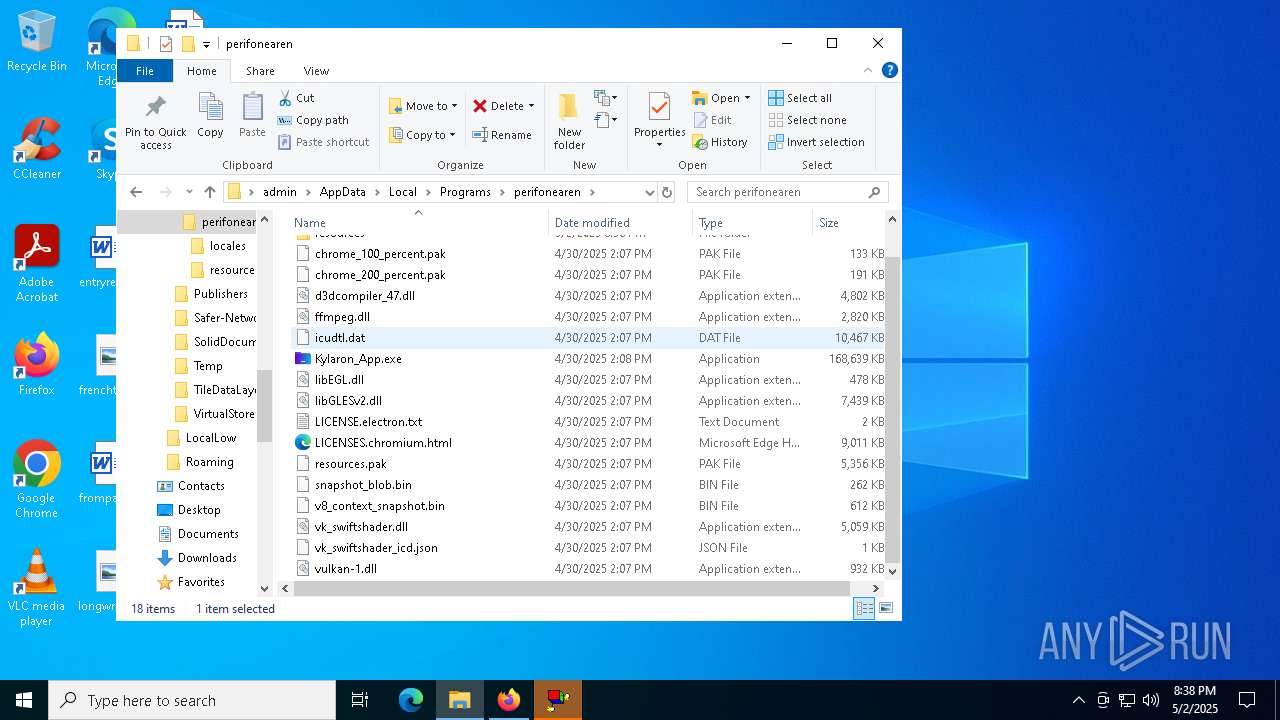
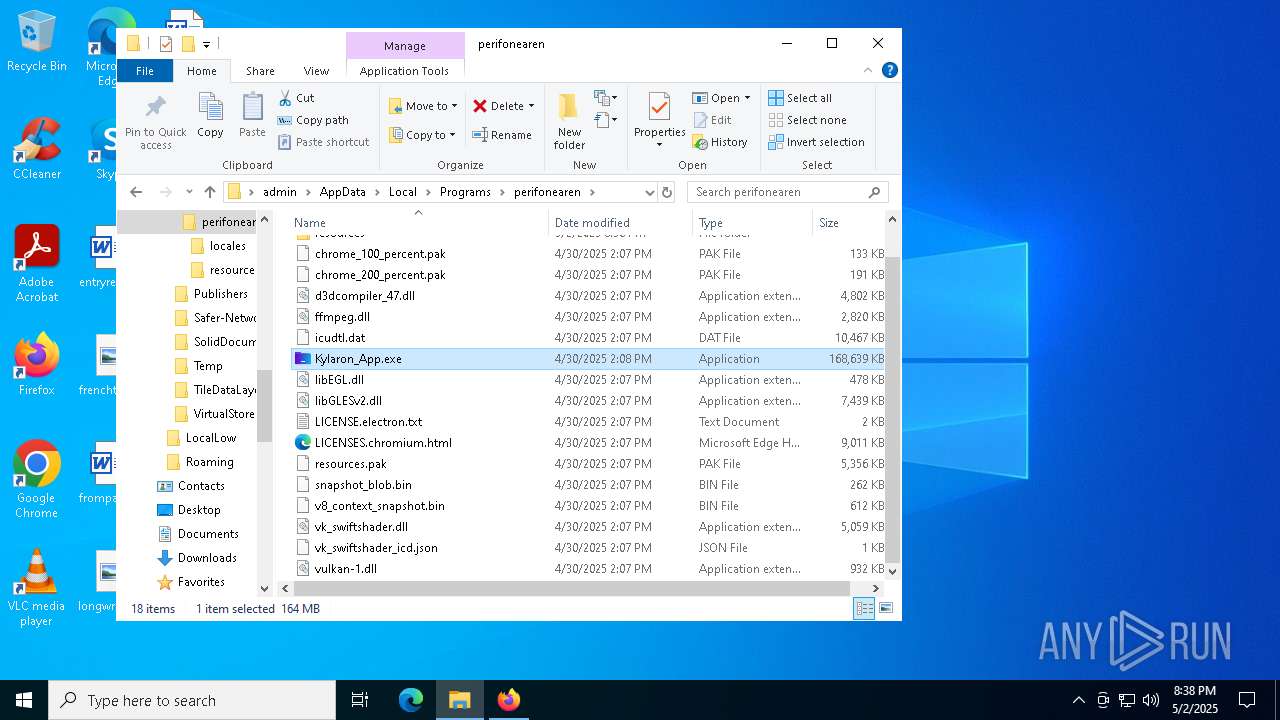
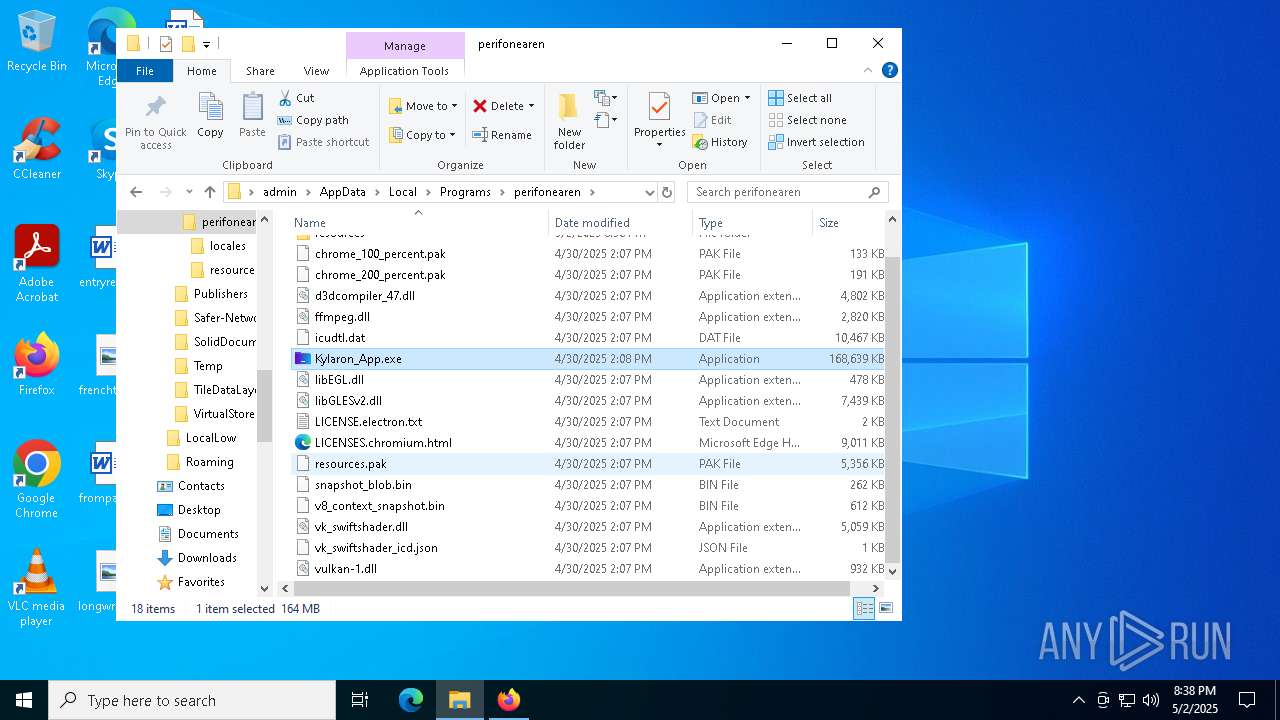
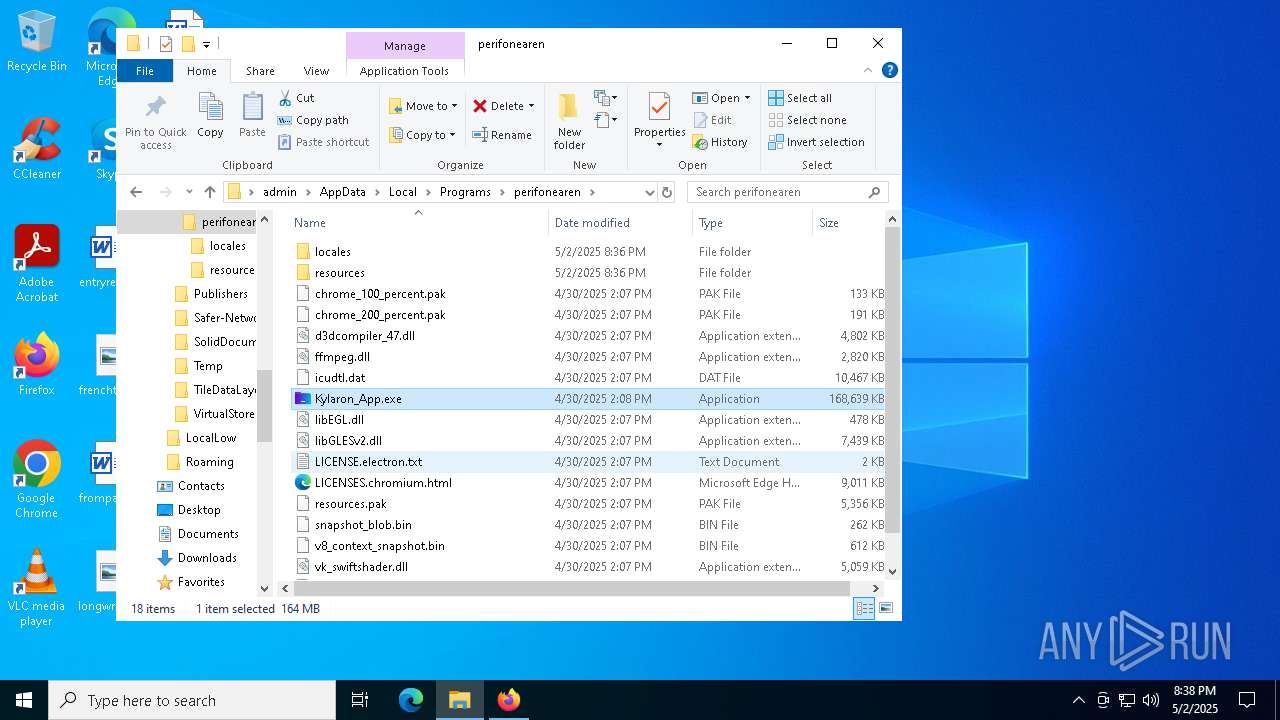
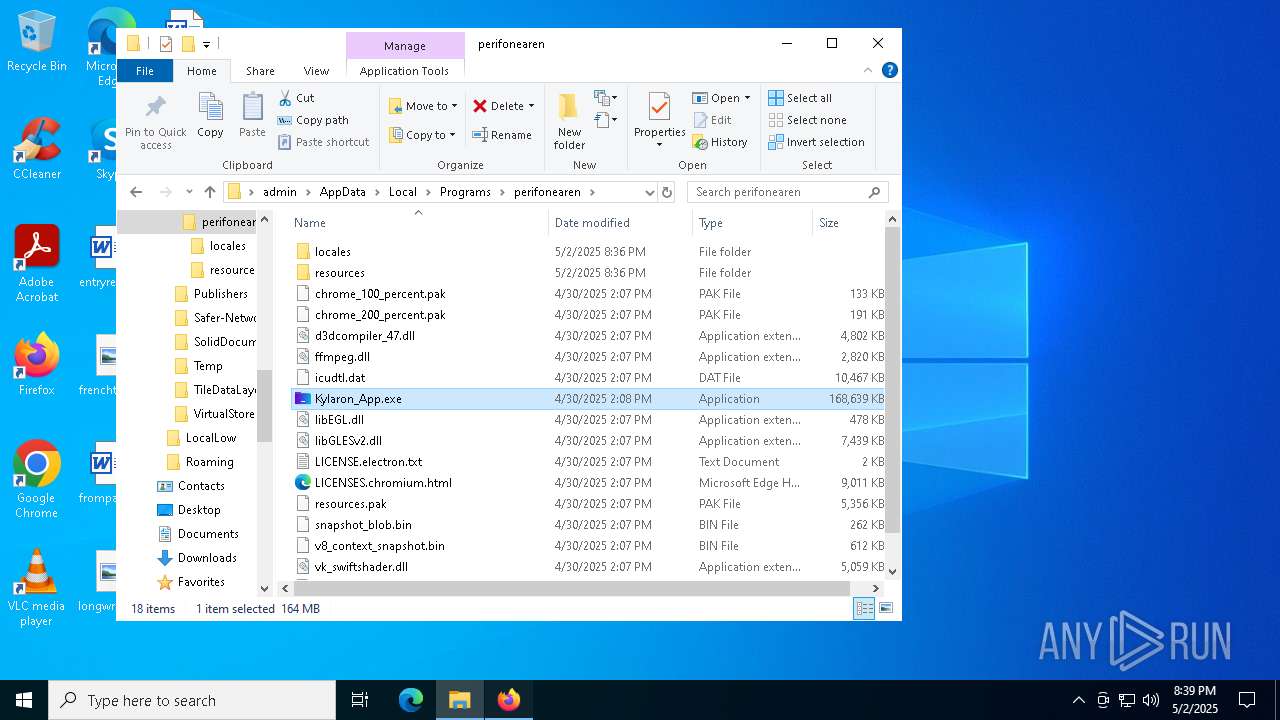
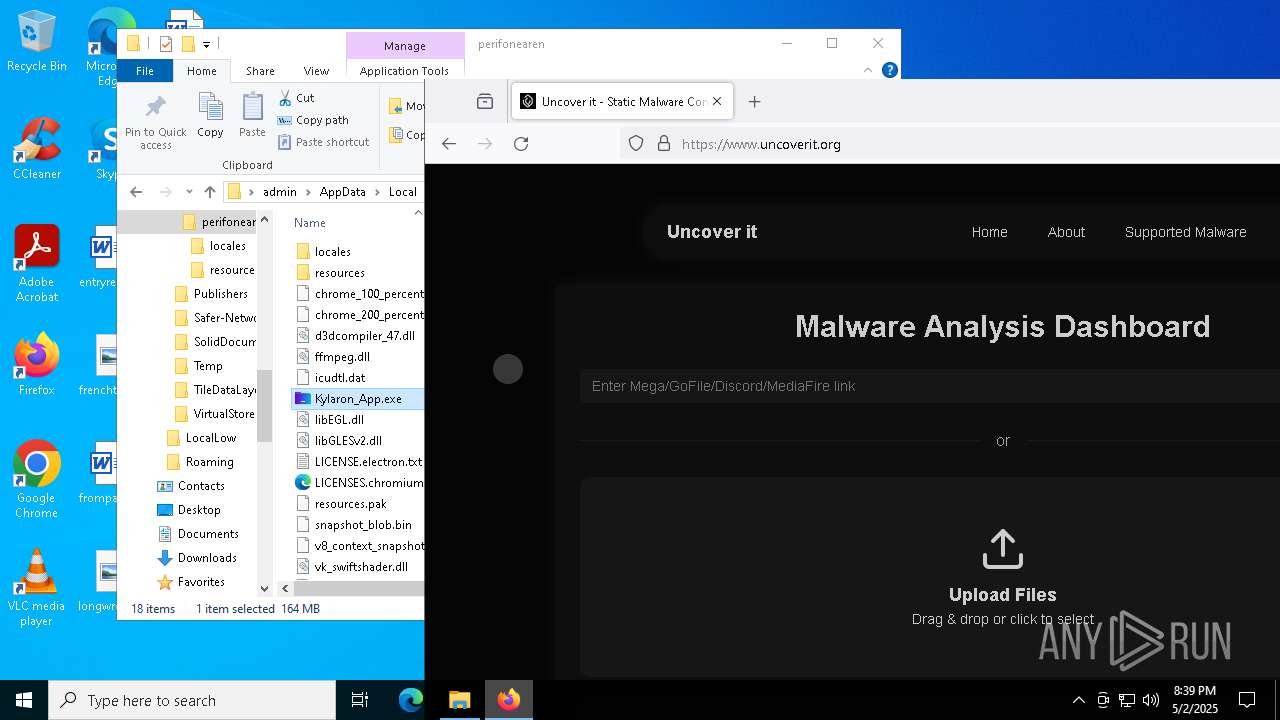
Application launched itself
- Kylaron_App.exe (PID: 660)
- Kylaron_App.exe (PID: 616)
- Kylaron_App.exe (PID: 5260)
- cmd.exe (PID: 9948)
- Kylaron_App.exe (PID: 968)
Get information on the list of running processes
- cmd.exe (PID: 5796)
- Kylaron_App.exe (PID: 660)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 7656)
- Kylaron_App.exe (PID: 616)
- Kylaron_App.exe (PID: 5260)
- cmd.exe (PID: 7440)
- Kylaron_App.exe (PID: 968)
- cmd.exe (PID: 1616)
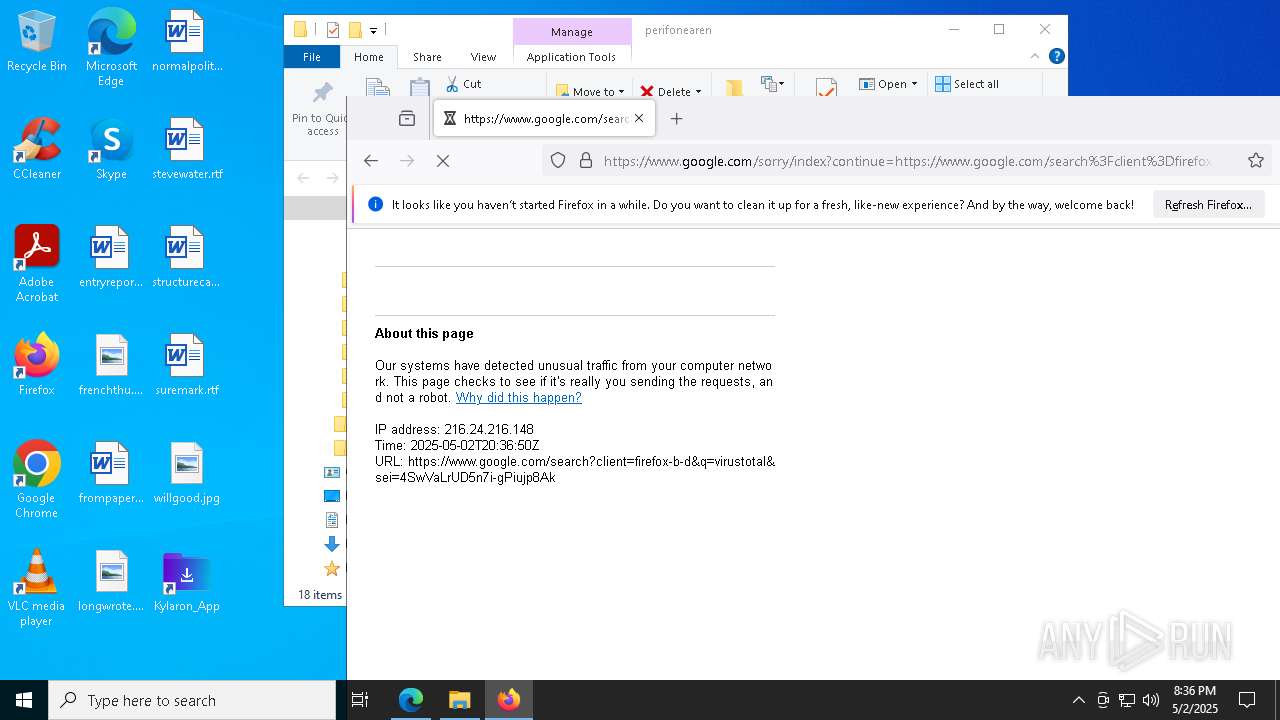
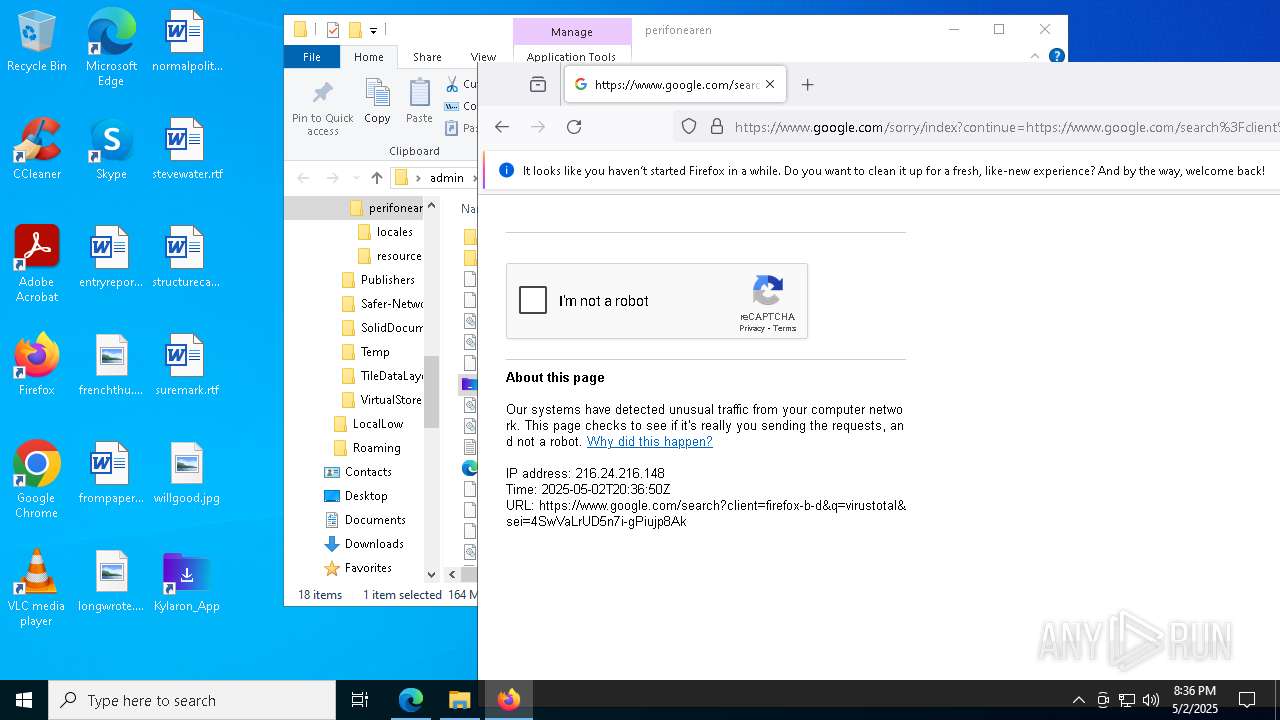
Checks for external IP
- svchost.exe (PID: 2196)
- Kylaron_App.exe (PID: 660)
- Kylaron_App.exe (PID: 616)
- Kylaron_App.exe (PID: 5260)
- Kylaron_App.exe (PID: 968)
Starts CMD.EXE for commands execution
- Kylaron_App.exe (PID: 660)
- Kylaron_App.exe (PID: 616)
- Kylaron_App.exe (PID: 5260)
- cmd.exe (PID: 9948)
- Kylaron_App.exe (PID: 968)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4152)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 9728)
- cmd.exe (PID: 9296)
- cmd.exe (PID: 10076)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 9804)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 9780)
- cmd.exe (PID: 10204)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 8200)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 5232)
- cmd.exe (PID: 9332)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 9724)
- cmd.exe (PID: 7436)
- cmd.exe (PID: 9948)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 9736)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 132)
- cmd.exe (PID: 9312)
- cmd.exe (PID: 9772)
- cmd.exe (PID: 8232)
- cmd.exe (PID: 680)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 2192)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 8008)
Starts process via Powershell
- powershell.exe (PID: 10076)
- powershell.exe (PID: 7620)
Uses TASKKILL.EXE to kill process
- Kylaron_App.exe (PID: 660)
- cmd.exe (PID: 9948)
The process executes Powershell scripts
- cmd.exe (PID: 10024)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 10024)
- cmd.exe (PID: 9948)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 10048)
The process executes VB scripts
- cmd.exe (PID: 9320)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 7440)
Uses WMIC.EXE to obtain operating system information
- Kylaron_App.exe (PID: 660)
Executing commands from a ".bat" file
- Kylaron_App.exe (PID: 660)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 9948)
The process hide an interactive prompt from the user
- cmd.exe (PID: 9948)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 9948)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Kylaron_App.exe (PID: 660)
Starts SC.EXE for service management
- cmd.exe (PID: 9696)
Creates a new Windows service
- sc.exe (PID: 8752)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 9948)
- cmd.exe (PID: 9156)
Hides command output
- cmd.exe (PID: 9156)
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 9948)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 9948)
INFO
Checks supported languages
- identity_helper.exe (PID: 1280)
- identity_helper.exe (PID: 6940)
- msiexec.exe (PID: 8596)
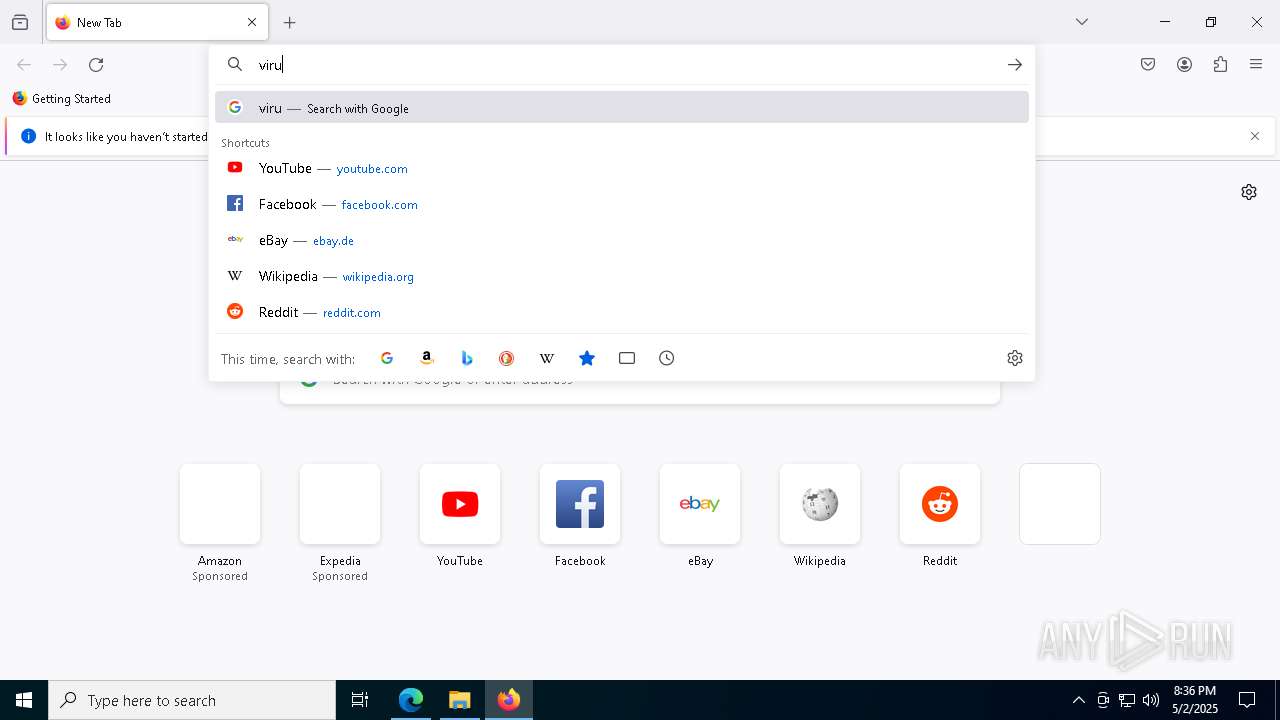
Application launched itself
- msedge.exe (PID: 5072)
- firefox.exe (PID: 2776)
- firefox.exe (PID: 5776)
- chrome.exe (PID: 8604)
- msedge.exe (PID: 6252)
- firefox.exe (PID: 7380)
- firefox.exe (PID: 9316)
Reads Environment values
- identity_helper.exe (PID: 1280)
- identity_helper.exe (PID: 6940)
Reads the computer name
- identity_helper.exe (PID: 1280)
- identity_helper.exe (PID: 6940)
- msiexec.exe (PID: 8596)
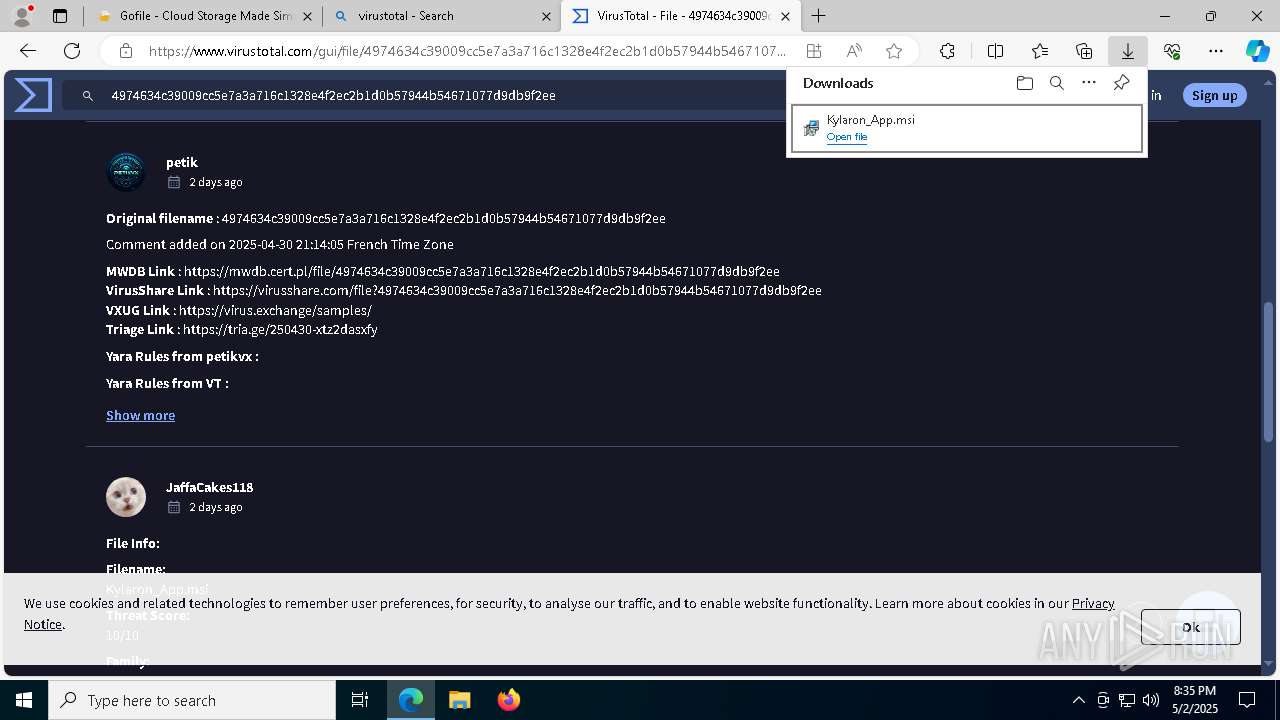
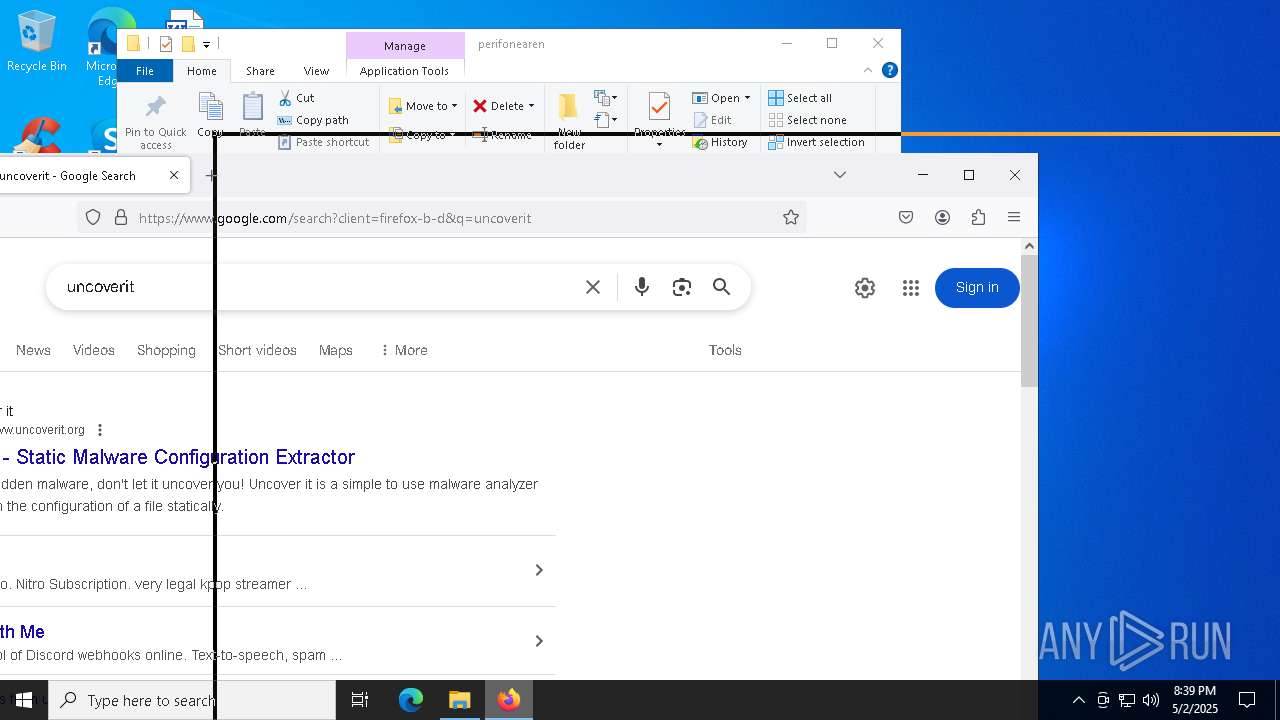
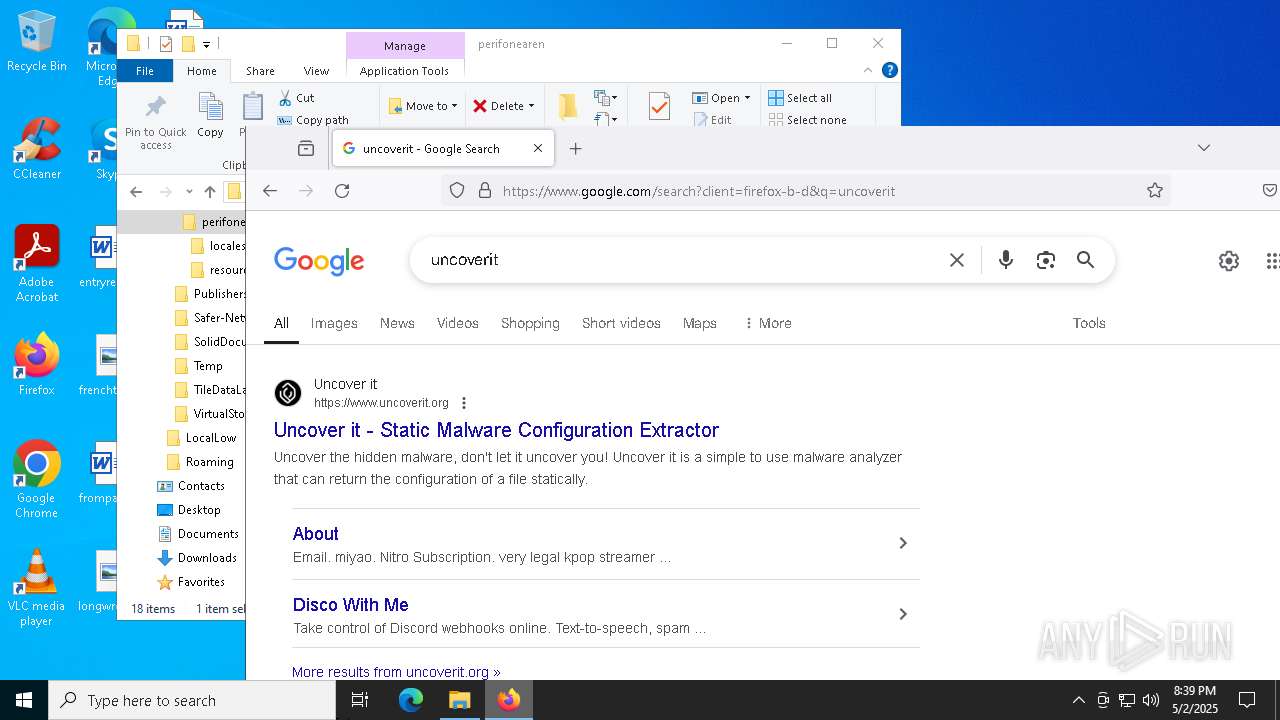
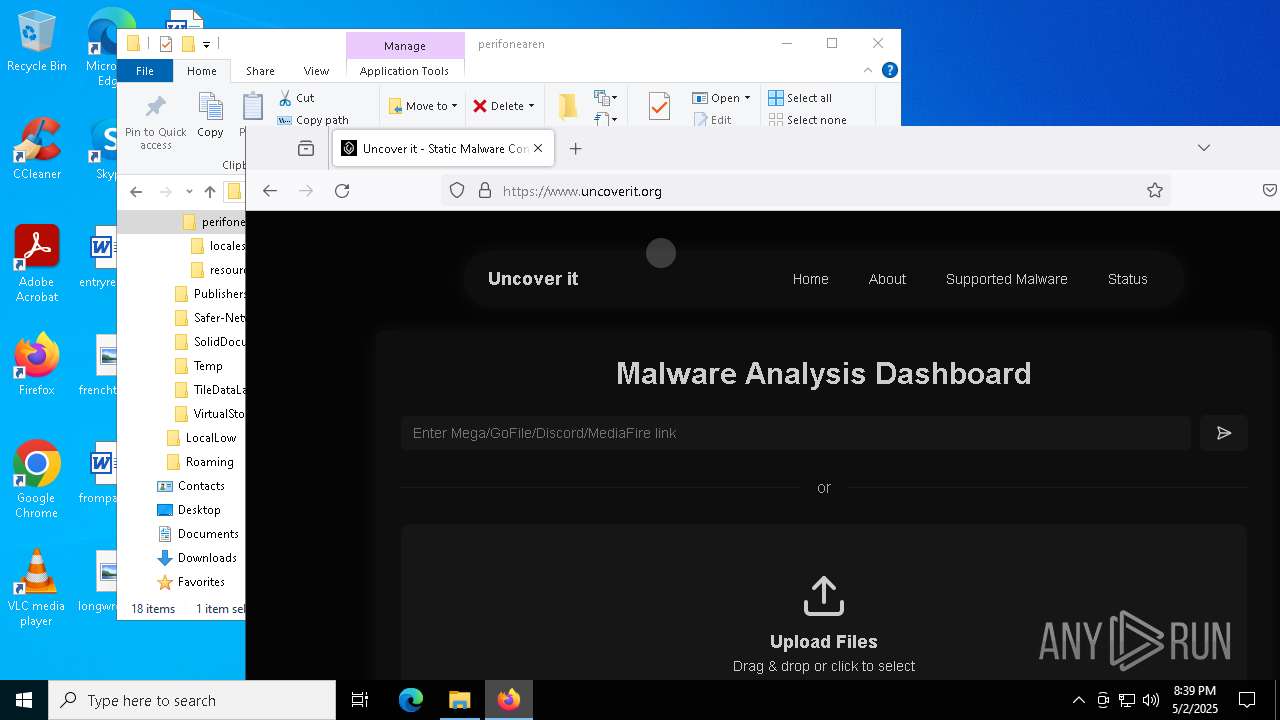
Attempting to use file storage service
- msedge.exe (PID: 7248)
Reads the software policy settings
- slui.exe (PID: 8100)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5072)
The sample compiled with english language support
- msiexec.exe (PID: 8596)
Manages system restore points
- SrTasks.exe (PID: 1056)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8596)
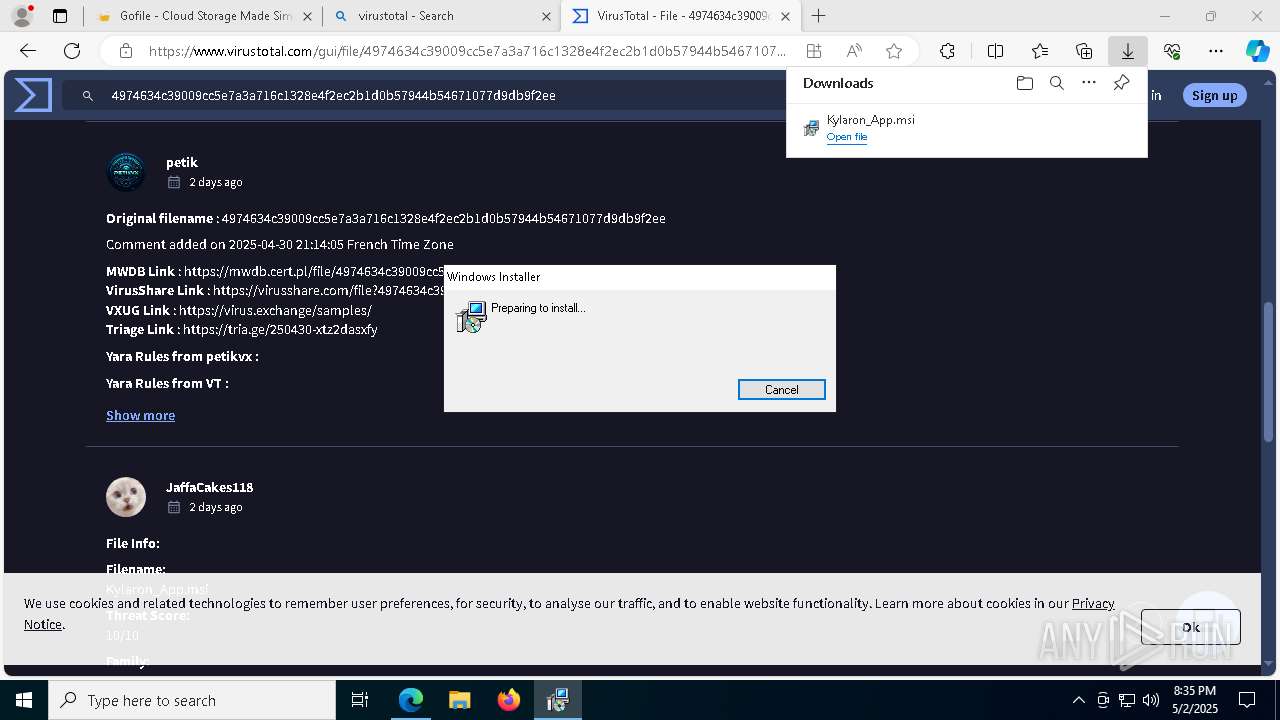
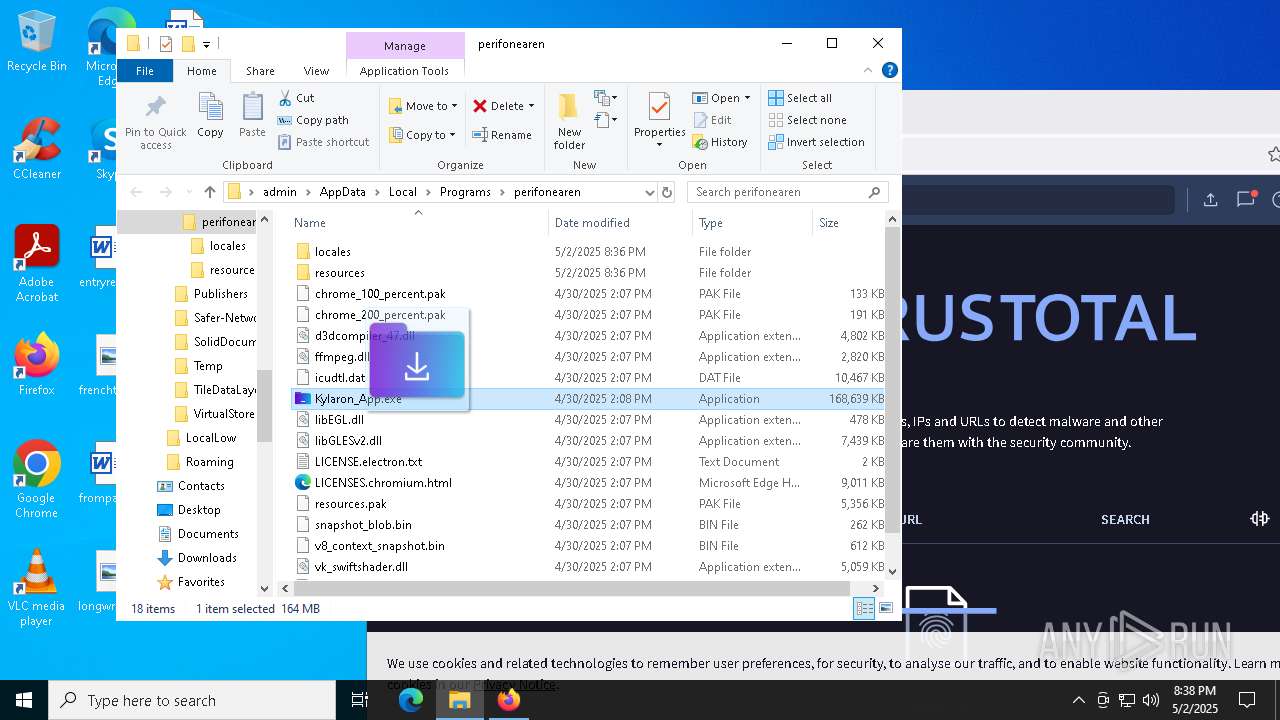
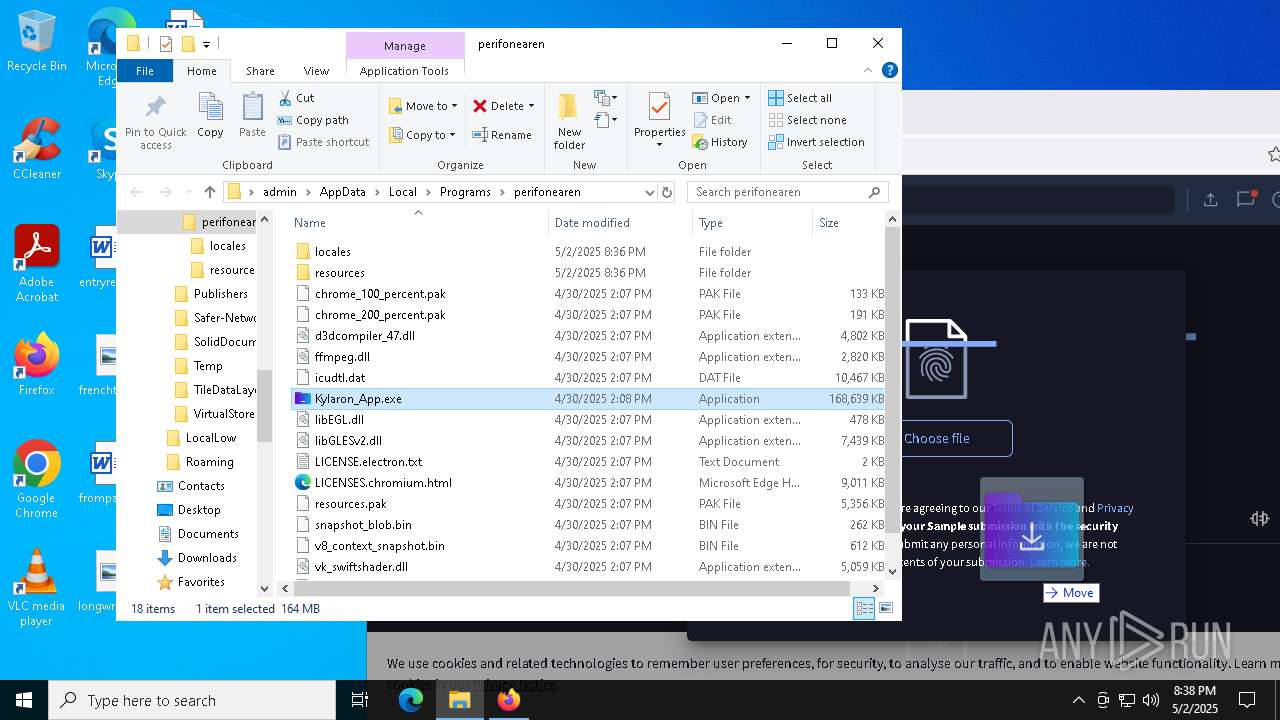
Manual execution by a user
- firefox.exe (PID: 5776)
- Kylaron_App.exe (PID: 5260)
- firefox.exe (PID: 7380)
The Powershell gets current clipboard
- powershell.exe (PID: 9824)
The executable file from the user directory is run by the Powershell process
- Kylaron_App.exe (PID: 616)
- Kylaron_App.exe (PID: 968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
629
Monitored processes
482
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | reg add "HKLM\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableBlockOnUnproven" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell -Command "Get-CimInstance Win32_PhysicalMemory | Select Capacity,Speed,Manufacturer,MemoryType,PartNumber,SerialNumber | ConvertTo-Json -Depth 2"" | C:\Windows\System32\cmd.exe | — | Kylaron_App.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | reg add "HKLM\SYSTEM\ControlSet001\Services\WdFilter" /v "Start" /t REG_DWORD /d "4" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | powershell -Command "Get-CimInstance Win32_OperatingSystem | Select-Object -ExpandProperty Caption | ConvertTo-Json -Depth 2" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | powershell -Command "Get-CimInstance Win32_PhysicalMemory | Select Capacity,Speed,Manufacturer,MemoryType,PartNumber,SerialNumber | ConvertTo-Json -Depth 2" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
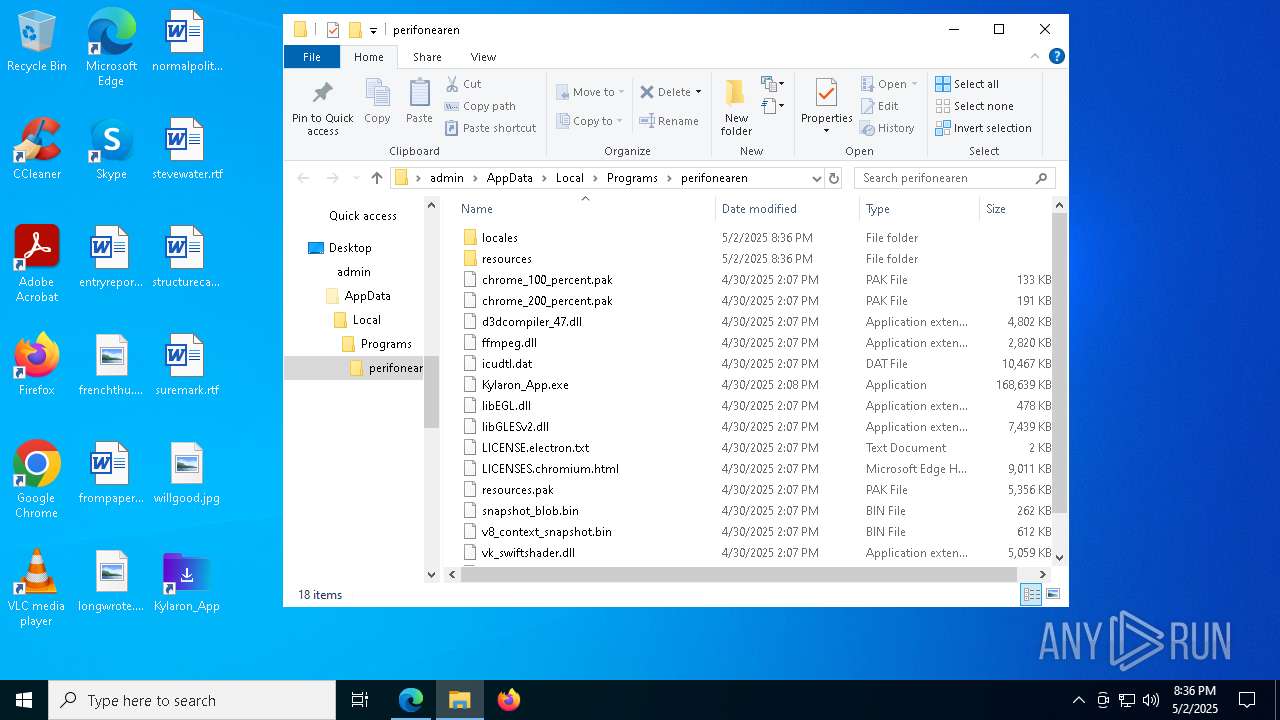
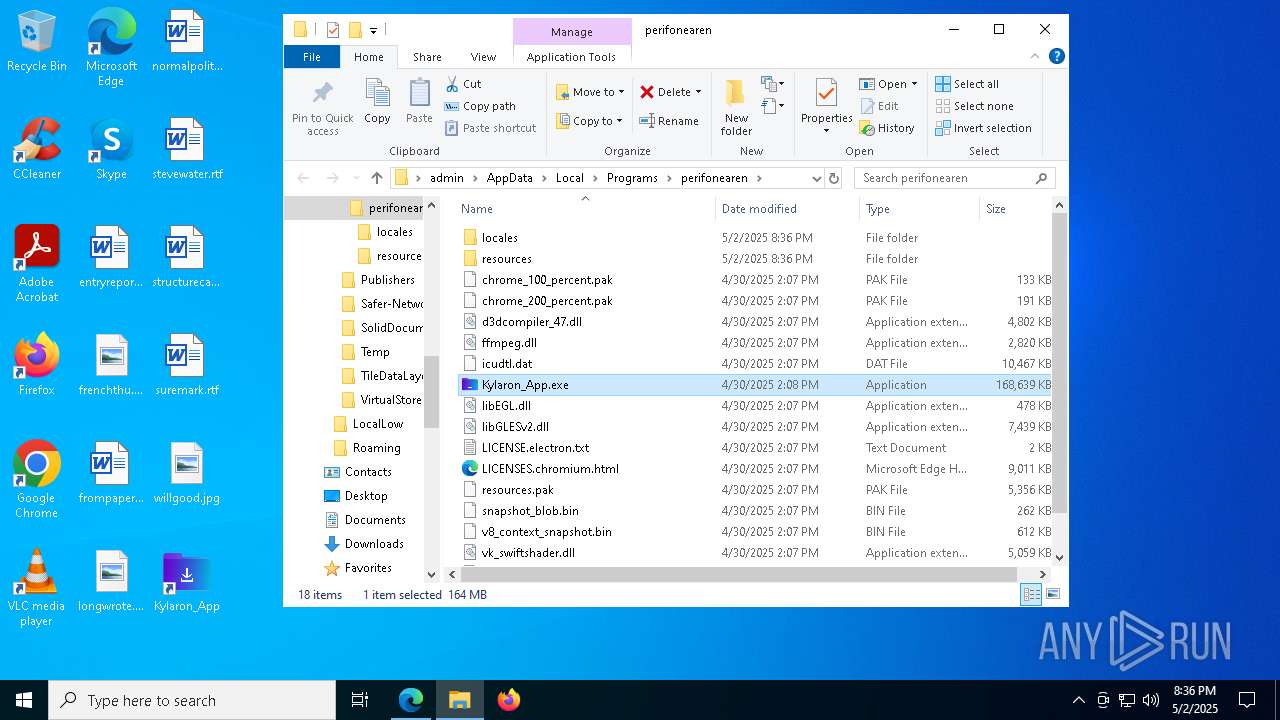
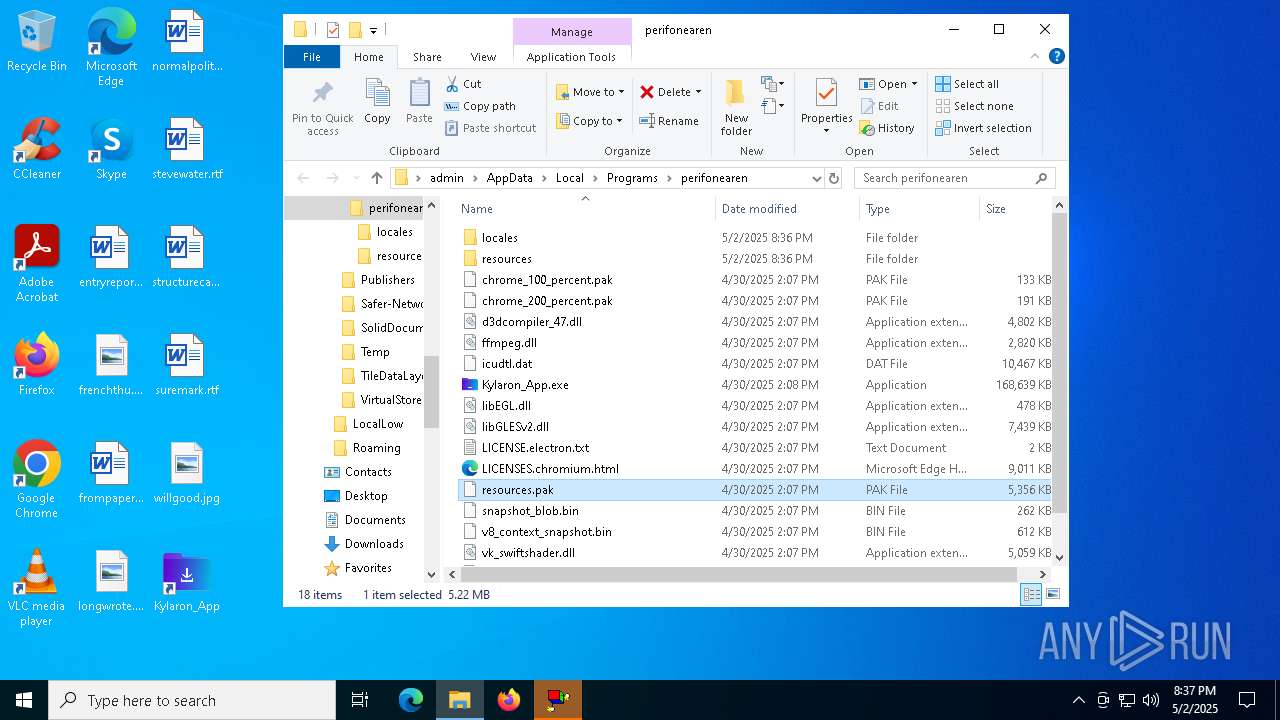
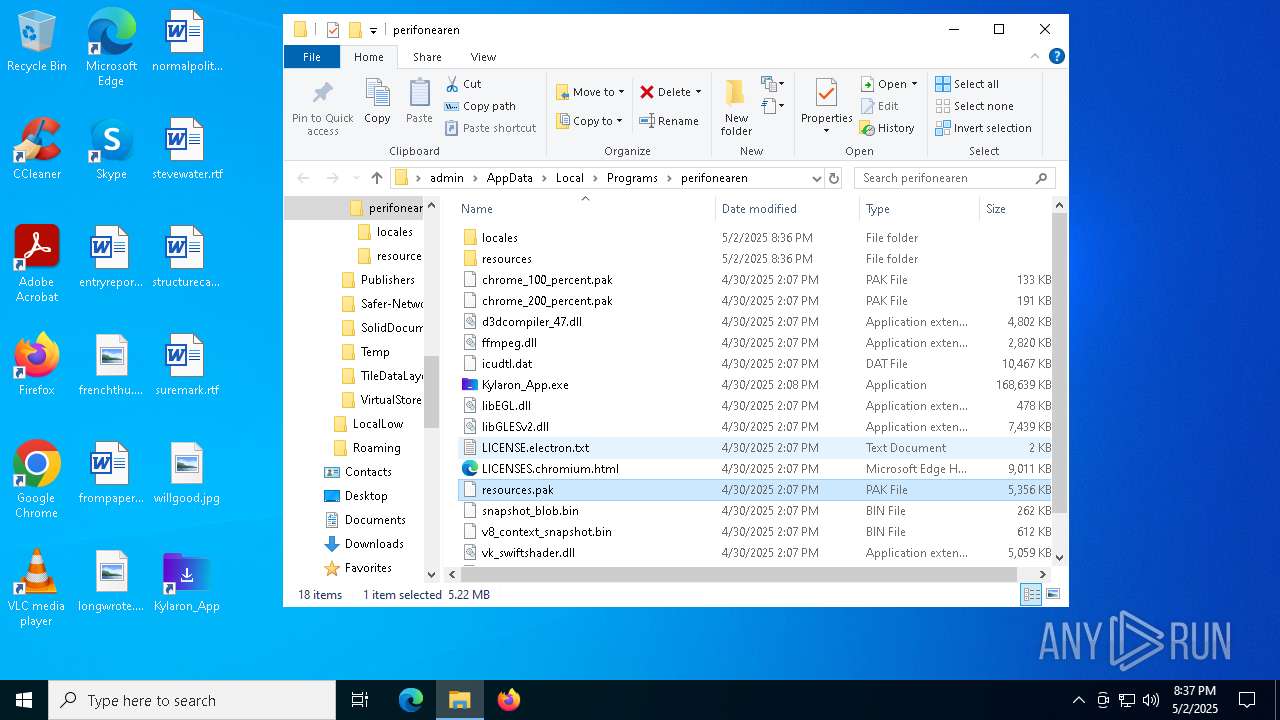
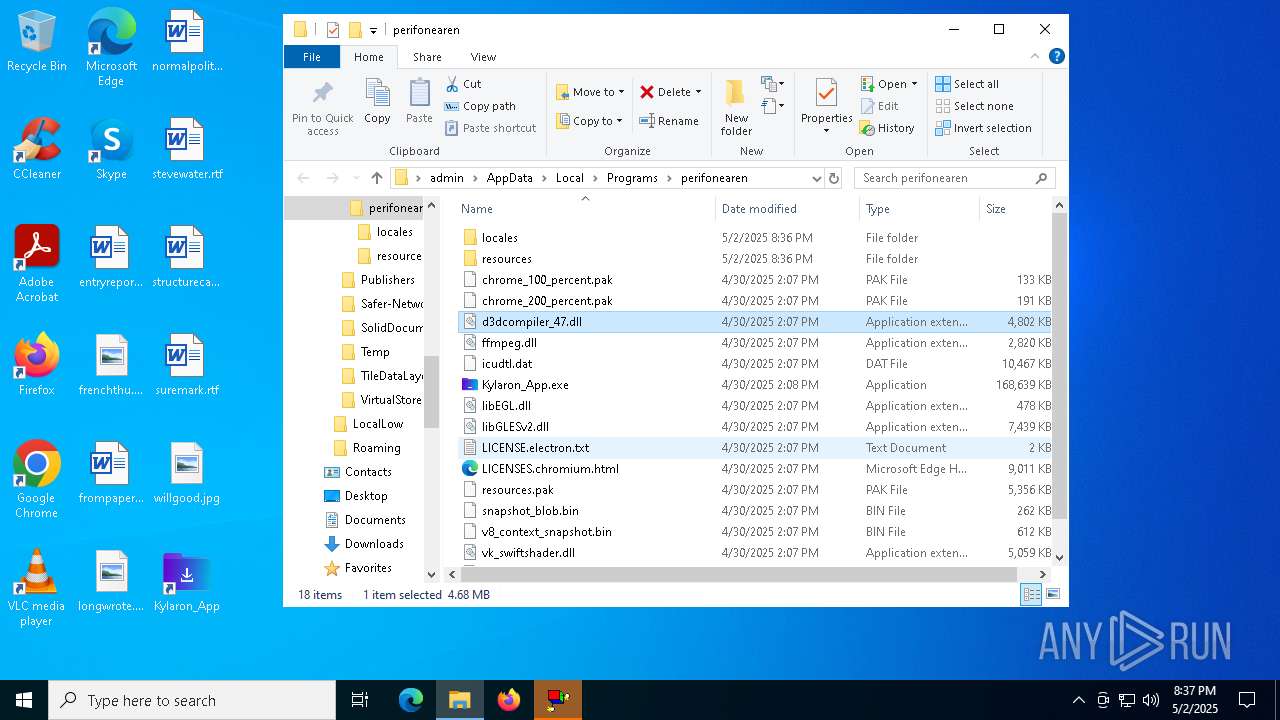
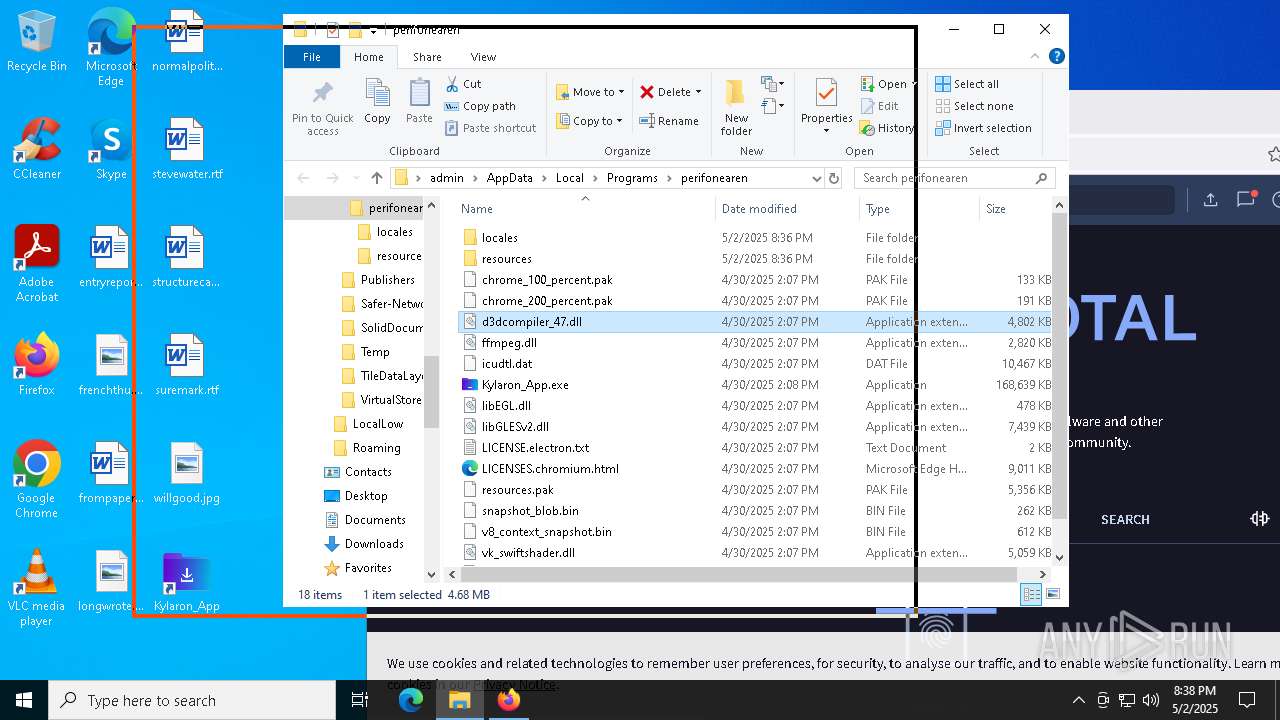
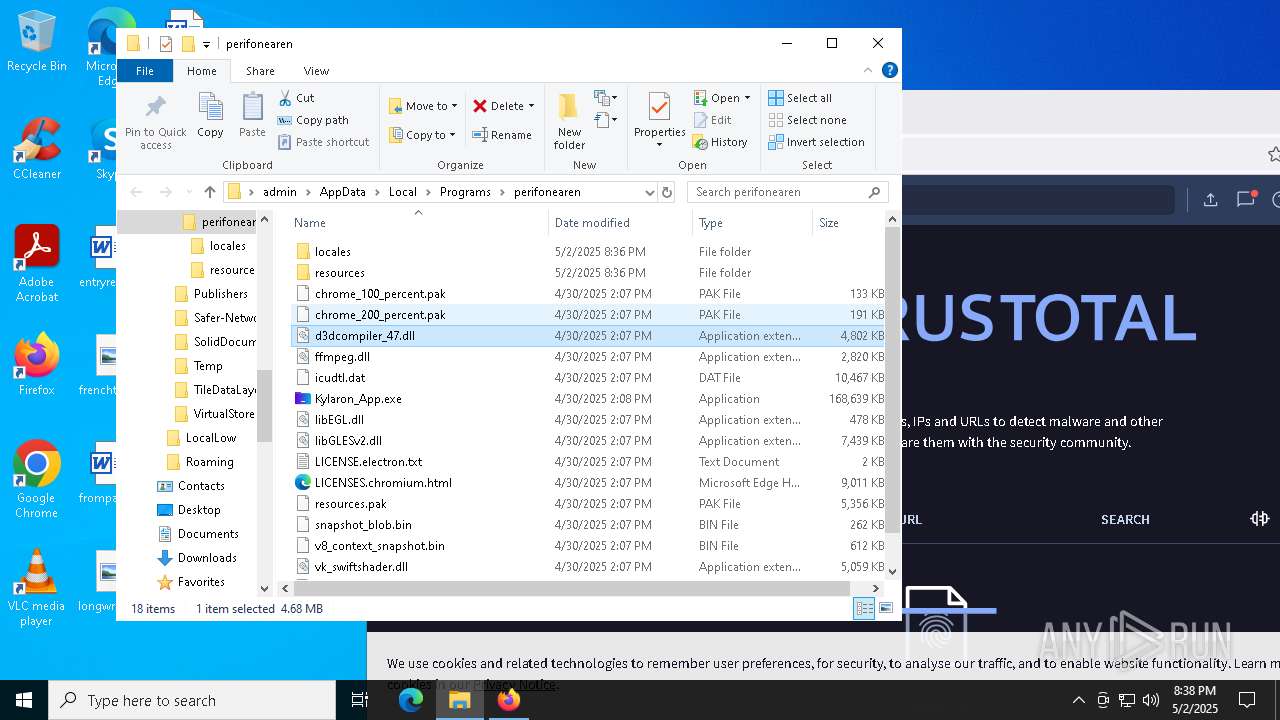
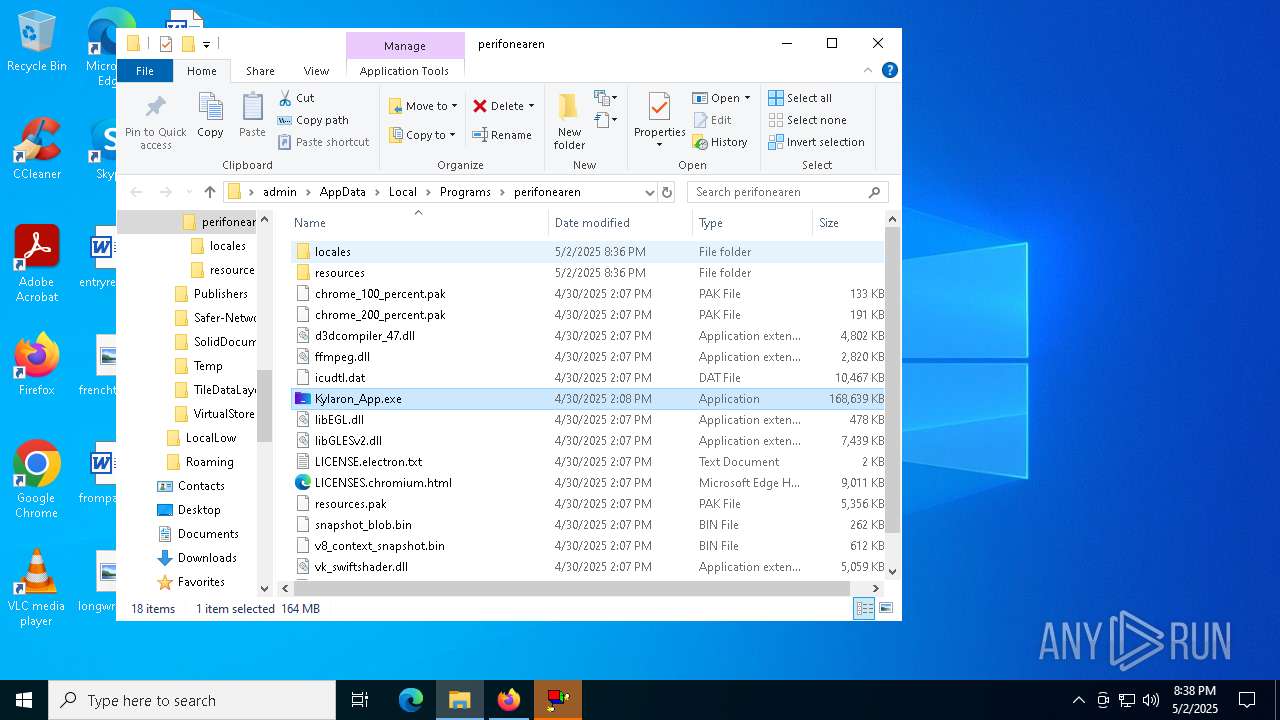
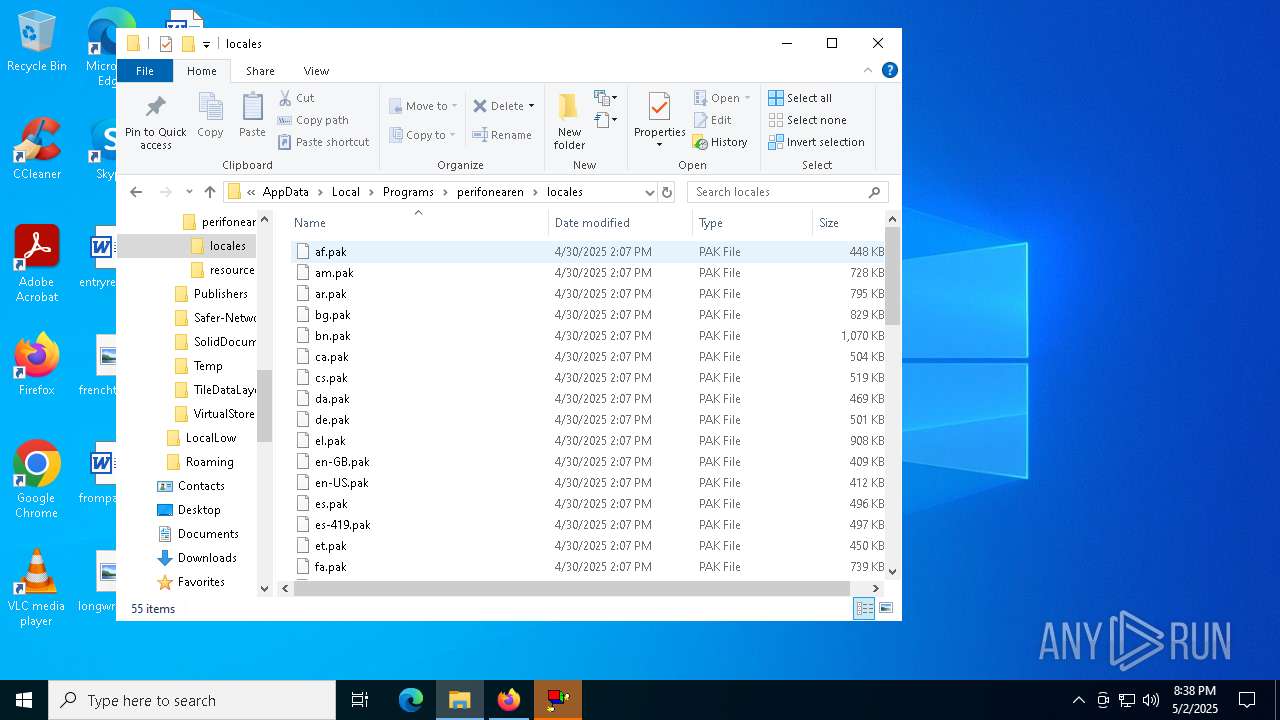
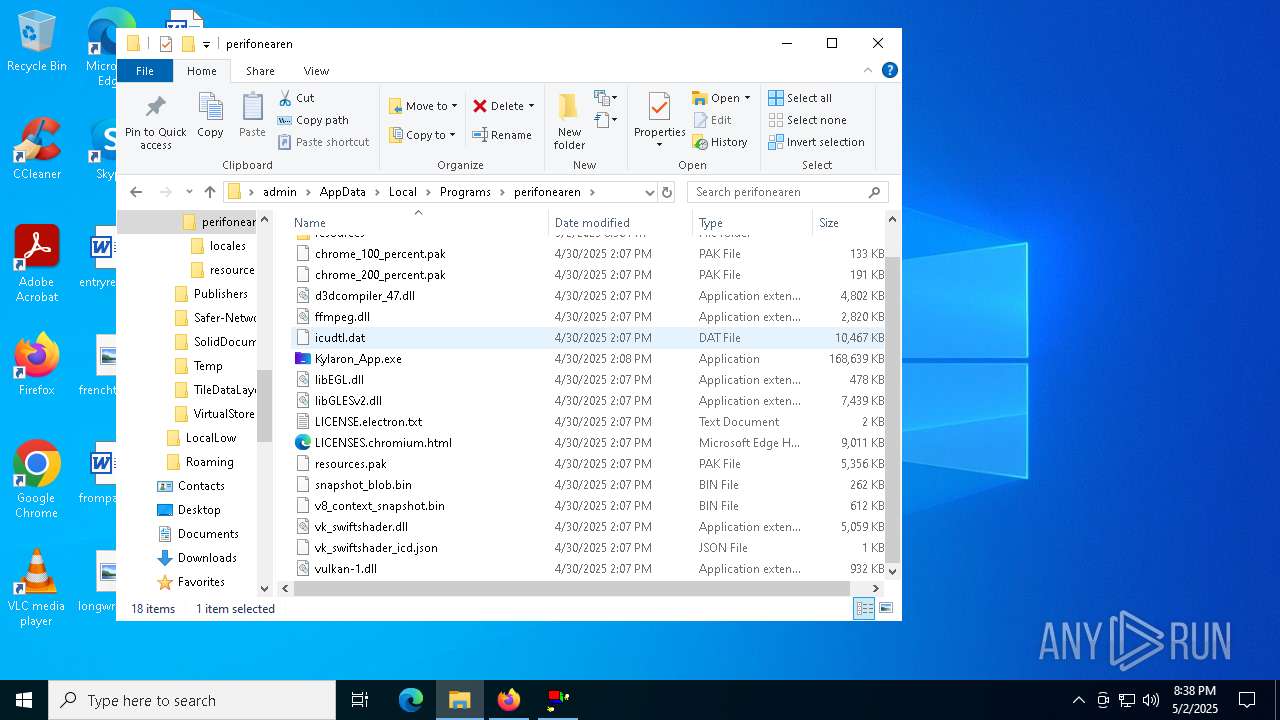
| 616 | "C:\Users\admin\AppData\Local\Programs\perifonearen\Kylaron_App.exe" C:\Users\admin\AppData\Local\Programs\perifonearen\Kylaron_App.exe --admin | C:\Users\admin\AppData\Local\Programs\perifonearen\Kylaron_App.exe | powershell.exe | ||||||||||||
User: admin Company: Kylaron Integrity Level: HIGH Description: Kylaron_App Exit code: 1 Version: 23.4.8 Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Users\admin\AppData\Local\Programs\perifonearen\Kylaron_App.exe" | C:\Users\admin\AppData\Local\Programs\perifonearen\Kylaron_App.exe | msiexec.exe | ||||||||||||
User: admin Company: Kylaron Integrity Level: MEDIUM Description: Kylaron_App Version: 23.4.8 Modules
| |||||||||||||||
| 680 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell -Command "Get-CimInstance Win32_OperatingSystem | Select-Object -ExpandProperty Caption | ConvertTo-Json -Depth 2"" | C:\Windows\System32\cmd.exe | — | Kylaron_App.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2176 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2140 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {453fd453-0d5f-4287-bd22-e1108607cb87} 2776 "\\.\pipe\gecko-crash-server-pipe.2776" 12cf6082b10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
Total events
228 852
Read events
228 423
Write events
411
Delete events
18
Modification events
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 04C9015DC3922F00 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DDEE0D5DC3922F00 | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\983786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9FBD673A-47F7-4E0A-93F2-CFE809AE6206} | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\983786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8D5DE748-8A5D-490F-A3F5-C77E0E4FEDFA} | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\983786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B6CF9B9C-A4F9-40EA-93FD-B9D0E819690C} | |||
| (PID) Process: | (5072) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\983786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1AAA0451-8D3E-4BD6-9975-8790F83DA98E} | |||
Executable files
65
Suspicious files
1 285
Text files
291
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10be41.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10be41.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10be50.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10be41.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10be8f.TMP | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
93
TCP/UDP connections
494
DNS requests
478
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8288 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8288 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8980 | svchost.exe | HEAD | 200 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746653427&P2=404&P3=2&P4=hNVQqLmuNmcAvPa5jnHMninjjgrVvNXiebjr4Vp91wo8WSFup9RBoElTRo5LVHKDMTz%2bI%2boZ8B9fMHj3jTkyWQ%3d%3d | unknown | — | — | whitelisted |
8980 | svchost.exe | GET | 206 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746653427&P2=404&P3=2&P4=hNVQqLmuNmcAvPa5jnHMninjjgrVvNXiebjr4Vp91wo8WSFup9RBoElTRo5LVHKDMTz%2bI%2boZ8B9fMHj3jTkyWQ%3d%3d | unknown | — | — | whitelisted |
8980 | svchost.exe | GET | 206 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746653427&P2=404&P3=2&P4=hNVQqLmuNmcAvPa5jnHMninjjgrVvNXiebjr4Vp91wo8WSFup9RBoElTRo5LVHKDMTz%2bI%2boZ8B9fMHj3jTkyWQ%3d%3d | unknown | — | — | whitelisted |
8980 | svchost.exe | GET | 206 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746653427&P2=404&P3=2&P4=hNVQqLmuNmcAvPa5jnHMninjjgrVvNXiebjr4Vp91wo8WSFup9RBoElTRo5LVHKDMTz%2bI%2boZ8B9fMHj3jTkyWQ%3d%3d | unknown | — | — | whitelisted |
8980 | svchost.exe | HEAD | 200 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1746653427&P2=404&P3=2&P4=J7jBKGlo69M%2finy%2fYyniiiNr3rD5qQuWVCz3FsBh%2bGRoeygda4fsWK660XT6WsQYrmLBpBDu2%2bs%2fgv%2bCTaPiTg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6708 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7248 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5072 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7248 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
7248 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7248 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7248 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7248 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7248 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7248 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7248 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7248 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7248 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7248 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7248 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |