| File name: | CyberLink_PowerProducer_Downloader.exe |
| Full analysis: | https://app.any.run/tasks/3054d09e-6fbb-4487-bc14-24d985f62db2 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2020, 08:39:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0DB9683B8186C776573237A8530B03EA |
| SHA1: | F88A1D92F424D9DE543812592C53E77E053601DE |
| SHA256: | 84A9A56BFAC914C8439554A87E9A9595D36D00CA5FA7FC5A392118401A22A4C1 |
| SSDEEP: | 24576:4MkU4waNLeWCAqWVxOZRRarXVhP5AcTOy3jqKEj4coCYHb0YLmj:eJKWV6RRabOyTqKEUcoph0 |
MALICIOUS
Actions looks like stealing of personal data
- CyberLink_PowerProducer_Downloader.exe (PID: 440)
SUSPICIOUS
Reads Internet Cache Settings
- CyberLink_PowerProducer_Downloader.exe (PID: 440)
Reads the cookies of Google Chrome
- CyberLink_PowerProducer_Downloader.exe (PID: 440)
Reads the cookies of Mozilla Firefox
- CyberLink_PowerProducer_Downloader.exe (PID: 440)
Creates files in the program directory
- CyberLink_PowerProducer_Downloader.exe (PID: 440)
Creates files in the user directory
- CyberLink_PowerProducer_Downloader.exe (PID: 440)
INFO
Reads settings of System Certificates
- CyberLink_PowerProducer_Downloader.exe (PID: 440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:16 09:57:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 636928 |
| InitializedDataSize: | 520192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8596e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.2816 |
| ProductVersionNumber: | 3.0.0.2816 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | CyberLink |
| FileDescription: | CyberLink Downloader |
| FileVersion: | 3.0.0.2816 |
| InternalName: | CLDownloader |
| LegalCopyright: | Copyright (C) CyberLink Corporation. All rights reserved |
| OriginalFileName: | CLDownloader.exe |
| ProductName: | CLDownloader |
| ProductVersion: | 3.0.0.2816 |
Total processes
39
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Users\admin\AppData\Local\Temp\CyberLink_PowerProducer_Downloader.exe" | C:\Users\admin\AppData\Local\Temp\CyberLink_PowerProducer_Downloader.exe | explorer.exe | ||||||||||||
User: admin Company: CyberLink Integrity Level: MEDIUM Description: CyberLink Downloader Exit code: 0 Version: 3.0.0.2816 Modules
| |||||||||||||||
Total events
86
Read events
66
Write events
20
Delete events
0
Modification events
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\CyberLink\CBE |
| Operation: | write | Name: | UUID |
Value: S-1-5-21-1302019708-1500728564-335382590-1000-ED18DB0F-A7B9-4689-A11F-535C21214356 | |||
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (440) CyberLink_PowerProducer_Downloader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
13
Text files
39
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Local\Temp\CabE425.tmp | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Local\Temp\TarE426.tmp | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\OTT239B1.txt | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\2RYL0J2Q.txt | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\R7KMSHZ5.txt | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\CPL5YVWD.txt | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\LNCO5A8S.txt | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\TU9SLZHV.txt | — | |
MD5:— | SHA256:— | |||
| 440 | CyberLink_PowerProducer_Downloader.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\5HQPL1XJ.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
22
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
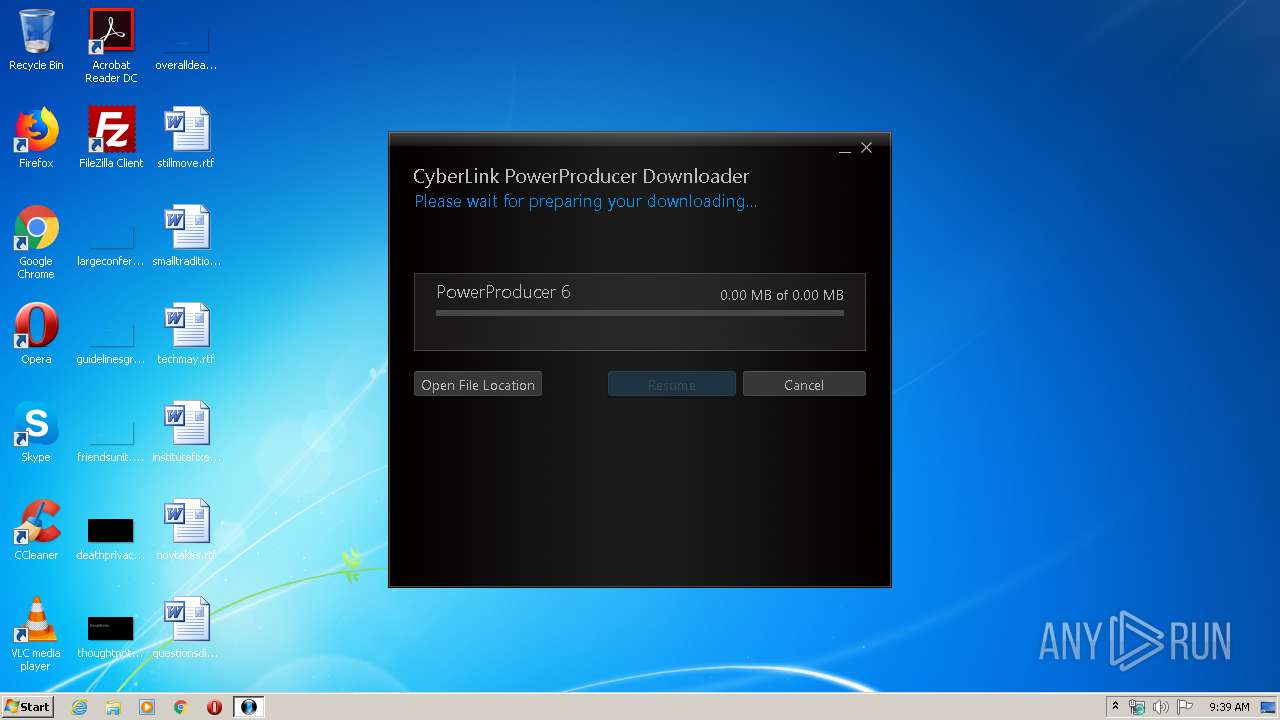
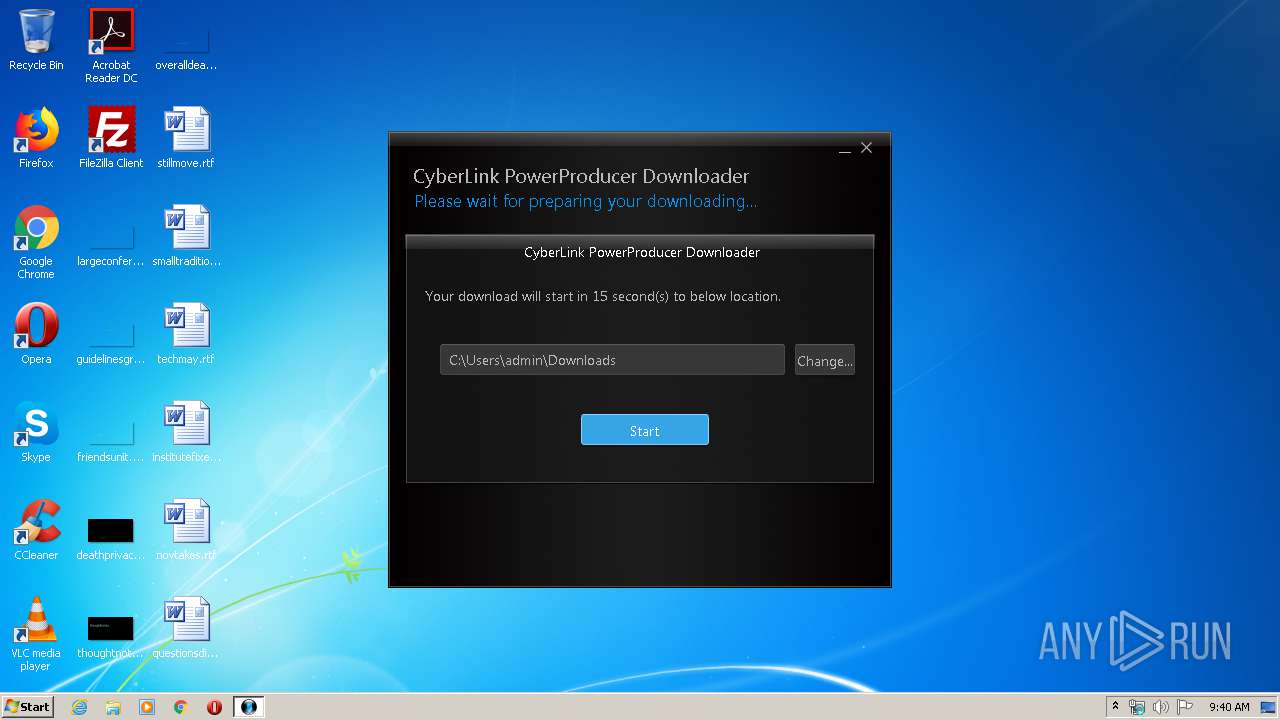
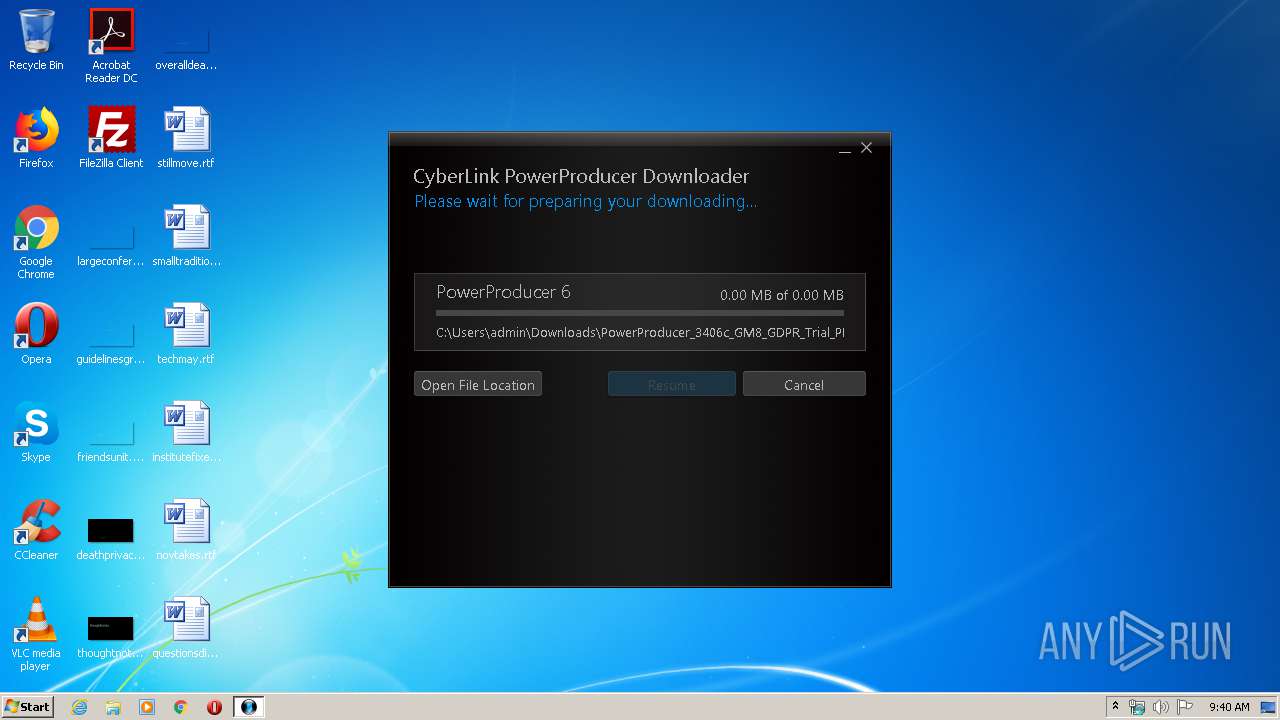
440 | CyberLink_PowerProducer_Downloader.exe | GET | — | 216.66.85.86:80 | http://update.cyberlink.com/Retail/PowerProducer/T6GX99BJCV9UX3BM/PowerProducer_3406c_GM8_GDPR_Trial_PPD180412-05.exe | US | — | — | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | GET | — | 216.66.85.86:80 | http://update.cyberlink.com/Retail/PowerProducer/T6GX99BJCV9UX3BM/PowerProducer_3406c_GM8_GDPR_Trial_PPD180412-05.exe | US | — | — | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | GET | — | 216.66.85.86:80 | http://update.cyberlink.com/Retail/PowerProducer/T6GX99BJCV9UX3BM/PowerProducer_3406c_GM8_GDPR_Trial_PPD180412-05.exe | US | — | — | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
440 | CyberLink_PowerProducer_Downloader.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
440 | CyberLink_PowerProducer_Downloader.exe | GET | — | 216.66.85.86:80 | http://update.cyberlink.com/Retail/PowerProducer/T6GX99BJCV9UX3BM/PowerProducer_3406c_GM8_GDPR_Trial_PPD180412-05.exe | US | — | — | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | GET | — | 216.66.85.86:80 | http://update.cyberlink.com/Retail/PowerProducer/T6GX99BJCV9UX3BM/PowerProducer_3406c_GM8_GDPR_Trial_PPD180412-05.exe | US | — | — | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | GET | — | 216.66.85.86:80 | http://update.cyberlink.com/Retail/PowerProducer/T6GX99BJCV9UX3BM/PowerProducer_3406c_GM8_GDPR_Trial_PPD180412-05.exe | US | — | — | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | GET | — | 216.66.85.86:80 | http://update.cyberlink.com/Retail/PowerProducer/T6GX99BJCV9UX3BM/PowerProducer_3406c_GM8_GDPR_Trial_PPD180412-05.exe | US | — | — | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEQDr6RCTje23Ge7S31mlTAMY | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
440 | CyberLink_PowerProducer_Downloader.exe | 52.88.16.80:443 | — | Amazon.com, Inc. | US | unknown |
440 | CyberLink_PowerProducer_Downloader.exe | 63.34.151.173:443 | downloader.cyberlink.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
440 | CyberLink_PowerProducer_Downloader.exe | 151.139.128.14:80 | dna.cyberlink.com | Highwinds Network Group, Inc. | US | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | 205.185.216.42:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
440 | CyberLink_PowerProducer_Downloader.exe | 216.66.85.86:80 | update.cyberlink.com | Hurricane Electric, Inc. | US | suspicious |
440 | CyberLink_PowerProducer_Downloader.exe | 72.52.91.58:443 | www.cyberlink.com | Hurricane Electric, Inc. | US | unknown |
440 | CyberLink_PowerProducer_Downloader.exe | 72.52.84.206:443 | liveupdate.cyberlink.com | Hurricane Electric, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dna.cyberlink.com |
| suspicious |
downloader.cyberlink.com |
| malicious |
ocsp.usertrust.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
update.cyberlink.com |
| suspicious |
www.cyberlink.com |
| suspicious |
liveupdate.cyberlink.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
440 | CyberLink_PowerProducer_Downloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |