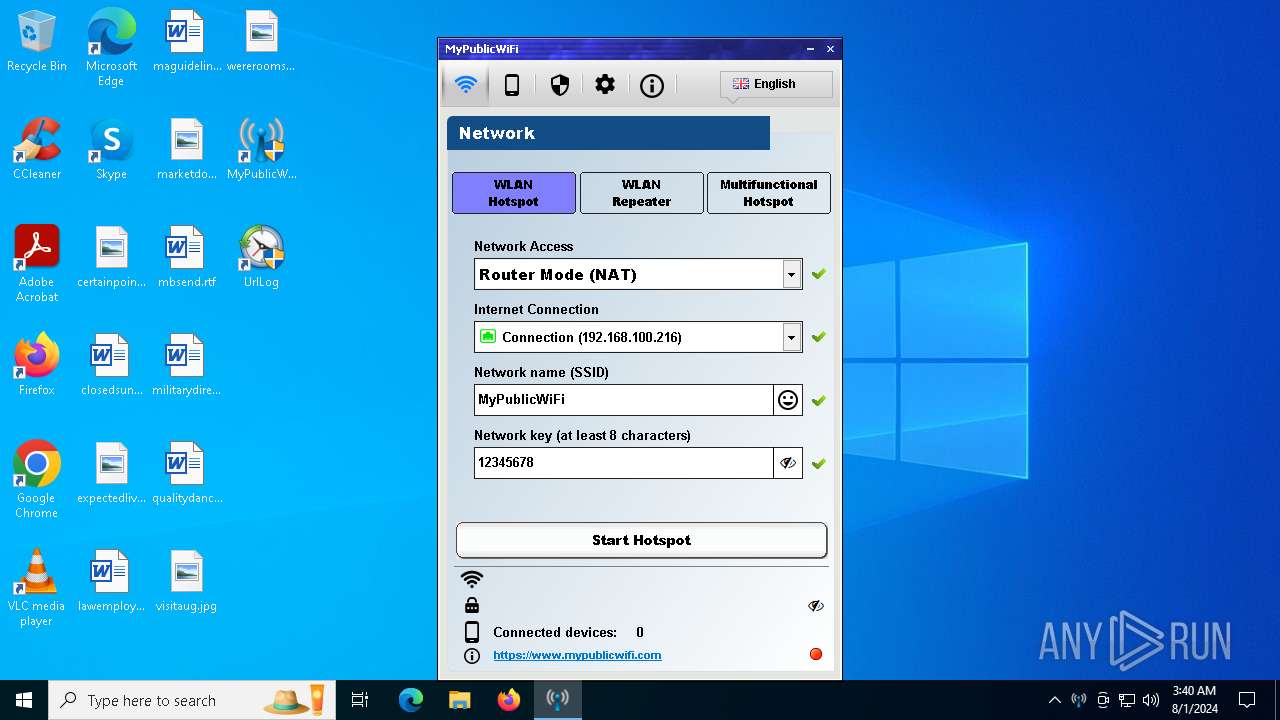
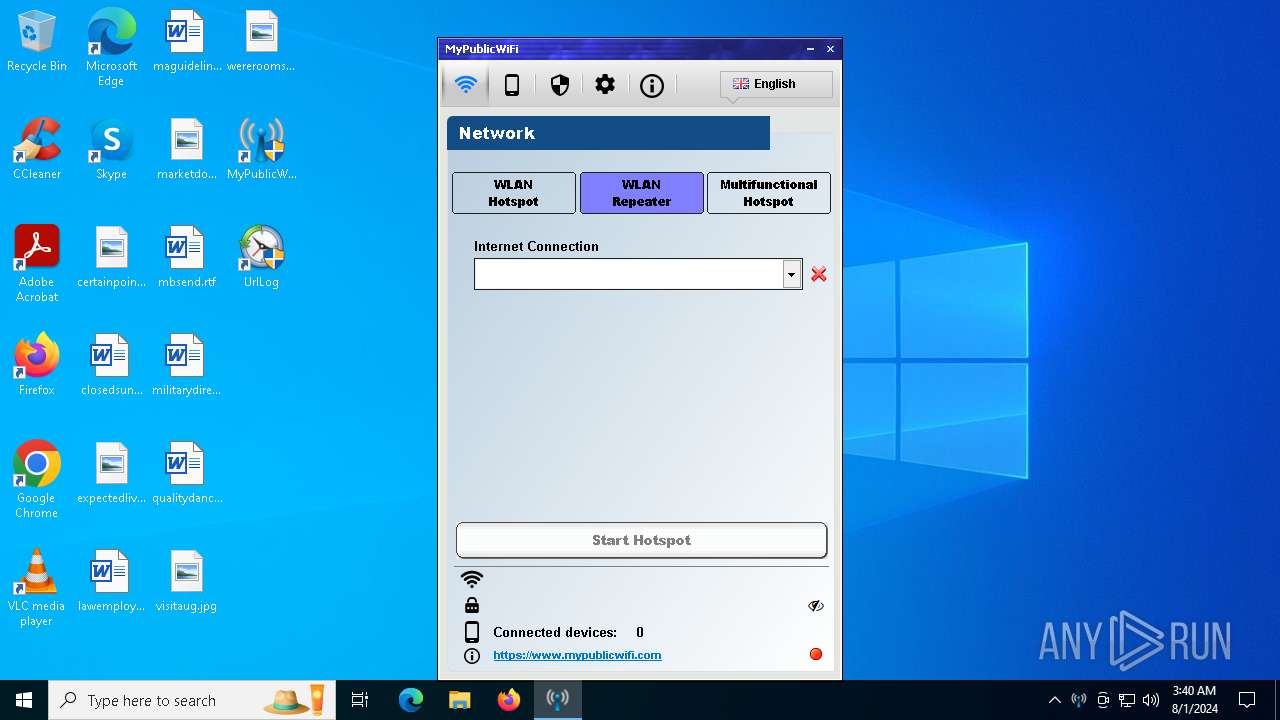
| File name: | MyPublicWiFi.exe |
| Full analysis: | https://app.any.run/tasks/48845e9e-08c1-4dff-8d7c-645edeb328bc |
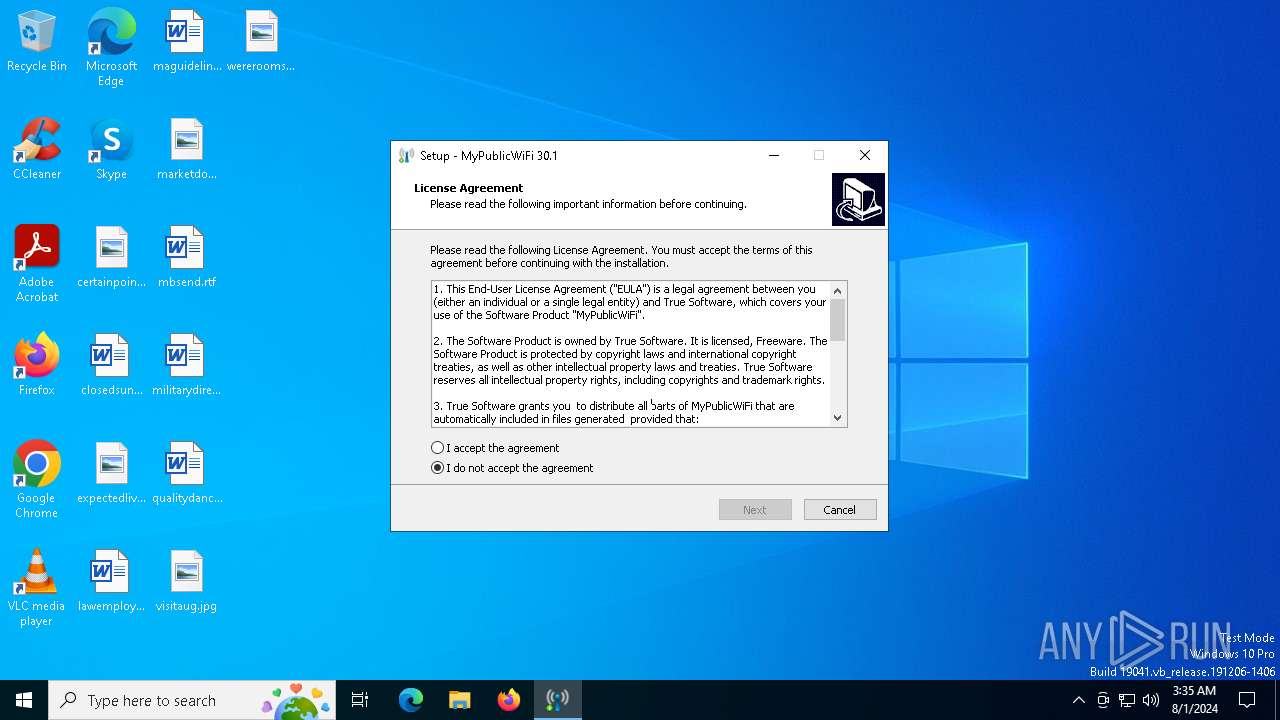
| Verdict: | Malicious activity |
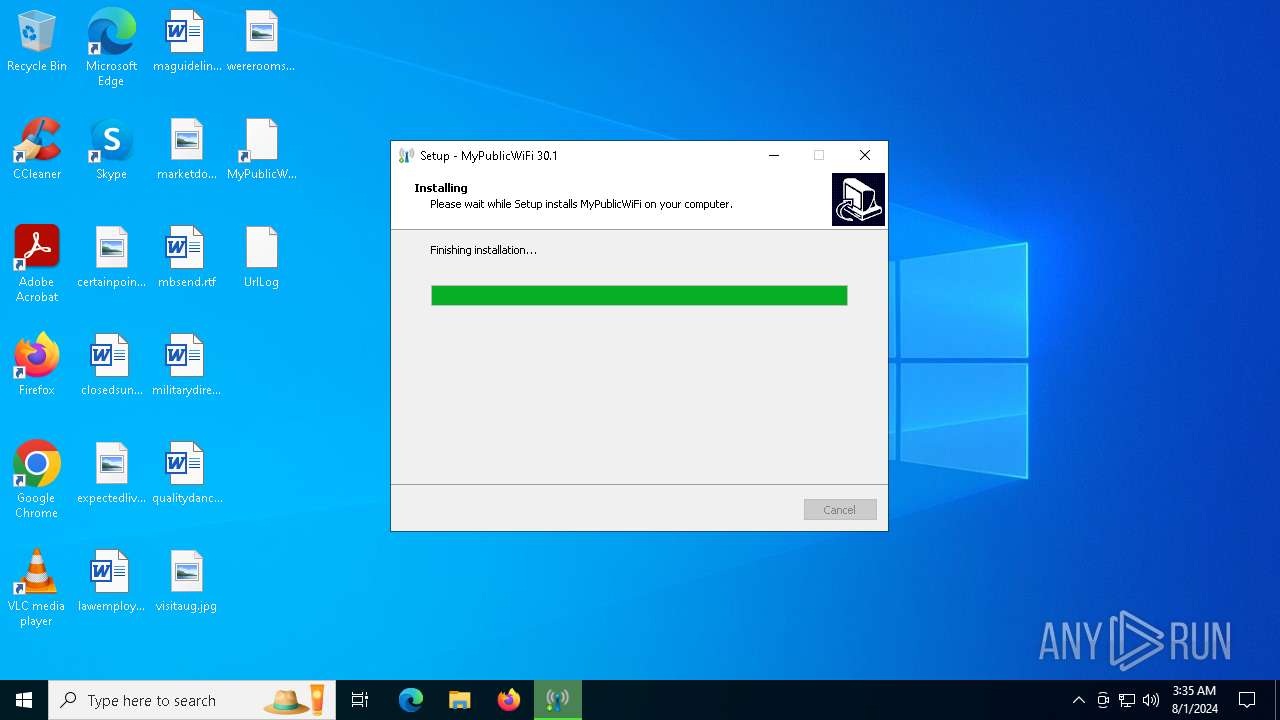
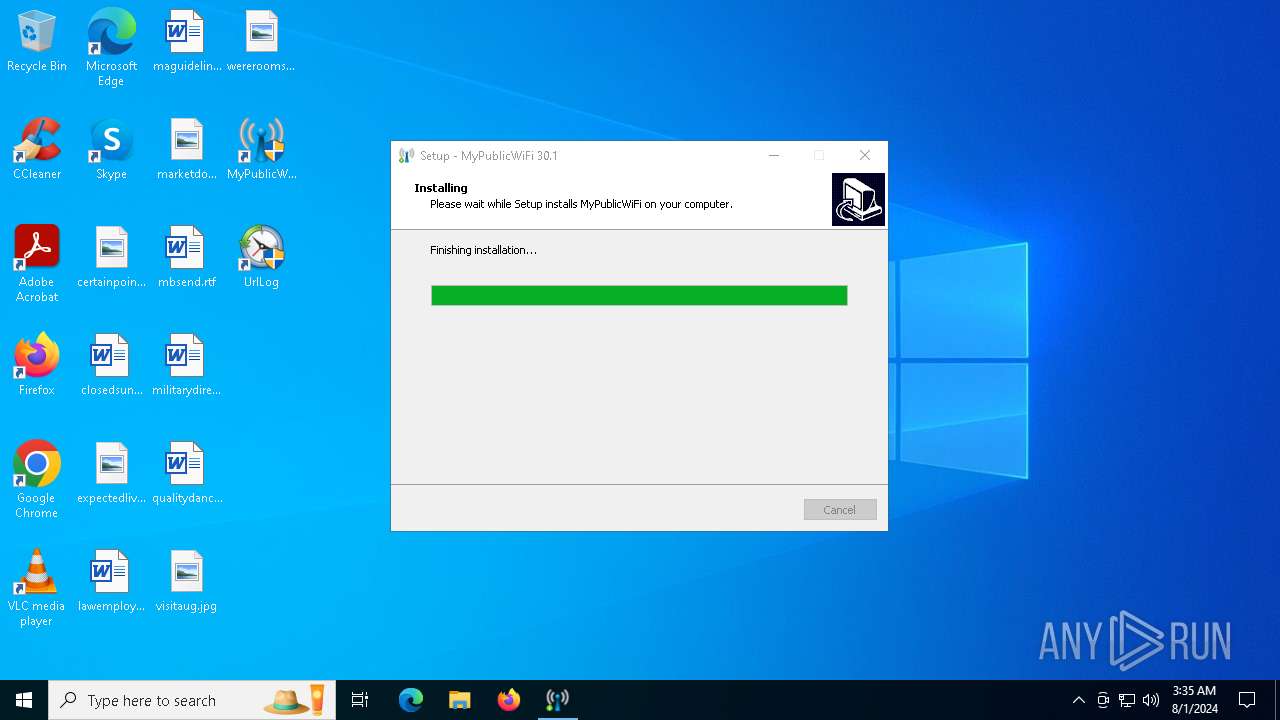
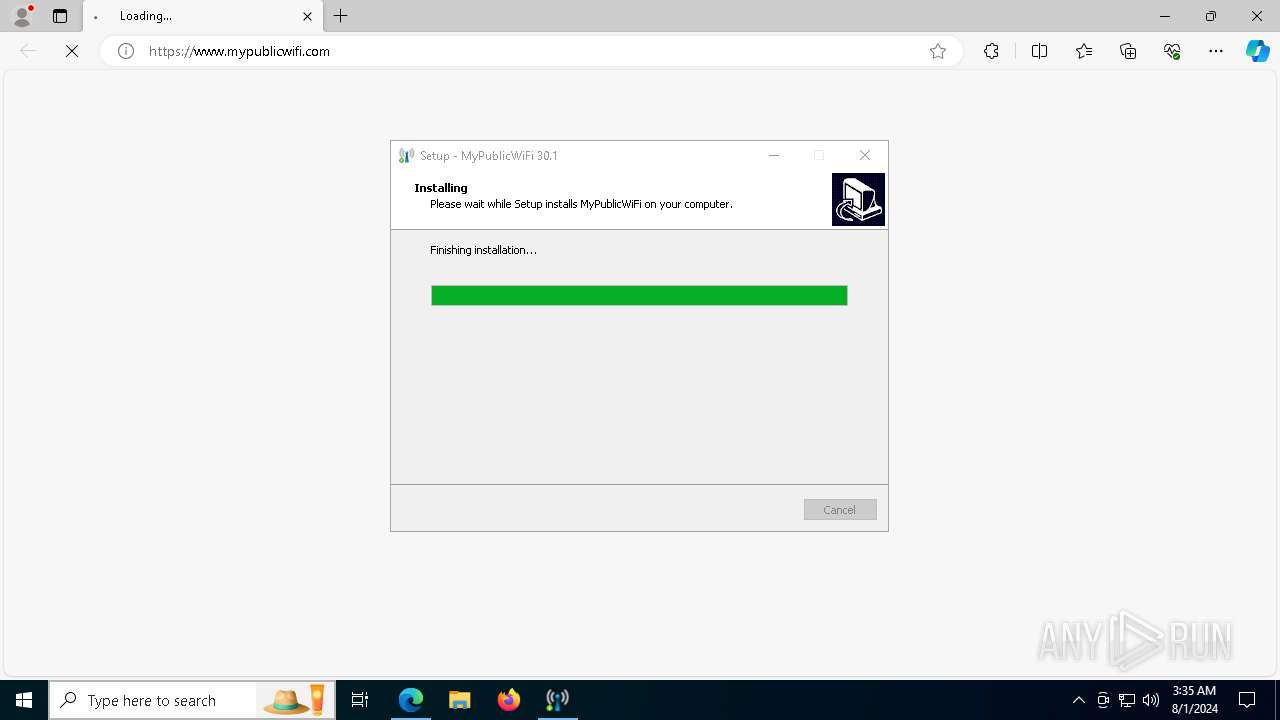
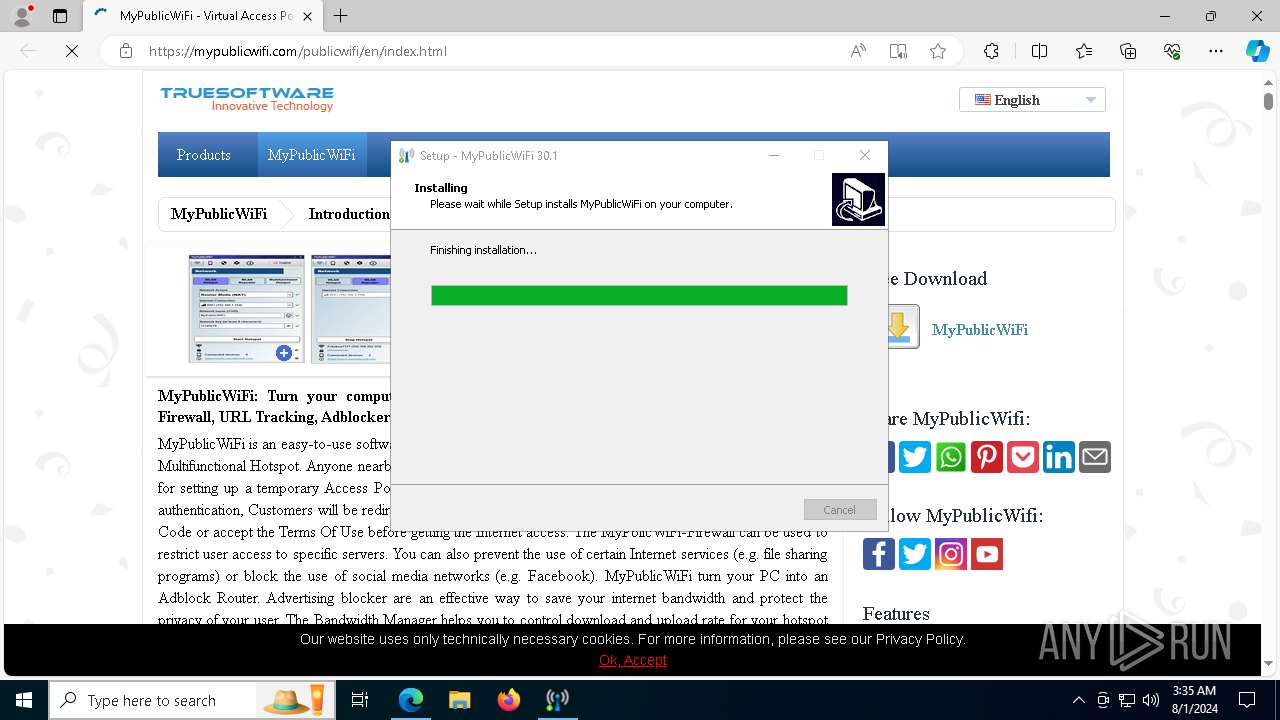
| Analysis date: | August 01, 2024, 03:35:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6EB403ECBC131FD2B3E0966E61400935 |
| SHA1: | D2313484B9CE8E8287D7DF971765955953B762B4 |
| SHA256: | 846E78D0696C04B6423469255C6D322E81B31593E46D1CFDC74B1CDB380F8D12 |
| SSDEEP: | 98304:J+QqZ8fkhGPVtMmqTJLnECCNtwXrmtzSQs6R90C0M8YP2ZE6VH3sBSwJaniDx1RY:7lLTbv2/zSC |
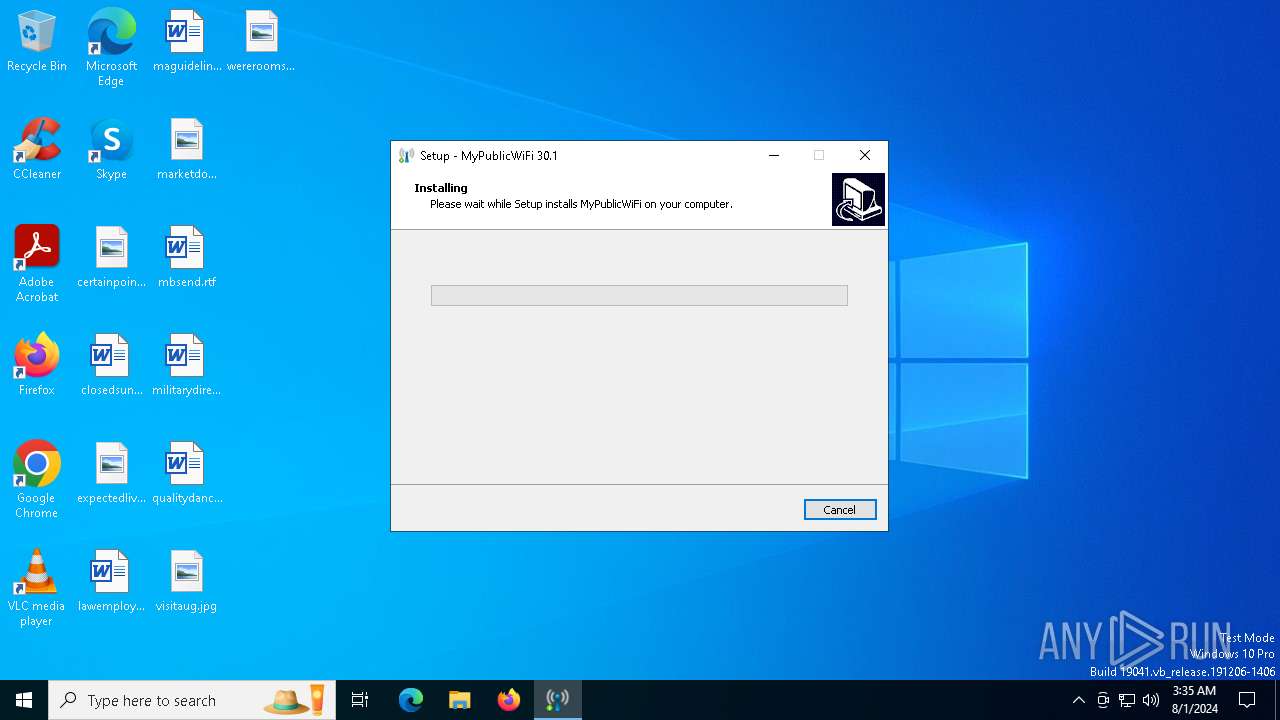
MALICIOUS
Drops the executable file immediately after the start
- MyPublicWiFi.exe (PID: 6444)
- MyPublicWiFi.exe (PID: 6536)
- MyPublicWiFi.tmp (PID: 6560)
- drvinst.exe (PID: 1360)
Starts NET.EXE for service management
- net.exe (PID: 4824)
- MyPublicWiFi.tmp (PID: 6560)
- net.exe (PID: 7764)
- MyPublicWiFi.exe (PID: 7192)
- net.exe (PID: 5908)
- net.exe (PID: 6412)
- net.exe (PID: 7580)
- net.exe (PID: 6360)
- net.exe (PID: 6420)
- net.exe (PID: 7820)
- net.exe (PID: 5084)
- net.exe (PID: 7424)
- MyPublicWiFi.exe (PID: 7892)
- net.exe (PID: 6464)
- net.exe (PID: 6160)
Changes the autorun value in the registry
- MyPublicWiFi.exe (PID: 7192)
- MyPublicWiFi.exe (PID: 7892)
SUSPICIOUS
Executable content was dropped or overwritten
- MyPublicWiFi.exe (PID: 6444)
- MyPublicWiFi.exe (PID: 6536)
- MyPublicWiFi.tmp (PID: 6560)
- netcfg.exe (PID: 5908)
- drvinst.exe (PID: 1360)
Reads the date of Windows installation
- MyPublicWiFi.tmp (PID: 6464)
Reads security settings of Internet Explorer
- MyPublicWiFi.tmp (PID: 6464)
- MyPublicWiFi.tmp (PID: 6560)
- MyPublicWiFi.exe (PID: 7192)
Reads the Windows owner or organization settings
- MyPublicWiFi.tmp (PID: 6560)
Adds/modifies Windows certificates
- certinst.exe (PID: 5880)
- certinst.exe (PID: 1688)
Drops a system driver (possible attempt to evade defenses)
- netcfg.exe (PID: 5908)
- drvinst.exe (PID: 1360)
- MyPublicWiFi.tmp (PID: 6560)
Creates files in the driver directory
- drvinst.exe (PID: 1360)
Checks Windows Trust Settings
- drvinst.exe (PID: 1360)
Executes as Windows Service
- PublicWiFiService.exe (PID: 7580)
- PublicWiFiService.exe (PID: 1564)
- PublicWiFiService.exe (PID: 6828)
- PublicWiFiService.exe (PID: 7684)
- PublicWiFiService.exe (PID: 7628)
Starts POWERSHELL.EXE for commands execution
- MyPublicWiFi.exe (PID: 7192)
- MyPublicWiFi.exe (PID: 7892)
Process uses powershell cmdlet to discover network configuration
- MyPublicWiFi.exe (PID: 7192)
- MyPublicWiFi.exe (PID: 7892)
Suspicious use of NETSH.EXE
- MyPublicWiFi.exe (PID: 7192)
There is functionality for taking screenshot (YARA)
- PublicWiFiService.exe (PID: 6828)
- PublicWiFiService.exe (PID: 7684)
There is functionality for communication over UDP network (YARA)
- PublicWiFiService.exe (PID: 6828)
- PublicWiFiService.exe (PID: 7684)
INFO
Checks supported languages
- MyPublicWiFi.exe (PID: 6444)
- MyPublicWiFi.tmp (PID: 6464)
- MyPublicWiFi.exe (PID: 6536)
- MyPublicWiFi.tmp (PID: 6560)
- certinst.exe (PID: 5880)
- certinst.exe (PID: 1688)
- drvinst.exe (PID: 1360)
- PublicWiFiService.exe (PID: 4236)
- PublicWiFiService.exe (PID: 7580)
- identity_helper.exe (PID: 7304)
- identity_helper.exe (PID: 7284)
- MyPublicWiFi.exe (PID: 7192)
- PublicWiFiService.exe (PID: 1564)
- identity_helper.exe (PID: 8076)
- PublicWiFiService.exe (PID: 6828)
- PublicWiFiService.exe (PID: 7684)
- MyPublicWiFi.exe (PID: 7892)
- PublicWiFiService.exe (PID: 7628)
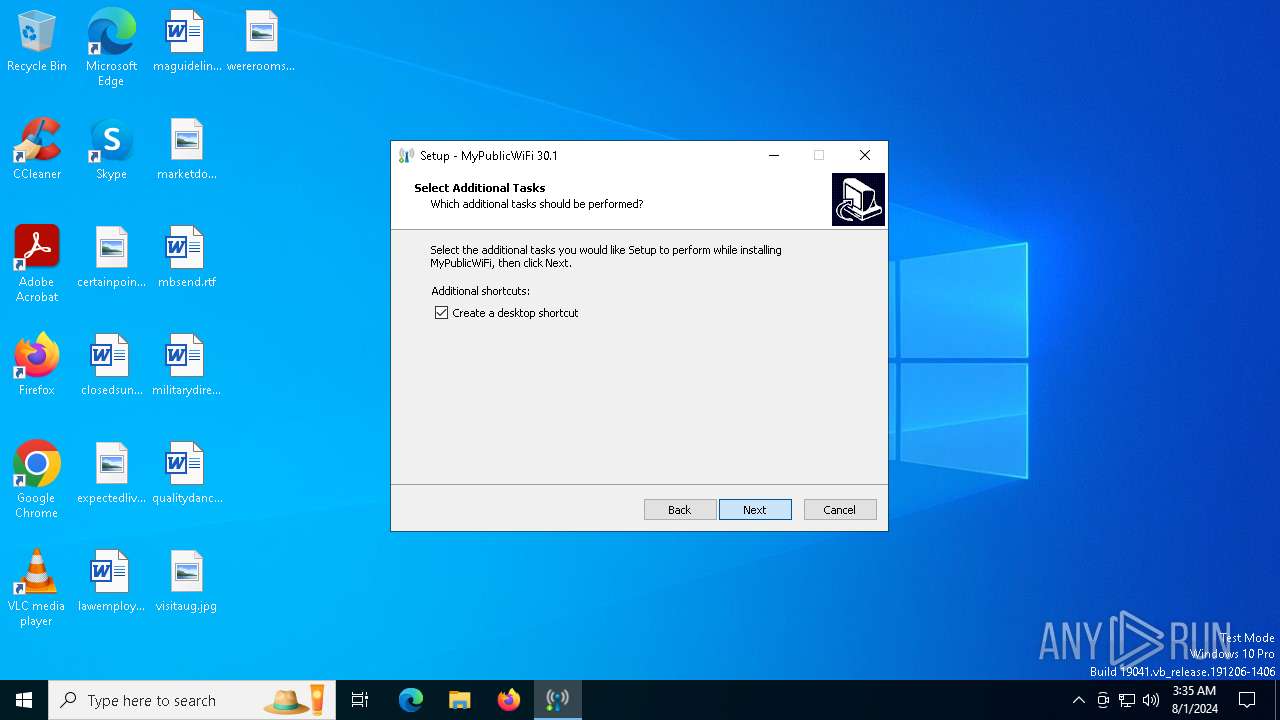
Create files in a temporary directory
- MyPublicWiFi.exe (PID: 6444)
- MyPublicWiFi.exe (PID: 6536)
- MyPublicWiFi.tmp (PID: 6560)
- netcfg.exe (PID: 5908)
- powershell.exe (PID: 236)
- powershell.exe (PID: 6268)
Reads the computer name
- MyPublicWiFi.tmp (PID: 6464)
- MyPublicWiFi.tmp (PID: 6560)
- drvinst.exe (PID: 1360)
- PublicWiFiService.exe (PID: 4236)
- PublicWiFiService.exe (PID: 7580)
- identity_helper.exe (PID: 7304)
- identity_helper.exe (PID: 7284)
- MyPublicWiFi.exe (PID: 7192)
- PublicWiFiService.exe (PID: 1564)
- identity_helper.exe (PID: 8076)
- PublicWiFiService.exe (PID: 6828)
- PublicWiFiService.exe (PID: 7684)
- MyPublicWiFi.exe (PID: 7892)
- PublicWiFiService.exe (PID: 7628)
Process checks computer location settings
- MyPublicWiFi.tmp (PID: 6464)
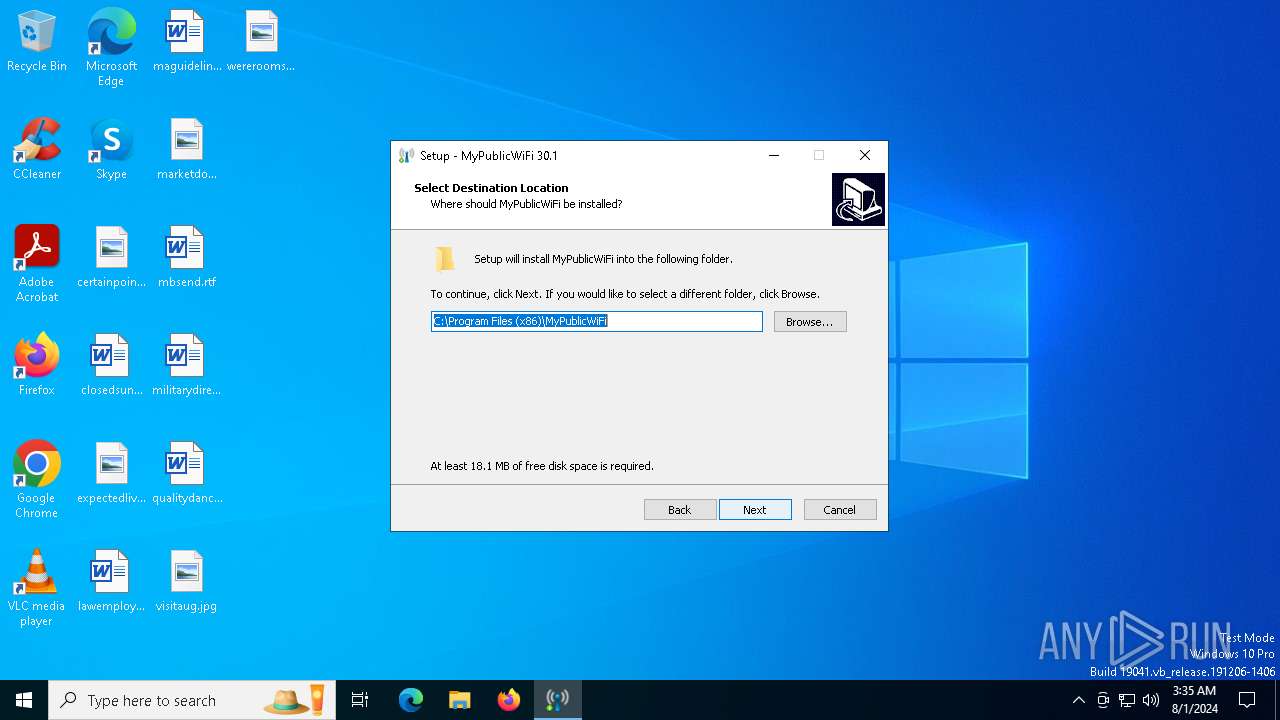
Creates files in the program directory
- MyPublicWiFi.tmp (PID: 6560)
Creates a software uninstall entry
- MyPublicWiFi.tmp (PID: 6560)
Reads the machine GUID from the registry
- certinst.exe (PID: 5880)
- certinst.exe (PID: 1688)
- drvinst.exe (PID: 1360)
Reads the software policy settings
- drvinst.exe (PID: 1360)
- powershell.exe (PID: 236)
- powershell.exe (PID: 6268)
Creates files in the driver directory
- netcfg.exe (PID: 5908)
Reads Microsoft Office registry keys
- MyPublicWiFi.tmp (PID: 6560)
- msedge.exe (PID: 7096)
- msedge.exe (PID: 5988)
- msedge.exe (PID: 7508)
- msedge.exe (PID: 4760)
- MyPublicWiFi.exe (PID: 7192)
Application launched itself
- msedge.exe (PID: 7096)
- msedge.exe (PID: 7508)
- msedge.exe (PID: 5988)
- msedge.exe (PID: 4760)
Manual execution by a user
- msedge.exe (PID: 5988)
- MyPublicWiFi.exe (PID: 7656)
- MyPublicWiFi.exe (PID: 7892)
Reads Environment values
- identity_helper.exe (PID: 7304)
- identity_helper.exe (PID: 7284)
- identity_helper.exe (PID: 8076)
Drops the executable file immediately after the start
- netcfg.exe (PID: 5908)
- msedge.exe (PID: 7508)
Reads security settings of Internet Explorer
- powershell.exe (PID: 236)
- powershell.exe (PID: 6268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 09:48:30+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 133120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | TRUE Software |
| FileDescription: | MyPublicWiFi Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | MyPublicWiFi |
| ProductVersion: |
Total processes
305
Monitored processes
158
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "powershell.exe" Get-Netadapter -IncludeHidden | where InterfaceDescription -match "Direct" | Enable-NetAdapter -Confirm:$false Get-Netadapter -IncludeHidden | where InterfaceDescription -match "Hosted" | Enable-NetAdapter -Confirm:$false Get-Netadapter -IncludeHidden | where InterfaceDescription -match "virtual" | Enable-NetAdapter -Confirm:$false | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | MyPublicWiFi.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5224 --field-trial-handle=2424,i,11424932758241520251,1423518838033140850,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 360 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3304 --field-trial-handle=2424,i,11424932758241520251,1423518838033140850,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=5404 --field-trial-handle=2424,i,11424932758241520251,1423518838033140850,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1248 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=6092 --field-trial-handle=2424,i,11424932758241520251,1423518838033140850,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1360 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{85e49f9a-5aa4-274d-a61d-b2f1cbae562f}\ndisrd_lwf.inf" "9" "4f9ac0c83" "00000000000001CC" "WinSta0\Default" "00000000000001E4" "208" "C:\864B69466849" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
68 405
Read events
68 182
Write events
208
Delete events
15
Modification events
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: A01900003313A0D4C3E3DA01 | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 81E67FAEE907CF3525F3FD0F6D5F8FEC6C2AB6BCF80F0E5B09D7D01A689A32E8 | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files (x86)\MyPublicWiFi\MyPublicWiFi.exe | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 4588731145821FD14587319D682FC250E16324270681905BE3C55A6B1FC2A584 | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip\Parameters |
| Operation: | write | Name: | IPEnableRouter |
Value: 0 | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Wan\{DDF44765-39EA-4B21-8276-7A4C58FAB756} |
| Operation: | write | Name: | Version |
Value: 114470 | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TrueSoftware\MyPublicWiFi |
| Operation: | write | Name: | Theme |
Value: 0 | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TrueSoftware\MyPublicWiFi |
| Operation: | write | Name: | PreferWiFiDirect |
Value: 1 | |||
| (PID) Process: | (6560) MyPublicWiFi.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\TrueSoftware\MyPublicWiFi |
| Operation: | write | Name: | PreferredWiFiDirect |
Value: 0 | |||
Executable files
44
Suspicious files
352
Text files
568
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6560 | MyPublicWiFi.tmp | C:\Program Files (x86)\MyPublicWiFi\Data\is-1ODAM.tmp | — | |
MD5:— | SHA256:— | |||
| 6560 | MyPublicWiFi.tmp | C:\Program Files (x86)\MyPublicWiFi\Data\BlackList | — | |
MD5:— | SHA256:— | |||
| 6444 | MyPublicWiFi.exe | C:\Users\admin\AppData\Local\Temp\is-0NJH7.tmp\MyPublicWiFi.tmp | executable | |
MD5:384082BB1D360A9B76CFD5942A6A7BE3 | SHA256:FEC9722AFBC9AAA0360E2596338908246DBBB211720907BF9881BEC9AAE8E82A | |||
| 6560 | MyPublicWiFi.tmp | C:\Program Files (x86)\MyPublicWiFi\PublicWiFiService.exe | executable | |
MD5:B62B78C5117771F6567E578EAC926EFB | SHA256:23A785C6B10CB402D103FCE330FDE4E40E3A15F5BCDEC06F2526D32CE737208F | |||
| 6560 | MyPublicWiFi.tmp | C:\Program Files (x86)\MyPublicWiFi\Data\is-3PMJE.tmp | csv | |
MD5:37D2609B133DC825E7224DD714BEF7E8 | SHA256:0F443A84A952DC8D5E0E3C32061BC2F7F4DC8B64925EBB3C34C4F192A37EF326 | |||
| 6536 | MyPublicWiFi.exe | C:\Users\admin\AppData\Local\Temp\is-3IEDA.tmp\MyPublicWiFi.tmp | executable | |
MD5:384082BB1D360A9B76CFD5942A6A7BE3 | SHA256:FEC9722AFBC9AAA0360E2596338908246DBBB211720907BF9881BEC9AAE8E82A | |||
| 6560 | MyPublicWiFi.tmp | C:\Program Files (x86)\MyPublicWiFi\MyPublicWiFi.exe | executable | |
MD5:975C5FEEC5D75663570BA21F9A29C4F6 | SHA256:E09D160366ACC41978AADB0C37069648B4C8AF15A42363CE7AAD218B4B50996E | |||
| 6560 | MyPublicWiFi.tmp | C:\Program Files (x86)\MyPublicWiFi\is-3PLA8.tmp | executable | |
MD5:975C5FEEC5D75663570BA21F9A29C4F6 | SHA256:E09D160366ACC41978AADB0C37069648B4C8AF15A42363CE7AAD218B4B50996E | |||
| 6560 | MyPublicWiFi.tmp | C:\Program Files (x86)\MyPublicWiFi\is-OA3BC.tmp | executable | |
MD5:B78EFE7647817E1081E5F754DC223963 | SHA256:A7DFBABA052DFE0C7D47AAEF42CD2BE41A6C50D4D5ED86D71A59F65266E573CC | |||
| 6560 | MyPublicWiFi.tmp | C:\Program Files (x86)\MyPublicWiFi\unins000.exe | executable | |
MD5:B78EFE7647817E1081E5F754DC223963 | SHA256:A7DFBABA052DFE0C7D47AAEF42CD2BE41A6C50D4D5ED86D71A59F65266E573CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
177
DNS requests
184
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | svchost.exe | GET | 304 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | — | — | whitelisted |
6832 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4296 | msedge.exe | GET | 304 | 23.53.40.129:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | DE | — | — | whitelisted |
6888 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4296 | msedge.exe | GET | 304 | 2.18.161.41:80 | http://r3.i.lencr.org/ | DE | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
3276 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4296 | msedge.exe | GET | 304 | 2.18.161.41:80 | http://x1.i.lencr.org/ | DE | — | — | whitelisted |
7936 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/83a0b9d9-1f4a-4df3-b56d-98e05382d780?P1=1723018265&P2=404&P3=2&P4=LX5n8Soha7CiEXDFwwZmdyQJwwxWJI%2bwjQF%2fm09dEA6usjBSb65DjjhqlJ%2bsfbNUy7UuvbMv8AzLjdm8ksd2Jw%3d%3d | DE | binary | 252 b | whitelisted |
7936 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/83a0b9d9-1f4a-4df3-b56d-98e05382d780?P1=1723018265&P2=404&P3=2&P4=LX5n8Soha7CiEXDFwwZmdyQJwwxWJI%2bwjQF%2fm09dEA6usjBSb65DjjhqlJ%2bsfbNUy7UuvbMv8AzLjdm8ksd2Jw%3d%3d | DE | binary | 6.92 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1420 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1076 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 2.16.110.121:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3276 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3276 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4296 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
4296 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |