| File name: | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe |
| Full analysis: | https://app.any.run/tasks/6dfd1711-e8ec-4761-8968-cb8c5c64c5a2 |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2024, 06:26:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AA03FF46A77747F907CB43B921EFB7D4 |
| SHA1: | 748DD0DC8BCEBC209C9DEA4331AF8DB445833C83 |
| SHA256: | 84A717B1B9DED0BF6700756164AE375E12EBD26FC2B204A0F31905686AB2939E |
| SSDEEP: | 98304:Ave8CxNOy8ERN+rGfbX22kxc8KUHCc60OlP5xWUuvin65HHWD5I0l81IvowR4dPp:bI2N2ZyYKu |
MALICIOUS
Drops the executable file immediately after the start
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
SUSPICIOUS
Process drops legitimate windows executable
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
The process drops C-runtime libraries
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
Process drops python dynamic module
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
Executable content was dropped or overwritten
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
Application launched itself
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
Loads Python modules
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 6860)
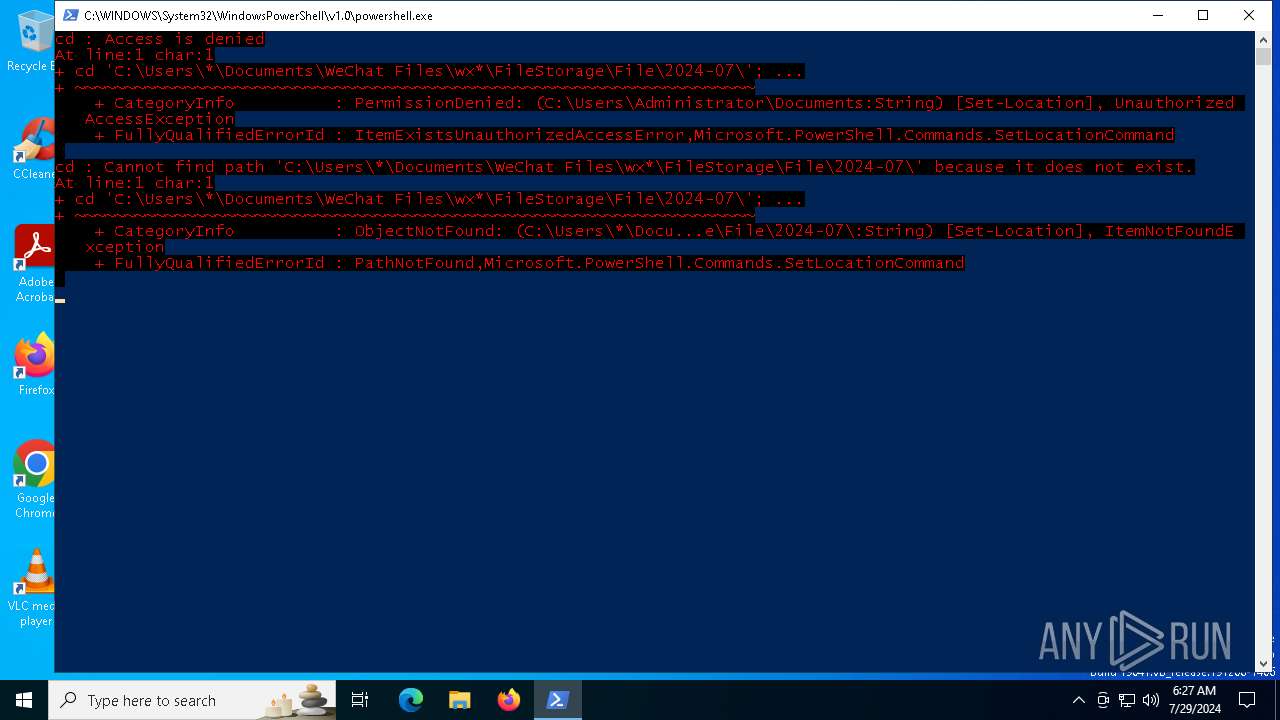
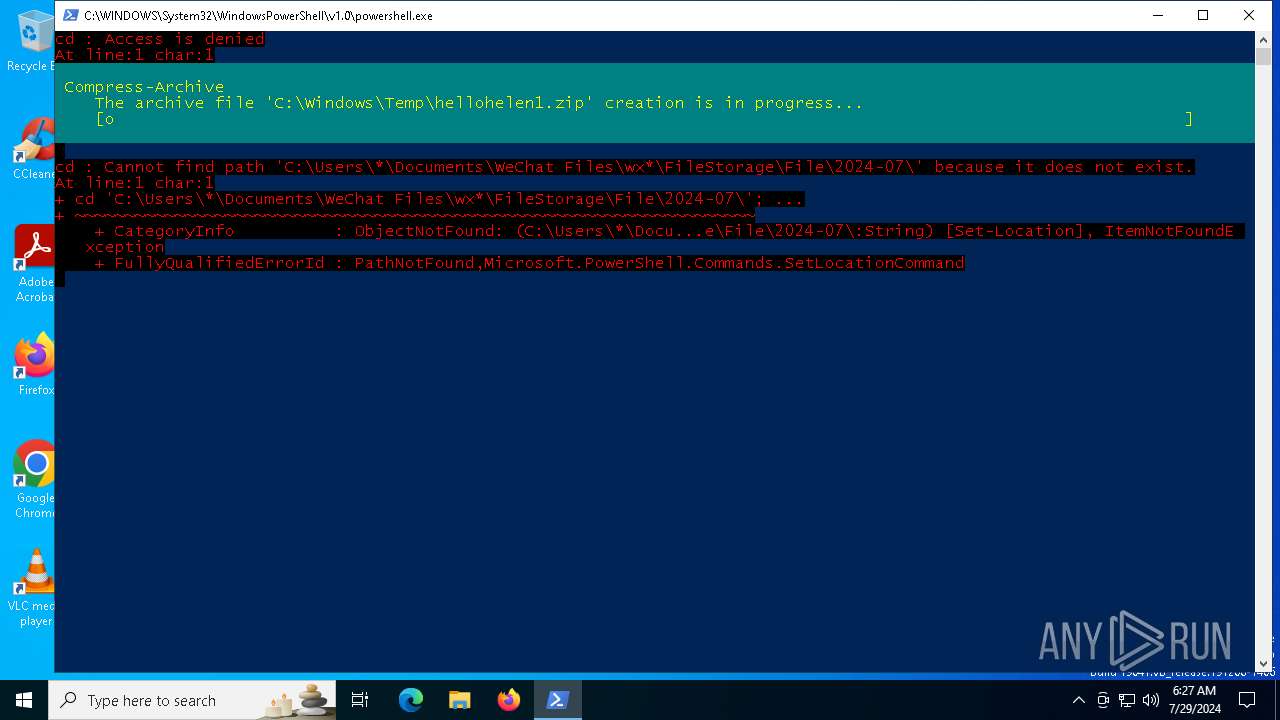
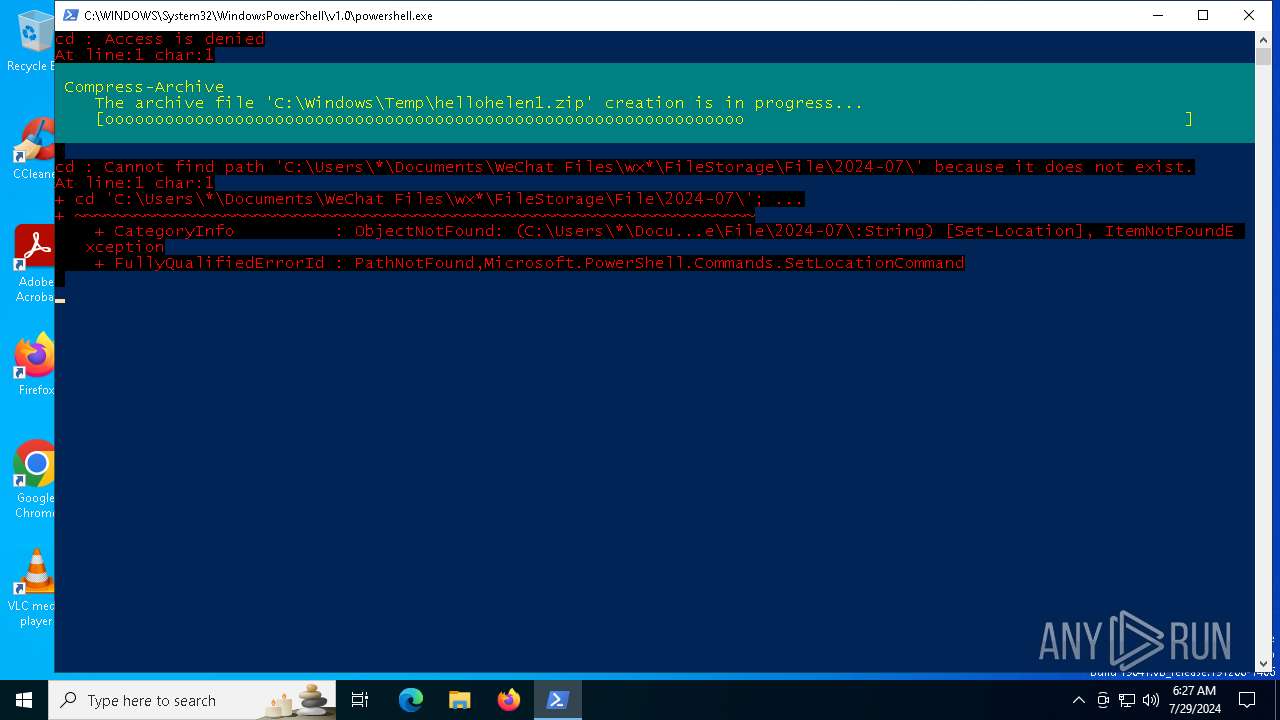
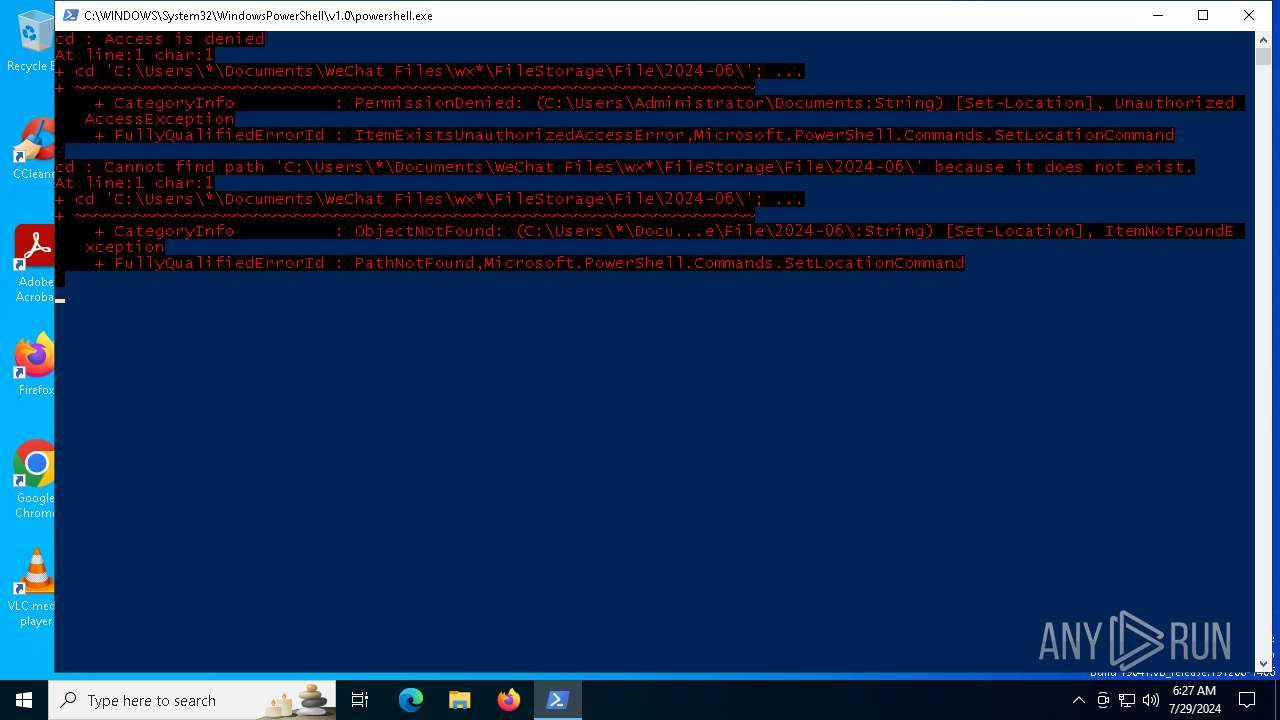
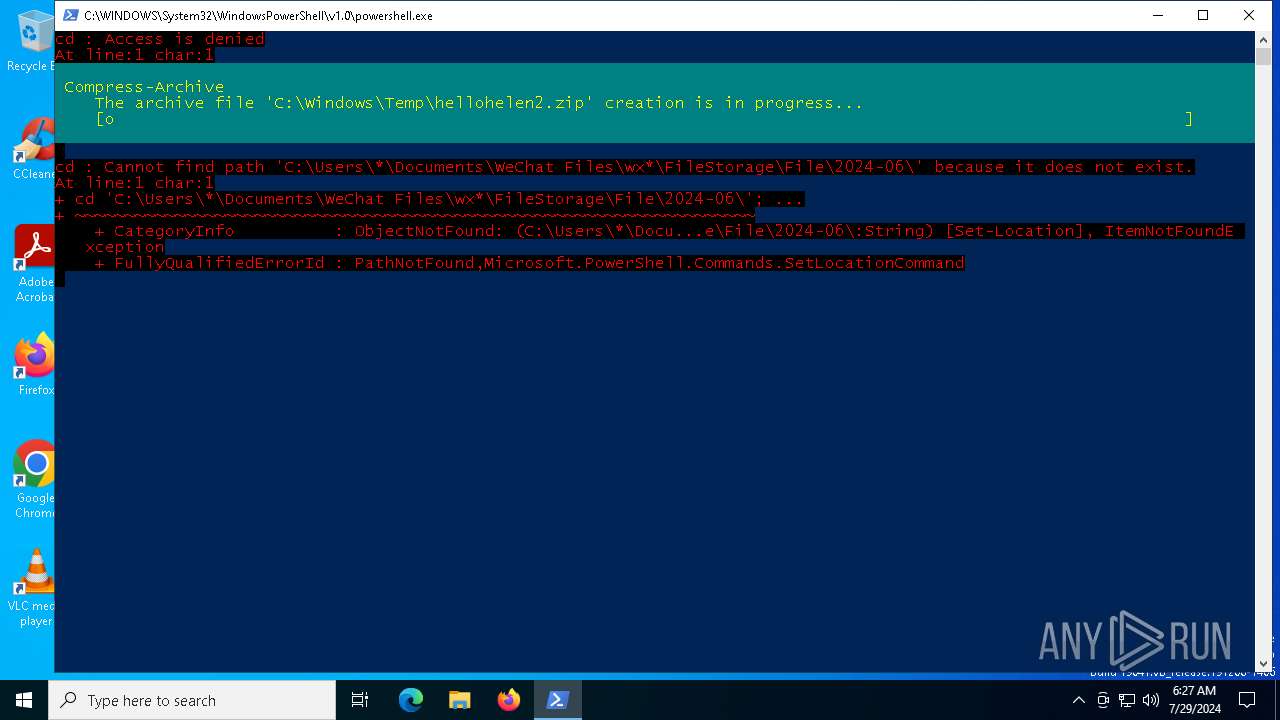
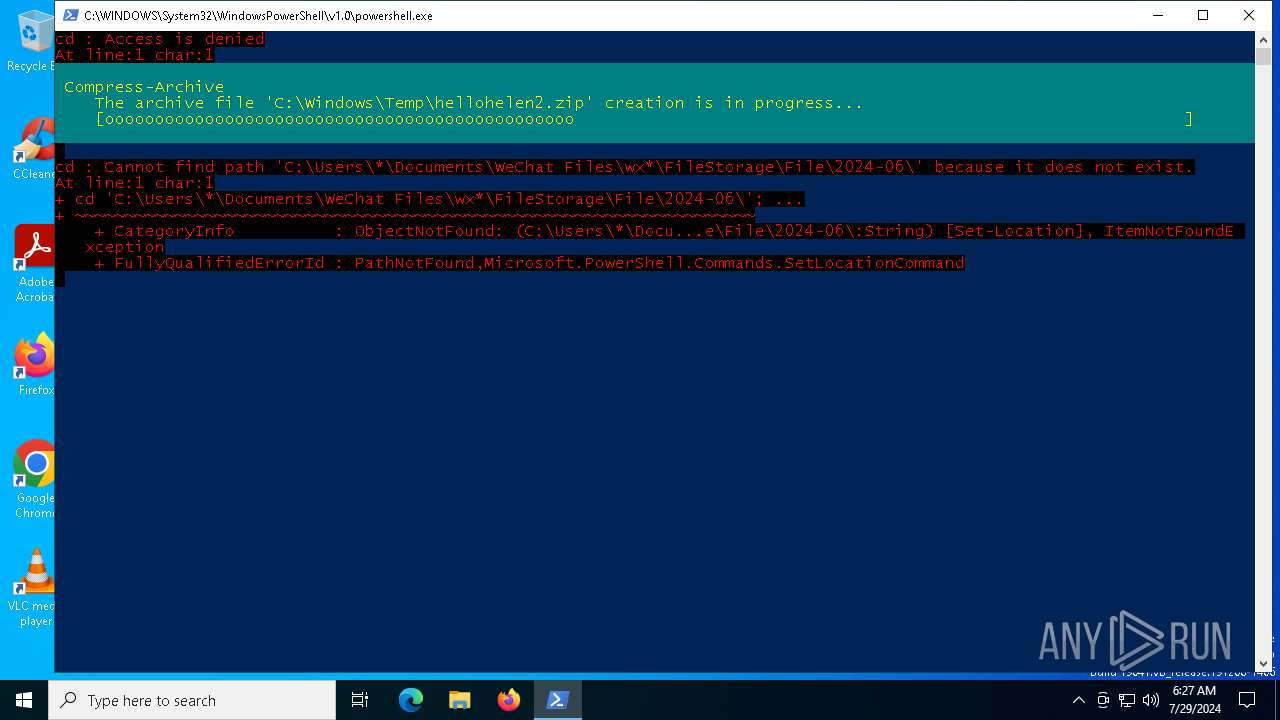
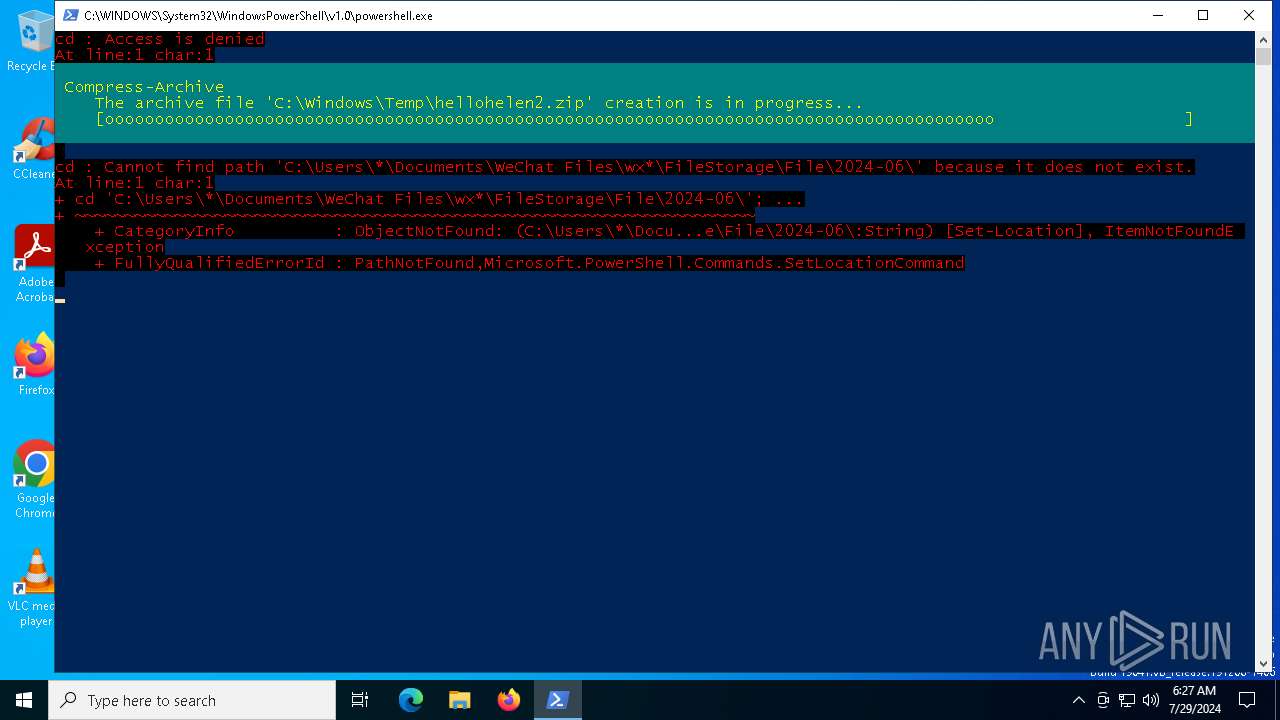
Starts POWERSHELL.EXE for commands execution
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 6860)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 236)
There is functionality for taking screenshot (YARA)
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 6860)
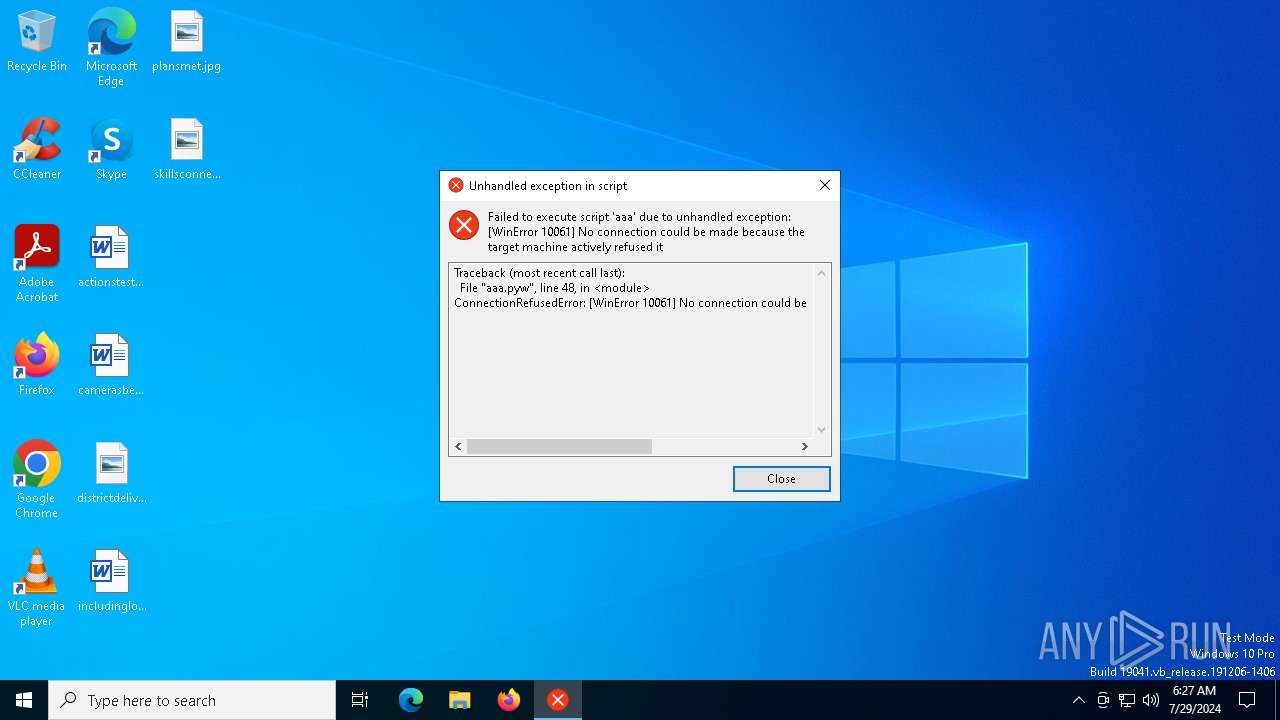
Connects to unusual port
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 6860)
INFO
Checks supported languages
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 6860)
Create files in a temporary directory
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
Reads the computer name
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 884)
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 6860)
Reads the machine GUID from the registry
- 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe (PID: 6860)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 236)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 236)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 236)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:24 07:26:40+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.4 |
| CodeSize: | 153600 |
| InitializedDataSize: | 82944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb210 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
148
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | powershell -Command "cd 'C:\Users\*\Documents\WeChat Files\wx*\FileStorage\File\2024-06\';Compress-Archive -Path * -DestinationPath C:\Windows\Temp\hellohelen2.zip" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 884 | "C:\Users\admin\AppData\Local\Temp\刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe" | C:\Users\admin\AppData\Local\Temp\刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1780 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3168 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5624 | powershell -Command "cd 'C:\Users\*\Documents\WeChat Files\wx*\FileStorage\File\2024-07\';Compress-Archive -Path * -DestinationPath C:\Windows\Temp\hellohelen1.zip" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6860 | "C:\Users\admin\AppData\Local\Temp\刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe" | C:\Users\admin\AppData\Local\Temp\刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 269
Read events
13 253
Write events
16
Delete events
0
Modification events
| (PID) Process: | (5624) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5624) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5624) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5624) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (236) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (236) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (236) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (236) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
18
Suspicious files
4
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\_bz2.pyd | executable | |
MD5:624CEACD3A77109802A64465BCCE5BE7 | SHA256:B683EFCFA97AB8F61C0D6819183F7B9929E1DA2F4E1B73B20966F090B022EC6E | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\_hashlib.pyd | executable | |
MD5:70C3FA1F69F9EE060D81E6079179852A | SHA256:CE2649DB951C4BE31627E666BA6280969418B8FDBA5F8D1296ADE4449F628CCB | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\_decimal.pyd | executable | |
MD5:1041B8813FB5C5E9C358CDECFD7CFDA2 | SHA256:FC42B6DC4083E1C48B27F07414E2273240DD6E89B0B737B7739A9C4D0AA3DE1A | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\_ssl.pyd | executable | |
MD5:9BFCDD632DABF81722DD3B8AE6ED76E0 | SHA256:BCE962BEA034AAF9A3A60984667BCEE15E138E0CCC63EADD1FFE2865F40539B2 | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\_lzma.pyd | executable | |
MD5:5C31A1D957CB96AA34F8C7792929BC59 | SHA256:2B526D4444CE7EADFEC564D0A19AD293585DFCE9E646A199D27017F01EDF4316 | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\_uuid.pyd | executable | |
MD5:6269A34234F7D6C2321D3D5324D48087 | SHA256:528C1AD06FBDB61DC31DC00B6A9AA51B2E4E94F34DC8F729898B81F0C08170C2 | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\_socket.pyd | executable | |
MD5:909030B95CB9CC3BA1A323889211098E | SHA256:702C1494CC2AD22DF6CA8FB9A2F0839C8EFB7A3468A712C96B273938140A3FB8 | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\libcrypto-1_1.dll | executable | |
MD5:AAD424A6A0AE6D6E7D4C50A1D96A17FC | SHA256:3A2DBA6098E77E36A9D20C647349A478CB0149020F909665D209F548DFA71377 | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\base_library.zip | compressed | |
MD5:1D365AC5BCDA32BB9F5477843217B5C8 | SHA256:7A7640D27B3A4E469E29BDB880D46579F633458A2584434939413139A5925F89 | |||
| 884 | 刘晨辉作品-Windows恶意应用自动化检测系统V1.3.exe | C:\Users\admin\AppData\Local\Temp\_MEI8842\libssl-1_1.dll | executable | |
MD5:697766ABA55F44BBD896CBD091A72B55 | SHA256:44A228B3646EB3575ABD5CBCB079E018DE11CA6B838A29E4391893DE69E0CF4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
42
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
2456 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5368 | SearchApp.exe | 92.123.104.50:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6012 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4648 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2472 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4788 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2668 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |