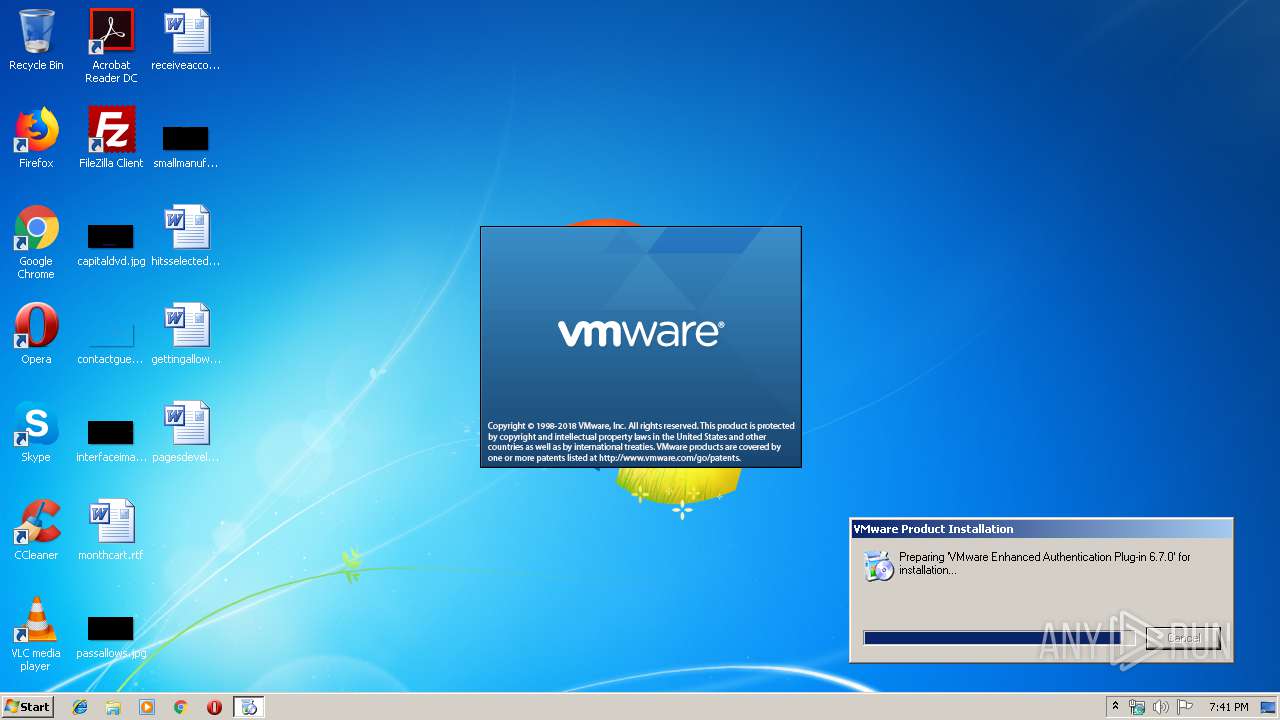
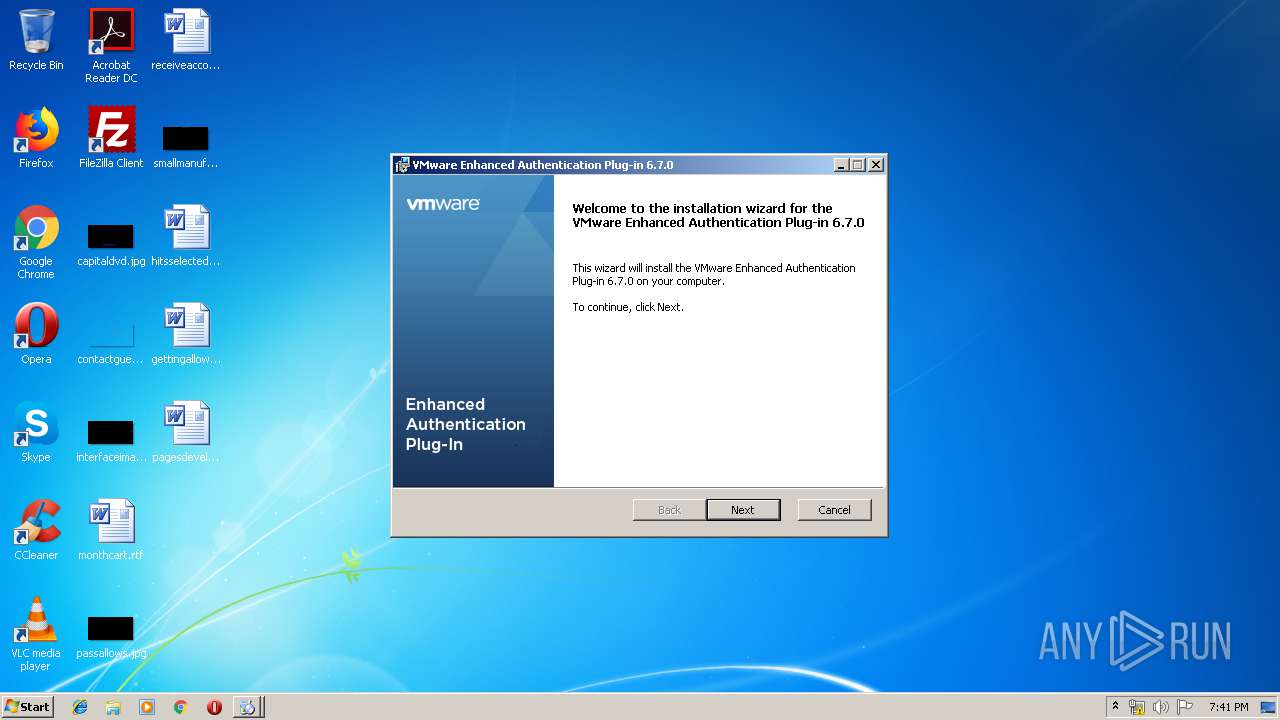
| download: | VMware-EnhancedAuthenticationPlugin-6.7.0.exe |
| Full analysis: | https://app.any.run/tasks/b9ad512f-1f6d-4083-a9cc-473bff82801a |
| Verdict: | Suspicious activity |
| Analysis date: | December 06, 2019, 19:40:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8AF0372F4ADCC7A174E5D150EA11E530 |
| SHA1: | E0C06A9CC9BE7373FA4000508755DB4C02718E41 |
| SHA256: | 8441D77A98CFC7C58B31062918BD292459C394DEE4A3C30653B8BEC766F9D683 |
| SSDEEP: | 786432:wWYXhMZ2N6SKCUMFdz/ccprqVAxJakXns:lYyZ2N6TZMH/ccpAAxE |
MALICIOUS
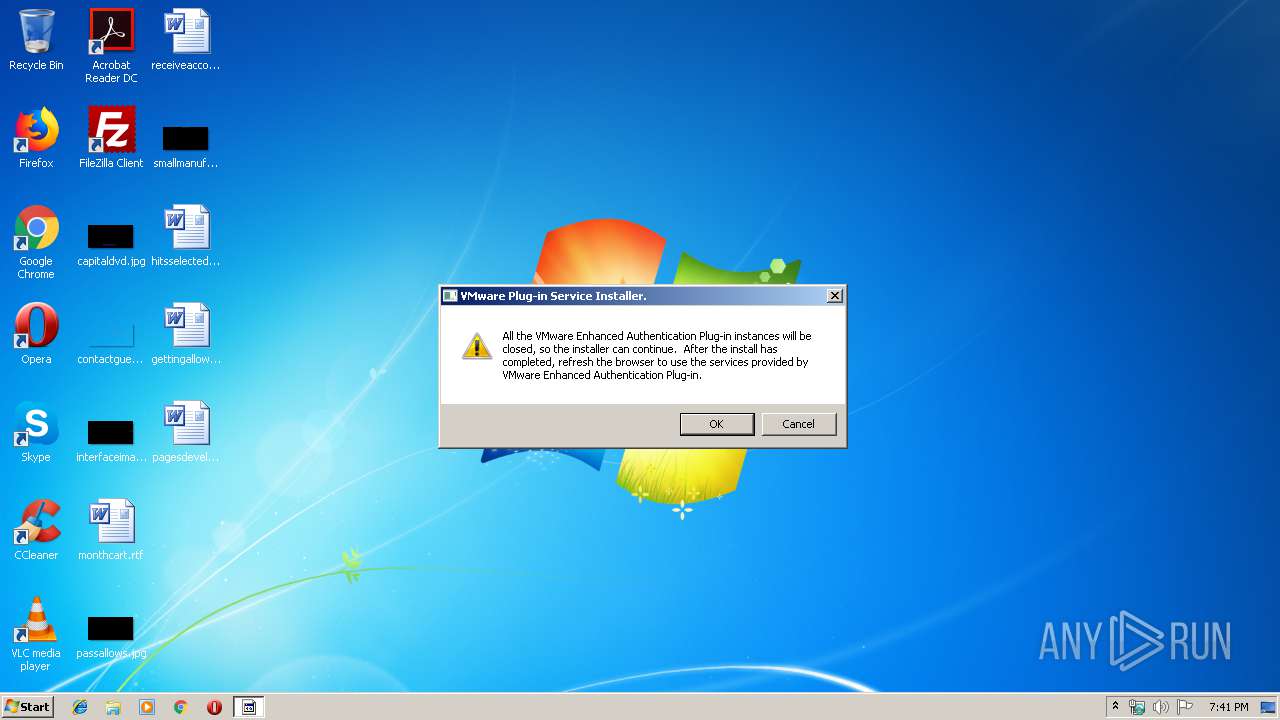
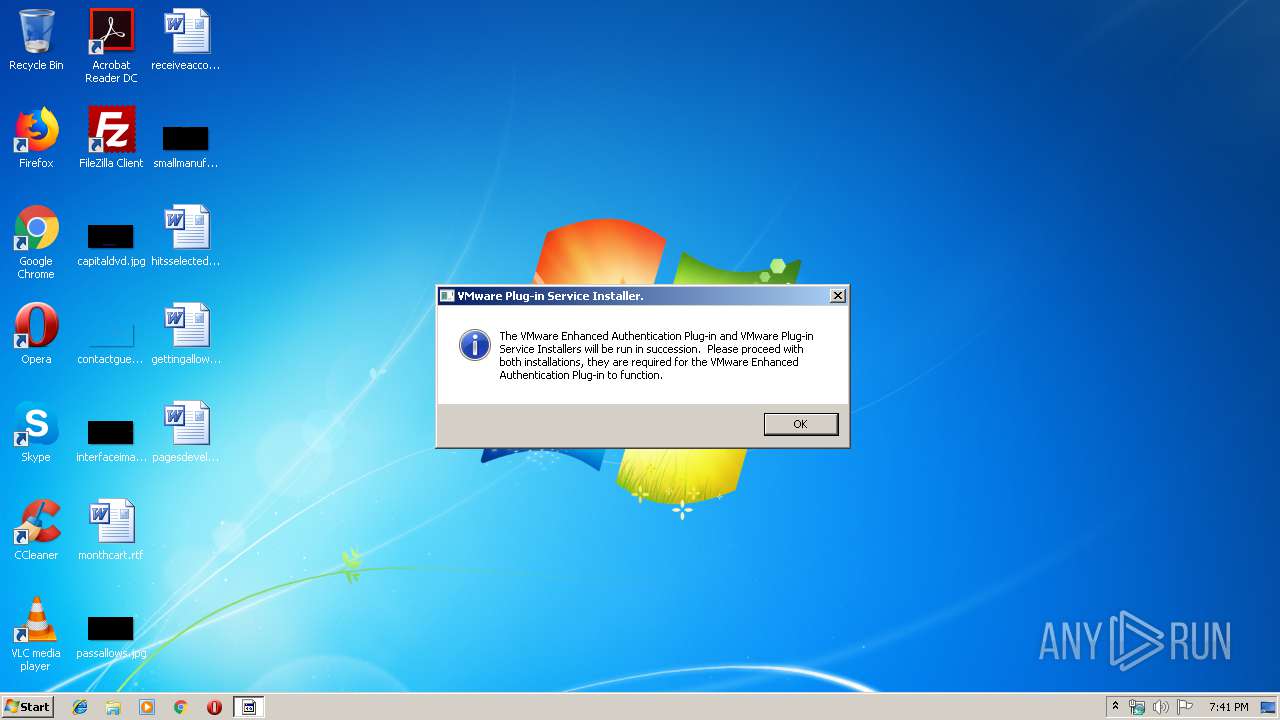
Application was dropped or rewritten from another process
- runsetups.exe (PID: 4064)
- VMware-ClientIntegrationPlugin.win32.exe (PID: 856)
Starts NET.EXE for service management
- runsetups.exe (PID: 4064)
SUSPICIOUS
Executable content was dropped or overwritten
- VMware-EnhancedAuthenticationPlugin-6.7.0.exe (PID: 1404)
- VMware-ClientIntegrationPlugin.win32.exe (PID: 856)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 17:27:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 104960 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14b04 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.20.0.0 |
| ProductVersionNumber: | 9.20.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 9.2 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2010 16:27:35 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 9.20 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Nov-2010 16:27:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000199EA | 0x00019A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60849 |
.rdata | 0x0001B000 | 0x00004494 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.36802 |
.data | 0x00020000 | 0x00005A48 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.37054 |
.sxdata | 0x00026000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00027000 | 0x00000A60 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.30196 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.44049 | 700 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.18403 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
500 | 3.09294 | 184 | UNKNOWN | English - United States | RT_DIALOG |
Imports
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
44
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | .\VMware-ClientIntegrationPlugin.win32.exe | C:\Users\admin\AppData\Local\Temp\7zSDEA2.tmp\VMware-ClientIntegrationPlugin.win32.exe | runsetups.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: HIGH Description: VMware installation launcher Exit code: 0 Version: 6.7.0.4882 Modules
| |||||||||||||||
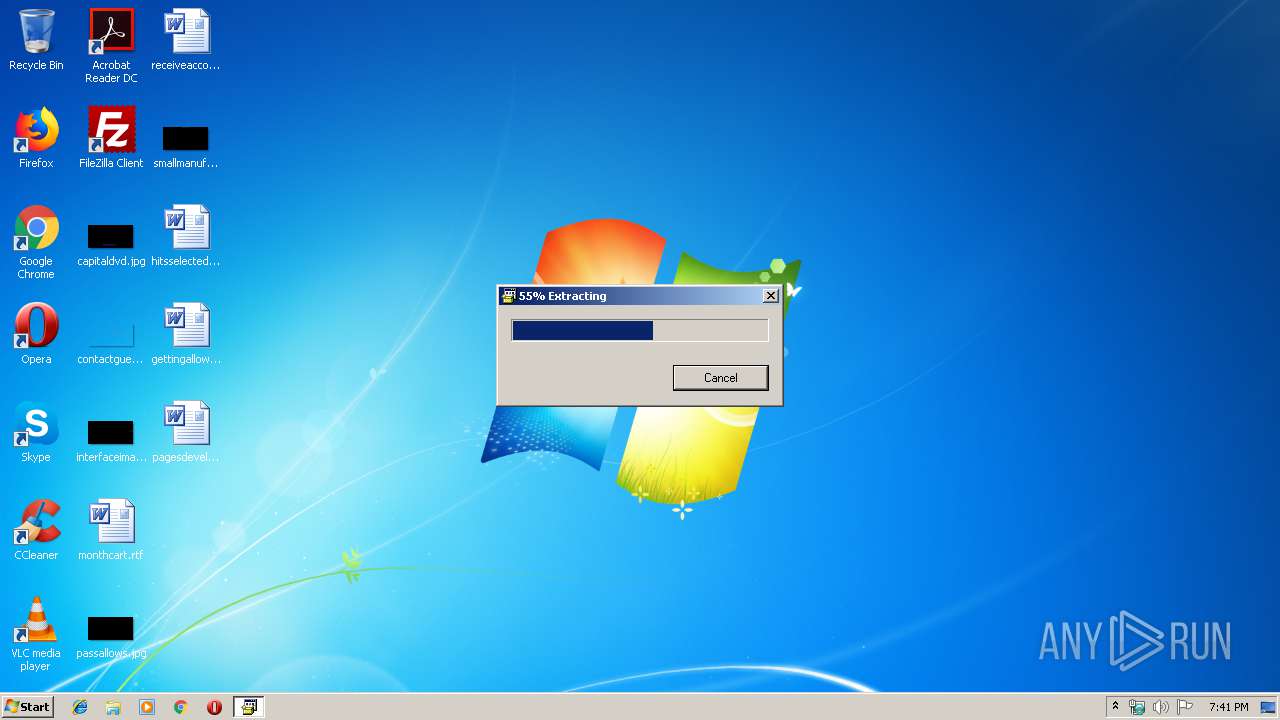
| 1404 | "C:\Users\admin\AppData\Local\Temp\VMware-EnhancedAuthenticationPlugin-6.7.0.exe" | C:\Users\admin\AppData\Local\Temp\VMware-EnhancedAuthenticationPlugin-6.7.0.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 2536 | C:\Windows\system32\net stop CipMsgProxyService | C:\Windows\system32\net.exe | — | runsetups.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\AppData\Local\Temp\VMware-EnhancedAuthenticationPlugin-6.7.0.exe" | C:\Users\admin\AppData\Local\Temp\VMware-EnhancedAuthenticationPlugin-6.7.0.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX Exit code: 3221226540 Version: 9.20 Modules
| |||||||||||||||
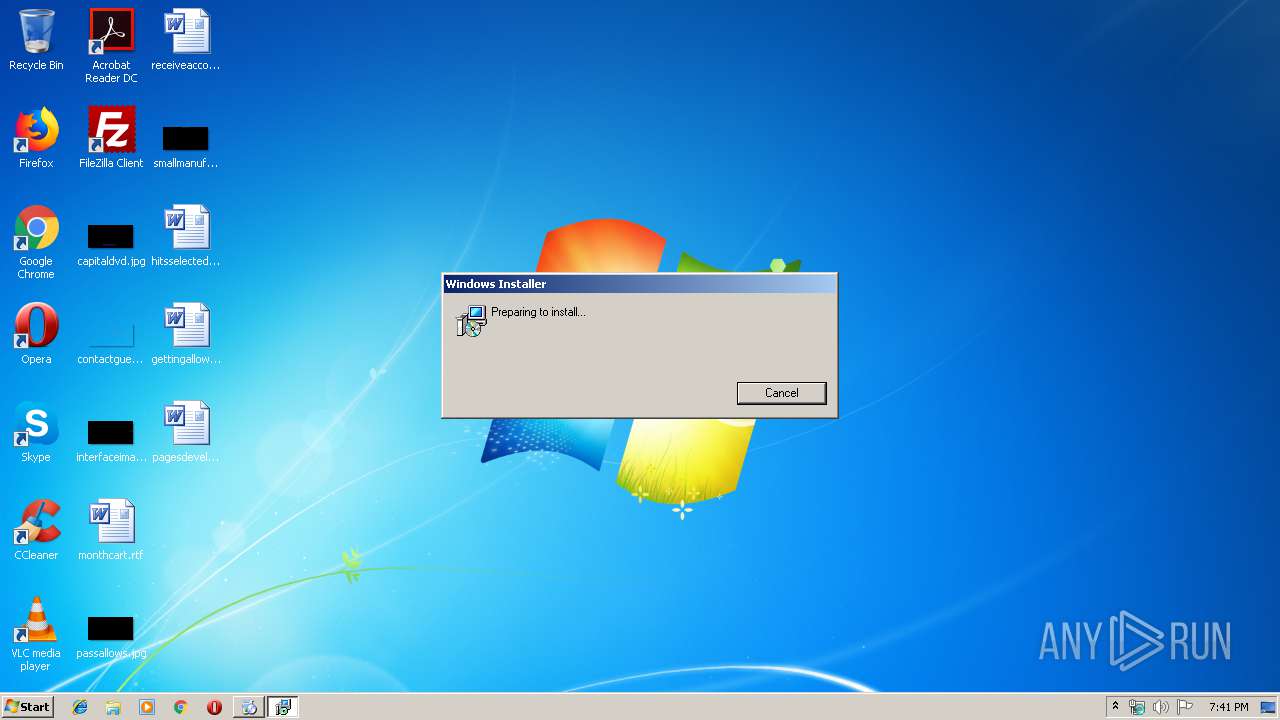
| 3532 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3844 | C:\Windows\system32\net1 stop CipMsgProxyService | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4064 | .\runsetups.exe | C:\Users\admin\AppData\Local\Temp\7zSDEA2.tmp\runsetups.exe | VMware-EnhancedAuthenticationPlugin-6.7.0.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
136
Read events
126
Write events
10
Delete events
0
Modification events
| (PID) Process: | (856) VMware-ClientIntegrationPlugin.win32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
5
Suspicious files
5
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 856 | VMware-ClientIntegrationPlugin.win32.exe | C:\Users\admin\AppData\Local\Temp\{AA33F9ED-8FD1-480D-8786-FB2E2F9BE1EE}~setup\VMware-ClientIntegrationPlugin-csd-6.7.0.8730067.msi | — | |
MD5:— | SHA256:— | |||
| 856 | VMware-ClientIntegrationPlugin.win32.exe | C:\Users\admin\AppData\Local\Temp\Cab73FD.tmp | — | |
MD5:— | SHA256:— | |||
| 856 | VMware-ClientIntegrationPlugin.win32.exe | C:\Users\admin\AppData\Local\Temp\Tar73FE.tmp | — | |
MD5:— | SHA256:— | |||
| 856 | VMware-ClientIntegrationPlugin.win32.exe | C:\Users\admin\AppData\Local\Temp\Cab740E.tmp | — | |
MD5:— | SHA256:— | |||
| 856 | VMware-ClientIntegrationPlugin.win32.exe | C:\Users\admin\AppData\Local\Temp\Tar740F.tmp | — | |
MD5:— | SHA256:— | |||
| 856 | VMware-ClientIntegrationPlugin.win32.exe | C:\Users\admin\AppData\Local\Temp\Cab74AD.tmp | — | |
MD5:— | SHA256:— | |||
| 856 | VMware-ClientIntegrationPlugin.win32.exe | C:\Users\admin\AppData\Local\Temp\Tar74AE.tmp | — | |
MD5:— | SHA256:— | |||
| 4064 | runsetups.exe | C:\Users\admin\AppData\Local\VMware\CIP\csd\config\cipRunSetups-settings.js | text | |
MD5:— | SHA256:— | |||
| 1404 | VMware-EnhancedAuthenticationPlugin-6.7.0.exe | C:\Users\admin\AppData\Local\Temp\7zSDEA2.tmp\VMware-ClientIntegrationPlugin.win32.exe | executable | |
MD5:6BA8E99D2FA62DEC89AEEEEA4CAEB1FD | SHA256:42D7E18CBDAA940D528B31C914CDB3684B0CD26A4EF7EBABF3061039887D7485 | |||
| 1404 | VMware-EnhancedAuthenticationPlugin-6.7.0.exe | C:\Users\admin\AppData\Local\Temp\7zSDEA2.tmp\VMware-ClientIntegrationService.win32.exe | executable | |
MD5:16354EEB3A64712D326F533287CFCCD8 | SHA256:46C0B288C3D7FEF32B3279BAA7D472269669D7B2EF451776543C288271D08174 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | VMware-ClientIntegrationPlugin.win32.exe | GET | 200 | 92.122.213.201:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
856 | VMware-ClientIntegrationPlugin.win32.exe | 92.122.213.201:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
runsetups.exe | CodeSet_Init: no ICU
|
VMware-ClientIntegrationPlugin.win32.exe | Start Pre-load DLLs.
|