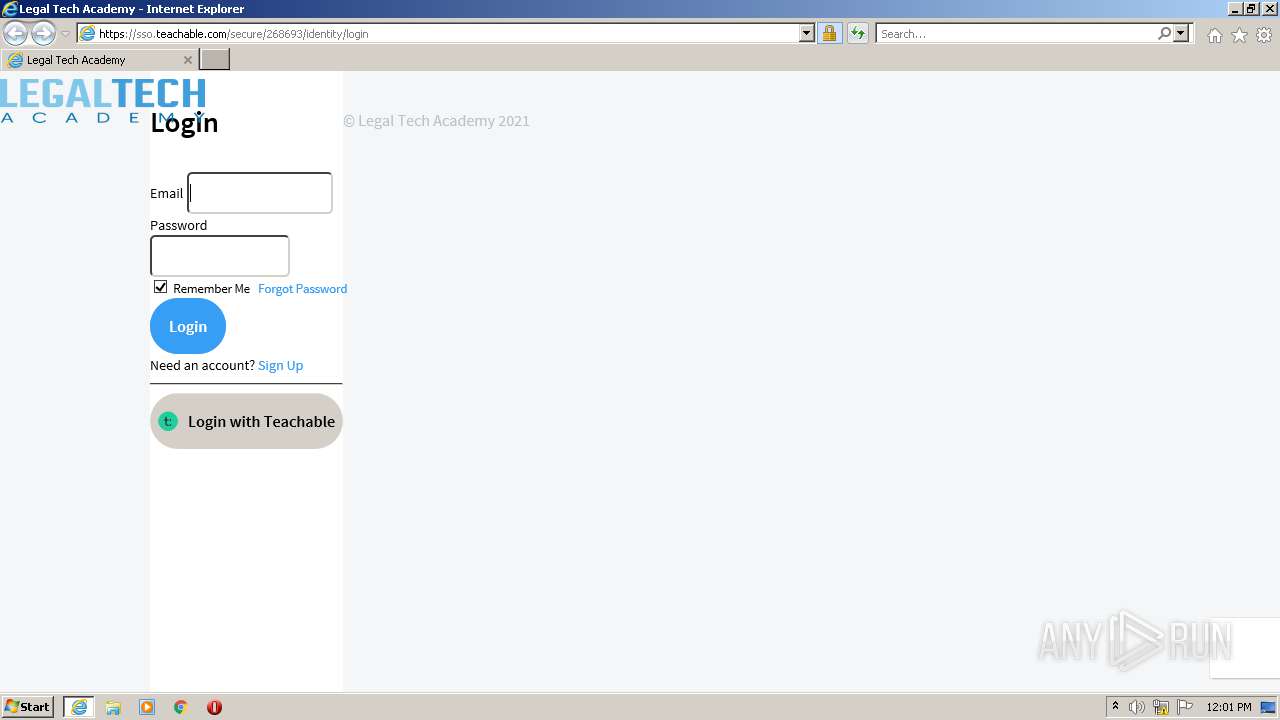
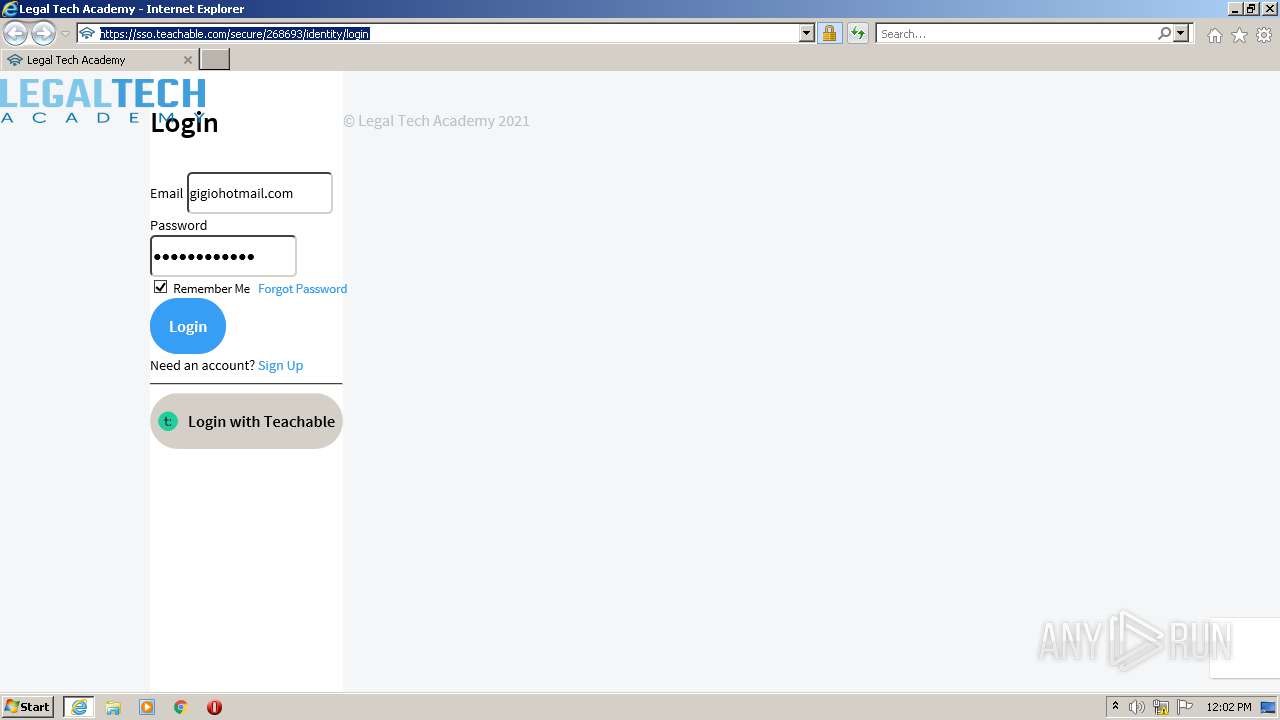
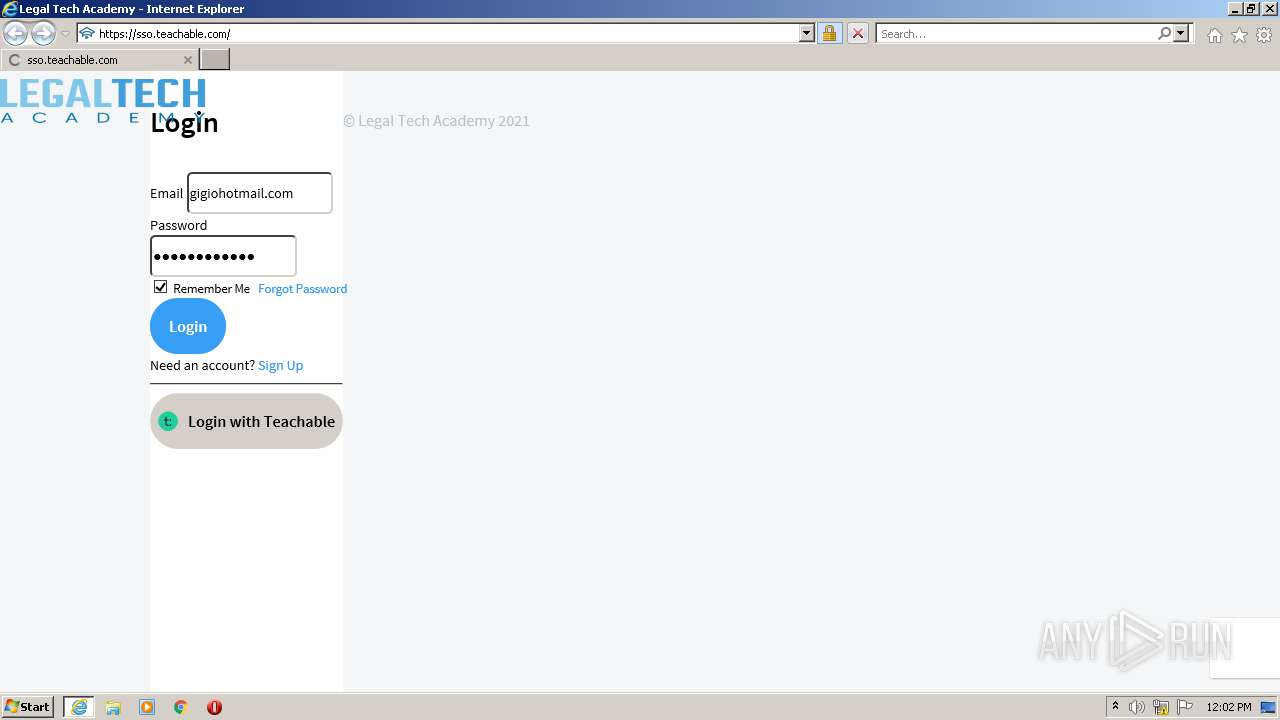
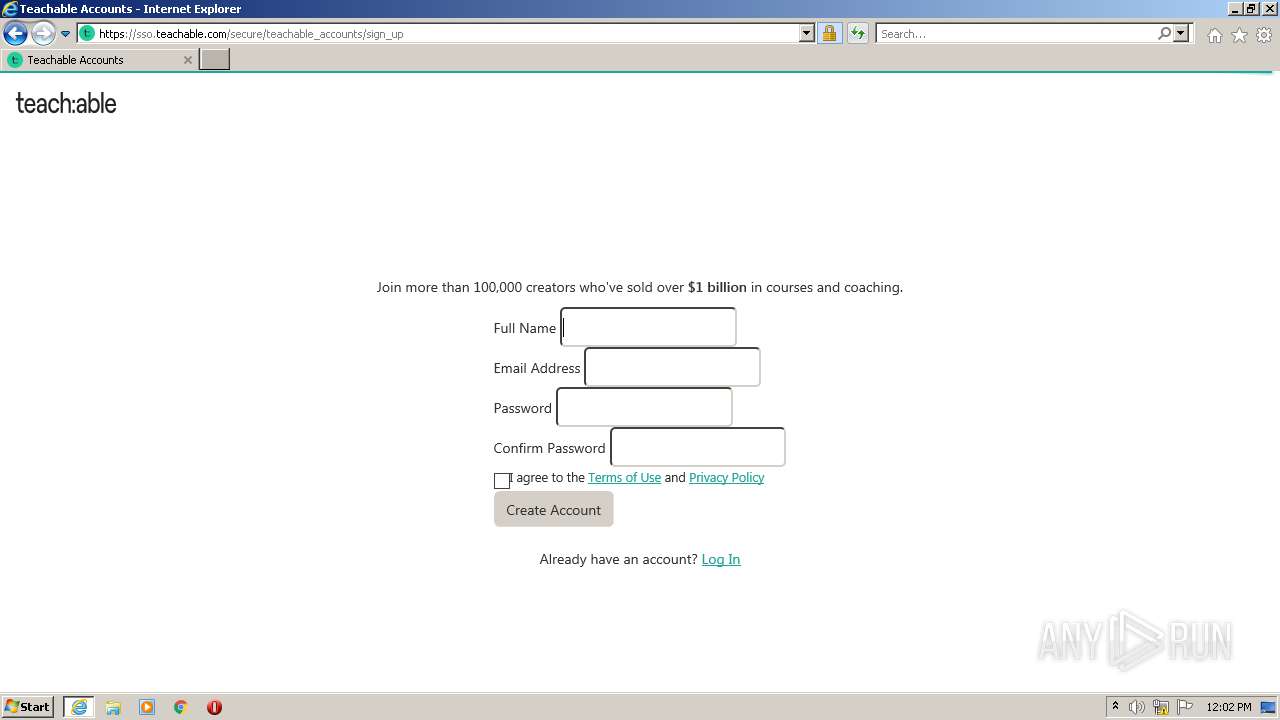
| URL: | https://sso.teachable.com/secure/268693/identity/login?state=109aea3b-8ab6-4a90-89db-9cb8c8382f5d |
| Full analysis: | https://app.any.run/tasks/b57f9cb0-7215-406e-b258-2e655ffdbf20 |
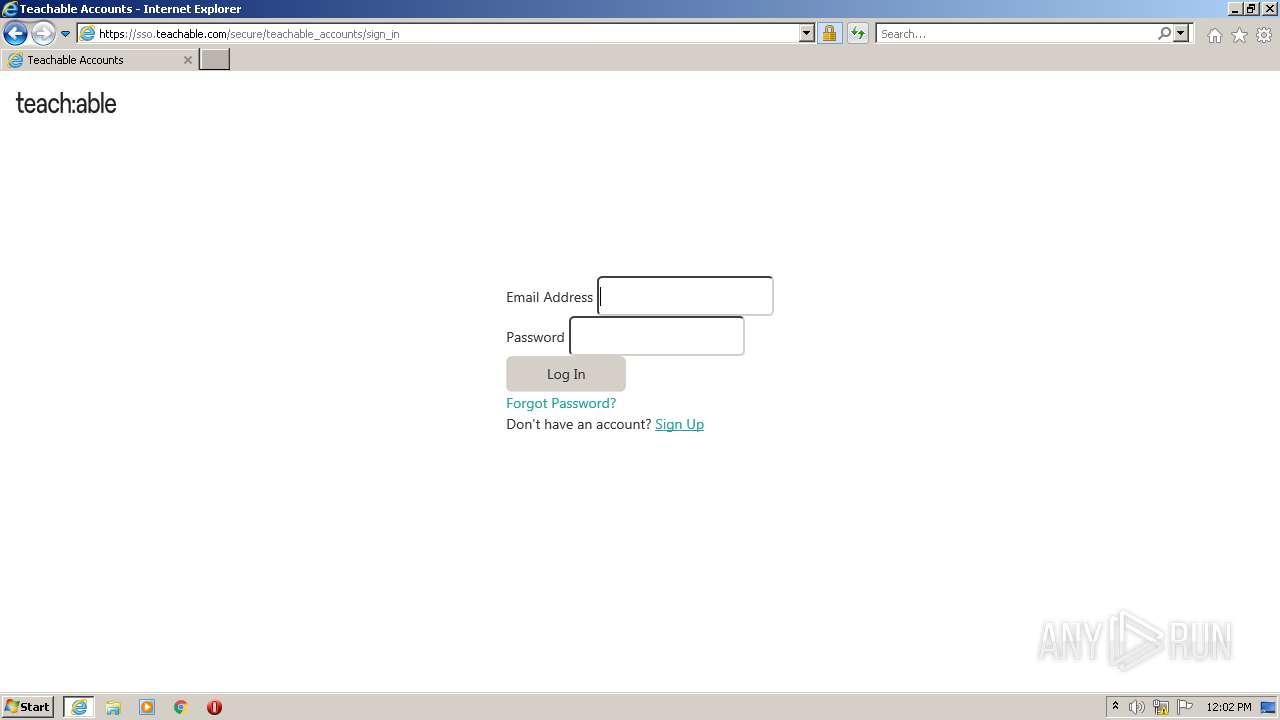
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2021, 12:00:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A8A13952D0A9BA5DD351A13F7BB19CC2 |
| SHA1: | B13C653525C28132721392D66B0A527D49A93CEF |
| SHA256: | 84A1C6DFE3BD29BBD9EDFC53FCD7247A1A17CBD99F82E3E9A3B4D6BF4B486DC7 |
| SSDEEP: | 3:N8bEhauZAGWDdTRAlJSZKT4yfAIduEGc8EEXA:2W/ZuTmlgZKR4IduEL3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3304)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 592)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 592)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 592)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 592)
INFO
Application launched itself
- iexplore.exe (PID: 3772)
Reads the computer name
- iexplore.exe (PID: 3304)
- iexplore.exe (PID: 3772)
Checks supported languages
- iexplore.exe (PID: 3772)
- iexplore.exe (PID: 3304)
Checks Windows Trust Settings
- iexplore.exe (PID: 3772)
- iexplore.exe (PID: 3304)
Reads CPU info
- iexplore.exe (PID: 3304)
Reads settings of System Certificates
- iexplore.exe (PID: 3772)
- iexplore.exe (PID: 3304)
Changes internet zones settings
- iexplore.exe (PID: 3772)
Creates files in the user directory
- iexplore.exe (PID: 3304)
- iexplore.exe (PID: 3772)
Reads internet explorer settings
- iexplore.exe (PID: 3304)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3772)
Changes settings of System certificates
- iexplore.exe (PID: 3772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3304 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3772 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3772 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://sso.teachable.com/secure/268693/identity/login?state=109aea3b-8ab6-4a90-89db-9cb8c8382f5d" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
24 088
Read events
23 832
Write events
252
Delete events
4
Modification events
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 738839616 | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30930329 | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30930329 | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3772) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
40
Text files
101
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:76A7FF00262B4675A633F351F8DE21C1 | SHA256:0597FE18458308ABD7FBB9B260A6912072EF35076688ED5A776D3EB1857FC2B1 | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:076CACB9C61F974F72AABB65B9632EA8 | SHA256:1A39B0BC634314512BF0E538A46B371D0D89D00C3026B3EF31CE3B65A35A790E | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Y9H0ZNKV.txt | text | |
MD5:AB6B57501240EA3E554D536FF2094F05 | SHA256:98A2C9C967CF4904F5FD1C5BFB68CE5CA14396841828A8A5198812E1651EC7E1 | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\VB5IBGNV.txt | text | |
MD5:38DDE00970F5EA7578B04B2B36551BE0 | SHA256:5954B7F2B1C536E6AA03D321120DFD36B1917DB9A5716D5CD8CC6065CD57263E | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5DC943NC.txt | text | |
MD5:EDC48144D616A05F099C2548CBC0AC7E | SHA256:D2AB4414615BAF25568433F07C50CDF97613976D22487ABA2DBF5AFCC43FDAE9 | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Y1FLK2Y9.txt | text | |
MD5:2D3D836746194CA3375A8CD2D2DD6858 | SHA256:B3FB67FCEEBE5A087149C3958BFC17368577C320D98813B0C77278A59693EC0A | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:83D6D840A3B0DBB14B4474AA5B3D0630 | SHA256:6EB142EAC6346D331D947163FB4DCB524AC50FD0A4CA4BAB685CB8FE817BEC6D | |||
| 3772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:0F2B8ACD0F546292CD59CD99F6C4F162 | SHA256:E957741679B936A724254958CDC2670A73DEC7D3250F6D44707A20FDEA0B3060 | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XTACZ780.txt | text | |
MD5:7D40FC2EE415446A7773DEADF147C6C8 | SHA256:DDA508D20CCB610B9B5346C5481C30925A4A4E5FB32B9356AD9600DF97A82651 | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KBSNK3VY.txt | text | |
MD5:7D84AC3D5B735BC653B934263495D552 | SHA256:44195972412F1B84C25EED4511BDDBF16AB09C50556D3A7D87072522CA4DB3CB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
142
DNS requests
62
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3304 | iexplore.exe | GET | 200 | 13.225.84.42:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3304 | iexplore.exe | GET | 200 | 13.225.84.175:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3772 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
3304 | iexplore.exe | GET | — | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECiWvl1%2BUB7cCgAAAAEl%2F%2BI%3D | US | — | — | whitelisted |
3772 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
3772 | iexplore.exe | GET | 200 | 2.16.186.56:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cd22d12eedb0c3b6 | unknown | compressed | 4.70 Kb | whitelisted |
3772 | iexplore.exe | GET | 200 | 2.16.186.56:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5648759d9f31c215 | unknown | compressed | 4.70 Kb | whitelisted |
3304 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3304 | iexplore.exe | GET | 200 | 142.250.186.46:80 | http://crls.pki.goog/gts1c3/QOvJ0N1sT2A.crl | US | der | 6.65 Kb | whitelisted |
3304 | iexplore.exe | GET | 200 | 13.225.84.49:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3304 | iexplore.exe | 104.19.238.117:443 | sso.teachable.com | Cloudflare Inc | US | shared |
3772 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3772 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3304 | iexplore.exe | 142.250.186.163:443 | www.recaptcha.net | Google Inc. | US | whitelisted |
3304 | iexplore.exe | 104.19.239.117:443 | sso.teachable.com | Cloudflare Inc | US | shared |
3304 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3304 | iexplore.exe | 151.101.2.49:443 | process.fs.teachablecdn.com | Fastly | US | malicious |
3304 | iexplore.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3304 | iexplore.exe | 151.101.2.110:443 | fast.wistia.com | Fastly | US | suspicious |
3304 | iexplore.exe | 13.224.193.12:443 | themes2.teachablecdn.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sso.teachable.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fast.wistia.com |
| whitelisted |
www.recaptcha.net |
| whitelisted |
fedora.teachablecdn.com |
| shared |
themes2.teachablecdn.com |
| whitelisted |
process.fs.teachablecdn.com |
| whitelisted |