| File name: | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom |
| Full analysis: | https://app.any.run/tasks/ae57f06e-ca58-456b-a1e1-3b911c5a607e |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 04:28:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | D1D59828CA74B548D636615B6C828CC5 |
| SHA1: | E39E1440971C62E48BD344125826489D840C4825 |
| SHA256: | 84A2E709B53EB187E8F16B951BFEACB5D60E0D41B3FDA6DC1AC92ABFD5FB7B46 |
| SSDEEP: | 196608:HHXvfktYFHBtiN881mwU/kivNAnI9Wkkoo:HHXvfkt8tiN6wU/jFAYpJo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
Process drops python dynamic module
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
The process drops C-runtime libraries
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
Application launched itself
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
Process drops legitimate windows executable
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
Loads Python modules
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7604)
INFO
Create files in a temporary directory
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
Checks supported languages
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7604)
Reads the computer name
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7604)
Checks proxy server information
- slui.exe (PID: 7972)
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7604)
Reads the software policy settings
- slui.exe (PID: 7972)
The sample compiled with english language support
- 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe (PID: 7520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:17 17:41:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 173568 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce30 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
128
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7520 | "C:\Users\admin\Desktop\2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe" | C:\Users\admin\Desktop\2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7604 | "C:\Users\admin\Desktop\2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe" | C:\Users\admin\Desktop\2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 7972 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 654
Read events
3 654
Write events
0
Delete events
0
Modification events
Executable files
71
Suspicious files
1
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_chacha20.pyd | executable | |
MD5:0114E07B71F554D9696789BA4100062F | SHA256:ECB6C3CCB37BEE0A8B2A5C31C15ACA500C6AEEDDE825A749479660F65CCED39D | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_raw_aes.pyd | executable | |
MD5:A927B92173974652EE1570F53A5B419D | SHA256:3A01018171AEEFAE474A6791F0318DAA3373731B7D0F3C165118DF5C12DA3B41 | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_ARC4.pyd | executable | |
MD5:657643049554B6FF747D7FE645E4CCC7 | SHA256:0EC5270929B9A8E347BE684E2699D2C72A965B3304045475BBC06F3965CBC6B5 | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_Salsa20.pyd | executable | |
MD5:B27444F62C2050FE3DF13A92663FA174 | SHA256:10037AE4A433426966098AF1C7FCB8DA3F9BF6698C629B9EFA098EEB20ABED5E | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_raw_cfb.pyd | executable | |
MD5:26ED0DD5AC8C656A62246A9C9F3E935C | SHA256:96F26FFAA3131134785F8C6F97A70F00AE1058A928514863838D88E8D6F406F9 | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_raw_cast.pyd | executable | |
MD5:65FCF0C7D282BC4755BAFCDA6710F257 | SHA256:34627A78E8EDA0B6C517725839A0D34D4DB4D1D3602549F870330332B165A465 | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_raw_blowfish.pyd | executable | |
MD5:C7F70FBFB429D18144BCEAFF5FCC268B | SHA256:C883025EA591713C9C8CFA9DA76C528F7A75BDD0853B877A55C4C639DBAA595F | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_raw_arc2.pyd | executable | |
MD5:FE0E87F93714087FC66CBEB095A3E2BB | SHA256:CCDA26DE5920C34339038AC93FBB7A6CCB5139AF7A5F8087E08B6E0BC1E47733 | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_raw_ecb.pyd | executable | |
MD5:360B2E66F14161CBAB45387EBDD3A6E3 | SHA256:AB68361BCA3F5D49B6CDFC838D0B5E1B2B2BF161859EAEDD1F92CDA18EA0DF32 | |||
| 7520 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | C:\Users\admin\AppData\Local\Temp\_MEI75202\Crypto\Cipher\_raw_des3.pyd | executable | |
MD5:A03344A790C603C5D15820FB434E3ED9 | SHA256:3554BF2DC1556F81F19D51B54A2B634BFAEA8B610B131E9FFC36D07D10315CFA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
24
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1196 | RUXIMICS.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1196 | RUXIMICS.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1196 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1196 | RUXIMICS.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
1196 | RUXIMICS.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
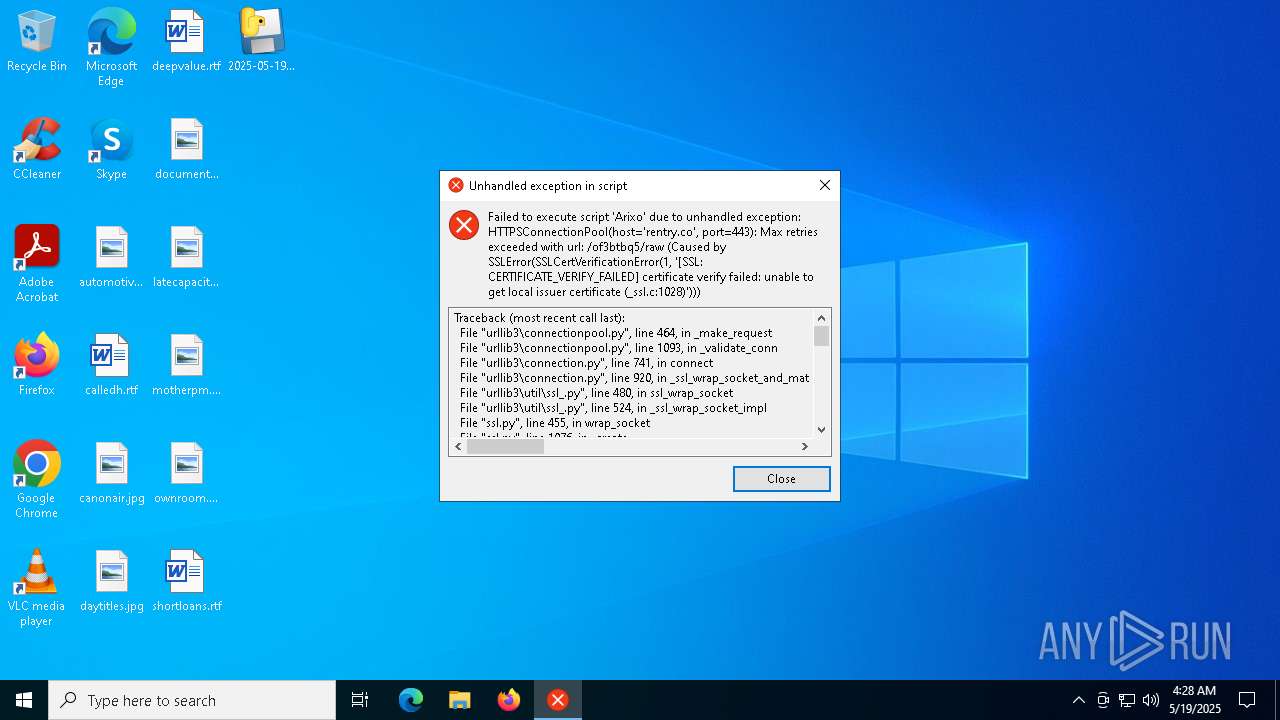
7604 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | 172.67.75.40:443 | rentry.co | CLOUDFLARENET | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
rentry.co |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
7604 | 2025-05-19_d1d59828ca74b548d636615b6c828cc5_black-basta_cobalt-strike_satacom.exe | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |