| File name: | ButtonReaderInstall.exe |
| Full analysis: | https://app.any.run/tasks/15354676-8816-4ae8-98ea-25359f2427f2 |
| Verdict: | Malicious activity |
| Analysis date: | October 23, 2023, 18:38:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 2E520FC8550F2182833EB6C5B860B197 |
| SHA1: | 8DAAC59C9A9D7BF1AD0B6121D3265FF93DC78F73 |
| SHA256: | 8452F89DB8C2DF4B28BE71E2B2DC30BB02E0B4297A472B0B9C4460199600B312 |
| SSDEEP: | 98304:A8jpSiGJ0QOA03s4Mb6o7UhBwd7h82xs6J4cdv8UDxR7vm4kBVBnwGavzmsZ+U3R:vy/XuEJkZ3xLm |
MALICIOUS
Drops the executable file immediately after the start
- ButtonReaderInstall.exe (PID: 3688)
Loads dropped or rewritten executable
- ButtonReaderInstall.exe (PID: 3688)
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- nsD235.tmp (PID: 2968)
Starts application with an unusual extension
- ButtonReaderInstall.exe (PID: 3688)
Checks Windows Trust Settings
- msiexec.exe (PID: 560)
INFO
Reads the computer name
- ButtonReaderInstall.exe (PID: 3688)
- msiexec.exe (PID: 560)
Checks supported languages
- ButtonReaderInstall.exe (PID: 3688)
- nsD235.tmp (PID: 2968)
- nsD2B3.tmp (PID: 2564)
- msiexec.exe (PID: 560)
Creates files in the program directory
- ButtonReaderInstall.exe (PID: 3688)
Create files in a temporary directory
- ButtonReaderInstall.exe (PID: 3688)
- msiexec.exe (PID: 560)
Reads the machine GUID from the registry
- msiexec.exe (PID: 560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 06:39:33+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 263680 |
| UninitializedDataSize: | 8192 |
| EntryPoint: | 0x324f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
47
Monitored processes
7
Malicious processes
1
Suspicious processes
1
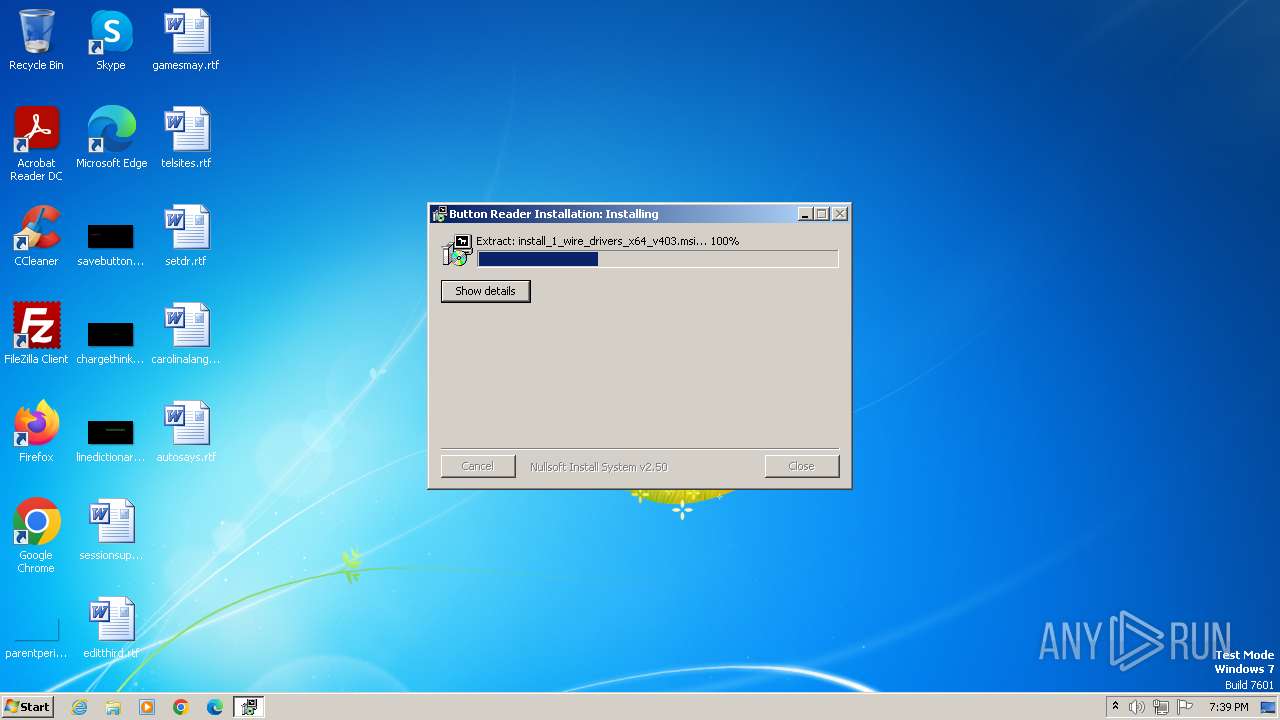
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1884 | "C:\Users\admin\AppData\Local\Temp\ButtonReaderInstall.exe" | C:\Users\admin\AppData\Local\Temp\ButtonReaderInstall.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2392 | regedit /s "C:\Program Files\Maxim Integrated Products\1-Wire Drivers x64\1-Wire_Trusted_Publisher.reg" | C:\Windows\regedit.exe | — | nsD235.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | "C:\Users\admin\AppData\Local\Temp\nscD234.tmp\nsD2B3.tmp" msiexec.exe /i "C:\Program Files\Maxim Integrated Products\1-Wire Drivers x64\install_1_wire_drivers_x64_v403.msi" /qn /norestart | C:\Users\admin\AppData\Local\Temp\nscD234.tmp\nsD2B3.tmp | — | ButtonReaderInstall.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1633 Modules
| |||||||||||||||
| 2956 | msiexec.exe /i "C:\Program Files\Maxim Integrated Products\1-Wire Drivers x64\install_1_wire_drivers_x64_v403.msi" /qn /norestart | C:\Windows\System32\msiexec.exe | — | nsD2B3.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1633 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2968 | "C:\Users\admin\AppData\Local\Temp\nscD234.tmp\nsD235.tmp" regedit /s "C:\Program Files\Maxim Integrated Products\1-Wire Drivers x64\1-Wire_Trusted_Publisher.reg" | C:\Users\admin\AppData\Local\Temp\nscD234.tmp\nsD235.tmp | — | ButtonReaderInstall.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3688 | "C:\Users\admin\AppData\Local\Temp\ButtonReaderInstall.exe" | C:\Users\admin\AppData\Local\Temp\ButtonReaderInstall.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
5 647
Read events
5 634
Write events
13
Delete events
0
Modification events
| (PID) Process: | (560) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3688) ButtonReaderInstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | PATH |
Value: C:\Program Files\Common Files\Oracle\Java\javapath;C:\ProgramData\Oracle\Java\javapath;%SystemRoot%\system32;%SystemRoot%;%SystemRoot%\System32\Wbem;%SYSTEMROOT%\System32\WindowsPowerShell\v1.0\;%systemroot%\System32\WindowsPowerShell\v1.0\;C:\Program Files\PowerShell\7\ | |||
Executable files
3
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | ButtonReaderInstall.exe | C:\Program Files\Maxim Integrated Products\1-Wire Drivers x64\install_1_wire_drivers_x64_v403.msi | — | |
MD5:— | SHA256:— | |||
| 560 | msiexec.exe | C:\Windows\Installer\1ed38a.msi | — | |
MD5:— | SHA256:— | |||
| 3688 | ButtonReaderInstall.exe | C:\Users\admin\AppData\Local\Temp\nsvCD80.tmp | — | |
MD5:— | SHA256:— | |||
| 3688 | ButtonReaderInstall.exe | C:\Users\admin\AppData\Local\Temp\nscD234.tmp\nsD235.tmp | executable | |
MD5:F9BE9E9ED447E7650434A7E46431BAEA | SHA256:5797BA15A18B8C713DF62D4A630DDD81FEFEEB01A87D65D486D829991A1EDC83 | |||
| 3688 | ButtonReaderInstall.exe | C:\Program Files\Maxim Integrated Products\1-Wire Drivers x64\1-Wire_Trusted_Publisher.reg | text | |
MD5:5055CA45A05B36D5520742A6776A4C0E | SHA256:698D448607E46C7D2C9721BFFE29DE9A9E51C2224BD1FDB87306CBC3C1011BAB | |||
| 3688 | ButtonReaderInstall.exe | C:\Users\admin\AppData\Local\Temp\nscD234.tmp\nsExec.dll | executable | |
MD5:F9BE9E9ED447E7650434A7E46431BAEA | SHA256:5797BA15A18B8C713DF62D4A630DDD81FEFEEB01A87D65D486D829991A1EDC83 | |||
| 560 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 560 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:62B41350A3FAE8E778B1B6189A636A33 | SHA256:4C356E258D1EE2E7424ACB8D612DC36A3745C995DCD32FD6DB0CD96389779D6F | |||
| 560 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CabD4F1.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 560 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\TarD4F2.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
560 | msiexec.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1d625fb5f4a4a1fd | US | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
560 | msiexec.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |